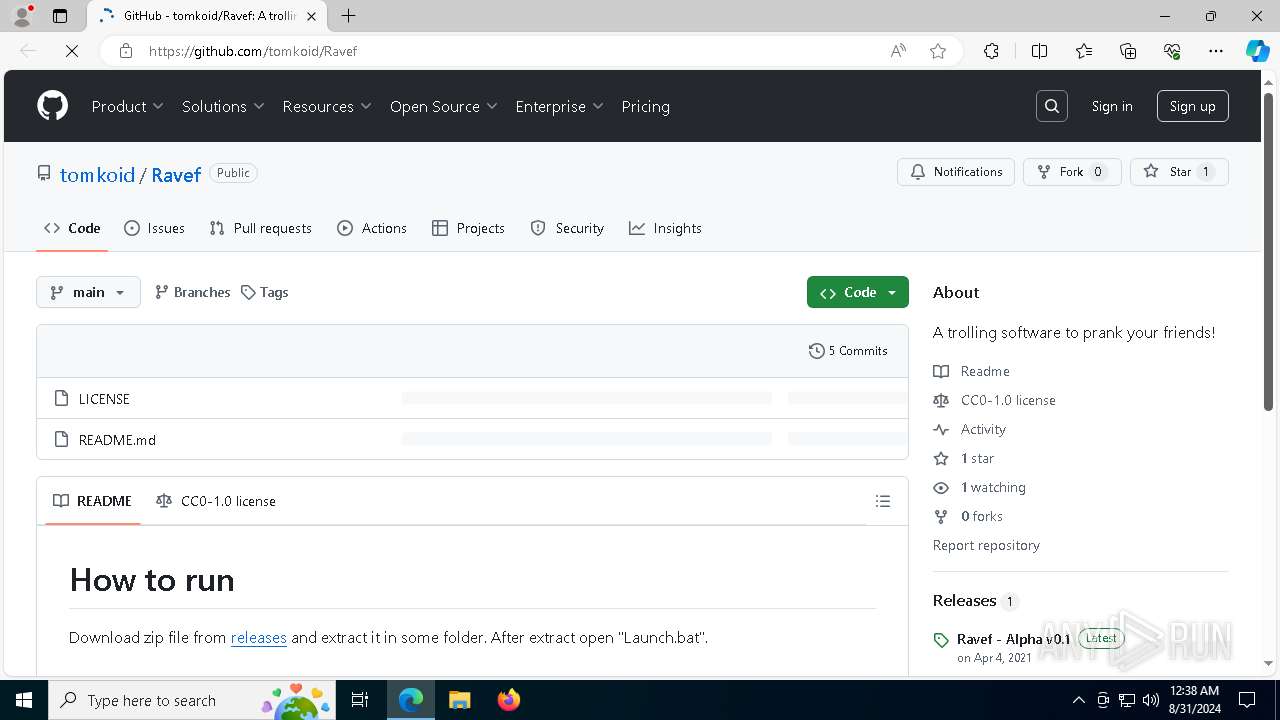
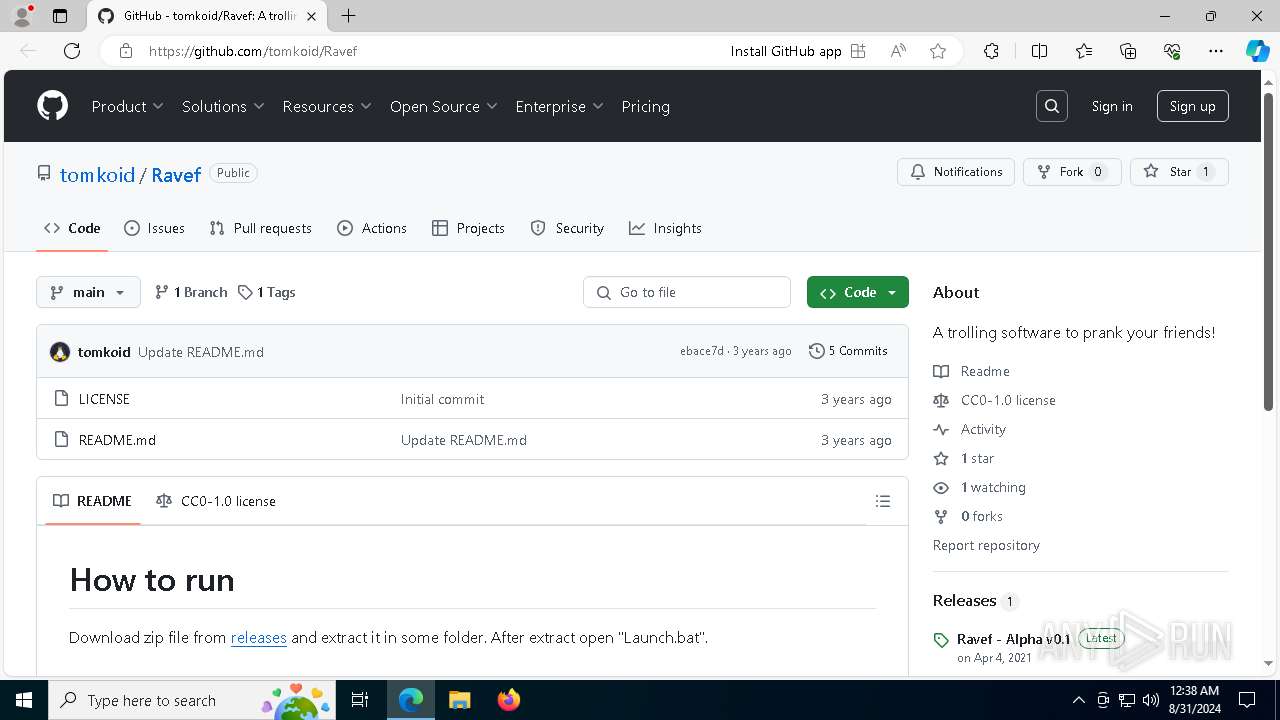
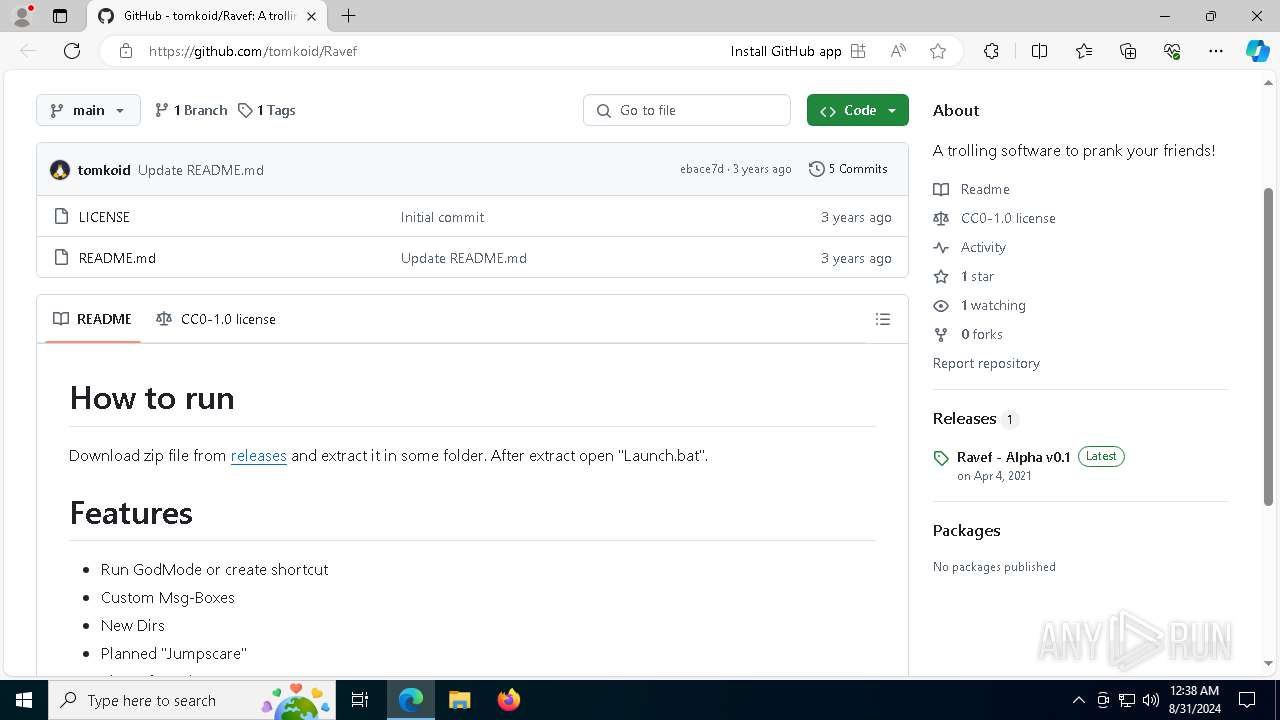
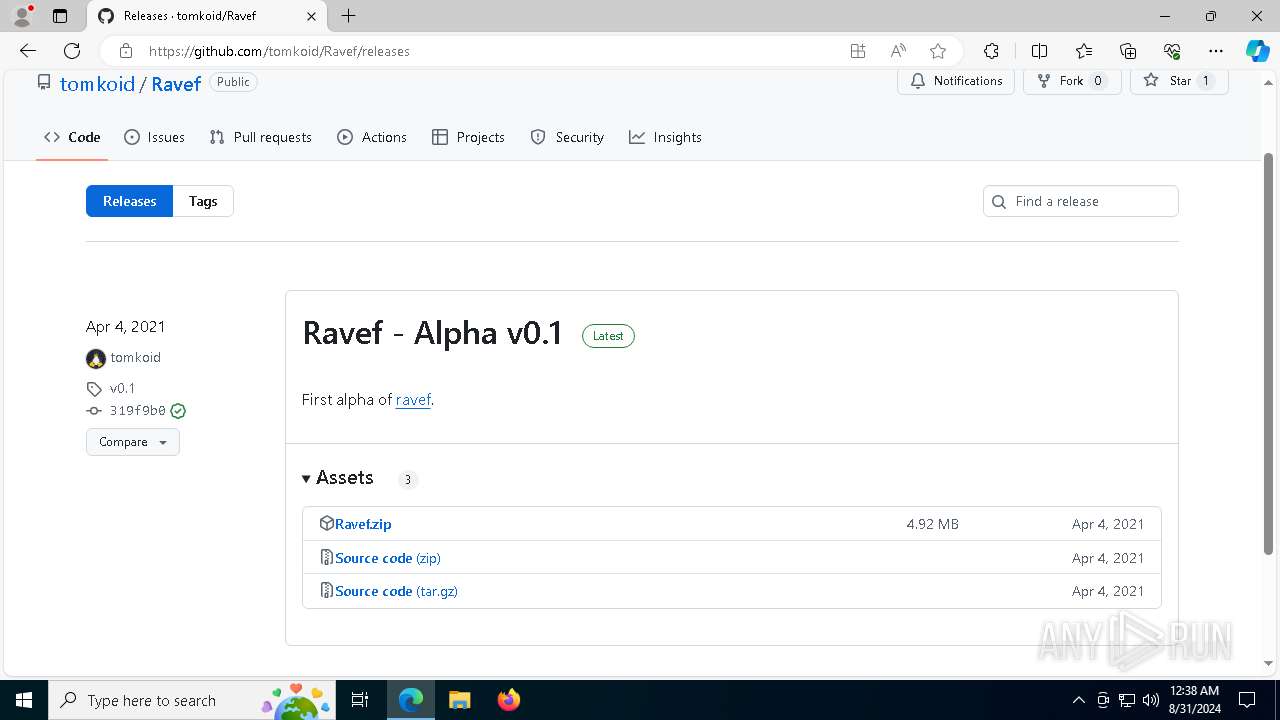
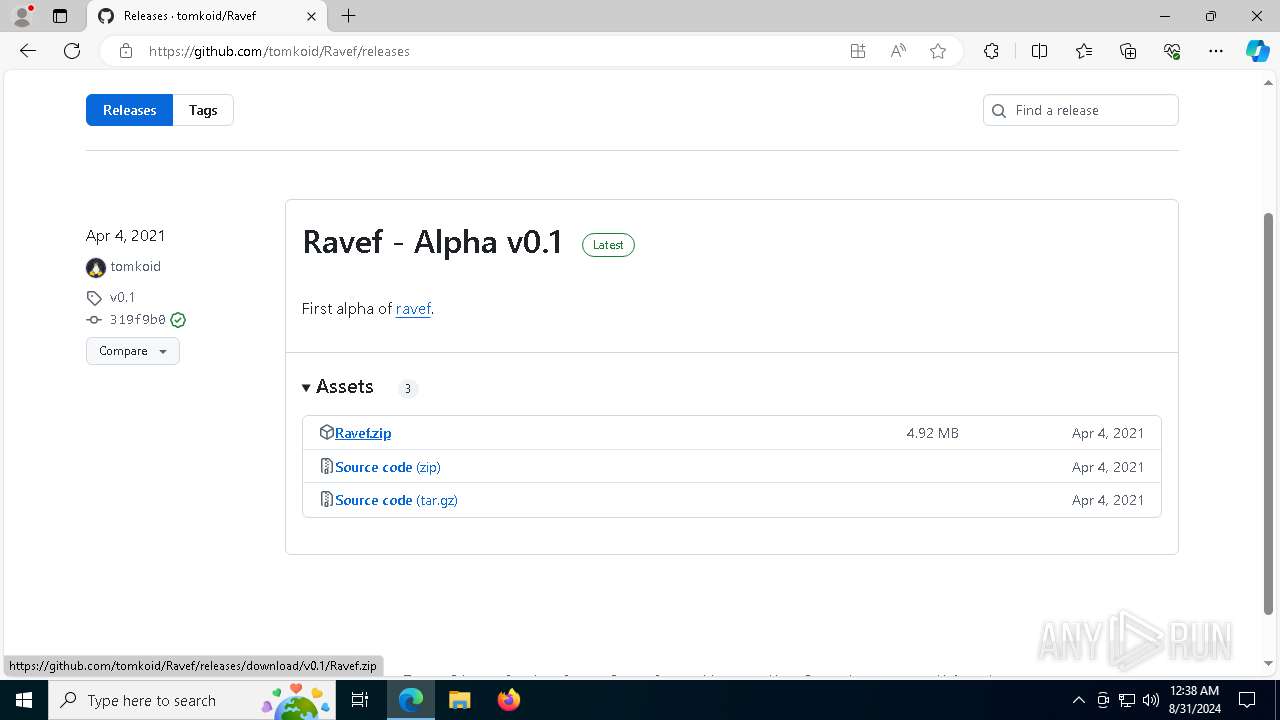
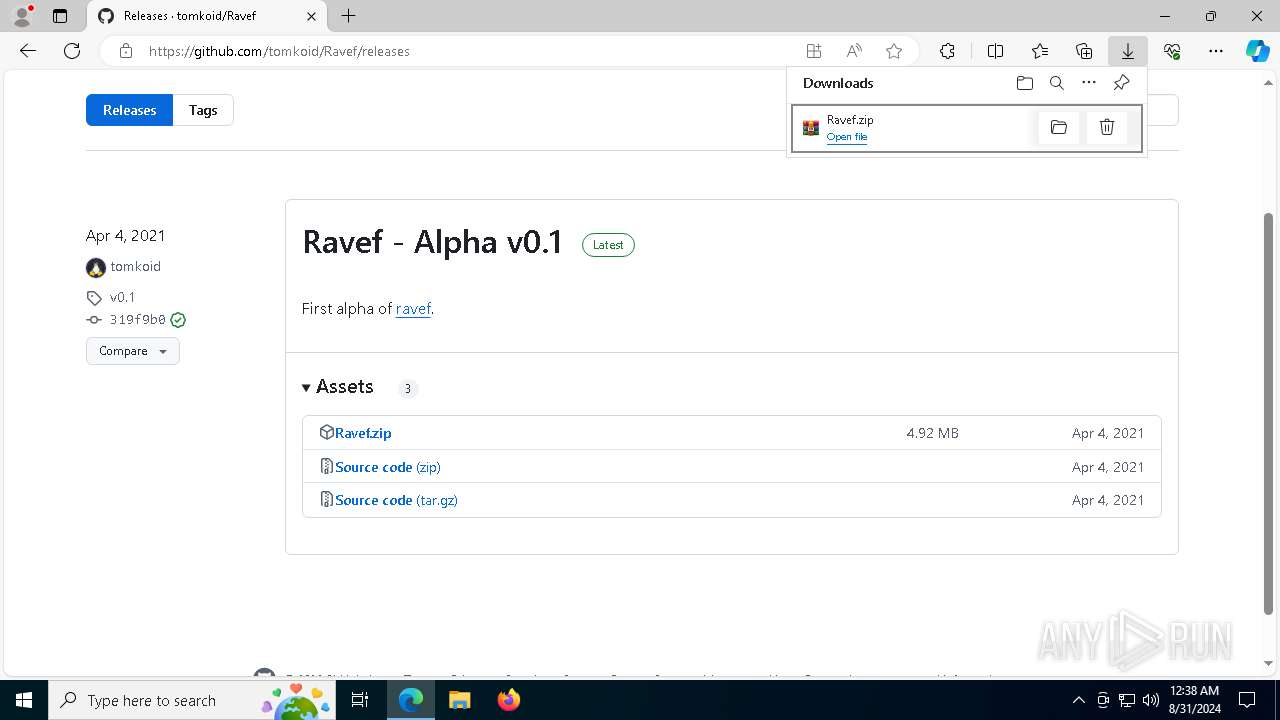
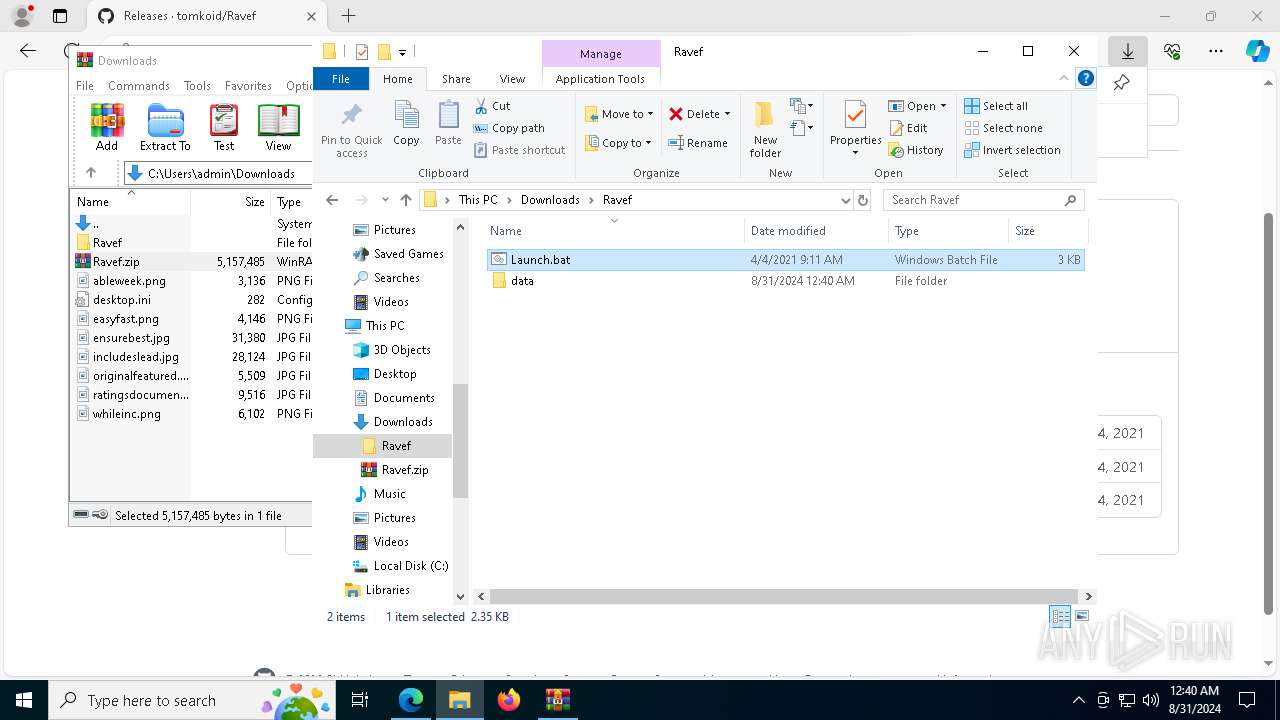
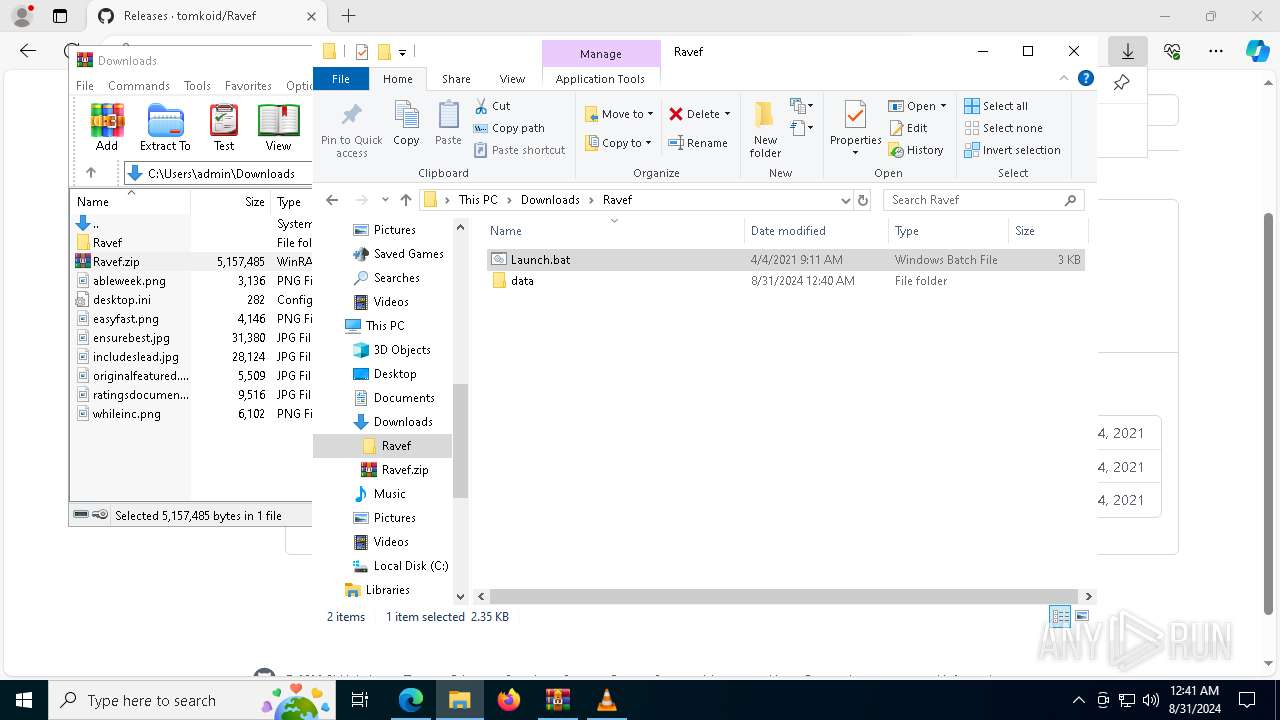
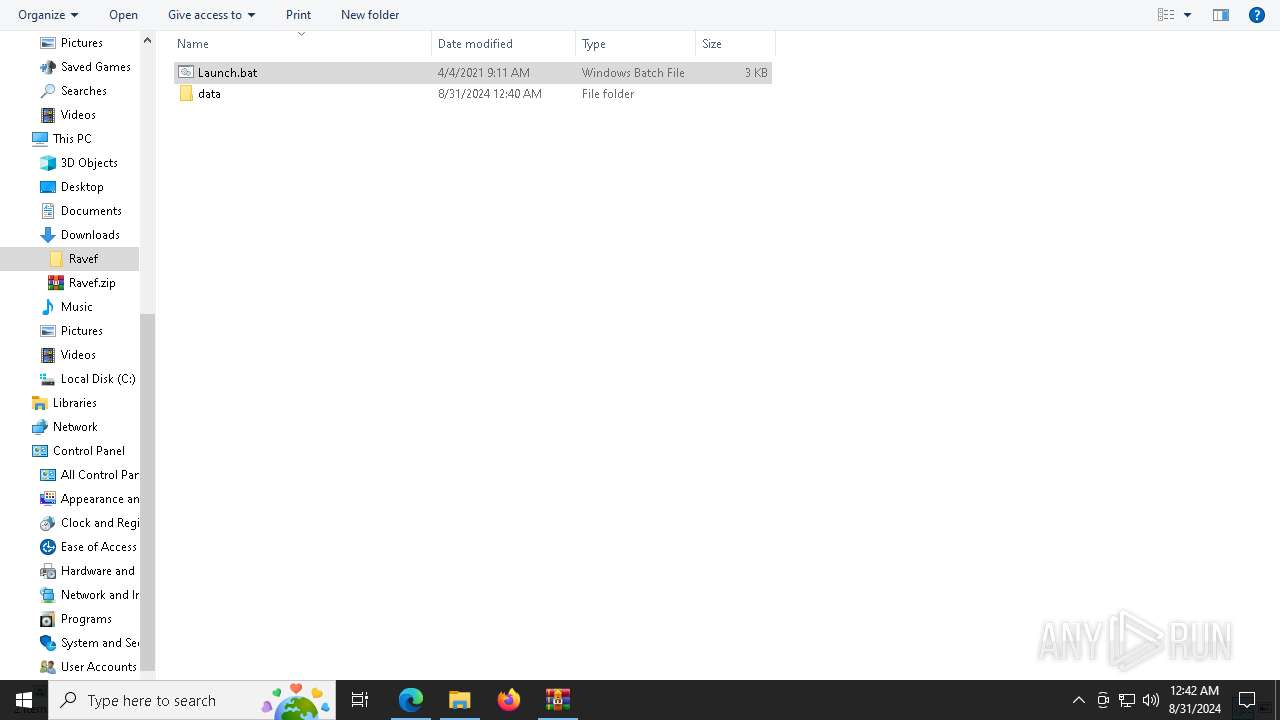
| URL: | https://github.com/tomkoid/Ravef |
| Full analysis: | https://app.any.run/tasks/9bb03849-2d1c-4b67-8328-0e4726628152 |
| Verdict: | Malicious activity |
| Analysis date: | August 31, 2024, 00:37:51 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
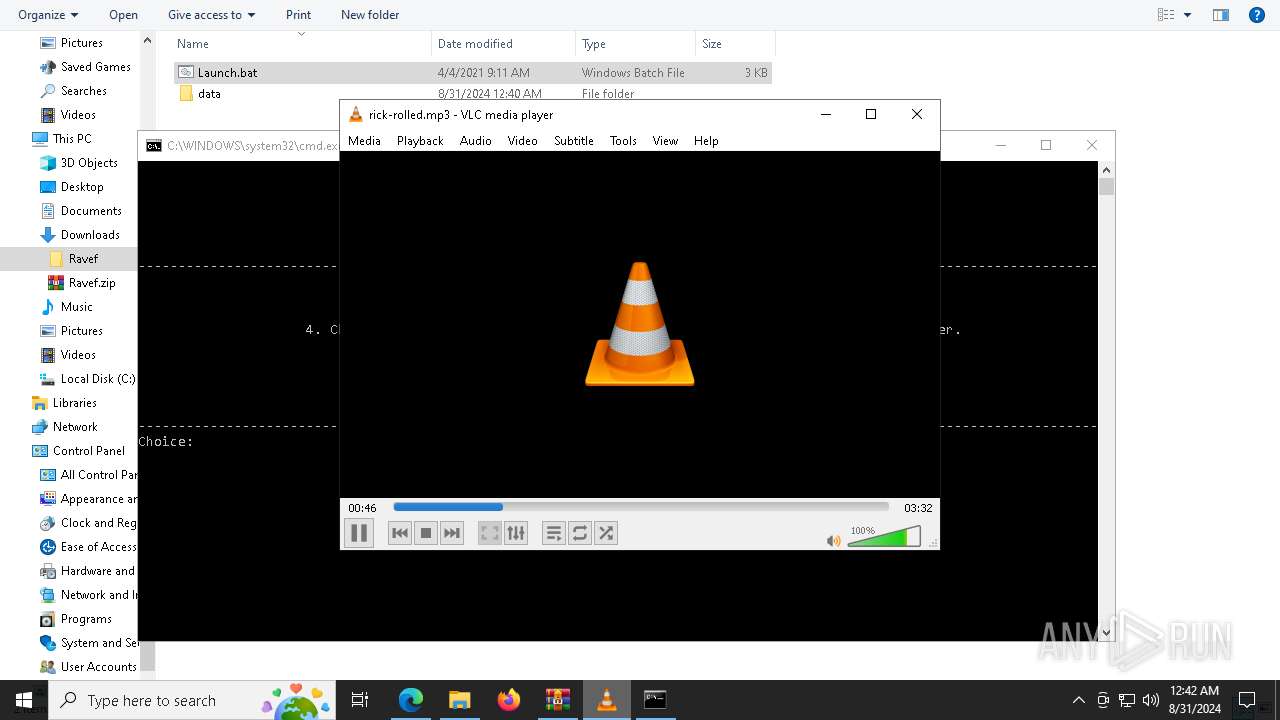
| Tags: | |
| Indicators: | |
| MD5: | BF28B5CF1051ACB1CA9C601FF256F0F8 |
| SHA1: | DC95D2D322C4887C3945EEC88C00047BEB8B3ACB |
| SHA256: | 9B6C9C12CD4D64C327D7AB874C70740895DE89610DBA65F4D6EFA156CF359570 |
| SSDEEP: | 3:N8tEdhKmAlC:2u6Fs |
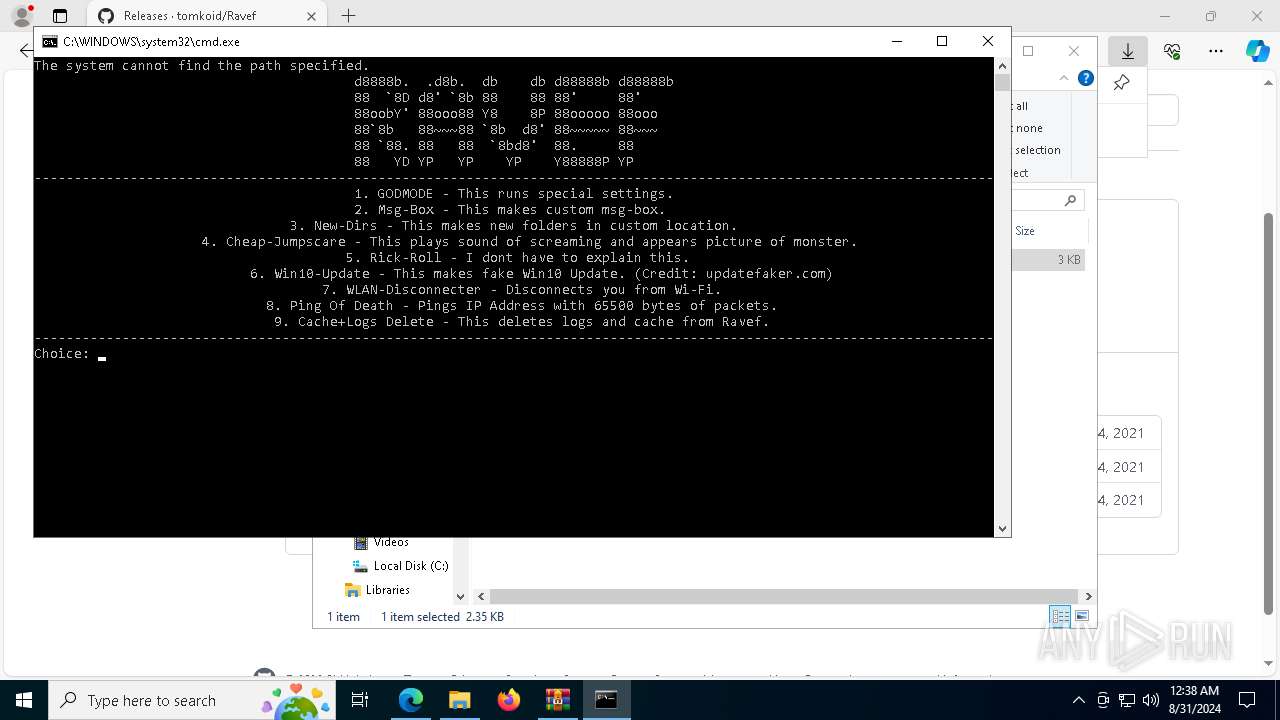
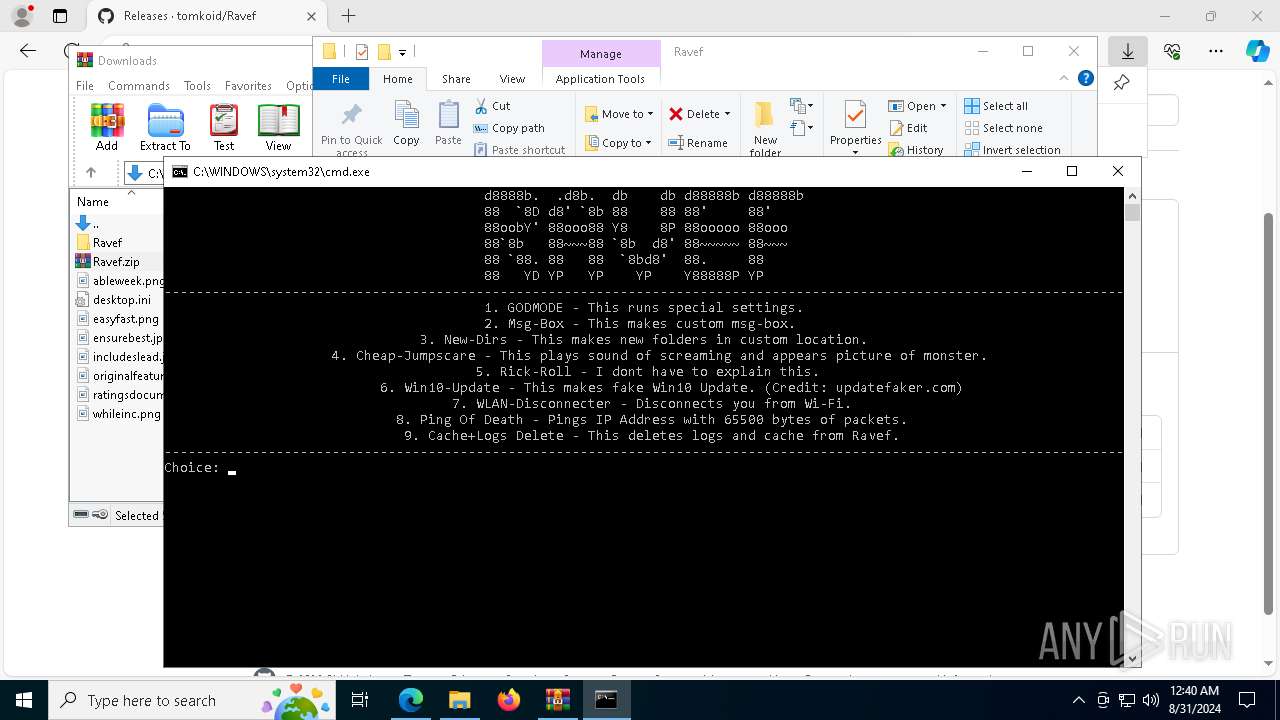
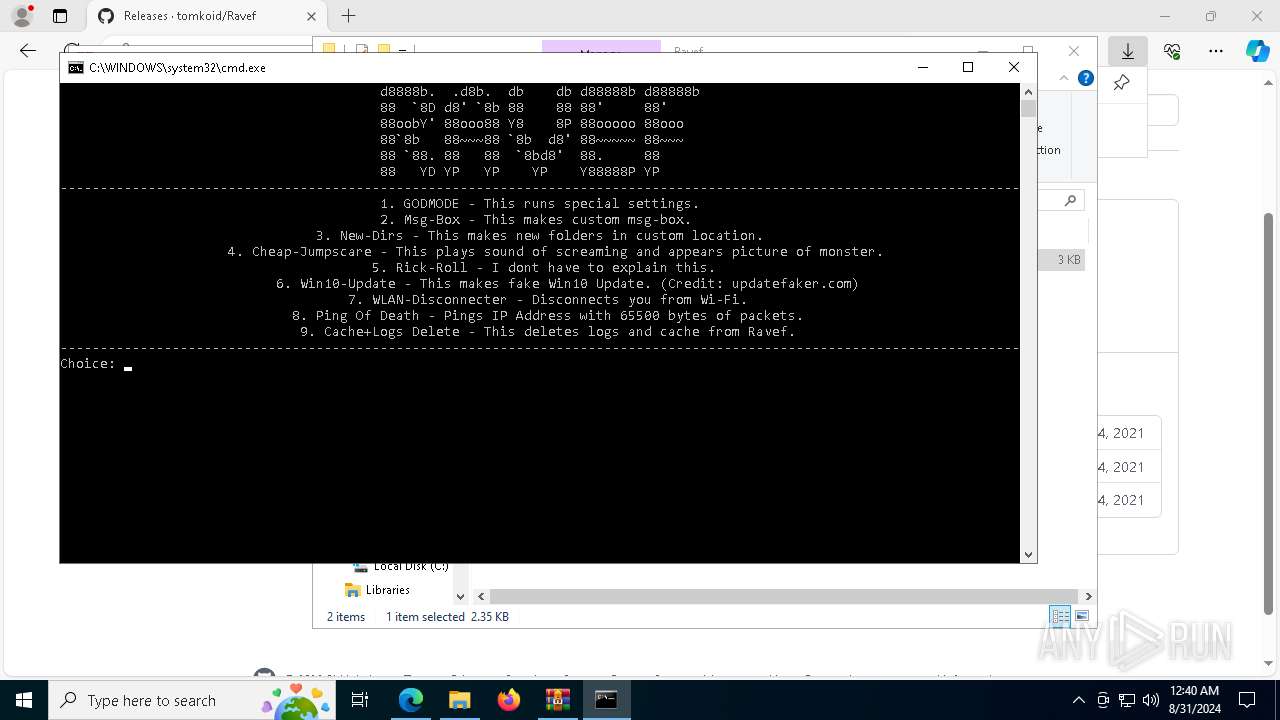
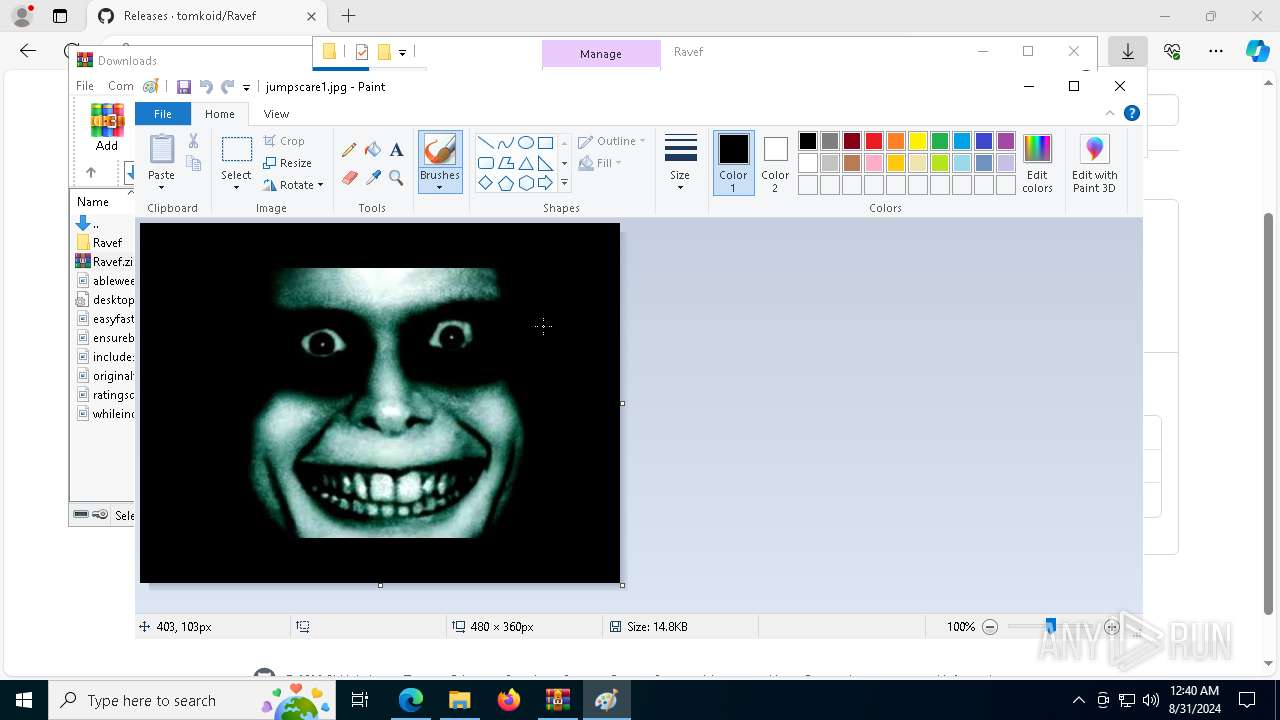
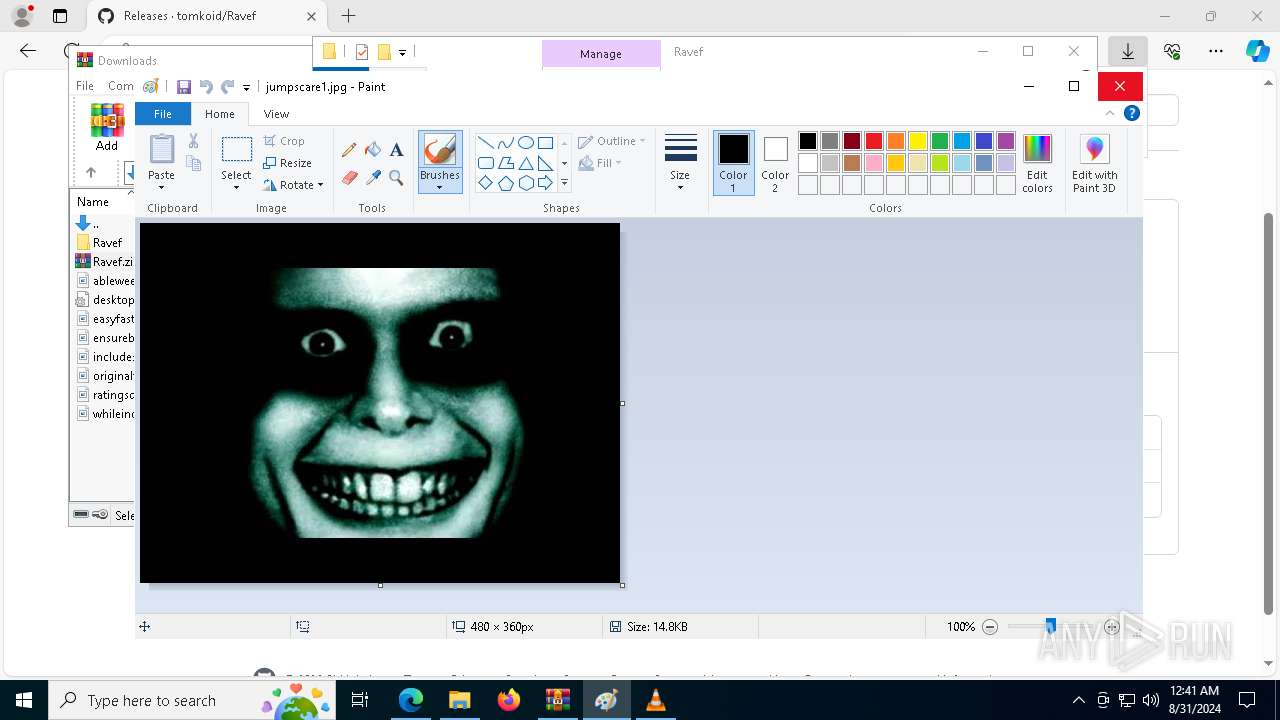
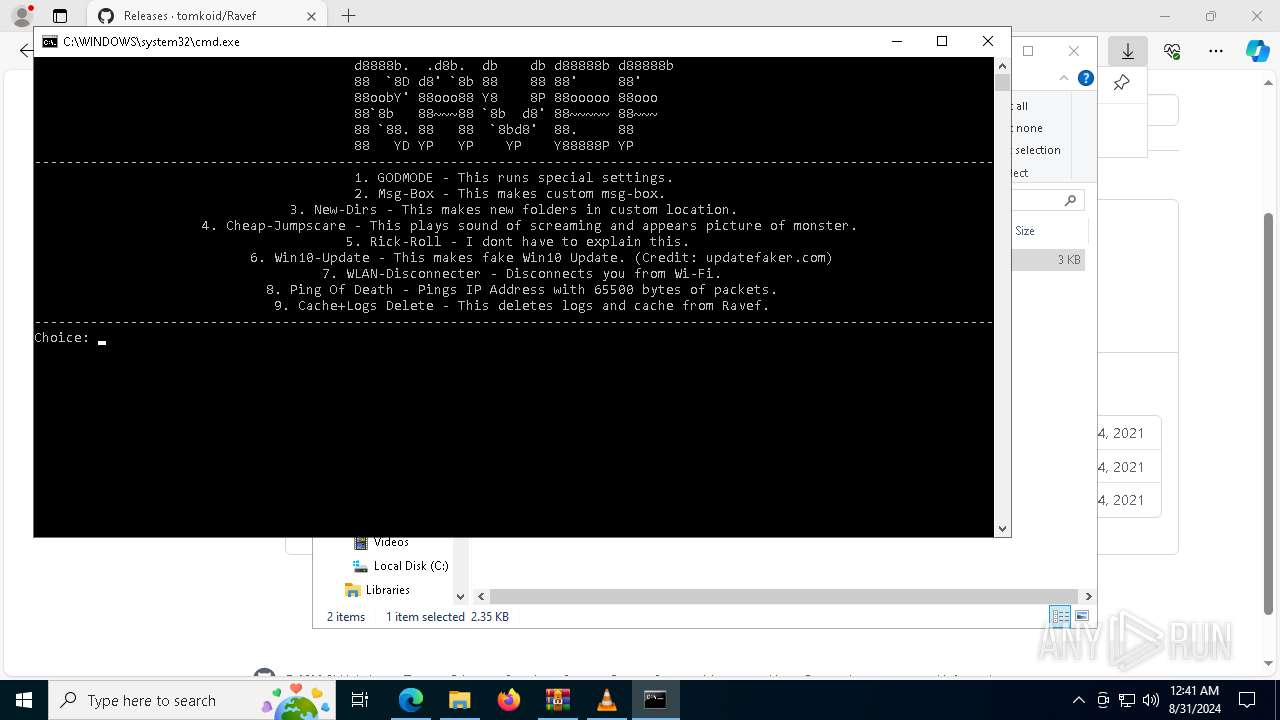
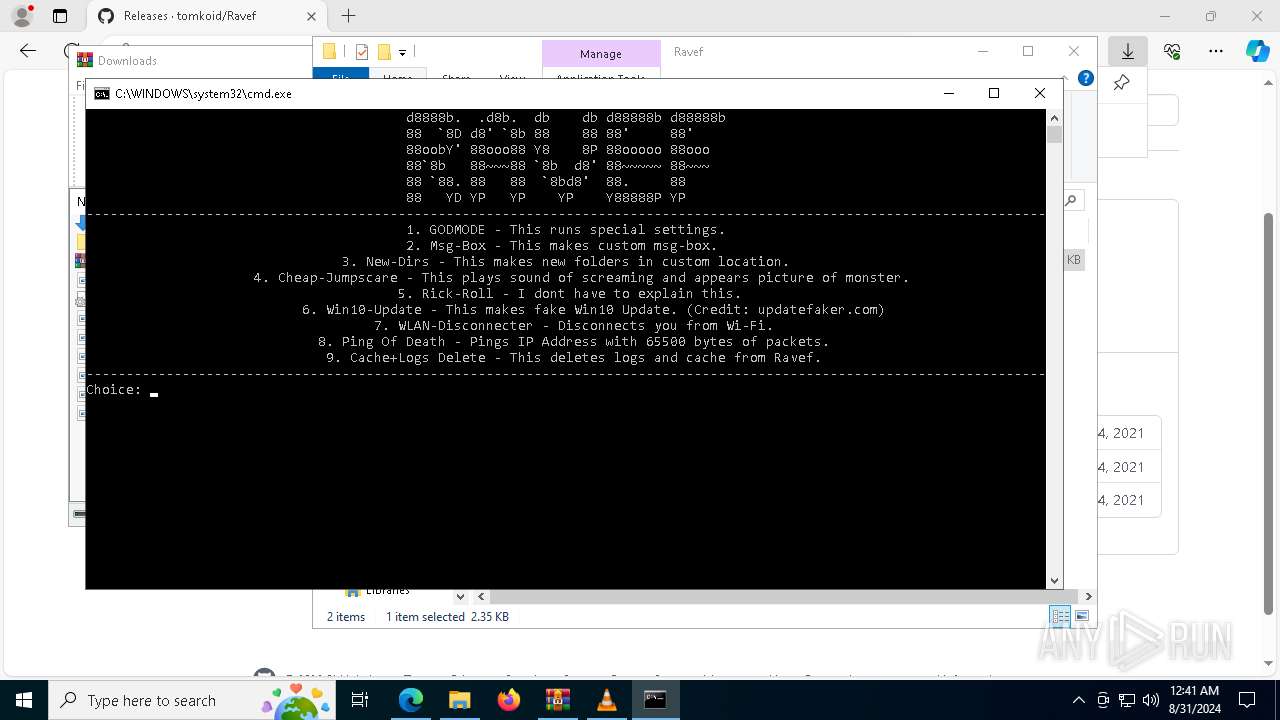
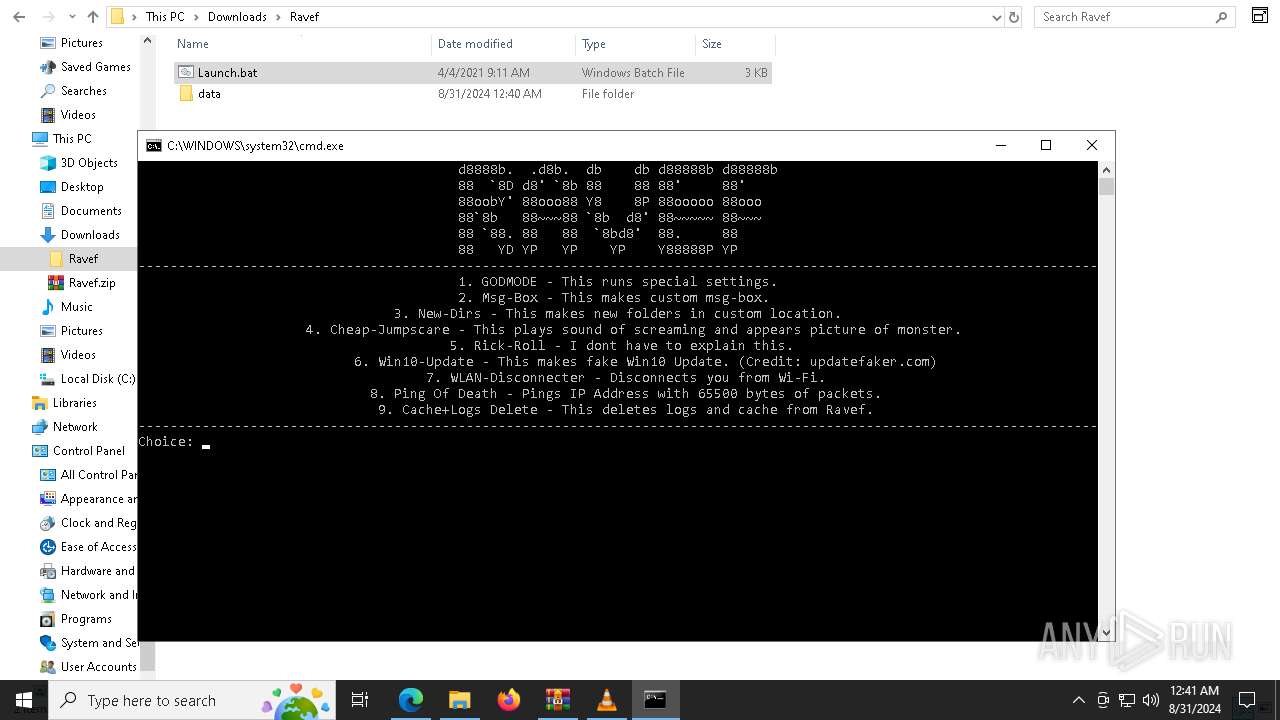
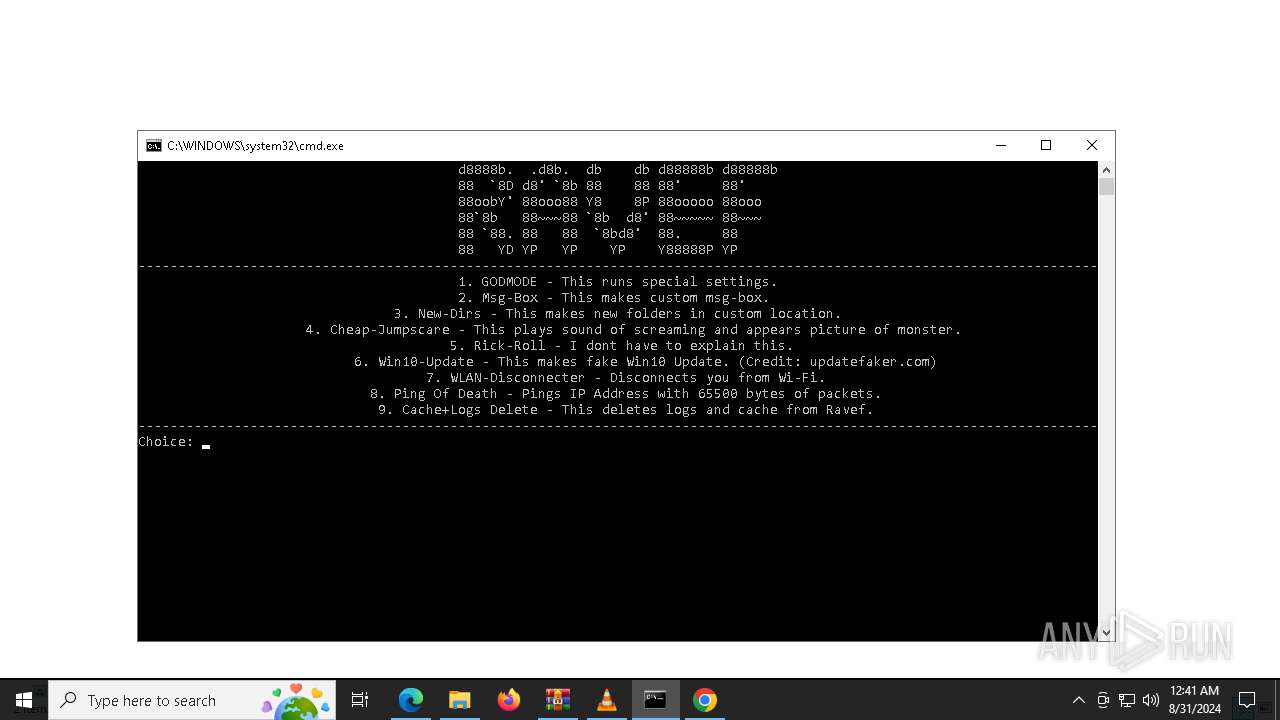
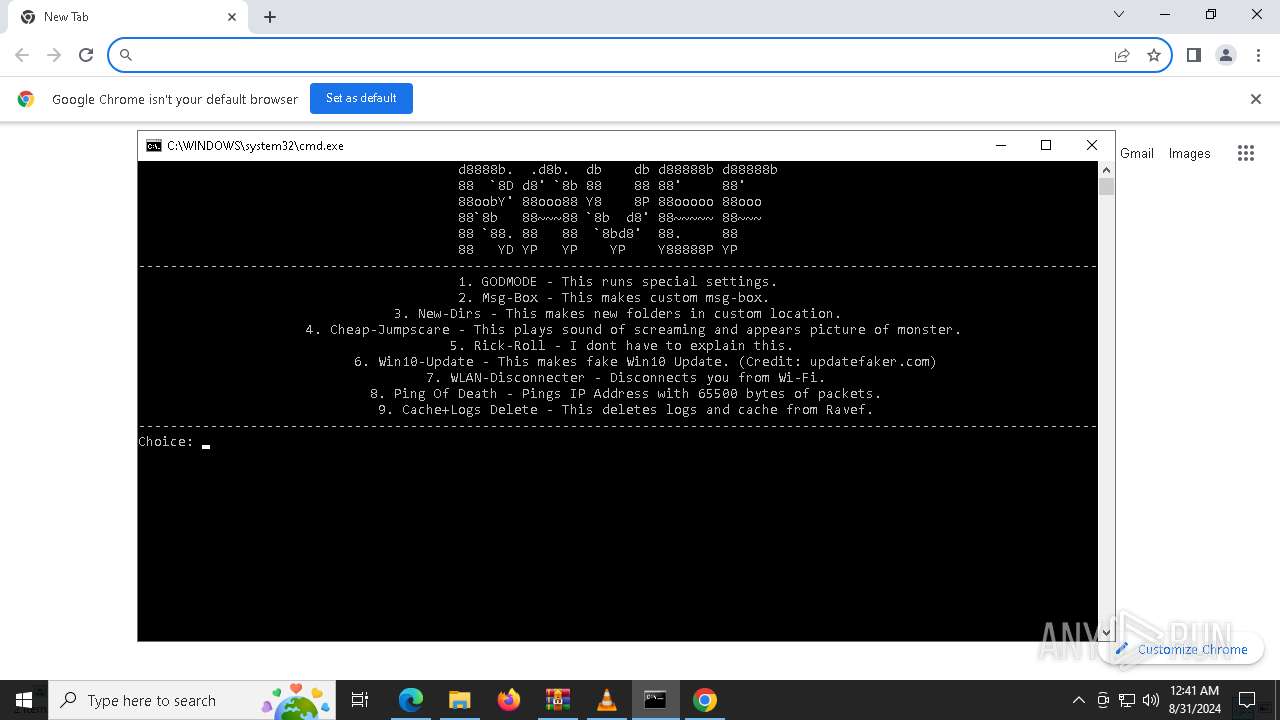
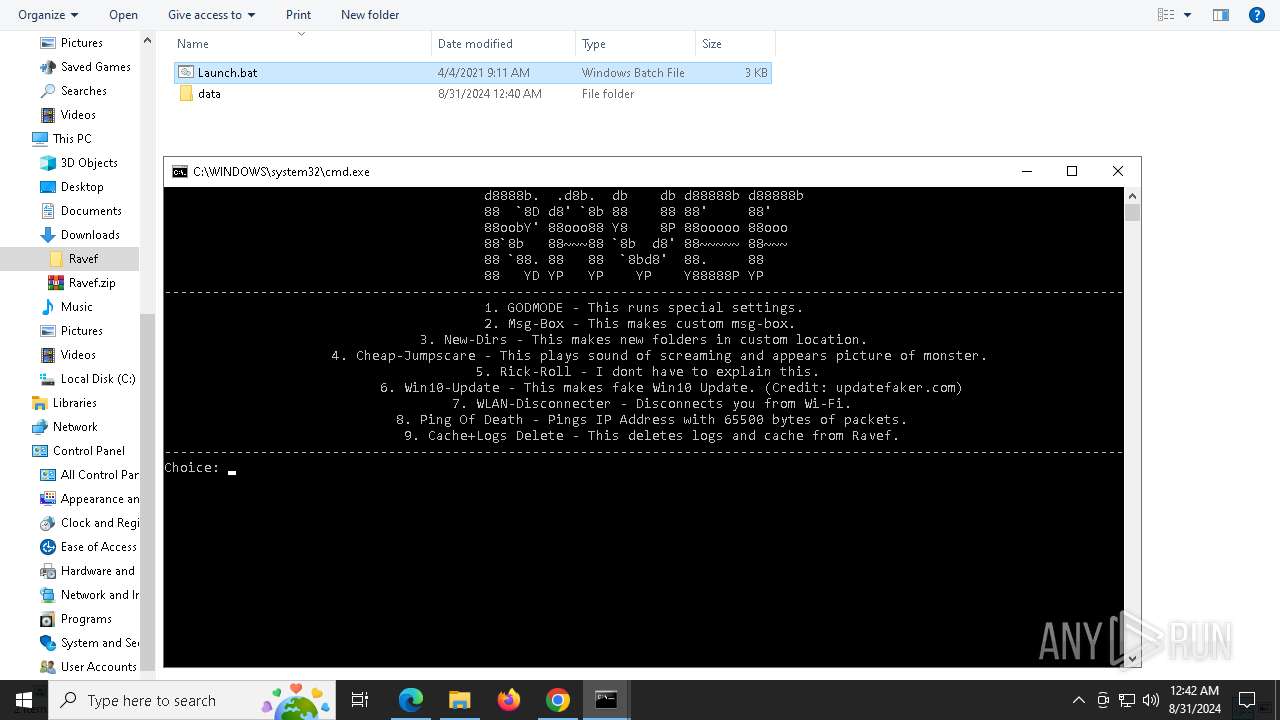
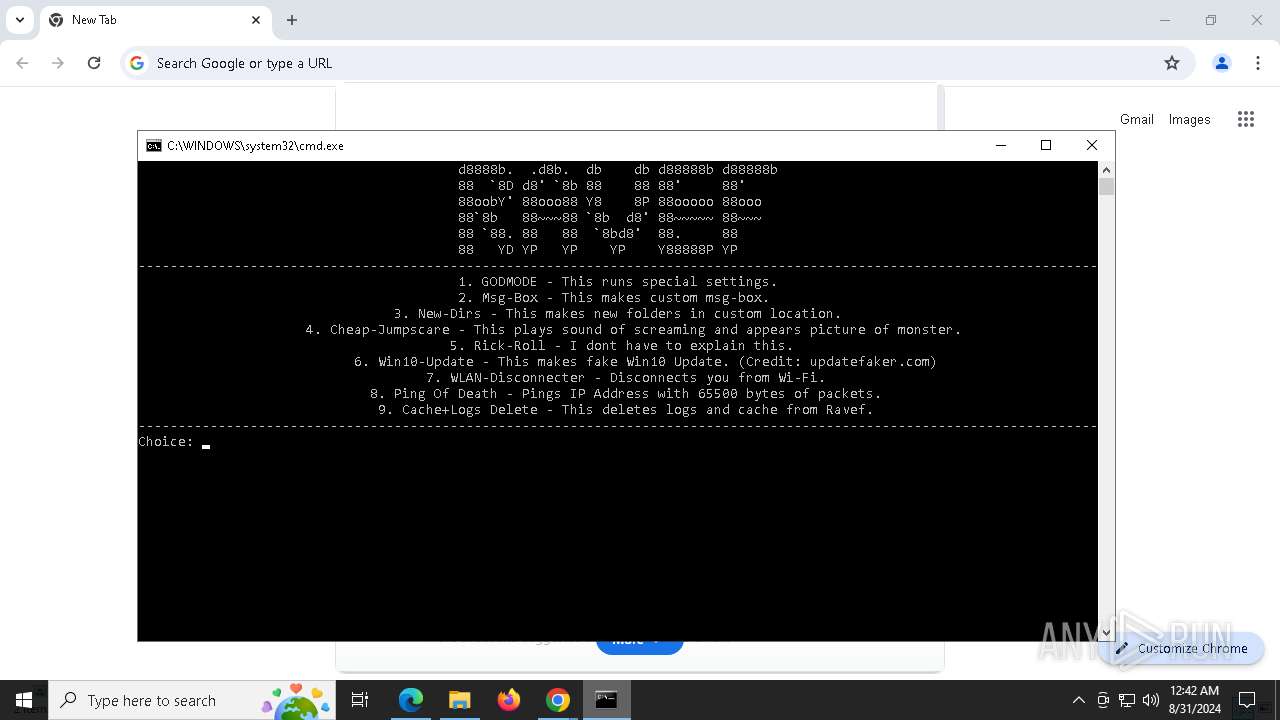
MALICIOUS
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 8156)
- wscript.exe (PID: 400)
- wscript.exe (PID: 7088)
SUSPICIOUS
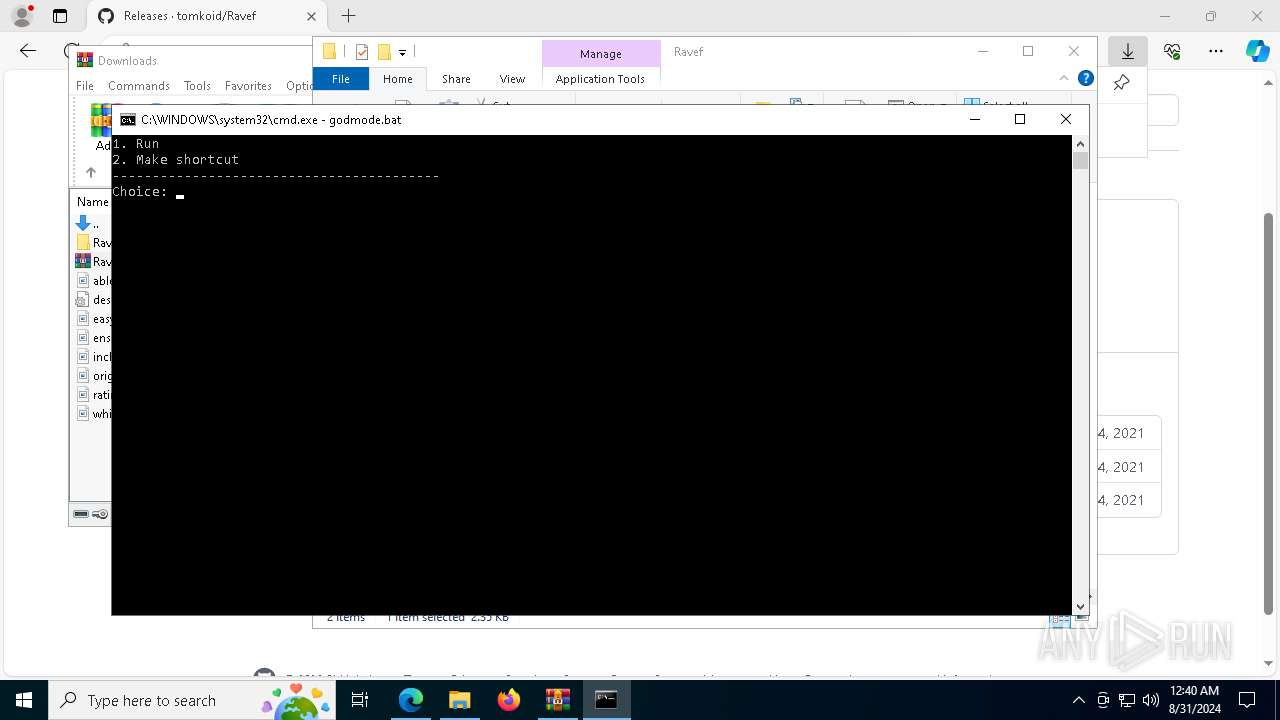
Application launched itself
- cmd.exe (PID: 892)
- cmd.exe (PID: 7108)
- cmd.exe (PID: 4672)
- cmd.exe (PID: 2368)
- cmd.exe (PID: 6512)
- cmd.exe (PID: 7288)
- cmd.exe (PID: 6952)
- cmd.exe (PID: 2384)
- cmd.exe (PID: 7652)
- cmd.exe (PID: 6692)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7108)
- cmd.exe (PID: 892)
- cmd.exe (PID: 4672)
- cmd.exe (PID: 2368)
- cmd.exe (PID: 6512)
- cmd.exe (PID: 7288)
- cmd.exe (PID: 6952)
- cmd.exe (PID: 2384)
- cmd.exe (PID: 7652)
- cmd.exe (PID: 6692)
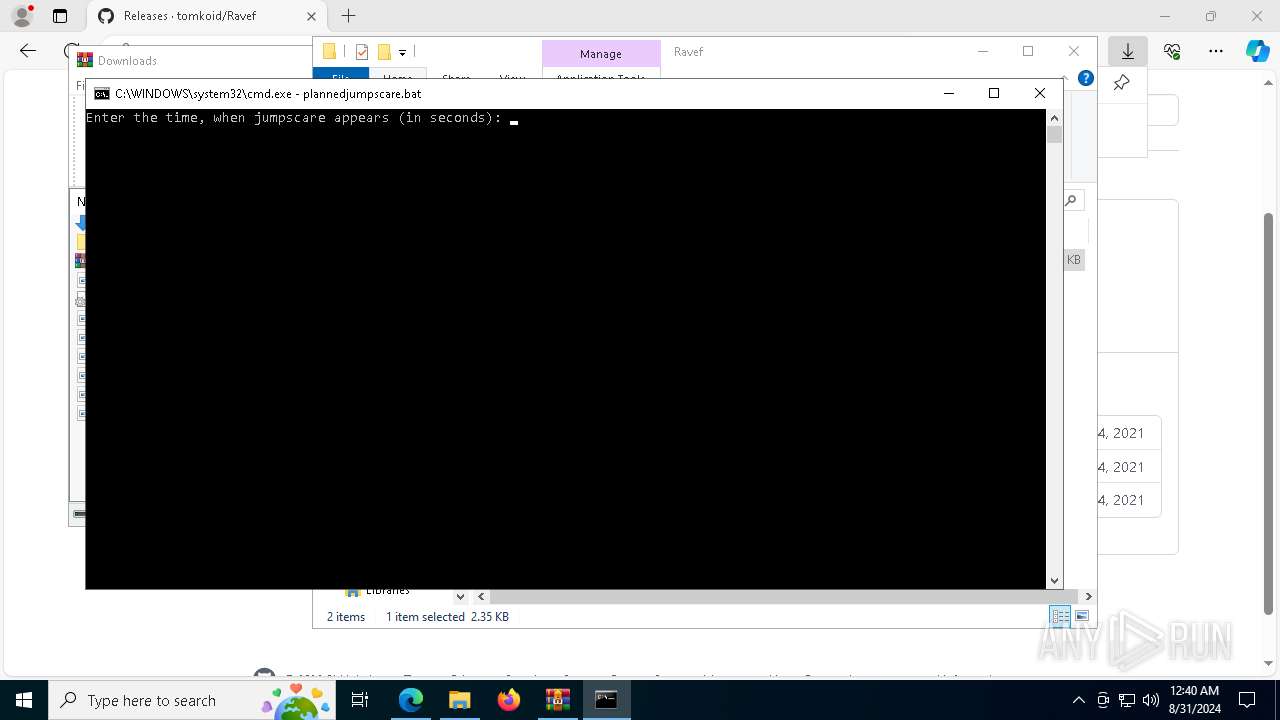
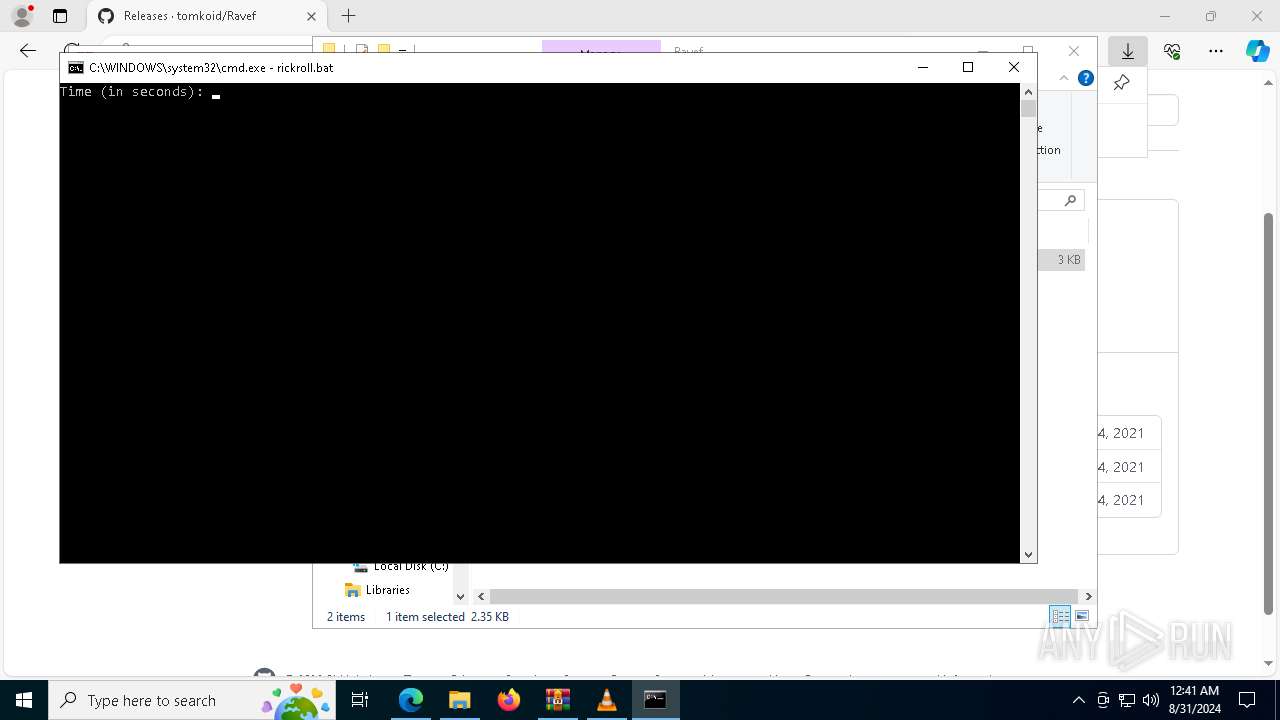
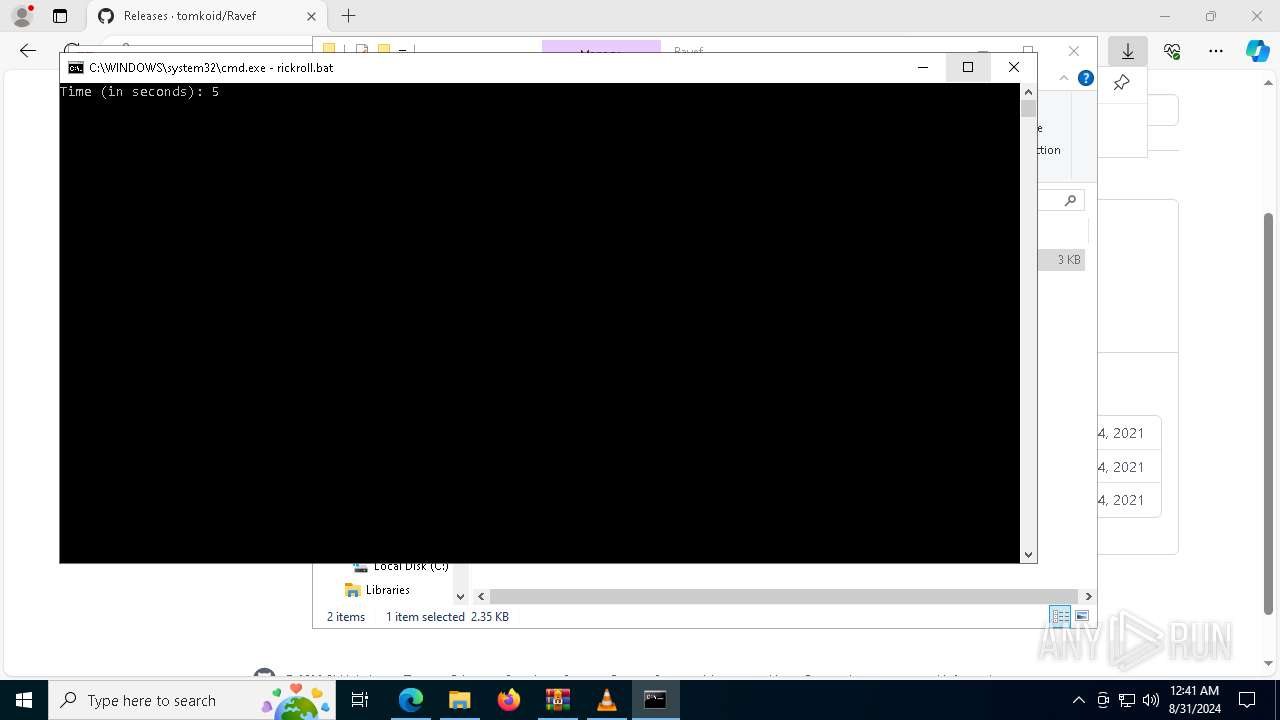
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7208)
- cmd.exe (PID: 6108)
- cmd.exe (PID: 6212)
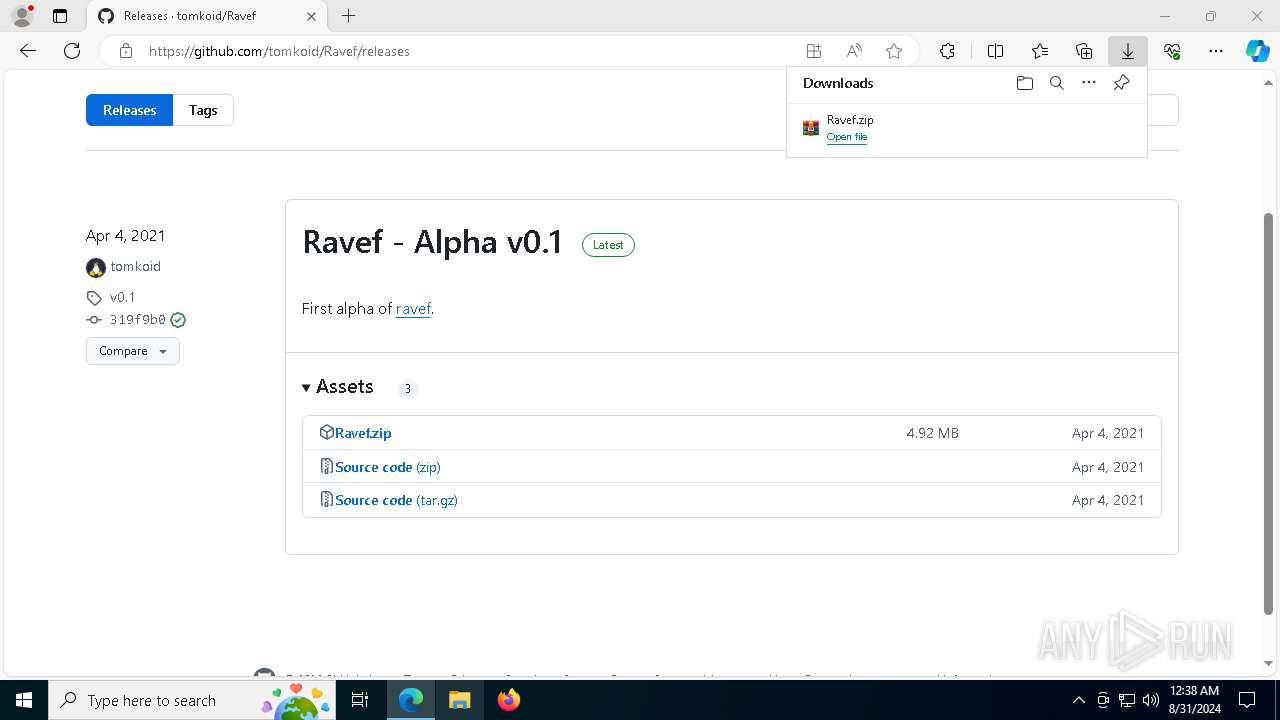
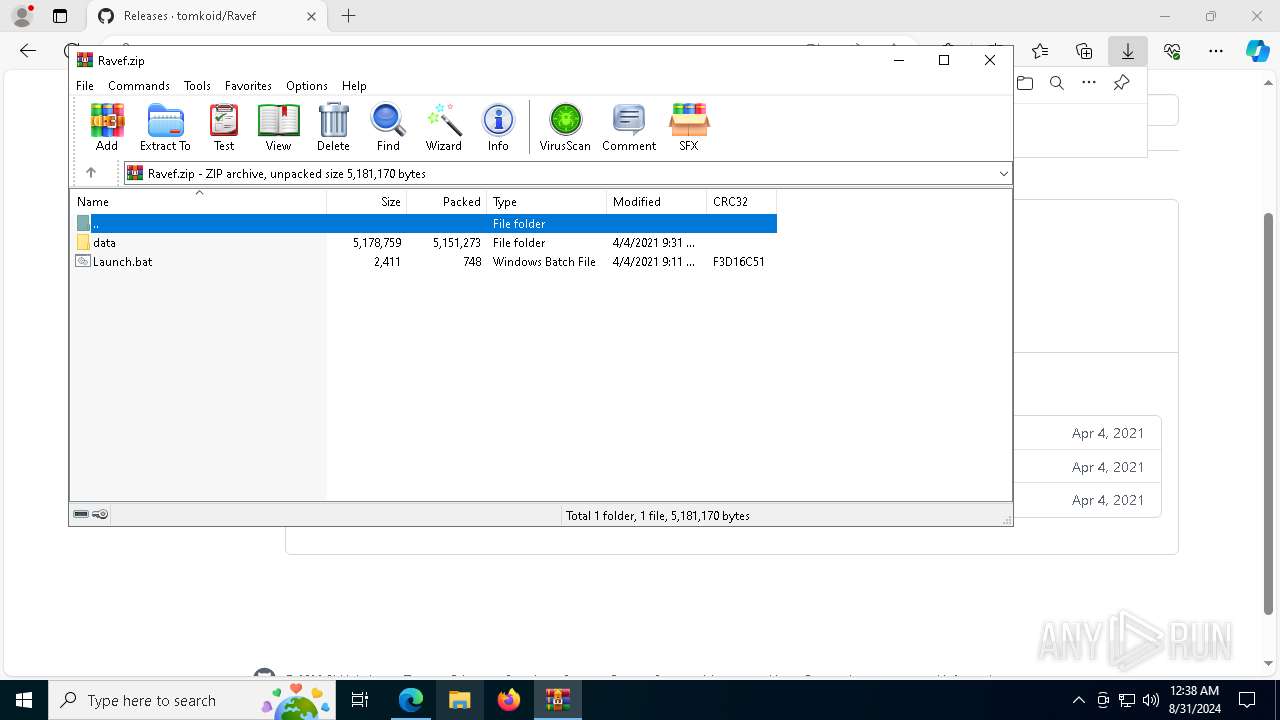
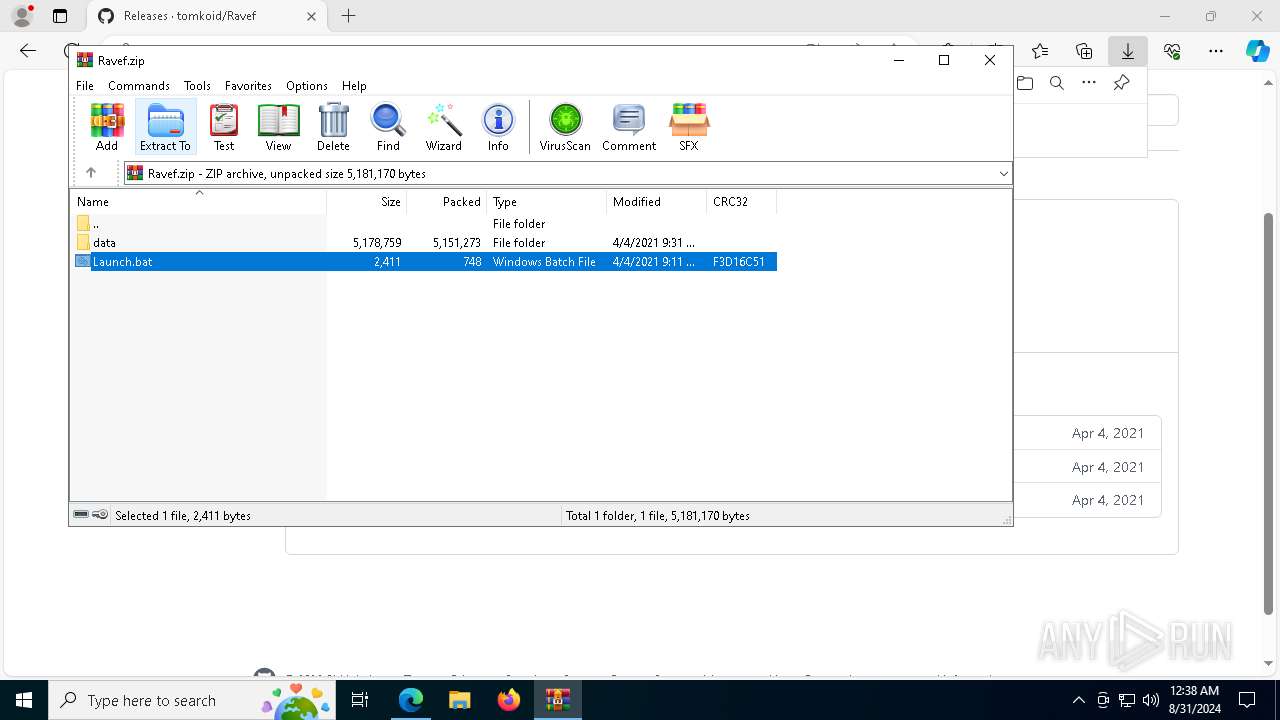
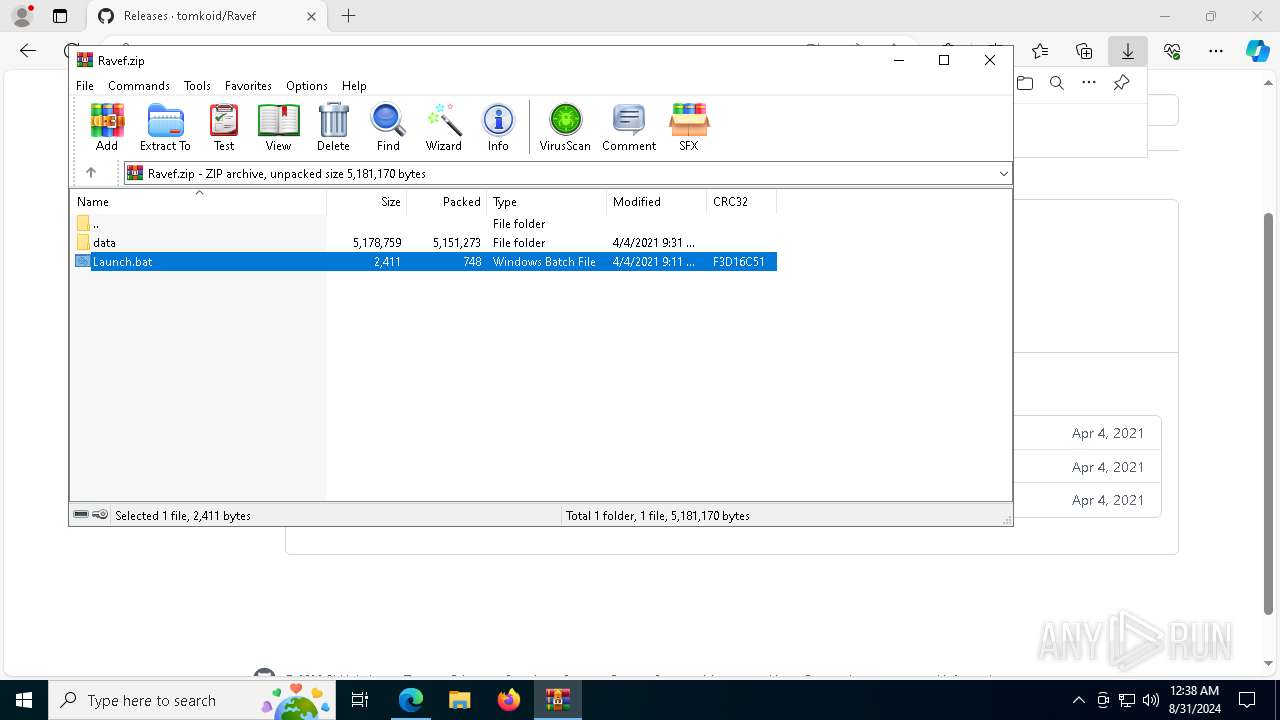
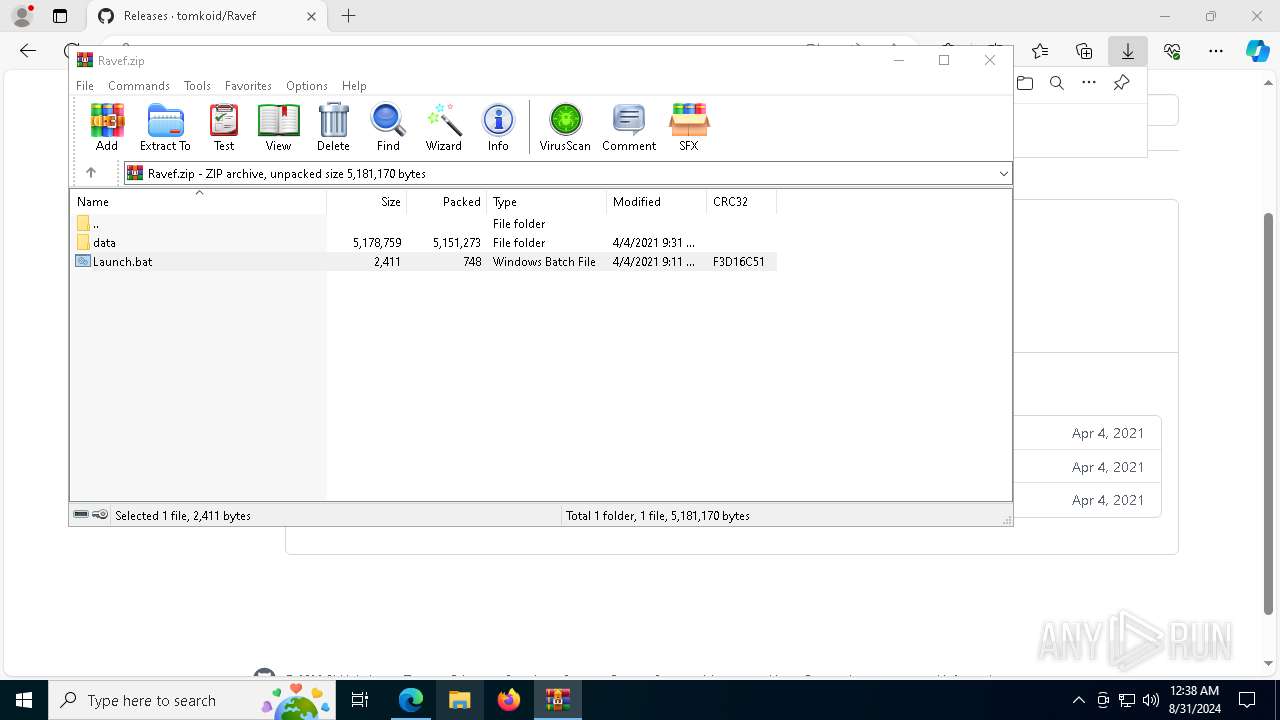
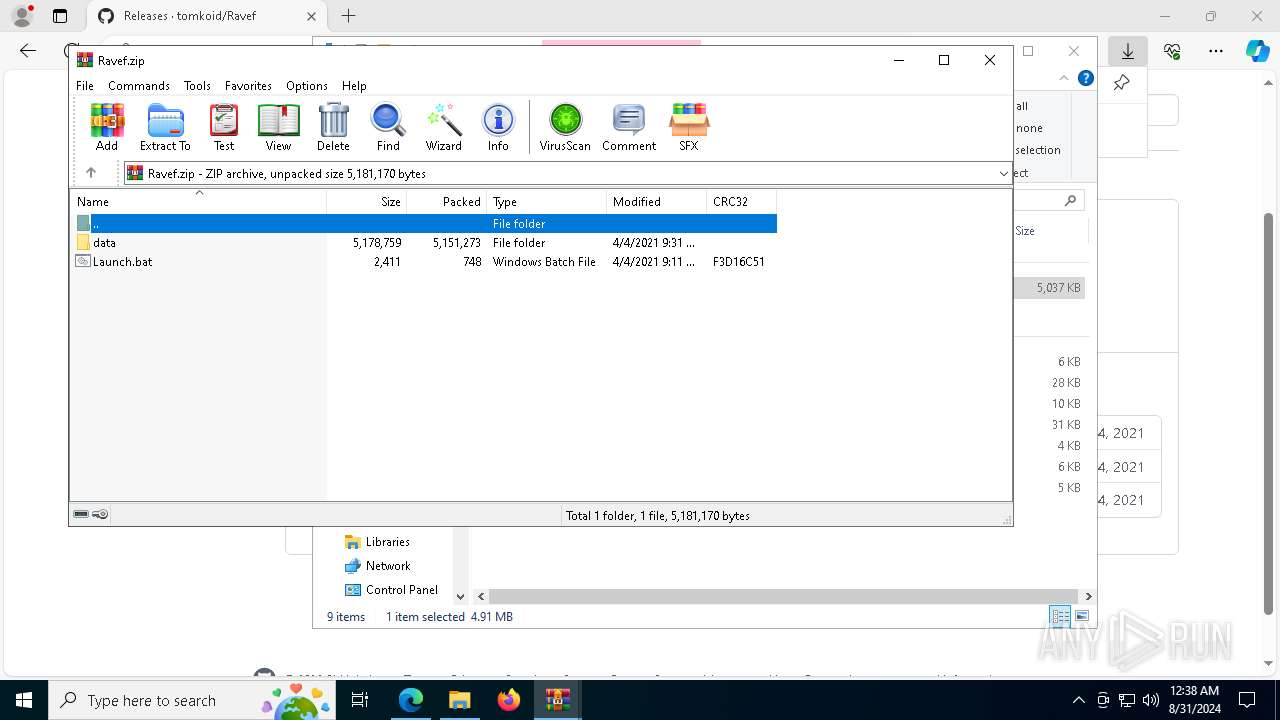
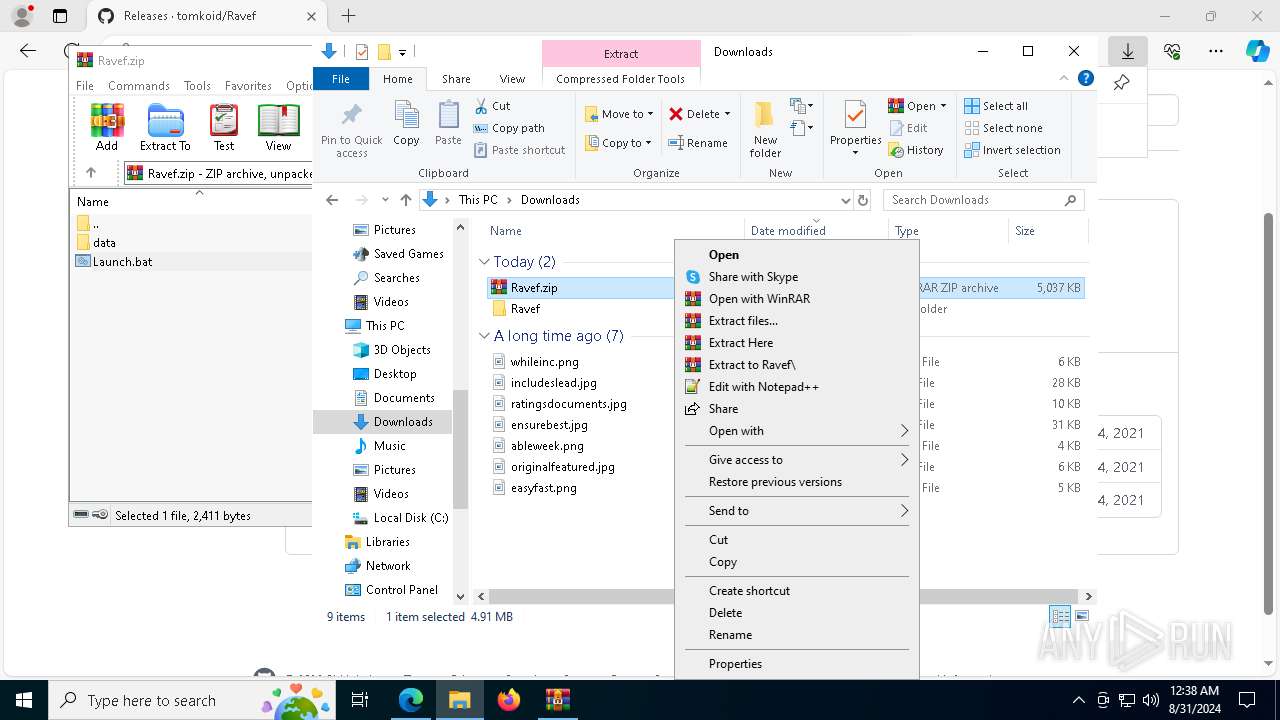
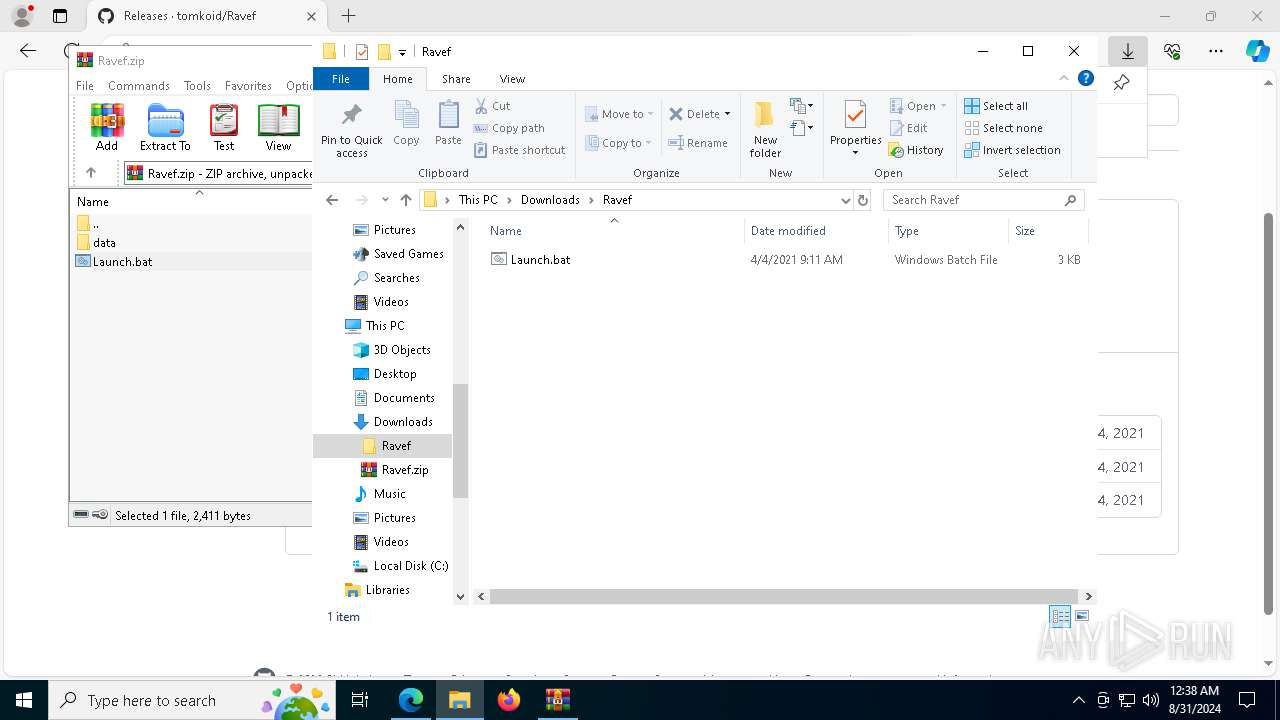
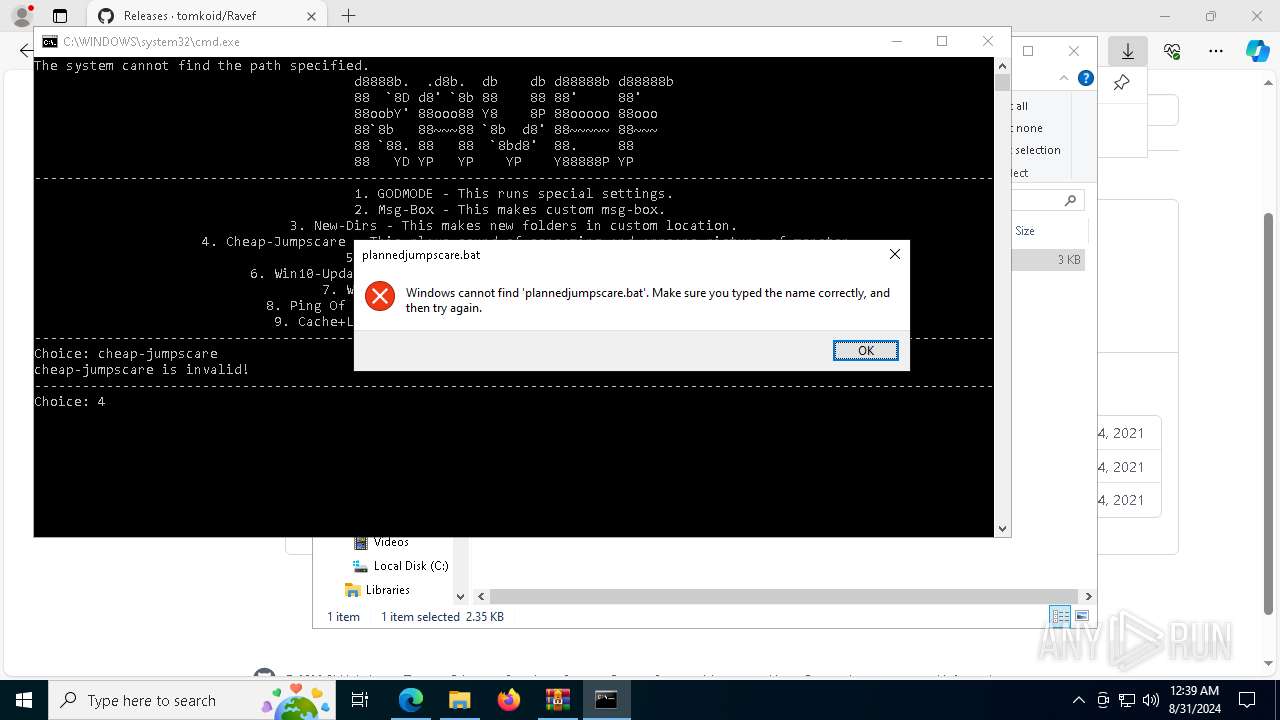
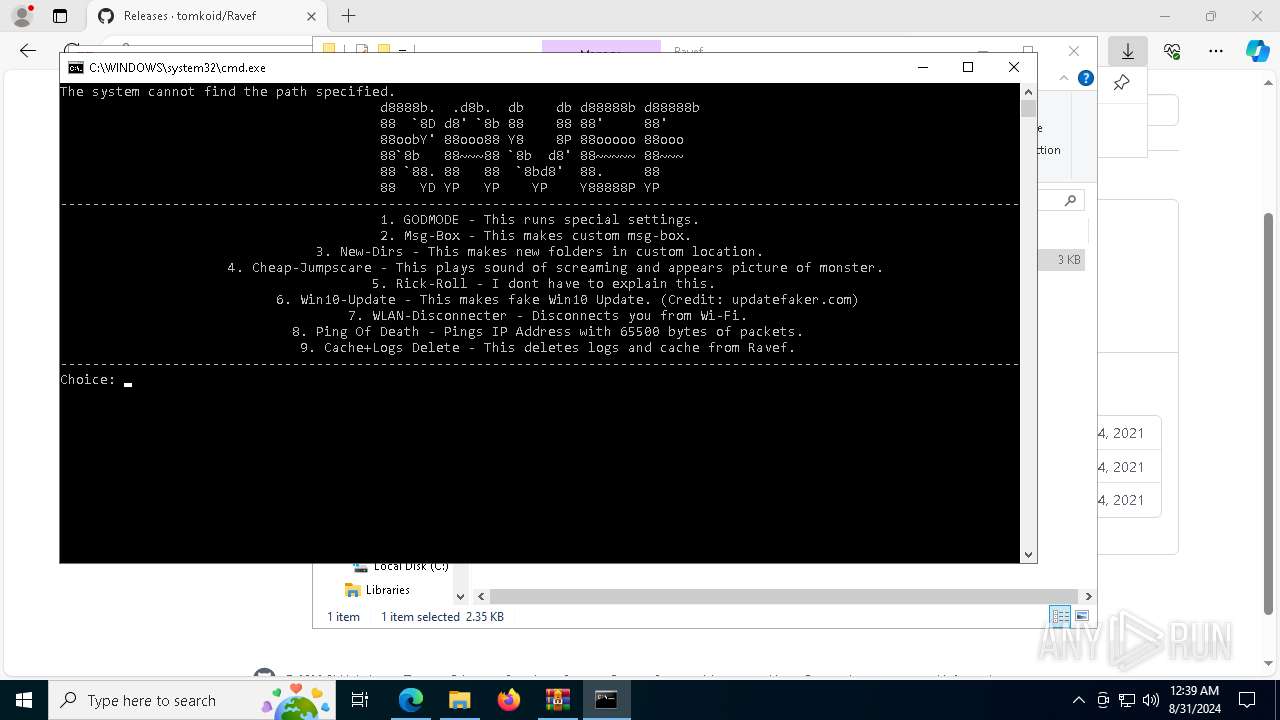
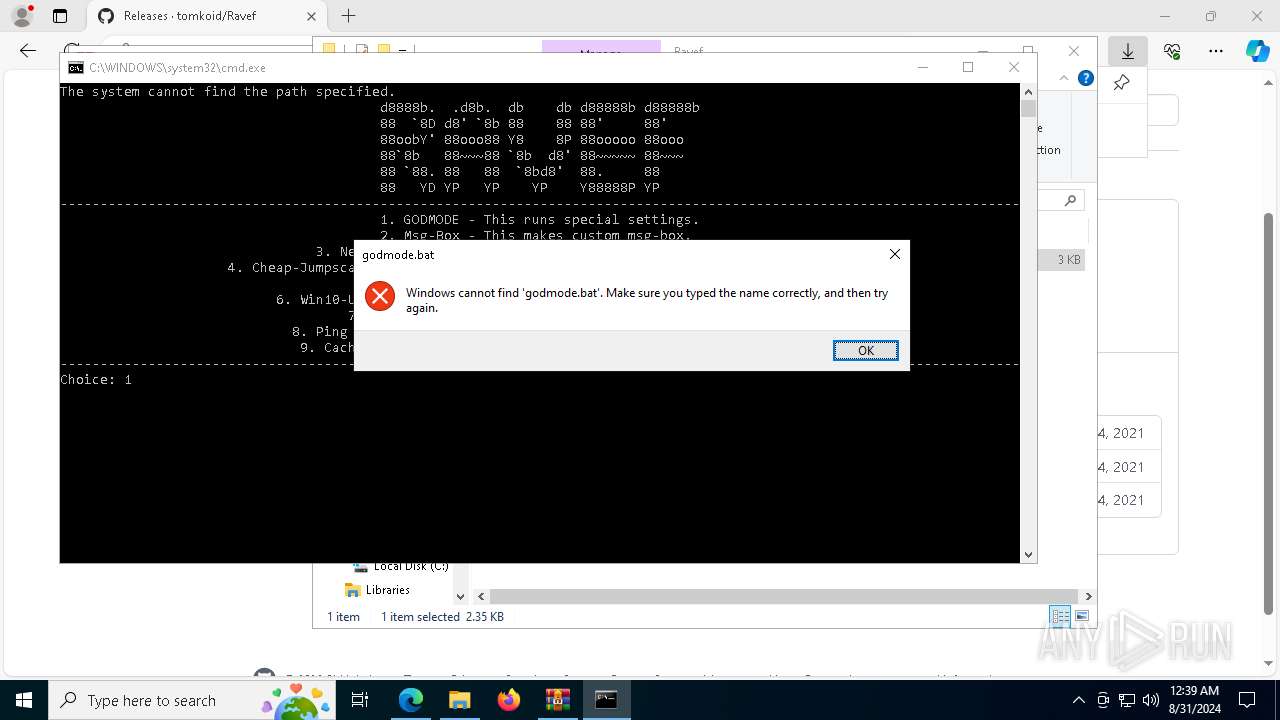
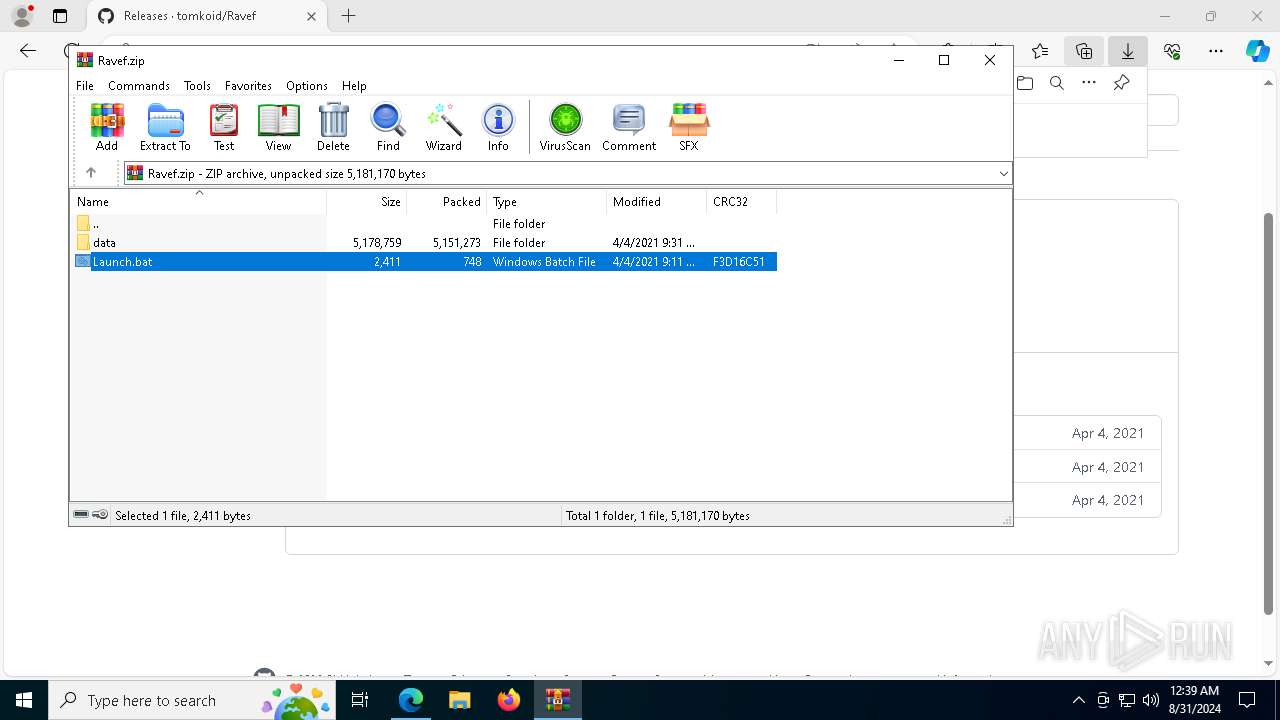
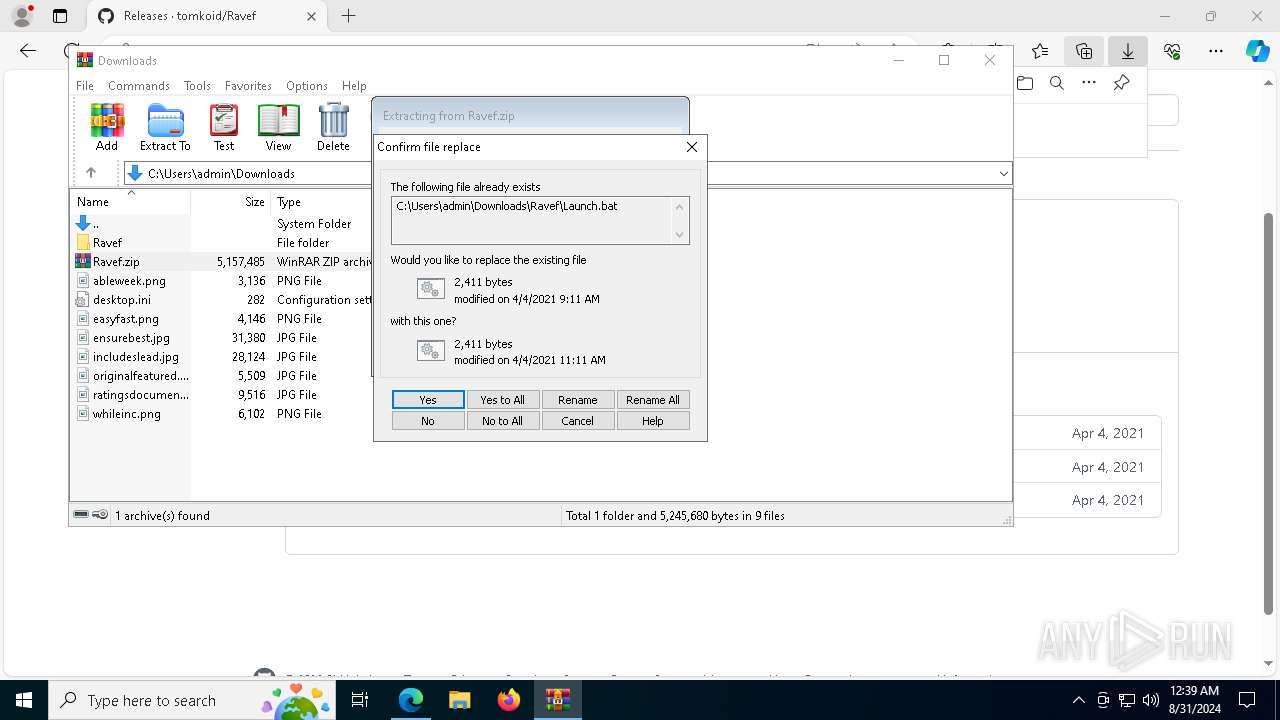
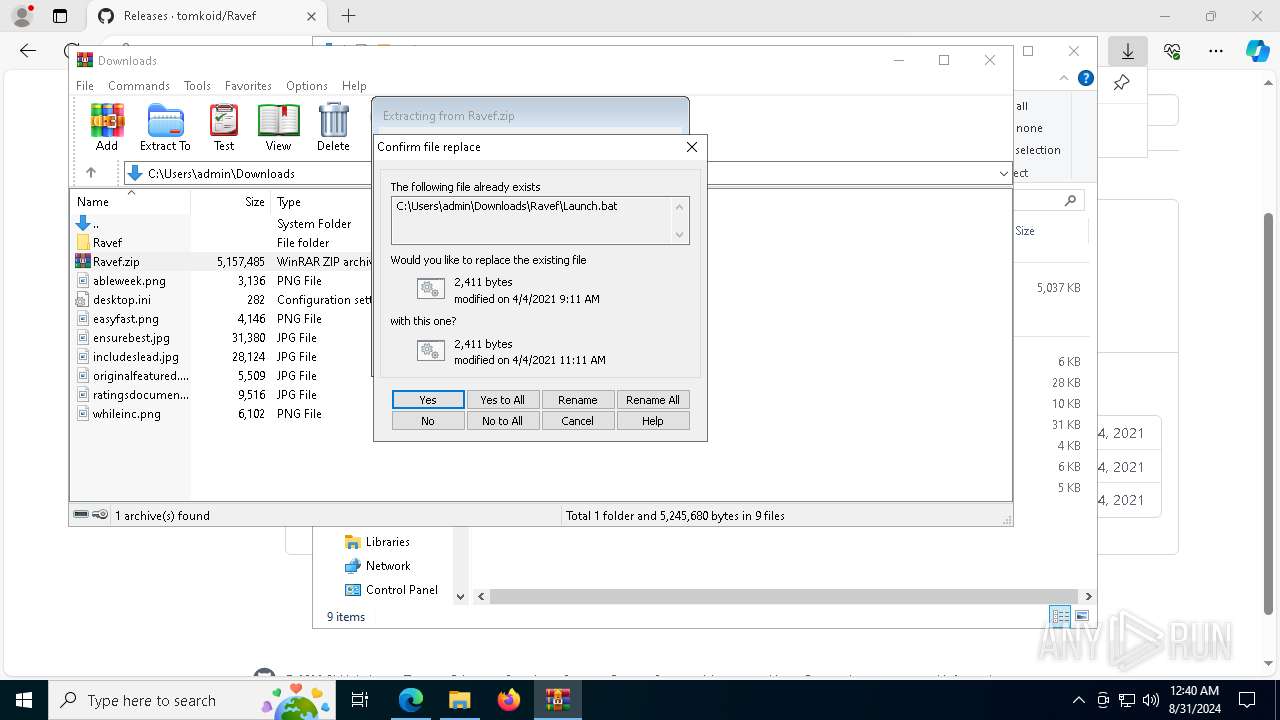
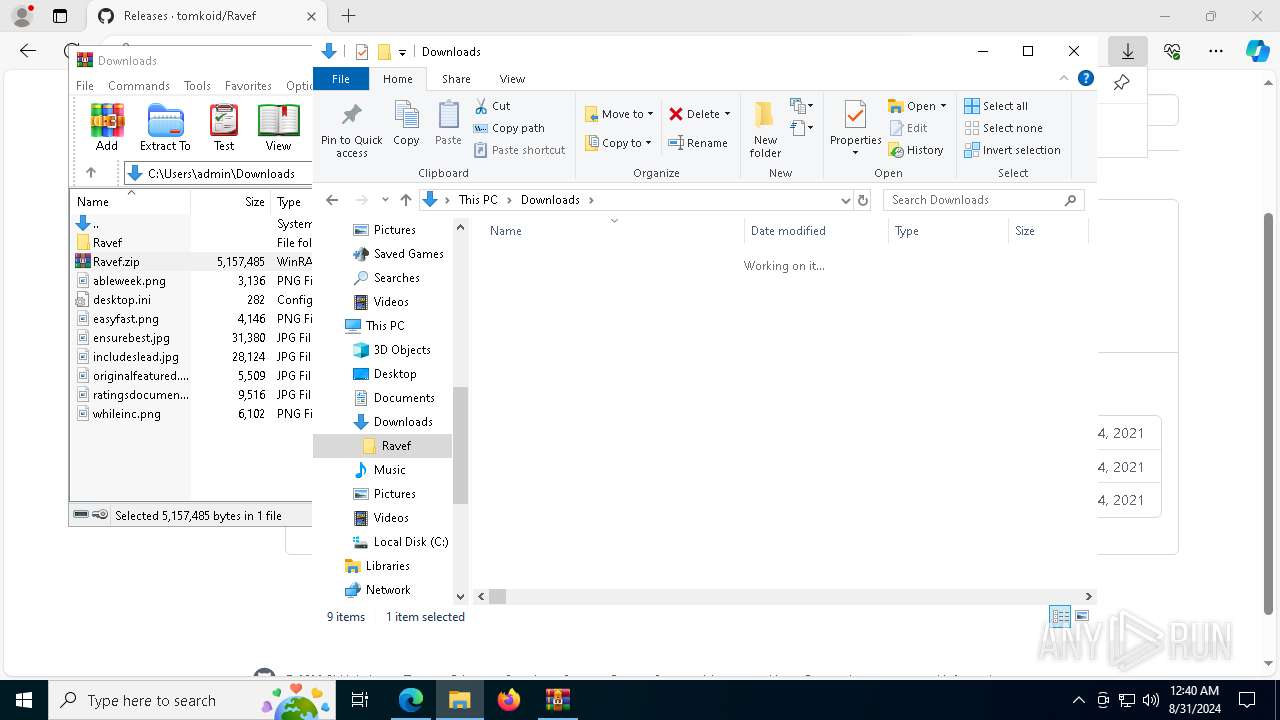
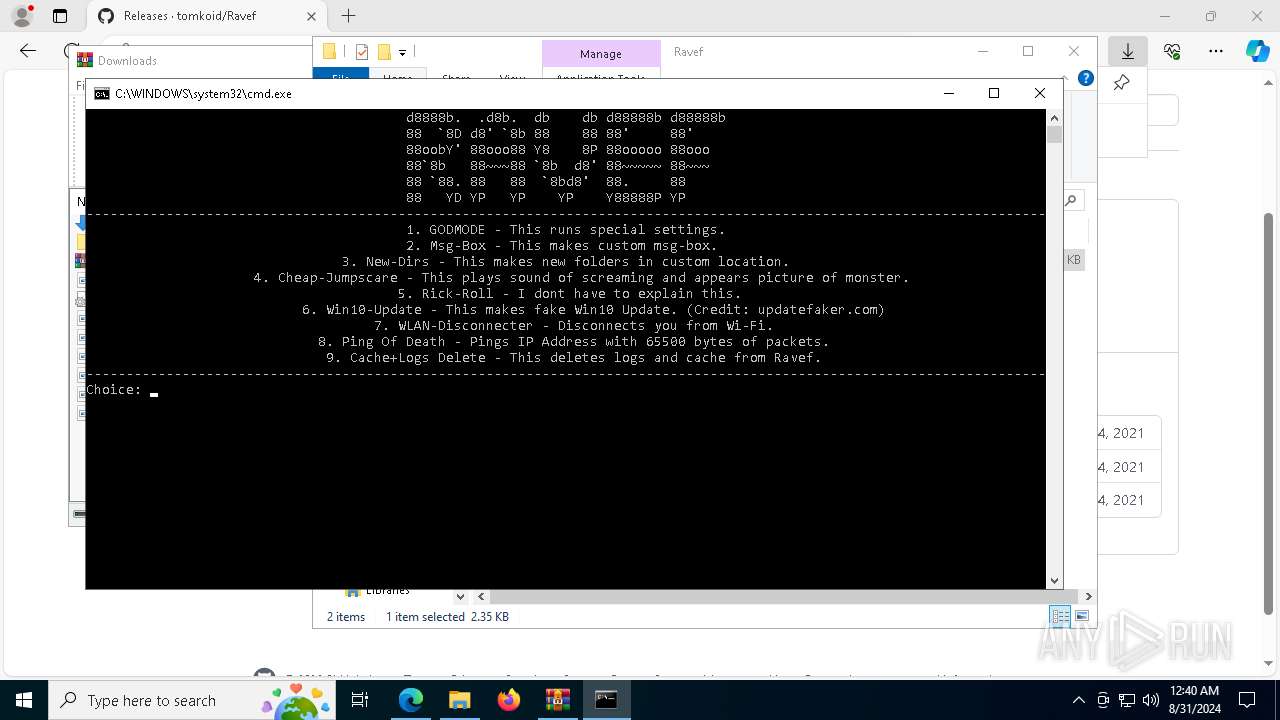
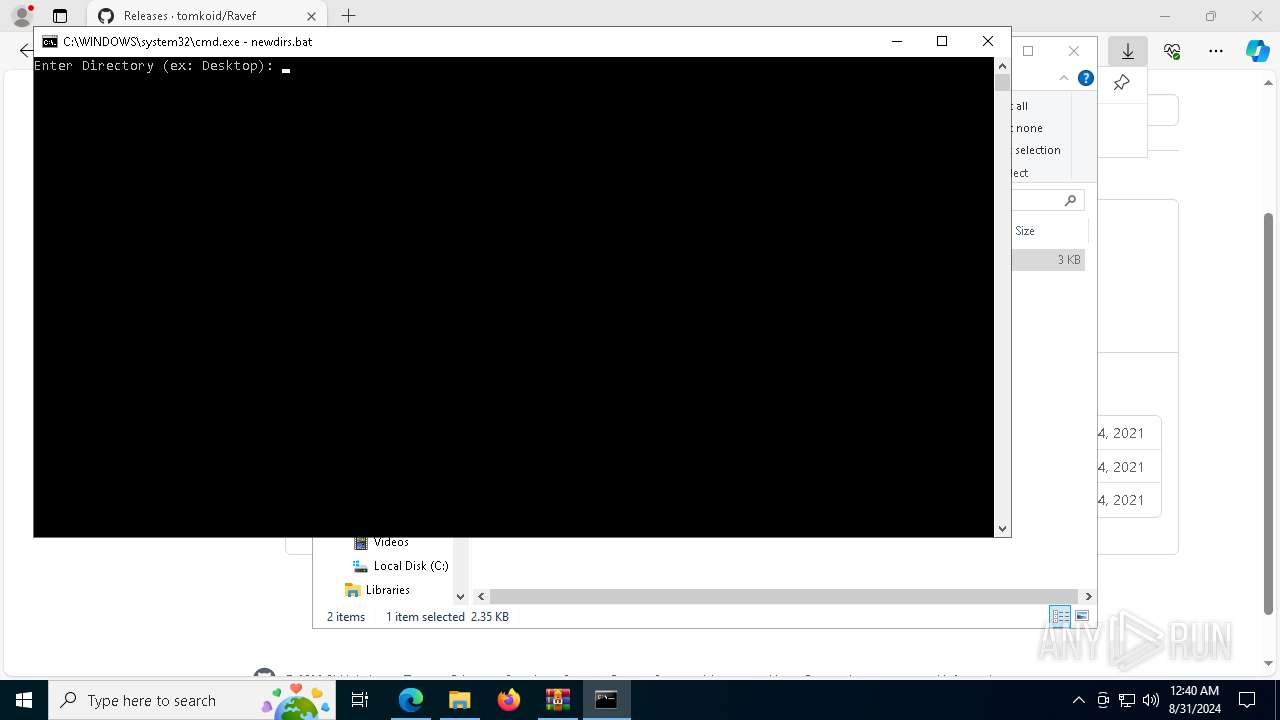
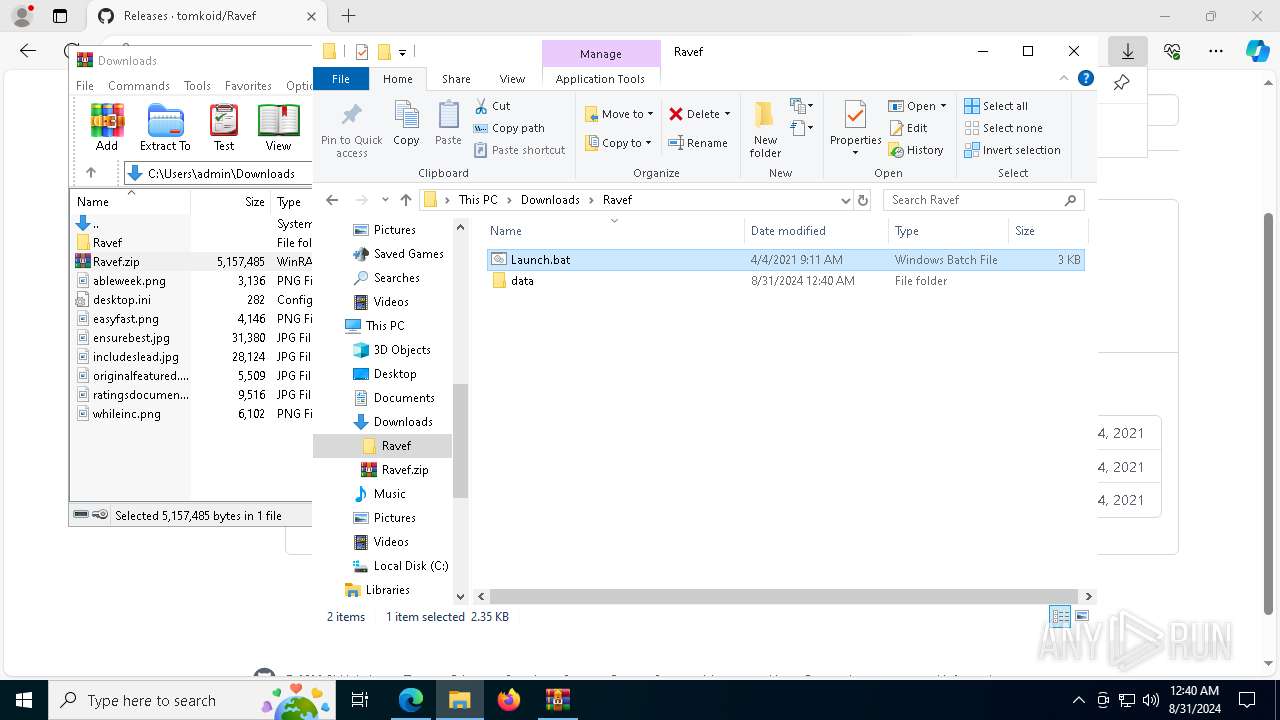
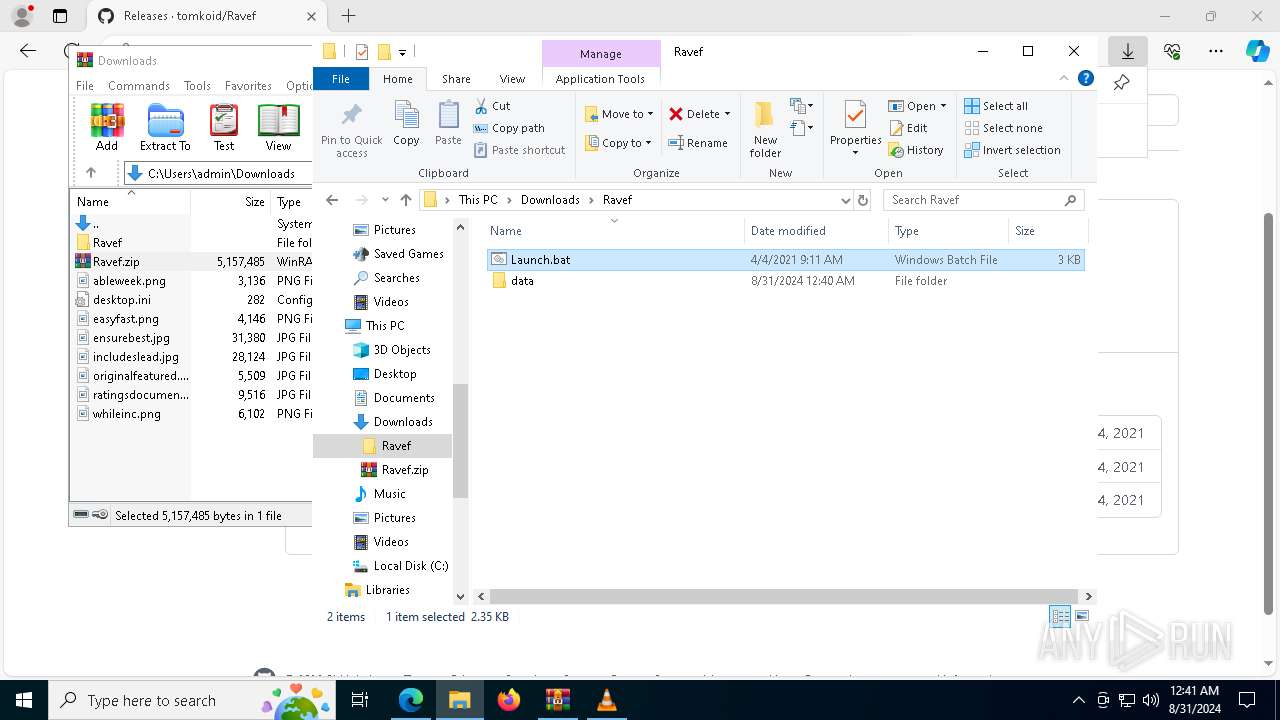
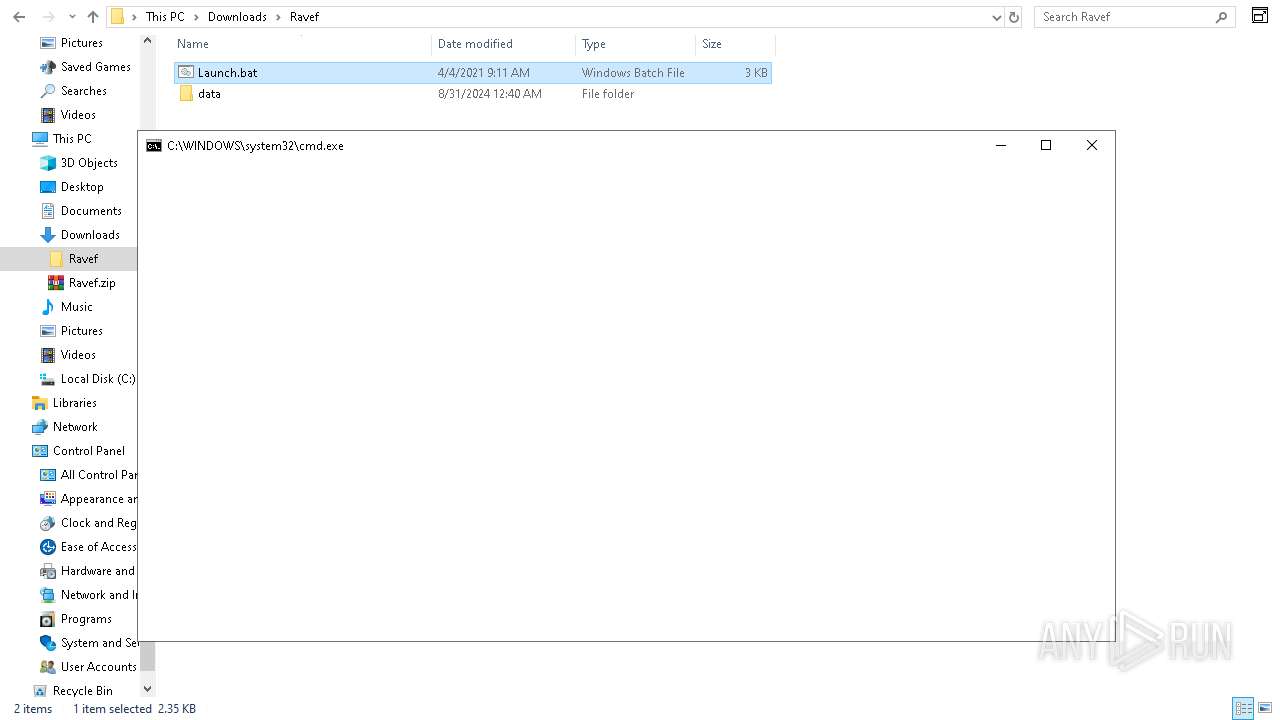
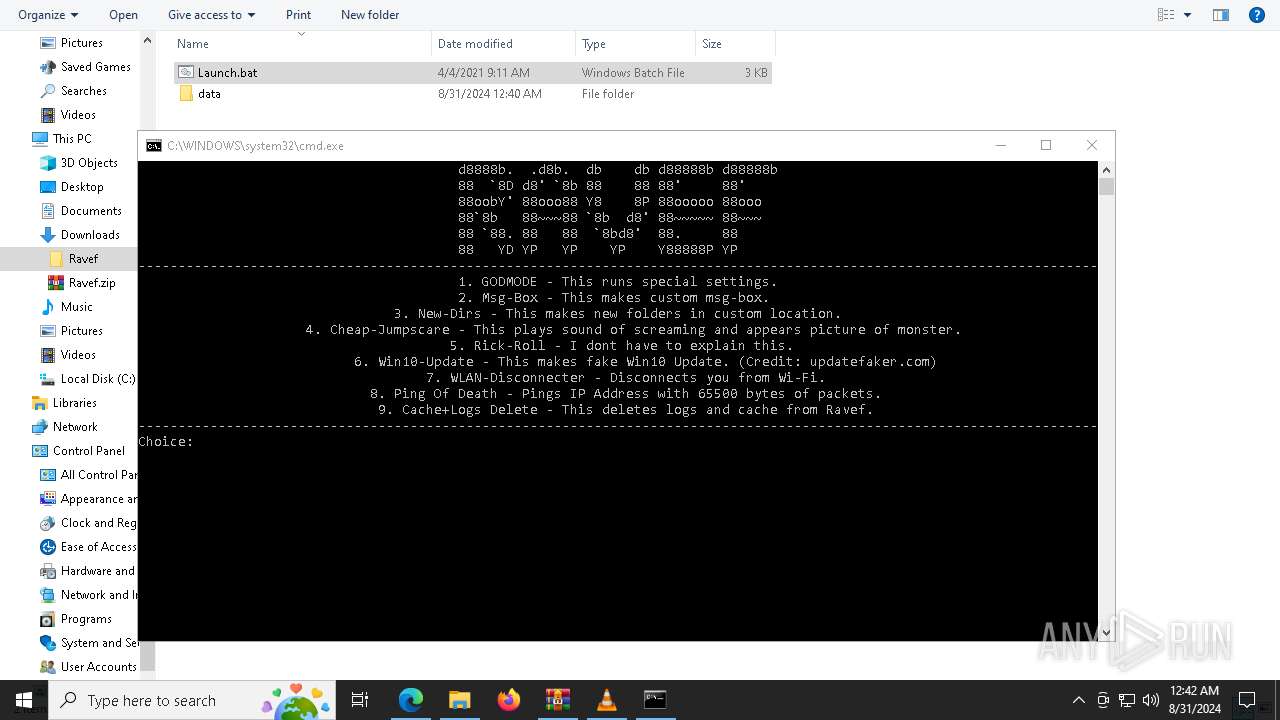
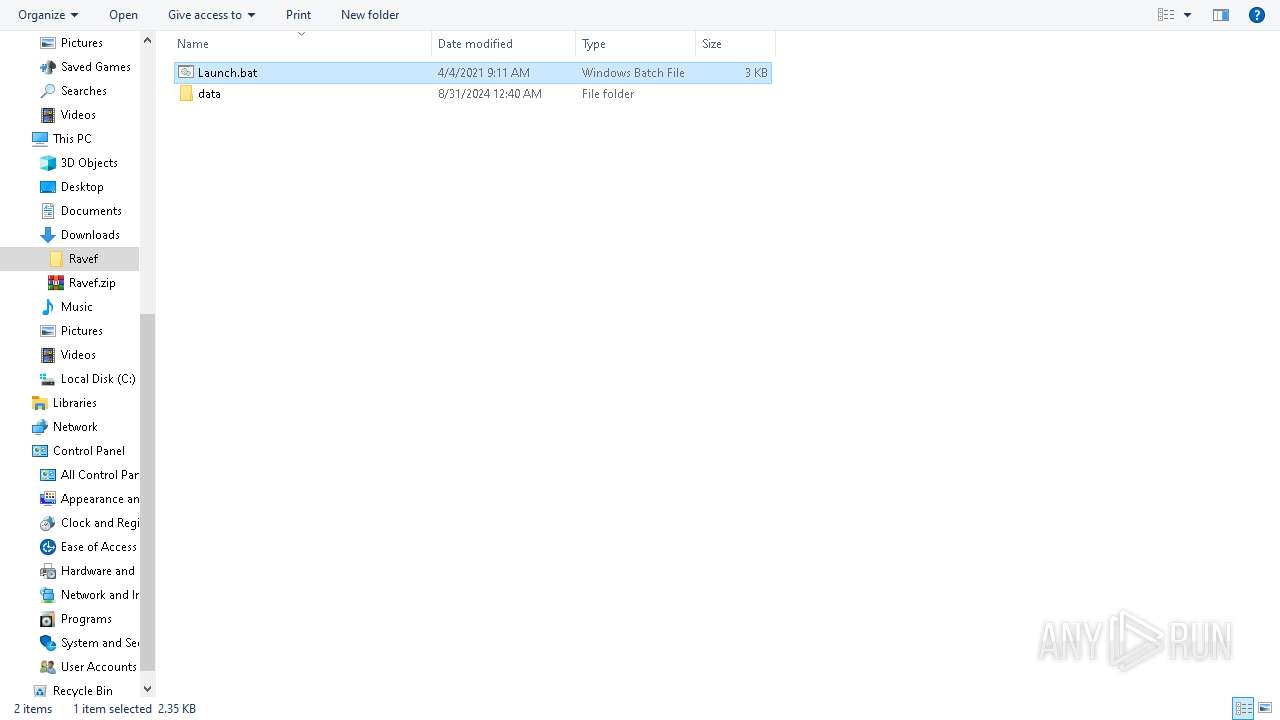
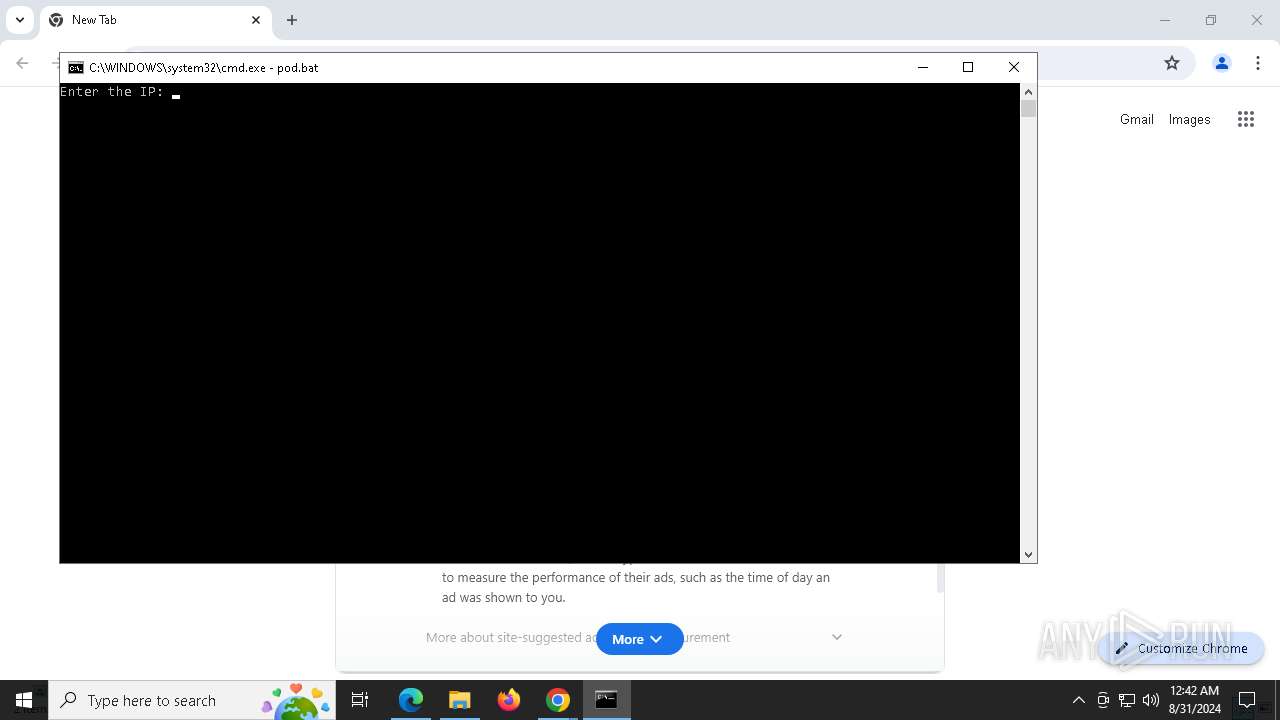
Executing commands from a ".bat" file
- cmd.exe (PID: 892)
- cmd.exe (PID: 7108)
- cmd.exe (PID: 4672)
- cmd.exe (PID: 2368)
- cmd.exe (PID: 6512)
- cmd.exe (PID: 7288)
- cmd.exe (PID: 6952)
- cmd.exe (PID: 2384)
- cmd.exe (PID: 6692)
- cmd.exe (PID: 7652)
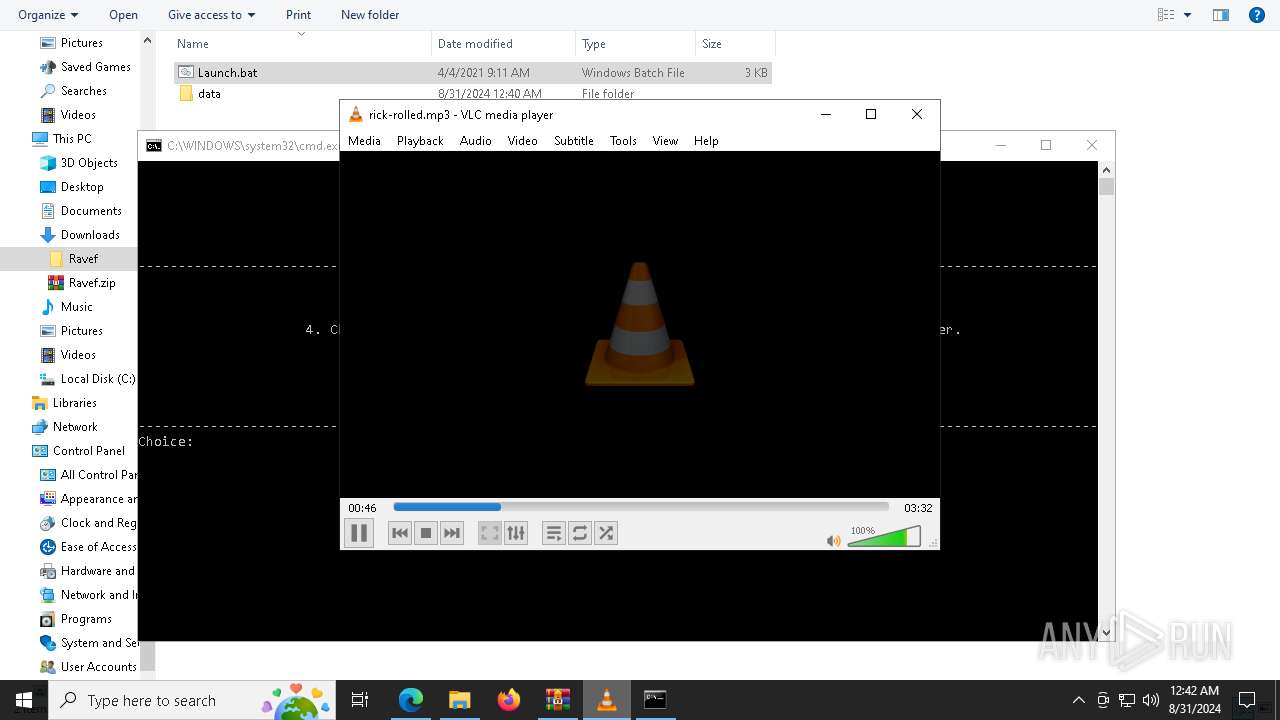
There is functionality for taking screenshot (YARA)
- vlc.exe (PID: 6580)
The process executes VB scripts
- cmd.exe (PID: 7868)
- cmd.exe (PID: 6056)
- cmd.exe (PID: 32)
Runs shell command (SCRIPT)
- wscript.exe (PID: 8156)
- wscript.exe (PID: 400)
- wscript.exe (PID: 7088)
INFO
Application launched itself
- msedge.exe (PID: 6988)
- chrome.exe (PID: 6456)
- chrome.exe (PID: 8128)
- chrome.exe (PID: 8104)
Checks supported languages
- identity_helper.exe (PID: 7992)
- vlc.exe (PID: 6580)
- vlc.exe (PID: 7780)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6988)
- chrome.exe (PID: 6456)
- chrome.exe (PID: 8128)
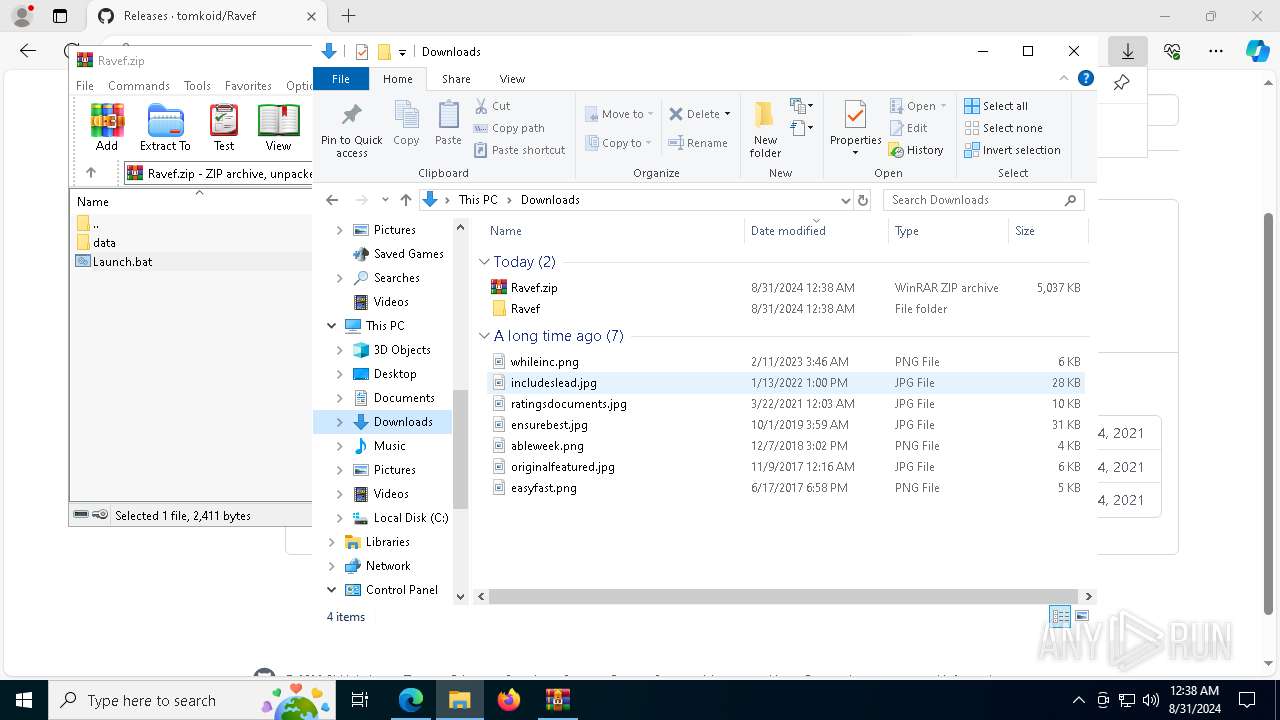
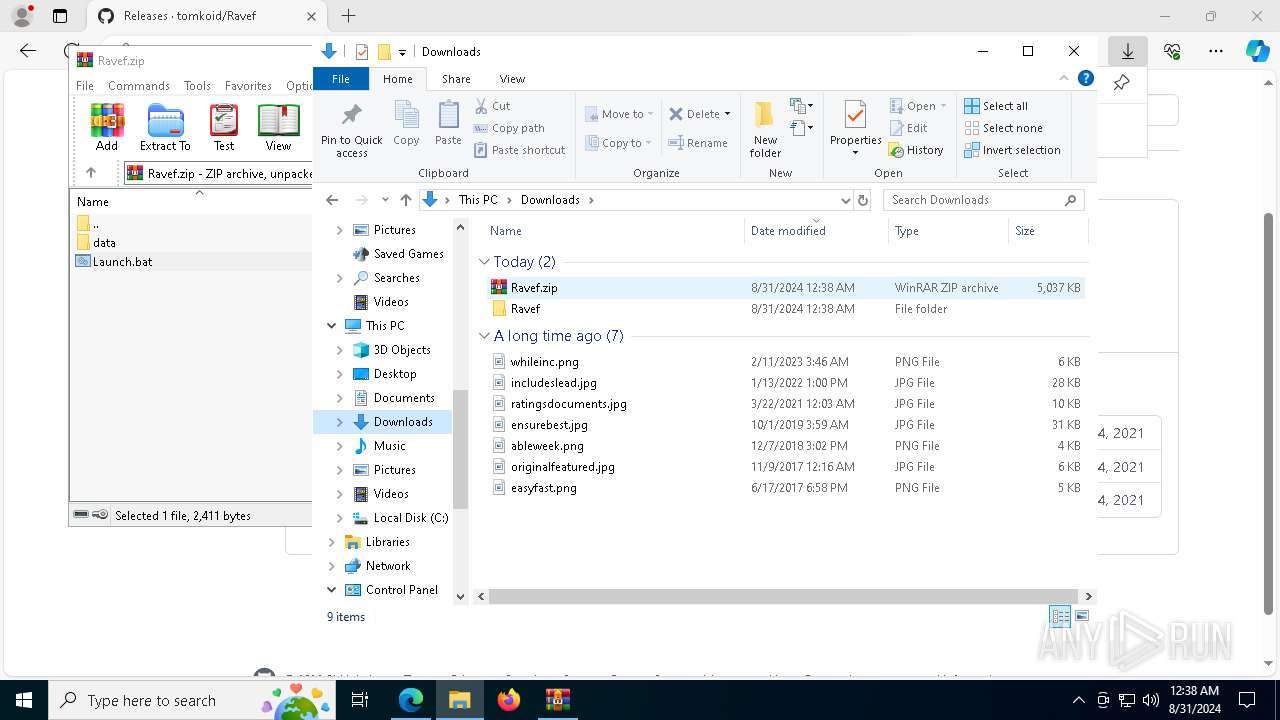
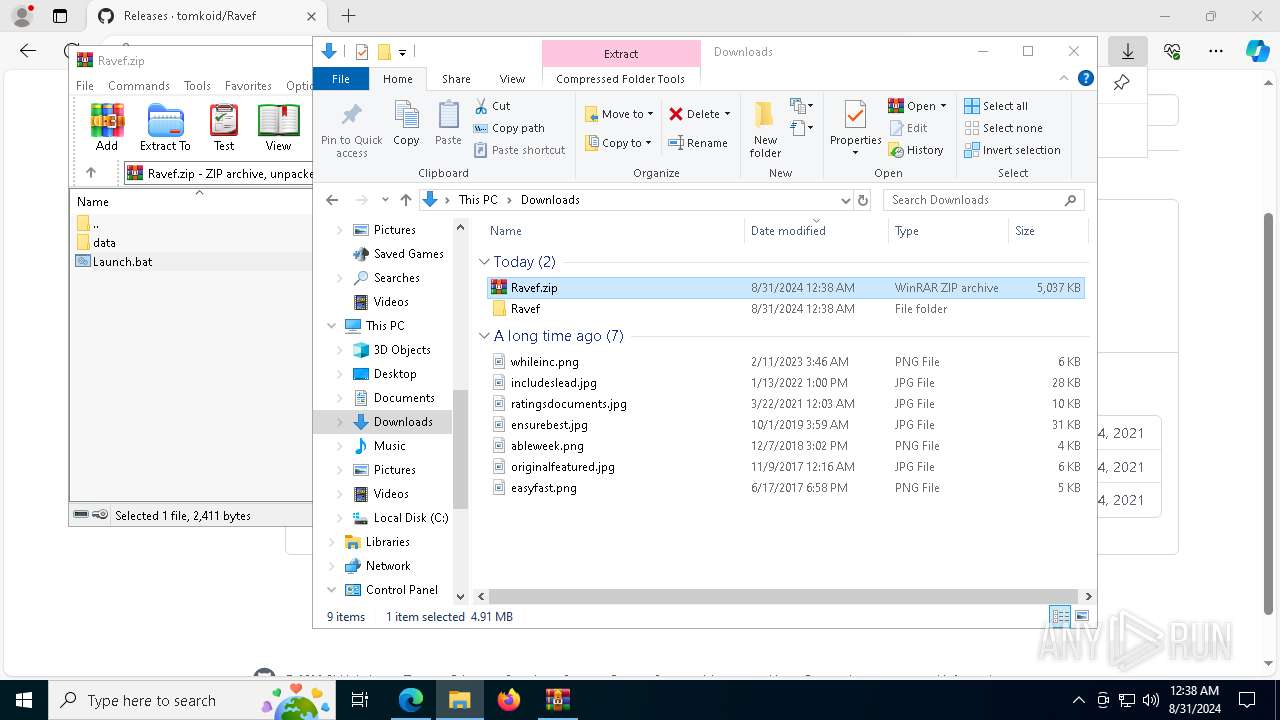
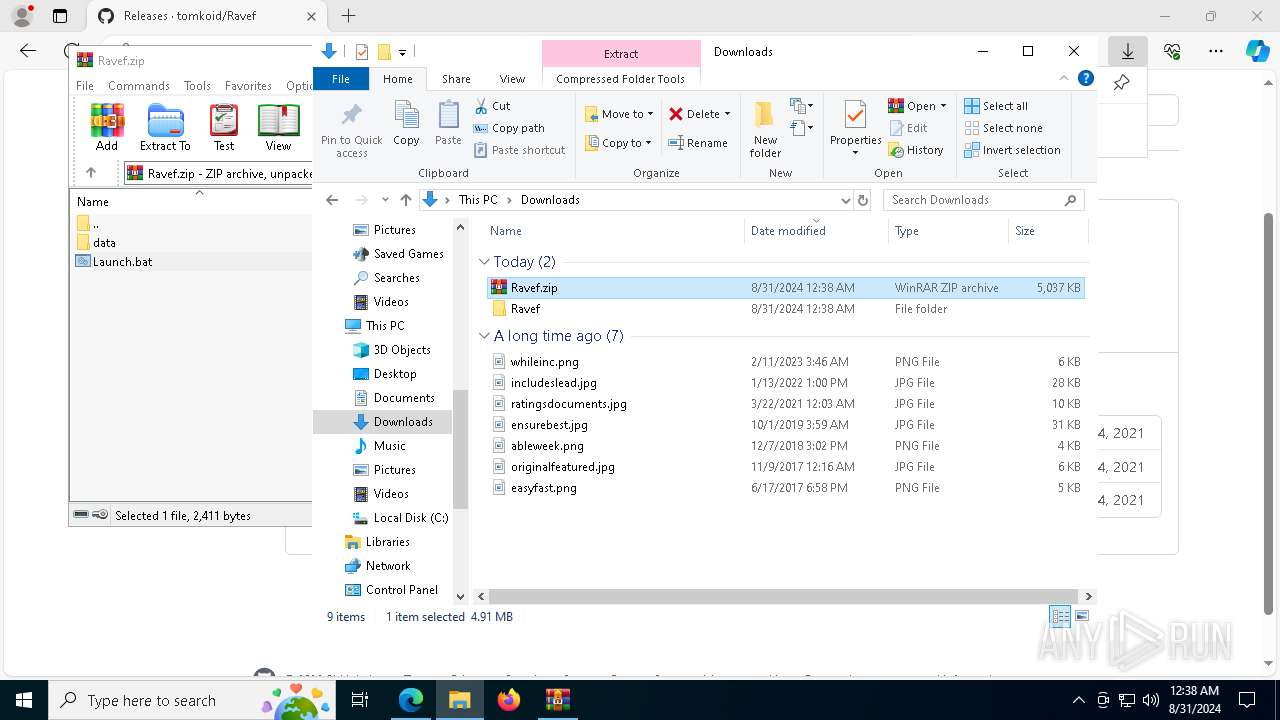
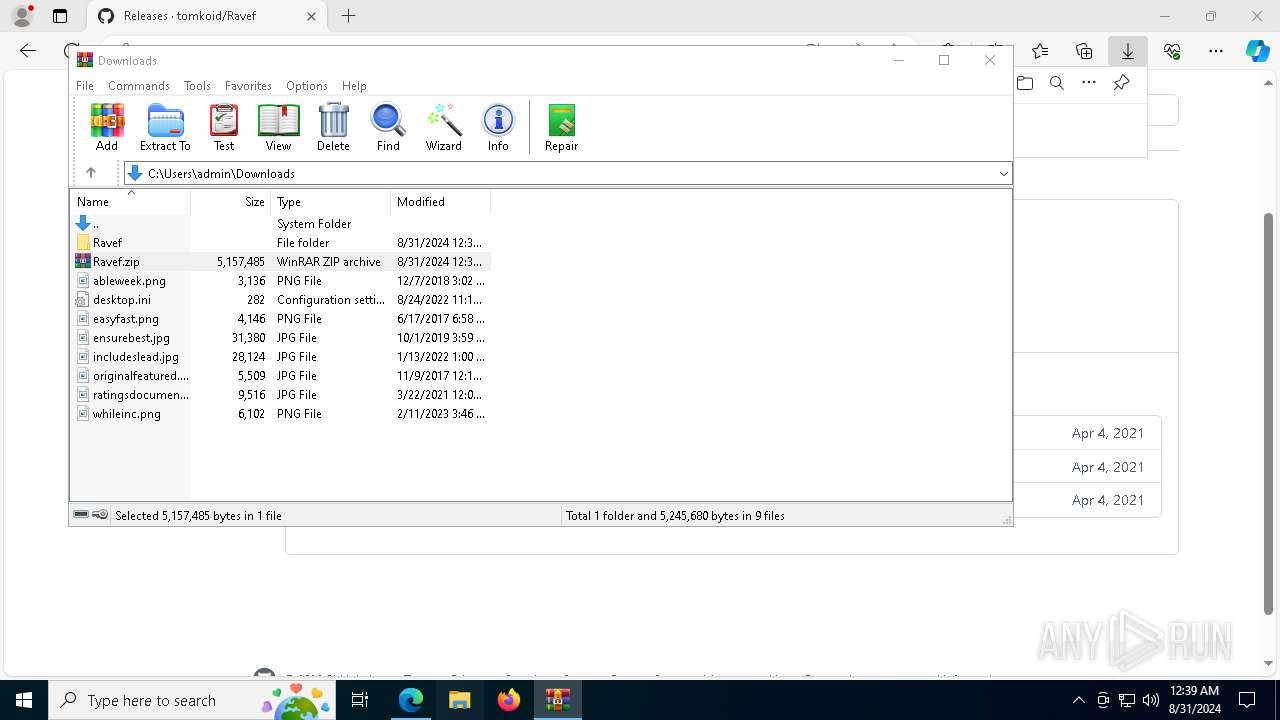
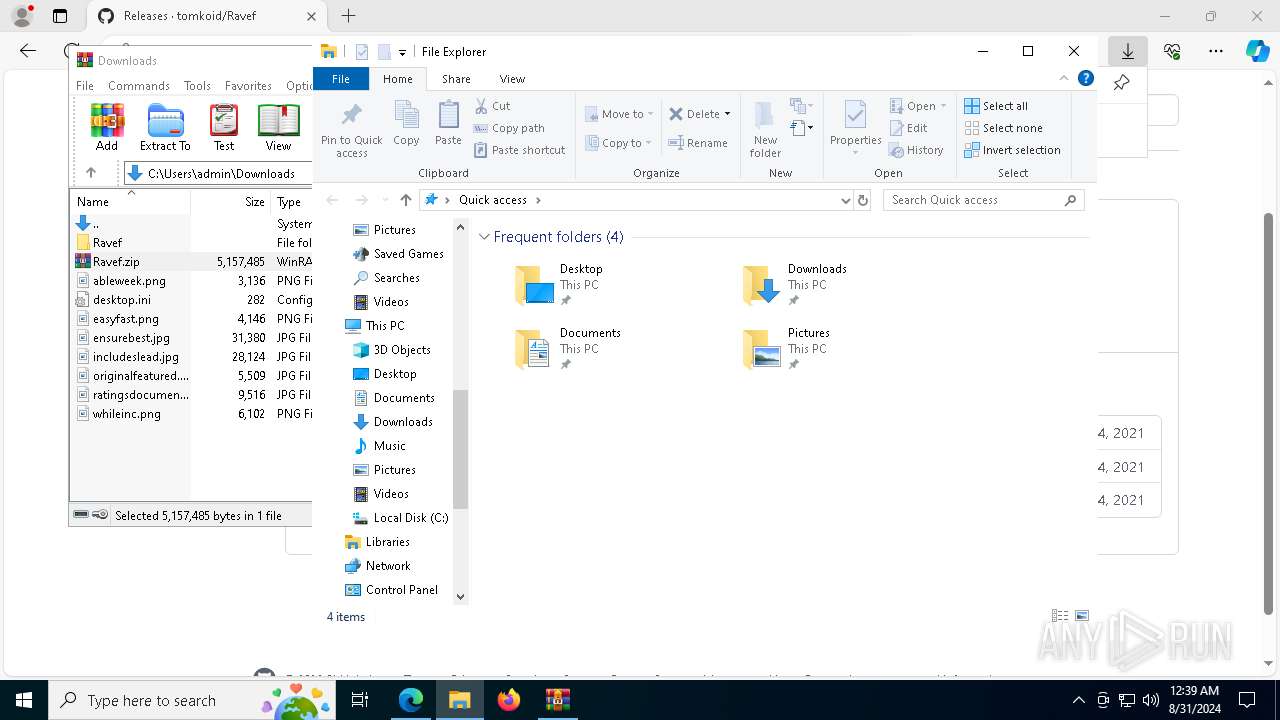
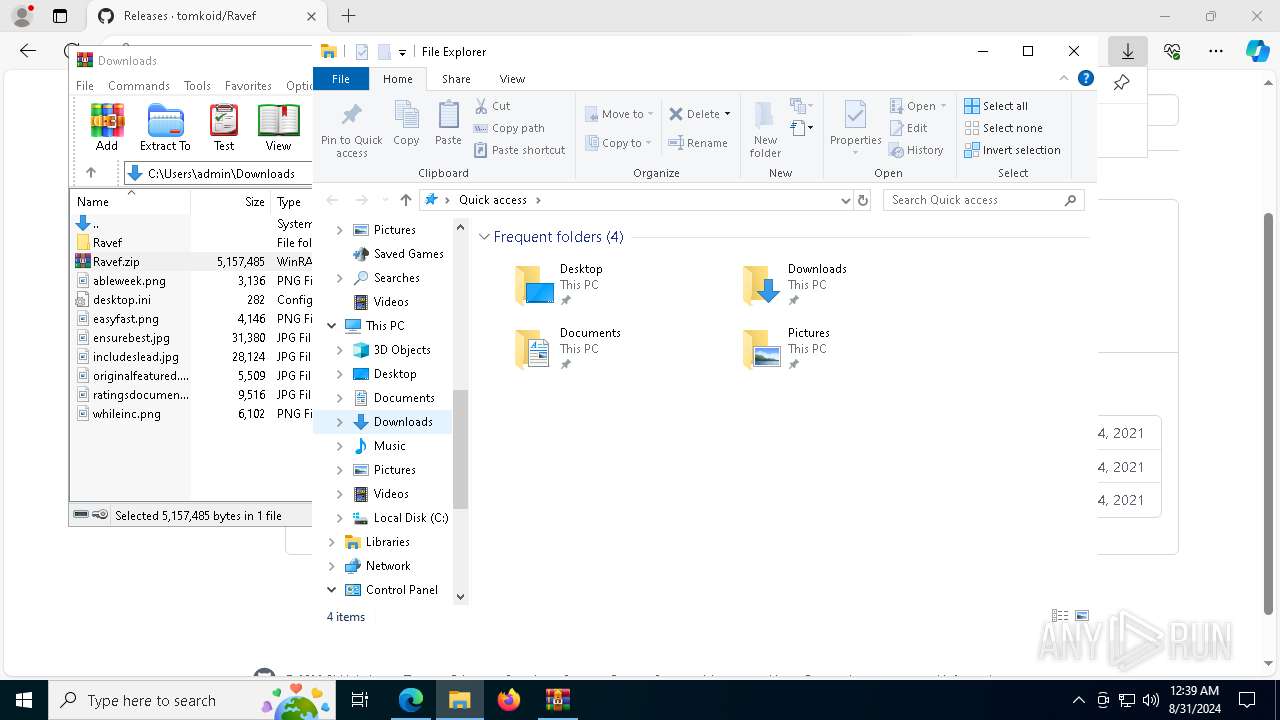
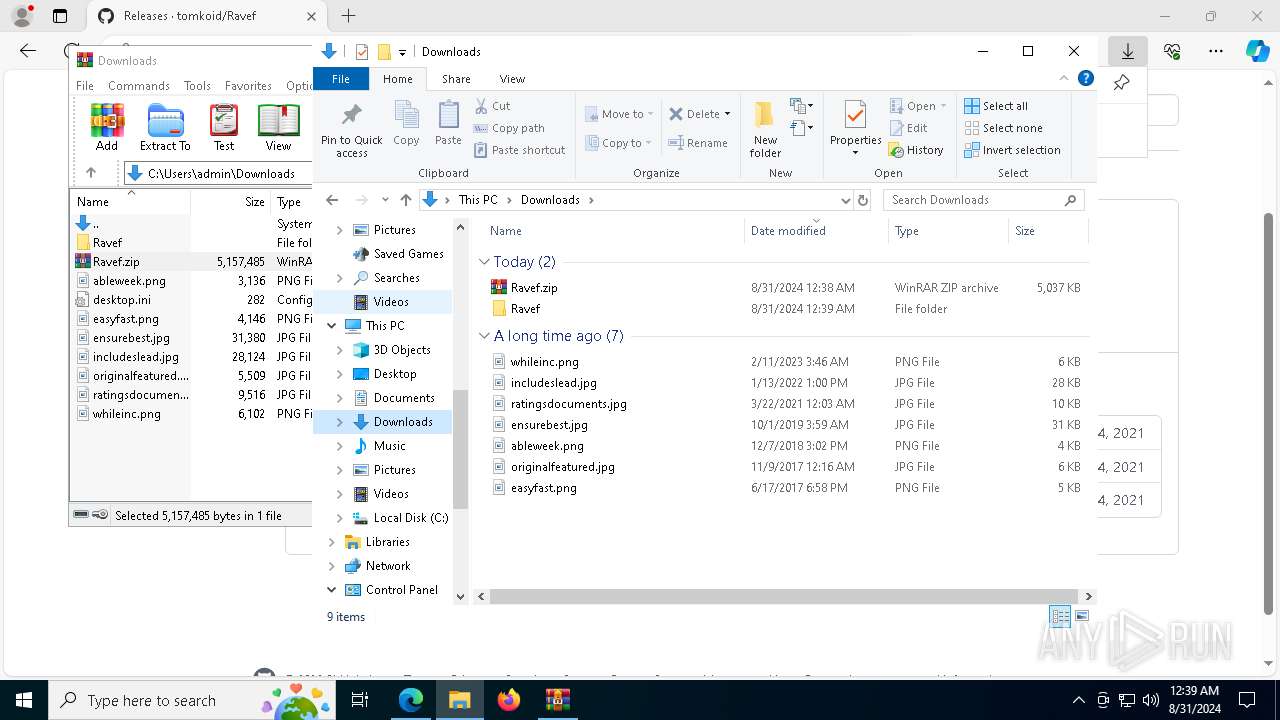
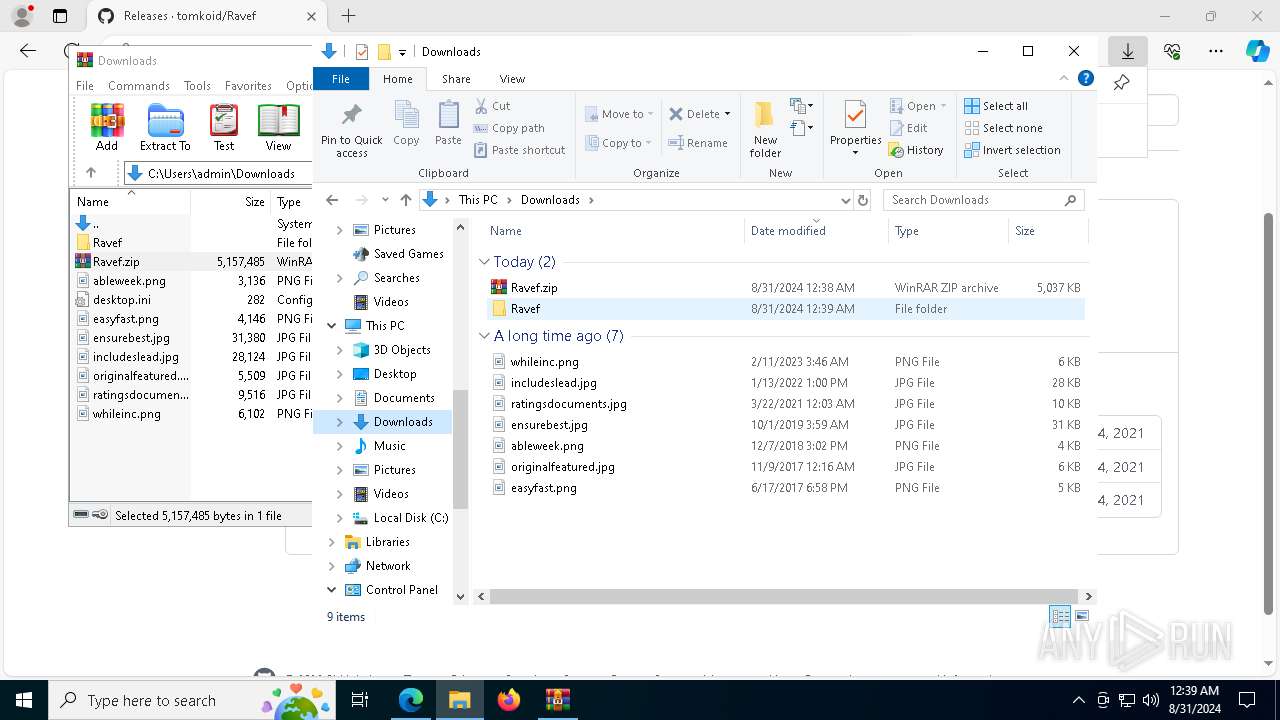
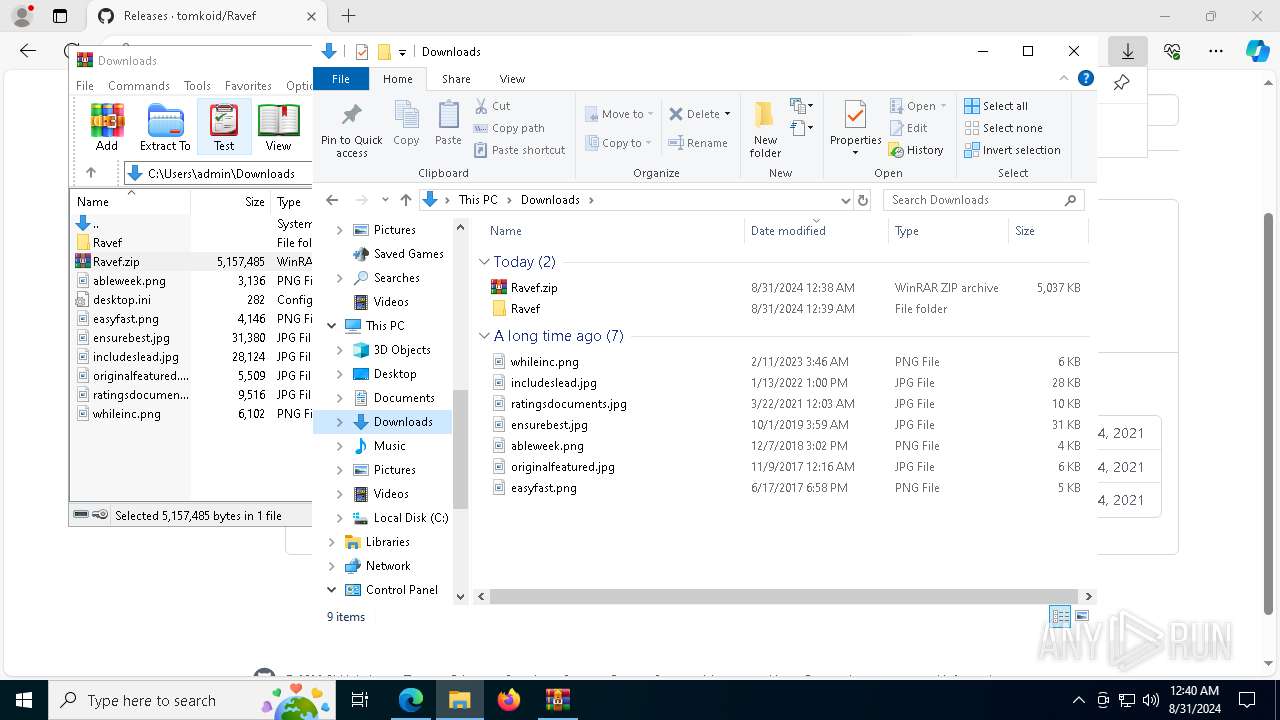
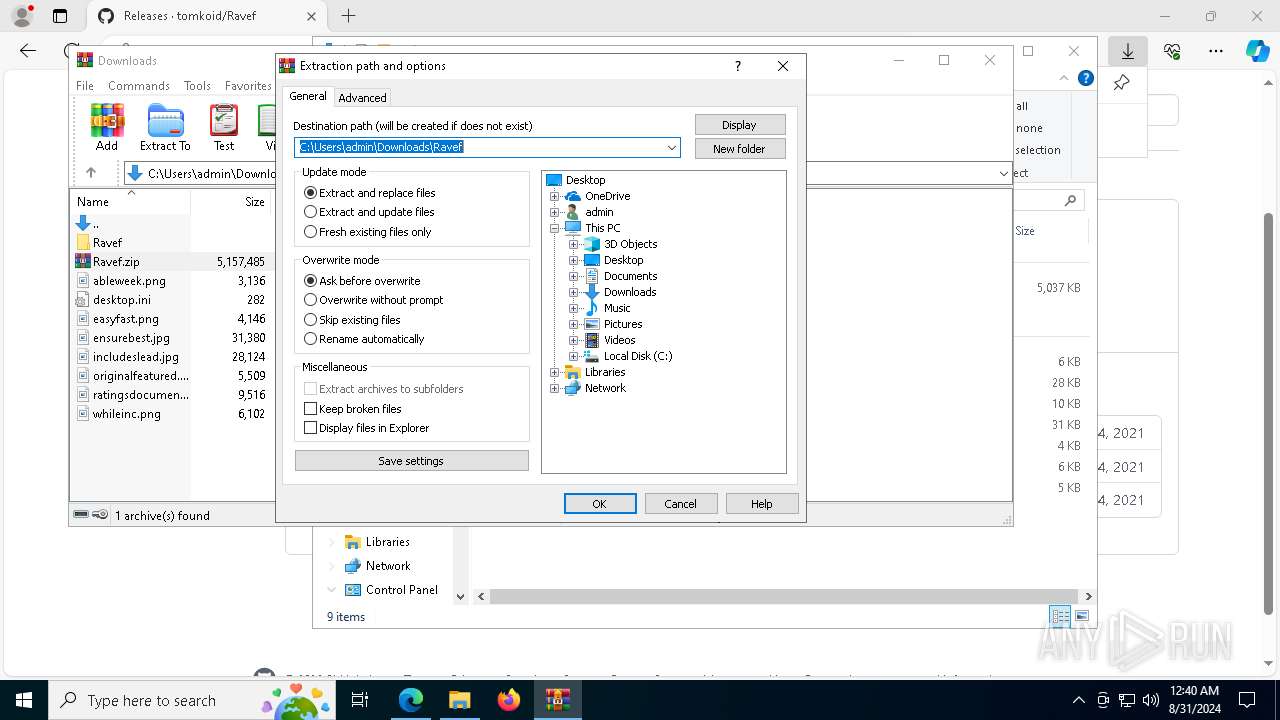
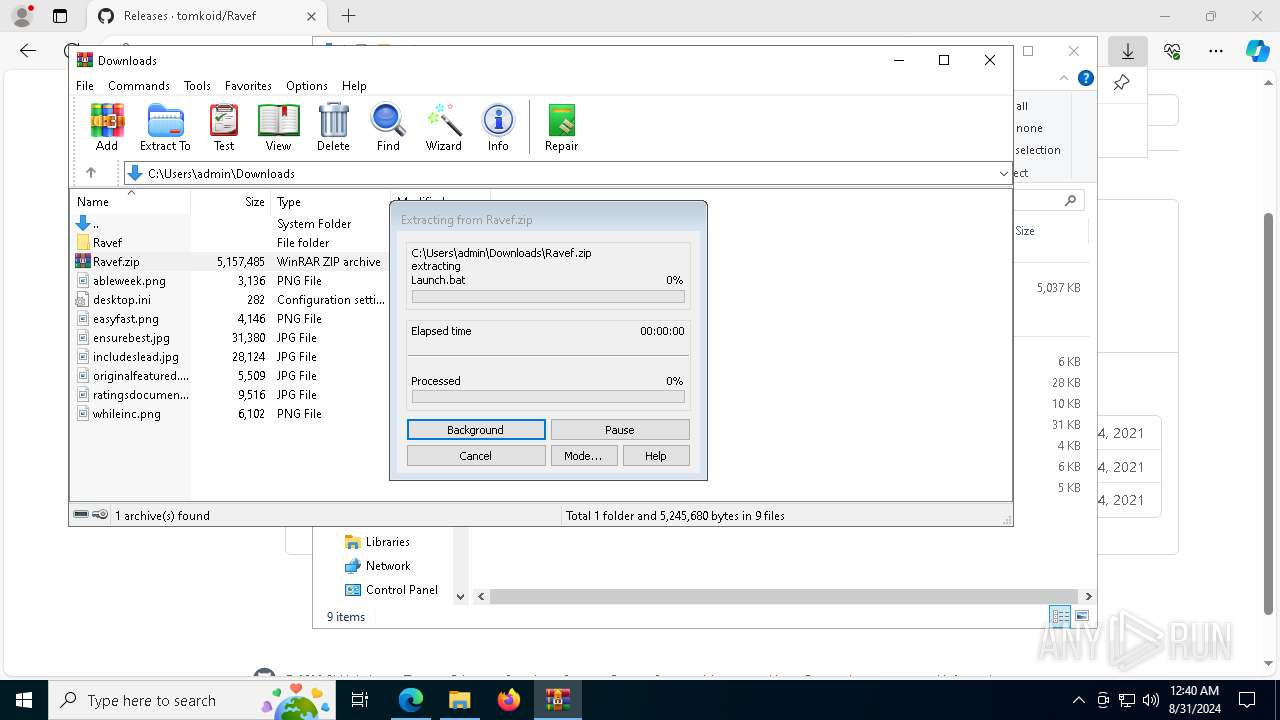
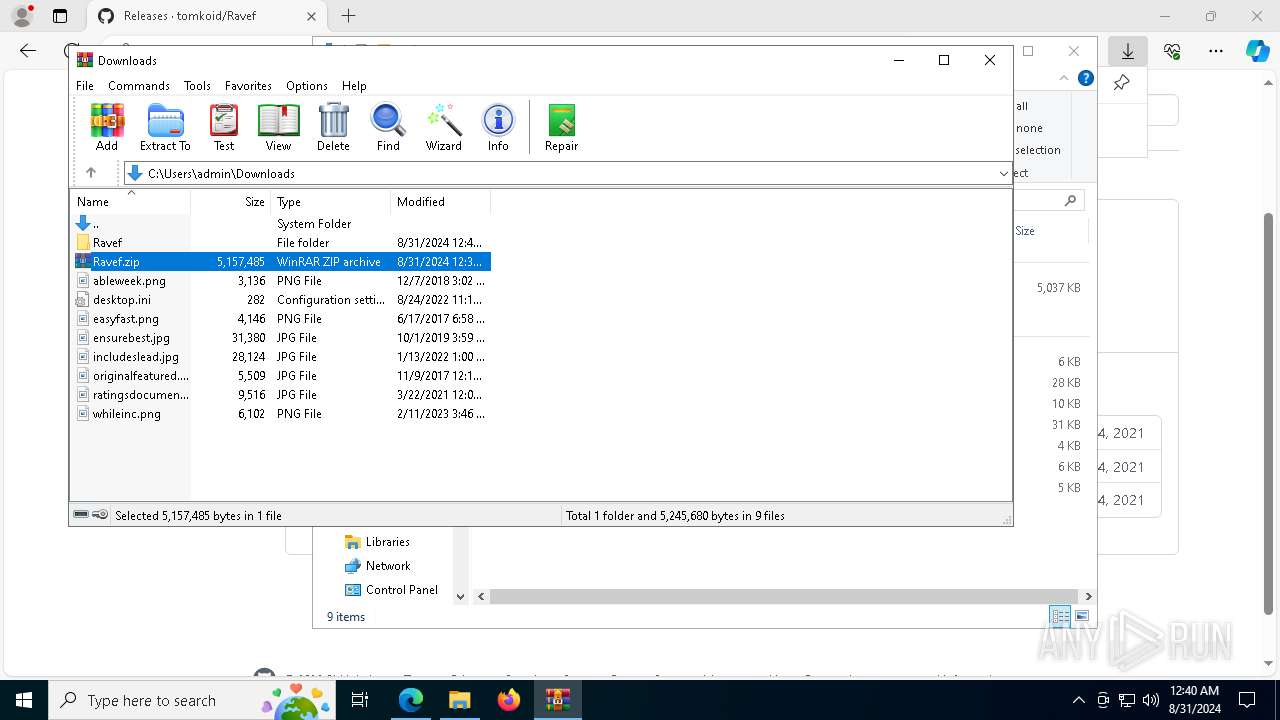
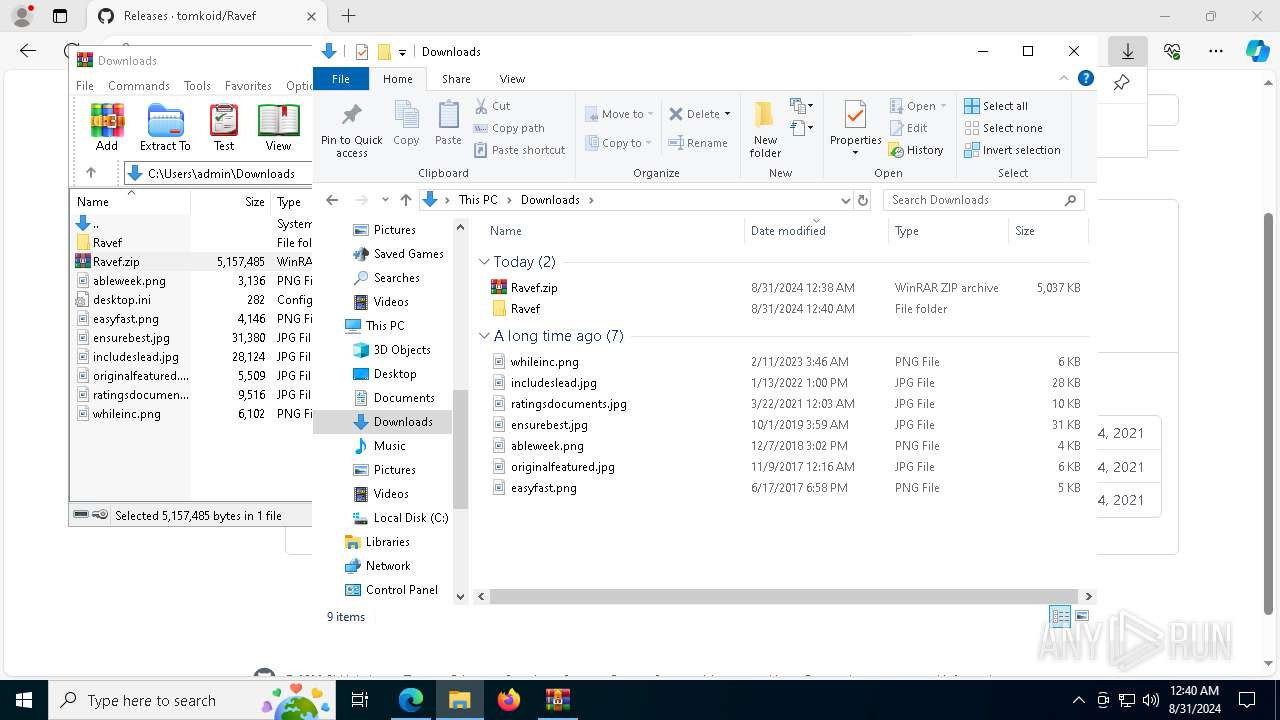
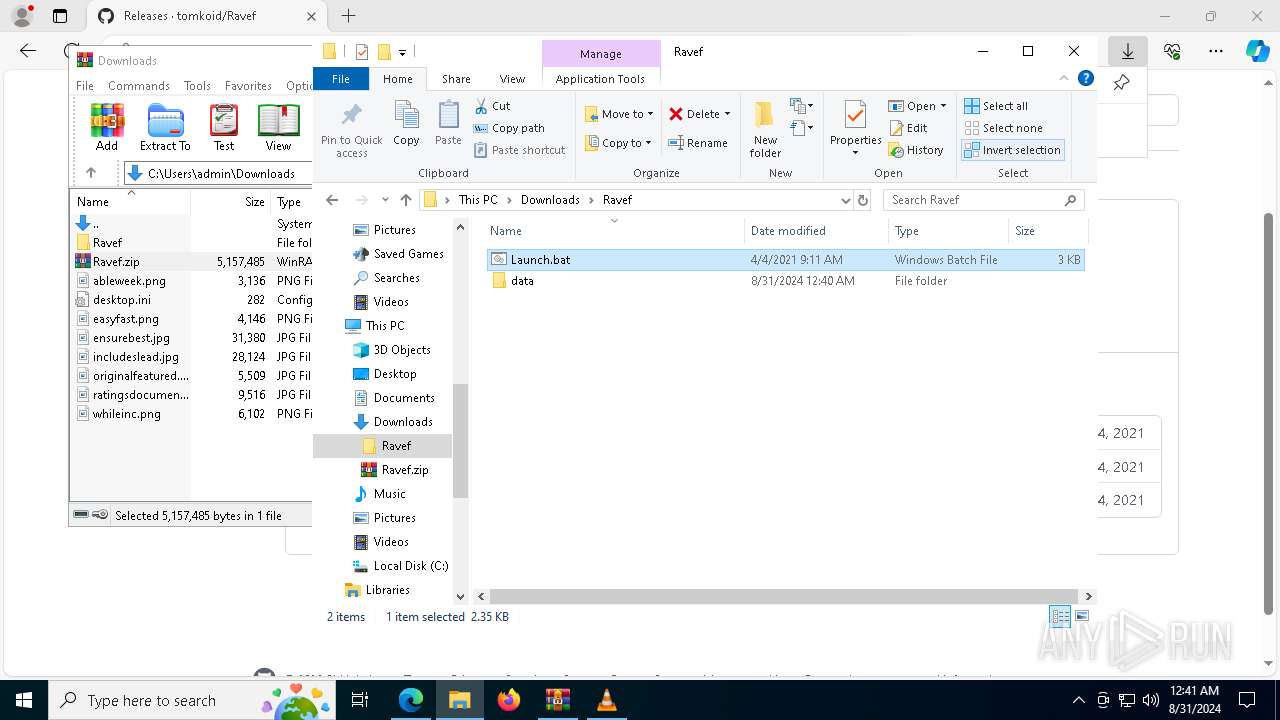
The process uses the downloaded file
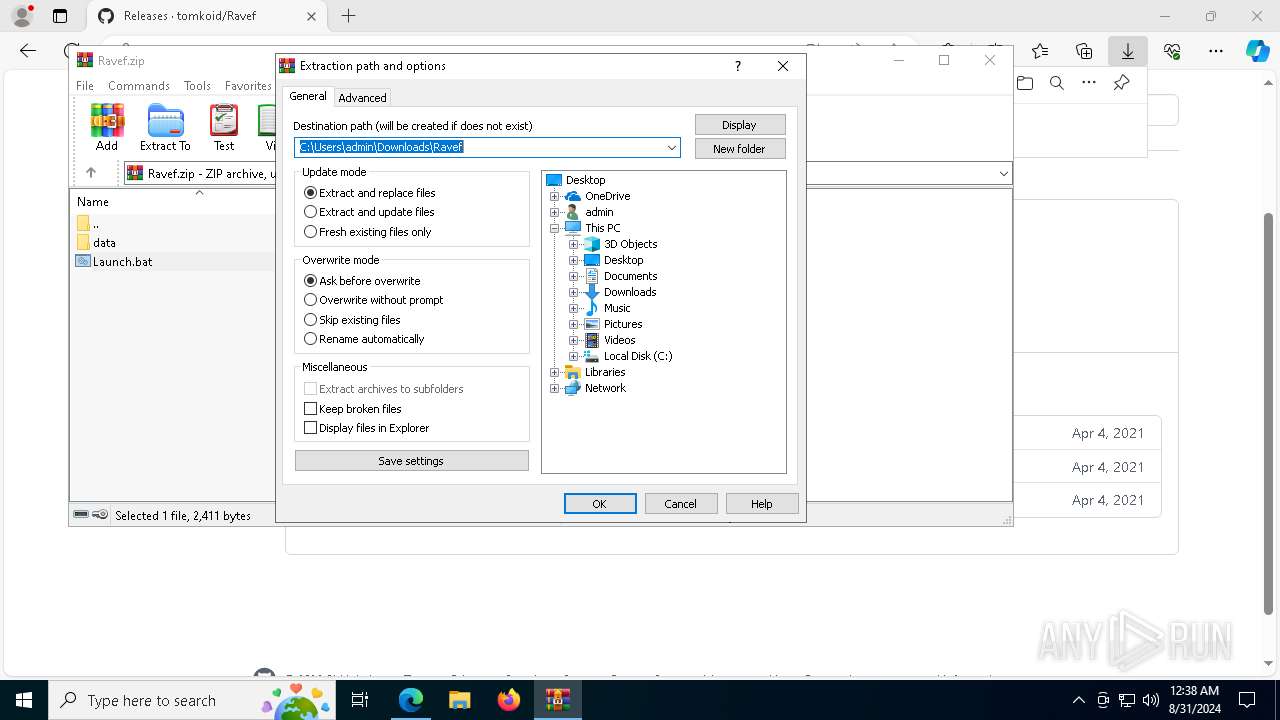
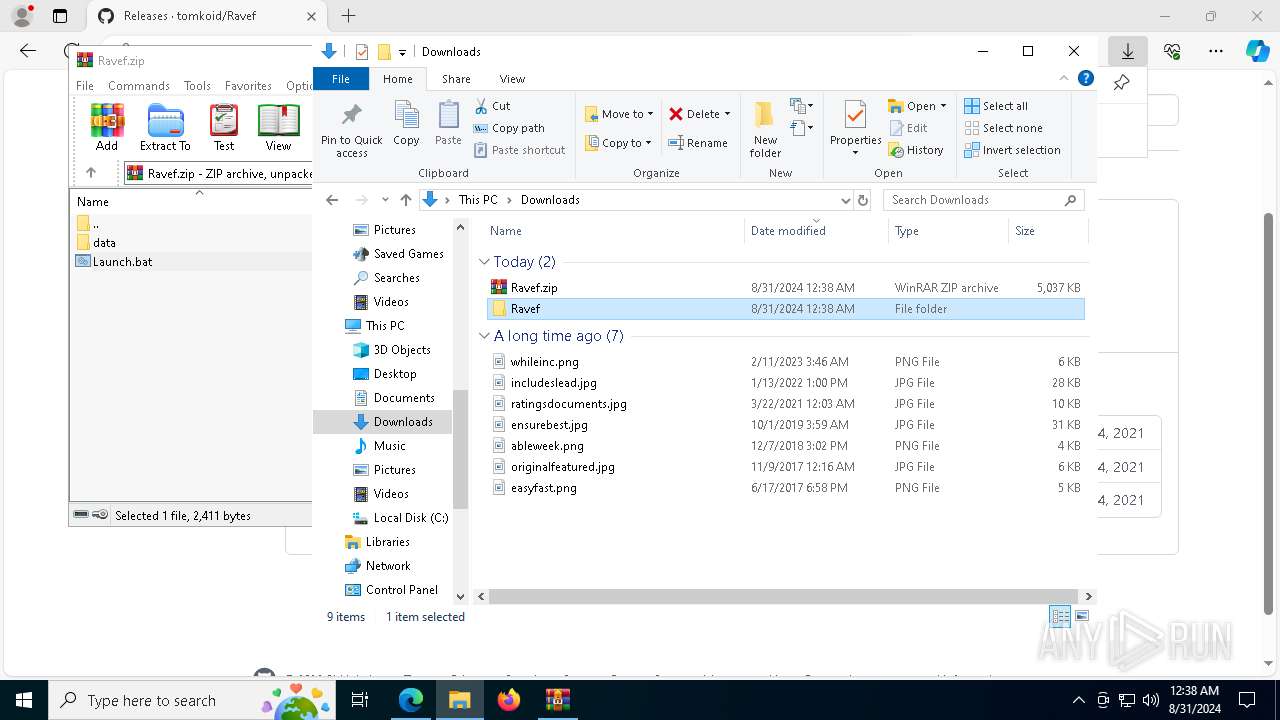
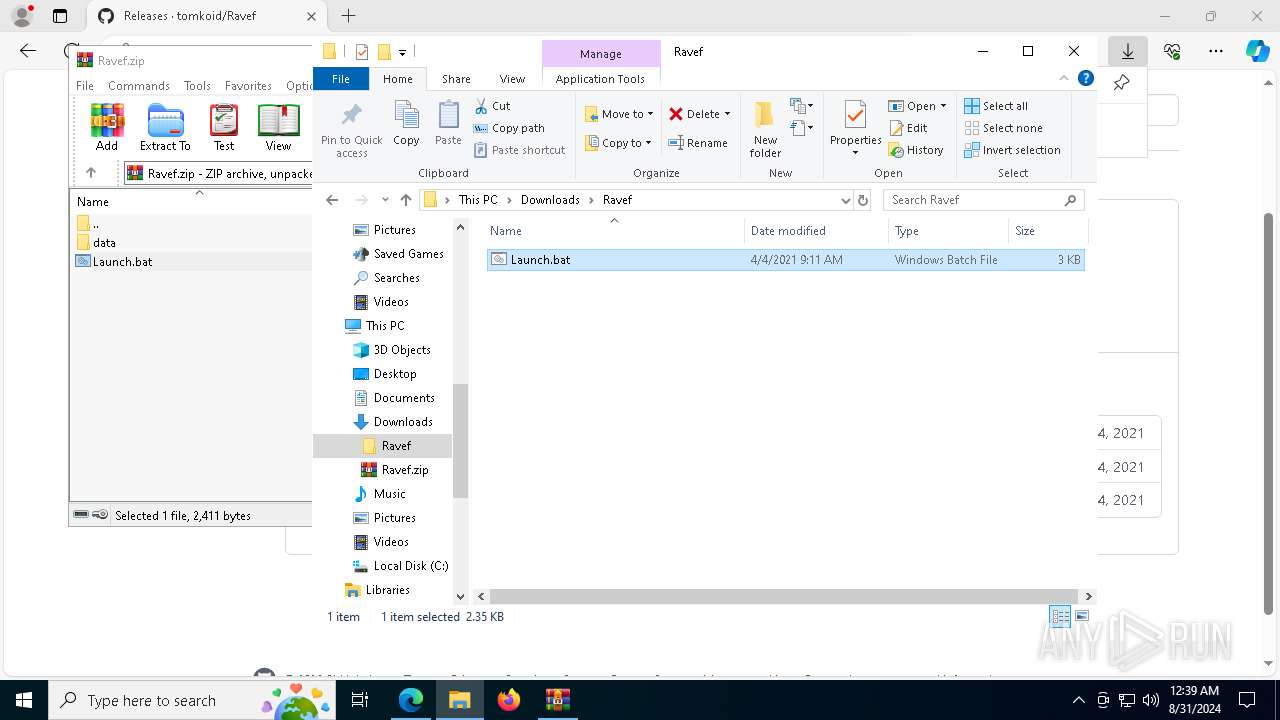
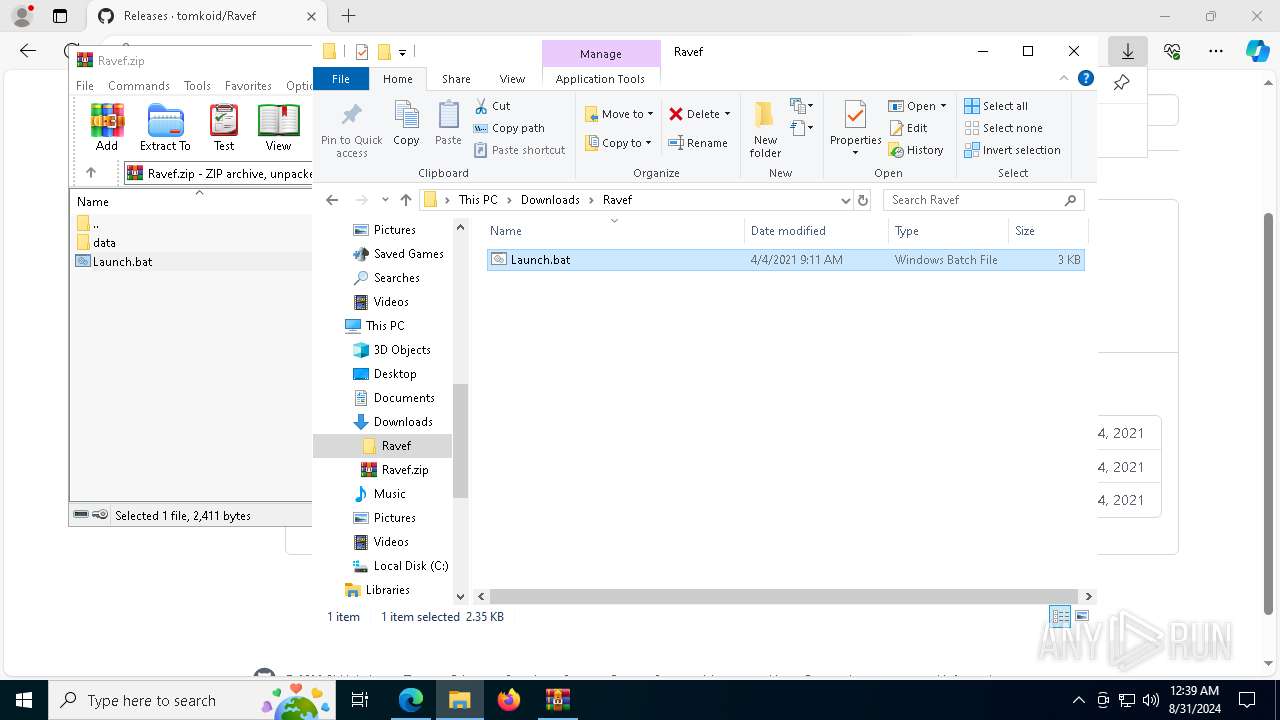
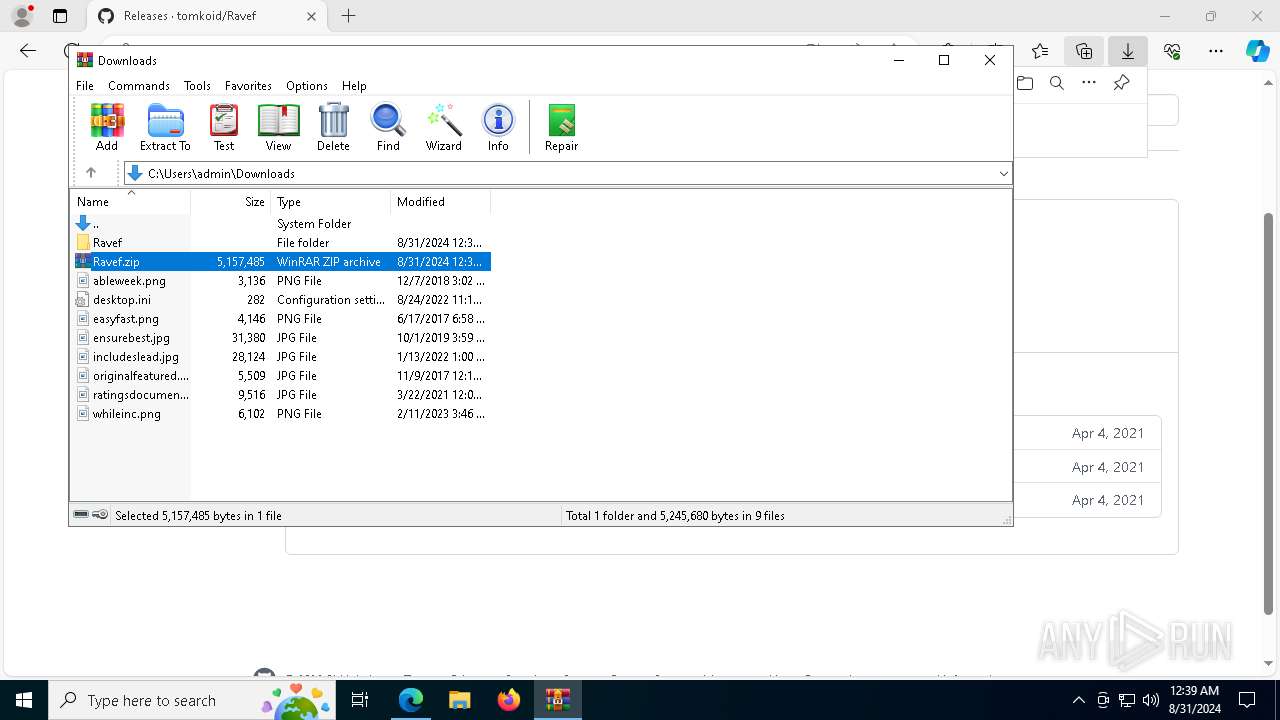
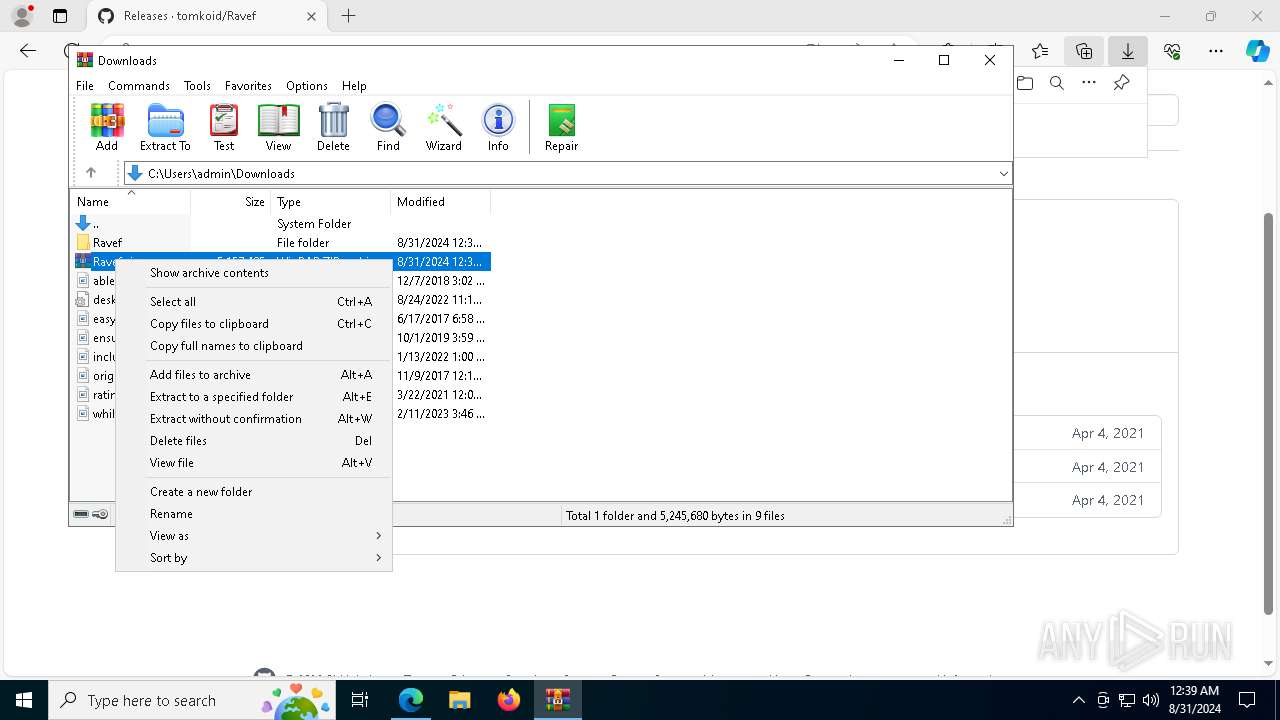
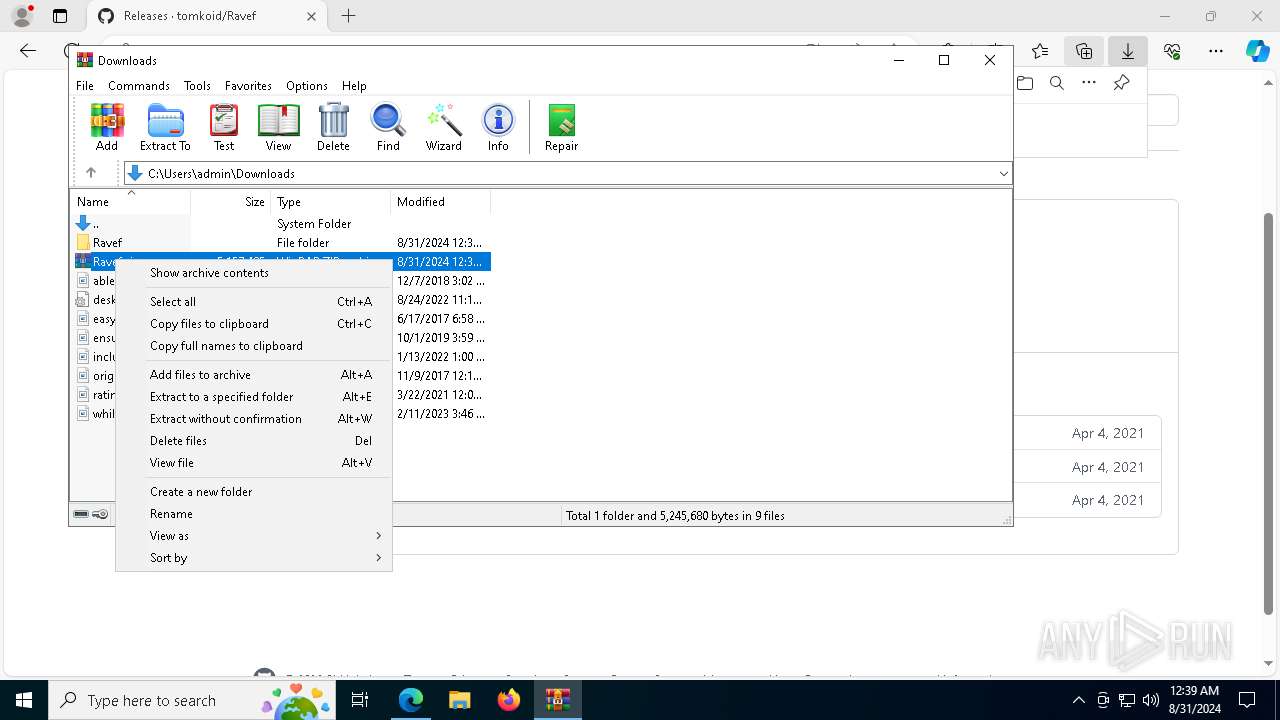
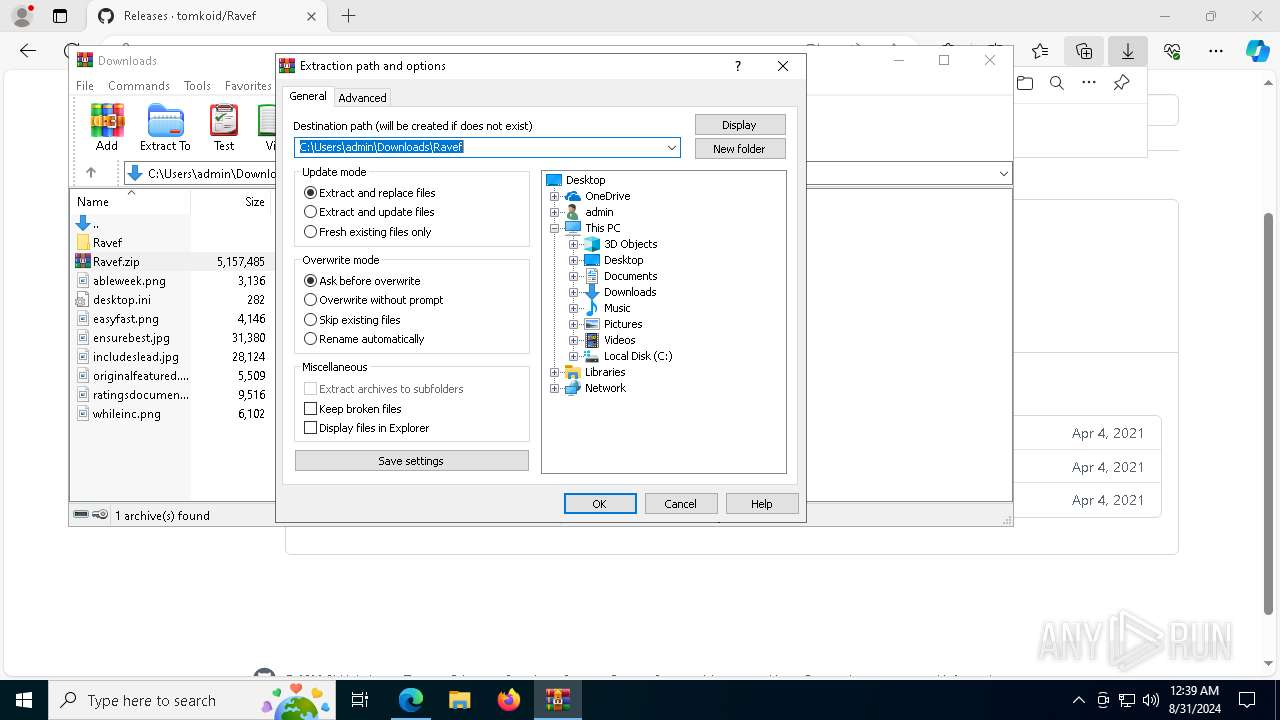
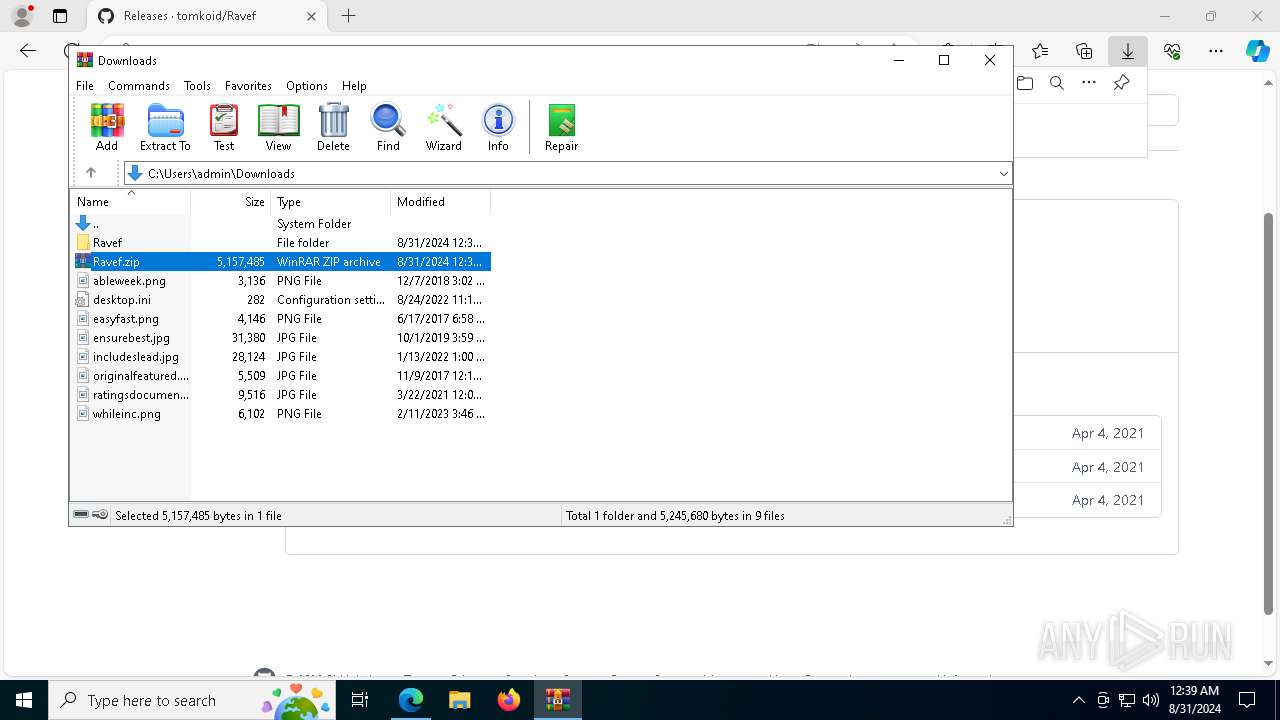
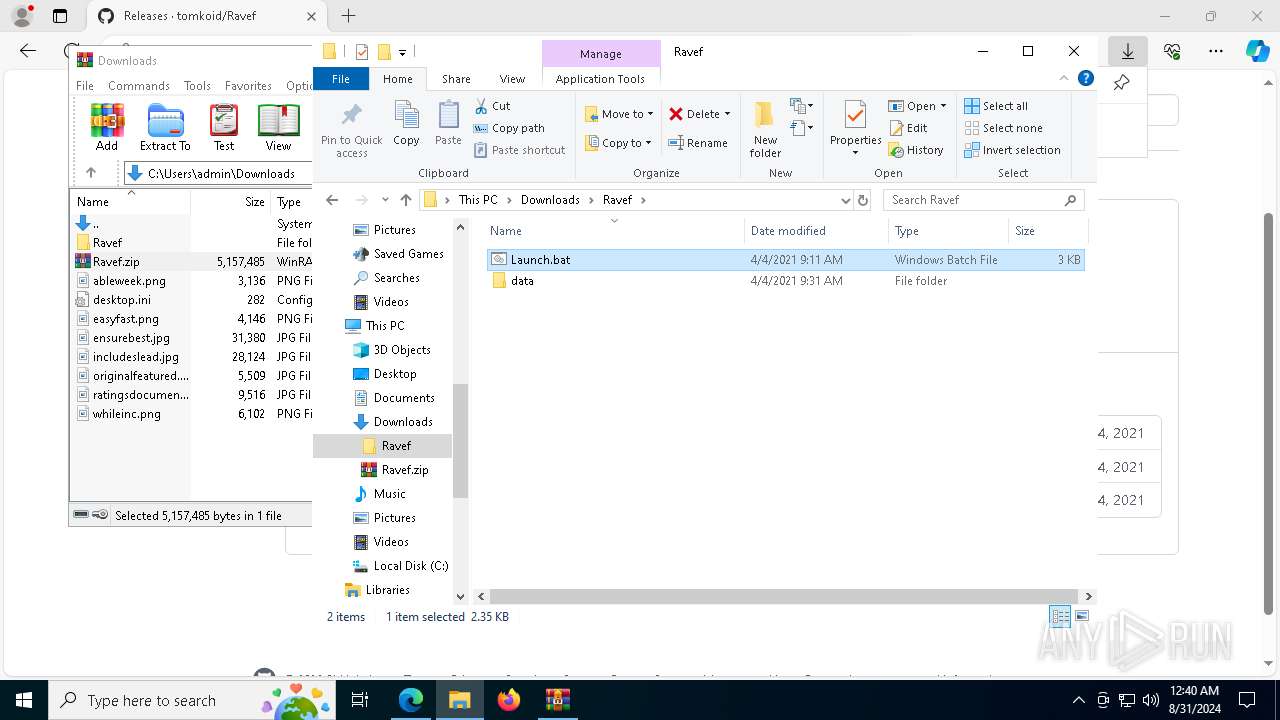
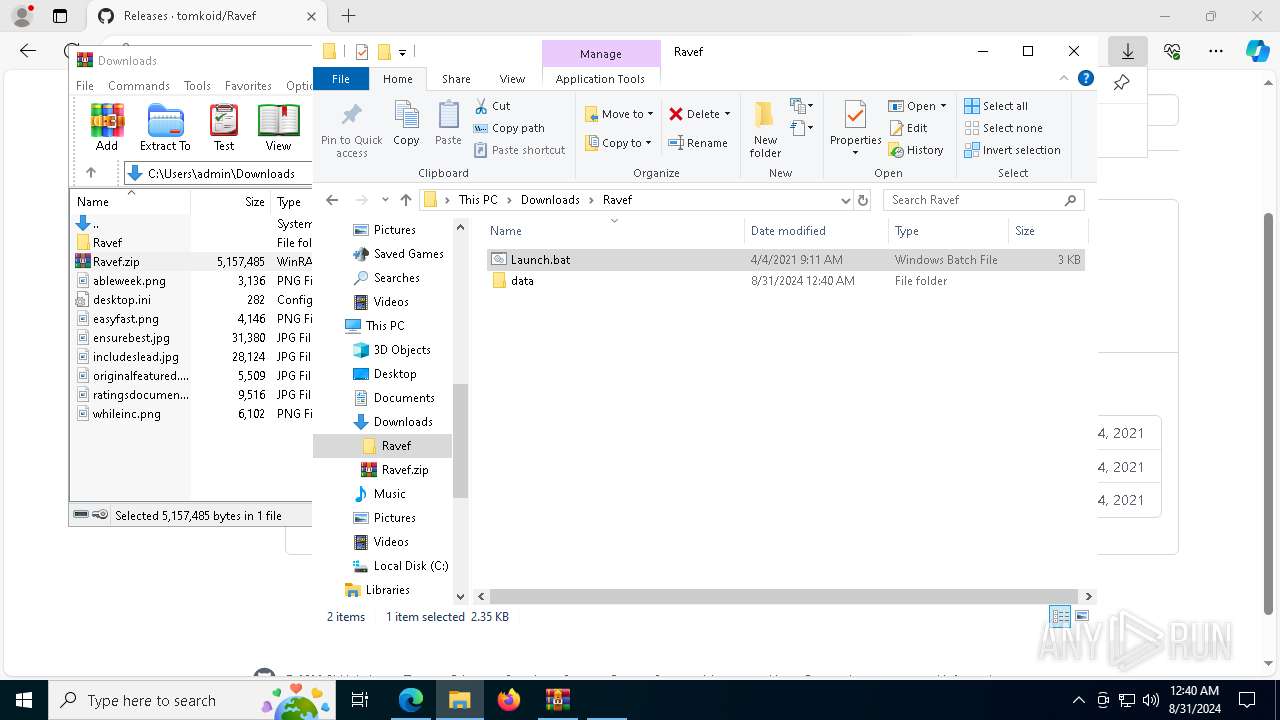
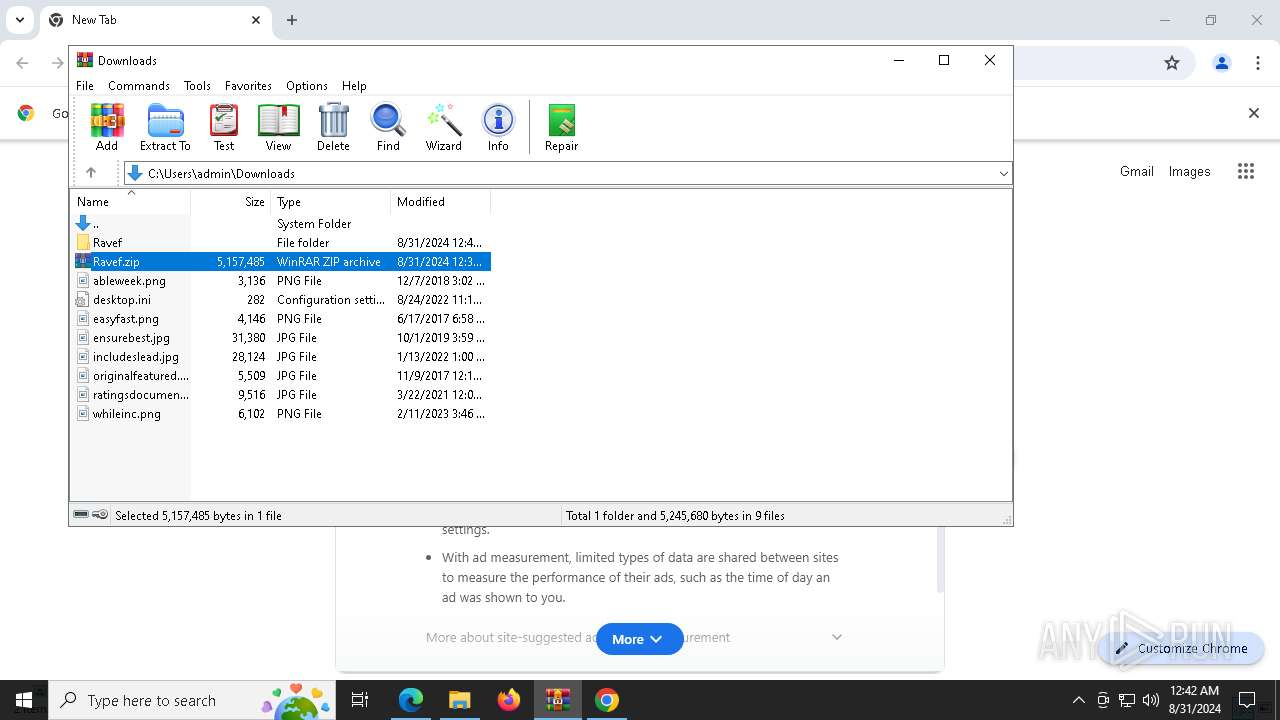
- WinRAR.exe (PID: 7740)
- msedge.exe (PID: 7672)
- msedge.exe (PID: 6988)
- cmd.exe (PID: 6108)
- cmd.exe (PID: 6212)
- wscript.exe (PID: 8156)
- cmd.exe (PID: 7868)
- chrome.exe (PID: 3144)
- chrome.exe (PID: 3784)
- cmd.exe (PID: 6056)
- wscript.exe (PID: 400)
- chrome.exe (PID: 6584)
- chrome.exe (PID: 6636)
- chrome.exe (PID: 1076)
- chrome.exe (PID: 2016)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 3896)
- chrome.exe (PID: 3568)
- chrome.exe (PID: 4128)
- chrome.exe (PID: 6492)
- chrome.exe (PID: 7020)
- cmd.exe (PID: 32)
- wscript.exe (PID: 7088)
Reads Environment values
- identity_helper.exe (PID: 7992)
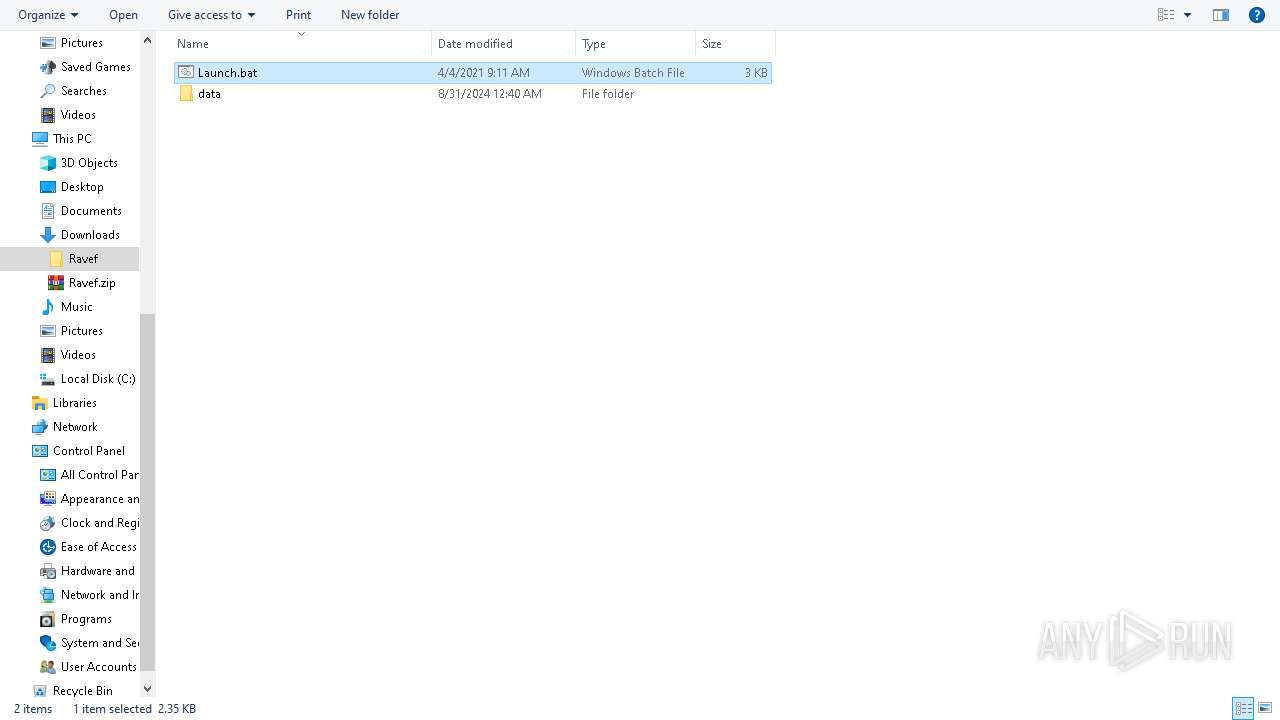
Manual execution by a user
- cmd.exe (PID: 7428)
- WinRAR.exe (PID: 2400)
- cmd.exe (PID: 7660)
- cmd.exe (PID: 892)
- cmd.exe (PID: 4672)
- cmd.exe (PID: 2368)
- cmd.exe (PID: 6512)
- cmd.exe (PID: 7288)
- cmd.exe (PID: 6952)
- cmd.exe (PID: 6692)
- cmd.exe (PID: 2384)
Reads the computer name
- identity_helper.exe (PID: 7992)
- vlc.exe (PID: 6580)
The process uses lua
- vlc.exe (PID: 6580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
324
Monitored processes
191
Malicious processes
8
Suspicious processes
5
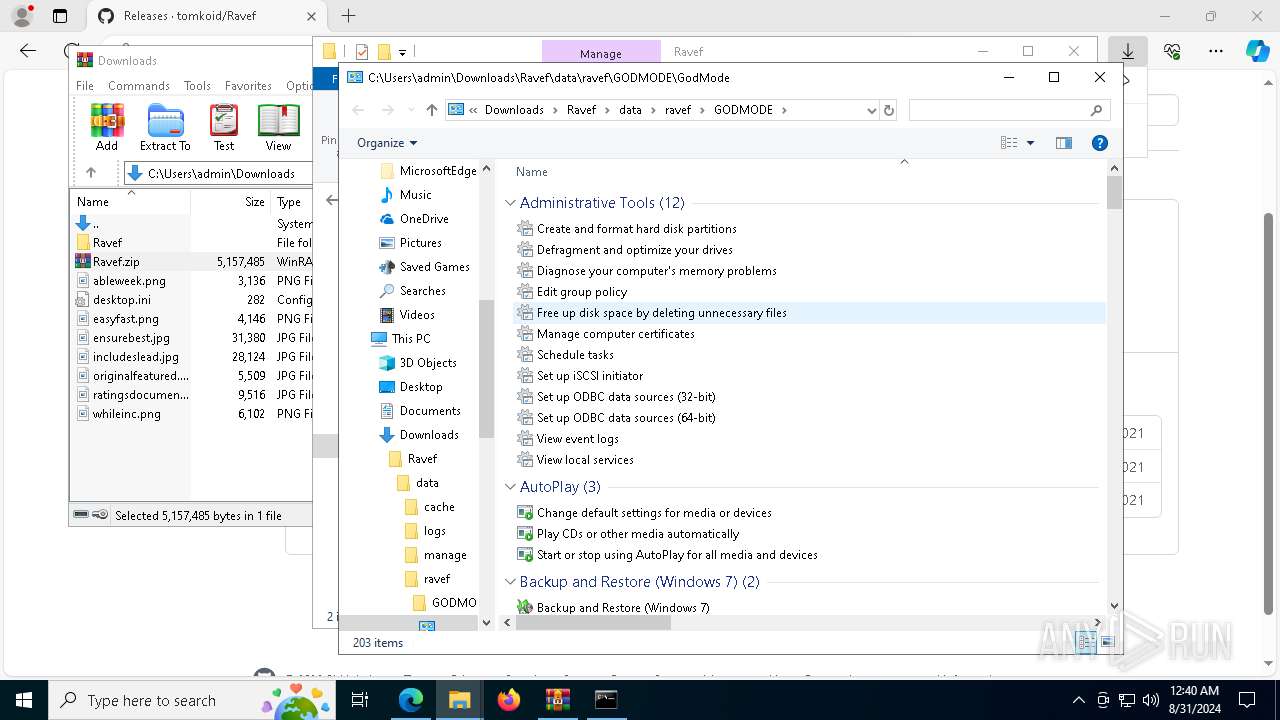
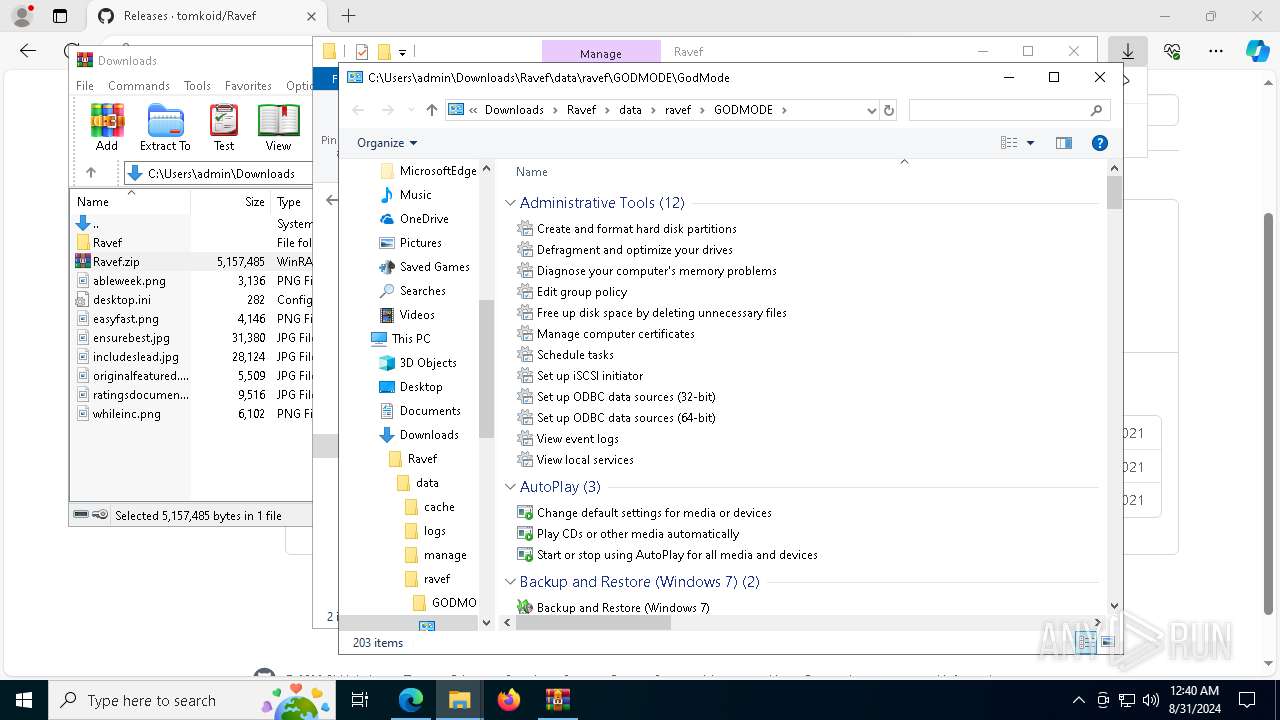
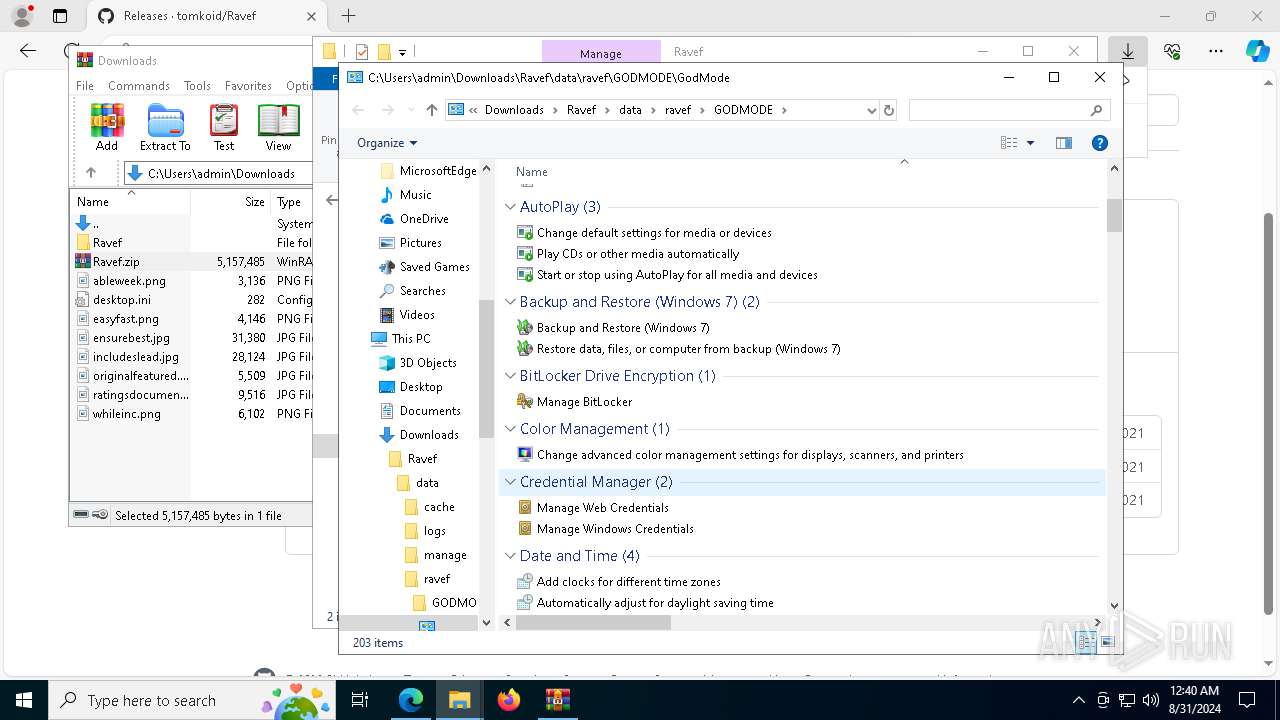
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | C:\WINDOWS\system32\cmd.exe /K win10update.bat | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 400 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\Downloads\Ravef\data\ravef\WIN10UPDATE\updater.vbs" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6112 --field-trial-handle=1936,i,16732024859371845485,15834094131036692252,262144 --variations-seed-version=20240830-130057.920000 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 892 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Downloads\Ravef\Launch.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1020 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1060 | timeout /t 5 /nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4548 --field-trial-handle=1936,i,16732024859371845485,15834094131036692252,262144 --variations-seed-version=20240830-130057.920000 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1064 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=1520 --field-trial-handle=2328,i,12781487836511631308,11540971710444619486,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5888 --field-trial-handle=1936,i,16732024859371845485,15834094131036692252,262144 --variations-seed-version=20240830-130057.920000 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5928 --field-trial-handle=1936,i,16732024859371845485,15834094131036692252,262144 --variations-seed-version=20240830-130057.920000 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
75 203
Read events
74 793
Write events
403
Delete events
7
Modification events
| (PID) Process: | (6988) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6988) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6988) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6988) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6988) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6988) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6988) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6988) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (6988) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6988) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
4
Suspicious files
529
Text files
209
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF12ab1d.TMP | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF12ab1d.TMP | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF12ab1d.TMP | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF12ab2c.TMP | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF12aba9.TMP | — | |
MD5:— | SHA256:— | |||
| 6988 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
104
DNS requests
133
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6916 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/05cb029e-7fd7-4659-8008-90788f8ebbc7?P1=1725572529&P2=404&P3=2&P4=S%2fKhvIKq5a5FIvXA3FDfA3BVV4rSRvRmQECBTnRuicZYwwnwYT4SV8ZupQf5XQ22R19Ttn65U6Hf9zvOUVhqBg%3d%3d | unknown | — | — | whitelisted |
2040 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6908 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6916 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/05cb029e-7fd7-4659-8008-90788f8ebbc7?P1=1725572529&P2=404&P3=2&P4=S%2fKhvIKq5a5FIvXA3FDfA3BVV4rSRvRmQECBTnRuicZYwwnwYT4SV8ZupQf5XQ22R19Ttn65U6Hf9zvOUVhqBg%3d%3d | unknown | — | — | whitelisted |
6916 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/05cb029e-7fd7-4659-8008-90788f8ebbc7?P1=1725572529&P2=404&P3=2&P4=S%2fKhvIKq5a5FIvXA3FDfA3BVV4rSRvRmQECBTnRuicZYwwnwYT4SV8ZupQf5XQ22R19Ttn65U6Hf9zvOUVhqBg%3d%3d | unknown | — | — | whitelisted |
6916 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/05cb029e-7fd7-4659-8008-90788f8ebbc7?P1=1725572529&P2=404&P3=2&P4=S%2fKhvIKq5a5FIvXA3FDfA3BVV4rSRvRmQECBTnRuicZYwwnwYT4SV8ZupQf5XQ22R19Ttn65U6Hf9zvOUVhqBg%3d%3d | unknown | — | — | whitelisted |
6916 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/05cb029e-7fd7-4659-8008-90788f8ebbc7?P1=1725572529&P2=404&P3=2&P4=S%2fKhvIKq5a5FIvXA3FDfA3BVV4rSRvRmQECBTnRuicZYwwnwYT4SV8ZupQf5XQ22R19Ttn65U6Hf9zvOUVhqBg%3d%3d | unknown | — | — | whitelisted |
6916 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1725572529&P2=404&P3=2&P4=eZ850ZdqCMqNHGXIJt6nTWRwOWyyZiQ5y%2bNiRzChVfmsV2l%2fgJy%2bz1t21%2bwPilf2aylg0PwijUdrqdrBY%2f%2fCJg%3d%3d | unknown | — | — | whitelisted |
6916 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1725572529&P2=404&P3=2&P4=eZ850ZdqCMqNHGXIJt6nTWRwOWyyZiQ5y%2bNiRzChVfmsV2l%2fgJy%2bz1t21%2bwPilf2aylg0PwijUdrqdrBY%2f%2fCJg%3d%3d | unknown | — | — | whitelisted |
6916 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1725572529&P2=404&P3=2&P4=eZ850ZdqCMqNHGXIJt6nTWRwOWyyZiQ5y%2bNiRzChVfmsV2l%2fgJy%2bz1t21%2bwPilf2aylg0PwijUdrqdrBY%2f%2fCJg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
6652 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6276 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1156 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6988 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1156 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | shared |
1156 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| shared |
edge.microsoft.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
Process | Message |
|---|---|
vlc.exe | main libvlc debug: VLC media player - 3.0.11 Vetinari
|
vlc.exe | main libvlc debug: Copyright © 1996-2020 the VideoLAN team
|
vlc.exe | main libvlc debug: revision 3.0.11-0-gdc0c5ced72
|
vlc.exe | main libvlc debug: configured with ../extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-dvdread' '--enable-shout' '--enable-goom' '--enable-caca' '--enable-qt' '--enable-skins2' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=x86_64-w64-mingw32' '--with-breakpad=https://win.crashes.videolan.org' 'host_alias=x86_64-w64-mingw32' 'PKG_CONFIG_LIBDIR=/home/jenkins/workspace/vlc-release/windows/vlc-release-win32-x64/contrib/x86_64-w64-mingw32/lib/pkgconfig'
|
vlc.exe | main libvlc debug: using multimedia timers as clock source
|
vlc.exe | main libvlc debug: min period: 1 ms, max period: 1000000 ms
|
vlc.exe | main libvlc debug: searching plug-in modules
|
vlc.exe | main libvlc debug: loading plugins cache file C:\Program Files\VideoLAN\VLC\plugins\plugins.dat
|
vlc.exe | main libvlc debug: recursively browsing `C:\Program Files\VideoLAN\VLC\plugins'
|
vlc.exe | main libvlc debug: plug-ins loaded: 494 modules
|