| File name: | overwolf-0-198-0-11.exe |
| Full analysis: | https://app.any.run/tasks/25e908d4-3fa7-472b-9acd-87e4c0e6ca26 |
| Verdict: | Malicious activity |
| Analysis date: | April 07, 2024, 23:03:00 |
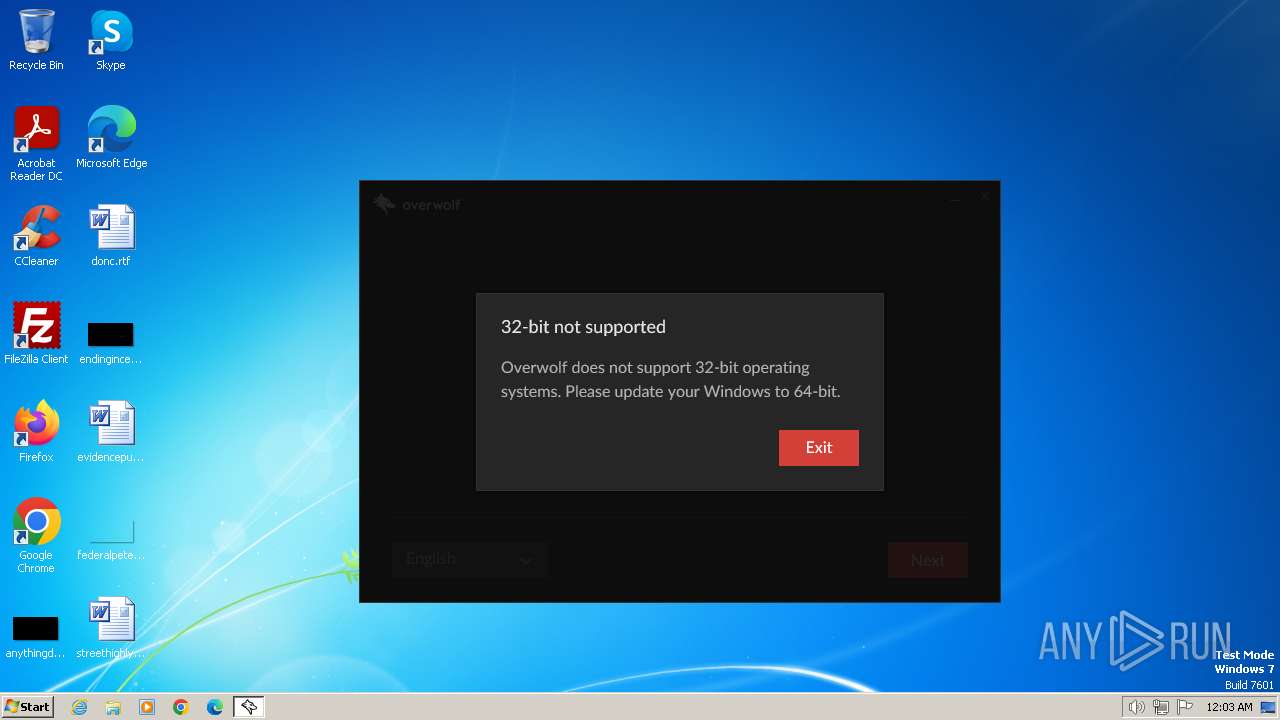
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 2825F1269E82A2C763D14A52FCF2CC69 |
| SHA1: | A6D70E6D07A31695EAFDDF755C93FD1824D47ADC |
| SHA256: | 9B6BE3D1A4462B4C435E4F9E7DC4CF97B61355D06D81ED0EA857611703DD6D0E |
| SSDEEP: | 49152:YFN3c7lNpx6Z9qJiEkzlWTUxuVZDwj+ha0gt721HdxG/4JH6ZgcFM58EERR88xvd:YFNMZQZ985kzYTVZDwjT0gtS19xG/QIb |
MALICIOUS
Drops the executable file immediately after the start
- overwolf-0-198-0-11.exe (PID: 1692)
- overwolf-0-198-0-11.exe (PID: 3180)
- OWinstaller.exe (PID: 1656)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- overwolf-0-198-0-11.exe (PID: 1692)
- overwolf-0-198-0-11.exe (PID: 3180)
Application launched itself
- overwolf-0-198-0-11.exe (PID: 1692)
The process creates files with name similar to system file names
- overwolf-0-198-0-11.exe (PID: 1692)
- overwolf-0-198-0-11.exe (PID: 3180)
Reads the Internet Settings
- overwolf-0-198-0-11.exe (PID: 3180)
- OWinstaller.exe (PID: 1656)
- dxdiag.exe (PID: 2564)
Reads security settings of Internet Explorer
- overwolf-0-198-0-11.exe (PID: 3180)
- OWinstaller.exe (PID: 1656)
Drops 7-zip archiver for unpacking
- overwolf-0-198-0-11.exe (PID: 3180)
Reads settings of System Certificates
- OWinstaller.exe (PID: 1656)
- dxdiag.exe (PID: 2564)
Adds/modifies Windows certificates
- OWinstaller.exe (PID: 1656)
Creates/Modifies COM task schedule object
- dxdiag.exe (PID: 2564)
Reads Microsoft Outlook installation path
- OWinstaller.exe (PID: 1656)
Checks Windows Trust Settings
- OWinstaller.exe (PID: 1656)
Reads Internet Explorer settings
- OWinstaller.exe (PID: 1656)
INFO
Checks supported languages
- overwolf-0-198-0-11.exe (PID: 1692)
- overwolf-0-198-0-11.exe (PID: 3180)
- OWinstaller.exe (PID: 1656)
Reads the computer name
- overwolf-0-198-0-11.exe (PID: 1692)
- overwolf-0-198-0-11.exe (PID: 3180)
- OWinstaller.exe (PID: 1656)
Checks proxy server information
- overwolf-0-198-0-11.exe (PID: 3180)
- OWinstaller.exe (PID: 1656)
Create files in a temporary directory
- overwolf-0-198-0-11.exe (PID: 1692)
- overwolf-0-198-0-11.exe (PID: 3180)
- dxdiag.exe (PID: 2564)
Reads the machine GUID from the registry
- overwolf-0-198-0-11.exe (PID: 3180)
- OWinstaller.exe (PID: 1656)
Creates files or folders in the user directory
- overwolf-0-198-0-11.exe (PID: 3180)
- OWinstaller.exe (PID: 1656)
- dxdiag.exe (PID: 2564)
Reads the software policy settings
- OWinstaller.exe (PID: 1656)
- dxdiag.exe (PID: 2564)
Reads product name
- OWinstaller.exe (PID: 1656)
Reads Environment values
- OWinstaller.exe (PID: 1656)
Reads security settings of Internet Explorer
- dxdiag.exe (PID: 2564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:12:25 05:01:44+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3229 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.195.0.0 |
| ProductVersionNumber: | 2.195.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Overwolf Ltd. |
| FileDescription: | Overwolf |
| FileVersion: | 2.195.0.0 |
| LegalCopyright: | Copyright (C) 2021 Overwolf Ltd. All Rights Reserved. |
| LegalTrademarks: | - |
| ProductName: | Overwolf |
| ProductVersion: | 2.195.0.0 |
Total processes
44
Monitored processes
4
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1656 | "C:\Users\admin\AppData\Local\Temp\nsi215F.tmp\OWinstaller.exe" Sel=0&Channel=web_dl_btn /UAC:14019C /NCRC -partnerCustomizationLevel 0 -exepath C:\Users\admin\AppData\Local\Temp\overwolf-0-198-0-11.exe | C:\Users\admin\AppData\Local\Temp\nsi215F.tmp\OWinstaller.exe | overwolf-0-198-0-11.exe | ||||||||||||
User: admin Company: Overwolf Integrity Level: HIGH Description: Overwolf Installer Version: 2.195.0.0 Modules
| |||||||||||||||
| 1692 | "C:\Users\admin\AppData\Local\Temp\overwolf-0-198-0-11.exe" | C:\Users\admin\AppData\Local\Temp\overwolf-0-198-0-11.exe | — | explorer.exe | |||||||||||
User: admin Company: Overwolf Ltd. Integrity Level: MEDIUM Description: Overwolf Version: 2.195.0.0 Modules
| |||||||||||||||
| 2564 | "C:\Windows\System32\DxDiag.exe" /tC:\Users\admin\AppData\Local\Overwolf\Temp\DxDiagOutput.txt | C:\Windows\System32\dxdiag.exe | OWinstaller.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft DirectX Diagnostic Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3180 | "C:\Users\admin\AppData\Local\Temp\overwolf-0-198-0-11.exe" /UAC:14019C /NCRC | C:\Users\admin\AppData\Local\Temp\overwolf-0-198-0-11.exe | overwolf-0-198-0-11.exe | ||||||||||||
User: admin Company: Overwolf Ltd. Integrity Level: HIGH Description: Overwolf Version: 2.195.0.0 Modules
| |||||||||||||||
Total events
27 690
Read events
27 406
Write events
248
Delete events
36
Modification events
| (PID) Process: | (3180) overwolf-0-198-0-11.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3180) overwolf-0-198-0-11.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (3180) overwolf-0-198-0-11.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
| (PID) Process: | (3180) overwolf-0-198-0-11.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoConfigURL |
Value: | |||
| (PID) Process: | (3180) overwolf-0-198-0-11.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoDetect |
Value: | |||
| (PID) Process: | (3180) overwolf-0-198-0-11.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005C010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3180) overwolf-0-198-0-11.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3180) overwolf-0-198-0-11.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3180) overwolf-0-198-0-11.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3180) overwolf-0-198-0-11.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
13
Suspicious files
13
Text files
78
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1692 | overwolf-0-198-0-11.exe | C:\Users\admin\AppData\Local\Temp\nsh2026.tmp\UserInfo.dll | executable | |
MD5:— | SHA256:— | |||
| 1692 | overwolf-0-198-0-11.exe | C:\Users\admin\AppData\Local\Temp\nsh2026.tmp\System.dll | executable | |
MD5:— | SHA256:— | |||
| 1692 | overwolf-0-198-0-11.exe | C:\Users\admin\AppData\Local\Temp\nsh2026.tmp\uac.dll | executable | |
MD5:— | SHA256:— | |||
| 1692 | overwolf-0-198-0-11.exe | C:\Users\admin\AppData\Local\Temp\nsh2026.tmp\nsProcess.dll | executable | |
MD5:— | SHA256:— | |||
| 3180 | overwolf-0-198-0-11.exe | C:\Users\admin\AppData\Local\Temp\nsi215F.tmp\UserInfo.dll | executable | |
MD5:— | SHA256:— | |||
| 3180 | overwolf-0-198-0-11.exe | C:\Users\admin\AppData\Local\Temp\nsi215F.tmp\System.dll | executable | |
MD5:— | SHA256:— | |||
| 3180 | overwolf-0-198-0-11.exe | C:\Users\admin\AppData\Local\Temp\nsi215F.tmp\uac.dll | executable | |
MD5:— | SHA256:— | |||
| 3180 | overwolf-0-198-0-11.exe | C:\Users\admin\AppData\Local\Temp\nsi215F.tmp\INetC.dll | executable | |
MD5:— | SHA256:— | |||
| 3180 | overwolf-0-198-0-11.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\Counter[1] | binary | |
MD5:— | SHA256:— | |||
| 3180 | overwolf-0-198-0-11.exe | C:\Users\admin\AppData\Local\Overwolf\OWInstall.log | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
21
DNS requests
10
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3180 | overwolf-0-198-0-11.exe | GET | 200 | 18.244.18.106:80 | http://analyticsnew.overwolf.com/analytics/Counter?Name=installer_uac_action&Value=1&Extra=%5b%7b%22Name%22%3a%22installer_version%22%2c%22Value%22%3a%222.195.0.0%22%7d%5d | unknown | — | — | unknown |
1656 | OWinstaller.exe | GET | 200 | 18.244.18.106:80 | http://analyticsnew.overwolf.com/analytics/Counter?CurrentVersion=2.195.0.0&PartnerID=0&Name=Manual_Funnel2_Installer_Launched&Value=1&UserName=&GameSessionId=&owver=0.195.0.8&MUID=04af837a-cacd-41f7-bfda-46c01c26ea76 | unknown | — | — | unknown |
1656 | OWinstaller.exe | GET | 200 | 18.244.18.106:80 | http://analyticsnew.overwolf.com/analytics/Counter?CurrentVersion=2.195.0.0&PartnerID=0&Name=Manual_Installer_Launched&Value=1&UserName=&GameSessionId=&owver=0.195.0.8&MUID=04af837a-cacd-41f7-bfda-46c01c26ea76 | unknown | — | — | unknown |
1656 | OWinstaller.exe | GET | 200 | 142.250.186.110:80 | http://www.google-analytics.com/__utm.gif?utmwv=4.7.2&utmn=30247403&utmhn=&utmcs=UTF-8&utmsr=-&utmsc=-&utmul=-&utmje=0&utmfl=-&utmdt=&utmhid=262242411&utmr=/&utmp=/&utmac=UA-18298709-8&utmcc=__utma%3D0.2102084912.1712530991.1712530991.1712530991.2%3B%2B__utmz%3D0.1712530991.1.1.utmcsr%3D(direct)%7Cutmccn%3D%7Cutmcmd%3D%3B&utme=5(Funnel2*Installer%20Launched*2.0.50727%20SP2%2C%203.0%20SP2%2C%203.5%20SP1%2C%204%20Client%2C%204%20Full%2C%204.0%20Client)()&gaq=1&utmt=event | unknown | — | — | unknown |
1656 | OWinstaller.exe | GET | 200 | 18.244.18.106:80 | http://analyticsnew.overwolf.com/analytics/Counter?CurrentVersion=2.195.0.0&PartnerID=0&Name=installer_webbrowser_init&Value=1&UserName=&GameSessionId=&Extra=%255b%257b%2522Name%2522%253a%2522ver%2522%252c%2522Value%2522%253a%252211.0.9600.19597%2522%257d%252c%257b%2522Name%2522%253a%2522OSBuild%2522%252c%2522Value%2522%253a%25226.1.7601.24546%2522%257d%255d&owver=0.195.0.8&MUID=04af837a-cacd-41f7-bfda-46c01c26ea76 | unknown | — | — | unknown |
1656 | OWinstaller.exe | GET | 200 | 142.250.186.110:80 | http://www.google-analytics.com/__utm.gif?utmwv=4.7.2&utmn=155621008&utmhn=&utmcs=UTF-8&utmsr=-&utmsc=-&utmul=-&utmje=0&utmfl=-&utmdt=&utmhid=180908536&utmr=/&utmp=/&utmac=UA-80584726-1&utmcc=__utma%3D0.2102084912.1712530991.1712530991.1712530991.2%3B%2B__utmz%3D0.1712530991.1.1.utmcsr%3D(direct)%7Cutmccn%3D%7Cutmcmd%3D%3B&utme=5(Funnel2*Installer%20Launched*2.0.50727%20SP2%2C%203.0%20SP2%2C%203.5%20SP1%2C%204%20Client%2C%204%20Full%2C%204.0%20Client)()&gaq=1&utmt=event | unknown | — | — | unknown |
1656 | OWinstaller.exe | GET | 200 | 18.244.18.106:80 | http://analyticsnew.overwolf.com/analytics/Counter?CurrentVersion=2.195.0.0&PartnerID=0&Name=installer_error_message&Value=22012&UserName=&GameSessionId=&Extra=%255b%257b%2522Name%2522%253a%2522state%2522%252c%2522Value%2522%253anull%257d%252c%257b%2522Name%2522%253a%2522OSBuild%2522%252c%2522Value%2522%253a%25226.1.7601.24546%2522%257d%255d&owver=0.195.0.8&MUID=04af837a-cacd-41f7-bfda-46c01c26ea76 | unknown | — | — | unknown |
1656 | OWinstaller.exe | GET | 304 | 23.53.40.49:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3ab299a1b8d7efac | unknown | — | — | unknown |
1656 | OWinstaller.exe | GET | 304 | 23.53.40.49:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1e64360b57564b50 | unknown | — | — | unknown |
1656 | OWinstaller.exe | GET | 304 | 23.53.40.49:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a61769e2cb9c77d0 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3180 | overwolf-0-198-0-11.exe | 18.244.18.106:80 | analyticsnew.overwolf.com | — | US | unknown |
1656 | OWinstaller.exe | 18.244.18.106:80 | analyticsnew.overwolf.com | — | US | unknown |
1656 | OWinstaller.exe | 142.250.186.110:80 | www.google-analytics.com | GOOGLE | US | whitelisted |
1656 | OWinstaller.exe | 18.245.86.78:443 | content.overwolf.com | — | US | unknown |
1656 | OWinstaller.exe | 23.53.40.49:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1656 | OWinstaller.exe | 142.250.186.170:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
1656 | OWinstaller.exe | 108.138.2.107:80 | o.ss2.us | AMAZON-02 | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
analyticsnew.overwolf.com |
| unknown |
www.google-analytics.com |
| whitelisted |
content.overwolf.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.rootca3.amazontrust.com |
| unknown |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3180 | overwolf-0-198-0-11.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
2 ETPRO signatures available at the full report