| File name: | lc.exe |
| Full analysis: | https://app.any.run/tasks/355a92b3-9b1f-43d5-bd58-e59ba5fc0fb2 |
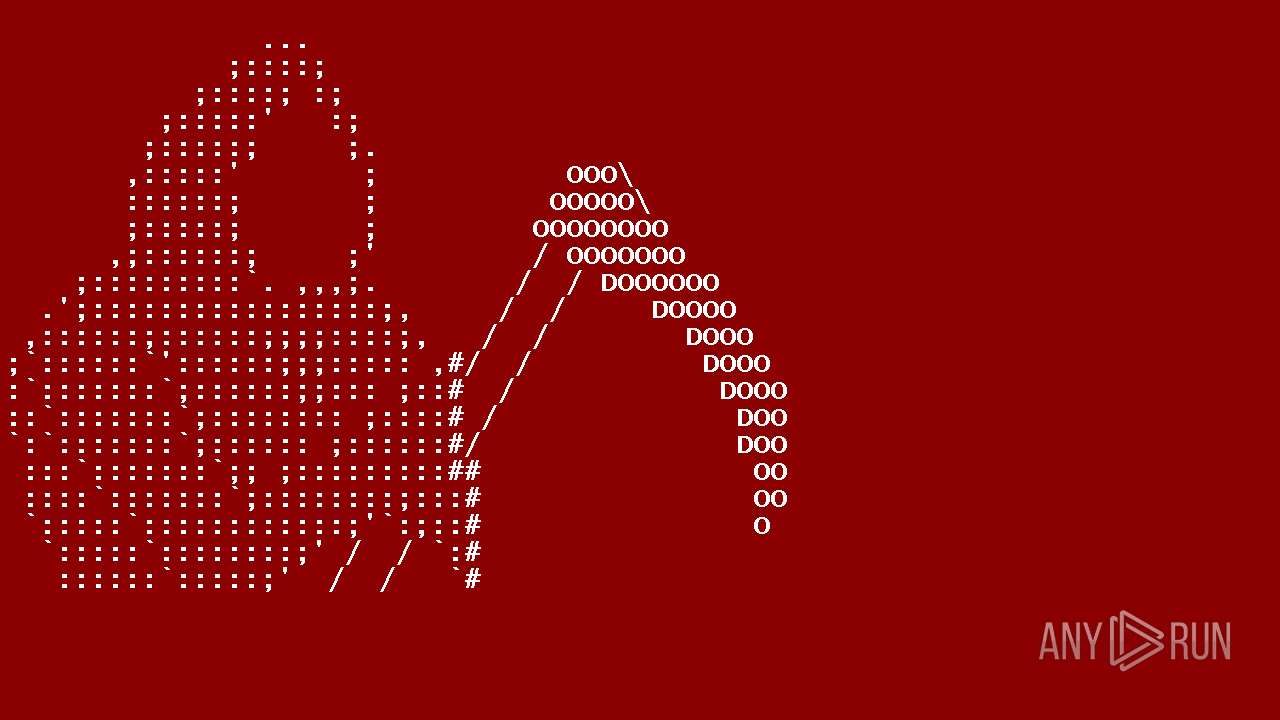
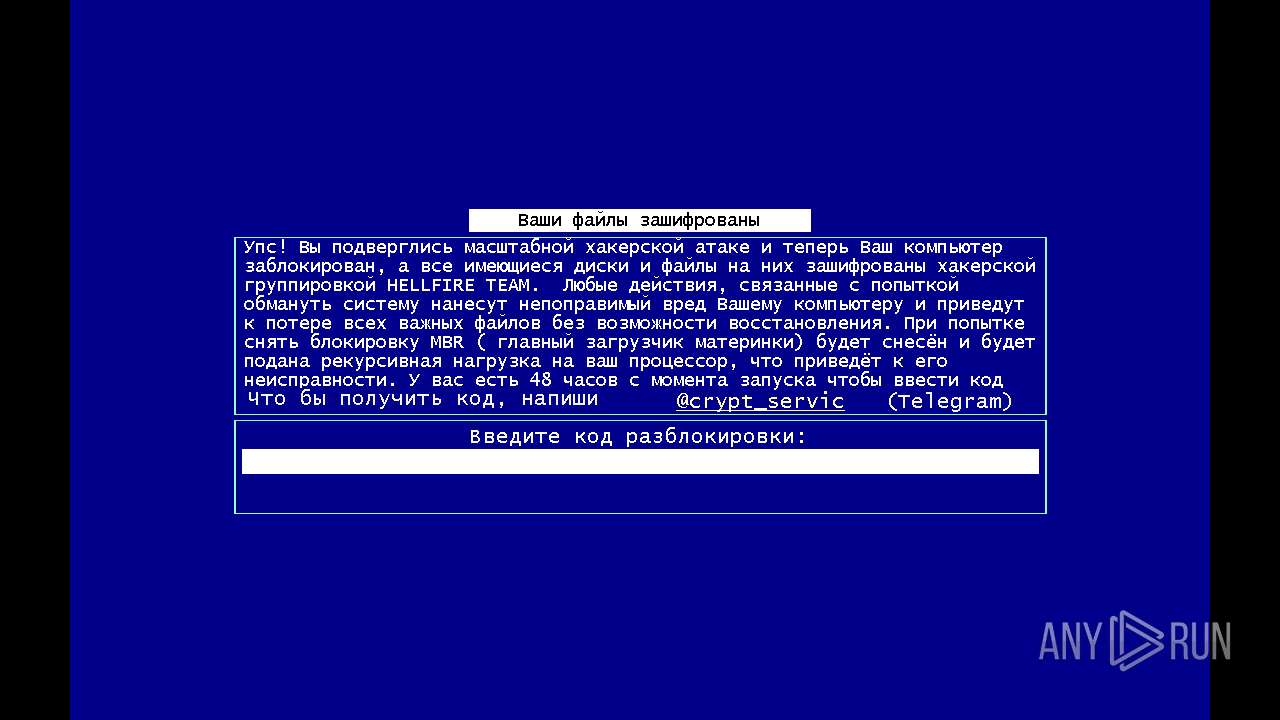
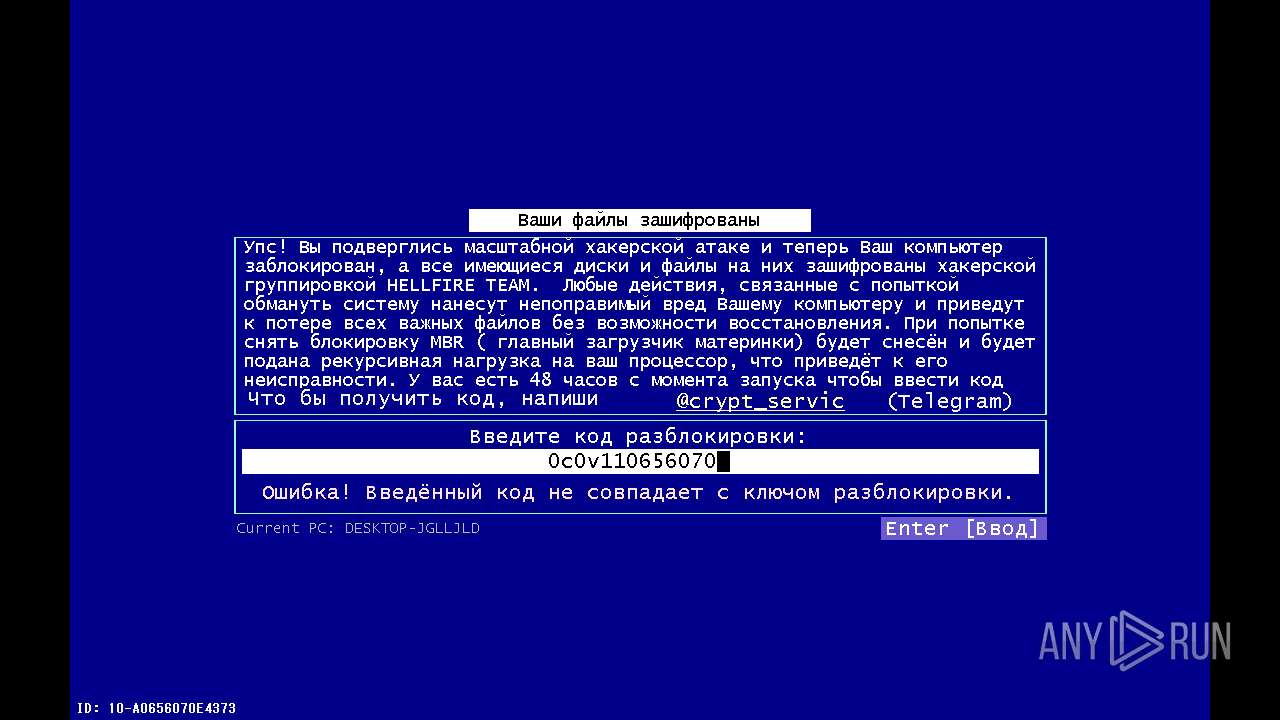
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2024, 06:55:59 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 7924C0F21738FAB05F61102C0CAF3DA2 |
| SHA1: | 09E6FD5797381EEB9EC60D5214F2932154636247 |
| SHA256: | 9B29F5A1F0B6C270C90B343F4C6D0E0843201D687068DC5273CBF5074083609F |
| SSDEEP: | 3072:sRuz2/auIDD6u4AFHNbJFoUZXzUCpM69/KImQi/6ebW6kTgwj3:FC/auMkAFtbJ9zUCpM69/KImQi/6ebl |
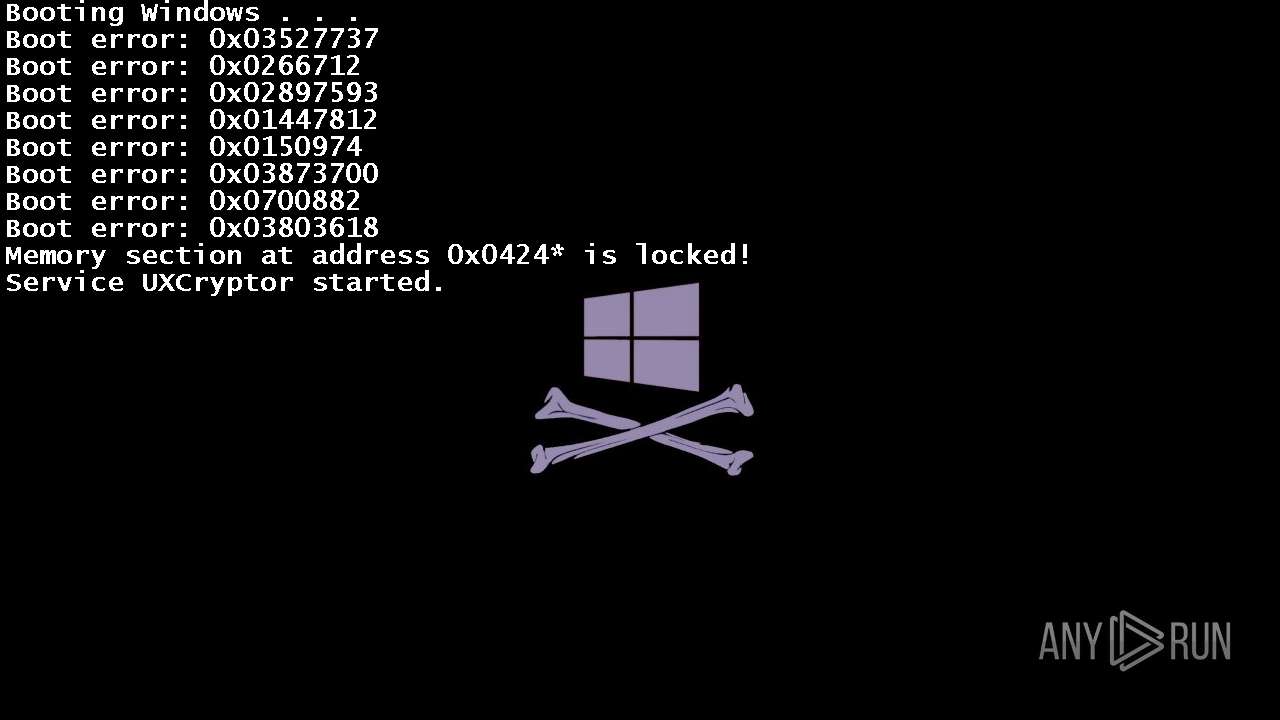
MALICIOUS
Drops the executable file immediately after the start
- lc.exe (PID: 4624)
Changes the autorun value in the registry
- lc.exe (PID: 4624)
Changes the login/logoff helper path in the registry
- lc.exe (PID: 4624)
Actions looks like stealing of personal data
- cmd.exe (PID: 4924)
SUSPICIOUS
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 6484)
- cmd.exe (PID: 6476)
- cmd.exe (PID: 6492)
- cmd.exe (PID: 6520)
- cmd.exe (PID: 6504)
- cmd.exe (PID: 6640)
- cmd.exe (PID: 6700)
- cmd.exe (PID: 4924)
- cmd.exe (PID: 6560)
- cmd.exe (PID: 5980)
Uses TASKKILL.EXE to kill process
- lc.exe (PID: 4624)
Starts CMD.EXE for commands execution
- lc.exe (PID: 4624)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 6484)
- cmd.exe (PID: 6640)
Reads security settings of Internet Explorer
- lc.exe (PID: 4624)
- GameBar.exe (PID: 5244)
- StartMenuExperienceHost.exe (PID: 6760)
Reads the date of Windows installation
- lc.exe (PID: 4624)
- StartMenuExperienceHost.exe (PID: 6760)
- SearchApp.exe (PID: 5764)
INFO
Reads the machine GUID from the registry
- lc.exe (PID: 4624)
- SearchApp.exe (PID: 5764)
Checks supported languages
- lc.exe (PID: 4624)
- GameBar.exe (PID: 5244)
- TextInputHost.exe (PID: 6812)
- StartMenuExperienceHost.exe (PID: 6760)
- SearchApp.exe (PID: 5764)
Reads the computer name
- lc.exe (PID: 4624)
- StartMenuExperienceHost.exe (PID: 6760)
- GameBar.exe (PID: 5244)
- TextInputHost.exe (PID: 6812)
- SearchApp.exe (PID: 5764)
Create files in a temporary directory
- lc.exe (PID: 4624)
.NET Reactor protector has been detected
- lc.exe (PID: 4624)
Process checks computer location settings
- lc.exe (PID: 4624)
- StartMenuExperienceHost.exe (PID: 6760)
- SearchApp.exe (PID: 5764)
Reads Microsoft Office registry keys
- explorer.exe (PID: 5644)
Reads security settings of Internet Explorer
- explorer.exe (PID: 5644)
Checks proxy server information
- SearchApp.exe (PID: 5764)
- explorer.exe (PID: 5644)
Reads Environment values
- SearchApp.exe (PID: 5764)
Process checks Internet Explorer phishing filters
- SearchApp.exe (PID: 5764)
Creates files or folders in the user directory
- explorer.exe (PID: 5644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:12:02 14:42:19+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 182272 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e72e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 0.0.0.0 |
| InternalName: | lc.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | lc.exe |
| ProductName: | - |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
185
Monitored processes
52
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2804 | attrib +h +s -r desktop.ini | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2872 | attrib +h +s -r desktop.ini | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3104 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3716 | C:\WINDOWS\System32\mobsync.exe -Embedding | C:\Windows\System32\mobsync.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Sync Center Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4616 | "C:\Windows\System32\cmd.exe" /k C:\WINDOWS\Explorer.exe | C:\Windows\System32\cmd.exe | — | lc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4624 | "C:\Users\admin\Desktop\lc.exe" | C:\Users\admin\Desktop\lc.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 4672 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4708 | attrib -h -s -r -i /D | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4808 | attrib +h +s -r desktop.ini | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4924 | cmd.exe /c cd "%userprofile%"&attrib -h -s -r -i /D & del info-0v92.txt /q /s & attrib +h +s -r desktop.ini | C:\Windows\System32\cmd.exe | lc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
37 728
Read events
37 474
Write events
226
Delete events
28
Modification events
| (PID) Process: | (4624) lc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | WindowsInstaller |
Value: "C:\Users\admin\Desktop\lc.exe" -startup | |||
| (PID) Process: | (4624) lc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MSEdgeUpdateX |
Value: "C:\Users\admin\Desktop\lc.exe" | |||
| (PID) Process: | (4624) lc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | System3264Wow |
Value: "C:\Users\admin\Desktop\lc.exe" --init | |||
| (PID) Process: | (4624) lc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | OneDrive10293 |
Value: "C:\Users\admin\Desktop\lc.exe" /setup | |||
| (PID) Process: | (4624) lc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | WINDOWS |
Value: "C:\Users\admin\Desktop\lc.exe" --wininit | |||
| (PID) Process: | (4624) lc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Shell |
Value: "C:\Users\admin\Desktop\lc.exe" | |||
| (PID) Process: | (4624) lc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\RunMRU |
| Operation: | write | Name: | a |
Value: YOU ARE HACKED!\1 | |||
| (PID) Process: | (4624) lc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\RunMRU |
| Operation: | write | Name: | b |
Value: HAHAHAHAHAHAHA\1 | |||
| (PID) Process: | (4624) lc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\RunMRU |
| Operation: | write | Name: | c |
Value: winlocker.ru\1 | |||
| (PID) Process: | (4624) lc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\RunMRU |
| Operation: | write | Name: | MRUList |
Value: abc | |||
Executable files
0
Suspicious files
3
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5764 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\DeviceSearchCache\AppCache133652410126785062.txt~RF1db2b8.TMP | — | |
MD5:— | SHA256:— | |||
| 6520 | cmd.exe | C:\Users\admin\info-0v92.txt | text | |
MD5:802D5D0BF305303D08FCEBCE7514DB29 | SHA256:DD0D8DF69182DAFA4E0E73D7AE675E8F74F0D2BD4A1970BF181C78F9B67814A8 | |||
| 6476 | cmd.exe | C:\Users\admin\Desktop\info-0v92.txt | text | |
MD5:802D5D0BF305303D08FCEBCE7514DB29 | SHA256:DD0D8DF69182DAFA4E0E73D7AE675E8F74F0D2BD4A1970BF181C78F9B67814A8 | |||
| 3104 | TiWorker.exe | C:\WINDOWS\Logs\CBS\CBS.log | text | |
MD5:B948909E7EFDD8AEE56122A641AAD348 | SHA256:4AABE14792254B948EA28FD797FB826070D1A8A922F70F62F9341A653482B092 | |||
| 5764 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\ConstraintIndex\Apps_{6b7bcc26-b664-4c7c-aa9d-9cd3bfe545b0}\0.0.filtertrie.intermediate.txt | text | |
MD5:313FB75B427790D01342FE144D9C3C06 | SHA256:50DBBA1A26C02E1C1B831C474708E68C9B11E3FCF6B254AE908A2C3007D88100 | |||
| 5764 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\DeviceSearchCache\AppCache133652410126785062.txt.~tmp | ini | |
MD5:EBA9D627AEFA0148EA256382E454768F | SHA256:85F02886D53B7427792E54BCEE97D366AD46F78CF90AA25DCC3FAE29ED7FA7F8 | |||
| 5764 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\DeviceSearchCache\AppCache133652410126785062.txt | ini | |
MD5:EBA9D627AEFA0148EA256382E454768F | SHA256:85F02886D53B7427792E54BCEE97D366AD46F78CF90AA25DCC3FAE29ED7FA7F8 | |||
| 6504 | cmd.exe | C:\Users\admin\Documents\info-0v92.txt | text | |
MD5:802D5D0BF305303D08FCEBCE7514DB29 | SHA256:DD0D8DF69182DAFA4E0E73D7AE675E8F74F0D2BD4A1970BF181C78F9B67814A8 | |||
| 5764 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\ConstraintIndex\Apps_{6b7bcc26-b664-4c7c-aa9d-9cd3bfe545b0}\0.2.filtertrie.intermediate.txt | text | |
MD5:C204E9FAAF8565AD333828BEFF2D786E | SHA256:D65B6A3BF11A27A1CED1F7E98082246E40CF01289FD47FE4A5ED46C221F2F73F | |||
| 5764 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\ConstraintIndex\Apps_{6b7bcc26-b664-4c7c-aa9d-9cd3bfe545b0}\Apps.index | binary | |
MD5:FE9A819377870FA6FDD677E5D3AA1A07 | SHA256:C43D46A72D282151F56E09F15CD47DB4414ECA02B536D41D26D5560AA5ADEC78 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
50
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5148 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3540 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6488 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6488 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5104 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5148 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4452 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4656 | SearchApp.exe | 92.123.104.33:443 | www.bing.com | Akamai International B.V. | DE | unknown |
2140 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5148 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4656 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5148 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
5148 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3540 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
arc.msn.com |
| whitelisted |