| File name: | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_000172 |
| Full analysis: | https://app.any.run/tasks/55b0c736-c3fb-4217-a3b3-003c0f8fb895 |
| Verdict: | Malicious activity |
| Analysis date: | October 22, 2023, 17:21:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 579AD85EC10C4C5751FE4410F2C96AC6 |
| SHA1: | 59ABDFA654EDA10922EF6F37A1B2B7A4F59085CC |
| SHA256: | 9B2C6C1AB49A5FEEBA0ED653E54449EE52E391E949F71939827751D88814C8F3 |
| SSDEEP: | 49152:Ly+tHdY2vj6X/c3dG+t24+vqrlZlPBfXeu7dKolk:W+pd/L6xOWyTZ1XeuAolk |
MALICIOUS
Drops the executable file immediately after the start
- f_000172.exe (PID: 2752)
- f_000172.exe (PID: 3824)
- f_000172.tmp (PID: 3632)
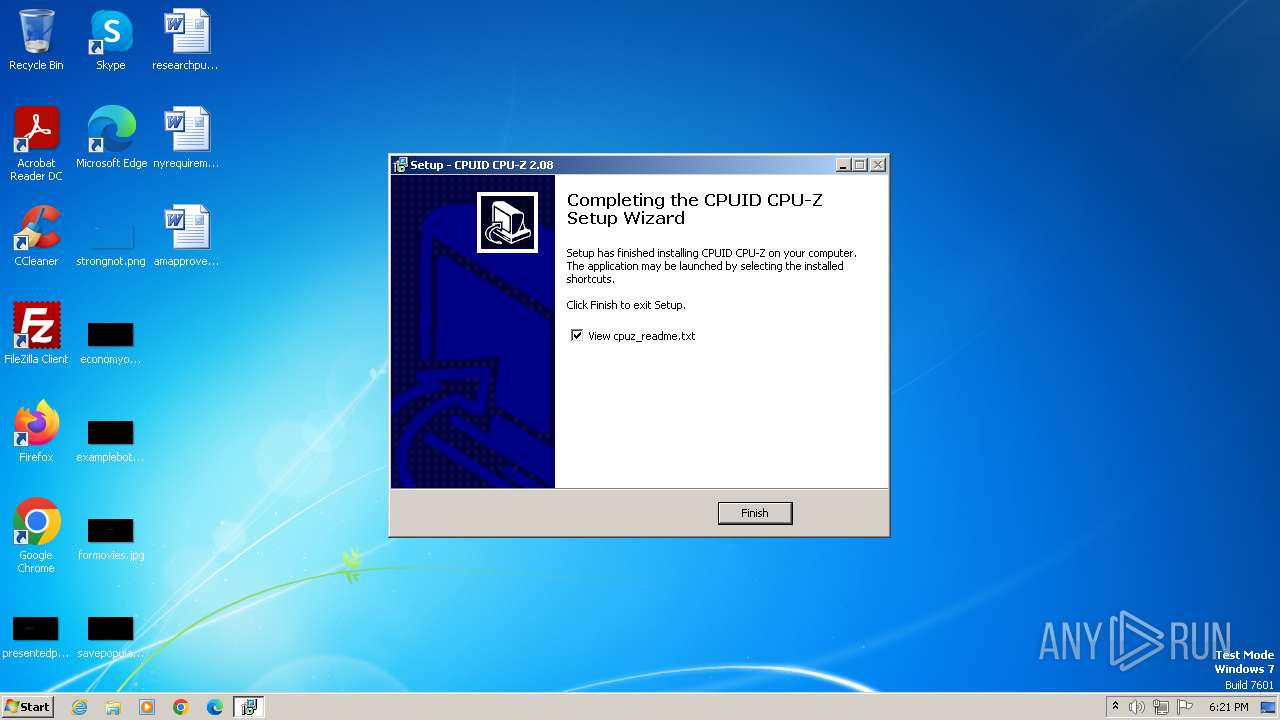
- cpuz.exe (PID: 3484)
Application was dropped or rewritten from another process
- cpuz.exe (PID: 3184)
- cpuz.exe (PID: 3484)
SUSPICIOUS
Reads the Windows owner or organization settings
- f_000172.tmp (PID: 3632)
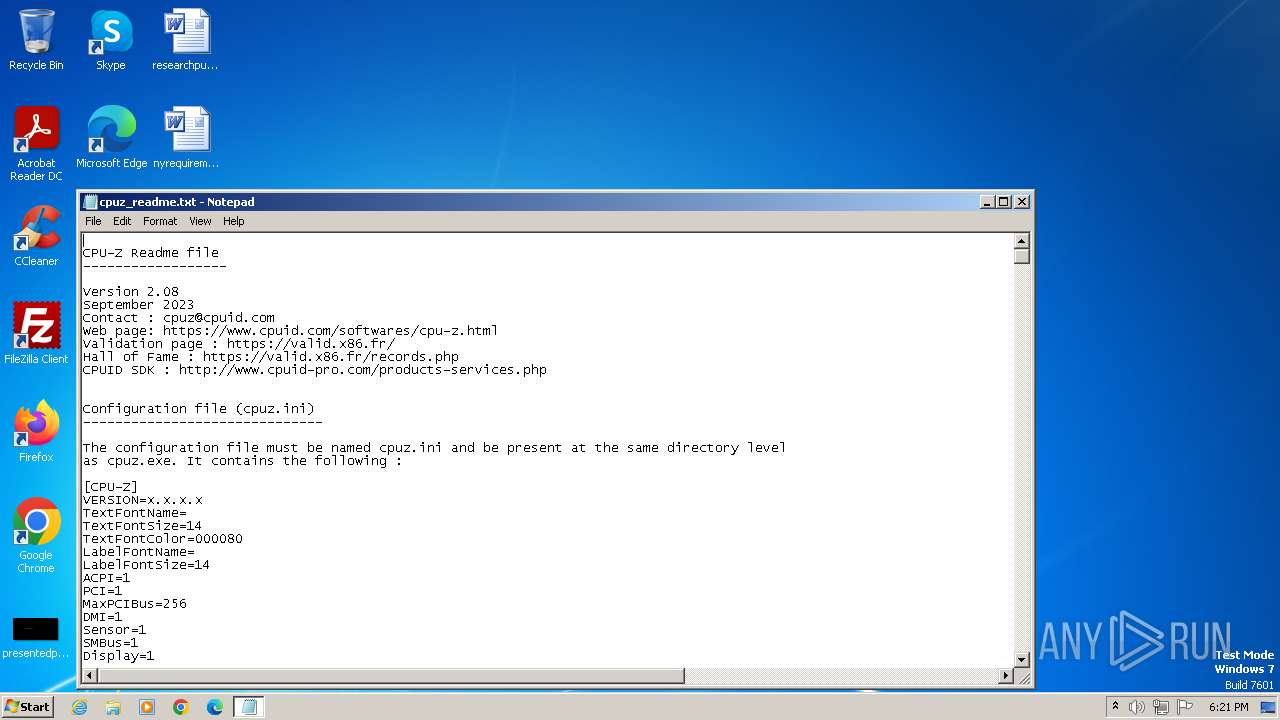
Start notepad (likely ransomware note)
- f_000172.tmp (PID: 2696)
Reads settings of System Certificates
- cpuz.exe (PID: 3484)
Reads the Internet Settings
- cpuz.exe (PID: 3484)
Drops a system driver (possible attempt to evade defenses)
- cpuz.exe (PID: 3484)
Checks Windows Trust Settings
- cpuz.exe (PID: 3484)
Reads security settings of Internet Explorer
- cpuz.exe (PID: 3484)
INFO
Checks supported languages
- f_000172.tmp (PID: 2696)
- f_000172.exe (PID: 2752)
- f_000172.exe (PID: 3824)
- f_000172.tmp (PID: 3632)
- cpuz.exe (PID: 3484)
Create files in a temporary directory
- f_000172.exe (PID: 3824)
- f_000172.exe (PID: 2752)
- cpuz.exe (PID: 3484)
Reads the computer name
- f_000172.tmp (PID: 2696)
- f_000172.tmp (PID: 3632)
- cpuz.exe (PID: 3484)
Application was dropped or rewritten from another process
- f_000172.tmp (PID: 3632)
- f_000172.tmp (PID: 2696)
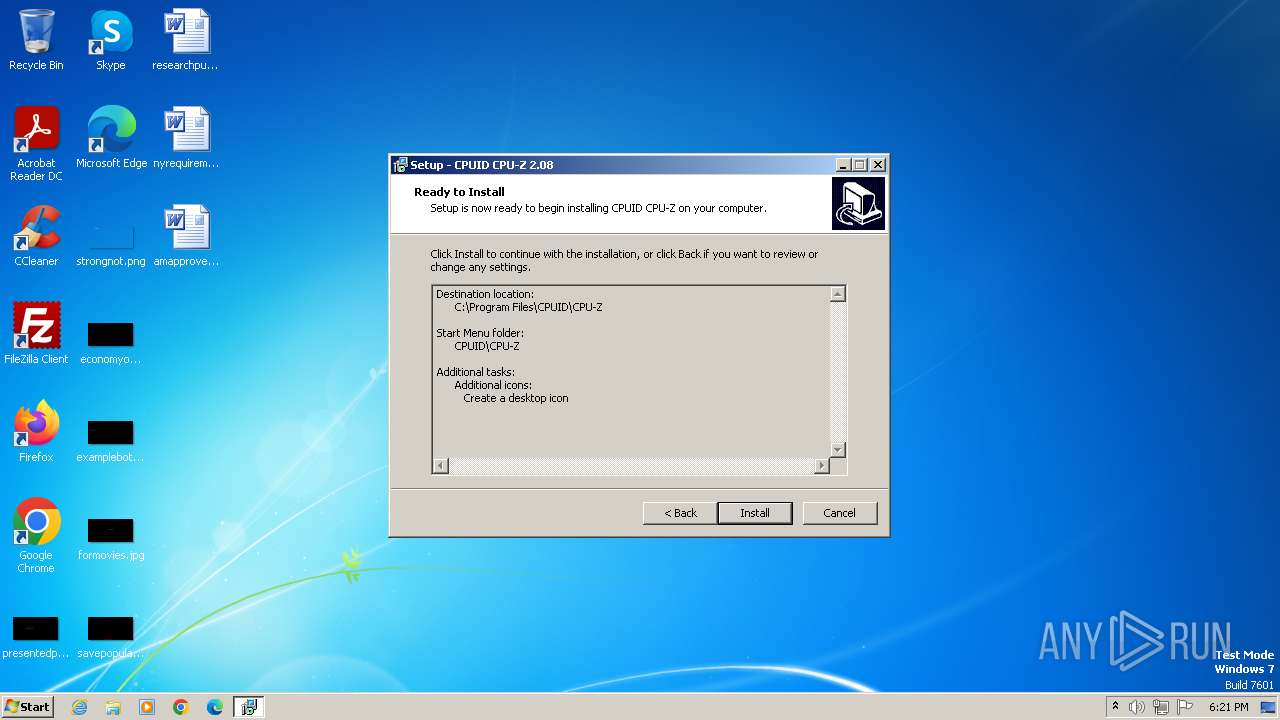
Creates files in the program directory
- f_000172.tmp (PID: 3632)
Manual execution by a user
- cpuz.exe (PID: 3184)
- cpuz.exe (PID: 3484)
Reads Environment values
- cpuz.exe (PID: 3484)
Creates files or folders in the user directory
- cpuz.exe (PID: 3484)
Checks proxy server information
- cpuz.exe (PID: 3484)
Reads the machine GUID from the registry
- cpuz.exe (PID: 3484)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| ProductVersion: | 2.08 |
|---|---|
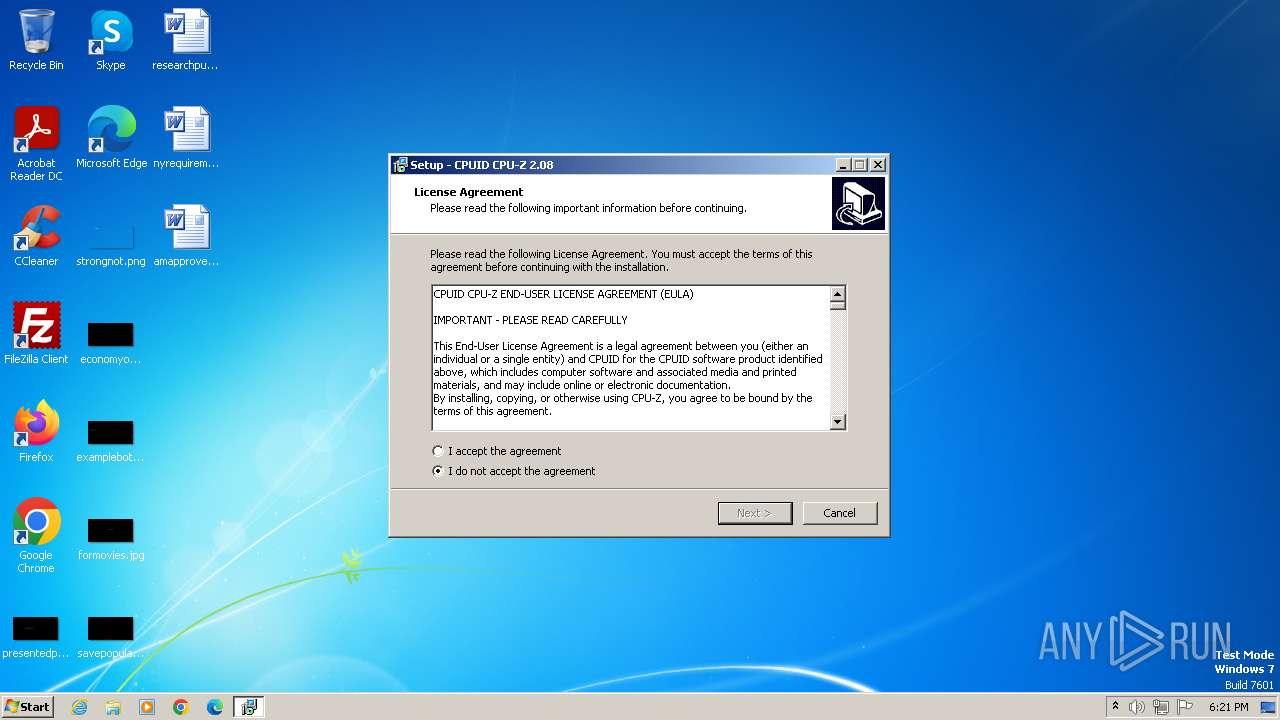
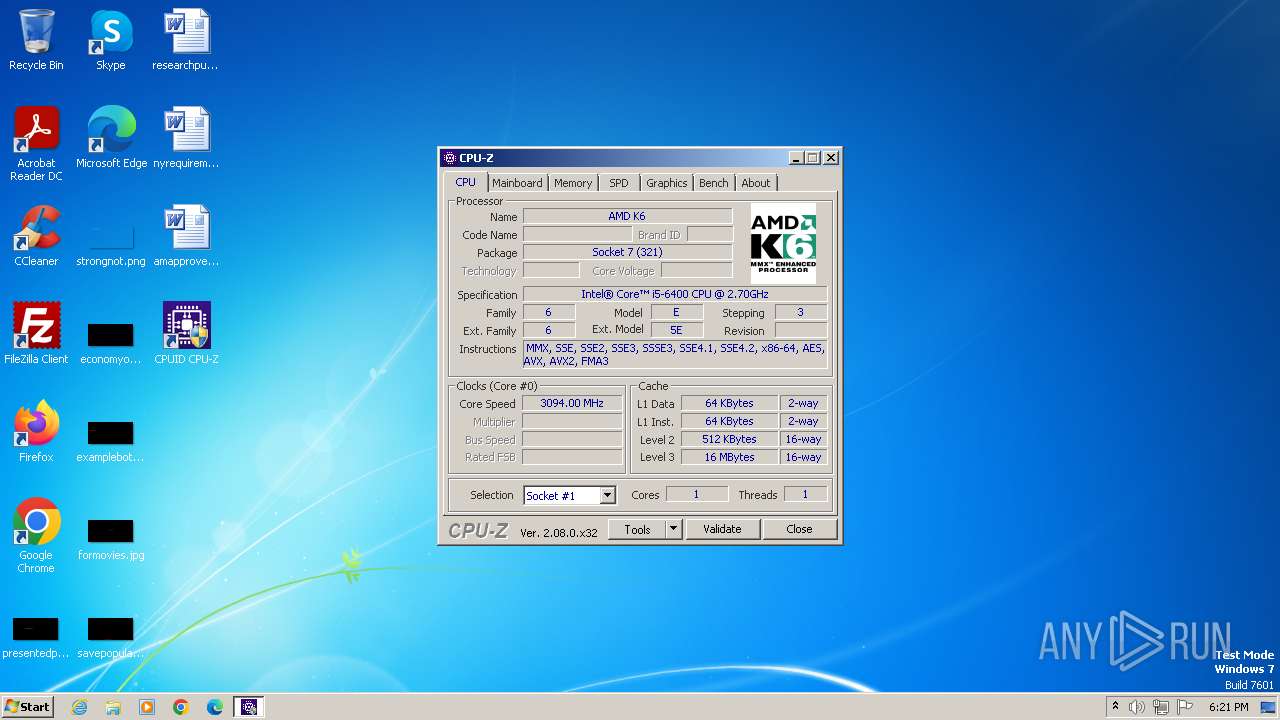
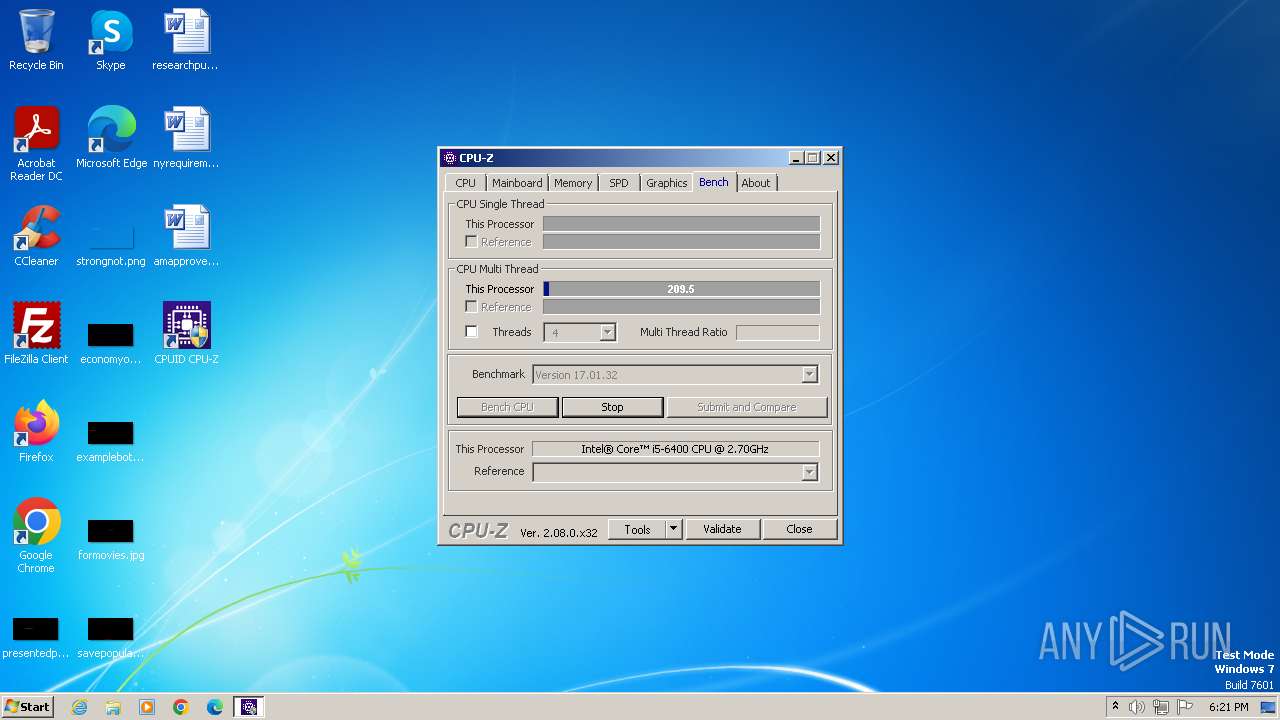
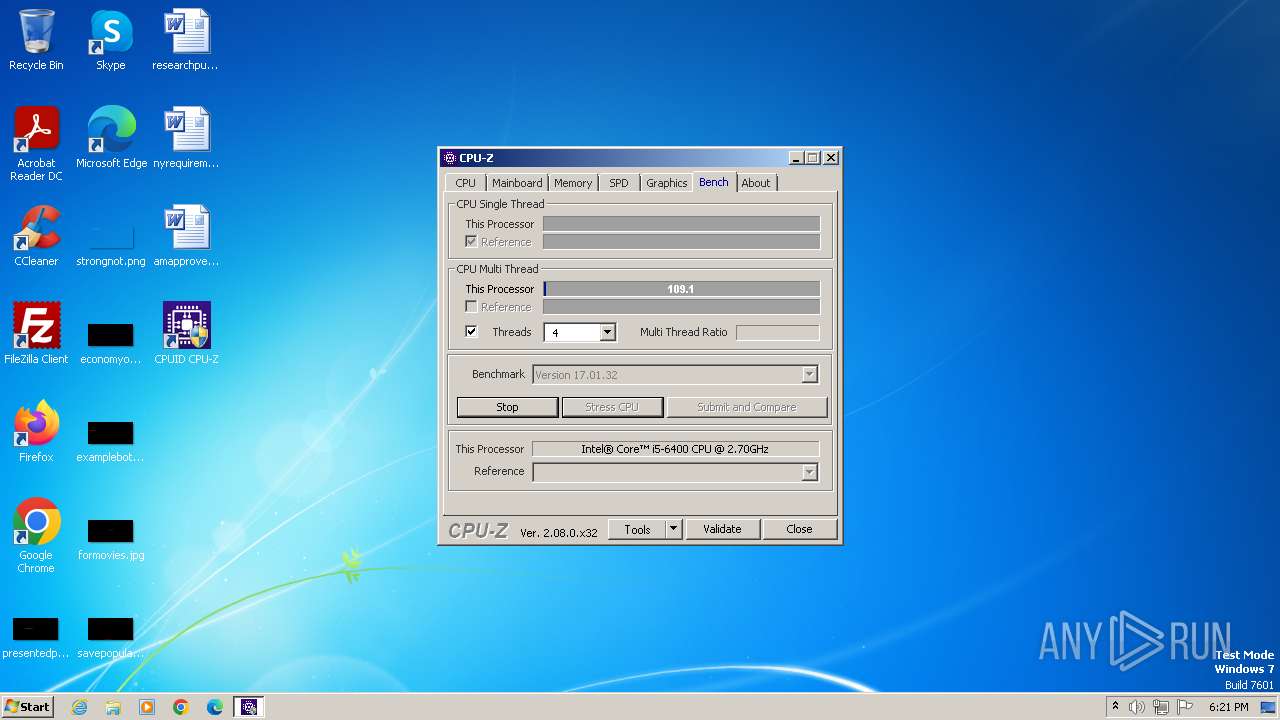
| ProductName: | CPUID CPU-Z |
| LegalCopyright: | |
| FileVersion: | |
| FileDescription: | CPUID CPU-Z Setup |
| CompanyName: | CPUID, Inc. |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 0.0.0.0 |
| FileVersionNumber: | 0.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 1 |
| EntryPoint: | 0xaad0 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 17920 |
| CodeSize: | 41984 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Total processes
51
Monitored processes
7
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2696 | "C:\Users\admin\AppData\Local\Temp\is-KRLK7.tmp\f_000172.tmp" /SL5="$602F8,1938476,58368,C:\Users\admin\AppData\Local\Temp\f_000172.exe" | C:\Users\admin\AppData\Local\Temp\is-KRLK7.tmp\f_000172.tmp | — | f_000172.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2752 | "C:\Users\admin\AppData\Local\Temp\f_000172.exe" | C:\Users\admin\AppData\Local\Temp\f_000172.exe | — | explorer.exe | |||||||||||
User: admin Company: CPUID, Inc. Integrity Level: MEDIUM Description: CPUID CPU-Z Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3184 | "C:\Program Files\CPUID\CPU-Z\cpuz.exe" | C:\Program Files\CPUID\CPU-Z\cpuz.exe | — | explorer.exe | |||||||||||
User: admin Company: CPUID Integrity Level: MEDIUM Description: CPU-Z Application Exit code: 3221226540 Version: 2, 0, 8, 0 Modules
| |||||||||||||||
| 3256 | "C:\Windows\system32\NOTEPAD.EXE" C:\Program Files\CPUID\CPU-Z\cpuz_readme.txt | C:\Windows\System32\notepad.exe | — | f_000172.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3484 | "C:\Program Files\CPUID\CPU-Z\cpuz.exe" | C:\Program Files\CPUID\CPU-Z\cpuz.exe | explorer.exe | ||||||||||||
User: admin Company: CPUID Integrity Level: HIGH Description: CPU-Z Application Exit code: 0 Version: 2, 0, 8, 0 Modules
| |||||||||||||||
| 3632 | "C:\Users\admin\AppData\Local\Temp\is-RNUE1.tmp\f_000172.tmp" /SL5="$60300,1938476,58368,C:\Users\admin\AppData\Local\Temp\f_000172.exe" /SPAWNWND=$4036C /NOTIFYWND=$602F8 | C:\Users\admin\AppData\Local\Temp\is-RNUE1.tmp\f_000172.tmp | — | f_000172.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 3824 | "C:\Users\admin\AppData\Local\Temp\f_000172.exe" /SPAWNWND=$4036C /NOTIFYWND=$602F8 | C:\Users\admin\AppData\Local\Temp\f_000172.exe | f_000172.tmp | ||||||||||||
User: admin Company: CPUID, Inc. Integrity Level: HIGH Description: CPUID CPU-Z Setup Exit code: 0 Version: Modules
| |||||||||||||||
Total events
6 993
Read events
6 961
Write events
26
Delete events
6
Modification events
| (PID) Process: | (3632) f_000172.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFilesHash |
Value: 5F2C04D26D286AB2E9D5786F6DFCB03B2A7CF5DEEF0A245F08B37FD768172A92 | |||
| (PID) Process: | (3632) f_000172.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFiles0000 |
Value: C:\Program Files\CPUID\CPU-Z\cpuz.exe | |||
| (PID) Process: | (3632) f_000172.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3632) f_000172.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | SessionHash |
Value: 6C5DAA00761576602990C57E4DFBC13A06E4145111DC6D24765768B81D91F1F8 | |||
| (PID) Process: | (3632) f_000172.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Owner |
Value: 300E0000C067F6260C05DA01 | |||
| (PID) Process: | (3632) f_000172.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3484) cpuz.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3484) cpuz.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000056010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3484) cpuz.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3484) cpuz.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
7
Suspicious files
16
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3824 | f_000172.exe | C:\Users\admin\AppData\Local\Temp\is-RNUE1.tmp\f_000172.tmp | executable | |
MD5:77B6D18B219D145C73F779D0D82F6BD0 | SHA256:AAB8B17924B8F250D1CA477FA705D342BF620FF5864EBBC0B5E5D177C43A1743 | |||
| 3632 | f_000172.tmp | C:\Program Files\CPUID\CPU-Z\is-5JF9Q.tmp | text | |
MD5:B02BD9A26ACA56C65E516E1E0621A0E0 | SHA256:92808E357B94A1D955D8D7C112C0D3DD46DAA50FAB6167E273B295C288C3E1FC | |||
| 3632 | f_000172.tmp | C:\Program Files\CPUID\CPU-Z\cpuz_readme.txt | text | |
MD5:6F17A8C4A1307E68515CBFE99AA94ECD | SHA256:2645CC947875658717E2B8C8E0DBAD80A09E8CB8AB80D26595CA06C73CF73542 | |||
| 3632 | f_000172.tmp | C:\Program Files\CPUID\CPU-Z\cpuz.exe | executable | |
MD5:AED8A6FC0E79C6EE1F073BAAFF2F5FBE | SHA256:E3FD159588488CC9D36B5EFD1904AAFC420397E3D2857EF12CAA3EA7DFED7EB9 | |||
| 3632 | f_000172.tmp | C:\Program Files\CPUID\CPU-Z\is-76UMQ.tmp | text | |
MD5:E44F547A3378E46171D56A8A80CE9A40 | SHA256:AB086F912FF00C8C3AB42B8CA6D01395A96ECA253FAE4B186A3CA72C230B66B0 | |||
| 3632 | f_000172.tmp | C:\Program Files\CPUID\CPU-Z\cpuz_eula.txt | text | |
MD5:E44F547A3378E46171D56A8A80CE9A40 | SHA256:AB086F912FF00C8C3AB42B8CA6D01395A96ECA253FAE4B186A3CA72C230B66B0 | |||
| 3632 | f_000172.tmp | C:\Program Files\CPUID\CPU-Z\unins000.exe | executable | |
MD5:77B6D18B219D145C73F779D0D82F6BD0 | SHA256:AAB8B17924B8F250D1CA477FA705D342BF620FF5864EBBC0B5E5D177C43A1743 | |||
| 3632 | f_000172.tmp | C:\Program Files\CPUID\CPU-Z\is-UHGVL.tmp | executable | |
MD5:77B6D18B219D145C73F779D0D82F6BD0 | SHA256:AAB8B17924B8F250D1CA477FA705D342BF620FF5864EBBC0B5E5D177C43A1743 | |||
| 3632 | f_000172.tmp | C:\Program Files\CPUID\CPU-Z\is-FICFF.tmp | text | |
MD5:6F17A8C4A1307E68515CBFE99AA94ECD | SHA256:2645CC947875658717E2B8C8E0DBAD80A09E8CB8AB80D26595CA06C73CF73542 | |||
| 3632 | f_000172.tmp | C:\Users\Public\Desktop\CPUID CPU-Z.lnk | binary | |
MD5:A52B7229BA4AA2F2350F9BDEA26F1F67 | SHA256:DDDCA26FDB59FCC88A3A9941FA68535E1F7CDB6029DF3BED3DE846091313E03E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
6
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3484 | cpuz.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?e88945892a42e25c | unknown | compressed | 61.6 Kb | unknown |
3484 | cpuz.exe | GET | 200 | 23.212.210.158:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
3484 | cpuz.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ddeec13fa64f29b8 | unknown | compressed | 4.66 Kb | unknown |
3484 | cpuz.exe | GET | 200 | 184.24.77.46:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgOtcy3iHUtqqXerqZ8ymWI%2FoA%3D%3D | unknown | binary | 503 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3484 | cpuz.exe | 195.154.81.43:443 | download.cpuid.com | Online S.a.s. | FR | unknown |
3484 | cpuz.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
3484 | cpuz.exe | 23.212.210.158:80 | x1.c.lencr.org | AKAMAI-AS | AU | unknown |
3484 | cpuz.exe | 184.24.77.46:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.cpuid.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |