| File name: | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591 |
| Full analysis: | https://app.any.run/tasks/80392382-6d8e-4271-af71-ec26ce54e06d |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 13:29:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B8D166F93360A3D5CCB03DC0C91A549A |
| SHA1: | F2B54D8406362227FC5E4630C53D577CFAE6546A |
| SHA256: | 9B15998362752D3B6ACAAD3F507F71EB851E19AE4626BDE3680F62063D943591 |
| SSDEEP: | 98304:LrOT0baBdxhfDD+sJ6oK5wo5GFrWx+D+QqHFZL0Fqba1tAC64+pl+Z:IhLCSevYF2+DlqHX0FqbaHA90 |
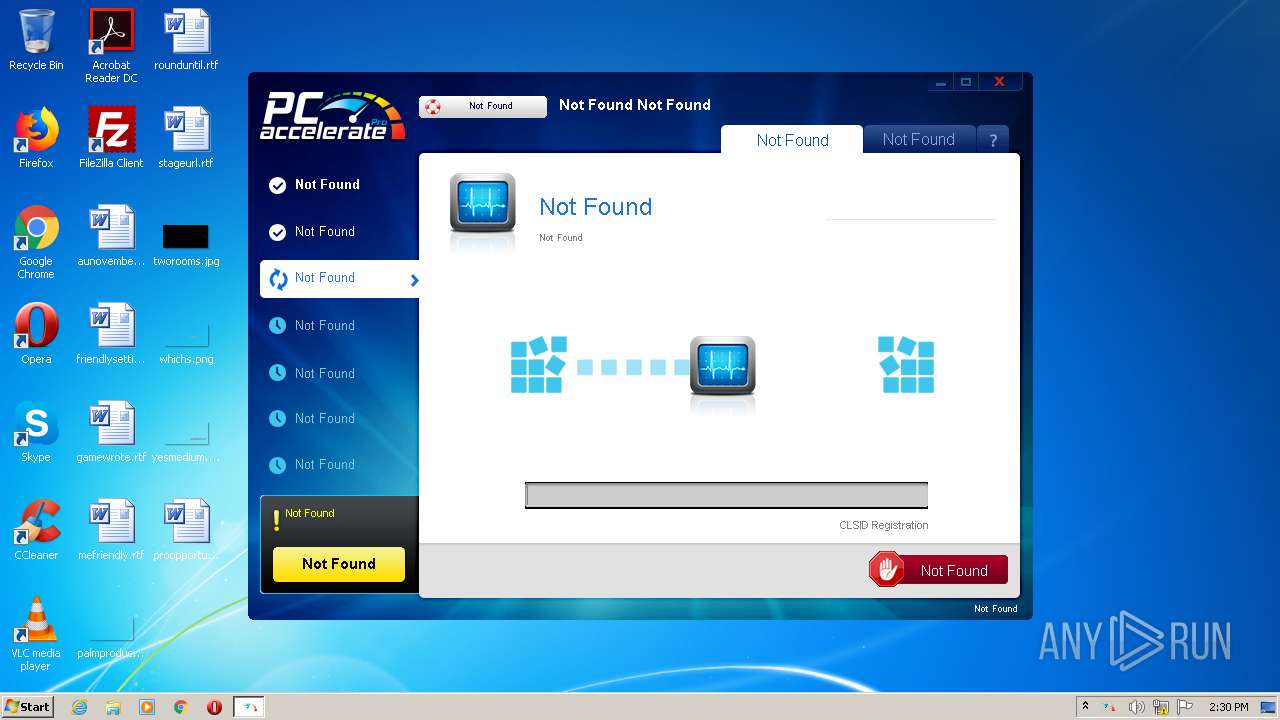
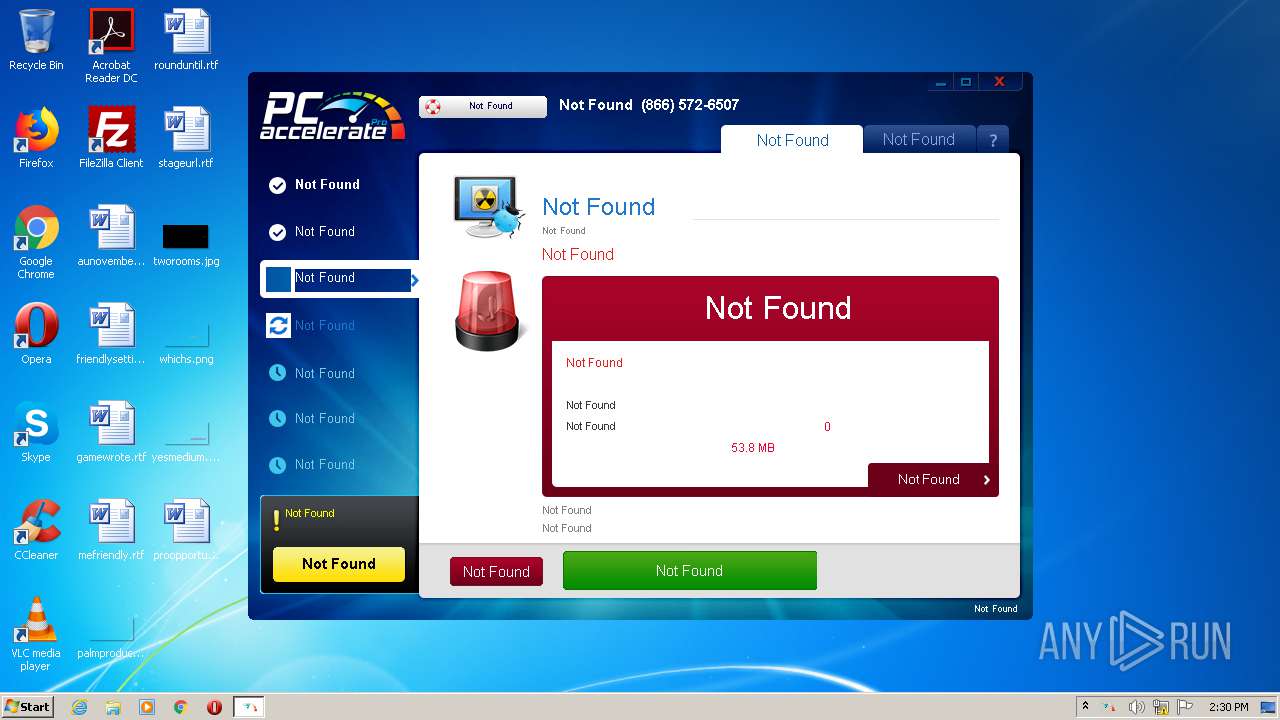
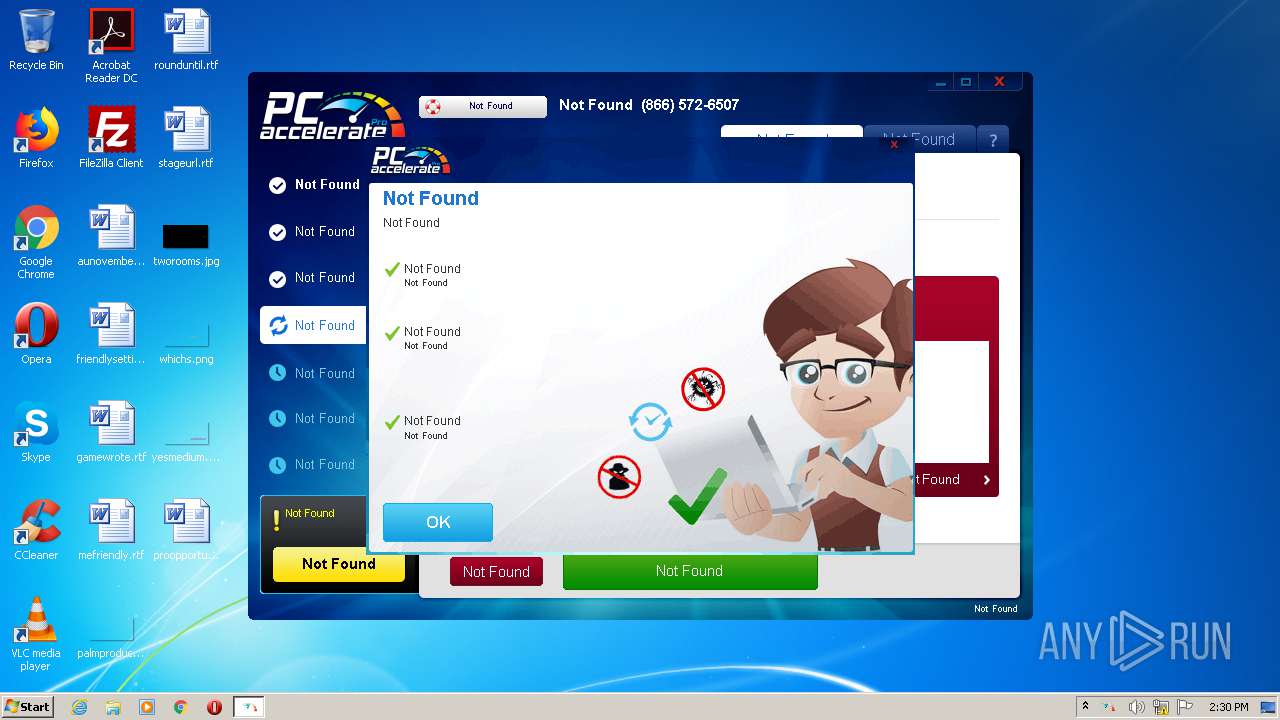
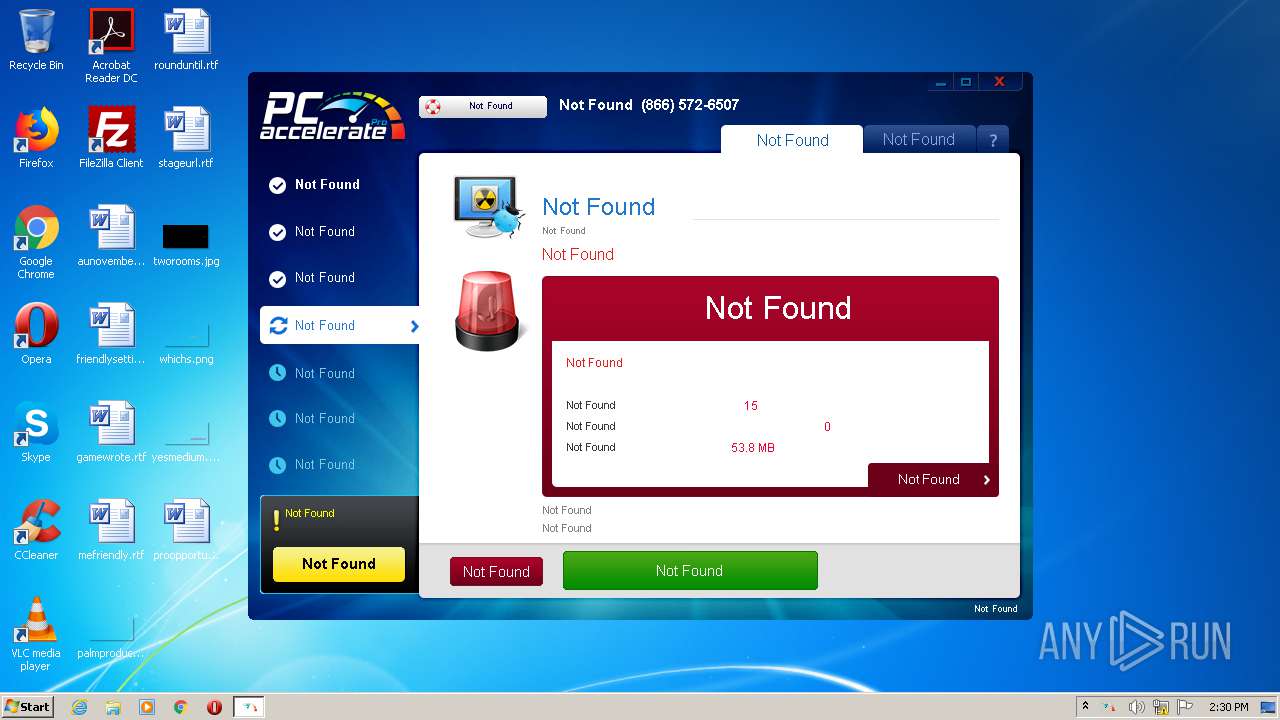
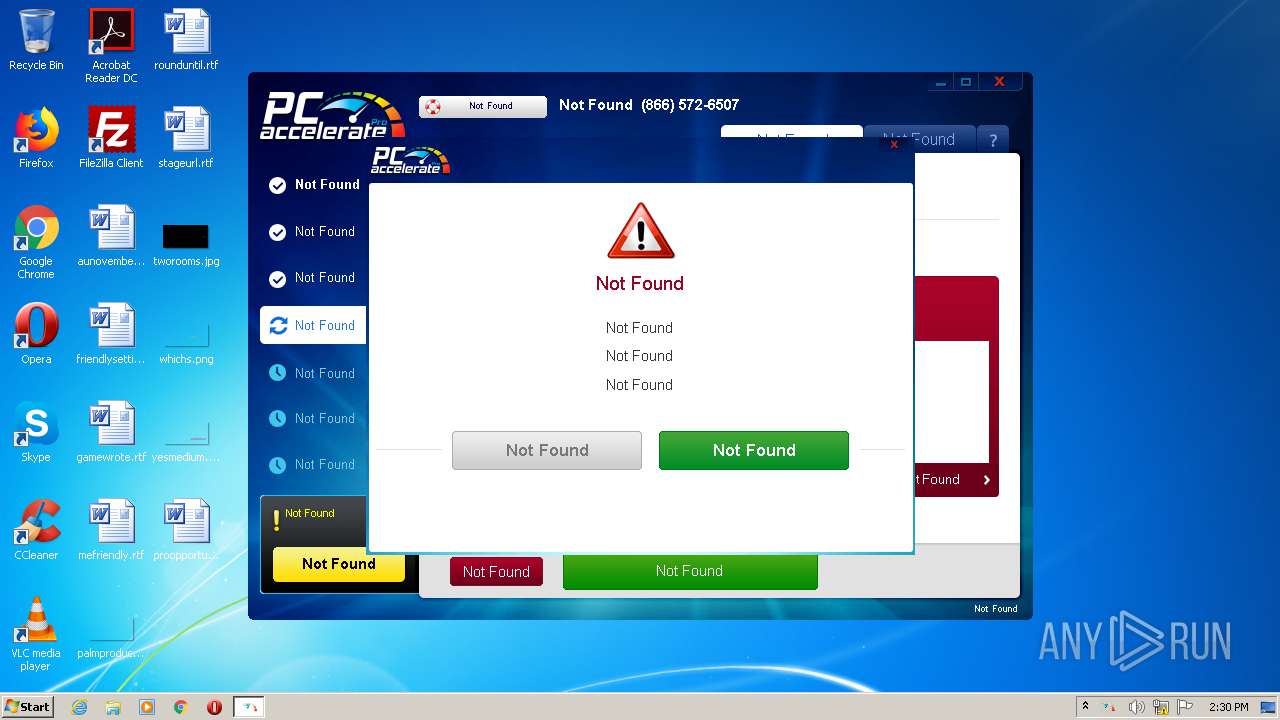
MALICIOUS
Actions looks like stealing of personal data
- 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe (PID: 2592)
SUSPICIOUS
Creates files in the user directory
- 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe (PID: 2592)
Reads Internet Cache Settings
- 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe (PID: 2592)
Changes IE settings (feature browser emulation)
- 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe (PID: 2592)
Searches for installed software
- 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe (PID: 2592)
Reads internet explorer settings
- 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe (PID: 2592)
INFO
Reads settings of System Certificates
- 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe (PID: 2592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (46.6) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (29.9) |
| .scr | | | Windows screen saver (14.1) |
| .exe | | | Win32 Executable (generic) (4.8) |
| .exe | | | Generic Win/DOS Executable (2.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:09:17 23:45:16+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 2984960 |
| InitializedDataSize: | 2691584 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1c1a2f |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.5.80 |
| ProductVersionNumber: | 1.0.5.80 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | KusushiSpeedup Soft |
| FileDescription: | KusushiSpeedup |
| InternalName: | KusushiSpeedup |
| OriginalFileName: | KusushiSpeedup |
| ProductName: | KusushiSpeedup |
| FileVersion: | 1.0.5.80 |
| LegalCopyright: | KusushiSpeedup Soft (c) 2020 |
| ProductVersion: | 1.0.5.80 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Sep-2020 21:45:16 |
| Detected languages: |
|
| CompanyName: | KusushiSpeedup Soft |
| FileDescription: | KusushiSpeedup |
| InternalName: | KusushiSpeedup |
| OriginalFilename: | KusushiSpeedup |
| ProductName: | KusushiSpeedup |
| FileVersion: | 1.0.5.80 |
| LegalCopyright: | KusushiSpeedup Soft (c) 2020 |
| ProductVersion: | 1.0.5.80 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 17-Sep-2020 21:45:16 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0028FAC3 | 0x0028FC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62923 |
.wb8gq5 | 0x00291000 | 0x00048FDC | 0x00049000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.52979 |
.rdata | 0x002DA000 | 0x000B58C4 | 0x000B5A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.25374 |
.data | 0x00390000 | 0x00023090 | 0x0000A800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.86198 |
