| File name: | cmd_fw_installer_138430009_eb.exe |
| Full analysis: | https://app.any.run/tasks/d53d7e32-2f3a-4796-9541-9c514e40f1ec |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2022, 04:32:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B48216DCA6F745A40645248384659FDD |
| SHA1: | 3BC265E7282BFB5C63BE6CC73A2B7AAD9A060904 |
| SHA256: | 9B6394B0D1DA147C5C718EBF3ABA211CE2D4AEFC63EB0DC80ED5CFC0DB269BCD |
| SSDEEP: | 98304:n3oeoi7dSeyJ6A89FbeCD25kvriejkx9sZjMK6vx6IF/M8aWzBWcPNkNzt9e:n3oeoYSeyJ6vnKCD25kvmeh6vFF//aFU |
MALICIOUS
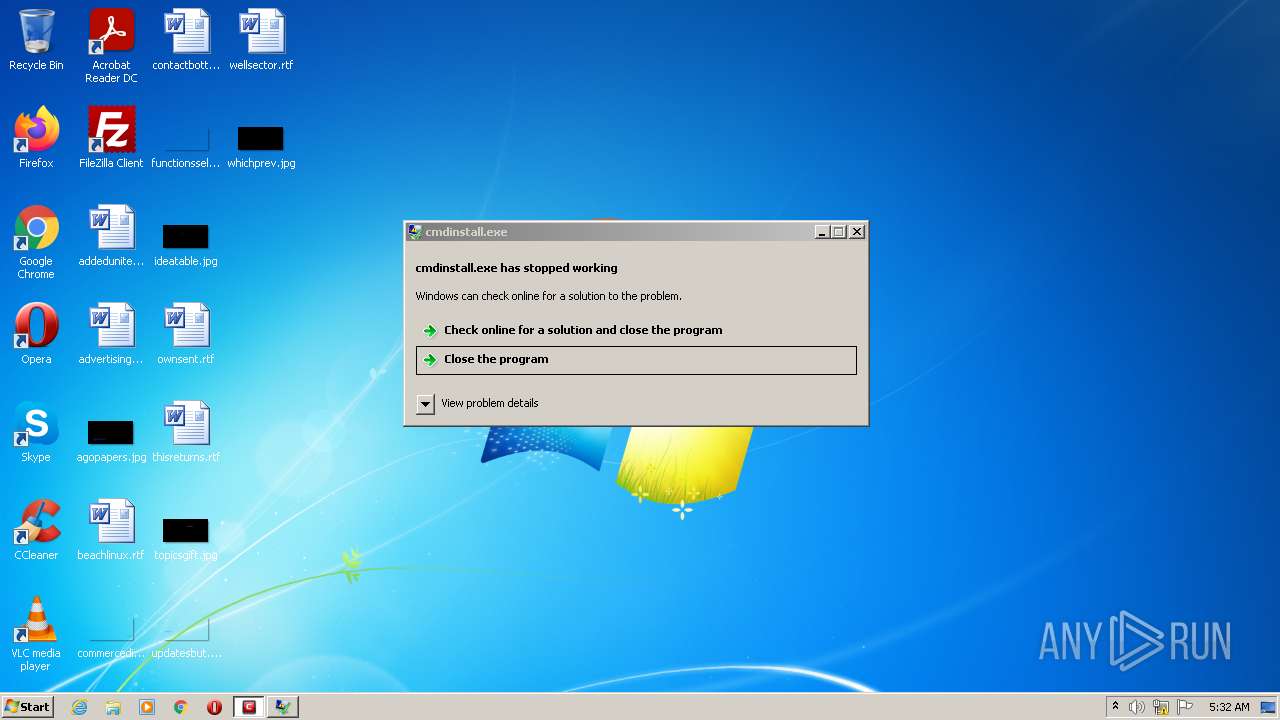
Drops executable file immediately after starts
- cmd_fw_installer_138430009_eb.exe (PID: 3108)
- cmdinstall.exe (PID: 4012)
- cmdinstall.exe (PID: 3660)
- cmdinstall_138430009_eb.exe (PID: 3544)
Changes settings of System certificates
- cmdinstall.exe (PID: 4012)
Application was dropped or rewritten from another process
- cmdinstall_138430009_eb.exe (PID: 3544)
- cmdinstall.exe (PID: 4012)
- cmdinstall.exe (PID: 3660)
Actions looks like stealing of personal data
- cmdinstall.exe (PID: 3660)
- cmdinstall_138430009_eb.exe (PID: 3544)
- cmdinstall.exe (PID: 4012)
Loads dropped or rewritten executable
- cmdinstall.exe (PID: 3660)
- cmdinstall_138430009_eb.exe (PID: 3544)
- cmdinstall.exe (PID: 4012)
Steals credentials from Web Browsers
- cmdinstall_138430009_eb.exe (PID: 3544)
SUSPICIOUS
Checks supported languages
- cmd_fw_installer_138430009_eb.exe (PID: 3108)
- cmdinstall.exe (PID: 3660)
- cmdinstall.exe (PID: 4012)
- cmdinstall_138430009_eb.exe (PID: 3544)
Drops a file with a compile date too recent
- cmd_fw_installer_138430009_eb.exe (PID: 3108)
- cmdinstall.exe (PID: 4012)
- cmdinstall.exe (PID: 3660)
- cmdinstall_138430009_eb.exe (PID: 3544)
Reads the computer name
- cmd_fw_installer_138430009_eb.exe (PID: 3108)
- cmdinstall.exe (PID: 3660)
- cmdinstall.exe (PID: 4012)
- cmdinstall_138430009_eb.exe (PID: 3544)
Executable content was dropped or overwritten
- cmd_fw_installer_138430009_eb.exe (PID: 3108)
- cmdinstall.exe (PID: 4012)
- cmdinstall.exe (PID: 3660)
- cmdinstall_138430009_eb.exe (PID: 3544)
Creates files in the program directory
- cmdinstall.exe (PID: 3660)
- cmdinstall.exe (PID: 4012)
- cmdinstall_138430009_eb.exe (PID: 3544)
Application launched itself
- cmdinstall.exe (PID: 3660)
Adds / modifies Windows certificates
- cmdinstall.exe (PID: 4012)
Starts itself from another location
- cmdinstall.exe (PID: 4012)
INFO
Dropped object may contain Bitcoin addresses
- cmd_fw_installer_138430009_eb.exe (PID: 3108)
- cmdinstall.exe (PID: 3660)
- cmdinstall_138430009_eb.exe (PID: 3544)
- cmdinstall.exe (PID: 4012)
Checks Windows Trust Settings
- cmdinstall.exe (PID: 3660)
- cmdinstall.exe (PID: 4012)
- cmdinstall_138430009_eb.exe (PID: 3544)
Reads settings of System Certificates
- cmdinstall.exe (PID: 3660)
- cmdinstall.exe (PID: 4012)
- cmdinstall_138430009_eb.exe (PID: 3544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| ProductVersion: | 12, 2, 2, 8012 |
|---|---|
| ProductName: | COMODO Internet Security |
| LegalCopyright: | 2005-2021 COMODO. All rights reserved. |
| FileDescription: | COMODO Internet Security |
| FileVersion: | 12, 2, 2, 8012 |
| CompanyName: | COMODO |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 12.2.2.8012 |
| FileVersionNumber: | 12.2.2.8012 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x1d0f6 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 1587200 |
| CodeSize: | 144384 |
| LinkerVersion: | 11 |
| PEType: | PE32 |
| TimeStamp: | 2016:02:18 15:47:52+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Feb-2016 14:47:52 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | COMODO |
| FileVersion: | 12, 2, 2, 8012 |
| FileDescription: | COMODO Internet Security |
| LegalCopyright: | 2005-2021 COMODO. All rights reserved. |
| ProductName: | COMODO Internet Security |
| ProductVersion: | 12, 2, 2, 8012 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0060 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 18-Feb-2016 14:47:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000233FF | 0x00023400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.65007 |
.rdata | 0x00025000 | 0x000089C8 | 0x00008A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.25011 |
.data | 0x0002E000 | 0x000077F0 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.93421 |
.rsrc | 0x00036000 | 0x00175ED8 | 0x00176000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.80676 |
.reloc | 0x001AC000 | 0x0000373E | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.76779 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.33456 | 1148 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.66119 | 19496 | Latin 1 / Western European | Ukrainian - Ukraine | RT_ICON |
3 | 5.68173 | 5672 | Latin 1 / Western European | Ukrainian - Ukraine | RT_ICON |
4 | 5.4657 | 3752 | Latin 1 / Western European | Ukrainian - Ukraine | RT_ICON |
5 | 5.62075 | 2216 | Latin 1 / Western European | Ukrainian - Ukraine | RT_ICON |
6 | 5.95385 | 1736 | Latin 1 / Western European | Ukrainian - Ukraine | RT_ICON |
7 | 4.40157 | 1384 | Latin 1 / Western European | Ukrainian - Ukraine | RT_ICON |
8 | 5.35101 | 270376 | Latin 1 / Western European | Ukrainian - Ukraine | RT_ICON |
9 | 5.40125 | 67624 | Latin 1 / Western European | Ukrainian - Ukraine | RT_ICON |
10 | 5.47119 | 16936 | Latin 1 / Western European | Ukrainian - Ukraine | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
43
Monitored processes
4
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3108 | "C:\Users\admin\AppData\Local\Temp\cmd_fw_installer_138430009_eb.exe" | C:\Users\admin\AppData\Local\Temp\cmd_fw_installer_138430009_eb.exe | Explorer.EXE | ||||||||||||
User: admin Company: COMODO Integrity Level: MEDIUM Description: COMODO Internet Security Exit code: 0 Version: 12, 2, 2, 8012 Modules
| |||||||||||||||
| 3544 | "C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\cmdinstall_138430009_eb.exe" -log -logfile "C:\Users\admin\AppData\Local\Temp\\cmdinstall.exe_22-05-21_05.32.10.log" -theme "lycia" -setupname "cmd_fw_installer_138430009_eb.exe" -type "web" -mode "cfwfree" -sfx "C:\Users\admin\AppData\Local\Temp" -elevated -parent 4012 "admin" 1080 | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\cmdinstall_138430009_eb.exe | cmdinstall.exe | ||||||||||||
User: admin Company: COMODO Integrity Level: HIGH Description: COMODO Internet Security Exit code: 4294967295 Version: 12, 2, 2, 8012 Modules
| |||||||||||||||
| 3660 | "C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\cmdinstall.exe" -log -setupname "cmd_fw_installer_138430009_eb.exe" -sfx "C:\Users\admin\AppData\Local\Temp" -theme lycia -type web -mode cfwfree | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\cmdinstall.exe | cmd_fw_installer_138430009_eb.exe | ||||||||||||
User: admin Company: COMODO Integrity Level: MEDIUM Description: COMODO Internet Security Exit code: 250477278 Version: 12, 2, 2, 8012 Modules
| |||||||||||||||
| 4012 | "C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\cmdinstall.exe" -log -theme "lycia" -setupname "cmd_fw_installer_138430009_eb.exe" -type "web" -mode "cfwfree" -sfx "C:\Users\admin\AppData\Local\Temp" -elevated -logfile "C:\Users\admin\AppData\Local\Temp\\cmdinstall.exe_22-05-21_05.32.10.log" -parent 3660 "admin" 1156 | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\cmdinstall.exe | cmdinstall.exe | ||||||||||||
User: admin Company: COMODO Integrity Level: HIGH Description: COMODO Internet Security Exit code: 4294967295 Version: 12, 2, 2, 8012 Modules
| |||||||||||||||
Total events
23 226
Read events
23 132
Write events
94
Delete events
0
Modification events
| (PID) Process: | (3108) cmd_fw_installer_138430009_eb.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3108) cmd_fw_installer_138430009_eb.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3108) cmd_fw_installer_138430009_eb.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3108) cmd_fw_installer_138430009_eb.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3660) cmdinstall.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3660) cmdinstall.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3660) cmdinstall.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3660) cmdinstall.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3660) cmdinstall.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4012) cmdinstall.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
9
Suspicious files
8
Text files
127
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3108 | cmd_fw_installer_138430009_eb.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\translations\1029.lang | xml | |
MD5:222E3AB01EECF99CF4DD23C35D82709E | SHA256:9766E8708E28C3B1F0767DC9B58CE3F0B3562D41DE94C17079FE411F528470FA | |||
| 3108 | cmd_fw_installer_138430009_eb.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\installer_langdata.bin | text | |
MD5:B80EDA6258E28B537651F8E5EBD997FF | SHA256:6E960DFED451C2DFB99352D25D3DF8DD46FE7D80C9AF79805C0CFBD1A99A2709 | |||
| 3108 | cmd_fw_installer_138430009_eb.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\translations\1028.lang | xml | |
MD5:98E6CA1FB834AF2009E84E42180AAAEC | SHA256:A97B4EB25F9E900295F905AC8DEBE03DADBEE0051566DFB0C11529B7F8E886FD | |||
| 3108 | cmd_fw_installer_138430009_eb.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\translations\1025.lang | xml | |
MD5:159295A63CF16D39C9D0944C696D6D22 | SHA256:B006045A62B6D1B336206FC522DCA7EE6968A6127A6BFB0C35E9E64F6BD7A7FA | |||
| 3108 | cmd_fw_installer_138430009_eb.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\translations\1026.lang | xml | |
MD5:4786A7FB4658F8F602CBF7FD1B258D1D | SHA256:557C24CF1E3888FF4A0B1DE77DFA09E5F3FE331DCF70B6AB9E5A12FC01B22B55 | |||
| 3108 | cmd_fw_installer_138430009_eb.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\themes\ilycia.set | executable | |
MD5:7B85F91536C8342AC64D3EDECE2AF7FE | SHA256:918E7AAD857776A895ECDF850665C355026882BCF1E0EBA279FF4F7AA4B6BBAE | |||
| 3108 | cmd_fw_installer_138430009_eb.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\translations\1041.lang | xml | |
MD5:283BF49692B268982A781BDEA2022541 | SHA256:E748B8B1CE8D151BB131D5B04D2FF2DE84F7B81B39267FE97C3D2BC41E68BCDD | |||
| 3108 | cmd_fw_installer_138430009_eb.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\translations\1031.lang | xml | |
MD5:4308208CEE6EE93EC49D385503A692BF | SHA256:0BAB7AE6CEDED50035A5FD748BB1140C3242FEE988136EF8121E79A1257A465A | |||
| 3108 | cmd_fw_installer_138430009_eb.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\translations\1036.lang | xml | |
MD5:886928F55017935E54DAD06B422E57D6 | SHA256:CEC906EFFCED50F53F3764FDCCFED133668CD48F5C2C5C88E088963C5972A4B5 | |||
| 3108 | cmd_fw_installer_138430009_eb.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\translations\1032.lang | xml | |
MD5:26BA47F25D22CFEBEFA3D4DAD607CB99 | SHA256:FF662CC5FC59E4D111FB537D06BA9CA7DE7CF183C1BF94ED9FA11F4170827EF3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
77
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3660 | cmdinstall.exe | GET | 200 | 95.140.236.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?af5ea77aa4d489f4 | GB | compressed | 60.0 Kb | whitelisted |
3660 | cmdinstall.exe | GET | 200 | 95.140.236.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?37fa4e6a426a0322 | GB | compressed | 4.70 Kb | whitelisted |
3660 | cmdinstall.exe | GET | 200 | 91.199.212.52:80 | http://crt.sectigo.com/SectigoRSAOrganizationValidationSecureServerCA.crt | GB | der | 1.53 Kb | whitelisted |
3660 | cmdinstall.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRXzFDqgcxizGsL1BkUc1gIwekZcAQU34%2FzIAzpyqYE2FtYNyo9q0bcg0kCEBtCewYOKGa%2FtYbMJn4cPqo%3D | US | der | 509 b | whitelisted |
3660 | cmdinstall.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSmEJ7s5DLYqQ4%2FaFKR54j1BHqdkgQUGqH4YRkgD8NBd0UojtE1XwYSBFUCEQCMd6AAj%2FTRsMY9nzpIg41r | US | der | 766 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3660 | cmdinstall.exe | 104.18.32.68:80 | ocsp.comodoca.com | Cloudflare Inc | US | suspicious |
3660 | cmdinstall.exe | 95.140.236.128:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | GB | malicious |
3660 | cmdinstall.exe | 172.64.155.188:80 | ocsp.comodoca.com | — | US | suspicious |
3660 | cmdinstall.exe | 178.255.82.5:443 | download.comodo.com | CCANET Limited | GB | suspicious |
4012 | cmdinstall.exe | 178.255.82.5:443 | download.comodo.com | CCANET Limited | GB | suspicious |
3660 | cmdinstall.exe | 69.57.168.134:443 | download.adtrustmedia.com | FortressITX | US | suspicious |
4012 | cmdinstall.exe | 185.59.220.194:443 | cdn.download.comodo.com | Datacamp Limited | DE | suspicious |
3544 | cmdinstall_138430009_eb.exe | 178.255.82.5:443 | download.comodo.com | CCANET Limited | GB | suspicious |
3660 | cmdinstall.exe | 91.199.212.52:80 | crt.sectigo.com | Comodo CA Ltd | GB | suspicious |
3544 | cmdinstall_138430009_eb.exe | 185.59.220.194:443 | cdn.download.comodo.com | Datacamp Limited | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
download.comodo.com |
| whitelisted |
cdn.download.comodo.com |
| whitelisted |
download.adtrustmedia.com |
| suspicious |
crt.sectigo.com |
| whitelisted |
vps.yinemeterwemec.com |
| malicious |
cmc.comodo.com |
| unknown |
licensing.security.comodo.com |
| whitelisted |
Threats
Process | Message |
|---|---|
cmdinstall.exe | Installer__ command line |
cmdinstall.exe | "C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\cmdinstall.exe" -log -setupname "cmd_fw_installer_138430009_eb.exe" -sfx "C:\Users\admin\AppData\Local\Temp" -theme lycia -type web -mode cfwfree |
cmdinstall.exe | Installer__ 5:32:10 d:\jenkins\workspace\cis_um_gitlab\installer_cmdinstall\base\appcheck.cpp:113 >> IsWow64Process said process is running NOT under WOW64 |
cmdinstall.exe | Installer__ 5:32:10 d:\jenkins\workspace\cis_um_gitlab\installer_cmdinstall\base\appcheck.cpp:126 >> Also test GetNativeSystemInfo: its said Processor Architecture is PROCESSOR_ARCHITECTURE_INTEL |
cmdinstall.exe | Installer__ 5:32:10 d:\jenkins\workspace\cis_um_gitlab\installer_cmdinstall\base\appcheck.cpp:141 >> User is Admin: NO |
cmdinstall.exe | Installer__ 5:32:10 d:\jenkins\workspace\cis_um_gitlab\installer_cmdinstall\base\appcheck.cpp:142 >> Windows Version test: x86 |
cmdinstall.exe | Installer__ 5:32:10 d:\jenkins\workspace\cis_um_gitlab\installer_cmdinstall\base\appcheck.cpp:143 >> Windows Version test: SERVER - NO |
cmdinstall.exe | Installer__ 5:32:10 d:\jenkins\workspace\cis_um_gitlab\installer_cmdinstall\base\appcheck.cpp:144 >> Windows Version test: XP - NO |
cmdinstall.exe | Installer__ 5:32:10 d:\jenkins\workspace\cis_um_gitlab\installer_cmdinstall\base\appcheck.cpp:145 >> Windows Version test: XP or VISTA - NO |
cmdinstall.exe | Installer__ 5:32:10 d:\jenkins\workspace\cis_um_gitlab\installer_cmdinstall\base\appcheck.cpp:146 >> Windows Version test: XP or higher - YES |