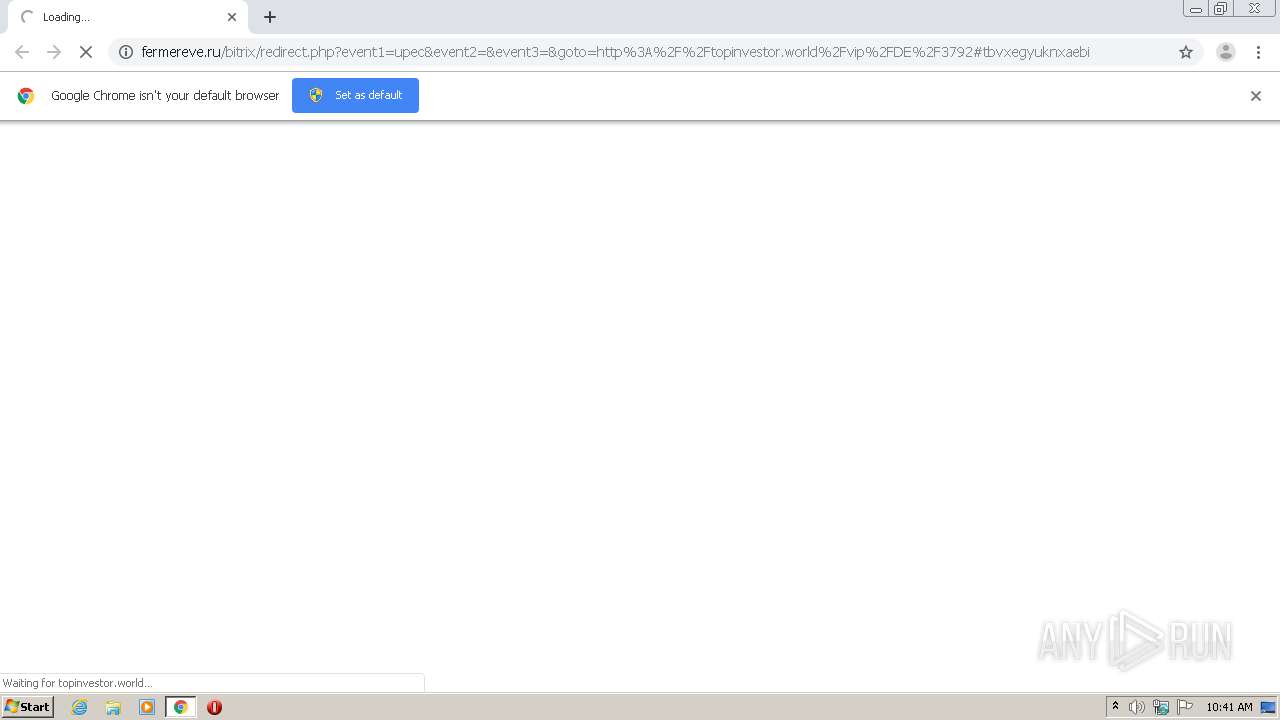
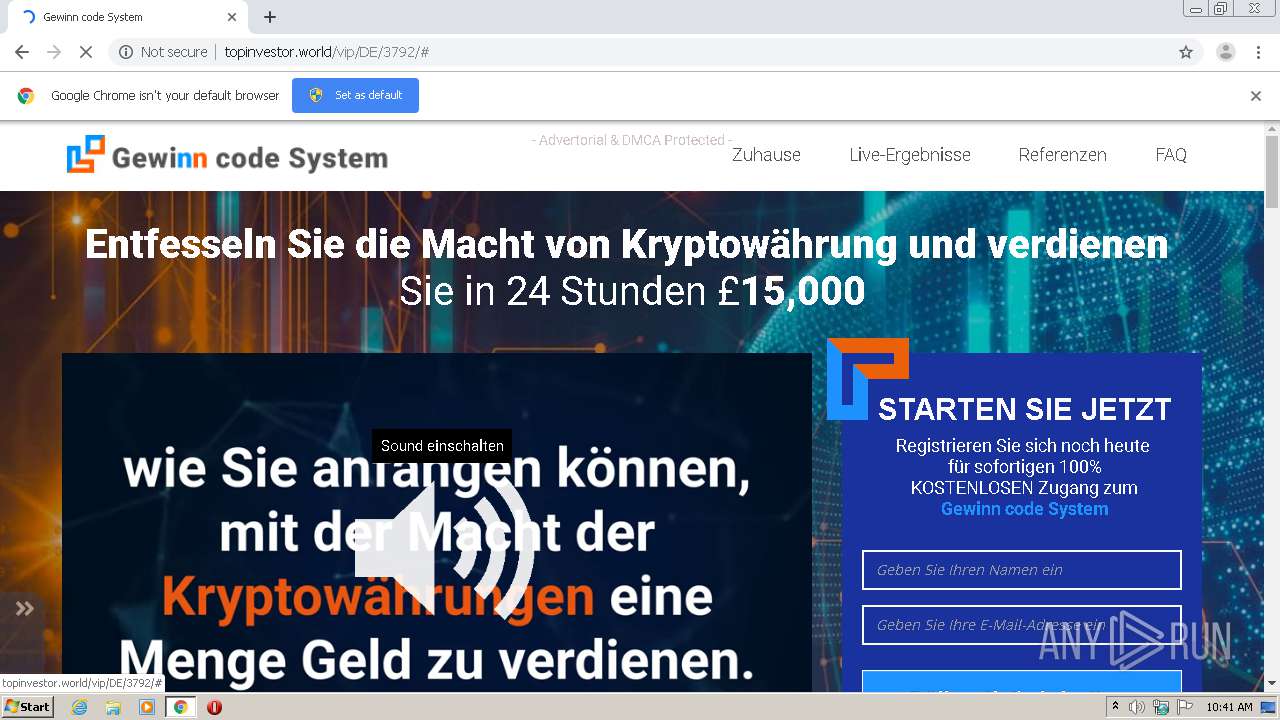
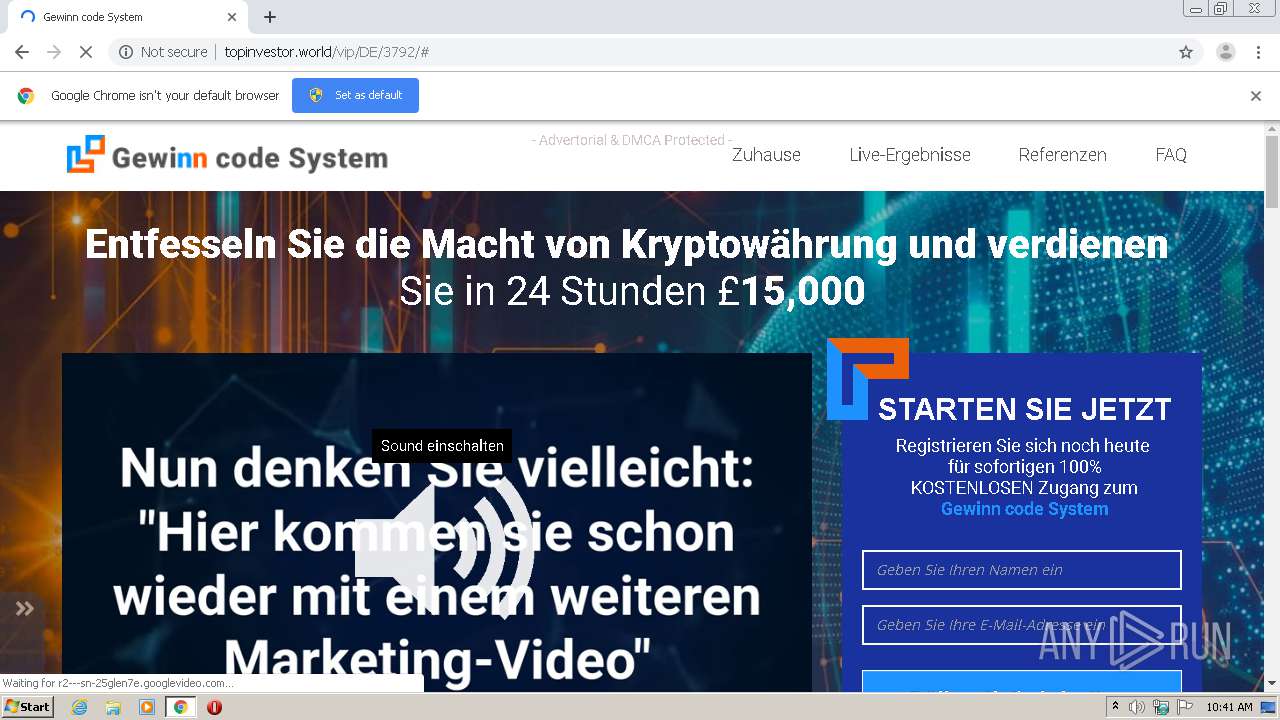
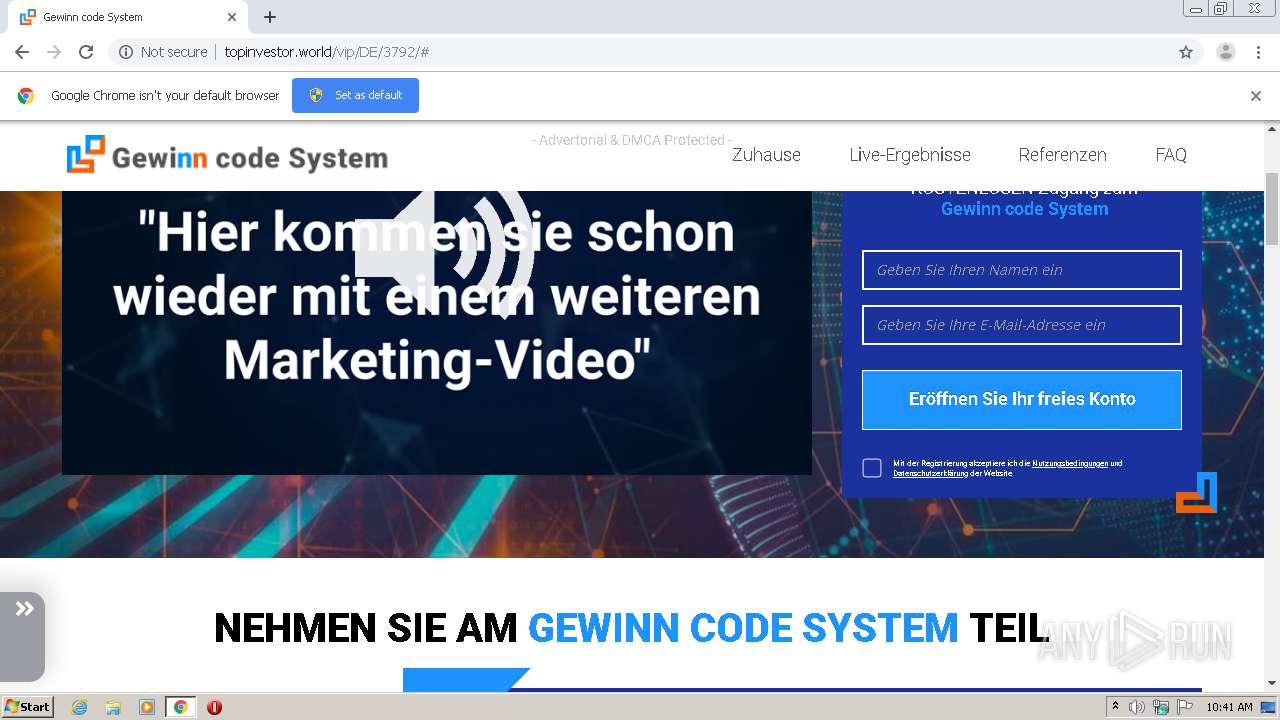
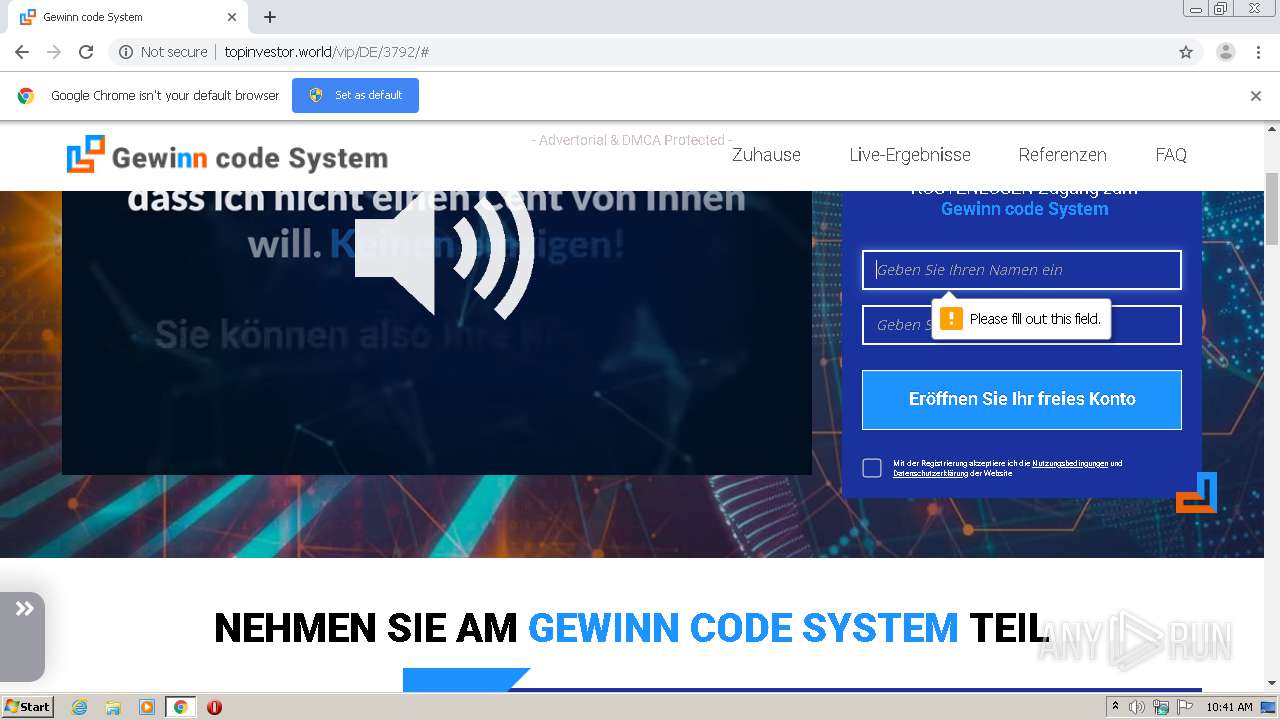
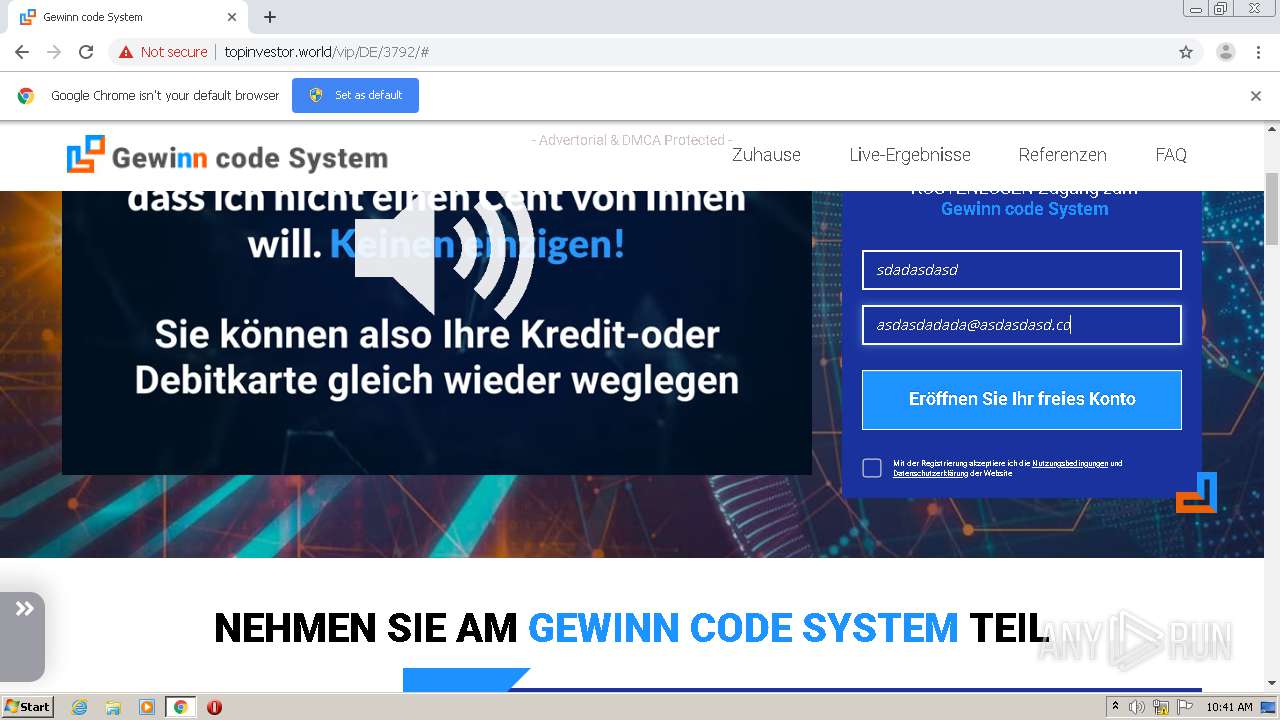
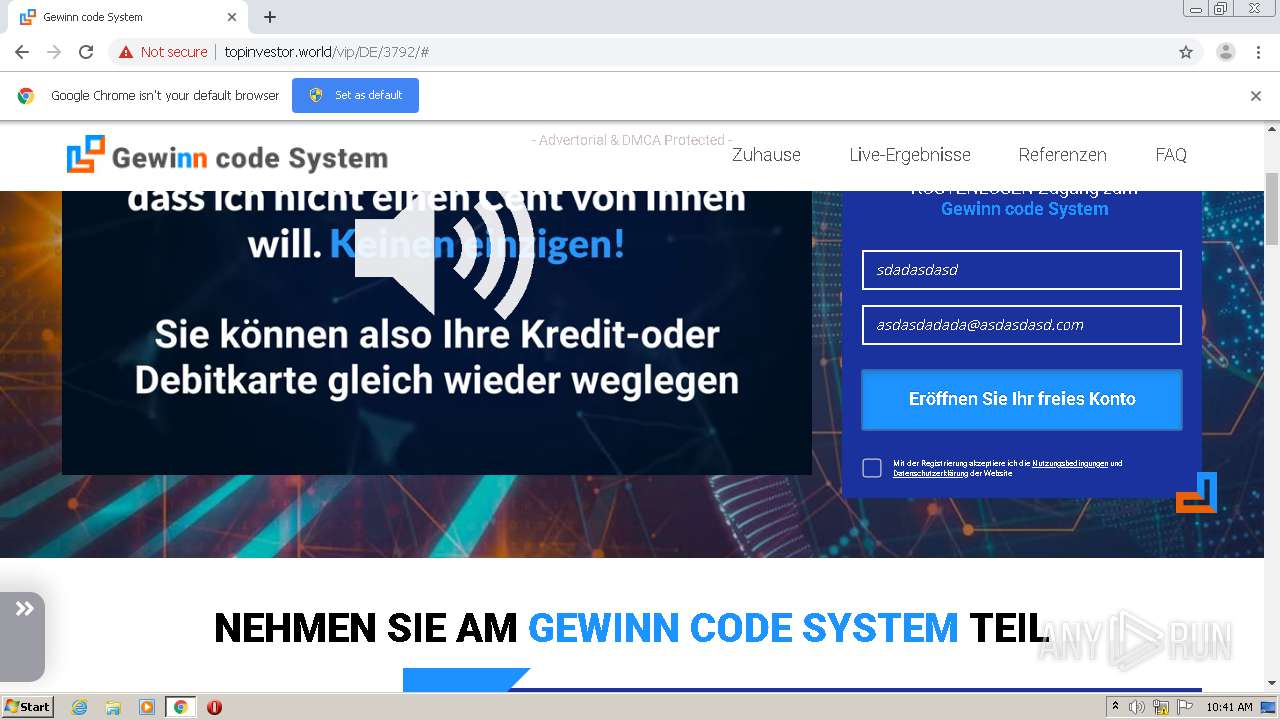
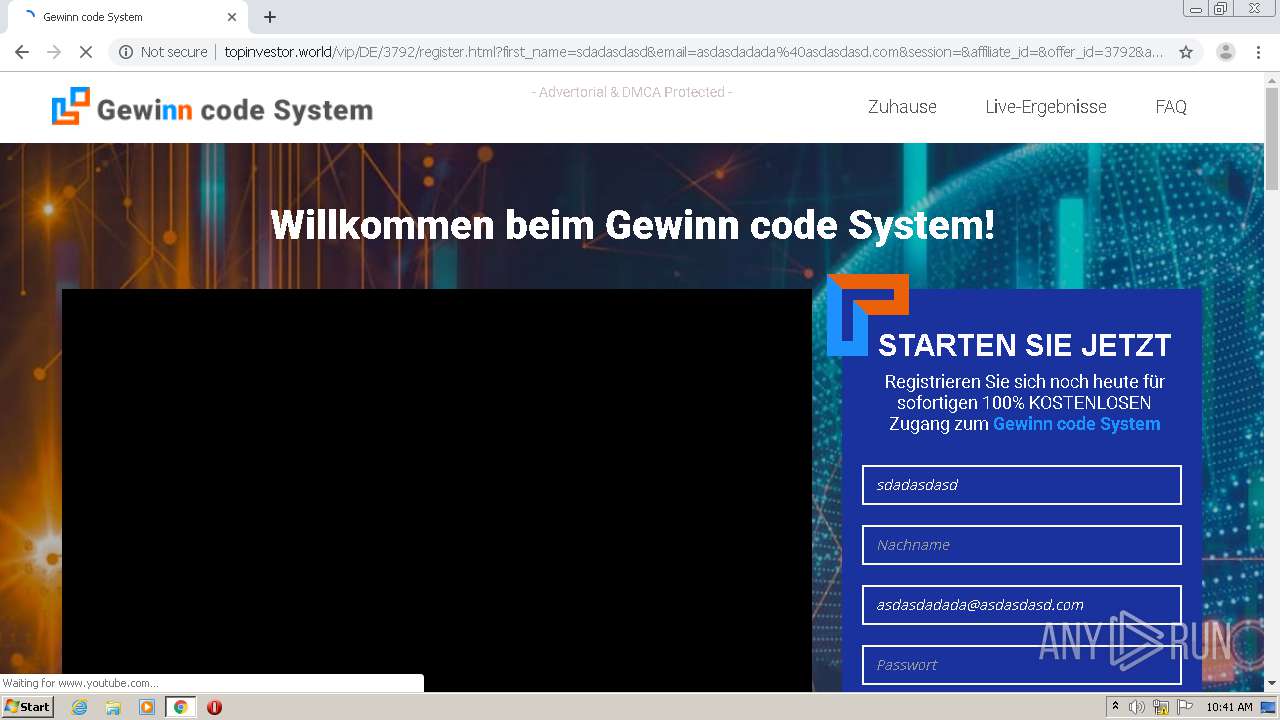
| URL: | http://fermereve.ru/bitrix/redirect.php?event1=upec&event2=&event3=&goto=http%3A%2F%2Ftopinvestor.world%2Fvip%2FDE%2F3792#tbvxegyuknxaebi |
| Full analysis: | https://app.any.run/tasks/899ea0b3-3b79-4545-a5b4-6722e8e18062 |
| Verdict: | Malicious activity |
| Analysis date: | April 21, 2021, 09:40:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C80CFE18D4EF4EB363602321A0D7CEE0 |
| SHA1: | 6C458C41DB249696688EBED93EE7603D5F0E7BF9 |
| SHA256: | 9B7D73CFE53E6D355C430A5D3795FA5F1DB07F31DF3A24E08632DFF6AA628038 |
| SSDEEP: | 3:N1KYkiMK6jTuRXPKWuCKpJsXjdgPAzTpjzwGdAM:CYlMK6jKxNYbszSm1D |
MALICIOUS
No malicious indicators.SUSPICIOUS
Drops a file with a compile date too recent
- chrome.exe (PID: 684)
Modifies files in Chrome extension folder
- chrome.exe (PID: 684)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 1504)
Reads the hosts file
- chrome.exe (PID: 1504)
- chrome.exe (PID: 684)
Application launched itself
- chrome.exe (PID: 684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
68
Monitored processes
31
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,11359946229961989995,13198071763923980538,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17480022619261376801 --mojo-platform-channel-handle=3712 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://fermereve.ru/bitrix/redirect.php?event1=upec&event2=&event3=&goto=http%3A%2F%2Ftopinvestor.world%2Fvip%2FDE%2F3792#tbvxegyuknxaebi" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,11359946229961989995,13198071763923980538,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13094236053653275167 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2264 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,11359946229961989995,13198071763923980538,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10461760984758443292 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3304 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,11359946229961989995,13198071763923980538,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=76852430098887479 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3616 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,11359946229961989995,13198071763923980538,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11643758428008603048 --mojo-platform-channel-handle=3740 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,11359946229961989995,13198071763923980538,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14266287365350106290 --mojo-platform-channel-handle=4452 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,11359946229961989995,13198071763923980538,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=12453106298736624467 --mojo-platform-channel-handle=1632 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,11359946229961989995,13198071763923980538,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6142341533188143198 --mojo-platform-channel-handle=3468 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1408 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
746
Read events
669
Write events
73
Delete events
4
Modification events
| (PID) Process: | (684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1892) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 684-13263471667224625 |
Value: 259 | |||
| (PID) Process: | (684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (684) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
78
Text files
312
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-607FF333-2AC.pma | — | |
MD5:— | SHA256:— | |||
| 684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c13d7fa0-db84-462d-968f-c01770e06d41.tmp | — | |
MD5:— | SHA256:— | |||
| 684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RF134375.TMP | text | |
MD5:— | SHA256:— | |||
| 684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1342b9.TMP | text | |
MD5:— | SHA256:— | |||
| 684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF13429a.TMP | text | |
MD5:— | SHA256:— | |||
| 684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF1344bd.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
64
TCP/UDP connections
111
DNS requests
25
Threats
69
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1504 | chrome.exe | GET | 302 | 77.222.56.80:80 | http://fermereve.ru/bitrix/redirect.php?event1=upec&event2=&event3=&goto=http%3A%2F%2Ftopinvestor.world%2Fvip%2FDE%2F3792 | RU | — | — | unknown |
1504 | chrome.exe | GET | — | 47.91.88.69:80 | http://topinvestor.world/vip/DE/3792/css/css.css | US | — | — | suspicious |
1504 | chrome.exe | GET | — | 47.91.88.69:80 | http://topinvestor.world/vip/DE/3792/css/checkbox-svg.css | US | — | — | suspicious |
1504 | chrome.exe | GET | — | 47.91.88.69:80 | http://topinvestor.world/vip/DE/3792/fonts/OpenSans-Regular.ttf | US | — | — | suspicious |
1504 | chrome.exe | GET | 200 | 47.91.88.69:80 | http://topinvestor.world/vip/DE/3792/css/bootstrap-theme.min.css | US | text | 23.8 Kb | suspicious |
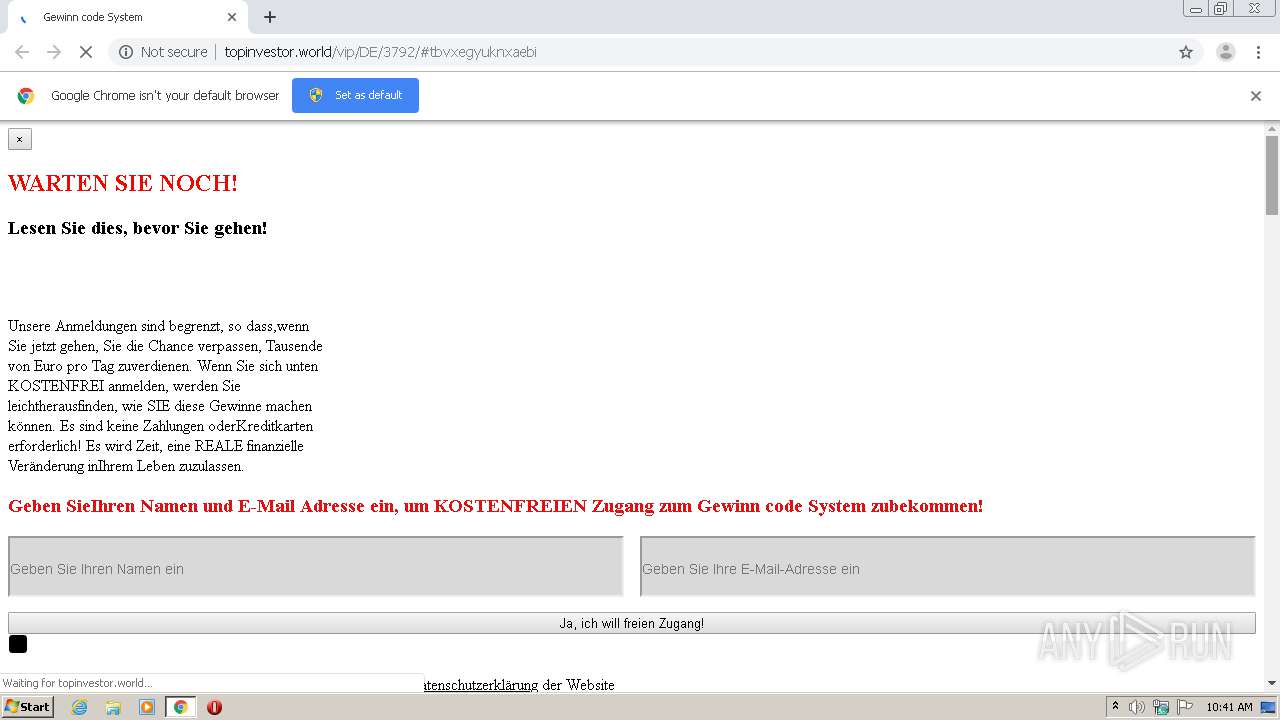
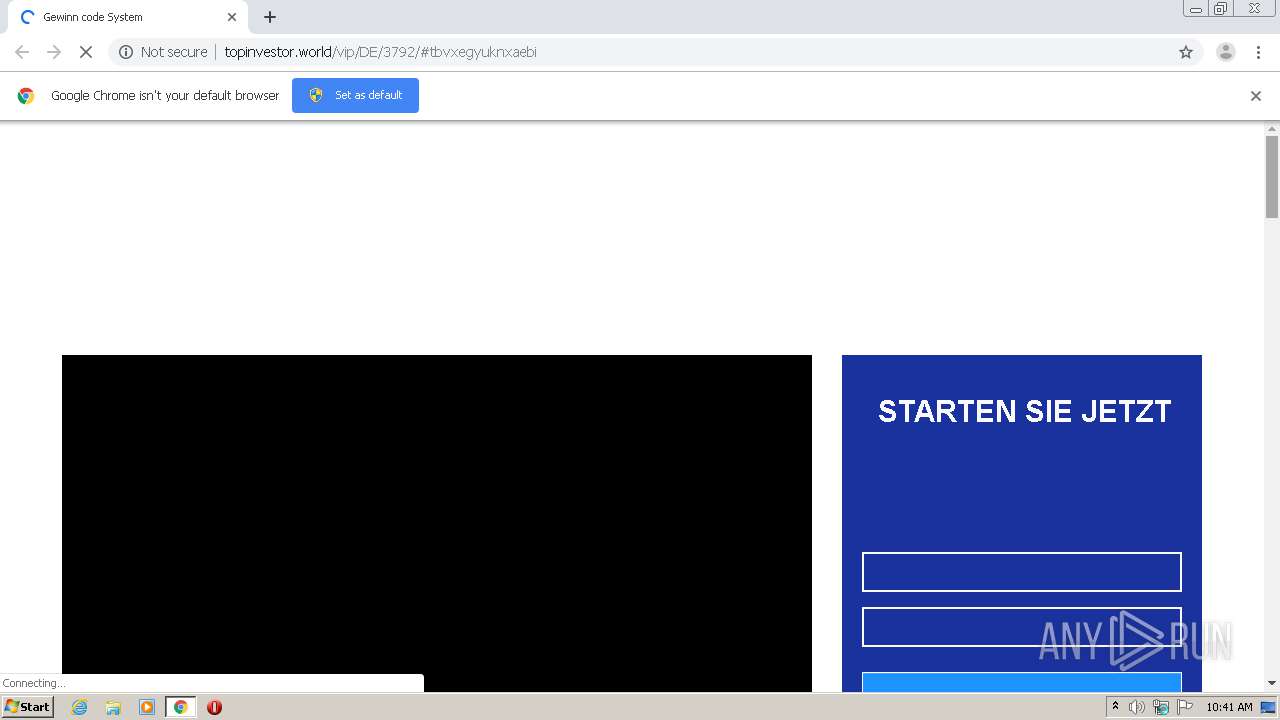
1504 | chrome.exe | GET | 200 | 47.91.88.69:80 | http://topinvestor.world/vip/DE/3792/ | US | html | 30.2 Kb | suspicious |
1504 | chrome.exe | GET | 200 | 47.91.88.69:80 | http://topinvestor.world/vip/DE/3792/css/bootstrap.min.css | US | text | 118 Kb | suspicious |
1504 | chrome.exe | GET | 200 | 195.181.175.49:80 | http://web.webpushs.com/js/push/9cc21736df519d8fd4775ffb7ff2f90a_1.js | DE | text | 34.4 Kb | whitelisted |
1504 | chrome.exe | GET | 200 | 47.91.88.69:80 | http://topinvestor.world/vip/DE/3792/css/style.css | US | text | 37.1 Kb | suspicious |
1504 | chrome.exe | GET | 200 | 47.91.88.69:80 | http://topinvestor.world/vip/DE/3792/css/stylesheet.css | US | text | 27.2 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1504 | chrome.exe | 172.217.18.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
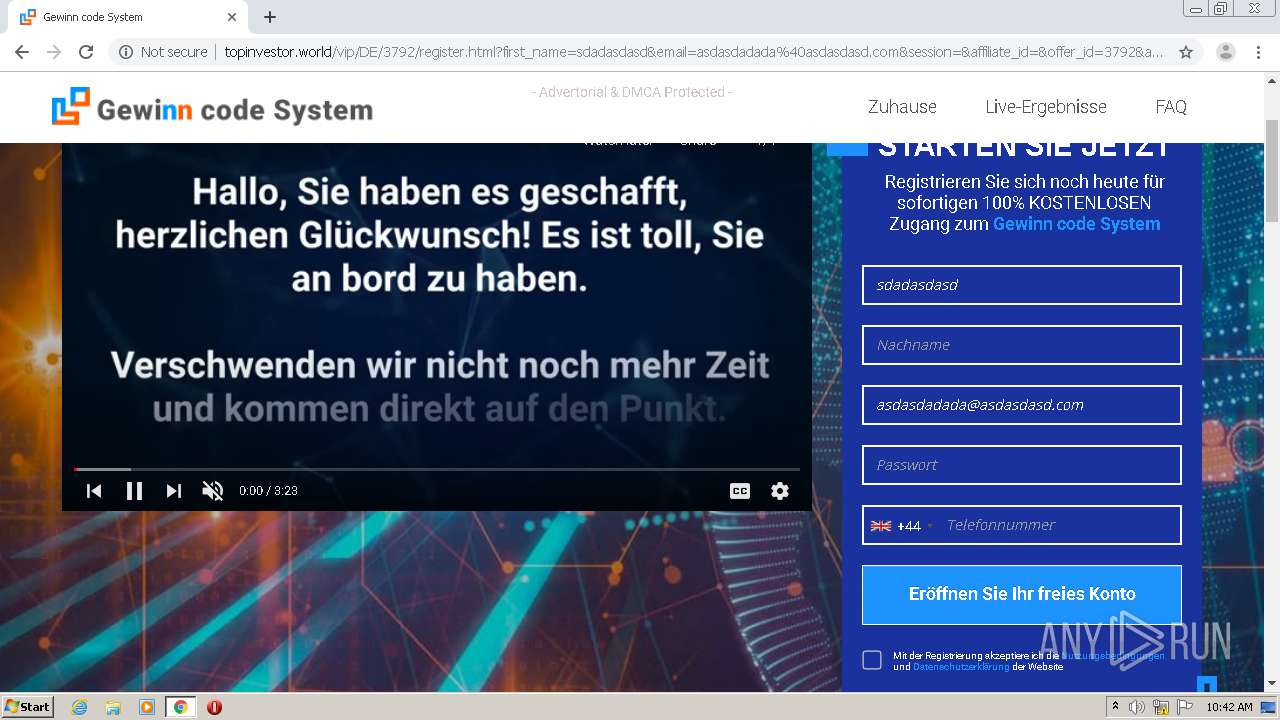
1504 | chrome.exe | 142.250.185.142:443 | www.youtube.com | Google Inc. | US | whitelisted |
1504 | chrome.exe | 142.250.185.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1504 | chrome.exe | 142.250.185.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
1504 | chrome.exe | 77.222.56.80:80 | fermereve.ru | SpaceWeb Ltd | RU | unknown |
1504 | chrome.exe | 195.181.175.49:80 | web.webpushs.com | Datacamp Limited | DE | suspicious |
1504 | chrome.exe | 47.91.88.69:80 | topinvestor.world | Alibaba (China) Technology Co., Ltd. | US | suspicious |
— | — | 47.91.88.69:80 | topinvestor.world | Alibaba (China) Technology Co., Ltd. | US | suspicious |
1504 | chrome.exe | 142.250.186.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1504 | chrome.exe | 216.58.213.4:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fermereve.ru |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
topinvestor.world |
| suspicious |
web.webpushs.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
amos-mamaya.fun |
| suspicious |
s.ytimg.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .world TLD |
1504 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.world Domain |
1504 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.world Domain |
1504 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.world Domain |
1504 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.world Domain |
1504 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.world Domain |
1504 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.world Domain |
1504 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.world Domain |
1504 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.world Domain |
1504 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.world Domain |