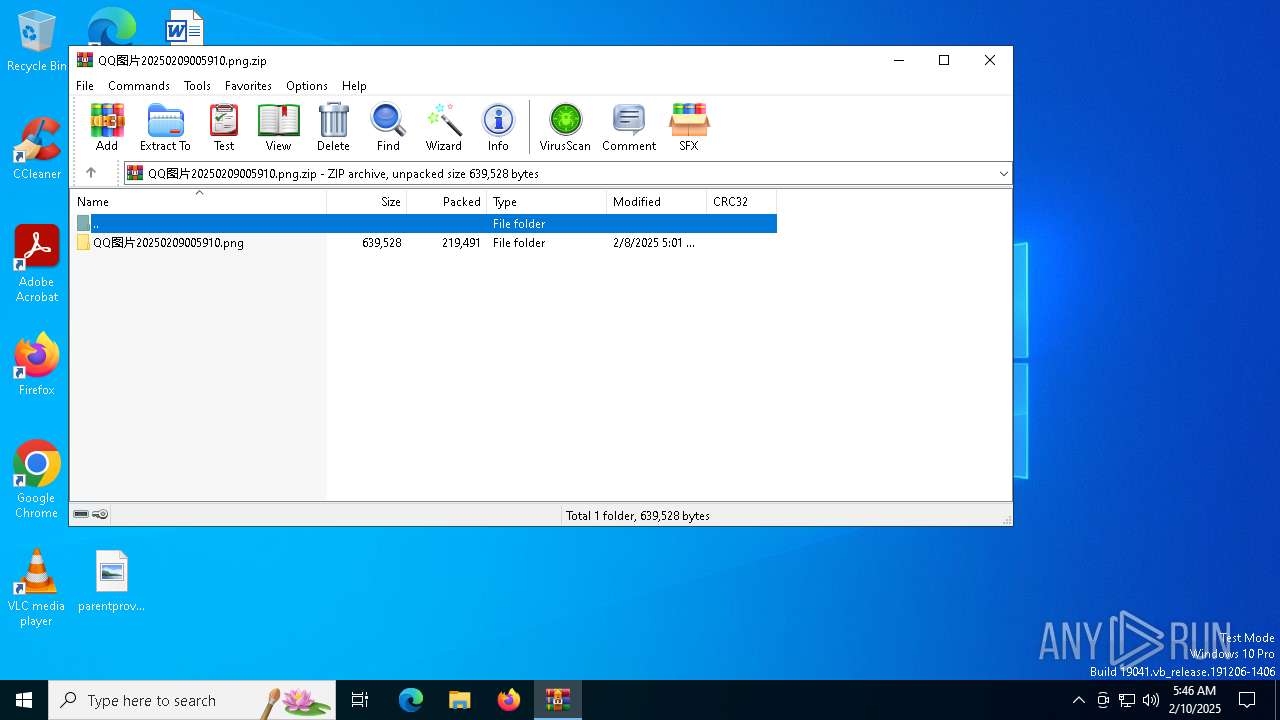
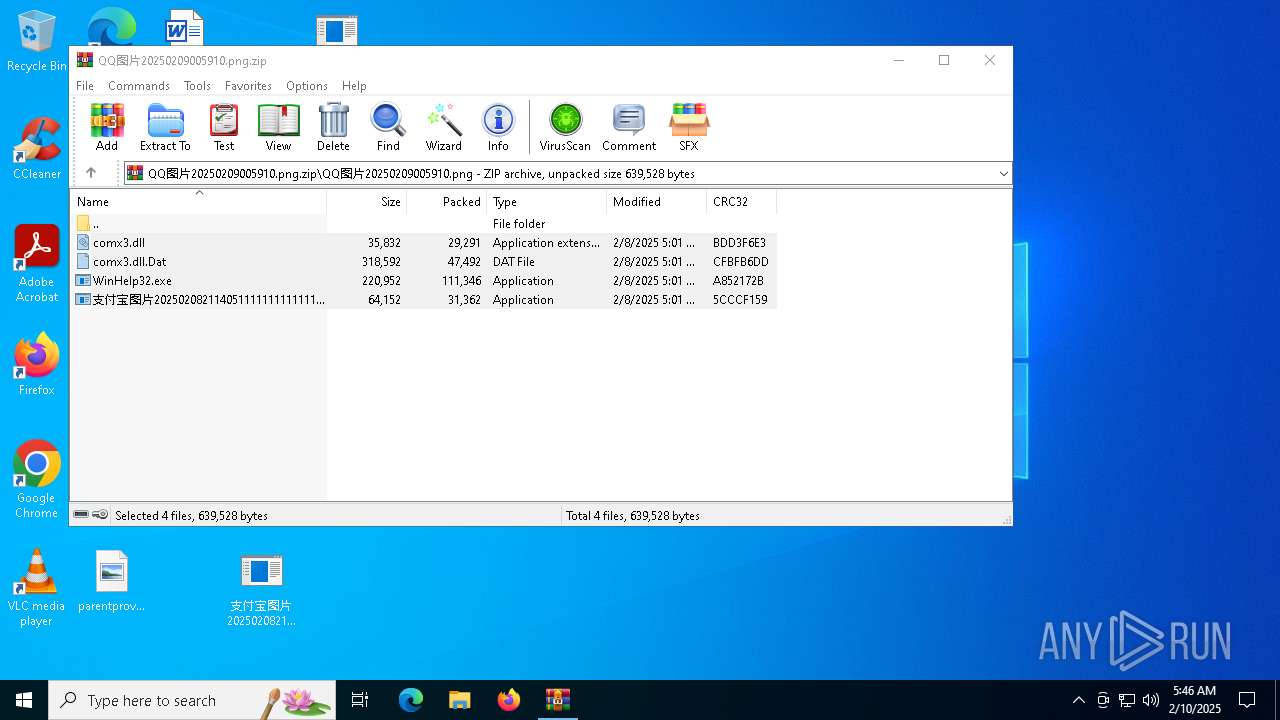
| File name: | QQ图片20250209005910.png.zip |
| Full analysis: | https://app.any.run/tasks/b8b084fa-c42b-41b7-beb3-5d68e126fb03 |
| Verdict: | Malicious activity |
| Analysis date: | February 10, 2025, 05:46:19 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 350E725D0E310A29DE1FBF939AED882F |
| SHA1: | 7CFF13E1ADFD8A3149EC88C43EA25297D3D6ADF4 |
| SHA256: | 9AF9E0784AB9D5DDBD7F21C4065F23ED7A5BA224FB28A66DAFEB528DEA5525A0 |
| SSDEEP: | 6144:NOLK3UO34DnIDP3EUIi1g+MCHaOr2qgYgor6oD:eK3W7WUFng6oD |
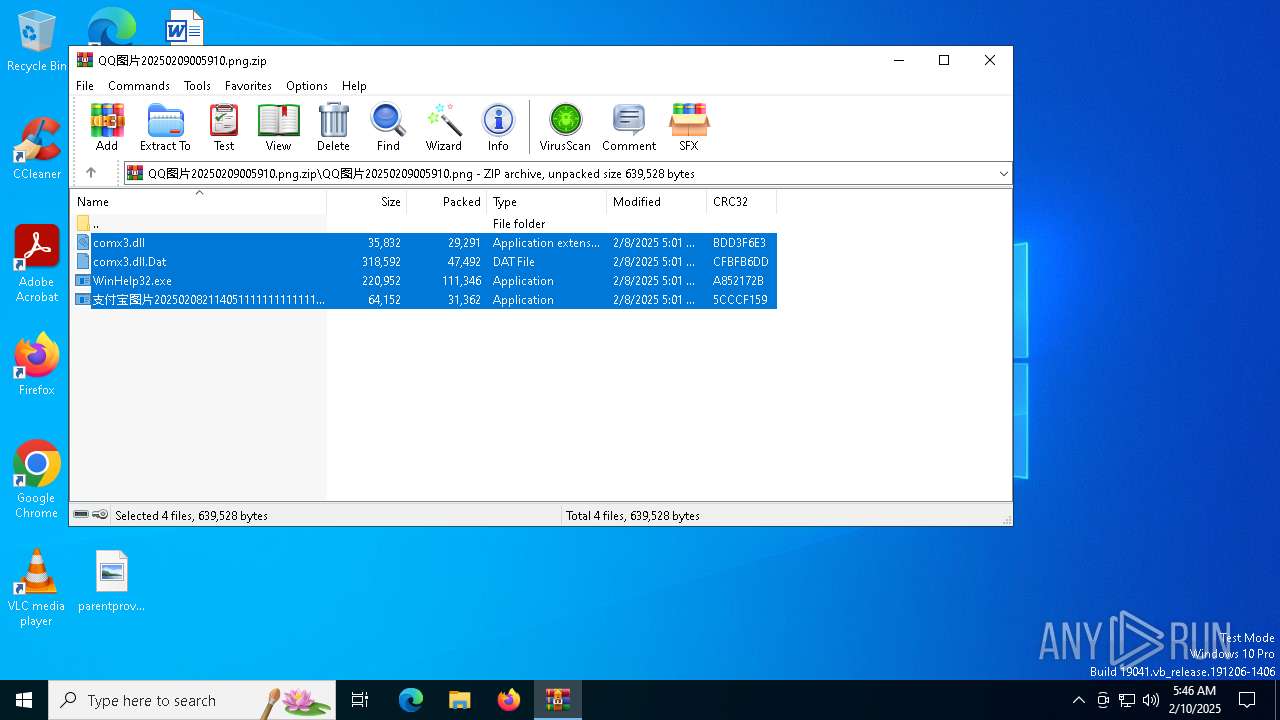
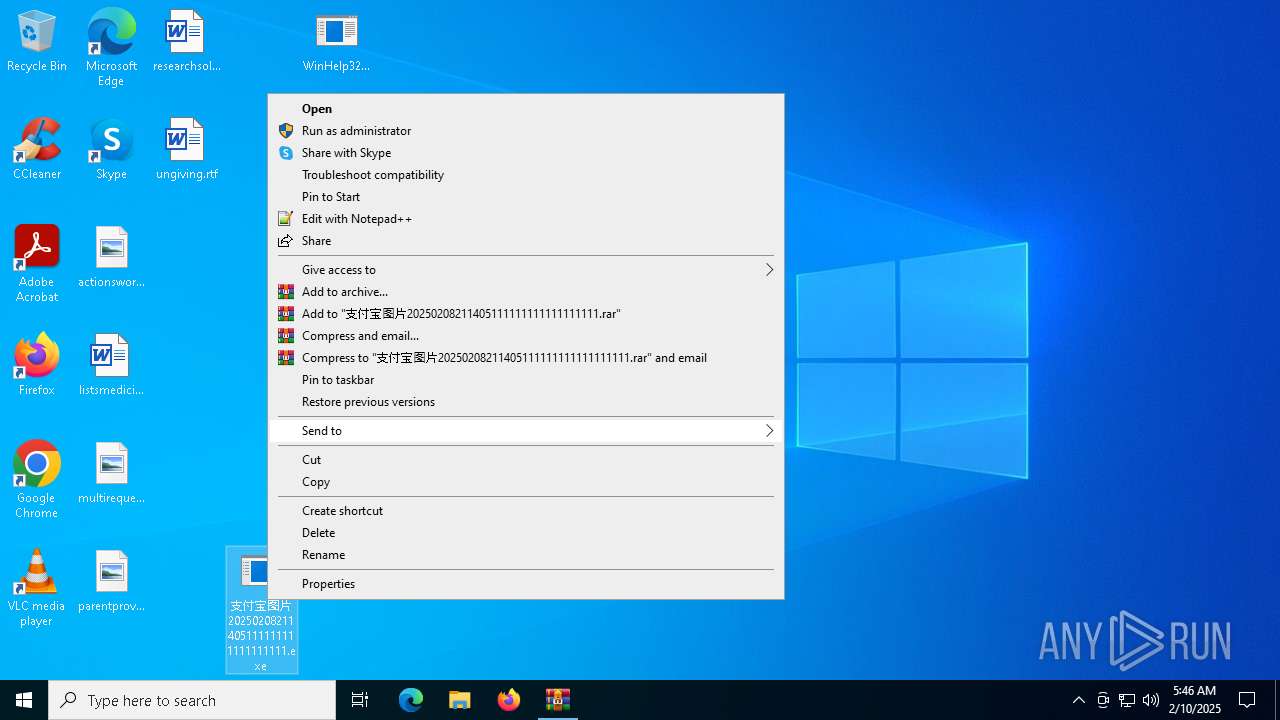
MALICIOUS
Executing a file with an untrusted certificate
- 支付宝图片20250208211405111111111111111111.exe (PID: 7096)
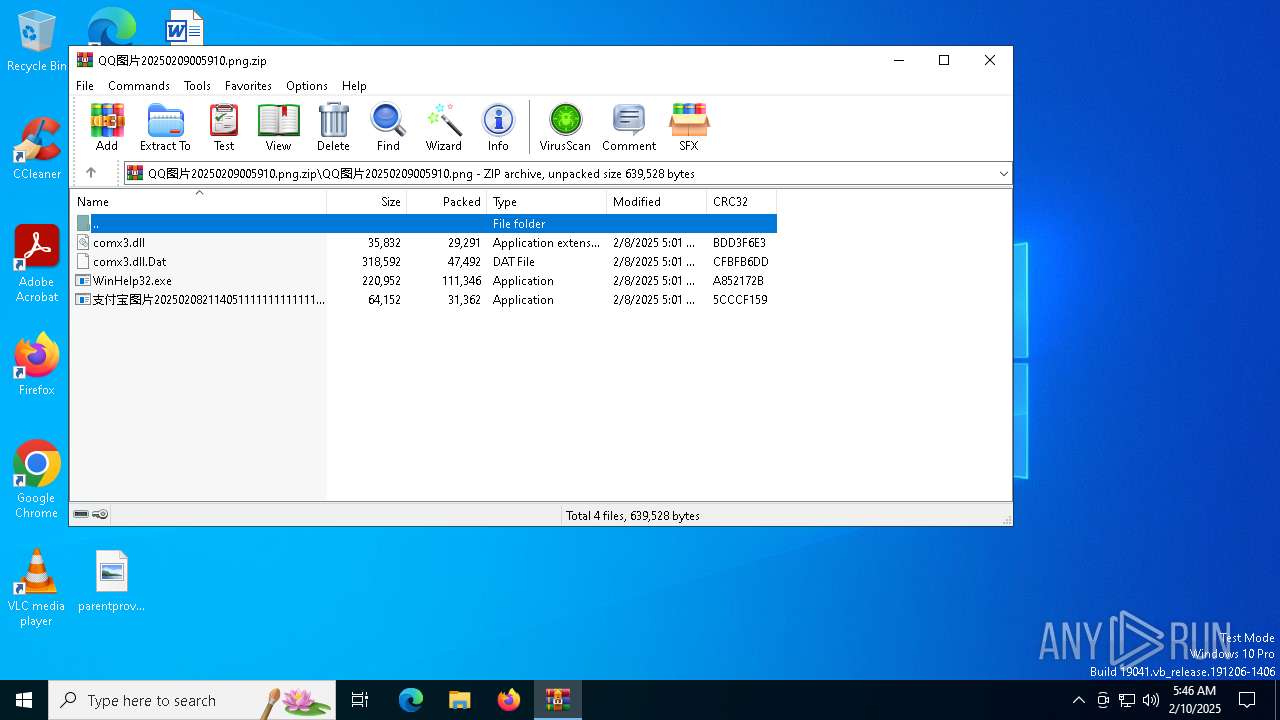
Generic archive extractor
- WinRAR.exe (PID: 1480)
SUSPICIOUS
Executable content was dropped or overwritten
- 支付宝图片20250208211405111111111111111111.exe (PID: 7096)
Executes as Windows Service
- WinHelp32.exe (PID: 7124)
Connects to unusual port
- svchost.exe (PID: 7156)
INFO
The sample compiled with chinese language support
- WinRAR.exe (PID: 1480)
- 支付宝图片20250208211405111111111111111111.exe (PID: 7096)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1480)
Manual execution by a user
- 支付宝图片20250208211405111111111111111111.exe (PID: 7096)
Reads the computer name
- 支付宝图片20250208211405111111111111111111.exe (PID: 7096)
- WinHelp32.exe (PID: 7124)
Checks supported languages
- 支付宝图片20250208211405111111111111111111.exe (PID: 7096)
- WinHelp32.exe (PID: 7124)
Creates files in the program directory
- WinHelp32.exe (PID: 7124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:02:09 01:01:44 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | QQͼƬ20250209005910.png/ |
Total processes
130
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1480 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\QQ图片20250209005910.png.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7096 | "C:\Users\admin\Desktop\支付宝图片20250208211405111111111111111111.exe" | C:\Users\admin\Desktop\支付宝图片20250208211405111111111111111111.exe | explorer.exe | ||||||||||||
User: admin Company: Beijing Rising Information Technology Co., Ltd. Integrity Level: HIGH Description: RsStub Application Exit code: 0 Version: 1.0.0.9 Modules
| |||||||||||||||
| 7124 | C:\windows\WinHelp32.exe -svc | C:\Windows\WinHelp32.exe | services.exe | ||||||||||||
User: SYSTEM Company: Beijing Rising Information Technology Co., Ltd. Integrity Level: SYSTEM Description: RsMgrSvc Application Exit code: 0 Version: 1.0.0.69 Modules
| |||||||||||||||
| 7156 | C:\WINDOWS\SysWOW64\svchost.exe -Puppet | C:\Windows\SysWOW64\svchost.exe | WinHelp32.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 161
Read events
2 153
Write events
8
Delete events
0
Modification events
| (PID) Process: | (1480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\QQ图片20250209005910.png.zip | |||
| (PID) Process: | (1480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1480) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
5
Suspicious files
2
Text files
2
Unknown types
0
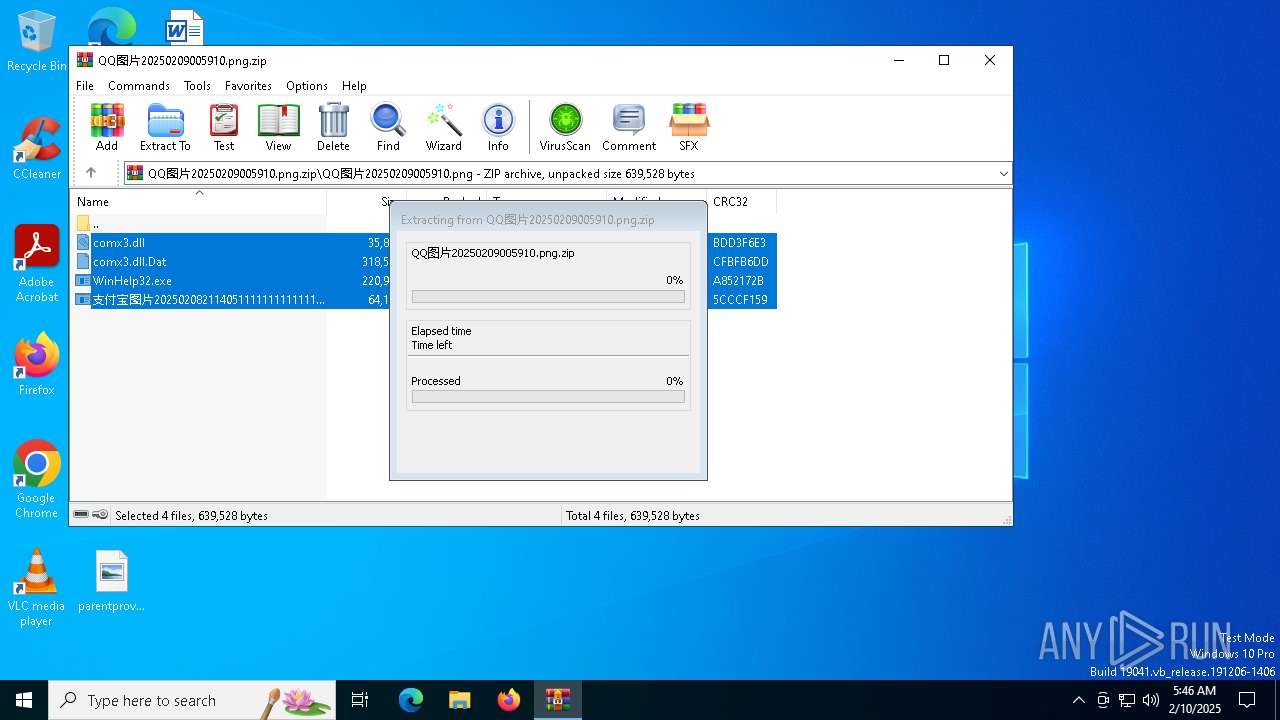
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1480 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1480.20356\QQ图片20250209005910.png\支付宝图片20250208211405111111111111111111.exe | executable | |
MD5:7A762BE1D46BB1ED07EACEC047CBD1CC | SHA256:6BF8B140A8E451227050ACD5A2B586AD1B2E4DA27C32AE1BB9FB64E2B58D8B29 | |||
| 1480 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1480.20356\QQ图片20250209005910.png\comx3.dll | executable | |
MD5:82A4B7EE845D0F4EAA79B810723EBB8D | SHA256:B6203C9D086B6D78D1C5BCC50847FAD88D9F0951ABE231D4167602D42DB9C74F | |||
| 1480 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1480.20356\QQ图片20250209005910.png\WinHelp32.exe | executable | |
MD5:648A00D1C34ECED63339D82E876463A5 | SHA256:C85637900DA9D36FD65DC2E900AC74A1458AC1F9B51815247542E79B9C4F3B3D | |||
| 1480 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1480.20356\QQ图片20250209005910.png\comx3.dll.Dat | binary | |
MD5:423307D9ABE8B34C8FC8CD96AA9F3AEC | SHA256:0151F803EFBA1555694EAC5FC53B023F60568257610E48E230C099EBFC9A2D5E | |||
| 7096 | 支付宝图片20250208211405111111111111111111.exe | C:\Windows\comx3.dll | executable | |
MD5:82A4B7EE845D0F4EAA79B810723EBB8D | SHA256:B6203C9D086B6D78D1C5BCC50847FAD88D9F0951ABE231D4167602D42DB9C74F | |||
| 7124 | WinHelp32.exe | C:\Windows\WinHelp32.exe.log | text | |
MD5:C2F4B55E0C82139747F741396DFB71E1 | SHA256:1493EDE7461D7B8C94D1A06A3C63292440C8A6FB0A87C563F590AF26633E2B97 | |||
| 7096 | 支付宝图片20250208211405111111111111111111.exe | C:\Windows\WinHelp32.exe | executable | |
MD5:648A00D1C34ECED63339D82E876463A5 | SHA256:C85637900DA9D36FD65DC2E900AC74A1458AC1F9B51815247542E79B9C4F3B3D | |||
| 7096 | 支付宝图片20250208211405111111111111111111.exe | C:\Windows\comx3.dll.dat | binary | |
MD5:423307D9ABE8B34C8FC8CD96AA9F3AEC | SHA256:0151F803EFBA1555694EAC5FC53B023F60568257610E48E230C099EBFC9A2D5E | |||
| 7096 | 支付宝图片20250208211405111111111111111111.exe | C:\Windows\SysWOW64\ini.ini | text | |
MD5:FE9AF7587D65300338177538AA72F924 | SHA256:556243E27A369FBDFF1ECFB413B7540F1EB4E6BECBA03B76D221443B0D022351 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
65
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5064 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6560 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6896 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6896 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6068 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 104.126.37.153:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1176 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1076 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
6896 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
WinHelp32.exe | [2025-02-10][05:46:59:732][7124][7144]: [ALERT]Failed to call RegSaveKey, err = 0x0
|