.rsrc | 0x003B4000 | 0x001B8438 | 0x001B8600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.02226 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.17402 | 1974 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.66321 | 38056 | UNKNOWN | English - United States | RT_ICON |
3 | 2.51242 | 16936 | UNKNOWN | English - United States | RT_ICON |
4 | 2.63758 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 2.45891 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 2.64842 | 2440 | UNKNOWN | English - United States | RT_ICON |
7 | 5.14664 | 4232 | UNKNOWN | English - United States | RT_ICON |
8 | 4.50079 | 3548 | UNKNOWN | English - United States | RT_ICON |
9 | 3.02745 | 1712 | UNKNOWN | English - United States | RT_ICON |
10 | 5.15662 | 3616 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
MSIMG32.dll |
OLEACC.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
36
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2592 | "C:\Users\admin\AppData\Local\Temp\9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe" | C:\Users\admin\AppData\Local\Temp\9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | explorer.exe | ||||||||||||
User: admin Company: KusushiSpeedup Soft Integrity Level: MEDIUM Description: KusushiSpeedup Exit code: 0 Version: 1.0.5.80 Modules
| |||||||||||||||
Total events
521
Read events
500
Write events
21
Delete events
0
Modification events
| (PID) Process: | (2592) 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe |
Value: 9999 | |||
| (PID) Process: | (2592) 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2592) 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2592) 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2592) 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2592) 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2592) 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | Key: | HKEY_CURRENT_USER\Software\KusushiSpeedup |
| Operation: | write | Name: | SrvcHrtBt |
Value: 202010201430 | |||
| (PID) Process: | (2592) 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2592) 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2592) 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
7
Text files
45
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\UM52Q2YI.txt | — | |
MD5:— | SHA256:— | |||
| 2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | C:\Users\admin\AppData\Local\9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591\t001.dat | — | |
MD5:— | SHA256:— | |||
| 2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | C:\Users\admin\AppData\Local\Temp\CabDDE1.tmp | — | |
MD5:— | SHA256:— | |||
| 2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | C:\Users\admin\AppData\Local\Temp\TarDDE2.tmp | — | |
MD5:— | SHA256:— | |||
| 2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9FF67FB3141440EED32363089565AE60_26579B01BE290BF40CCB784614BC86AE | der | |
MD5:— | SHA256:— | |||
| 2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\C0K3HJFN.txt | text | |
MD5:— | SHA256:— | |||
| 2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | C:\Users\admin\AppData\Local\9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591\9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.cfg | text | |
MD5:— | SHA256:— | |||
| 2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9FF67FB3141440EED32363089565AE60_26579B01BE290BF40CCB784614BC86AE | binary | |
MD5:— | SHA256:— | |||
| 2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9FF67FB3141440EED32363089565AE60_E45AF39ECCE2A721324EF5F805E67D42 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
12
DNS requests
8
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | GET | 200 | 172.245.127.171:80 | http://config.instantsupport.help/api/get_phone/pcap/05c9df37f97e18faf584e2fa7dedf91d | US | text | 88 b | malicious |
2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | GET | 200 | 172.245.127.102:80 | http://softwarehelpdata.com/pcap.php?a=dpi_96&c=0&id=05c9df37f97e18faf584e2fa7dedf91d&t=20143001&v=580&aff= | US | binary | 1 b | suspicious |
2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | GET | 200 | 172.245.127.102:80 | http://softwarehelpdata.com/pcap.php?a=ppo&c=0&id=05c9df37f97e18faf584e2fa7dedf91d&t=20143039&v=580&aff= | US | binary | 1 b | suspicious |
2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | POST | 200 | 104.18.14.189:80 | http://softremoval.pcaccel.com/purchasesoft | US | text | 136 b | malicious |
2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | GET | 200 | 104.18.24.31:80 | http://spywaremaid.com/whitelist?smv=1.0.1.2&wlv=0.0&id=05c9df37f97e18faf584e2fa7dedf91d | US | text | 30 b | malicious |
2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | GET | 200 | 104.18.24.31:80 | http://spywaremaid.com/wsm.dat | US | binary | 30.9 Kb | malicious |
2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | GET | 200 | 172.245.127.102:80 | http://softwarehelpdata.com/pcap.php?a=rs&c=137&id=05c9df37f97e18faf584e2fa7dedf91d&t=20143029&v=580&aff= | US | binary | 1 b | suspicious |
2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | GET | 200 | 104.18.31.113:80 | http://pcacceleratepro.com/clamav.php | US | text | 26 b | malicious |
2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEATyU9nepAStDNLUsvGnUgQ%3D | US | der | 280 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 104.18.24.31:80 | spywaremaid.com | Cloudflare Inc | US | malicious |
2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | 172.245.127.171:80 | config.instantsupport.help | ColoCrossing | US | malicious |
2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 104.18.30.113:443 | pcacceleratepro.com | Cloudflare Inc | US | malicious |
2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | 172.245.127.102:80 | softwarehelpdata.com | ColoCrossing | US | malicious |
— | — | 104.18.31.113:80 | pcacceleratepro.com | Cloudflare Inc | US | suspicious |
— | — | 104.18.14.189:80 | softremoval.pcaccel.com | Cloudflare Inc | US | unknown |
— | — | 104.18.55.230:443 | securedshopgate.com | Cloudflare Inc | US | unknown |
2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | 104.18.30.113:443 | pcacceleratepro.com | Cloudflare Inc | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
spywaremaid.com |
| malicious |
pcacceleratepro.com |
| malicious |
softwarehelpdata.com |
| suspicious |
config.instantsupport.help |
| malicious |
softremoval.pcaccel.com |
| malicious |
secure2.pcacceleratepro.com |
| malicious |
ocsp.digicert.com |
| whitelisted |
securedshopgate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2592 | 9b15998362752d3b6acaad3f507f71eb851e19ae4626bde3680f62063d943591.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |