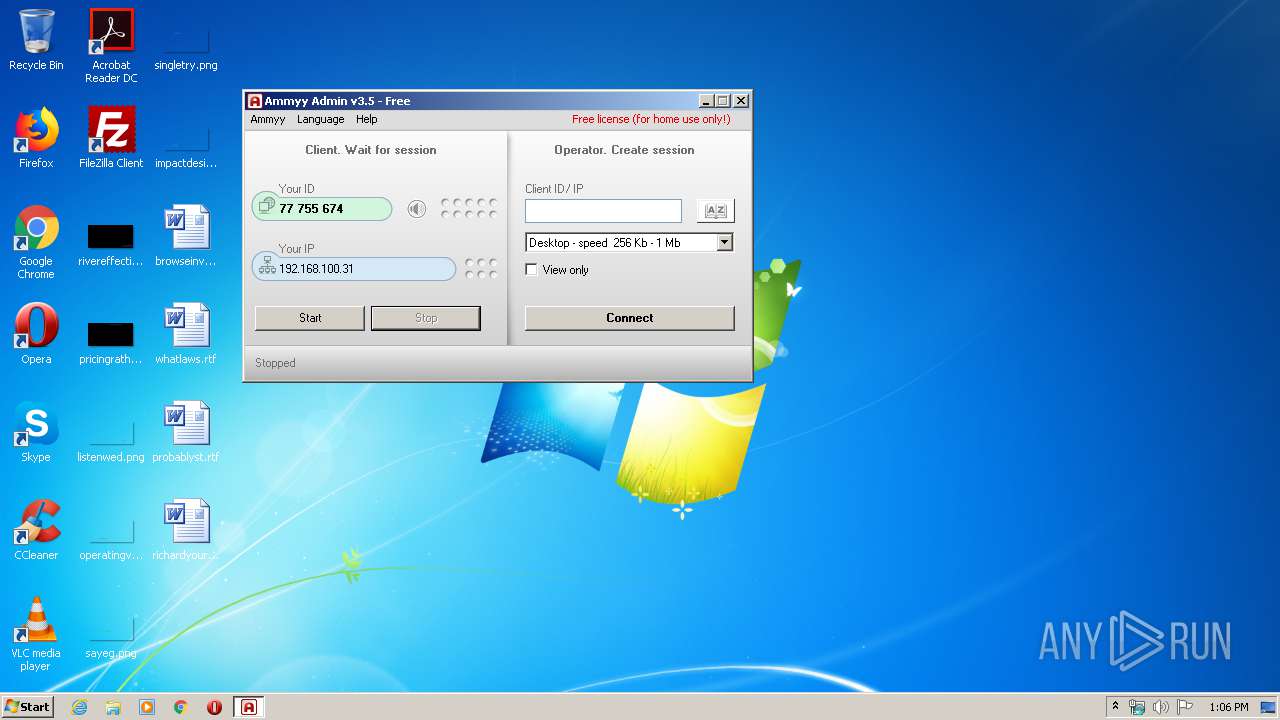
| download: | ammyy.exe |
| Full analysis: | https://app.any.run/tasks/e22f32eb-e16c-499a-b85e-230c677fec9c |
| Verdict: | Malicious activity |
| Analysis date: | March 03, 2020, 13:05:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2CBF5657FFD8858A9597F296A60270C2 |
| SHA1: | B130611C92788337C4F6BB9E9454FF06EB409166 |
| SHA256: | 9B3F4D6A9BAE4D7F9CFE45E706DB8FE4BAEF51AE12353941E8B1532B231E6EAC |
| SSDEEP: | 12288:6NgEvTkYGzXUMA7PTgM0YOg26y4RtcxcUwhqb3omaY80NP6gL:6XTszE7PTgM0YOgA4RtcbwhsSYFVL |
MALICIOUS
Deletes the SafeBoot registry key
- ammyy.exe (PID: 660)
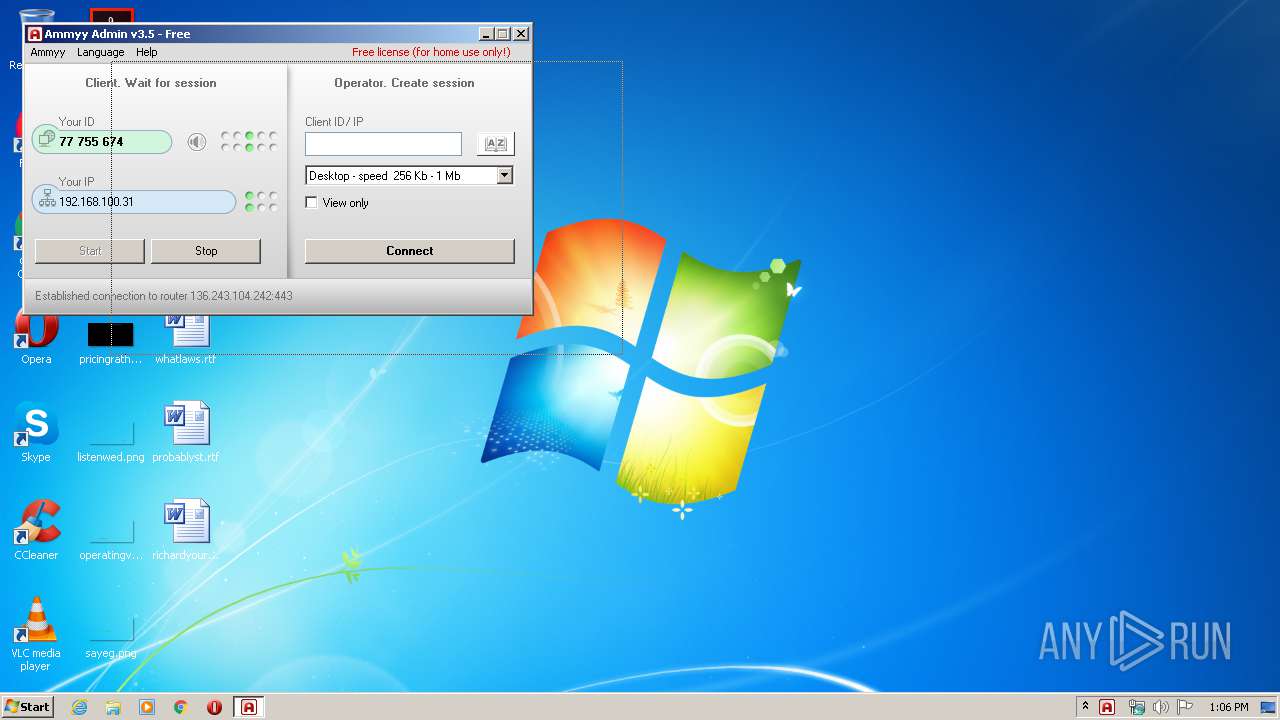
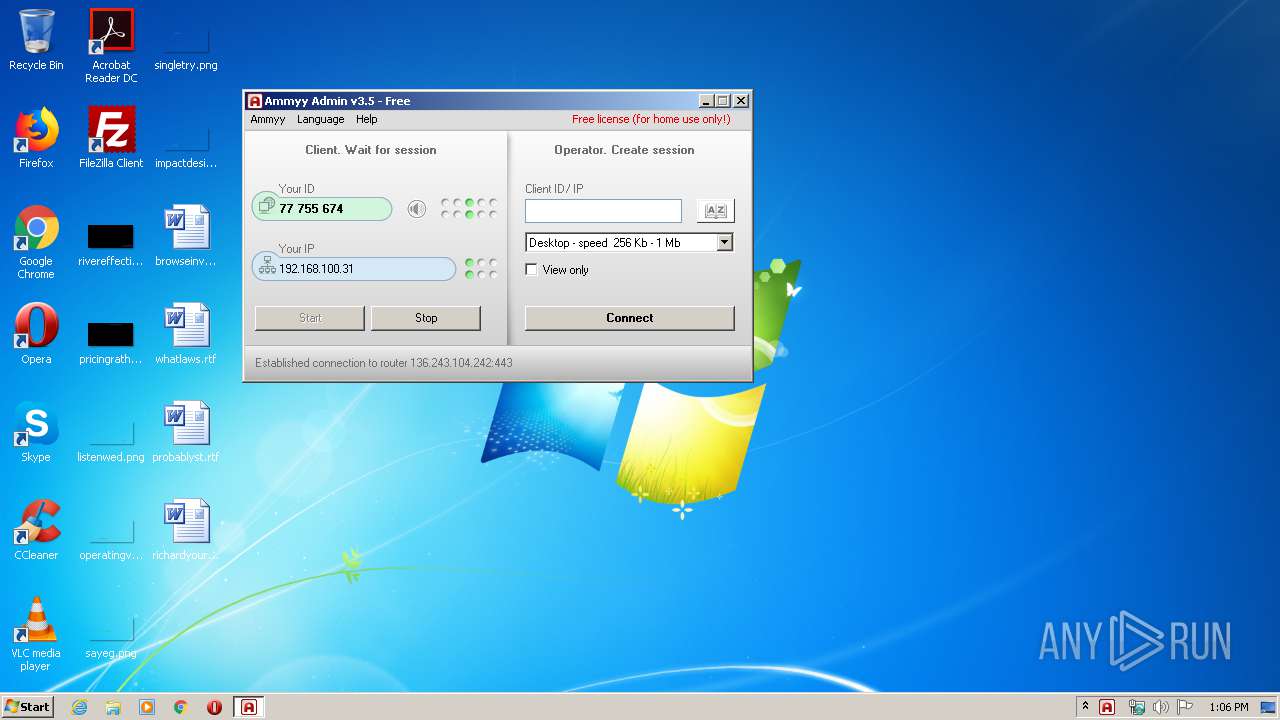
Connects to CnC server
- ammyy.exe (PID: 3924)
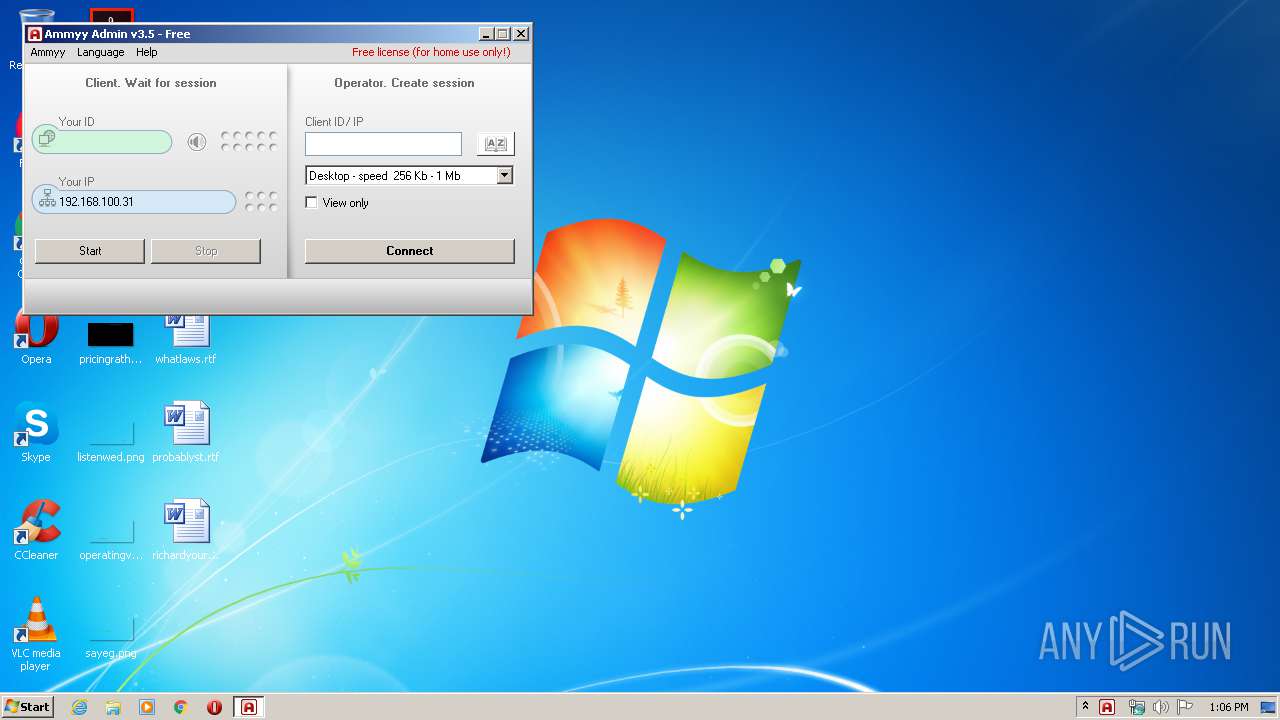
AMMYY was detected
- ammyy.exe (PID: 3924)
SUSPICIOUS
Creates files in the program directory
- ammyy.exe (PID: 3744)
Executed as Windows Service
- ammyy.exe (PID: 2960)
Application launched itself
- ammyy.exe (PID: 3744)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:09:10 01:23:16+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 532480 |
| InitializedDataSize: | 253952 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7c3de |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.5.0.0 |
| ProductVersionNumber: | 3.5.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Ammyy LLC |
| FileDescription: | Ammyy Admin |
| FileVersion: | 3.5 |
| InternalName: | Ammyy Admin |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| PrivateBuild: | - |
| ProductName: | Ammyy Admin |
| ProductVersion: | 3.5 |
| SpecialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Sep-2014 23:23:16 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Ammyy LLC |
| FileDescription: | Ammyy Admin |
| FileVersion: | 3.5 |
| InternalName: | Ammyy Admin |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | - |
| PrivateBuild: | - |
| ProductName: | Ammyy Admin |
| ProductVersion: | 3.5 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 09-Sep-2014 23:23:16 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00081F12 | 0x00082000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70544 |
.rdata | 0x00083000 | 0x000178FC | 0x00018000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.17319 |
.data | 0x0009B000 | 0x0001A7E0 | 0x00013000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.08185 |
.rsrc | 0x000B6000 | 0x0000A5E0 | 0x0000B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.39778 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.841 | 637 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 5.72434 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 6.13946 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 1.65331 | 308 | UNKNOWN | English - United States | RT_CURSOR |
5 | 1.19249 | 308 | UNKNOWN | English - United States | RT_CURSOR |
6 | 1.34234 | 308 | UNKNOWN | English - United States | RT_CURSOR |
100 | 3.53552 | 334 | UNKNOWN | UNKNOWN | RT_DIALOG |
103 | 5.72337 | 1768 | UNKNOWN | Russian - Russia | RT_BITMAP |
104 | 3.07153 | 174 | UNKNOWN | Russian - Russia | RT_DIALOG |
105 | 5.94736 | 1768 | UNKNOWN | Russian - Russia | RT_BITMAP |
Imports
ADVAPI32.dll |
COMCTL32.dll |
DSOUND.dll |
GDI32.dll |
KERNEL32.dll |
MSVCP60.dll |
MSVCRT.dll |
SETUPAPI.dll |
SHELL32.dll |
SHLWAPI.dll |
Total processes
39
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | "C:\Users\admin\AppData\Local\Temp\ammyy.exe" -elevated | C:\Users\admin\AppData\Local\Temp\ammyy.exe | ammyy.exe | ||||||||||||
User: admin Company: Ammyy LLC Integrity Level: HIGH Description: Ammyy Admin Exit code: 0 Version: 3.5 Modules
| |||||||||||||||
| 2960 | "C:\Users\admin\AppData\Local\Temp\ammyy.exe" -service -lunch | C:\Users\admin\AppData\Local\Temp\ammyy.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Ammyy LLC Integrity Level: SYSTEM Description: Ammyy Admin Exit code: 0 Version: 3.5 Modules
| |||||||||||||||
| 3744 | "C:\Users\admin\AppData\Local\Temp\ammyy.exe" | C:\Users\admin\AppData\Local\Temp\ammyy.exe | — | explorer.exe | |||||||||||
User: admin Company: Ammyy LLC Integrity Level: MEDIUM Description: Ammyy Admin Exit code: 0 Version: 3.5 Modules
| |||||||||||||||
| 3924 | "C:\Users\admin\AppData\Local\Temp\ammyy.exe" -elevated | C:\Users\admin\AppData\Local\Temp\ammyy.exe | ammyy.exe | ||||||||||||
User: SYSTEM Company: Ammyy LLC Integrity Level: SYSTEM Description: Ammyy Admin Exit code: 0 Version: 3.5 Modules
| |||||||||||||||
Total events
374
Read events
358
Write events
15
Delete events
1
Modification events
| (PID) Process: | (3744) ammyy.exe | Key: | HKEY_CURRENT_USER\Software\Ammyy\Admin |
| Operation: | write | Name: | hr |
Value: 537D5673663160F3C71425D0B452 | |||
| (PID) Process: | (3744) ammyy.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Ammyy\Admin |
| Operation: | write | Name: | hr |
Value: 537D5673663160F3C71425D0B452 | |||
| (PID) Process: | (3744) ammyy.exe | Key: | HKEY_CURRENT_USER\Software\Ammyy\Admin |
| Operation: | write | Name: | hr3 |
Value: C477B43E66BBA2343EB057386552BEE0CBAF2017610576DB725B7570691049AEE2906155945E9F6C2109EC3E7922CEDFB46E689CBE659B314AA151EC | |||
| (PID) Process: | (3744) ammyy.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Ammyy\Admin |
| Operation: | write | Name: | hr3 |
Value: C477B43E66BBA2343EB057386552BEE0CBAF2017610576DB725B7570691049AEE2906155945E9F6C2109EC3E7922CEDFB46E689CBE659B314AA151EC | |||
| (PID) Process: | (3744) ammyy.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3744) ammyy.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (660) ammyy.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Network\AmmyyAdmin_294 |
| Operation: | write | Name: | |
Value: Service | |||
| (PID) Process: | (3924) ammyy.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3924) ammyy.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (660) ammyy.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Network\AmmyyAdmin_294 |
| Operation: | delete key | Name: | |
Value: | |||
Executable files
0
Suspicious files
5
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3744 | ammyy.exe | C:\ProgramData\AMMYY\hr | binary | |
MD5:ABF503219C1FA5BF1C1ADCC7D44BB7BA | SHA256:AF03887D64FACD2F585A3F8490BD956AA3212D9DED6E08DCA57268A12E8FCD13 | |||
| 3744 | ammyy.exe | C:\ProgramData\AMMYY\hr3 | binary | |
MD5:789780A4470C563AF57B560730EAA16A | SHA256:A694050C3680614173729B34E423BC9FE3A178936013E809DE2A9A6640735C36 | |||
| 3924 | ammyy.exe | C:\ProgramData\AMMYY\hr | binary | |
MD5:F459D41261543161D487C81B967068D3 | SHA256:039D00CA77BC0E212BE01AD9C925F216AB04E54F64D6901B05F904D7FA3DEAD3 | |||
| 3924 | ammyy.exe | C:\ProgramData\AMMYY\hr3 | binary | |
MD5:EAE175AA8AD7D5AC3C0744109C9B31A6 | SHA256:C84868F432C69C2E1596FB4B37687598088E3927026649F840EEE6D2DAAD6DCF | |||
| 3744 | ammyy.exe | C:\ProgramData\AMMYY\settings3.bin | binary | |
MD5:714F2508D4227F74B6ADACFEF73815D8 | SHA256:A5579945F23747541C0E80B79E79375D4CA44FEAFCD425EE9BD9302E35312480 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
1
Threats
5
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3924 | ammyy.exe | 188.42.129.148:80 | rl.ammyy.com | Servers.com, Inc. | NL | malicious |
3924 | ammyy.exe | 136.243.104.242:443 | — | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rl.ammyy.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3924 | ammyy.exe | Potential Corporate Privacy Violation | REMOTE [PTsecurity] Ammyy |
3924 | ammyy.exe | Potential Corporate Privacy Violation | REMOTE [PTsecurity] Ammyy |
3924 | ammyy.exe | Potential Corporate Privacy Violation | REMOTE [PTsecurity] Ammyy |
3924 | ammyy.exe | Potential Corporate Privacy Violation | REMOTE [PTsecurity] Ammyy |
1 ETPRO signatures available at the full report