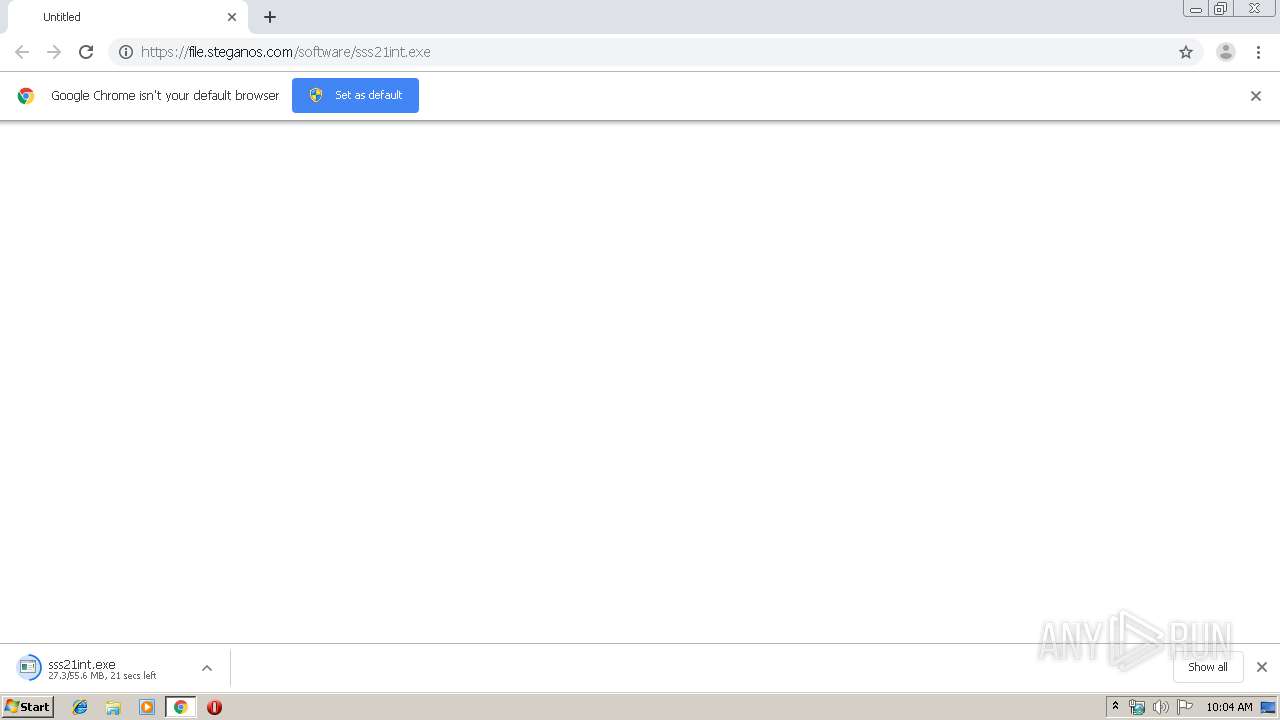
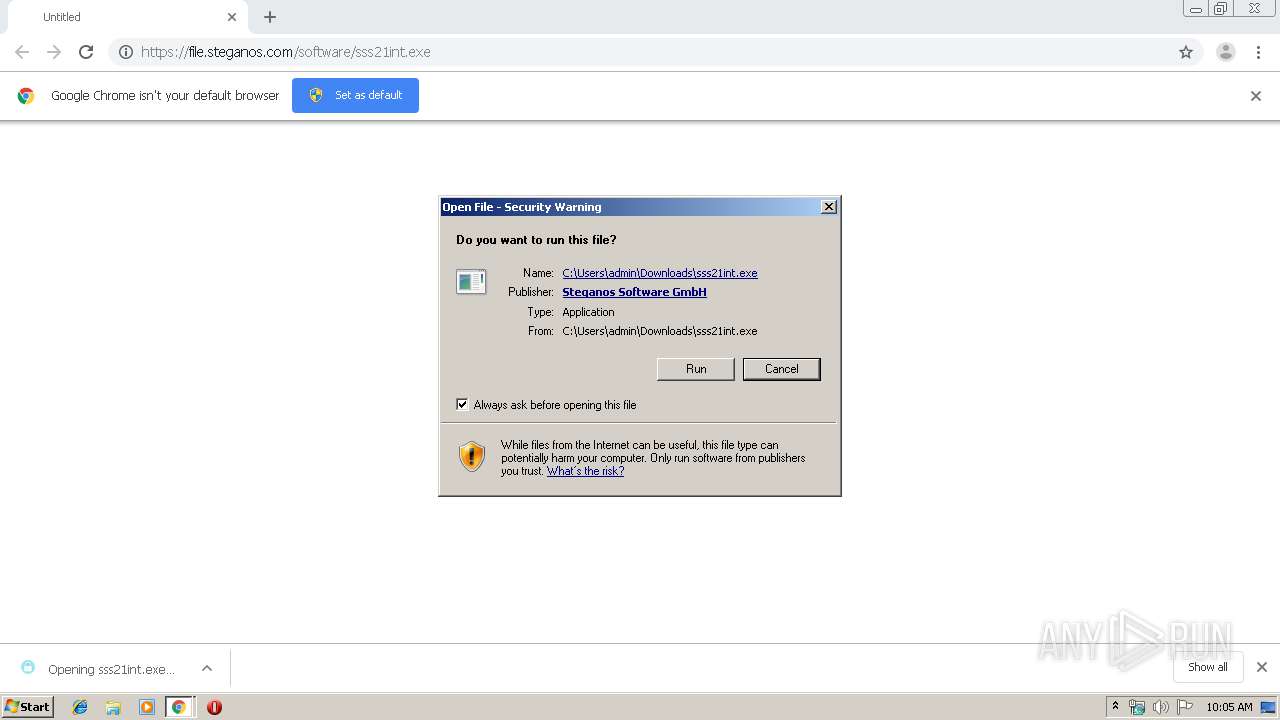
| URL: | https://file.steganos.com/software/sss21int.exe |
| Full analysis: | https://app.any.run/tasks/6b1521cd-8e2b-41f4-9170-d7e239012d2c |
| Verdict: | Malicious activity |
| Analysis date: | September 27, 2019, 09:04:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 77F0A52892A2287DD703CA76CADD9726 |
| SHA1: | 5165BA0519A55D03C74837473B5B7A816BEA7B18 |
| SHA256: | 9AFBB8105D0B69FBED06707490031A923A61D83D656CDF49024438EDBB0FFC46 |
| SSDEEP: | 3:N8OK7C:2Ot |
MALICIOUS
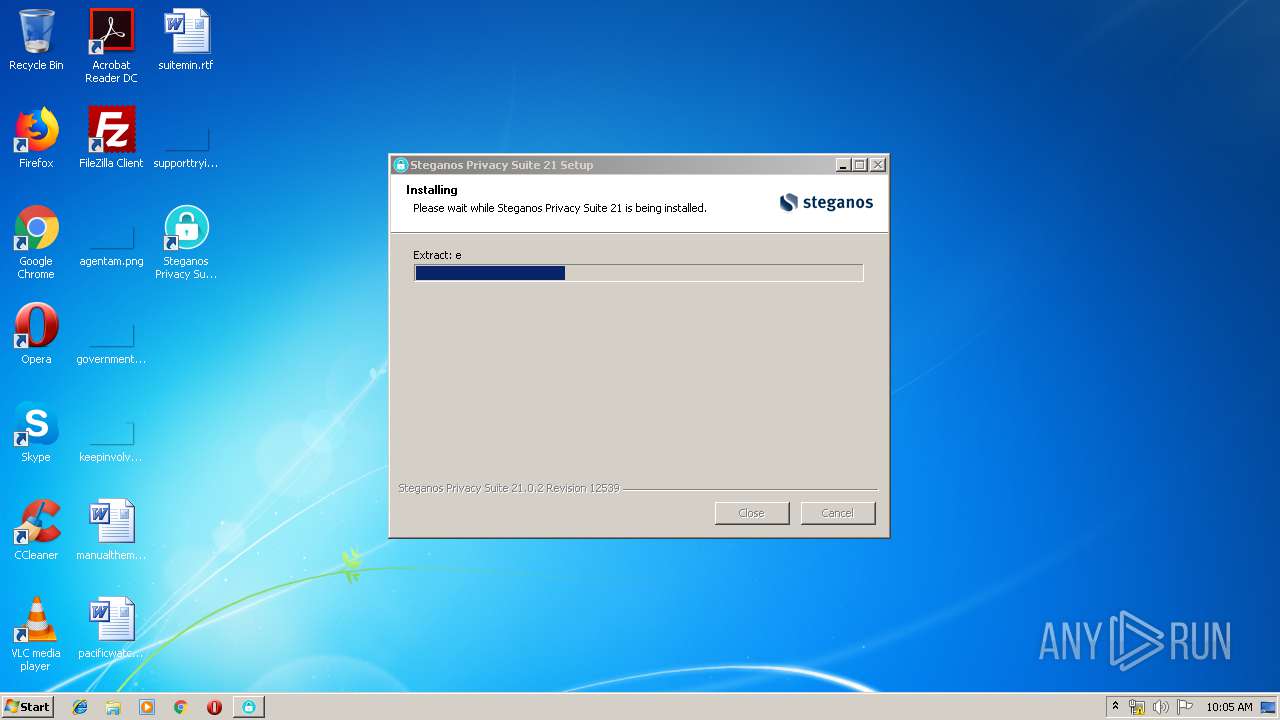
Application was dropped or rewritten from another process
- sss21int.exe (PID: 2836)
- sss21int.exe (PID: 1888)
- SteganosHotKeyService.exe (PID: 3284)
- passwordmanagercom.exe (PID: 3724)
- PasswordManager.exe (PID: 2948)
- Notifier.exe (PID: 3880)
- SteganosHotKeyService.exe (PID: 3192)
- RegisterDLL.exe (PID: 2720)
- Updater.exe (PID: 2956)
- ResetPendingMoves.exe (PID: 3516)
- 7za.exe (PID: 1152)
- Safe.exe (PID: 3304)
- 7za.exe (PID: 3856)
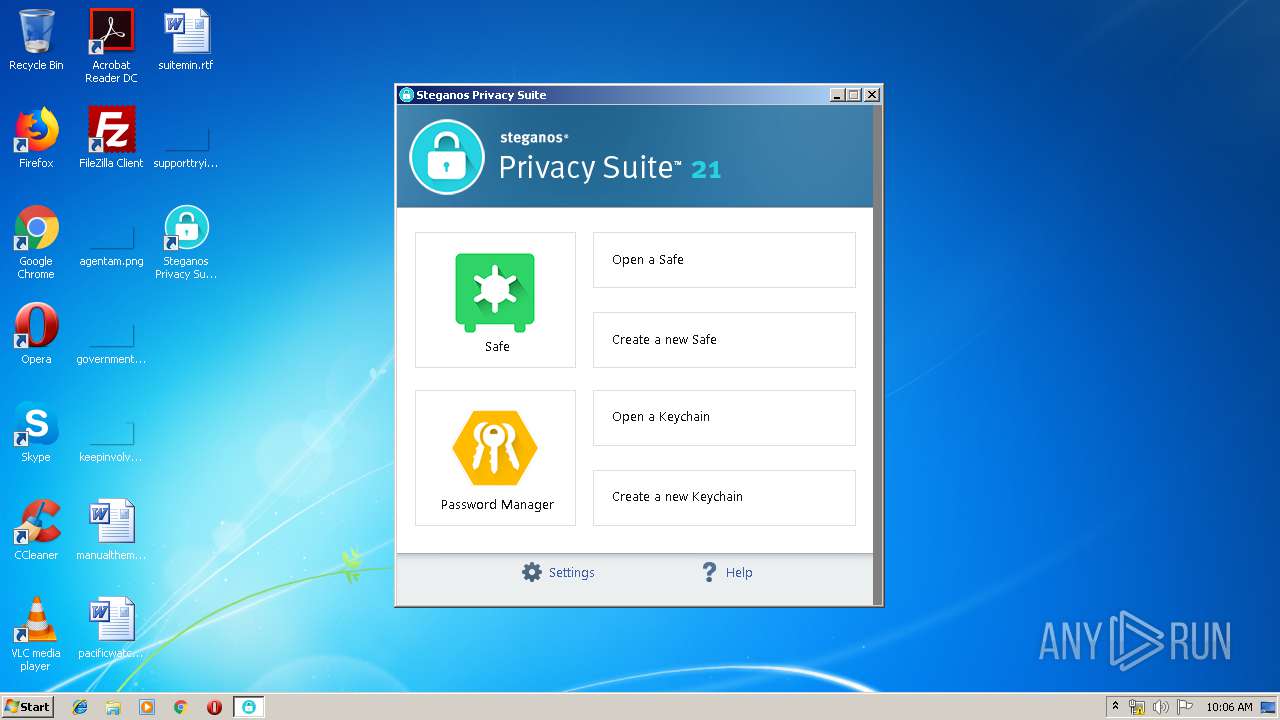
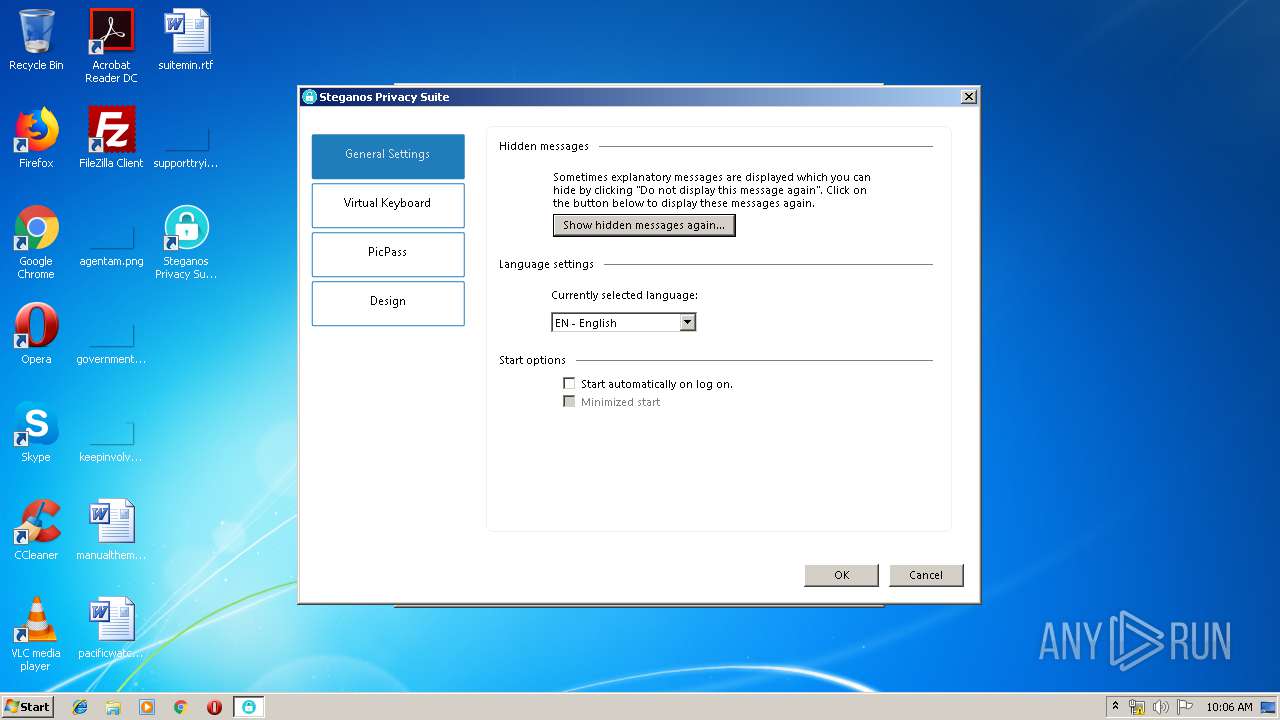
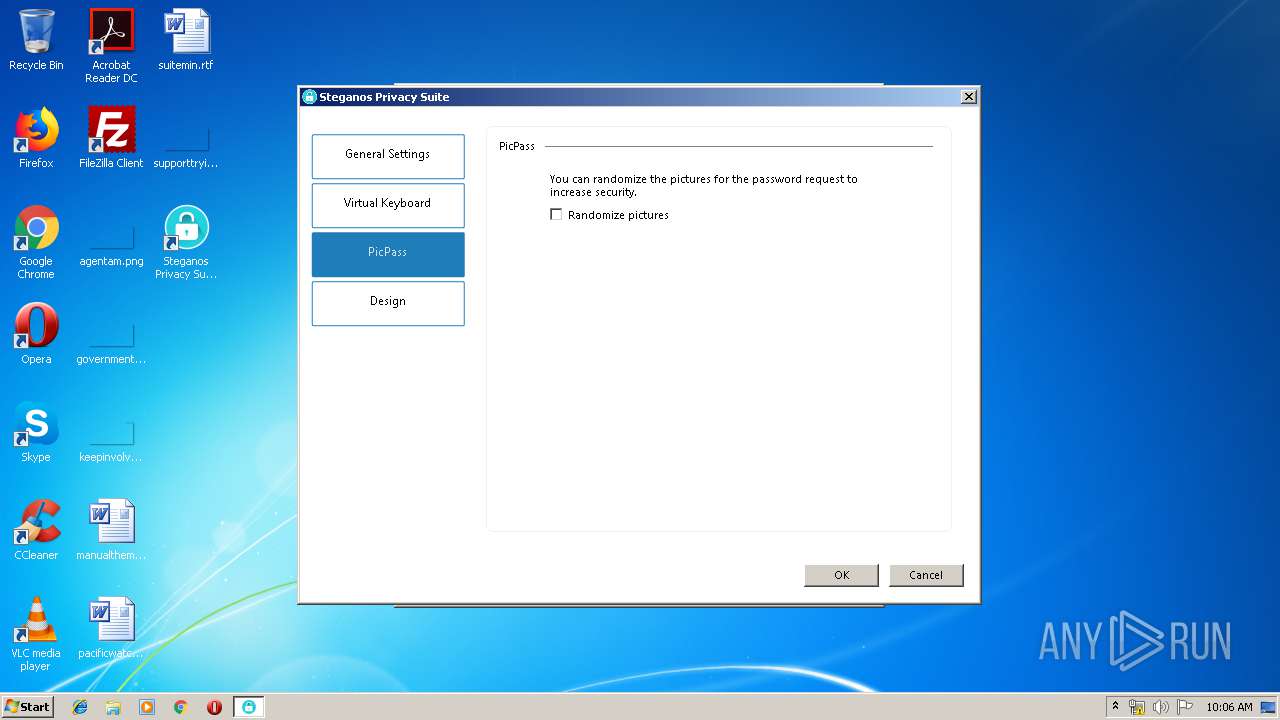
- Suite.exe (PID: 3004)
- Suite.exe (PID: 980)
- Updater.exe (PID: 3680)
- Suite.exe (PID: 2588)
Loads dropped or rewritten executable
- sss21int.exe (PID: 2836)
- sss21int.exe (PID: 1888)
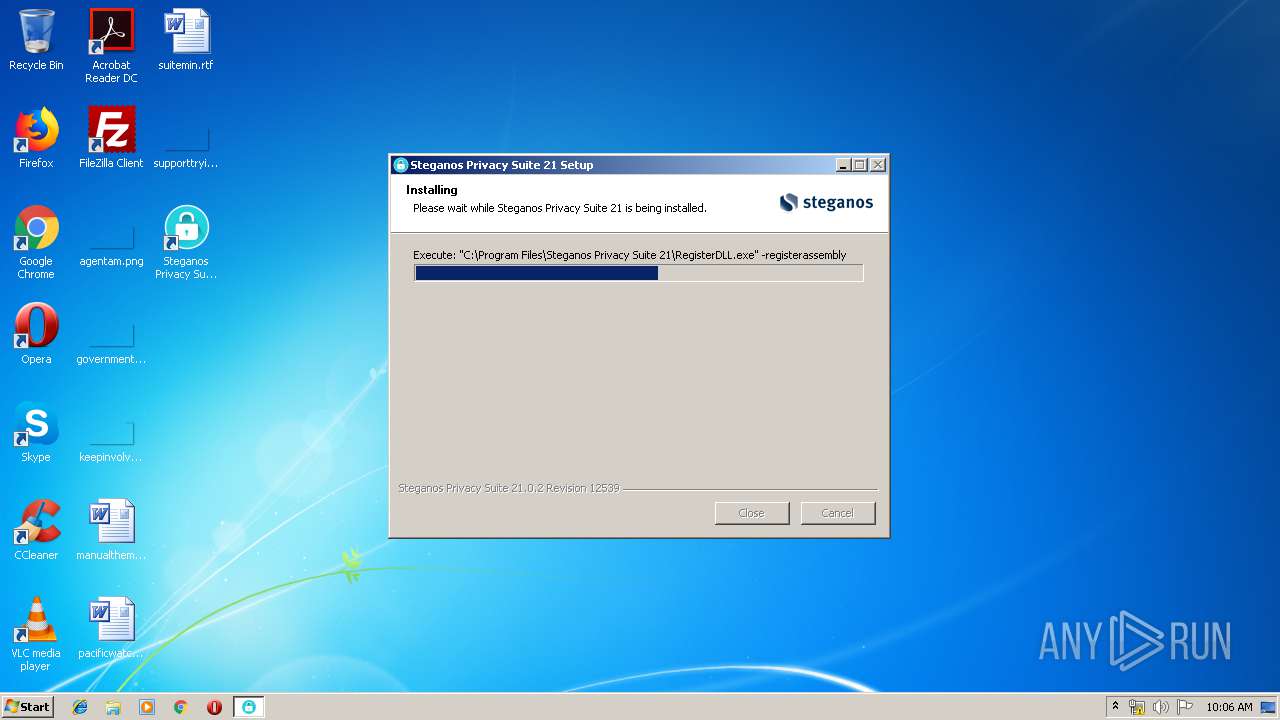
- RegisterDLL.exe (PID: 2720)
- regsvr32.exe (PID: 2188)
- iexplore.exe (PID: 3720)
- SteganosHotKeyService.exe (PID: 3192)
- SteganosHotKeyService.exe (PID: 3284)
- regsvr32.exe (PID: 700)
- Safe.exe (PID: 3304)
- PasswordManager.exe (PID: 2948)
Changes the autorun value in the registry
- SteganosHotKeyService.exe (PID: 3284)
- sss21int.exe (PID: 1888)
Detects Cygwin installation
- sss21int.exe (PID: 1888)
Registers / Runs the DLL via REGSVR32.EXE
- sss21int.exe (PID: 1888)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2924)
- sss21int.exe (PID: 2836)
- sss21int.exe (PID: 1888)
Cleans NTFS data-stream (Zone Identifier)
- chrome.exe (PID: 2924)
Application launched itself
- sss21int.exe (PID: 2836)
- Suite.exe (PID: 3004)
Executed as Windows Service
- vssvc.exe (PID: 2488)
Searches for installed software
- sss21int.exe (PID: 1888)
- DllHost.exe (PID: 1752)
Executed via COM
- DllHost.exe (PID: 1752)
- DrvInst.exe (PID: 3396)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3120)
Creates files in the Windows directory
- sss21int.exe (PID: 1888)
Creates files in the user directory
- passwordmanagercom.exe (PID: 3724)
- SteganosHotKeyService.exe (PID: 3284)
- PasswordManager.exe (PID: 2948)
- sss21int.exe (PID: 1888)
- 7za.exe (PID: 1152)
- 7za.exe (PID: 3856)
- Suite.exe (PID: 980)
- regsvr32.exe (PID: 2188)
- Updater.exe (PID: 2956)
- Suite.exe (PID: 3004)
- Notifier.exe (PID: 3880)
- Safe.exe (PID: 3304)
Creates files in the driver directory
- sss21int.exe (PID: 1888)
Creates COM task schedule object
- RegisterDLL.exe (PID: 2720)
- regsvr32.exe (PID: 700)
- regsvr32.exe (PID: 2188)
Creates a software uninstall entry
- sss21int.exe (PID: 1888)
Modifies the open verb of a shell class
- sss21int.exe (PID: 1888)
Starts Internet Explorer
- Updater.exe (PID: 2956)
Creates files in the program directory
- sss21int.exe (PID: 1888)
Reads internet explorer settings
- Suite.exe (PID: 3004)
- Safe.exe (PID: 3304)
Changes IE settings (feature browser emulation)
- Notifier.exe (PID: 3880)
Reads Internet Cache Settings
- Suite.exe (PID: 3004)
INFO
Application launched itself
- chrome.exe (PID: 2924)
- iexplore.exe (PID: 3720)
Reads the hosts file
- chrome.exe (PID: 944)
- chrome.exe (PID: 2924)
Reads Internet Cache Settings
- chrome.exe (PID: 2924)
- iexplore.exe (PID: 1536)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2488)
Changes internet zones settings
- iexplore.exe (PID: 3720)
Reads settings of System Certificates
- Suite.exe (PID: 3004)
- iexplore.exe (PID: 3720)
- Safe.exe (PID: 3304)
Reads internet explorer settings
- iexplore.exe (PID: 1536)
Creates files in the user directory
- iexplore.exe (PID: 1536)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
78
Monitored processes
35
Malicious processes
8
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x705ba9d0,0x705ba9e0,0x705ba9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 700 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\Steganos Privacy Suite 21\ShellExtension.dll" | C:\Windows\system32\regsvr32.exe | — | sss21int.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,8595921916206362550,4542714112104632850,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=14831669685992368009 --mojo-platform-channel-handle=1536 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 980 | "C:\Program Files\Steganos Privacy Suite 21\Suite.exe" -install | C:\Program Files\Steganos Privacy Suite 21\Suite.exe | — | sss21int.exe | |||||||||||
User: admin Company: Steganos Software GmbH Integrity Level: MEDIUM Description: Steganos Privacy Suite Exit code: 4294967295 Version: 21.0.2.12539 Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Steganos Privacy Suite 21\7za.exe" x -t7z -y "SSS21.7z" -o"C:\Users\admin\AppData\Roaming\Steganos\Themes" | C:\Program Files\Steganos Privacy Suite 21\7za.exe | — | Suite.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Standalone Console Exit code: 0 Version: 9.20 Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,8595921916206362550,4542714112104632850,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5444148431850326577 --mojo-platform-channel-handle=1052 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3720 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1752 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1888 | "C:\Users\admin\Downloads\sss21int.exe" /UAC:2017C /NCRC | C:\Users\admin\Downloads\sss21int.exe | sss21int.exe | ||||||||||||
User: admin Company: Steganos Software GmbH Integrity Level: HIGH Exit code: 1223 Version: 21.0.2.0 Rev 12539 Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,8595921916206362550,4542714112104632850,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16166264904745494527 --mojo-platform-channel-handle=3488 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 187
Read events
2 475
Write events
694
Delete events
18
Modification events
| (PID) Process: | (3140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2924-13214048672365000 |
Value: 259 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
85
Suspicious files
819
Text files
391
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\27801476-799b-4284-8e09-9b1675180883.tmp | — | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFf45e9.TMP | text | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFf45e9.TMP | text | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RFf4676.TMP | text | |
MD5:— | SHA256:— | |||
| 2924 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFf45e9.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
43
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3004 | Suite.exe | GET | — | 8.248.119.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
3720 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3004 | Suite.exe | 159.122.87.148:443 | dev.visualwebsiteoptimizer.com | SoftLayer Technologies Inc. | DE | unknown |
1536 | iexplore.exe | 74.125.206.82:443 | html5shim.googlecode.com | Google Inc. | US | whitelisted |
1536 | iexplore.exe | 216.58.210.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3004 | Suite.exe | 8.248.119.254:80 | www.download.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
1536 | iexplore.exe | 104.109.64.186:443 | use.typekit.net | Akamai International B.V. | NL | whitelisted |
3004 | Suite.exe | 64.233.167.156:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
1536 | iexplore.exe | 172.217.22.40:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
944 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
944 | chrome.exe | 37.208.111.94:443 | file.steganos.com | uvensys GmbH | DE | suspicious |
944 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
file.steganos.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
steganos.com |
| suspicious |
backend.steganos.com |
| suspicious |
www.bing.com |
| whitelisted |
www.steganos.com |
| suspicious |
Threats
Process | Message |
|---|---|
regsvr32.exe | *** Dll attach |
Suite.exe | *** IE is in front, use SetForegroundWindow()... |