| download: | Roblox.Exe |
| Full analysis: | https://app.any.run/tasks/2323200a-3ea0-4b31-ae04-ecff1cba040d |
| Verdict: | Malicious activity |
| Analysis date: | August 14, 2020, 20:08:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E3F58E72FC2A6EDBF2EDD896805898FF |
| SHA1: | 76B0F8DC8953D07AA7B78CB758D6E9553CA1F86C |
| SHA256: | 9B6CB09B675510F54F179740AA31766977D8322D5A3EB5B14410A1E7C0BC363E |
| SSDEEP: | 49152:RP/eZV7eenkIZ9frjO/1sDtaTDM8rGb3HGMeQ/P+dAV7TX5b82ZK2l:RPC1/PDjO/C5b82P |
MALICIOUS
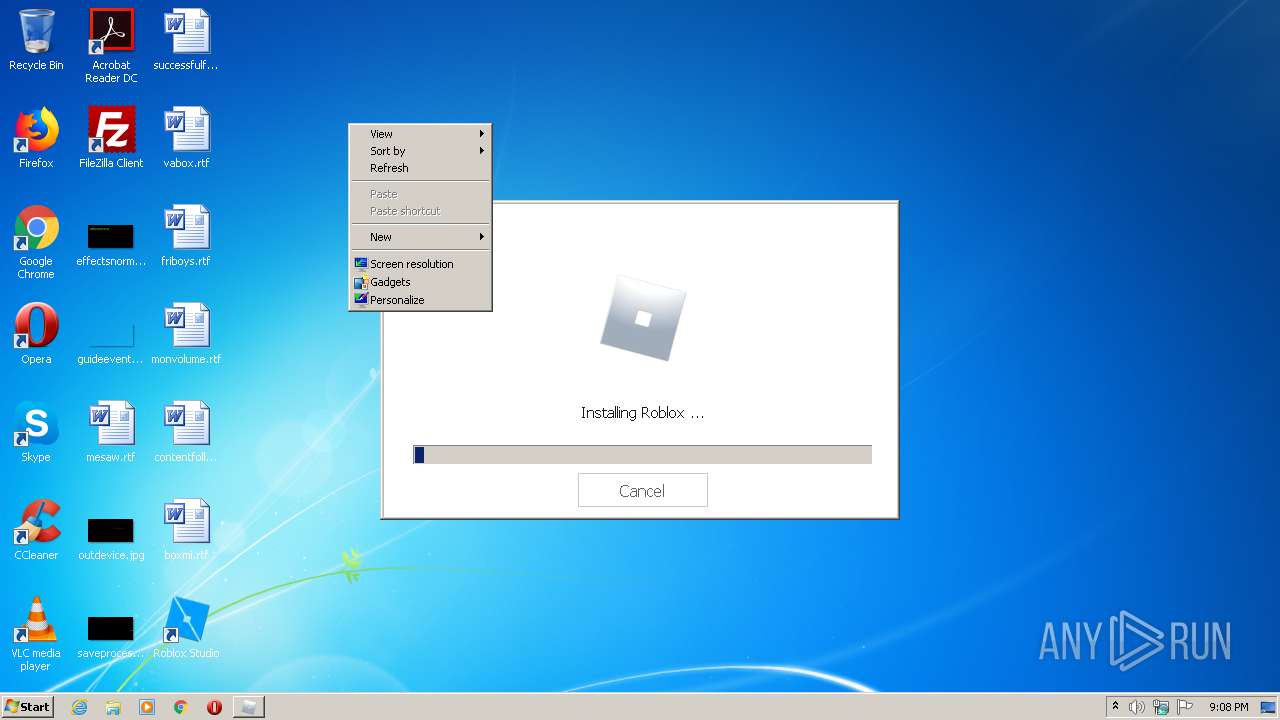
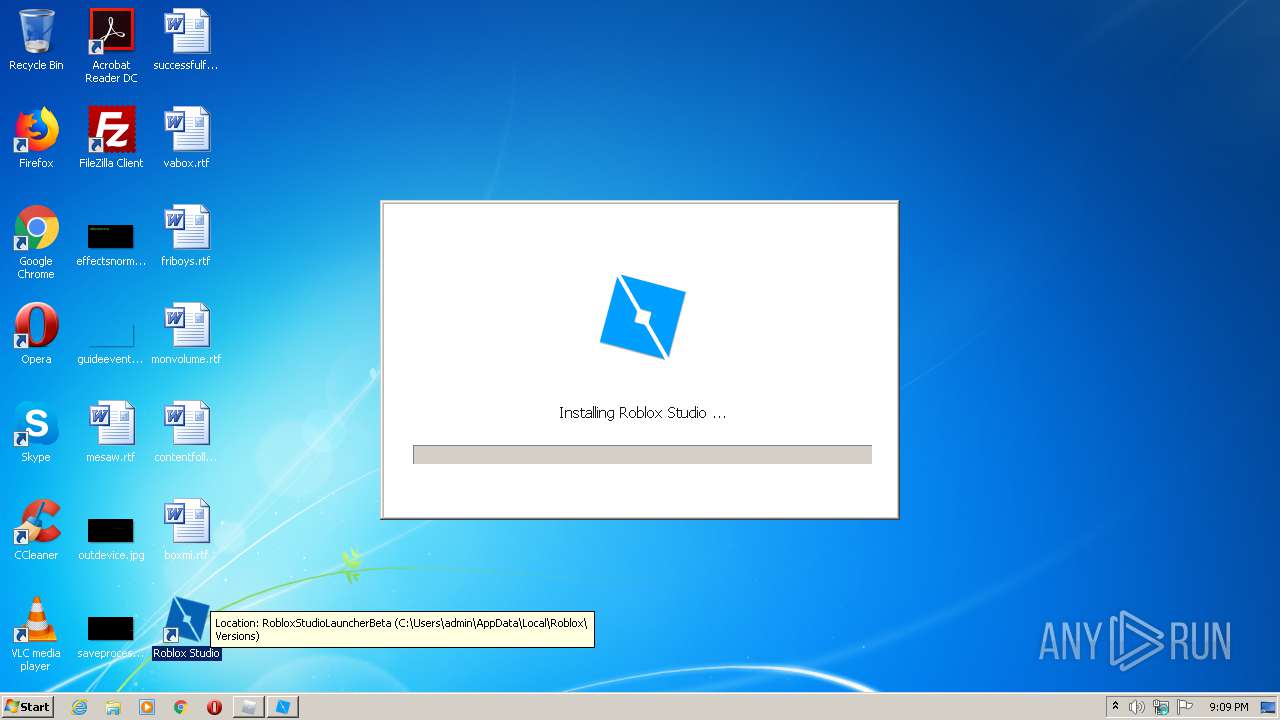
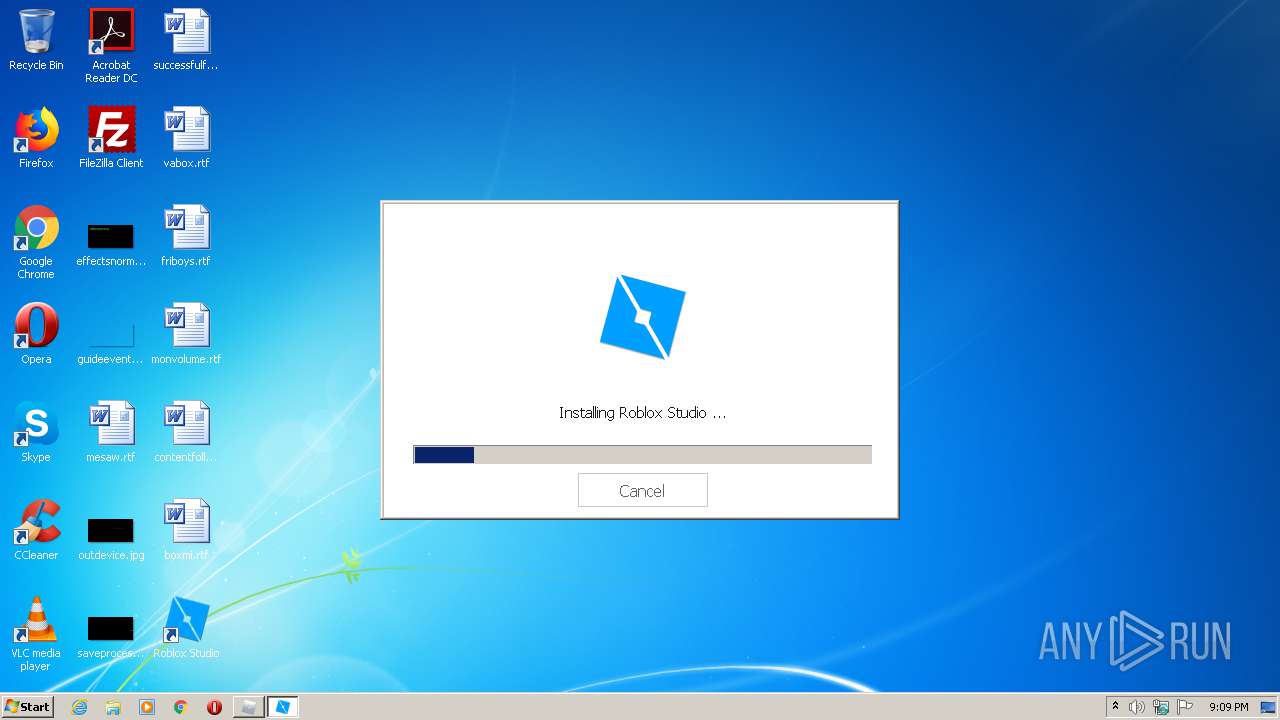
Application was dropped or rewritten from another process
- RobloxStudioLauncherBeta.exe (PID: 3740)
- RobloxStudioLauncherBeta.exe (PID: 2720)
SUSPICIOUS
Reads Internet Cache Settings
- Roblox.Exe (PID: 2700)
- RobloxStudioLauncherBeta.exe (PID: 2720)
- RobloxStudioLauncherBeta.exe (PID: 3740)
- Roblox.Exe (PID: 2140)
Application launched itself
- RobloxStudioLauncherBeta.exe (PID: 2720)
- Roblox.Exe (PID: 2700)
Modifies the open verb of a shell class
- Roblox.Exe (PID: 2700)
Creates files in the user directory
- Roblox.Exe (PID: 2700)
Executable content was dropped or overwritten
- RobloxStudioLauncherBeta.exe (PID: 2720)
- Roblox.Exe (PID: 2700)
INFO
Manual execution by user
- RobloxStudioLauncherBeta.exe (PID: 2720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:08:11 23:52:15+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 1090048 |
| InitializedDataSize: | 485376 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc1681 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.6.0.16625 |
| ProductVersionNumber: | 1.6.0.16625 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Roblox Corporation |
| FileDescription: | Roblox |
| FileVersion: | 1, 6, 0, 409841 |
| LegalCopyright: | Copyright © 2020 Roblox Corporation. All rights reserved. |
| OriginalFileName: | Roblox.exe |
| ProductName: | Roblox Bootstrapper |
| ProductVersion: | 1, 6, 0, 409841 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Aug-2020 21:52:15 |
| Detected languages: |
|
| TLS Callbacks: | 1 callback(s) detected. |
| Debug artifacts: |
|
| CompanyName: | Roblox Corporation |
| FileDescription: | Roblox |
| FileVersion: | 1, 6, 0, 409841 |
| LegalCopyright: | Copyright © 2020 Roblox Corporation. All rights reserved. |
| OriginalFilename: | Roblox.exe |
| ProductName: | Roblox Bootstrapper |
| ProductVersion: | 1, 6, 0, 409841 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 11-Aug-2020 21:52:15 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0010A1FC | 0x0010A200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.5445 |
.rdata | 0x0010C000 | 0x00048612 | 0x00048800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.67003 |
.data | 0x00155000 | 0x000577E0 | 0x00005C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.78766 |
CPADinfo( | 0x001AD000 | 0x00000028 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.122276 |
.rsrc | 0x001AE000 | 0x0001AF34 | 0x0001B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.91931 |
.reloc | 0x001C9000 | 0x0000D0E8 | 0x0000D200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.63881 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28732 | 1010 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.78815 | 76 | Latin 1 / Western European | Process Default Language | RT_GROUP_ICON |
3 | 4.77404 | 4264 | Latin 1 / Western European | Process Default Language | RT_ICON |
4 | 4.46883 | 16672 | Latin 1 / Western European | Process Default Language | RT_ICON |
5 | 4.5291 | 9640 | Latin 1 / Western European | Process Default Language | RT_ICON |
7 | 3.38178 | 488 | Latin 1 / Western European | Portuguese - Brazil | RT_STRING |
8 | 3.37397 | 942 | Latin 1 / Western European | Portuguese - Brazil | RT_STRING |
9 | 3.0813 | 666 | Latin 1 / Western European | Portuguese - Brazil | RT_STRING |
11 | 1.10136 | 46 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 0.38158 | 34 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
POWRPROF.dll |
SHELL32.dll |
SHLWAPI.dll |
SensApi.dll |
USER32.dll |
Total processes
41
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2140 | C:\Users\admin\AppData\Local\Temp\Roblox.Exe --crashpad --no-rate-limit --database=C:\Users\admin\AppData\Local\Temp\crashpad_roblox --metrics-dir=C:\Users\admin\AppData\Local\Temp\crashpad_roblox --url=https://upload.crashes.rbxinfra.com/post --annotation=UploadAttachmentKiloByteLimit=100 --annotation=UploadPercentage=100 --annotation=format=minidump --annotation=token=a2440b0bfdada85f34d79b43839f2b49ea6bba474bd7d126e844bc119271a1c3 --initial-client-data=0x4f4,0x4f8,0x4fc,0x4f0,0x504,0x157b5ac,0x157b5bc,0x157b5cc | C:\Users\admin\AppData\Local\Temp\Roblox.Exe | Roblox.Exe | ||||||||||||
User: admin Company: Roblox Corporation Integrity Level: MEDIUM Description: Roblox Exit code: 0 Version: 1, 6, 0, 409841 Modules
| |||||||||||||||
| 2700 | "C:\Users\admin\AppData\Local\Temp\Roblox.Exe" | C:\Users\admin\AppData\Local\Temp\Roblox.Exe | explorer.exe | ||||||||||||
User: admin Company: Roblox Corporation Integrity Level: MEDIUM Description: Roblox Exit code: 0 Version: 1, 6, 0, 409841 Modules
| |||||||||||||||
| 2720 | "C:\Users\admin\AppData\Local\Roblox\Versions\RobloxStudioLauncherBeta.exe" -ide | C:\Users\admin\AppData\Local\Roblox\Versions\RobloxStudioLauncherBeta.exe | explorer.exe | ||||||||||||
User: admin Company: Roblox Corporation Integrity Level: MEDIUM Description: Roblox Exit code: 0 Version: 1, 6, 0, 409841 Modules
| |||||||||||||||
| 3740 | C:\Users\admin\AppData\Local\Roblox\Versions\RobloxStudioLauncherBeta.exe --crashpad --no-rate-limit --database=C:\Users\admin\AppData\Local\Temp\crashpad_roblox --metrics-dir=C:\Users\admin\AppData\Local\Temp\crashpad_roblox --url=https://upload.crashes.rbxinfra.com/post --annotation=UploadAttachmentKiloByteLimit=100 --annotation=UploadPercentage=0 --annotation=format=minidump --annotation=token=a2440b0bfdada85f34d79b43839f2b49ea6bba474bd7d126e844bc119271a1c3 --initial-client-data=0x4f0,0x4f4,0x4f8,0x4e4,0x500,0x129555c,0x129556c,0x129557c | C:\Users\admin\AppData\Local\Roblox\Versions\RobloxStudioLauncherBeta.exe | RobloxStudioLauncherBeta.exe | ||||||||||||
User: admin Company: Roblox Corporation Integrity Level: MEDIUM Description: Roblox Exit code: 0 Version: 1, 6, 0, 409841 Modules
| |||||||||||||||
Total events
588
Read events
489
Write events
99
Delete events
0
Modification events
| (PID) Process: | (2700) Roblox.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2700) Roblox.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2700) Roblox.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2700) Roblox.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2700) Roblox.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2700) Roblox.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2700) Roblox.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2700) Roblox.Exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\136\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2700) Roblox.Exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\136\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (2700) Roblox.Exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\136\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
Executable files
5
Suspicious files
27
Text files
11
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2700 | Roblox.Exe | C:\Users\admin\AppData\Local\Temp\CabBBEE.tmp | — | |
MD5:— | SHA256:— | |||
| 2700 | Roblox.Exe | C:\Users\admin\AppData\Local\Temp\TarBBEF.tmp | — | |
MD5:— | SHA256:— | |||
| 2140 | Roblox.Exe | C:\Users\admin\AppData\Local\Temp\CabBDD2.tmp | — | |
MD5:— | SHA256:— | |||
| 2140 | Roblox.Exe | C:\Users\admin\AppData\Local\Temp\TarBDD3.tmp | — | |
MD5:— | SHA256:— | |||
| 2700 | Roblox.Exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\5DAQR2KL.txt | — | |
MD5:— | SHA256:— | |||
| 2700 | Roblox.Exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\GetInstallerCdns[1].json | — | |
MD5:— | SHA256:— | |||
| 2700 | Roblox.Exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | der | |
MD5:— | SHA256:— | |||
| 2700 | Roblox.Exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | binary | |
MD5:— | SHA256:— | |||
| 2700 | Roblox.Exe | C:\Users\admin\AppData\Local\Roblox\Downloads\736e1d0362b0cbe9a0dab00cea9a9610.part | — | |
MD5:— | SHA256:— | |||
| 2140 | Roblox.Exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\application[1].json | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
17
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2700 | Roblox.Exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
2700 | Roblox.Exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
2700 | Roblox.Exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2700 | Roblox.Exe | 104.111.227.55:443 | clientsettingscdn.roblox.com | Akamai International B.V. | NL | unknown |
2700 | Roblox.Exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2140 | Roblox.Exe | 104.111.227.55:443 | clientsettingscdn.roblox.com | Akamai International B.V. | NL | unknown |
2700 | Roblox.Exe | 192.124.249.23:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
2700 | Roblox.Exe | 205.185.216.10:443 | setup.rbxcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
2700 | Roblox.Exe | 128.116.123.3:443 | www.roblox.com | University Corporation for Atmospheric Research | US | suspicious |
2720 | RobloxStudioLauncherBeta.exe | 104.111.227.55:443 | clientsettingscdn.roblox.com | Akamai International B.V. | NL | unknown |
3740 | RobloxStudioLauncherBeta.exe | 104.111.227.55:443 | clientsettingscdn.roblox.com | Akamai International B.V. | NL | unknown |
2720 | RobloxStudioLauncherBeta.exe | 128.116.114.3:443 | ephemeralcounters.api.roblox.com | University Corporation for Atmospheric Research | US | unknown |
2720 | RobloxStudioLauncherBeta.exe | 205.185.216.42:443 | setup.rbxcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientsettingscdn.roblox.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ephemeralcounters.api.roblox.com |
| whitelisted |
setup.rbxcdn.qq.com |
| suspicious |
clientsettingscdn.roblox.qq.com |
| unknown |
setup.rbxcdn.com |
| whitelisted |
setup-ak.rbxcdn.com |
| whitelisted |
setup-ll.rbxcdn.com |
| whitelisted |
setup-cfly.rbxcdn.com |
| suspicious |
setup-hw.rbxcdn.com |
| suspicious |