| File name: | KMSPico11.exe |
| Full analysis: | https://app.any.run/tasks/937c952e-cd58-423f-8fa8-b3662a5e73cc |
| Verdict: | Malicious activity |
| Analysis date: | May 31, 2024, 16:01:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | C99A9FC14DAF7FDA75234789FCFA069B |
| SHA1: | B52CA38B7F5D3BC689D434172A40D05CC8F09542 |
| SHA256: | 9B26CB4A160402A6ED7651C122A7BCE6A14220A6E1737685C13A246844D188D6 |
| SSDEEP: | 3072:yfReIiDWRTZ/4tcPskg2MCz/y/JaiLO79npJ1sR+RM+tp4S9:yZeIqIQtKskN/z/IJDu9nP1sdjS9 |
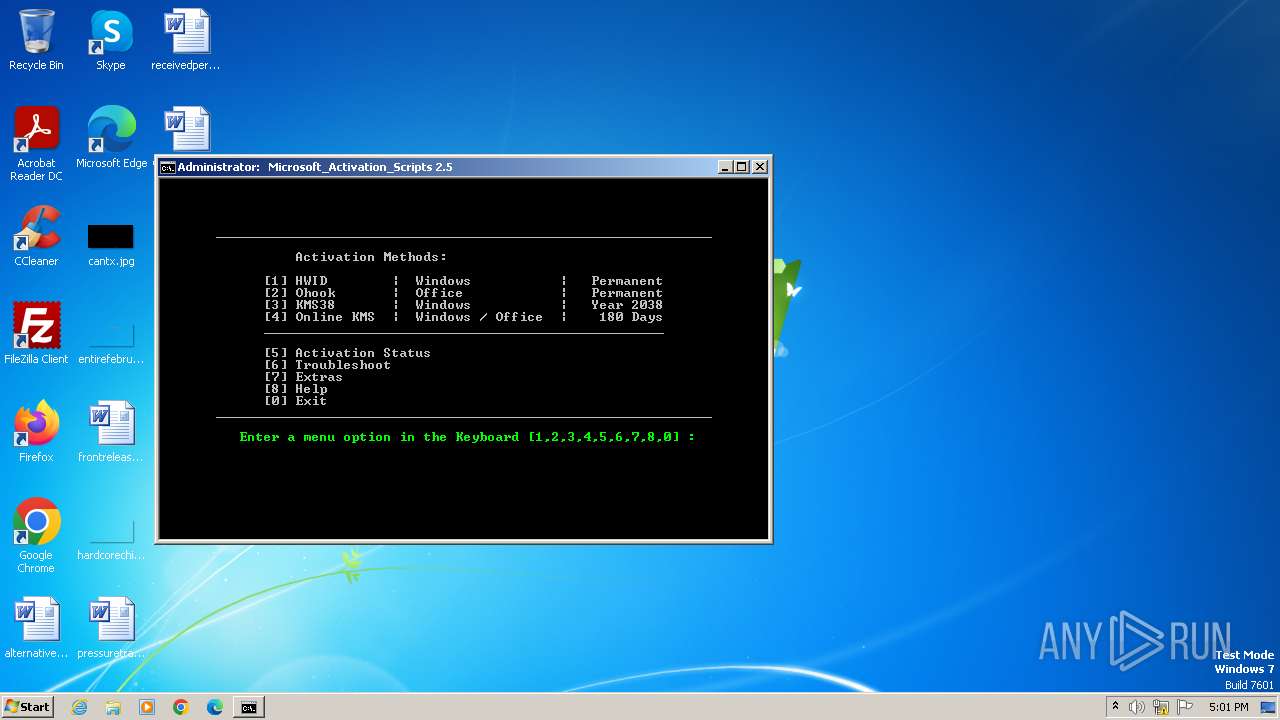
MALICIOUS
Drops the executable file immediately after the start
- KMSPico11.exe (PID: 3968)
SUSPICIOUS
Reads the Internet Settings
- KMSPico11.exe (PID: 3968)
- powershell.exe (PID: 1036)
Reads security settings of Internet Explorer
- KMSPico11.exe (PID: 3968)
Starts CMD.EXE for commands execution
- KMSPico11.exe (PID: 3968)
- cmd.exe (PID: 4008)
- powershell.exe (PID: 1036)
- cmd.exe (PID: 524)
Executing commands from ".cmd" file
- KMSPico11.exe (PID: 3968)
- cmd.exe (PID: 4008)
- powershell.exe (PID: 1036)
- cmd.exe (PID: 524)
Starts SC.EXE for service management
- cmd.exe (PID: 4008)
- cmd.exe (PID: 524)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 4008)
- cmd.exe (PID: 524)
Application launched itself
- cmd.exe (PID: 4008)
- cmd.exe (PID: 524)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4008)
- cmd.exe (PID: 524)
INFO
Checks supported languages
- KMSPico11.exe (PID: 3968)
- mode.com (PID: 1900)
Reads the computer name
- KMSPico11.exe (PID: 3968)
Checks operating system version
- cmd.exe (PID: 4008)
- cmd.exe (PID: 524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2104:01:25 09:06:36+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 122368 |
| InitializedDataSize: | 1536 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1fc92 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
82
Monitored processes
46
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | find /i "/" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 524 | "C:\Windows\System32\cmd.exe" /c ""C:\Users\admin\Documents\cloud_b706281f-97bf-4335-8b05-9bf2783dd5dc.cmd" -el " | C:\Windows\System32\cmd.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 588 | sc query Null | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 768 | C:\Windows\system32\cmd.exe /S /D /c" echo "-el" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1020 | find /i "C:\Users\admin\AppData\Local\Temp" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1024 | C:\Windows\system32\cmd.exe /S /D /c" echo "C:\Users\admin\Documents\cloud_b706281f-97bf-4335-8b05-9bf2783dd5dc.cmd" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1036 | powershell.exe "start cmd.exe -arg '/c \""""C:\Users\admin\Documents\cloud_b706281f-97bf-4335-8b05-9bf2783dd5dc.cmd""" -el \"' -verb runas" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1212 | C:\Windows\system32\cmd.exe /S /D /c" echo "-el" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1332 | C:\Windows\system32\cmd.exe /c ver | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1424 | C:\Windows\system32\cmd.exe /c ver | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
10 091
Read events
10 075
Write events
16
Delete events
0
Modification events
| (PID) Process: | (3968) KMSPico11.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3968) KMSPico11.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3968) KMSPico11.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3968) KMSPico11.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1036) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1036) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1036) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1036) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
8
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 524 | cmd.exe | C:\Windows\Temp\' | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3968 | KMSPico11.exe | C:\Users\admin\Documents\cloud_b706281f-97bf-4335-8b05-9bf2783dd5dc.cmd | text | |
MD5:721E3F8CACEDDB2BCB8CD85FA400F61A | SHA256:2AED5BB373191CB92B3284BE3DE8B2EE6DD746FF71ACC8AE10968CB6A514C95F | |||
| 1036 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 1036 | powershell.exe | C:\Users\admin\AppData\Local\Temp\lywrqbq4.ig5.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1964 | powershell.exe | C:\Users\admin\AppData\Local\Temp\1uphfxzb.vcj.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1964 | powershell.exe | C:\Users\admin\AppData\Local\Temp\rd30kyx1.mal.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2340 | powershell.exe | C:\Users\admin\AppData\Local\Temp\brul4dqm.5je.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1036 | powershell.exe | C:\Users\admin\AppData\Local\Temp\z3pl3g4u.to3.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2340 | powershell.exe | C:\Users\admin\AppData\Local\Temp\vsbemvdr.pq3.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 524 | cmd.exe | C:\Windows\Temp\`.txt | text | |
MD5:01950D578D2BAE1BD8F00614ED09CC93 | SHA256:2DB112C56E1AE46984F47A9EC720211918E5B2F39A184DC39C5CBAA3E861350C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
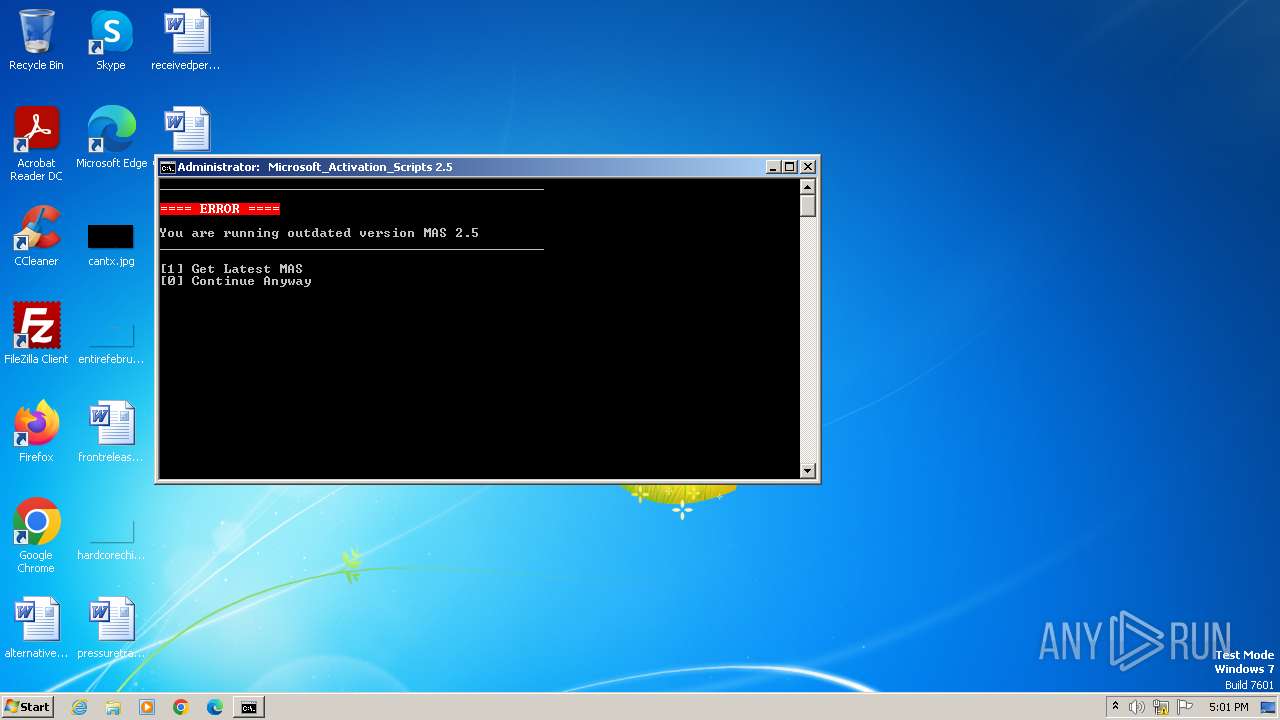
updatecheck.massgrave.dev |
| unknown |