| File name: | sample_54.zip |
| Full analysis: | https://app.any.run/tasks/2adcc80a-db6b-4dda-8de5-584ad6724fd7 |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 09:41:46 |
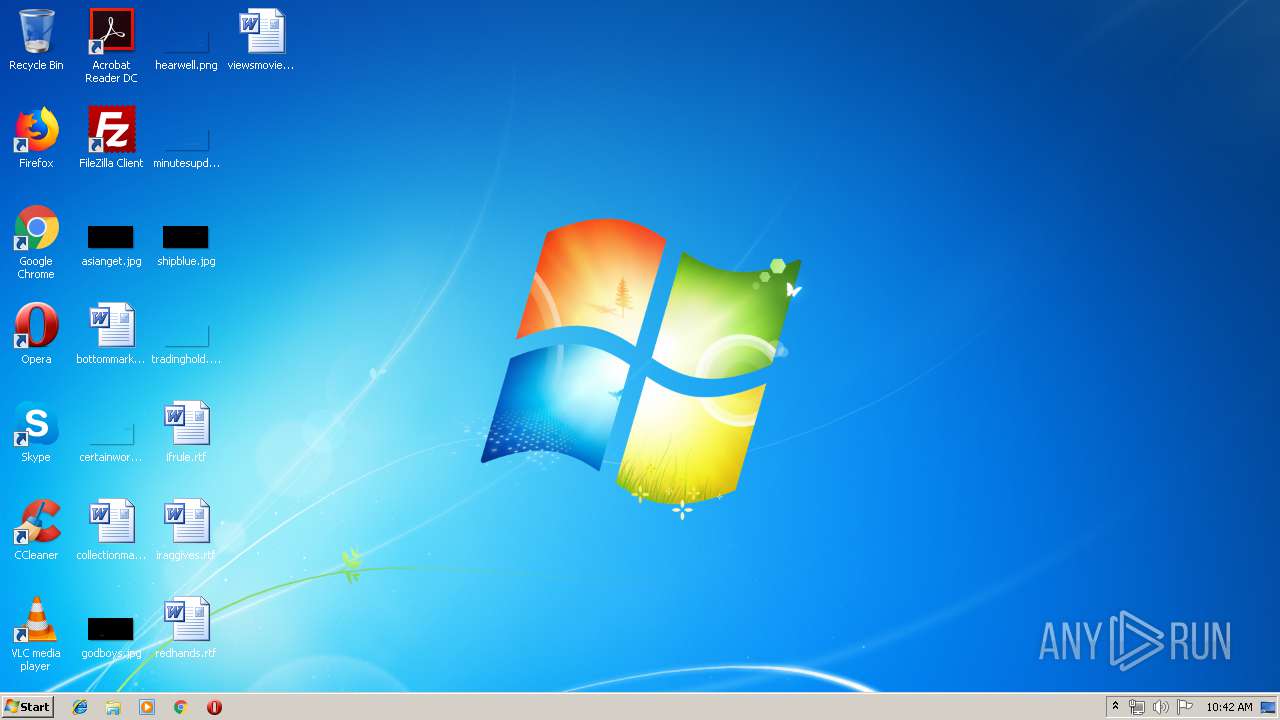
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | BCB190CCF99832695EE16E53E1C5A312 |
| SHA1: | EF846EA6C5AFEF044AE4040D06145E8DEDEA7020 |
| SHA256: | 9B3916500A3B41C485ED827752FE2DB1D64D2254FCF2BF1F16901A67B421E8F8 |
| SSDEEP: | 3072:6e4kmYVcywpVnR37OCbSZzD1M0iPrVXUsndSwvCj5aagsyiXXe8NxHHQP:6pkJVcywpHLSNiGsNCN3gGHe8NNU |
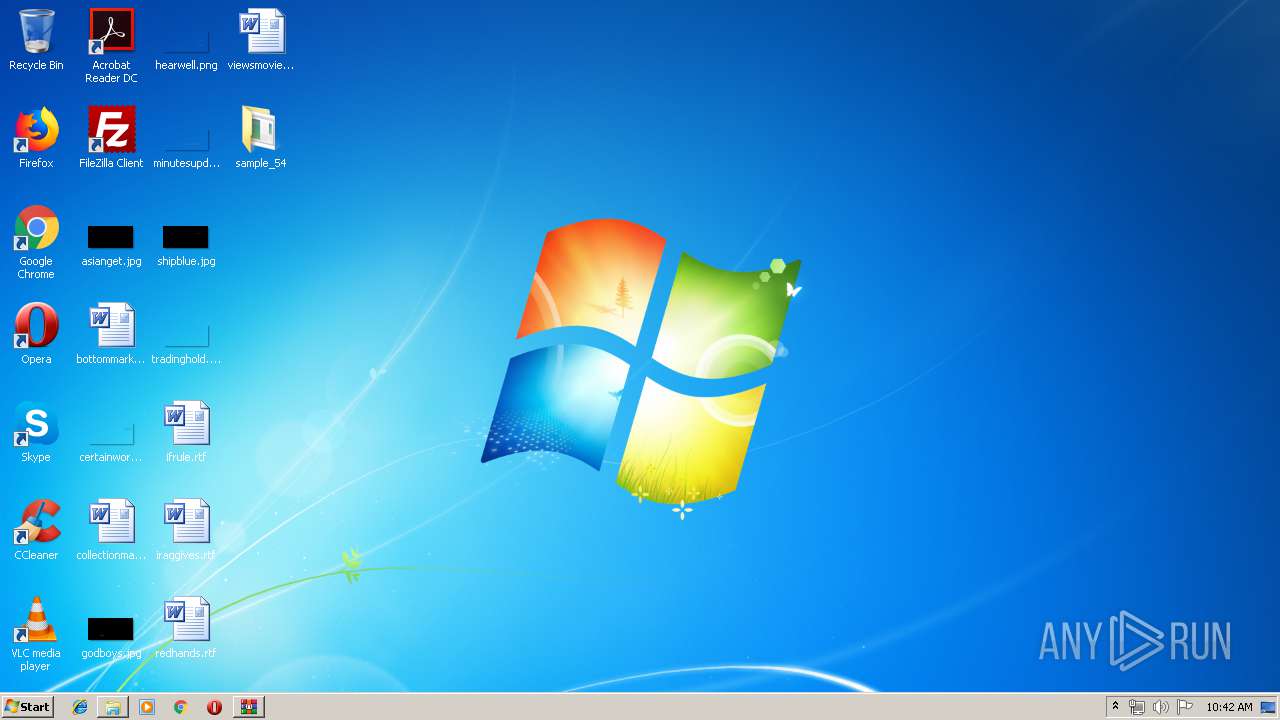
MALICIOUS
Changes the autorun value in the registry
- mahmud.exe (PID: 664)
Application was dropped or rewritten from another process
- sample_54.exe (PID: 2900)
