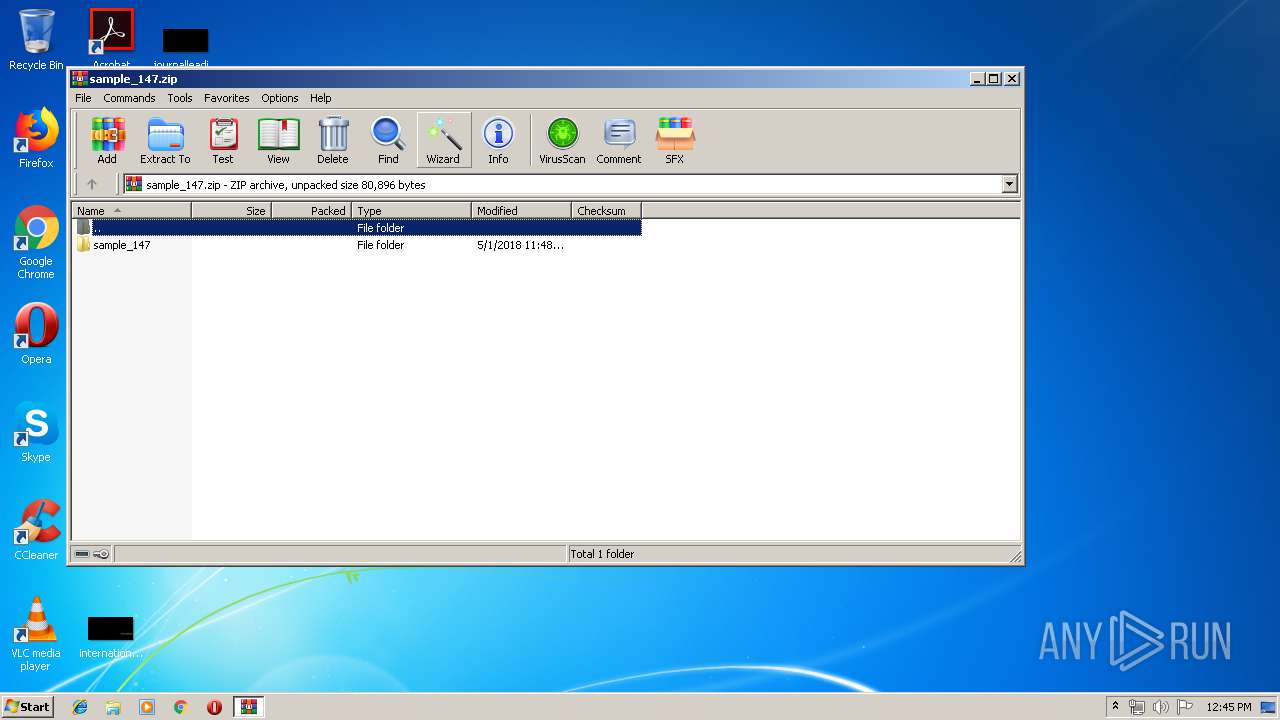
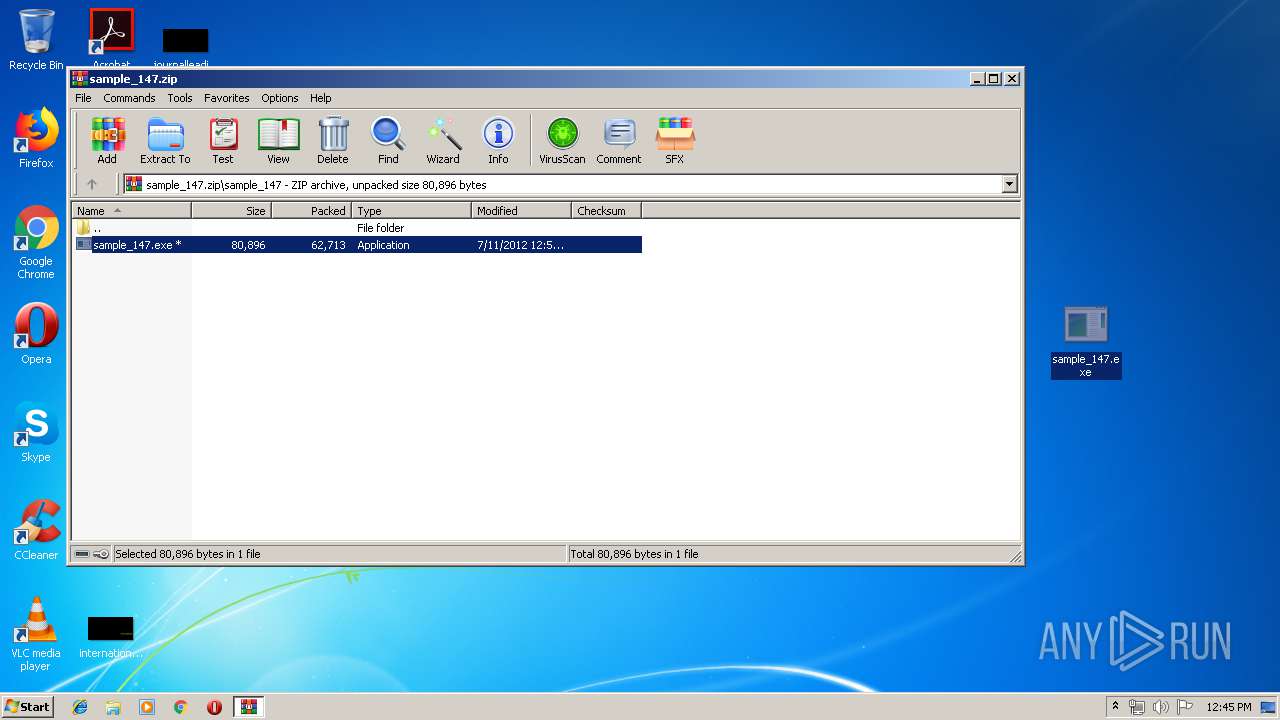
| File name: | sample_147.zip |
| Full analysis: | https://app.any.run/tasks/5df559a1-bd96-4522-b21e-ee0da0d930eb |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 11:44:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | D8D8AF12F55A6EE940DD02C8169EE74B |
| SHA1: | 87D1D92541FA0A56B68A850AF701F0D72E6625DA |
| SHA256: | 9B81D27D4078F5B9DDB041B319B638F4D2329B6C641A2F589CDEA65D2831D4DB |
| SSDEEP: | 1536:PMdsXxZMTkLbih0S+T7cQ3M4ZiZIIGPaPh2HSlMXmv3EFw:8DCbZzcUMRZyHPX406 |
MALICIOUS
Application was dropped or rewritten from another process
- sample_147.exe (PID: 3604)
- KB00137927.exe (PID: 3656)
Application was injected by another process
- ctfmon.exe (PID: 3780)
- taskeng.exe (PID: 3756)
- dwm.exe (PID: 1980)
- explorer.exe (PID: 2044)
- windanr.exe (PID: 2436)
Changes the autorun value in the registry
- sample_147.exe (PID: 3604)
Runs injected code in another process
- KB00137927.exe (PID: 3656)
SUSPICIOUS
Starts itself from another location
- sample_147.exe (PID: 3604)
Starts CMD.EXE for commands execution
- sample_147.exe (PID: 3604)
Creates files in the user directory
- sample_147.exe (PID: 3604)
- rundll32.exe (PID: 3992)
Executable content was dropped or overwritten
- sample_147.exe (PID: 3604)
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 2044)
Reads Internet Cache Settings
- rundll32.exe (PID: 3992)
INFO
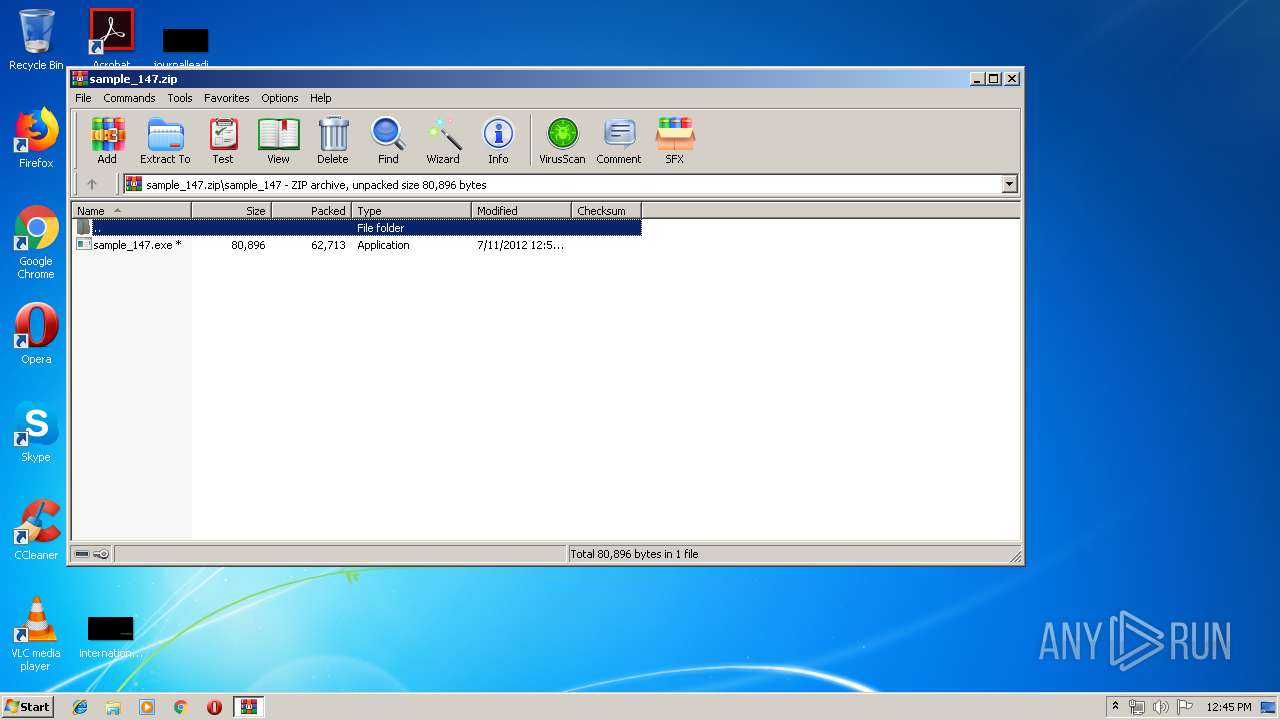
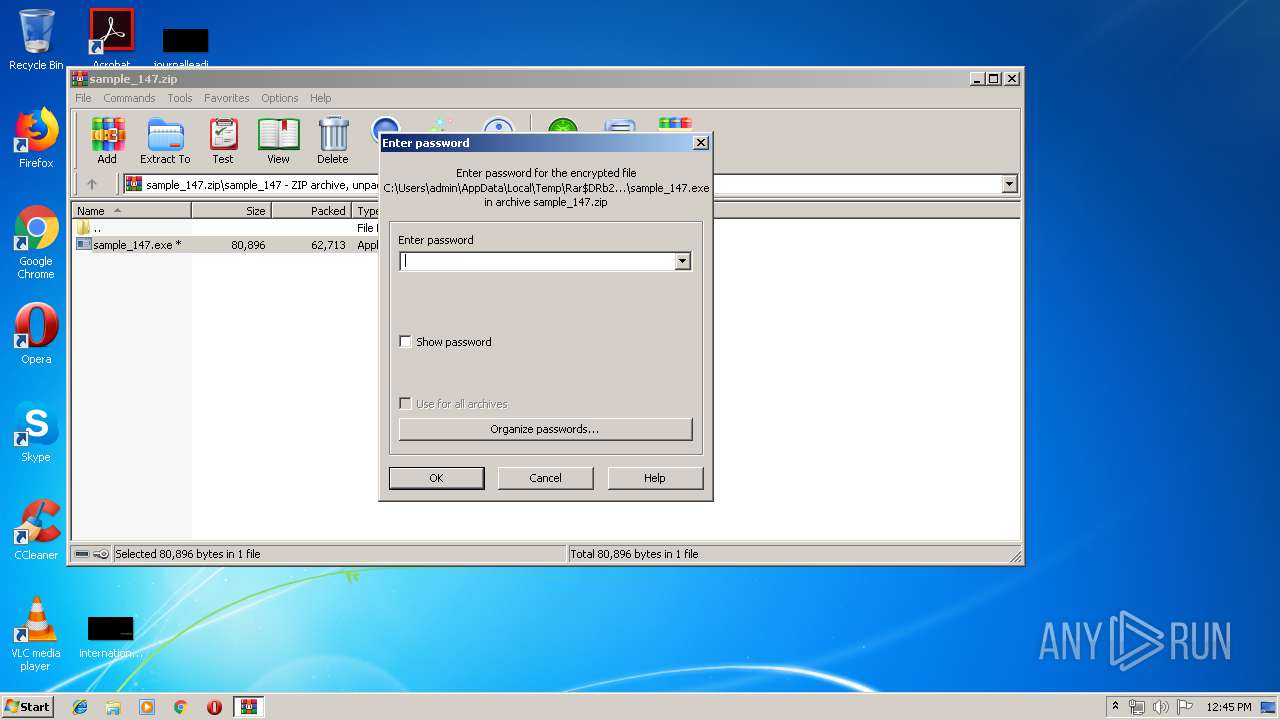
Manual execution by user
- sample_147.exe (PID: 3604)
- rundll32.exe (PID: 3992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:05:01 18:48:23 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | sample_147/ |
Total processes
38
Monitored processes
10
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1980 | "C:\Windows\system32\Dwm.exe" | C:\Windows\System32\dwm.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2044 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2436 | "windanr.exe" | C:\Windows\system32\windanr.exe | qemu-ga.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2688 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\sample_147.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3604 | "C:\Users\admin\Desktop\sample_147.exe" | C:\Users\admin\Desktop\sample_147.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3656 | "C:\Users\admin\AppData\Roaming\KB00137927.exe" | C:\Users\admin\AppData\Roaming\KB00137927.exe | — | sample_147.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3672 | "C:\Windows\system32\cmd.exe" /c "C:\Users\admin\AppData\Local\Temp\exp83D9.tmp.bat" | C:\Windows\system32\cmd.exe | — | sample_147.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3756 | taskeng.exe {7E1E8C9A-BE84-4A45-8FE2-CD8D351321B8} | C:\Windows\System32\taskeng.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Engine Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3780 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3992 | "C:\Windows\system32\rundll32.exe" "C:\Windows\system32\WININET.dll",DispatchAPICall 1 | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 171
Read events
2 150
Write events
21
Delete events
0
Modification events
| (PID) Process: | (2688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2688) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample_147.zip | |||
| (PID) Process: | (2688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2688) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2044) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (2044) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
2
Suspicious files
0
Text files
6
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2688 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2688.40843\sample_147\sample_147.exe | — | |
MD5:— | SHA256:— | |||
| 3604 | sample_147.exe | C:\Users\admin\AppData\Local\Temp\exp83D9.tmp.bat | — | |
MD5:— | SHA256:— | |||
| 3992 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\ZRVXNZYV\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3992 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2044 | explorer.exe | C:\Users\admin\Desktop\sample_147.exe | executable | |
MD5:35C8205B1C44C6234923B4CB21C5F24B | SHA256:994DD3AD07C7EF4DFD15F6FE60D384B0CC23EBECA1477EF320E3ABB376BFE329 | |||
| 3604 | sample_147.exe | C:\Users\admin\AppData\Roaming\KB00137927.exe | executable | |
MD5:35C8205B1C44C6234923B4CB21C5F24B | SHA256:994DD3AD07C7EF4DFD15F6FE60D384B0CC23EBECA1477EF320E3ABB376BFE329 | |||
| 3992 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3992 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:D7A950FEFD60DBAA01DF2D85FEFB3862 | SHA256:75D0B1743F61B76A35B1FEDD32378837805DE58D79FA950CB6E8164BFA72073A | |||
| 3992 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3992 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\9TVIO3ME\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
0
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2044 | explorer.exe | POST | — | 94.23.49.51:8080 | http://94.23.49.51:8080/za/v_01_b/in/ | FR | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2044 | explorer.exe | 94.23.49.51:8080 | — | OVH SAS | FR | malicious |