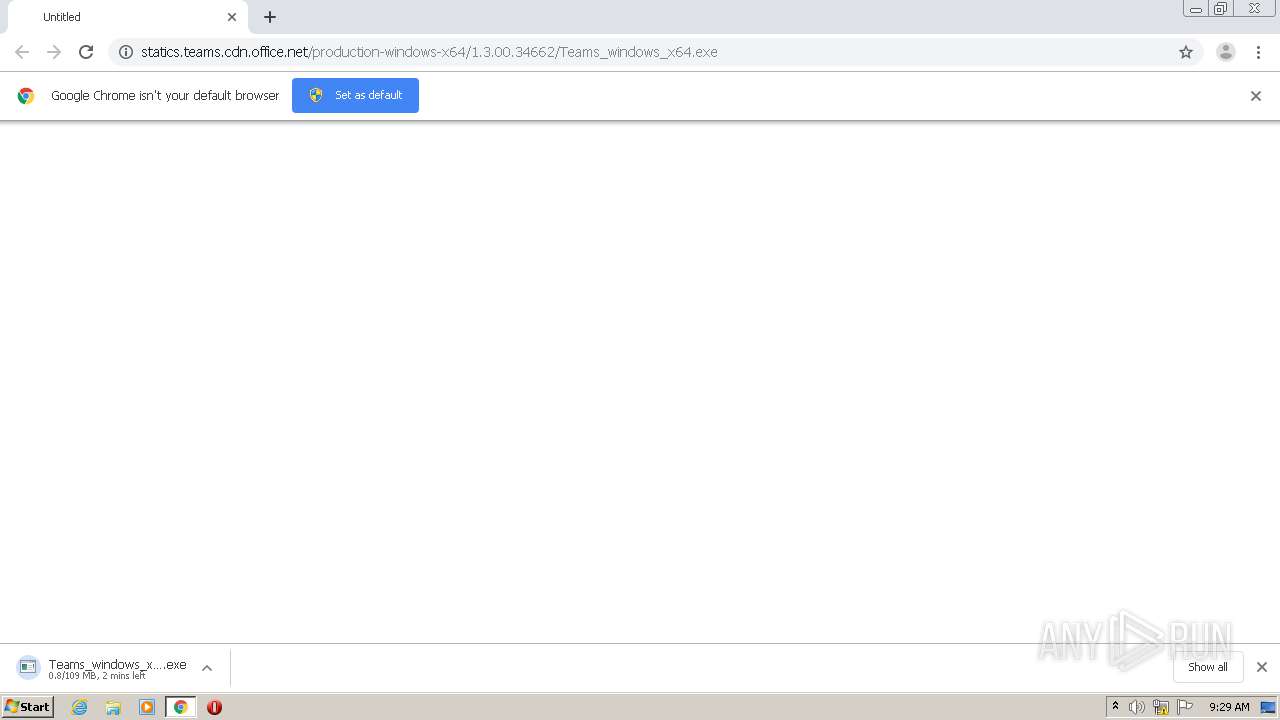
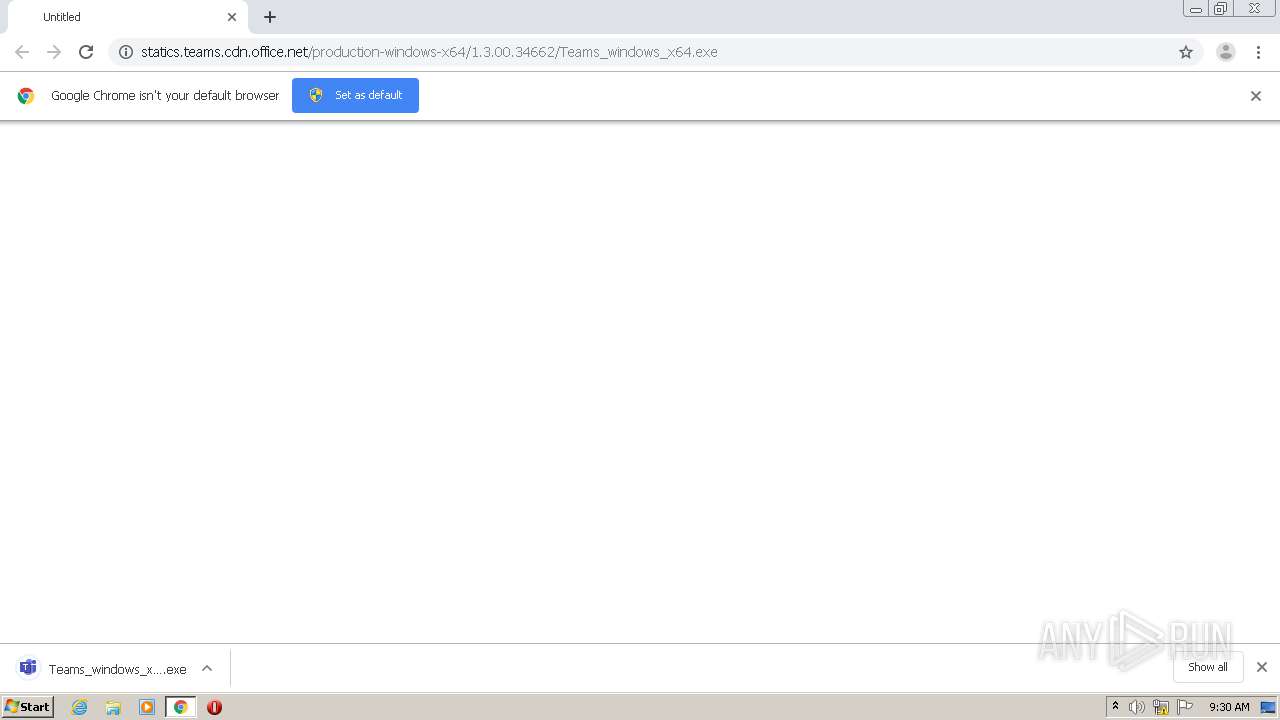
| URL: | http://statics.teams.cdn.office.net/production-windows-x64/1.3.00.34662/Teams_windows_x64.exe |
| Full analysis: | https://app.any.run/tasks/adbab9d1-4947-4e79-a0d4-8e89a8530cd0 |
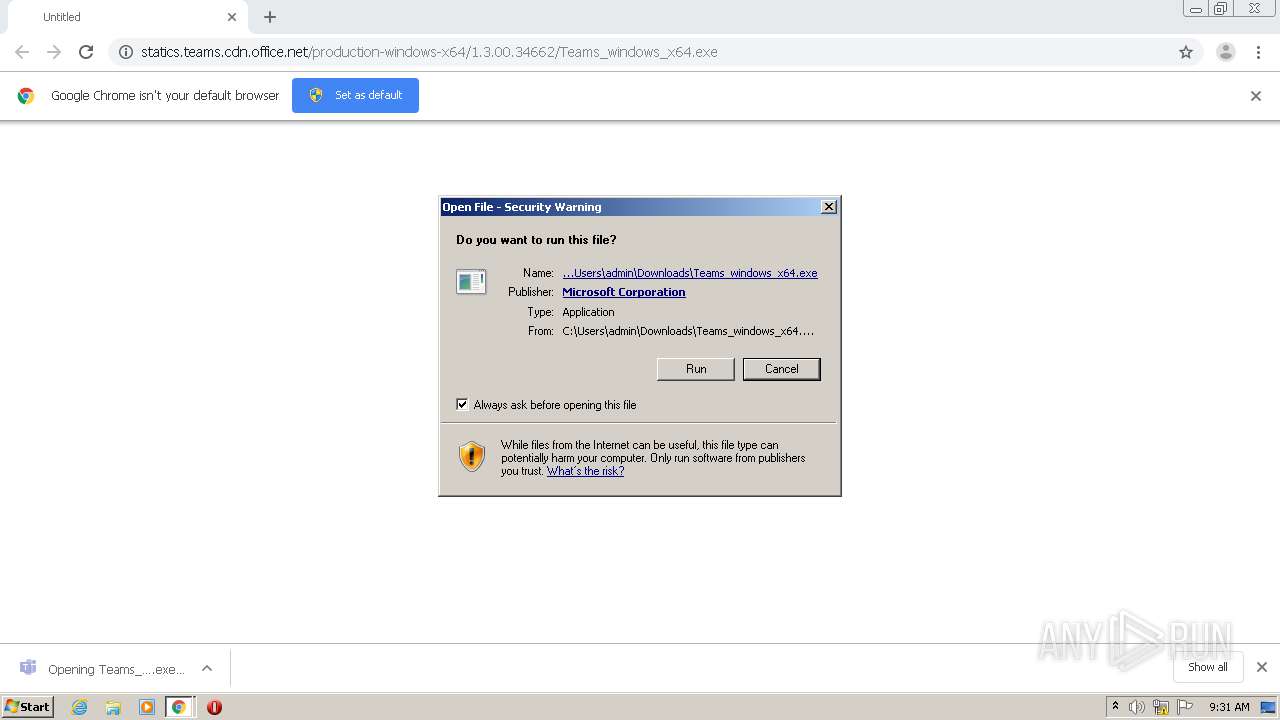
| Verdict: | Malicious activity |
| Analysis date: | January 21, 2021, 09:28:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 21A60125212C984CE8D7424A0DAA7ECF |
| SHA1: | 26D0FD92816DCE8FE6E8743F5FFA18B199E6E34A |
| SHA256: | 9B2805BF7AC799372C2BBD132C456E2E94E25E0FB73A737BA8794DC8D308B252 |
| SSDEEP: | 3:N1KNRwu9puaQGRMdv3LWDLWZaGEI9/xN:C3H7TRMdv3LrrEu5N |
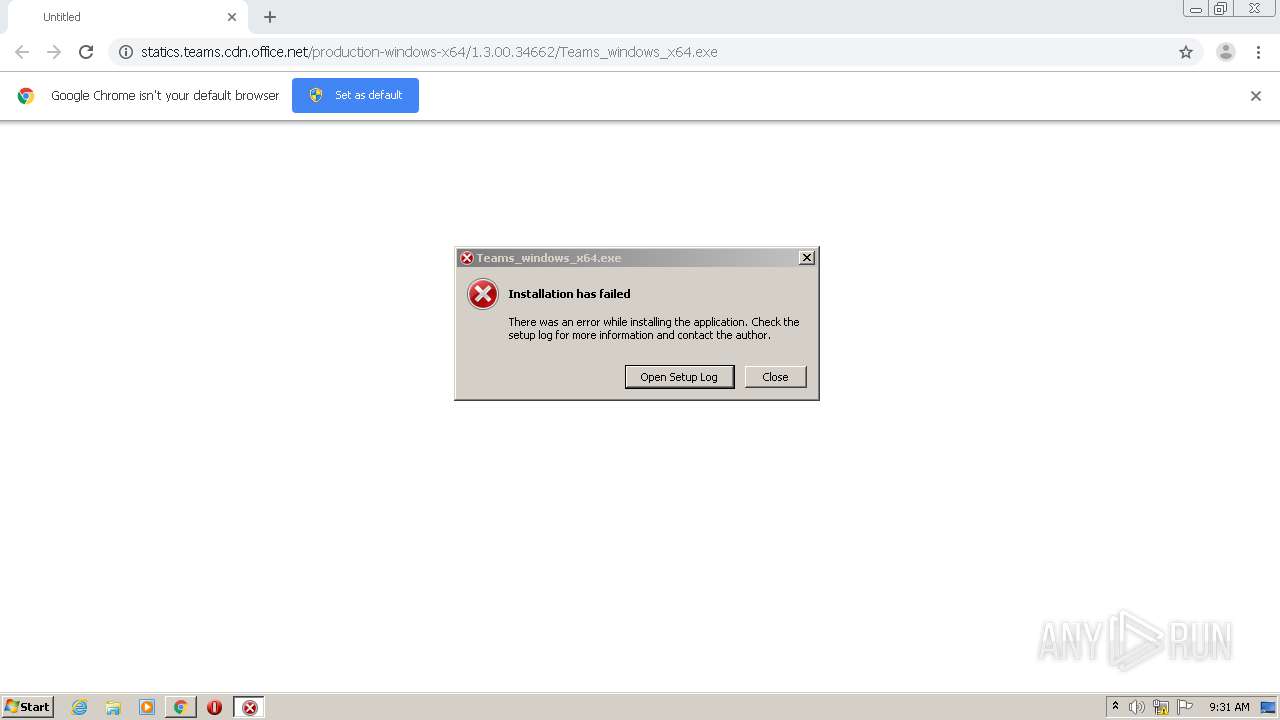
MALICIOUS
Application was dropped or rewritten from another process
- Teams_windows_x64.exe (PID: 2780)
- Update.exe (PID: 564)
- Squirrel.exe (PID: 1716)
SUSPICIOUS
Drops a file with a compile date too recent
- chrome.exe (PID: 1936)
- Teams_windows_x64.exe (PID: 2780)
- Update.exe (PID: 564)
- Squirrel.exe (PID: 1716)
Executable content was dropped or overwritten
- chrome.exe (PID: 2492)
- Teams_windows_x64.exe (PID: 2780)
- Squirrel.exe (PID: 1716)
- Update.exe (PID: 564)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 2492)
- Update.exe (PID: 564)
Reads Environment values
- Update.exe (PID: 564)
- Squirrel.exe (PID: 1716)
Creates files in the user directory
- Update.exe (PID: 564)
Drops a file with too old compile date
- Update.exe (PID: 564)
INFO
Reads the hosts file
- chrome.exe (PID: 2492)
- chrome.exe (PID: 1936)
Application launched itself
- chrome.exe (PID: 2492)
Reads Microsoft Office registry keys
- Update.exe (PID: 564)
- Squirrel.exe (PID: 1716)
Reads settings of System Certificates
- Update.exe (PID: 564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
14
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
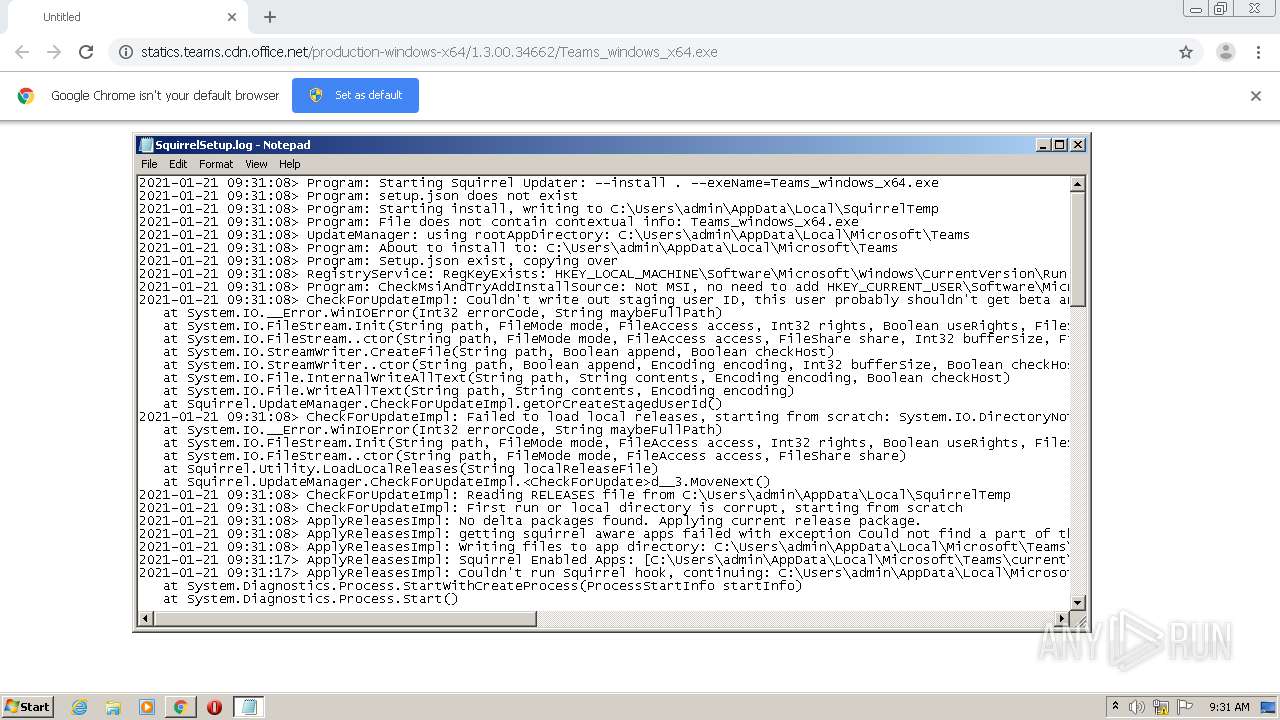
| 564 | "C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe" --install . --exeName=Teams_windows_x64.exe | C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe | Teams_windows_x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 4294967295 Version: 1.10.56.0 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,9716961057646429694,3374206213085204729,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5497565945690996087 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1716 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Squirrel.exe" --updateSelf=C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Squirrel.exe | Update.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.10.56.0 Modules
| |||||||||||||||
| 1936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,9716961057646429694,3374206213085204729,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=6253285651569502877 --mojo-platform-channel-handle=1532 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2348 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://statics.teams.cdn.office.net/production-windows-x64/1.3.00.34662/Teams_windows_x64.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,9716961057646429694,3374206213085204729,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11862392224182920905 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2184 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,9716961057646429694,3374206213085204729,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=7880040318456541122 --mojo-platform-channel-handle=2504 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2780 | "C:\Users\admin\Downloads\Teams_windows_x64.exe" | C:\Users\admin\Downloads\Teams_windows_x64.exe | chrome.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 4294967295 Version: 1.3.00.34662 Modules
| |||||||||||||||
| 2924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,9716961057646429694,3374206213085204729,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13136279119901840758 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2352 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 797
Read events
1 685
Write events
109
Delete events
3
Modification events
| (PID) Process: | (2424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2492-13255694954766125 |
Value: 259 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2492) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2492-13255694954766125 |
Value: 259 | |||
Executable files
291
Suspicious files
11
Text files
237
Unknown types
59
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6009496B-9BC.pma | — | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0c1c9db7-3dea-43d9-b1ac-dfd14656ec03.tmp | — | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF15023c.TMP | text | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF15023c.TMP | text | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2492 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF150410.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
8
DNS requests
5
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1936 | chrome.exe | GET | 200 | 2.16.107.41:80 | http://statics.teams.cdn.office.net/production-windows-x64/1.3.00.34662/Teams_windows_x64.exe | unknown | executable | 109 Mb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1936 | chrome.exe | 2.16.107.41:80 | statics.teams.cdn.office.net | Akamai International B.V. | — | malicious |
1936 | chrome.exe | 172.217.18.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1936 | chrome.exe | 74.125.202.100:443 | clients1.google.com | Google Inc. | US | whitelisted |
1716 | Squirrel.exe | 52.114.76.34:443 | mobile.pipe.aria.microsoft.com | Microsoft Corporation | IE | whitelisted |
1936 | chrome.exe | 108.177.111.84:443 | accounts.google.com | Google Inc. | US | unknown |
564 | Update.exe | 52.114.76.34:443 | mobile.pipe.aria.microsoft.com | Microsoft Corporation | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
statics.teams.cdn.office.net |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
mobile.pipe.aria.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1936 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1936 | chrome.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1936 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
Process | Message |
|---|---|
Update.exe | Update.exe Information: 0 : |
Update.exe | Starting TelemetryManager constructor
|
Update.exe | Update.exe Information: 0 : |
Update.exe | TelemetryManagerImpl creation started
|
Update.exe | Update.exe Information: 0 : |
Update.exe | Performance counters are disabled. Skipping creation of counters category.
|
Update.exe | Update.exe Information: 0 : |
Update.exe | RecordBatcherTask with ID 4 started.
|
Update.exe | Update.exe Information: 0 : |
Update.exe | DataPackageSender with UserAgent name: AST-exe-C#, version: 1.10.56.0, [Ast_Default_Source]
|