- mahmud.exe (PID: 664)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2124)
- sample_54.exe (PID: 2900)
Creates files in the user directory
- sample_54.exe (PID: 2900)
Starts CMD.EXE for commands execution
- sample_54.exe (PID: 2900)
Reads internet explorer settings
- mahmud.exe (PID: 664)
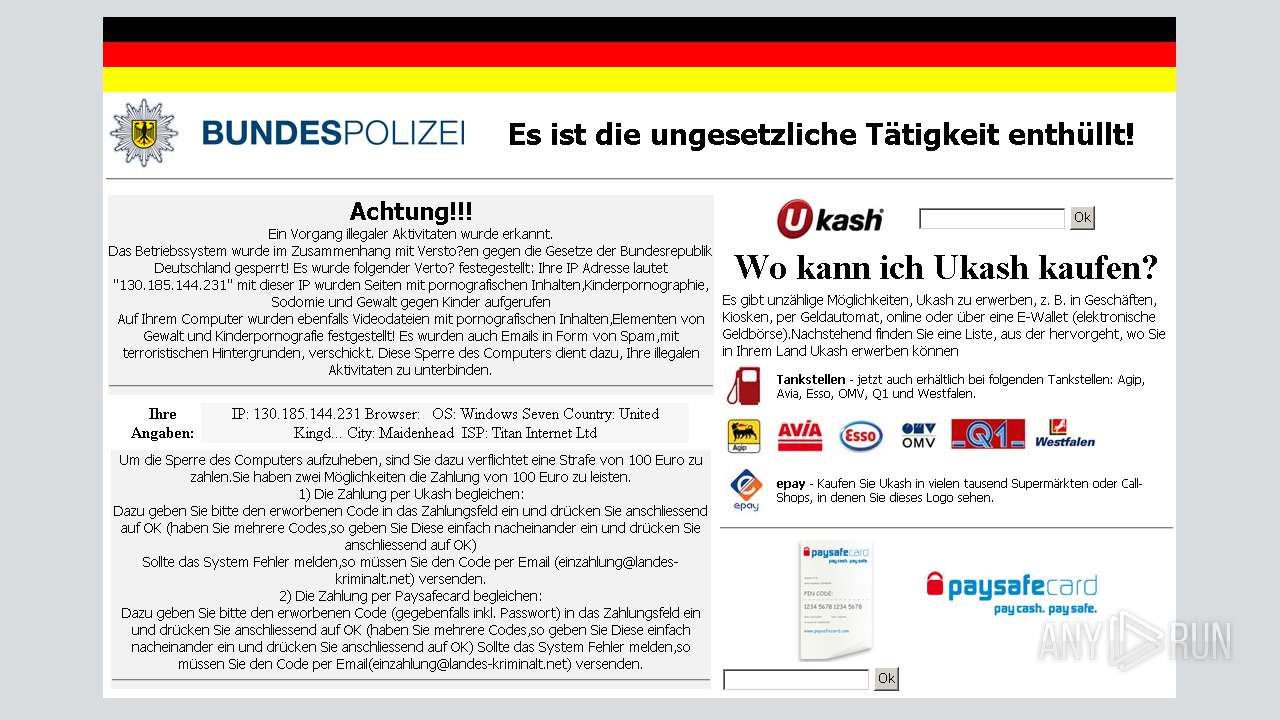
Checks for external IP
- mahmud.exe (PID: 664)
Starts itself from another location
- sample_54.exe (PID: 2900)
INFO
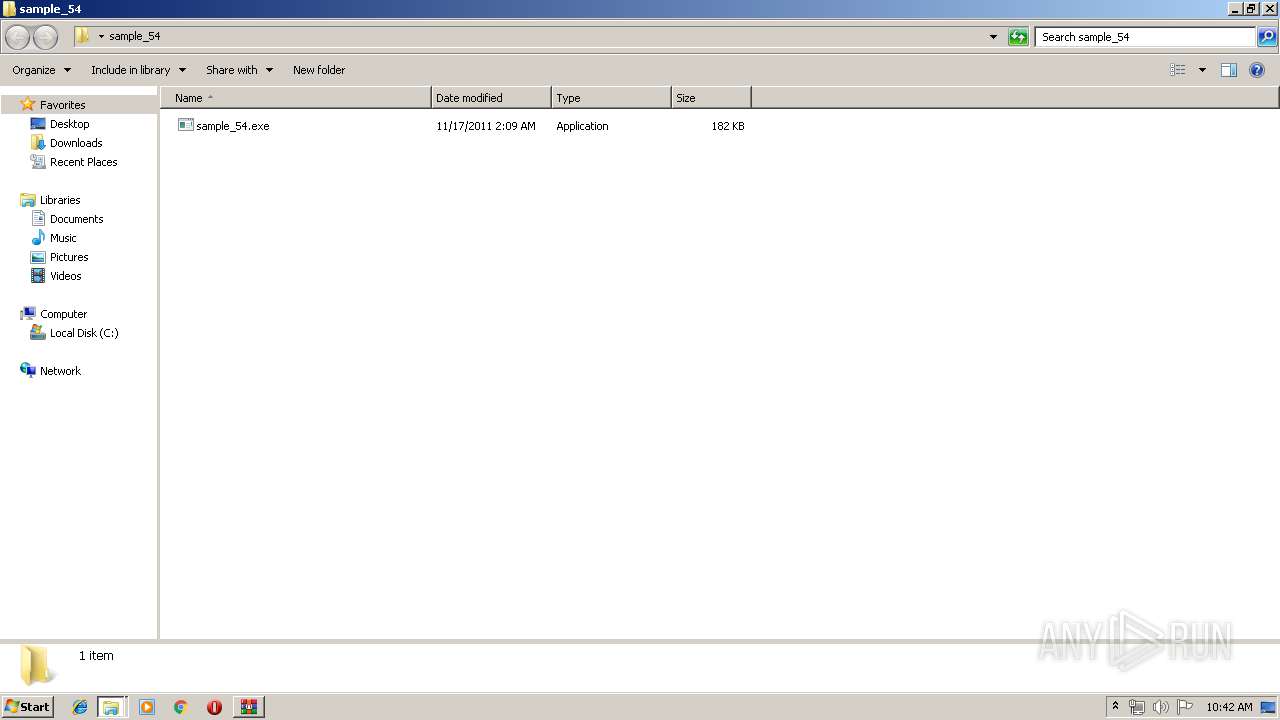
Manual execution by user
- sample_54.exe (PID: 2900)
- explorer.exe (PID: 1472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:05:01 18:48:22 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | sample_54/ |
Total processes
39
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Users\admin\AppData\Roaming\mahmud.exe" | C:\Users\admin\AppData\Roaming\mahmud.exe | sample_54.exe | ||||||||||||
User: admin Company: NEC Computers International Integrity Level: MEDIUM Description: Riggs Sub Faint Force Exit code: 0 Version: 7.8 Modules
| |||||||||||||||
| 1472 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
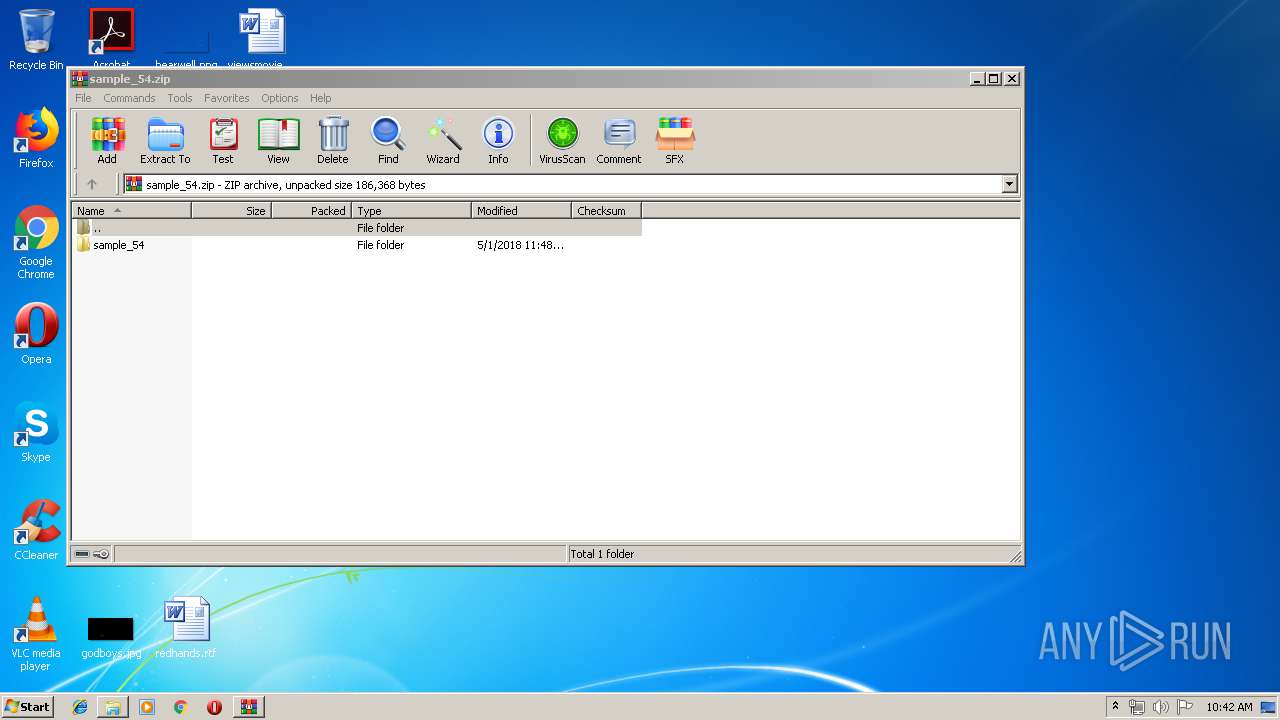
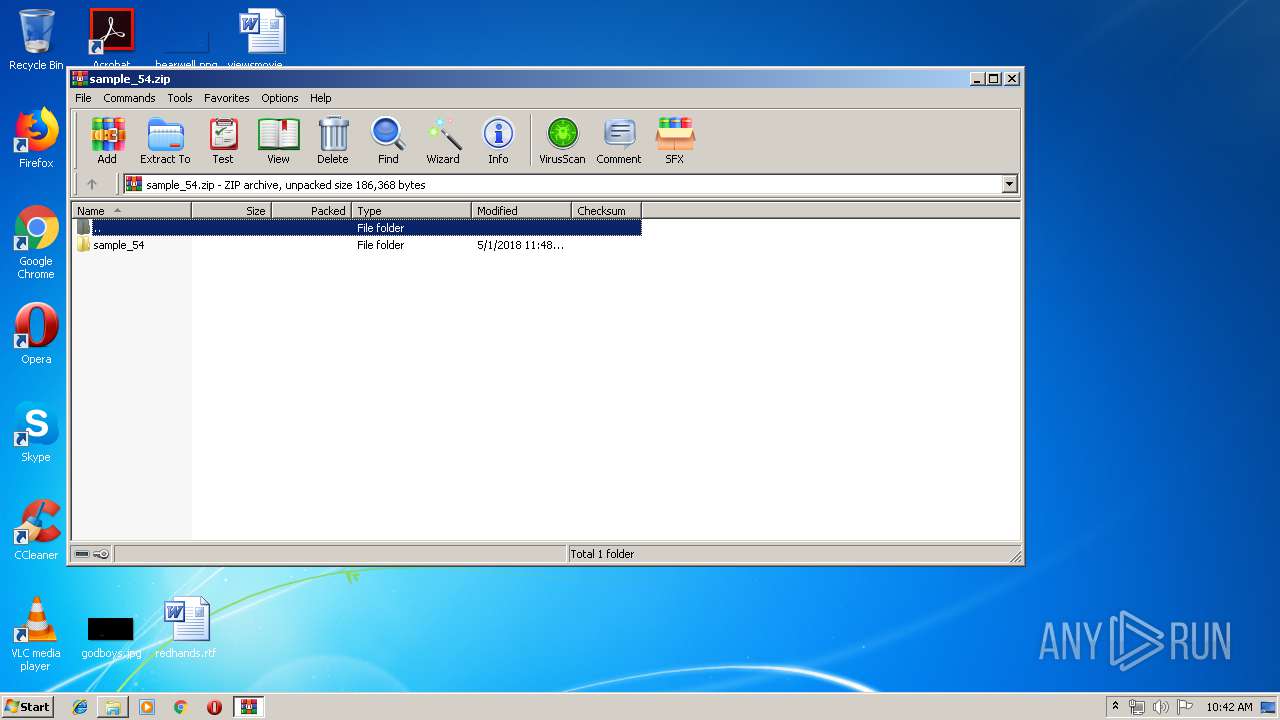
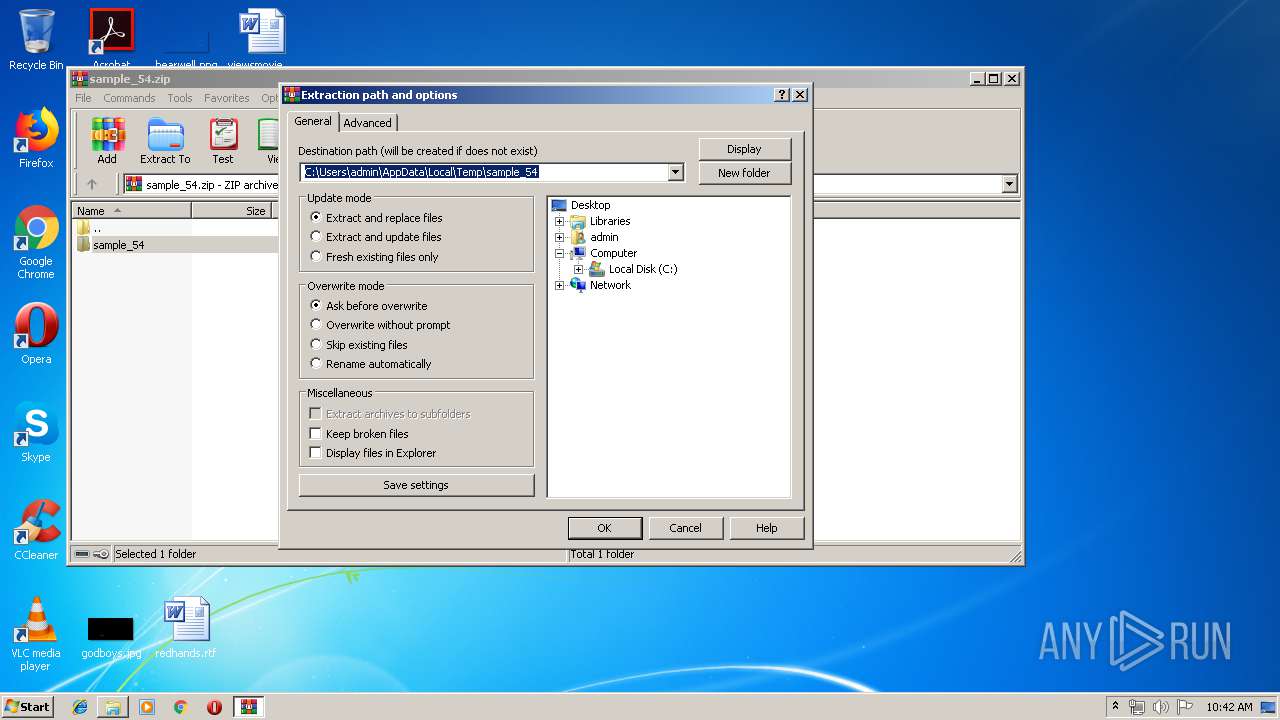
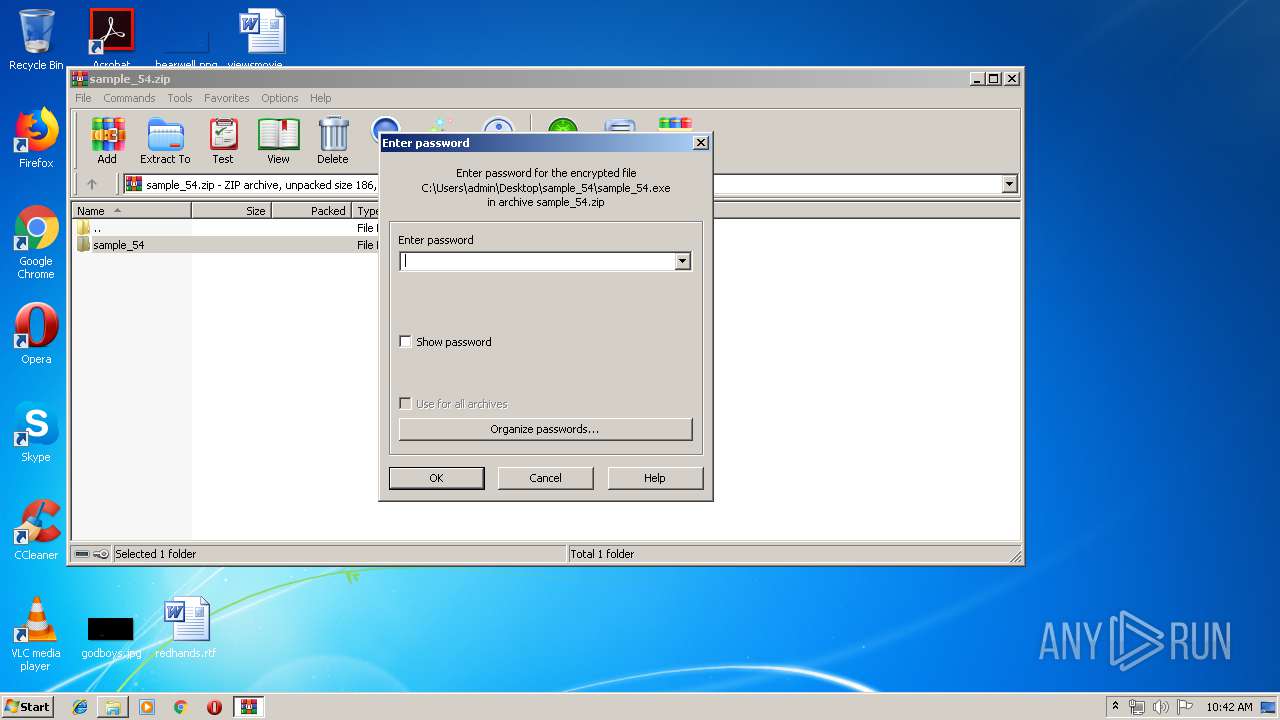
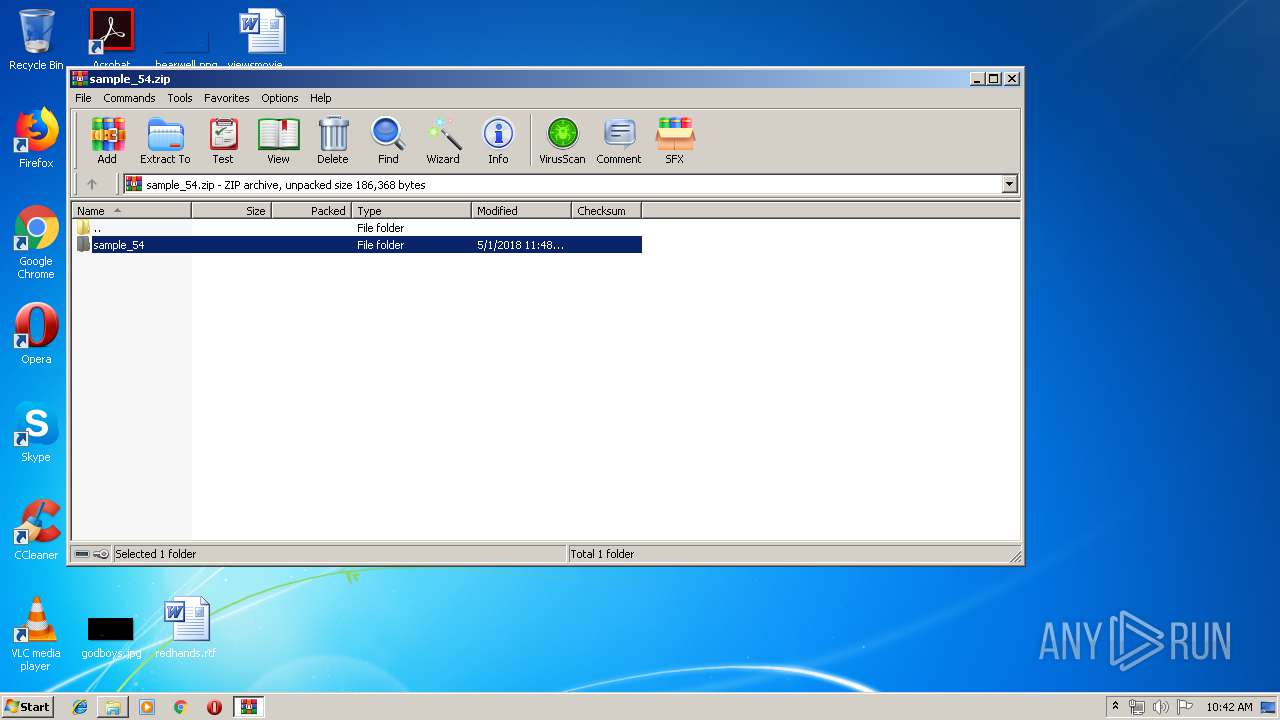
| 2124 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\sample_54.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2900 | "C:\Users\admin\Desktop\sample_54\sample_54.exe" | C:\Users\admin\Desktop\sample_54\sample_54.exe | explorer.exe | ||||||||||||
User: admin Company: NEC Computers International Integrity Level: MEDIUM Description: Riggs Sub Faint Force Exit code: 0 Version: 7.8 Modules
| |||||||||||||||
| 3416 | "C:\Windows\system32\cmd.exe" /c "for /L %i in (0,1,100000000) do (del "C:\Users\admin\Desktop\sample_54\sample_54.exe" && if not exist "C:\Users\admin\Desktop\sample_54\sample_54.exe" exit 1)" | C:\Windows\system32\cmd.exe | — | sample_54.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
901
Read events
867
Write events
34
Delete events
0
Modification events
| (PID) Process: | (2124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2124) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample_54.zip | |||
| (PID) Process: | (2124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (2124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
2
Suspicious files
0
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 664 | mahmud.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\ib2[1].txt | — | |
MD5:— | SHA256:— | |||
| 2900 | sample_54.exe | C:\Users\admin\AppData\Roaming\mahmud.exe | executable | |
MD5:FDE9986FE61AE7CE1D477C510D0B671E | SHA256:DC4A9B1AB1FEDDF13EF3AA0AA181D903014256D365BA93390C7B367D4B436B7E | |||
| 2124 | WinRAR.exe | C:\Users\admin\Desktop\sample_54\sample_54.exe | executable | |
MD5:FDE9986FE61AE7CE1D477C510D0B671E | SHA256:DC4A9B1AB1FEDDF13EF3AA0AA181D903014256D365BA93390C7B367D4B436B7E | |||
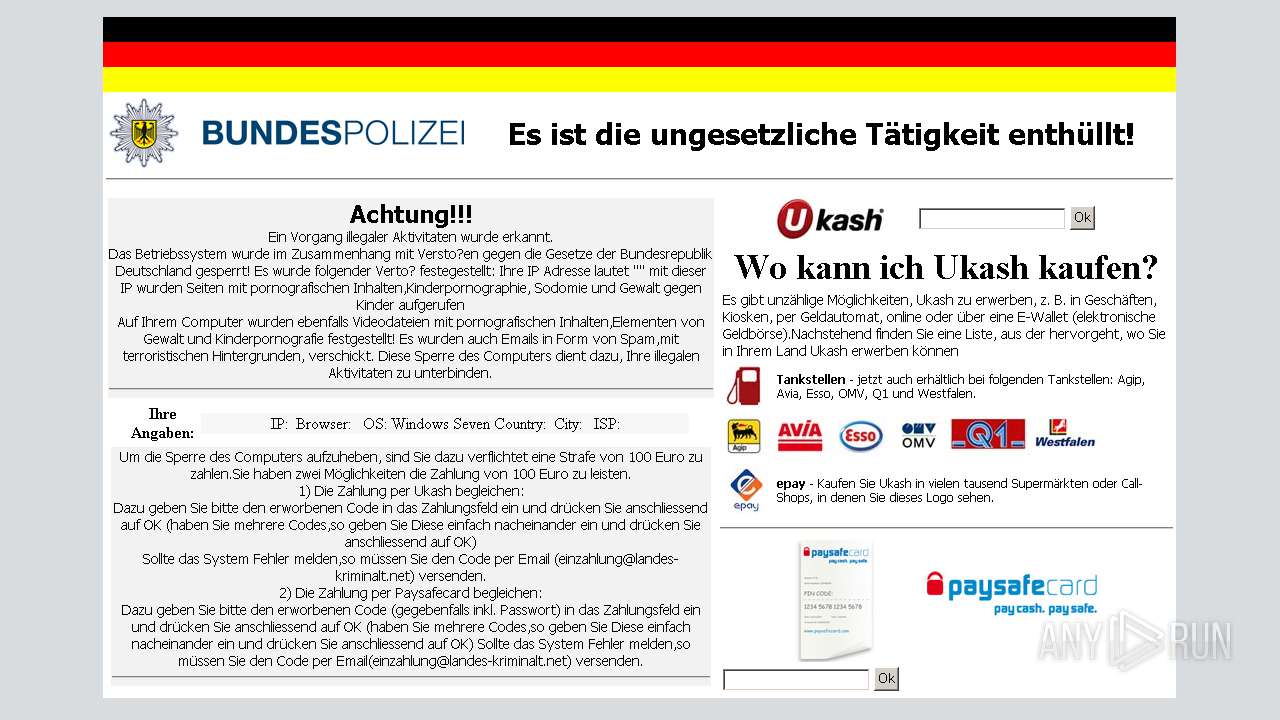
| 664 | mahmud.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\petrolstations[1] | image | |
MD5:DB956606BC0B1FC2DF846145C9540A6D | SHA256:599B7E358B2935EF7655F243BD6740867D2D0F4281ECC46505868045A4CD2948 | |||
| 664 | mahmud.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\ukash[1] | image | |
MD5:5C0DDE9B26AA79F81F848BDDC37CE473 | SHA256:7F5E254DD2ED4C447ADD6863E547DB0D40E9E912DCBFA9D81CBDF0443A193652 | |||
| 664 | mahmud.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\pay[1] | image | |
MD5:527A37488396E62995F76CF3487F8985 | SHA256:04FAC3F2D0743E0045F813AC49A207777268804BFADC0BA1DC15911C3292DF69 | |||
| 664 | mahmud.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\petrol[1] | image | |
MD5:E4E138DFC37B550ECBE1E0F5E87BCF4C | SHA256:AC32FC9FFDA439FAC9AB3F50EE2C7197B427E171450250CBF83F78CFF5DE93AD | |||
| 664 | mahmud.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\paysafe[1] | image | |
MD5:6567A5122FE1275B1AEEA76059B7501C | SHA256:FEFCB747EB01FB2C6F49666DC35E5A641C628F120C3EA2052975E30F707140E8 | |||
| 664 | mahmud.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\bpol_logo[1] | image | |
MD5:737A56206E245CC6E9DB01AA7E6DB088 | SHA256:43A747CE7AF8BBE3279E34FC90CED4F887DC99B39A8185BE142D6278D25DD62F | |||
| 664 | mahmud.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\main[1] | html | |
MD5:1AA4A8102F15E0EBB42DCC4A0BC81ACD | SHA256:136460859AFE66D6CBBEE4430B5661B52C690650B4415D5B8840E372A36CF974 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
2
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
664 | mahmud.exe | GET | 200 | 108.61.217.56:80 | http://tools.ip2location.com/ib2/ | US | html | 637 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
664 | mahmud.exe | 108.61.217.56:80 | tools.ip2location.com | Choopa, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
annner2y.com |
| unknown |
tools.ip2location.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
664 | mahmud.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup - ip2location.com |
664 | mahmud.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
1 ETPRO signatures available at the full report