| File name: | calc.exe |
| Full analysis: | https://app.any.run/tasks/435e98fe-a086-4d6c-a7eb-284e607b2b6e |
| Verdict: | Malicious activity |
| Analysis date: | October 01, 2024, 23:30:41 |
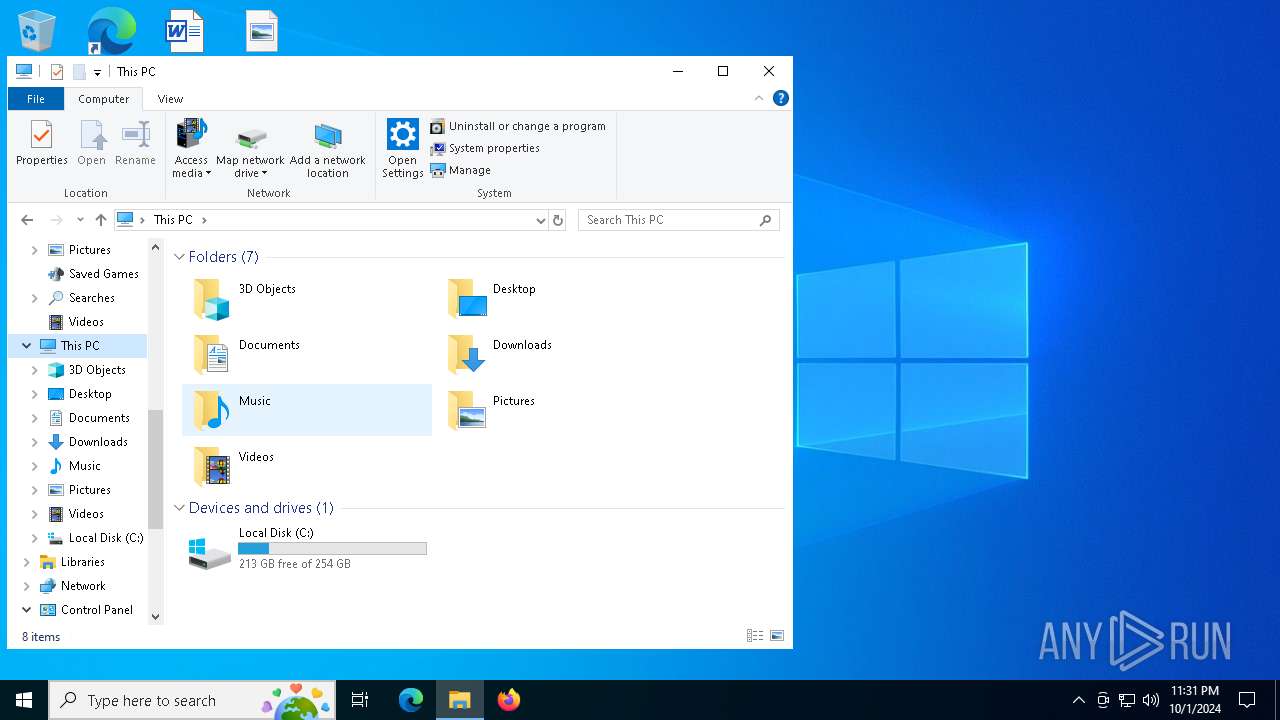
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 2F9FDAD776D8626F2CE8625211831E91 |
| SHA1: | 21D8413EB0D60B36FC249F8025C277B557FEFDE3 |
| SHA256: | 9B66A8EA0F1C64965B06E7A45AFBE56F2D4E6D5EF65F32446DEFCCBEBE730813 |
| SSDEEP: | 6144:BtzlwDwYgI9XLRlp7QsMd4yxrSGbs3/d0kJHQZgVu6IesIns6fN:lwcLqXLxkh4yxy/d0EHQuVu6IeLscN |
MALICIOUS
Starts NET.EXE to view/change users localgroup
- wscript.exe (PID: 1932)
- wscript.exe (PID: 6704)
- net.exe (PID: 5276)
- net.exe (PID: 1972)
- wscript.exe (PID: 796)
- net.exe (PID: 6208)
- wscript.exe (PID: 3836)
- wscript.exe (PID: 4792)
- net.exe (PID: 4644)
- wscript.exe (PID: 7132)
- net.exe (PID: 420)
- wscript.exe (PID: 4236)
- net.exe (PID: 3712)
- net.exe (PID: 1116)
Starts NET.EXE to view/add/change user profiles
- wscript.exe (PID: 1932)
- net.exe (PID: 2460)
- wscript.exe (PID: 6704)
- wscript.exe (PID: 796)
- net.exe (PID: 2628)
- net.exe (PID: 3860)
- wscript.exe (PID: 3836)
- wscript.exe (PID: 4792)
- net.exe (PID: 884)
- wscript.exe (PID: 4236)
- net.exe (PID: 892)
- net.exe (PID: 2708)
- net.exe (PID: 5656)
- wscript.exe (PID: 7132)
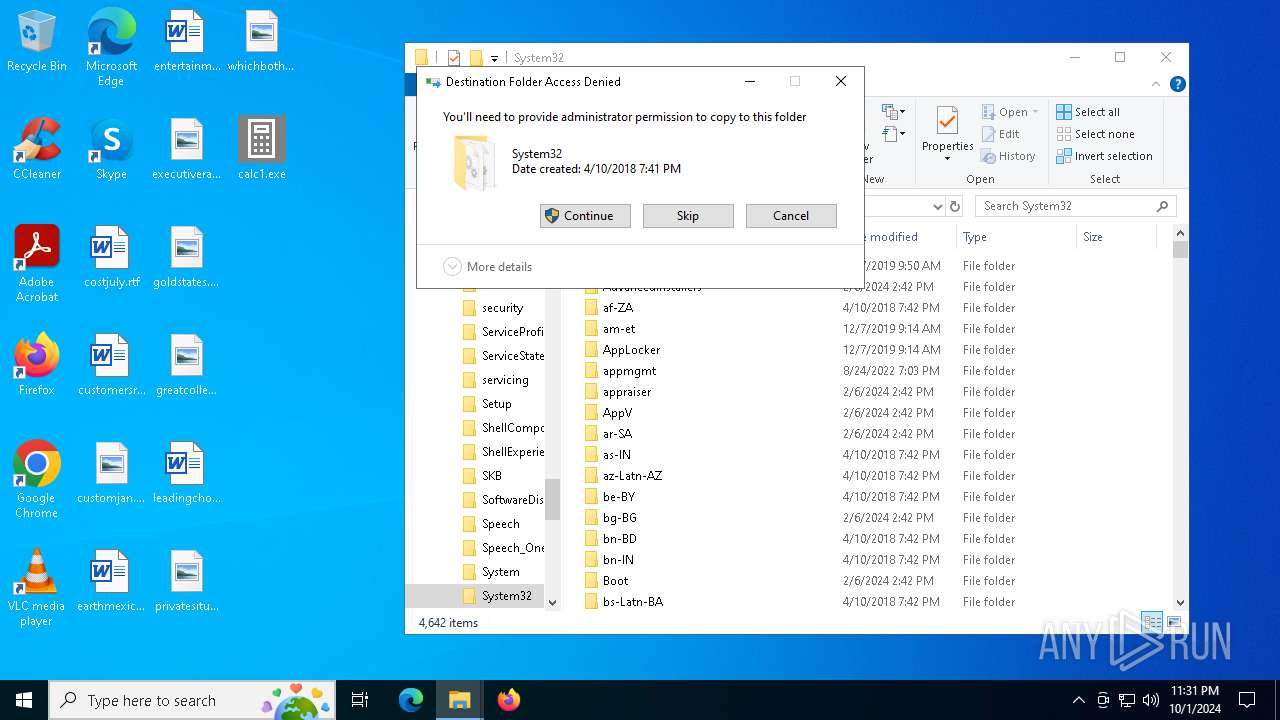
SUSPICIOUS
Executable content was dropped or overwritten
- dllhost.exe (PID: 3032)
INFO
The process uses AutoIt
- calc.exe (PID: 1640)
Checks supported languages
- calc.exe (PID: 1640)
Reads the computer name
- calc.exe (PID: 1640)
UPX packer has been detected
- calc.exe (PID: 1640)
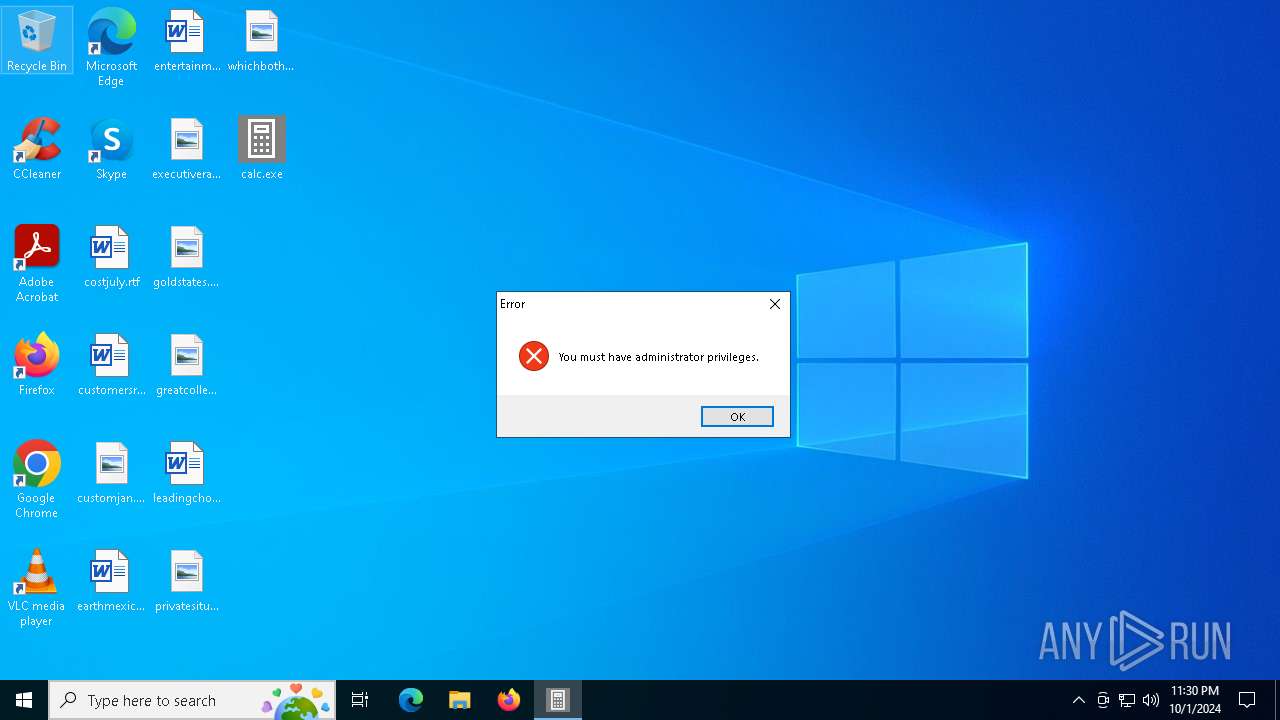
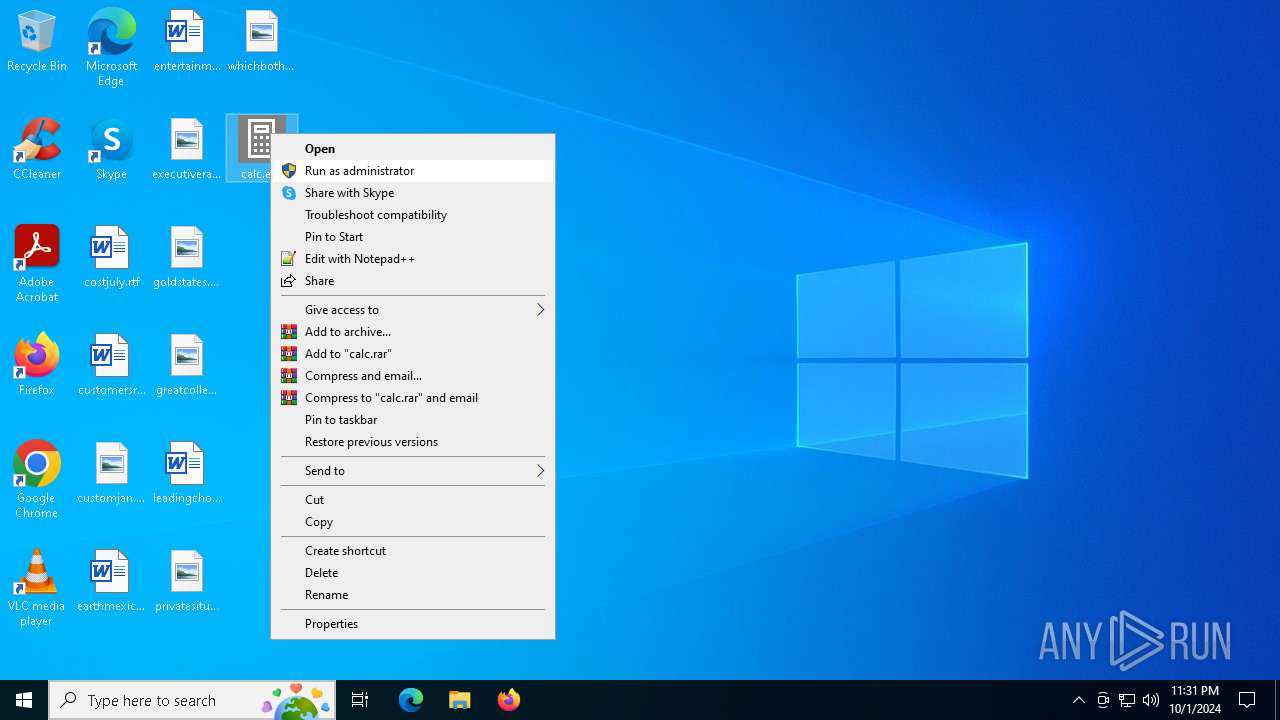
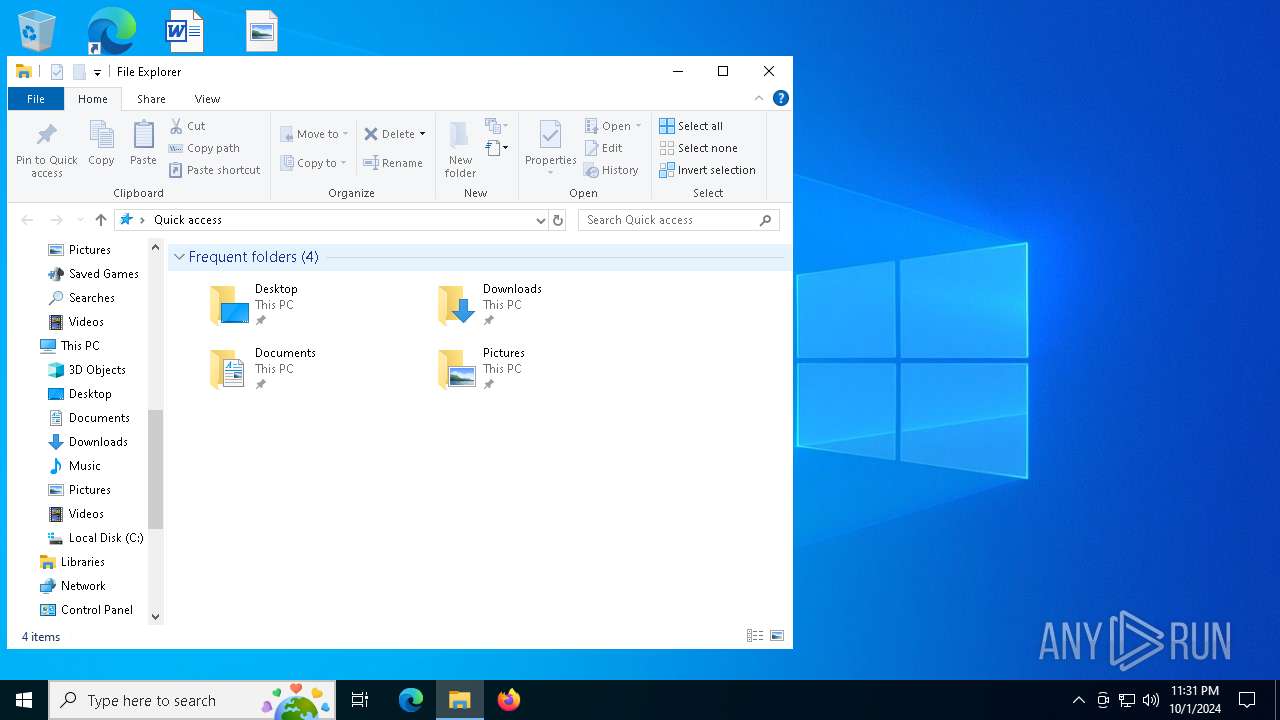
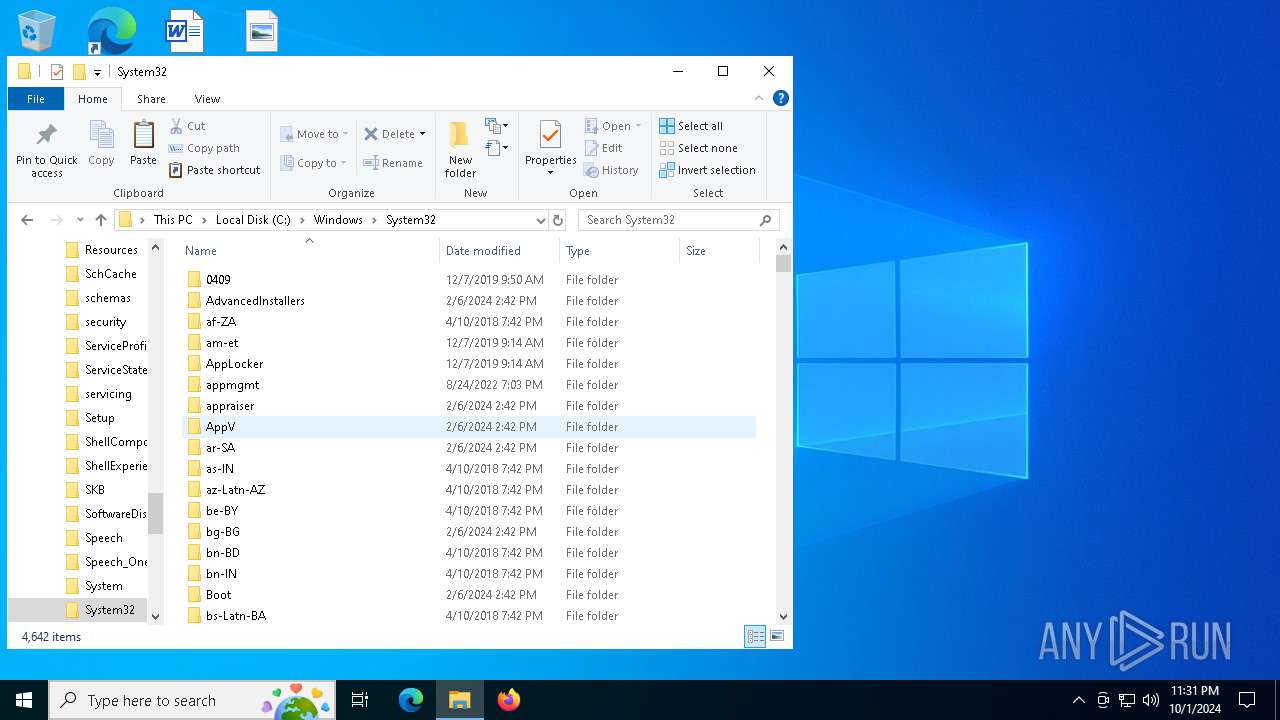
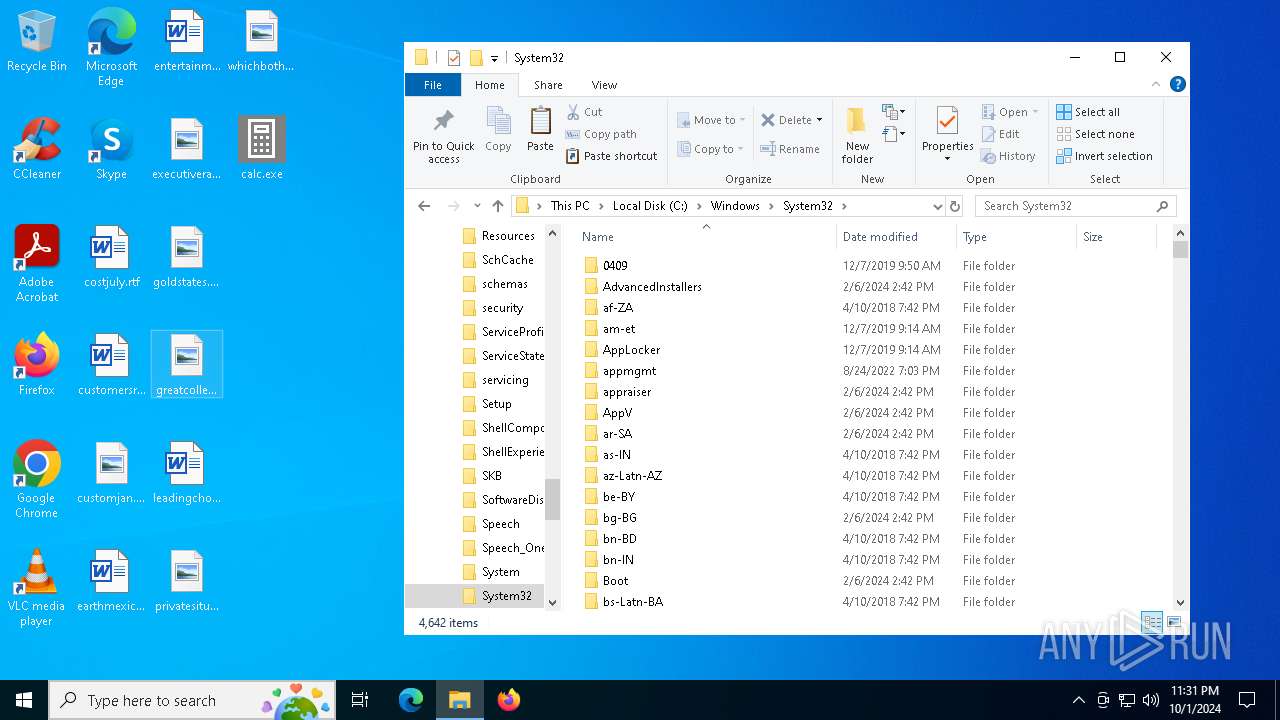
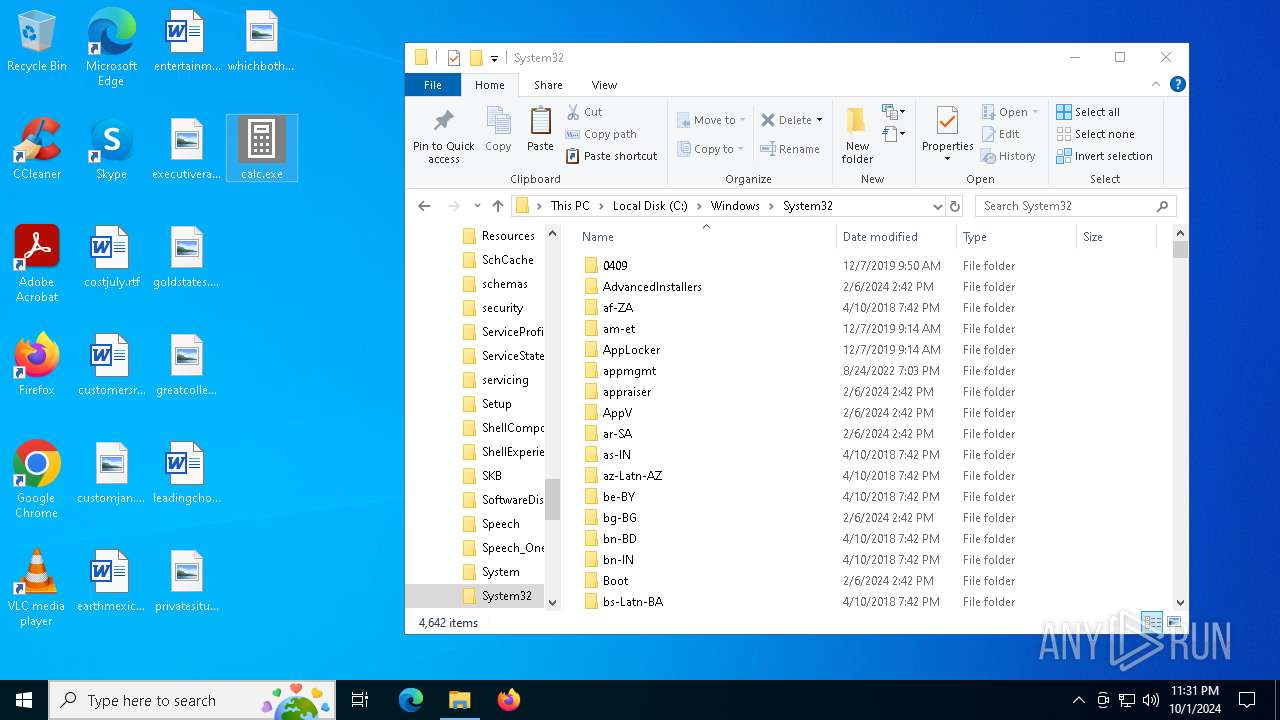
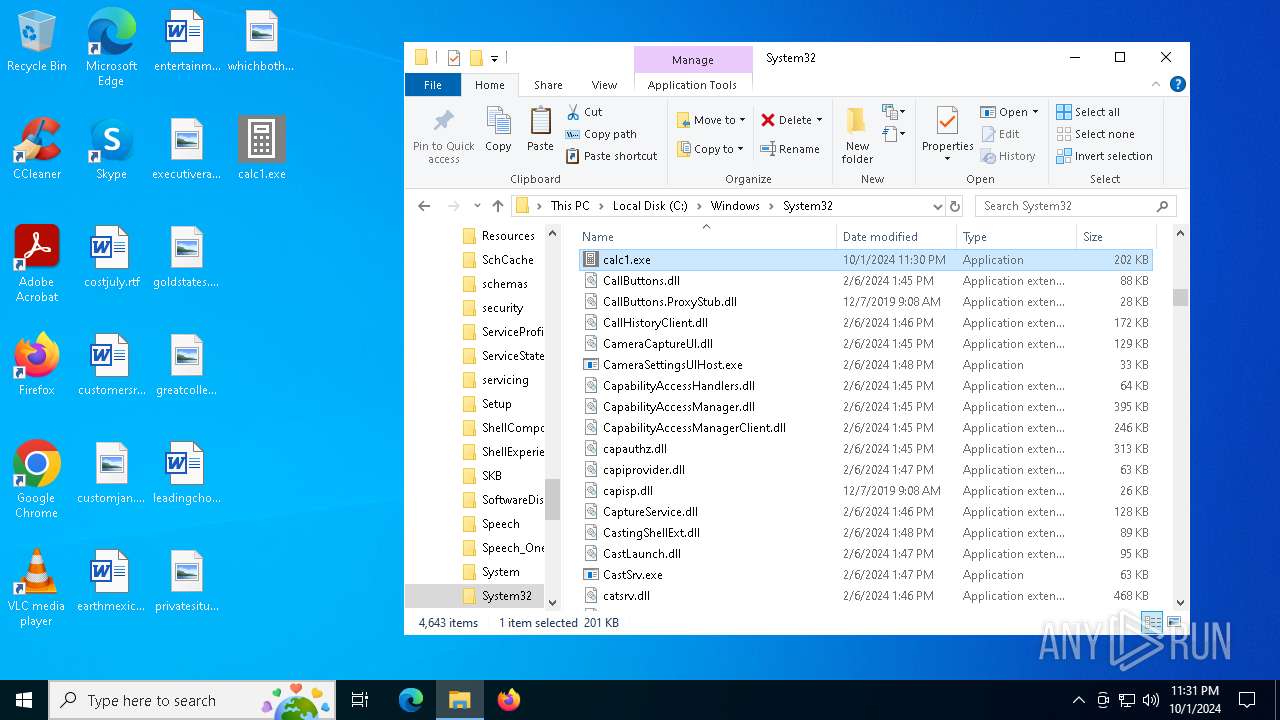
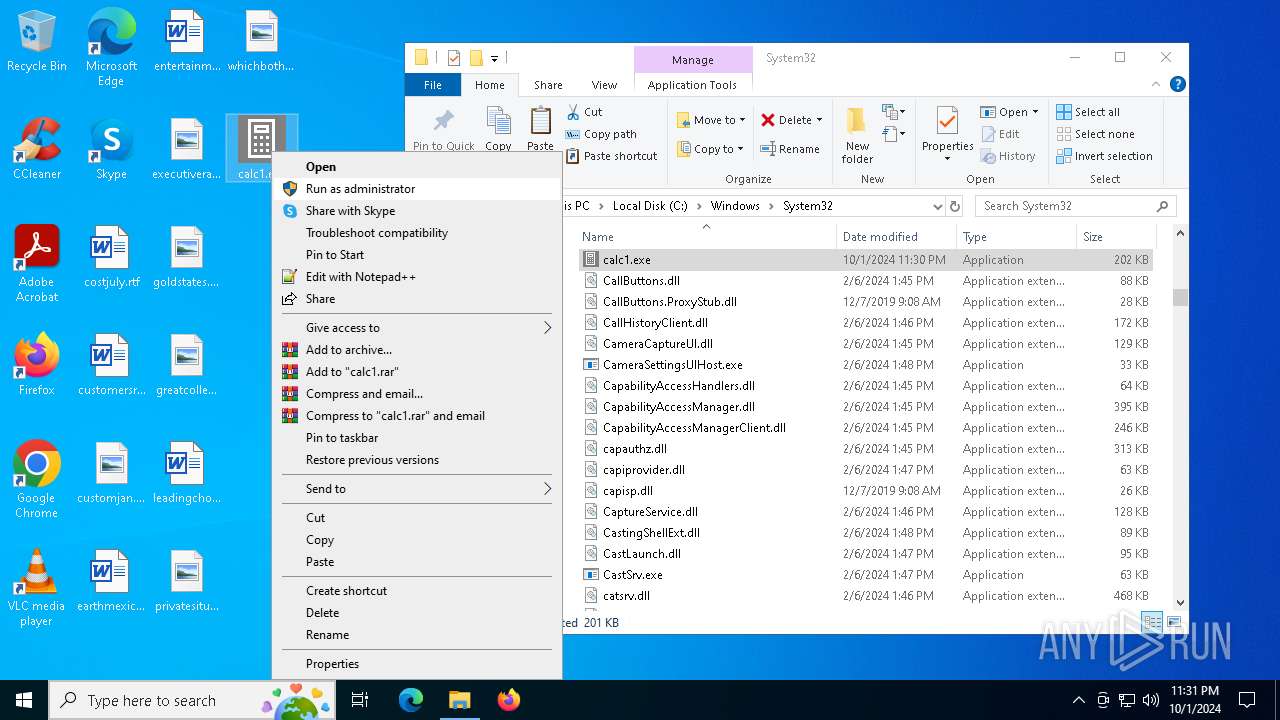
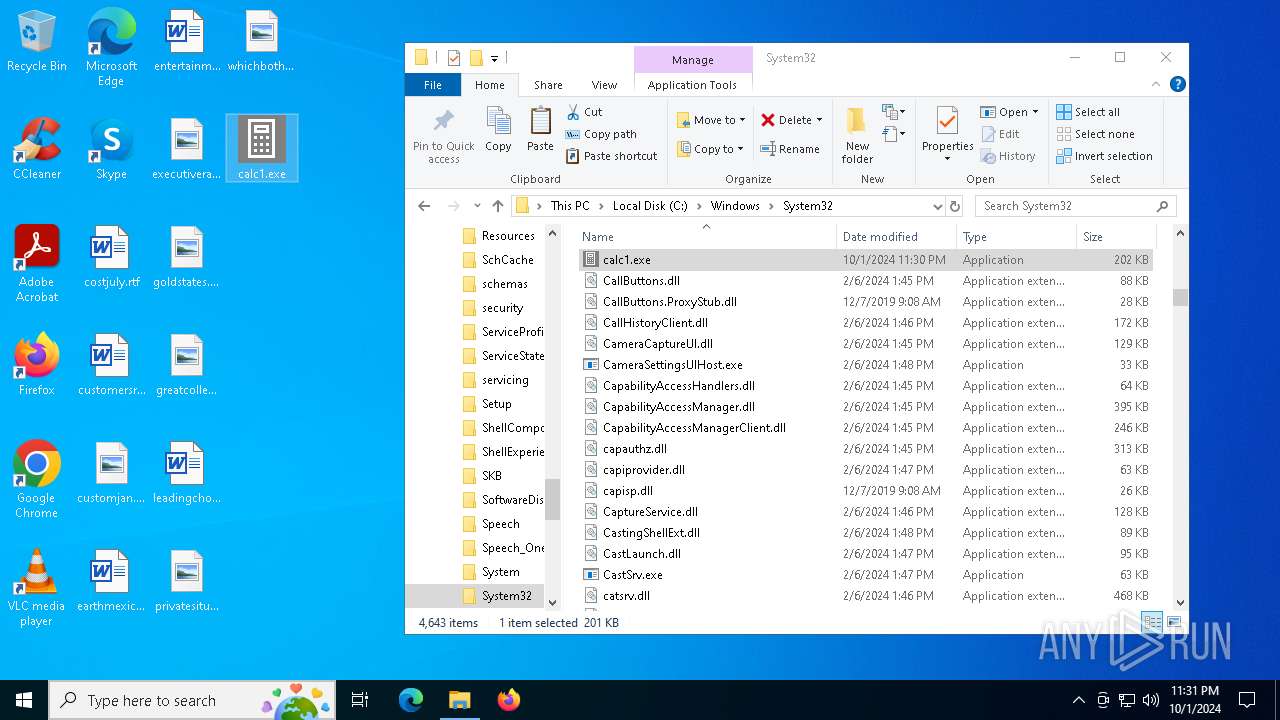
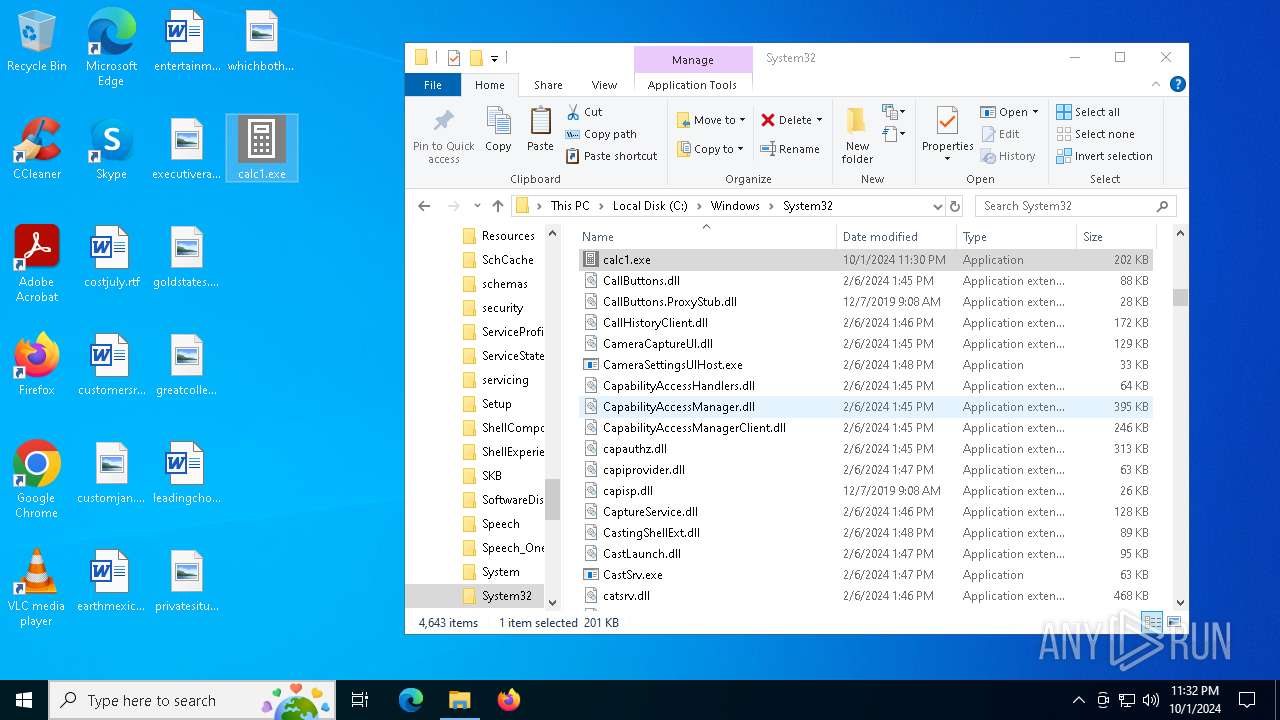
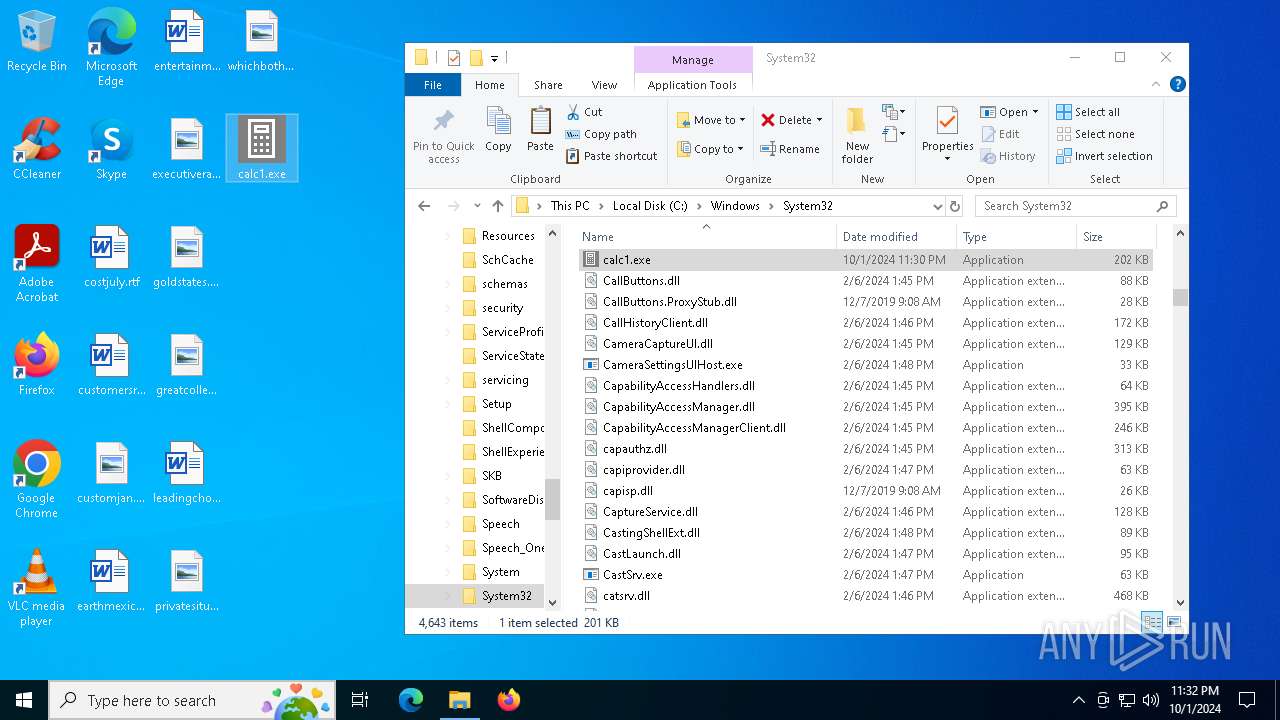
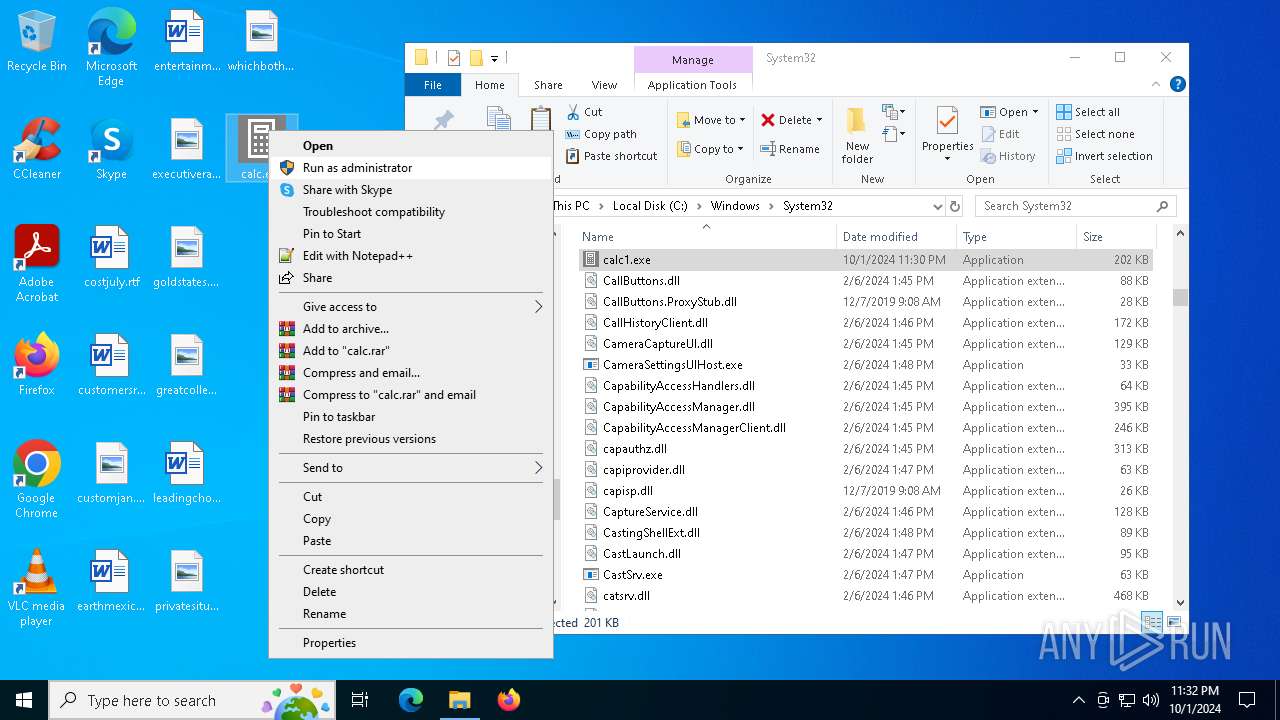
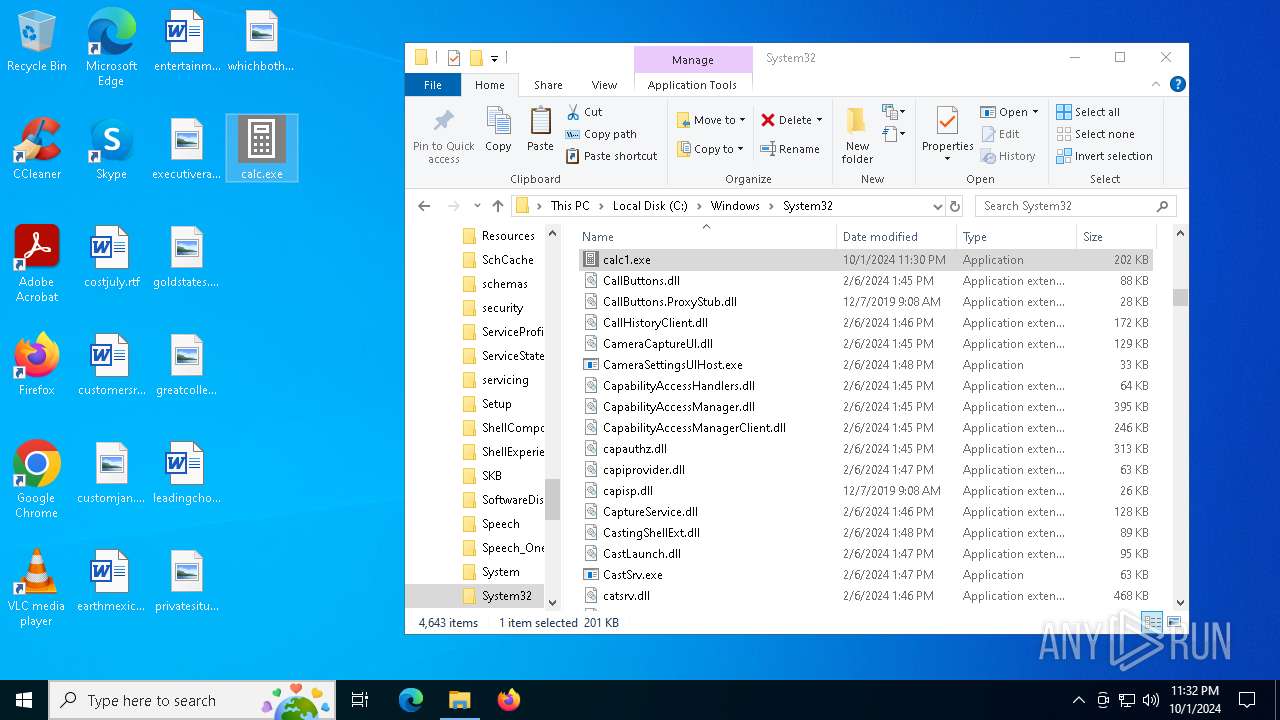
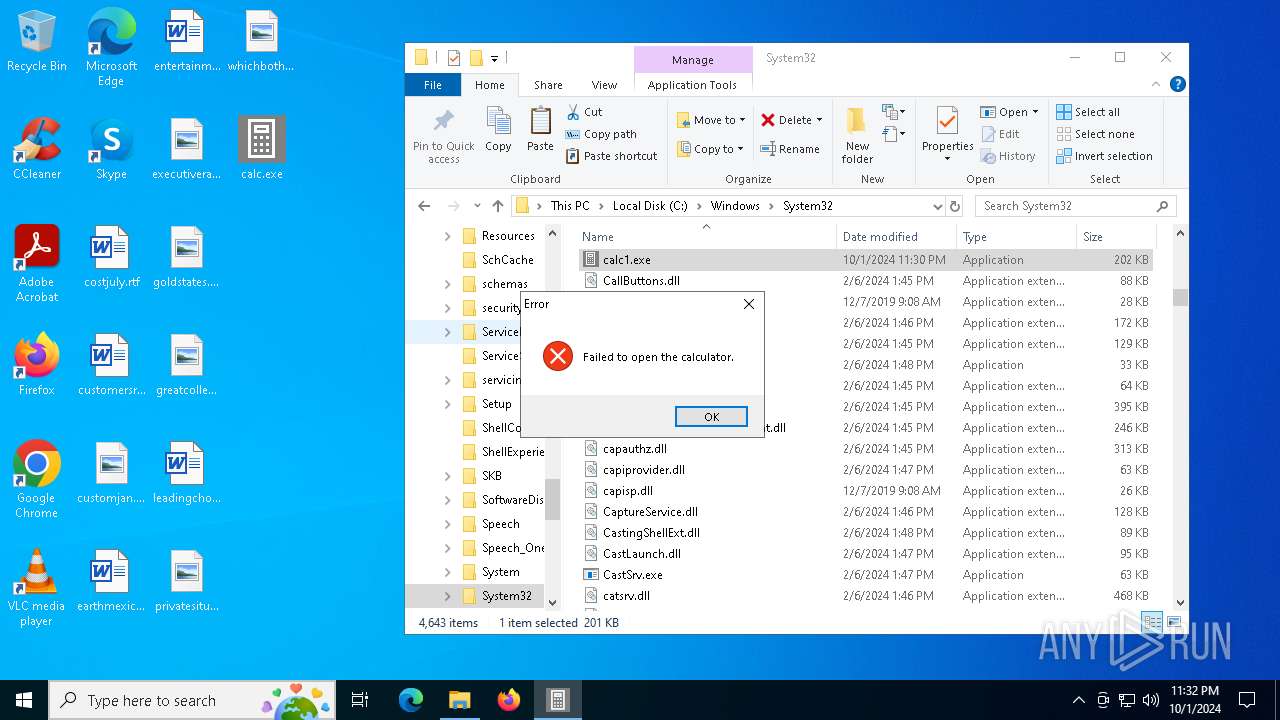
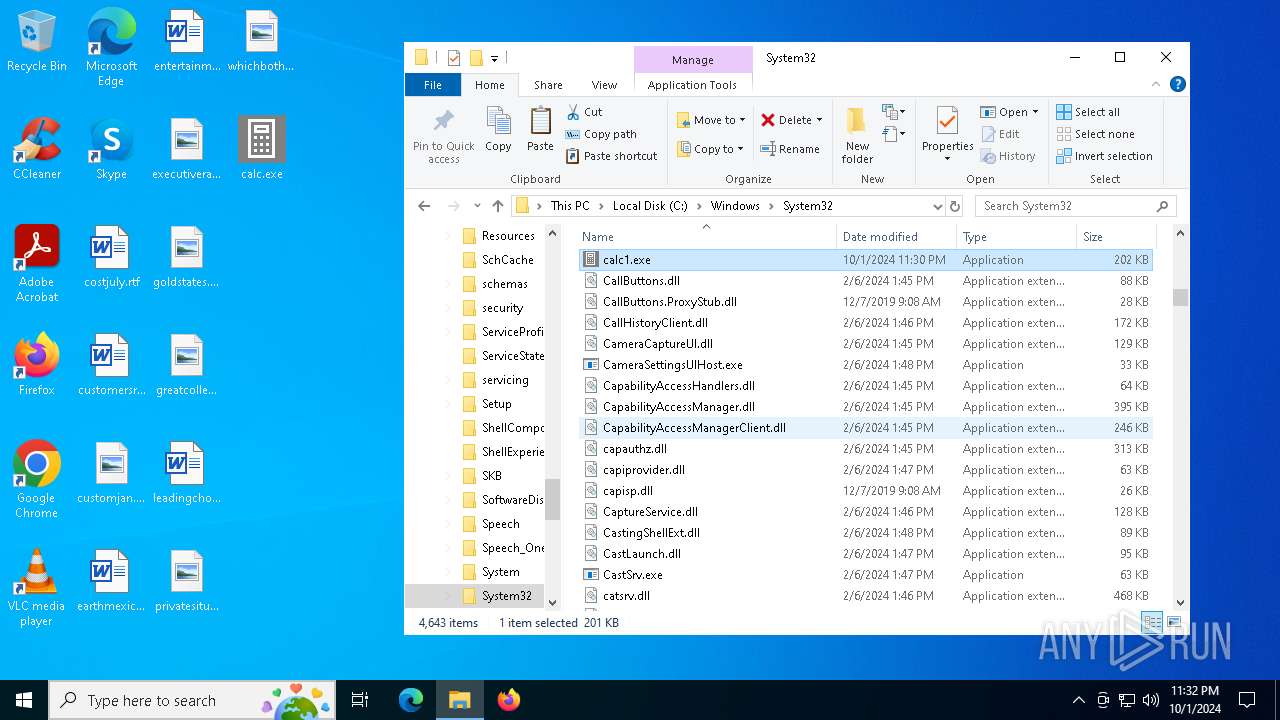
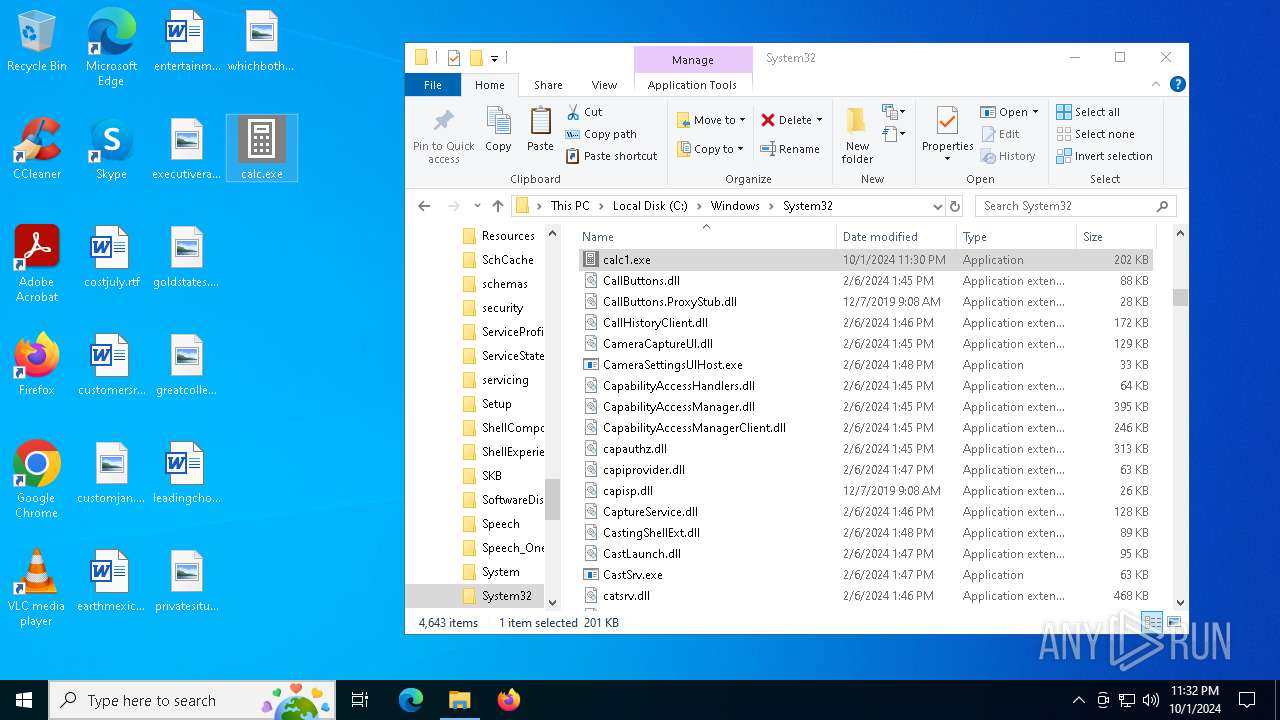
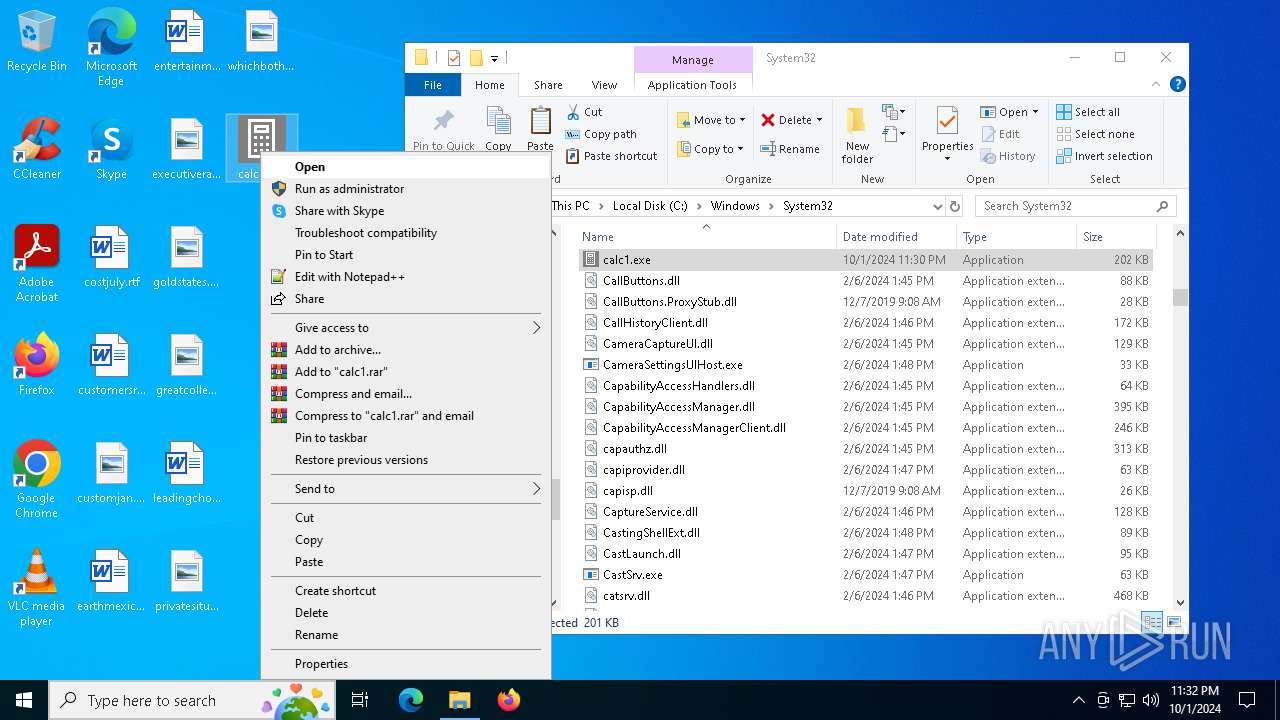
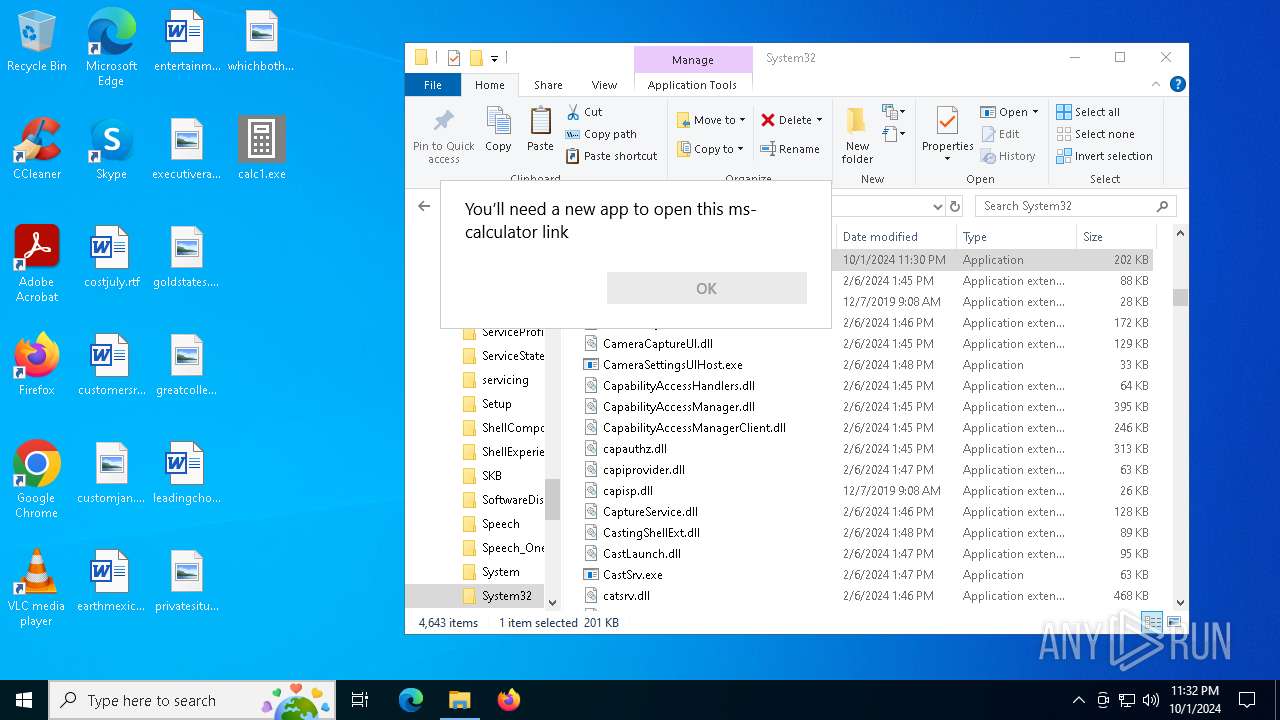
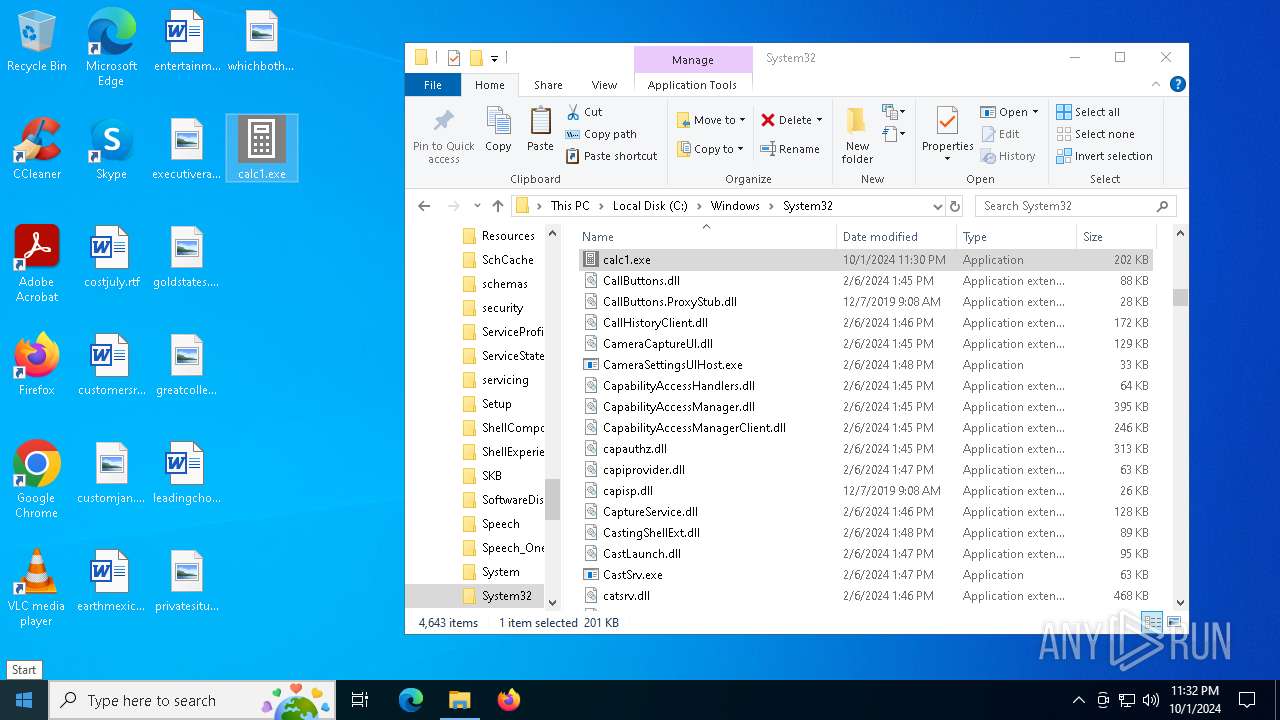
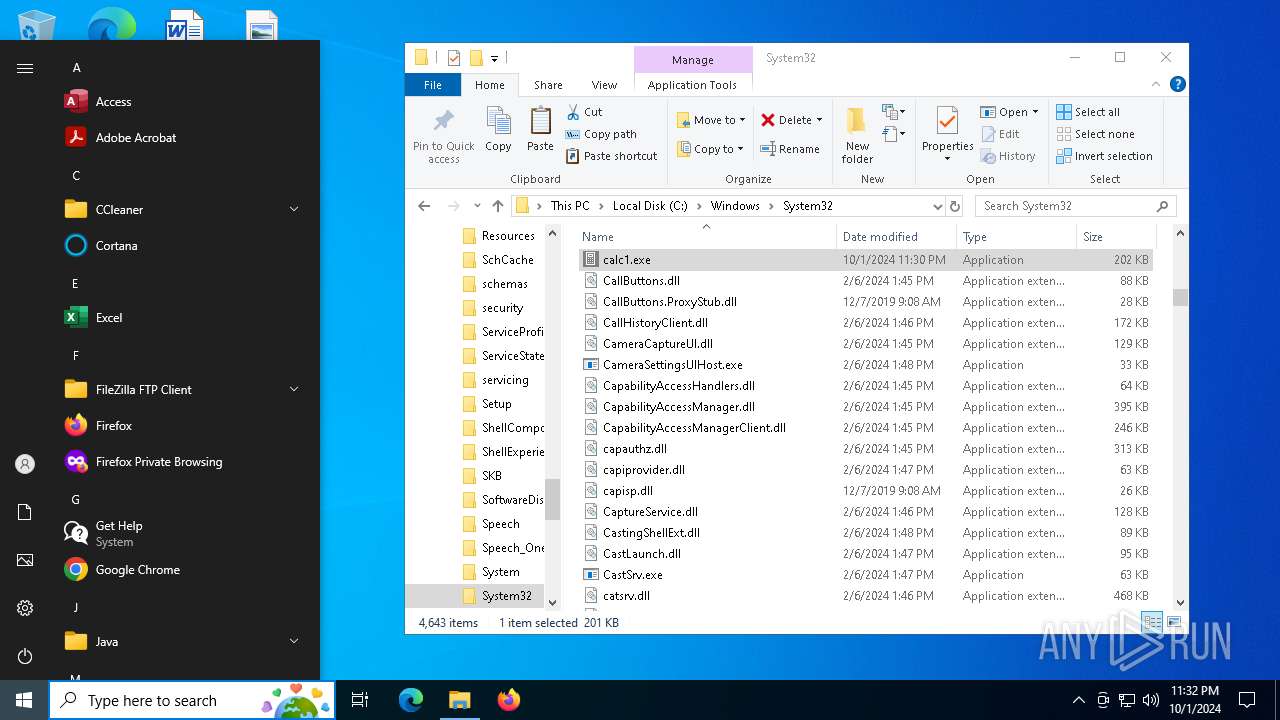
Manual execution by a user
- calc.exe (PID: 5328)
- calc1.exe (PID: 5476)
- calc.exe (PID: 6352)
- calc.exe (PID: 4528)
- calc1.exe (PID: 608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:05:25 14:27:07+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 200704 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | 356352 |
| EntryPoint: | 0x88080 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.2.4.9 |
| ProductVersionNumber: | 3.2.4.9 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileDescription: | - |
| FileVersion: | 3, 2, 4, 9 |
| CompiledScript: | AutoIt v3 Script : 3, 2, 4, 9 |
Total processes
205
Monitored processes
65
Malicious processes
3
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | C:\WINDOWS\system32\net1 localgroup administrators LocalAdministrator /add | C:\Windows\SysWOW64\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | "C:\Windows\System32\net.exe" localgroup administrators LocalAdministrator /add | C:\Windows\SysWOW64\net.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 608 | "C:\Users\admin\Desktop\calc1.exe" | C:\Users\admin\Desktop\calc1.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 3, 2, 4, 9 Modules
| |||||||||||||||
| 796 | "C:\Windows\System32\wscript.exe" 6z120R0QeM.jse | C:\Windows\SysWOW64\wscript.exe | — | calc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 880 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 884 | "C:\Windows\System32\net.exe" user LocalAdministrator /add | C:\Windows\SysWOW64\net.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 892 | "C:\Windows\System32\net.exe" user LocalAdministrator /add | C:\Windows\SysWOW64\net.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | "C:\Windows\System32\net.exe" localgroup administrators LocalAdministrator /add | C:\Windows\SysWOW64\net.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1220 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1360 | C:\WINDOWS\system32\net1 user LocalAdministrator /add | C:\Windows\SysWOW64\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 183
Read events
9 166
Write events
17
Delete events
0
Modification events
| (PID) Process: | (6352) calc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings |
| Operation: | write | Name: | JITDebug |
Value: 0 | |||
| (PID) Process: | (6352) calc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\calc.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: E7923F0000000000 | |||
| (PID) Process: | (1932) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\wscript.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: 19953F0000000000 | |||
| (PID) Process: | (5476) calc1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\calc1.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: 8F42400000000000 | |||
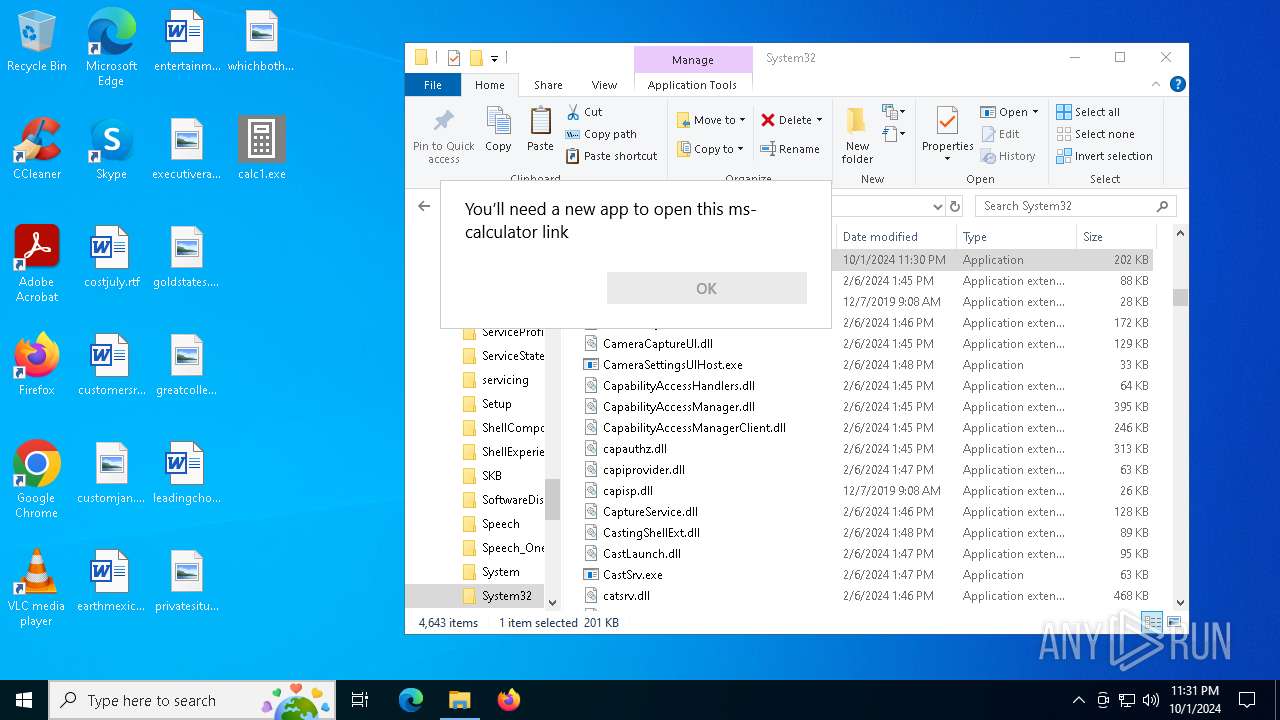
| (PID) Process: | (6476) calc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (6476) calc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6476) calc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6476) calc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2508) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2508) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
1
Suspicious files
8
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6352 | calc.exe | C:\Users\admin\Desktop\XyaLv0kqJO.jse | binary | |
MD5:B4EB7F28555DDA63F591A950F2DB89D1 | SHA256:00C9F54DC4DEEC12DB8BA086EC347D03F978E46222D9C5EC5C6240F7AC171C5C | |||
| 3032 | dllhost.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\f01b4d95cf55d32a.automaticDestinations-ms | binary | |
MD5:BD63BFAE0CDF542321234DFE1C2DE5E3 | SHA256:7092EF4C490D885173FD0F7F7063BE6AC37F876FB88F3D21630D7DE265319885 | |||
| 2576 | calc.exe | C:\Users\admin\Desktop\6z120R0QeM.jse | vbe | |
MD5:B4EB7F28555DDA63F591A950F2DB89D1 | SHA256:00C9F54DC4DEEC12DB8BA086EC347D03F978E46222D9C5EC5C6240F7AC171C5C | |||
| 4528 | calc.exe | C:\Users\admin\Desktop\LLWLkK7RtC.jse | vbe | |
MD5:B4EB7F28555DDA63F591A950F2DB89D1 | SHA256:00C9F54DC4DEEC12DB8BA086EC347D03F978E46222D9C5EC5C6240F7AC171C5C | |||
| 5212 | calc.exe | C:\Users\admin\Desktop\SnKPsfWBZl.jse | vbe | |
MD5:B4EB7F28555DDA63F591A950F2DB89D1 | SHA256:00C9F54DC4DEEC12DB8BA086EC347D03F978E46222D9C5EC5C6240F7AC171C5C | |||
| 5328 | calc.exe | C:\Users\admin\Desktop\GxXI1mCtvQ.jse | vbe | |
MD5:B4EB7F28555DDA63F591A950F2DB89D1 | SHA256:00C9F54DC4DEEC12DB8BA086EC347D03F978E46222D9C5EC5C6240F7AC171C5C | |||
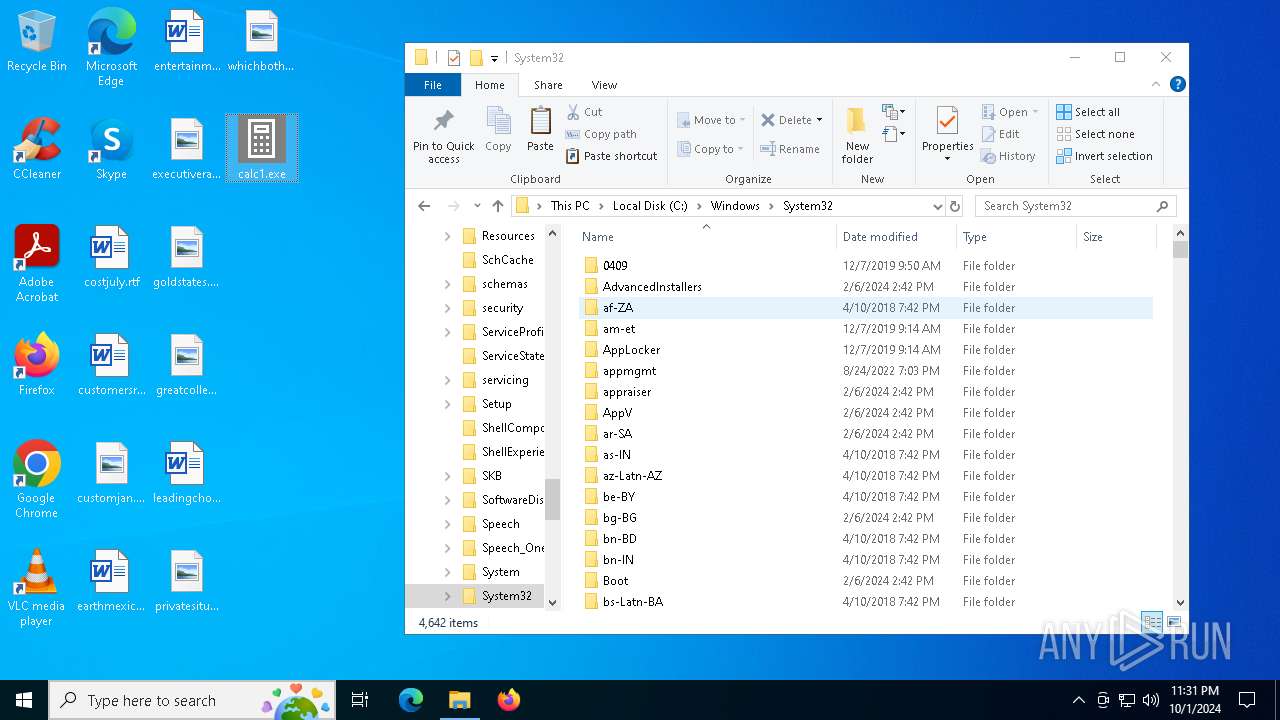
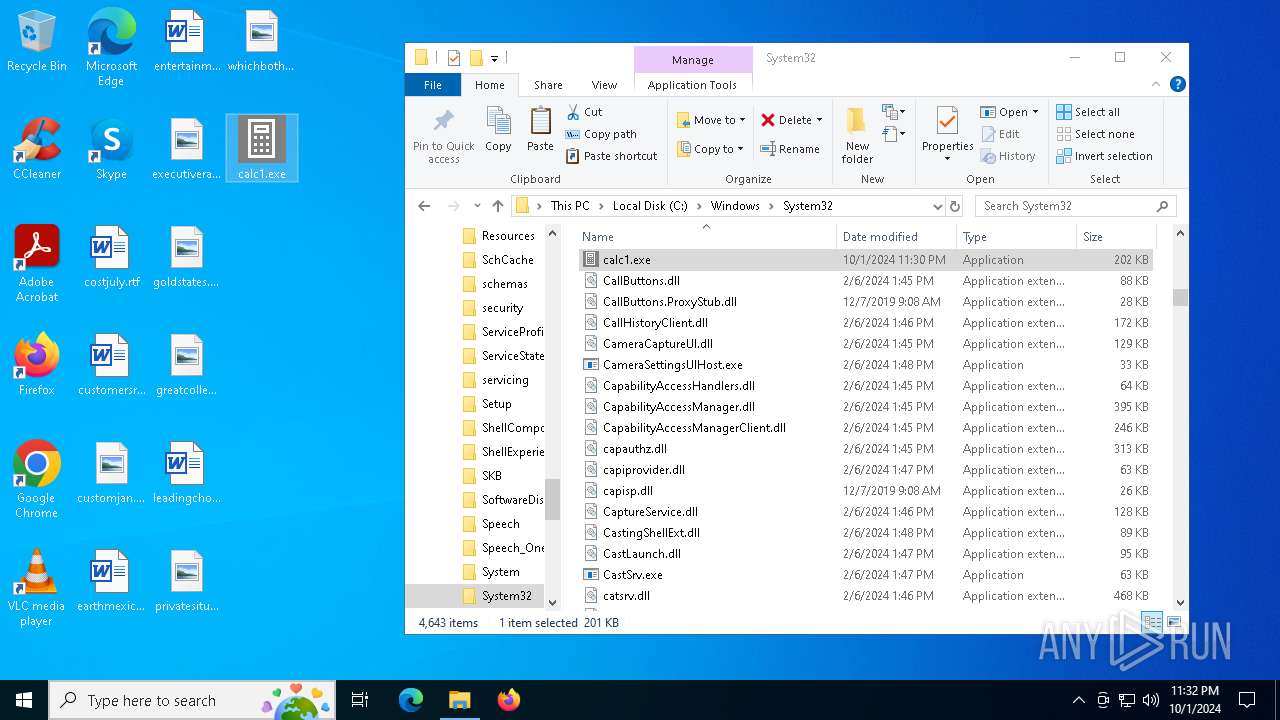
| 3032 | dllhost.exe | C:\Windows\System32\calc1.exe | executable | |
MD5:2F9FDAD776D8626F2CE8625211831E91 | SHA256:9B66A8EA0F1C64965B06E7A45AFBE56F2D4E6D5EF65F32446DEFCCBEBE730813 | |||
| 5476 | calc1.exe | C:\Users\admin\Desktop\XBqx1UXKHk.jse | vbe | |
MD5:B4EB7F28555DDA63F591A950F2DB89D1 | SHA256:00C9F54DC4DEEC12DB8BA086EC347D03F978E46222D9C5EC5C6240F7AC171C5C | |||
| 608 | calc1.exe | C:\Users\admin\Desktop\USgSMlIKpe.jse | binary | |
MD5:B4EB7F28555DDA63F591A950F2DB89D1 | SHA256:00C9F54DC4DEEC12DB8BA086EC347D03F978E46222D9C5EC5C6240F7AC171C5C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
44
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5880 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6352 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6352 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2356 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4324 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5000 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5880 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5880 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |