| File name: | lc.exe |
| Full analysis: | https://app.any.run/tasks/9447fa62-f24f-4270-a195-5ad095701601 |
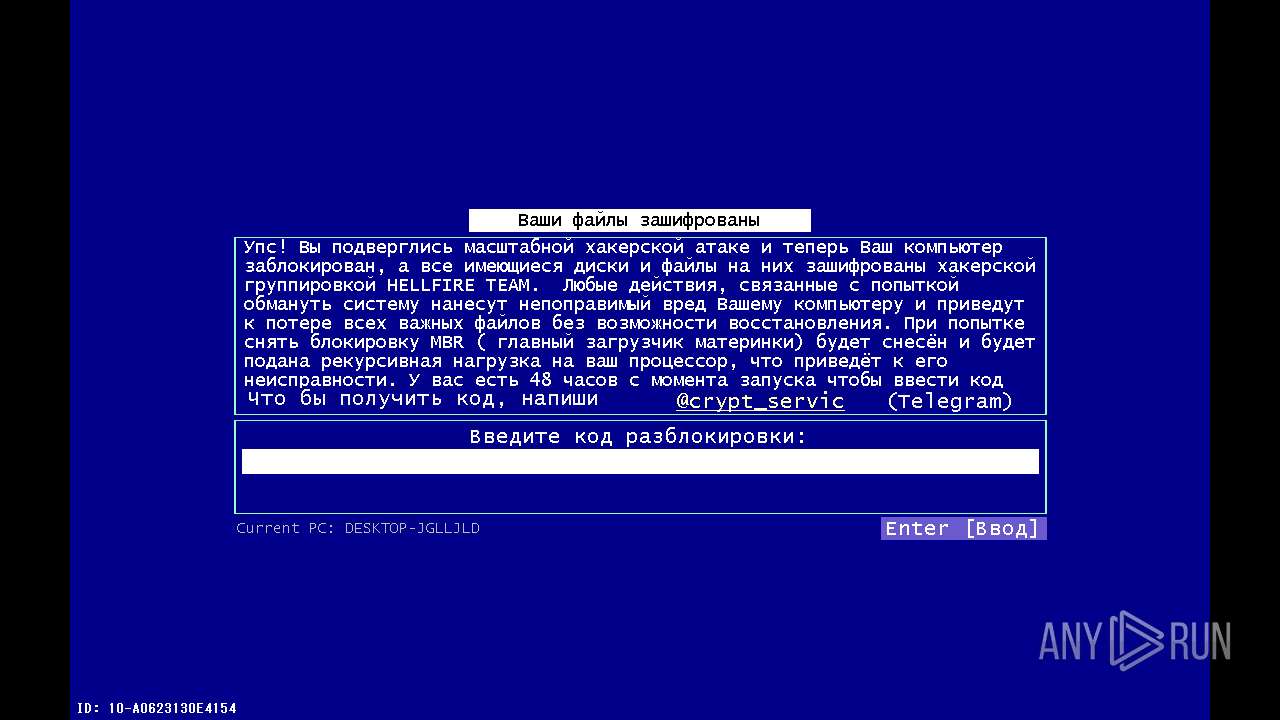
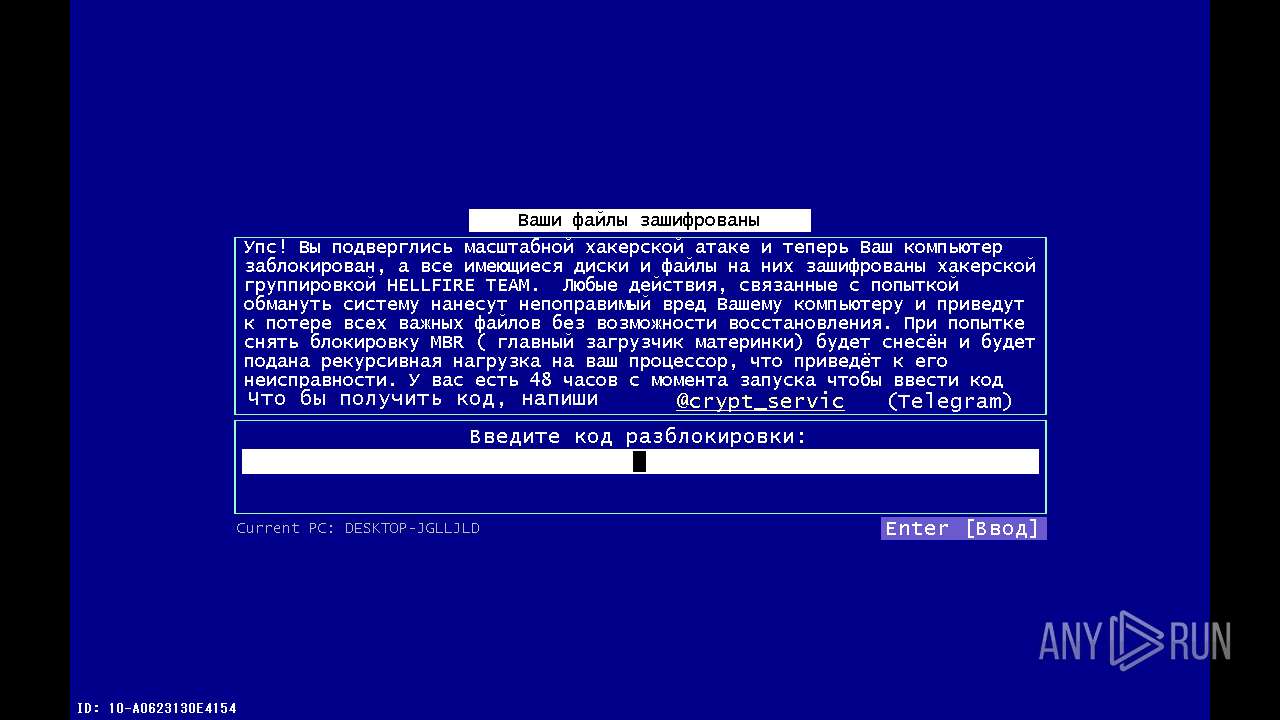
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2024, 06:23:01 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 7924C0F21738FAB05F61102C0CAF3DA2 |
| SHA1: | 09E6FD5797381EEB9EC60D5214F2932154636247 |
| SHA256: | 9B29F5A1F0B6C270C90B343F4C6D0E0843201D687068DC5273CBF5074083609F |
| SSDEEP: | 3072:sRuz2/auIDD6u4AFHNbJFoUZXzUCpM69/KImQi/6ebW6kTgwj3:FC/auMkAFtbJ9zUCpM69/KImQi/6ebl |
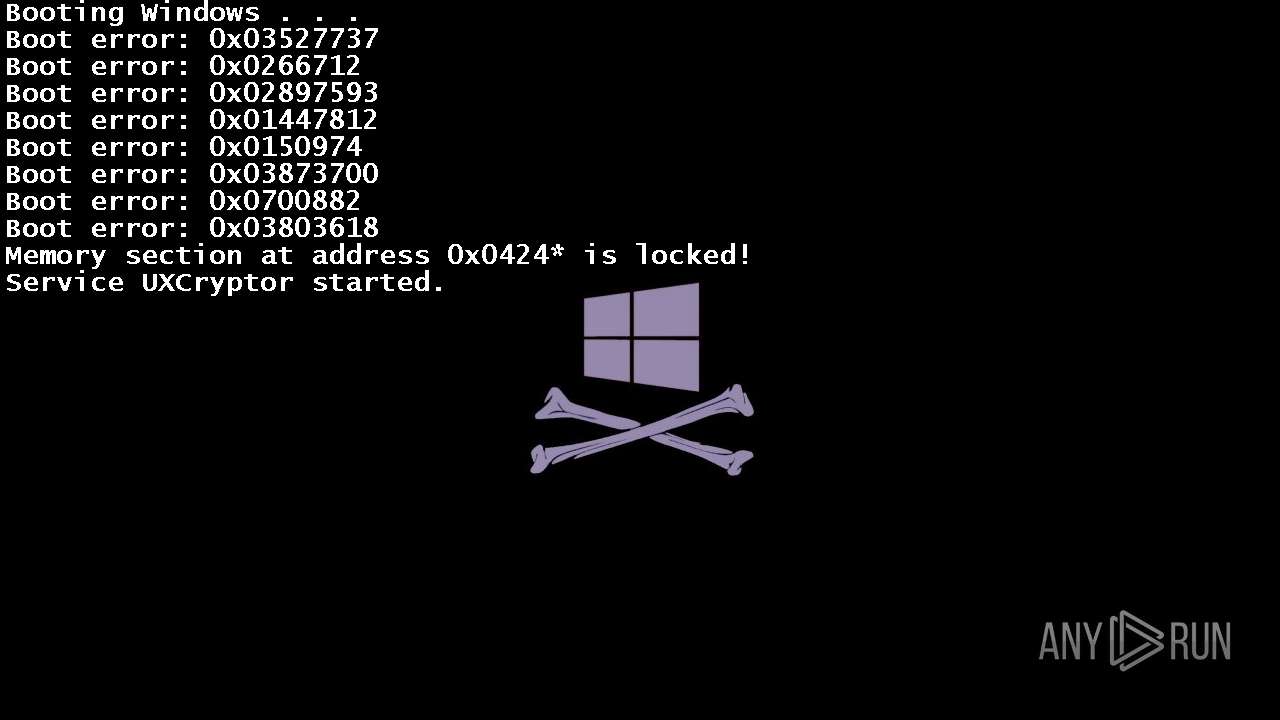
MALICIOUS
Drops the executable file immediately after the start
- lc.exe (PID: 452)
Changes the login/logoff helper path in the registry
- lc.exe (PID: 452)
Changes the autorun value in the registry
- lc.exe (PID: 452)
SUSPICIOUS
Starts CMD.EXE for commands execution
- lc.exe (PID: 452)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 3580)
Uses TASKKILL.EXE to kill process
- lc.exe (PID: 452)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 5096)
- cmd.exe (PID: 3908)
- cmd.exe (PID: 2272)
- cmd.exe (PID: 3580)
- cmd.exe (PID: 2860)
INFO
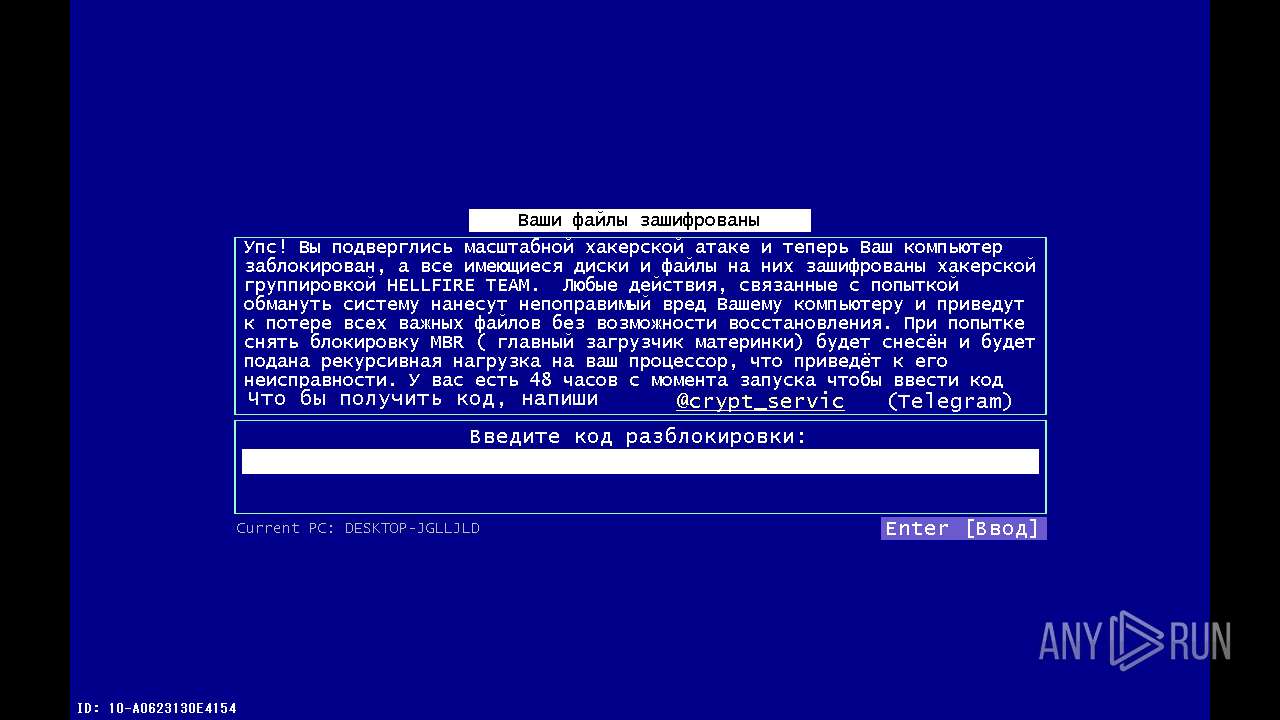
Reads the computer name
- lc.exe (PID: 452)
Reads the machine GUID from the registry
- lc.exe (PID: 452)
Checks supported languages
- lc.exe (PID: 452)
Create files in a temporary directory
- lc.exe (PID: 452)
.NET Reactor protector has been detected
- lc.exe (PID: 452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:12:02 14:42:19+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 182272 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e72e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 0.0.0.0 |
| InternalName: | lc.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | lc.exe |
| ProductName: | - |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
143
Monitored processes
23
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 452 | "C:\Users\admin\Desktop\lc.exe" | C:\Users\admin\Desktop\lc.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 0.0.0.0 Modules
| |||||||||||||||
| 1048 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1220 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2120 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
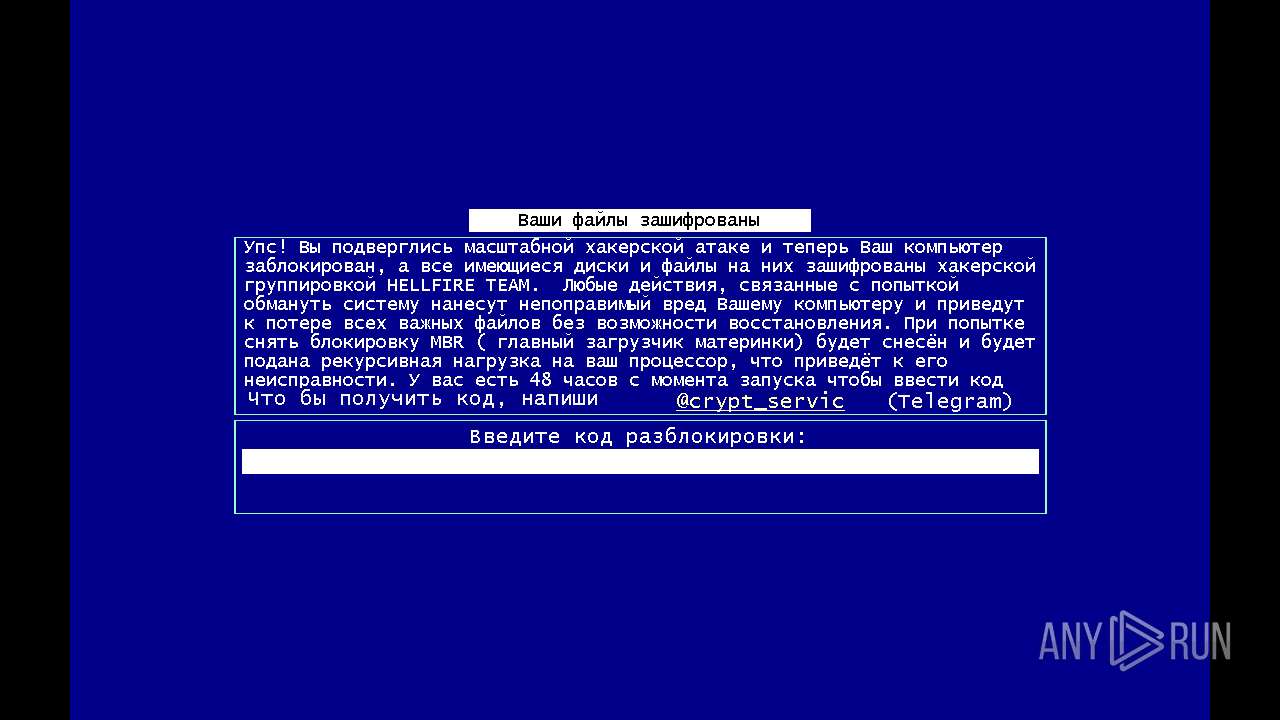
| 2272 | cmd.exe /c cd "%userprofile%\documents"&attrib +h +s +r +i /D & echo [%RANDOM%] Ooops! Your files are encrypted by the CryptoBytes hacker group! Telegram for contact: @yes_u_are_hacked 1>info-0v92.txt & attrib -h +s +r info-0v92.txt | C:\Windows\System32\cmd.exe | — | lc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2392 | attrib +h +s +r +i /D | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2556 | attrib -h +s +r info-0v92.txt | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2848 | attrib -h +s +r info-0v92.txt | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2860 | cmd.exe /c cd "%userprofile%"&attrib +h +s +r +i /D & echo [%RANDOM%] Ooops! Your files are encrypted by the CryptoBytes hacker group! Telegram for contact: @yes_u_are_hacked 1>info-0v92.txt & attrib -h +s +r info-0v92.txt | C:\Windows\System32\cmd.exe | — | lc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 808
Read events
1 790
Write events
18
Delete events
0
Modification events
| (PID) Process: | (452) lc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | WindowsInstaller |
Value: "C:\Users\admin\Desktop\lc.exe" -startup | |||
| (PID) Process: | (452) lc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MSEdgeUpdateX |
Value: "C:\Users\admin\Desktop\lc.exe" | |||
| (PID) Process: | (452) lc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | System3264Wow |
Value: "C:\Users\admin\Desktop\lc.exe" --init | |||
| (PID) Process: | (452) lc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | OneDrive10293 |
Value: "C:\Users\admin\Desktop\lc.exe" /setup | |||
| (PID) Process: | (452) lc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | WINDOWS |
Value: "C:\Users\admin\Desktop\lc.exe" --wininit | |||
| (PID) Process: | (452) lc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Shell |
Value: "C:\Users\admin\Desktop\lc.exe" | |||
| (PID) Process: | (452) lc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\RunMRU |
| Operation: | write | Name: | a |
Value: YOU ARE HACKED!\1 | |||
| (PID) Process: | (452) lc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\RunMRU |
| Operation: | write | Name: | b |
Value: HAHAHAHAHAHAHA\1 | |||
| (PID) Process: | (452) lc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\RunMRU |
| Operation: | write | Name: | c |
Value: winlocker.ru\1 | |||
| (PID) Process: | (452) lc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\RunMRU |
| Operation: | write | Name: | MRUList |
Value: abc | |||
Executable files
0
Suspicious files
0
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2272 | cmd.exe | C:\Users\admin\Documents\info-0v92.txt | text | |
MD5:9E72F7DEF34B5123DB17BB695B93C6F3 | SHA256:937493F186EA9FD938E1ED53874869FE917C3AF78C3C72A1530E2E29541C2B98 | |||
| 2860 | cmd.exe | C:\Users\admin\info-0v92.txt | text | |
MD5:9E72F7DEF34B5123DB17BB695B93C6F3 | SHA256:937493F186EA9FD938E1ED53874869FE917C3AF78C3C72A1530E2E29541C2B98 | |||
| 3908 | cmd.exe | C:\Users\admin\Downloads\info-0v92.txt | text | |
MD5:9E72F7DEF34B5123DB17BB695B93C6F3 | SHA256:937493F186EA9FD938E1ED53874869FE917C3AF78C3C72A1530E2E29541C2B98 | |||
| 5096 | cmd.exe | C:\Users\admin\Desktop\info-0v92.txt | text | |
MD5:9E72F7DEF34B5123DB17BB695B93C6F3 | SHA256:937493F186EA9FD938E1ED53874869FE917C3AF78C3C72A1530E2E29541C2B98 | |||
| 452 | lc.exe | C:\Users\admin\AppData\Local\Temp\$unlocker_id.ux-cryptobytes | text | |
MD5:99244073E9931D740C19F2BB0E5F3889 | SHA256:9512E6F8351B8BDFAA8441D65F547835C8616B03866CF9A45F5944C711886455 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
31
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2052 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4392 | svchost.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3776 | RUXIMICS.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3776 | RUXIMICS.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4392 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.52.64.200:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | unknown | binary | 9 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4392 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
3776 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2052 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 104.126.37.160:443 | — | Akamai International B.V. | DE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4392 | svchost.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
3776 | RUXIMICS.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
2052 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
3776 | RUXIMICS.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |