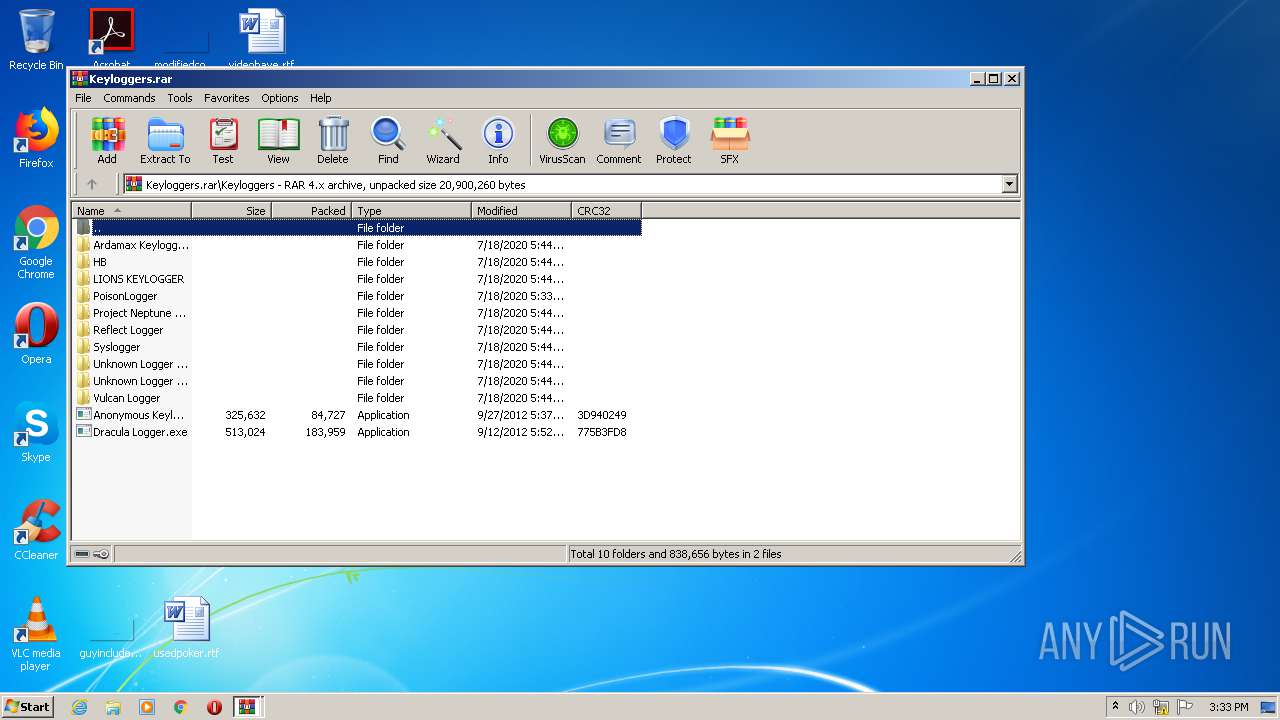
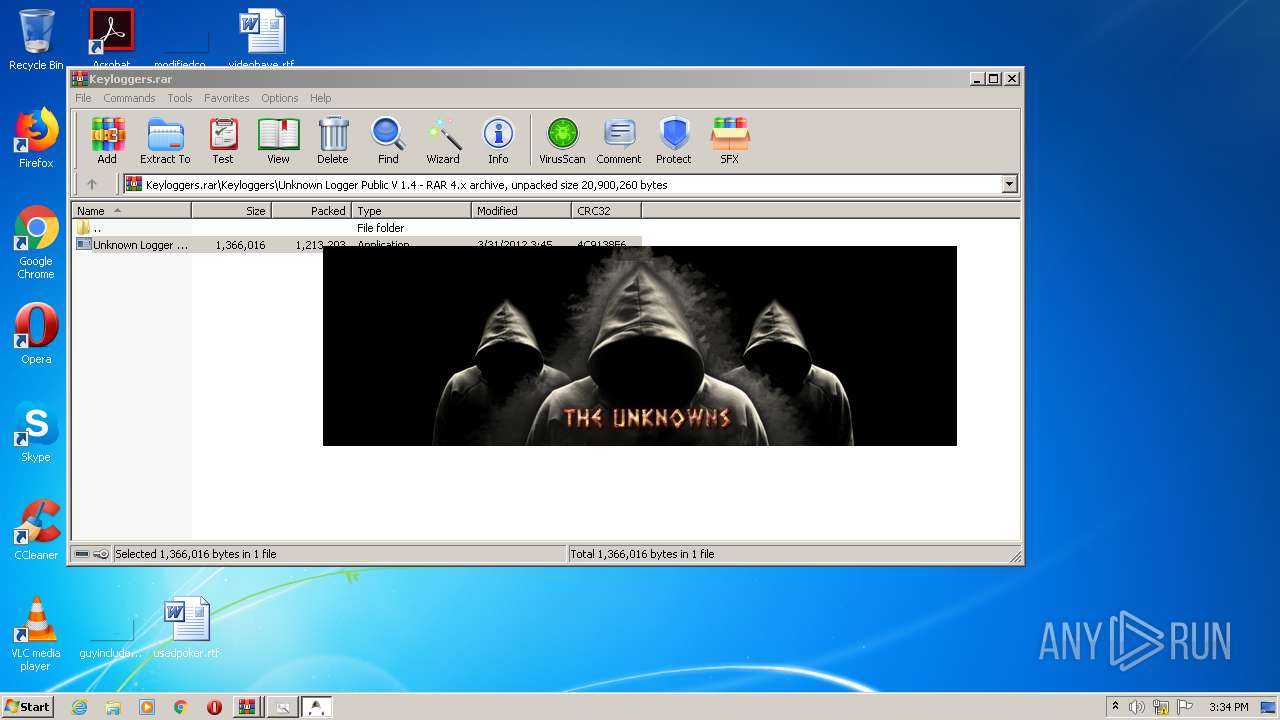
| File name: | Keyloggers.rar |
| Full analysis: | https://app.any.run/tasks/41a8fe5e-17b1-4925-8369-db72f77bdf6b |
| Verdict: | Suspicious activity |
| Analysis date: | July 18, 2020, 14:33:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | D24D2B25C241939B7E8BF92B8931D2D4 |
| SHA1: | 7BAA86890A904A988CCCC0658FAF422D2860EF9B |
| SHA256: | 9AF1EC46023D4201B15281C1635B241EA78DA04CEC850326FEC2DB08555F265E |
| SSDEEP: | 196608:2ZTH7PbJbEDkUoVYFM0j41K9ZsSkqCKA9dLvf:2ZTH7PVED5oVYFMY7xvCKsL3 |
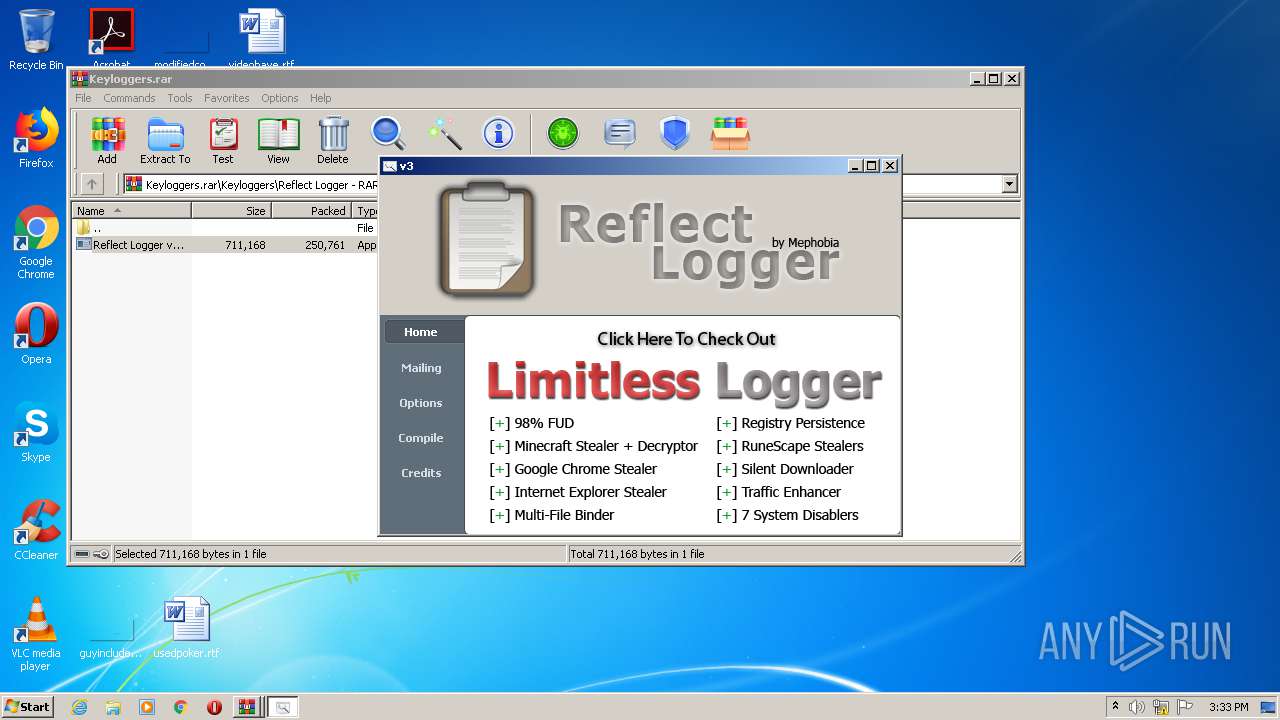
MALICIOUS
Application was dropped or rewritten from another process
- Reflect Logger v3.exe (PID: 3176)
- Reflect Logger v3.exe (PID: 2740)
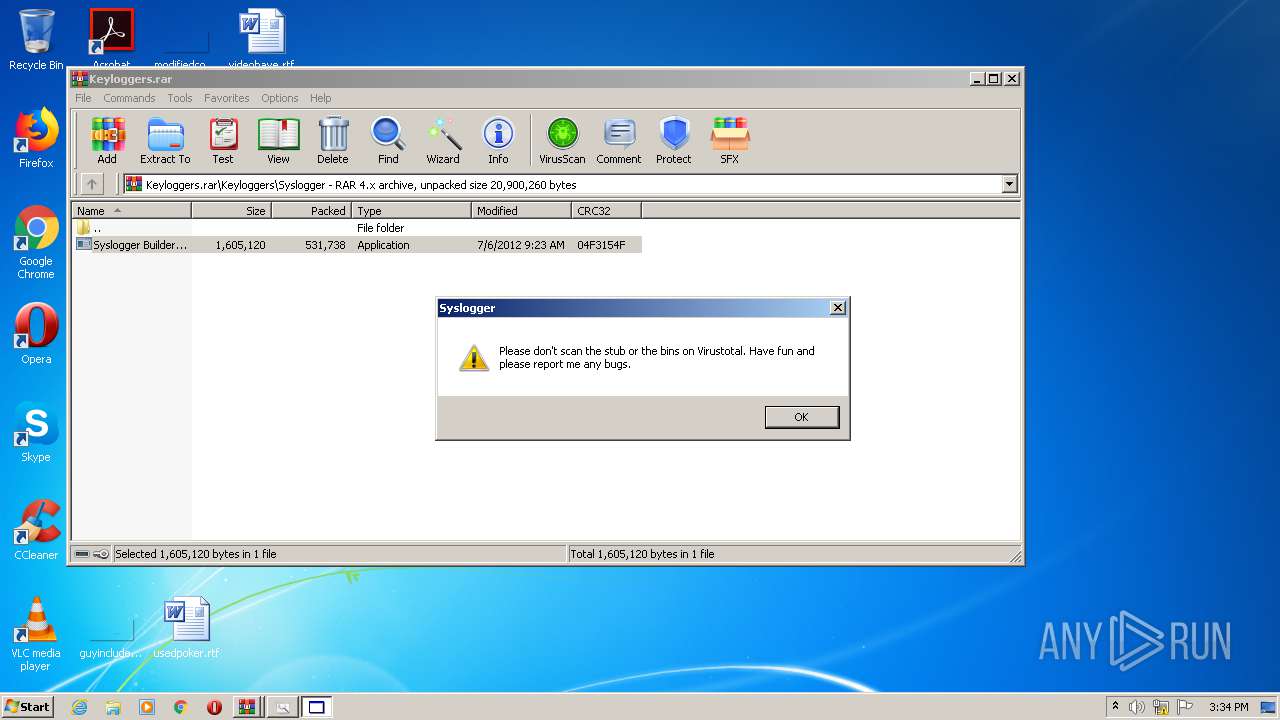
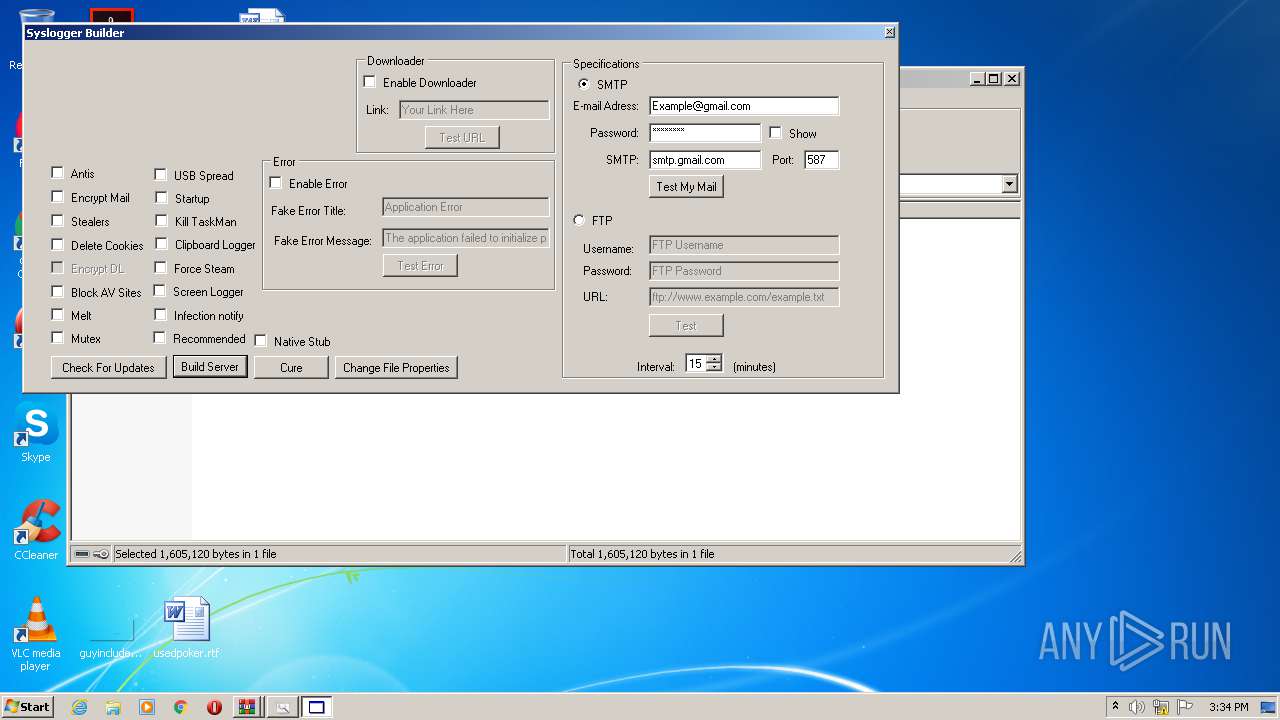
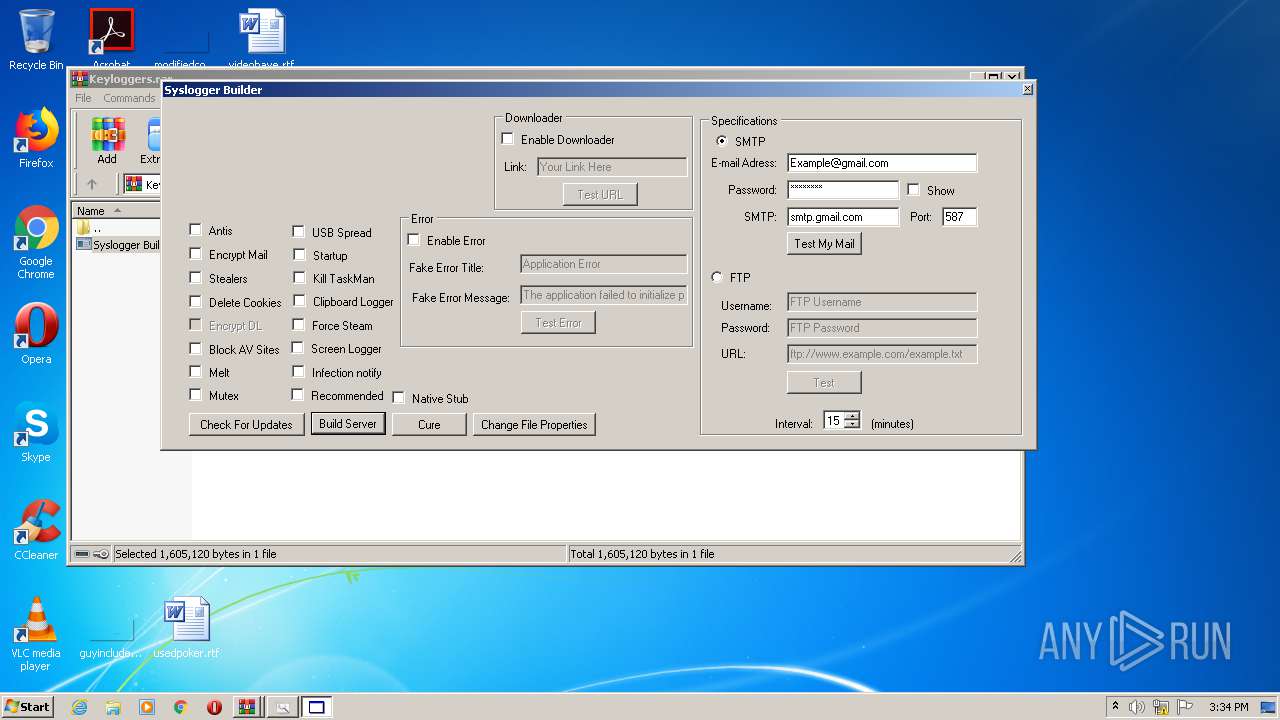
- Syslogger Builder.exe (PID: 3452)
- Unknown Logger Public V 1.4.exe (PID: 632)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3012)
Reads Internet Cache Settings
- Syslogger Builder.exe (PID: 3452)
INFO
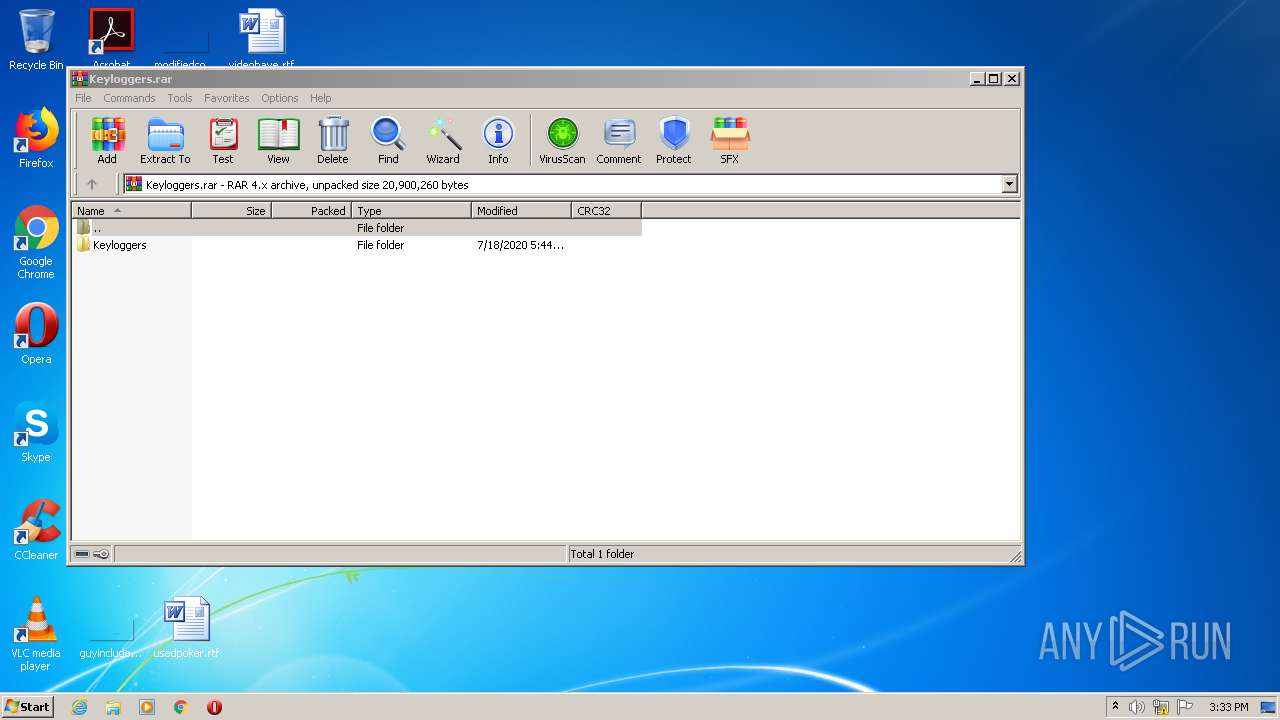
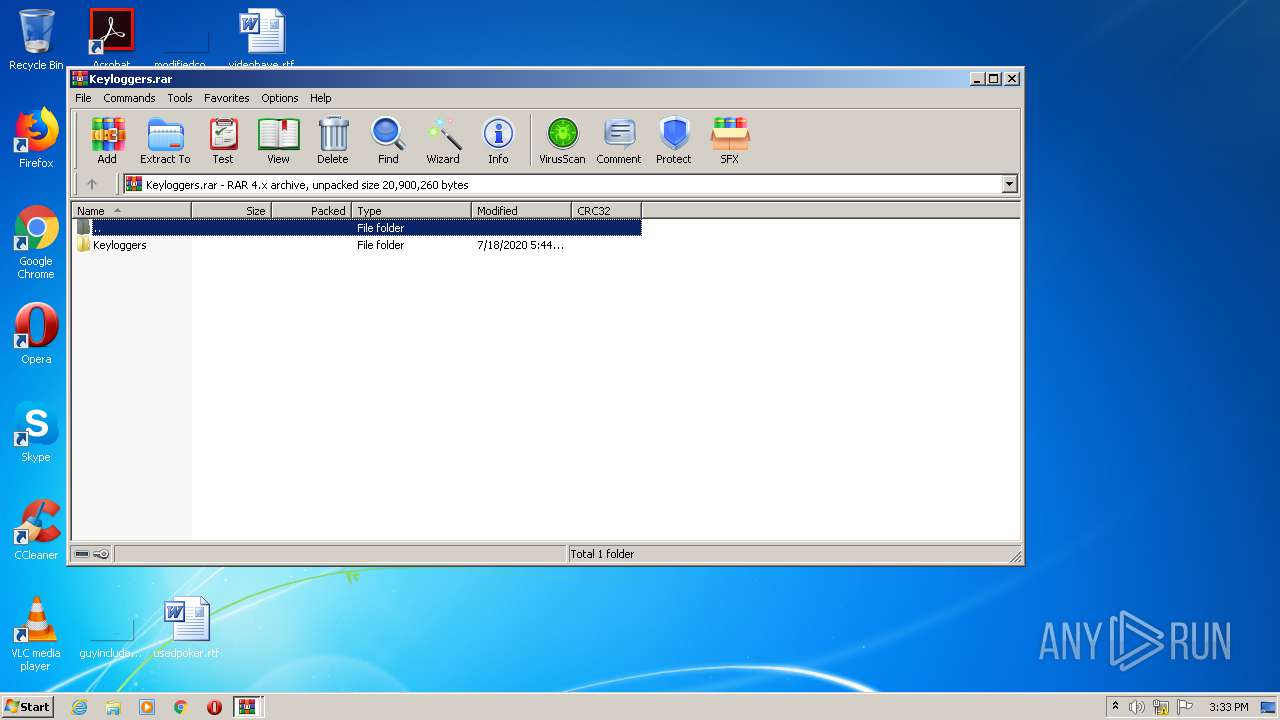
Manual execution by user
- WinRAR.exe (PID: 3012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
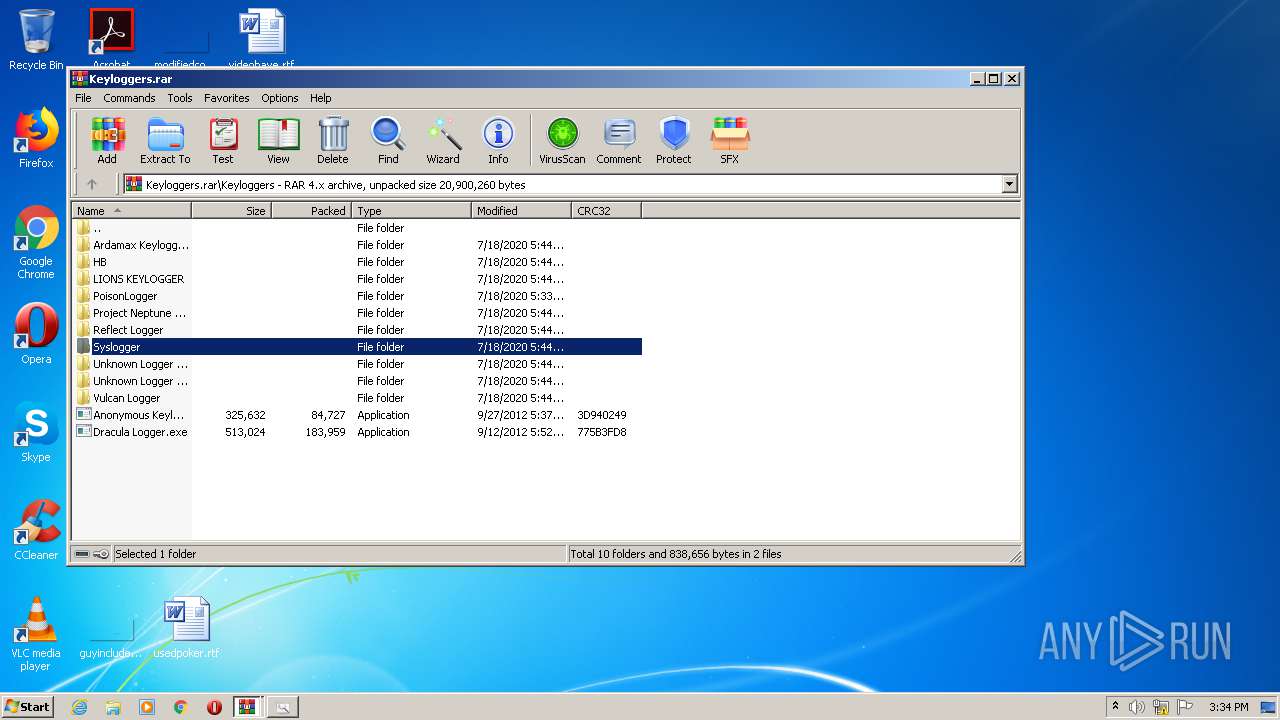
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 84782 |
|---|---|
| UncompressedSize: | 325632 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2012:09:27 05:37:16 |
| PackingMethod: | Normal |
| ArchivedFileName: | Keyloggers\Anonymous Keylogger.exe |
Total processes
43
Monitored processes
6
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
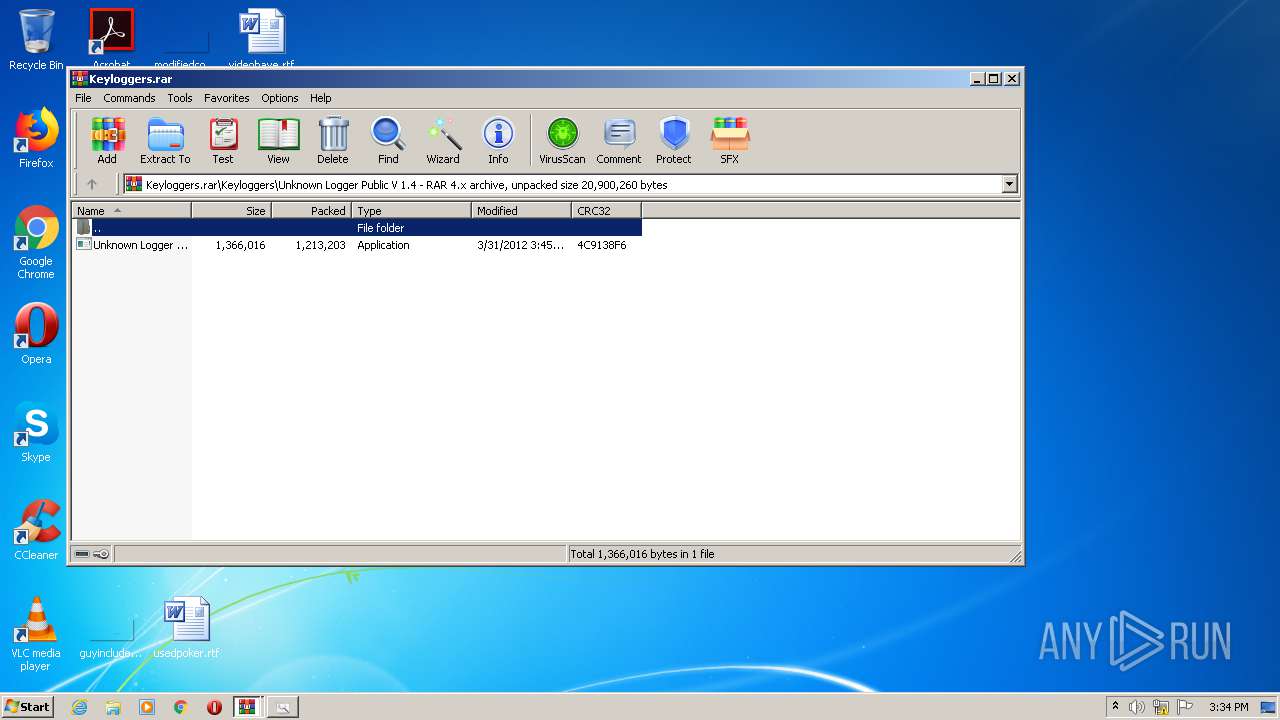
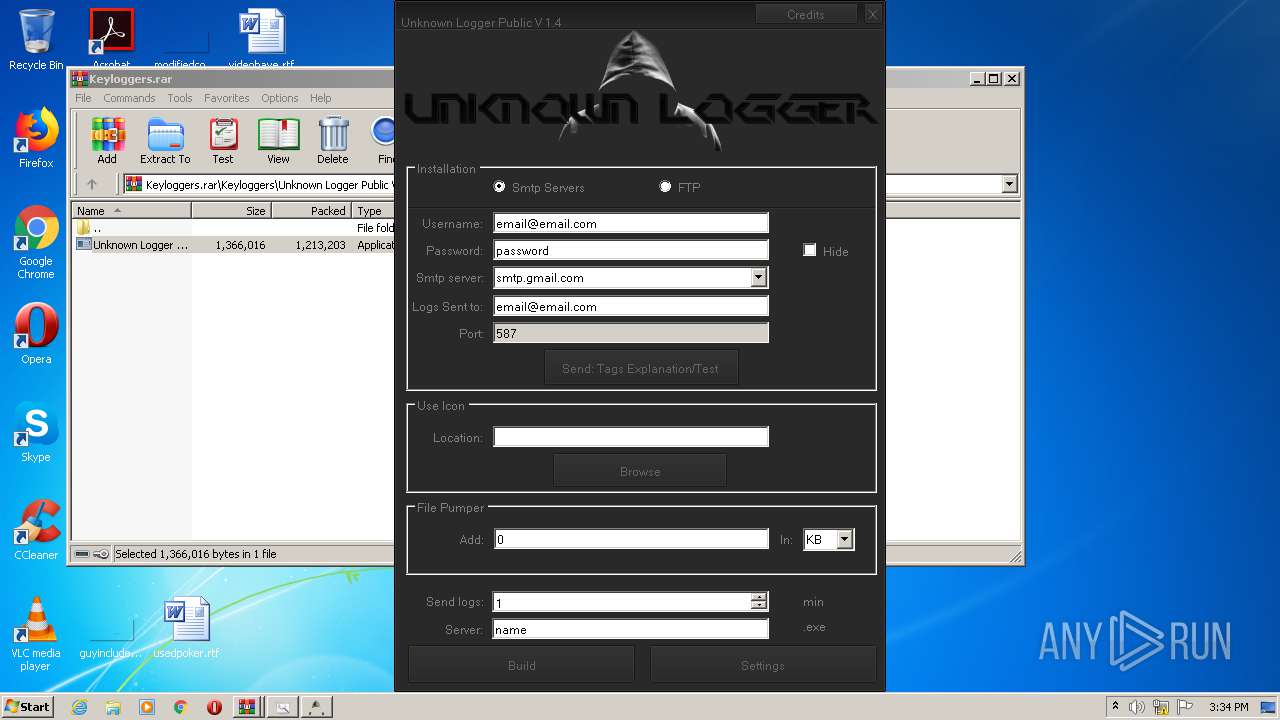
| 632 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3012.19653\Keyloggers\Unknown Logger Public V 1.4\Unknown Logger Public V 1.4.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3012.19653\Keyloggers\Unknown Logger Public V 1.4\Unknown Logger Public V 1.4.exe | — | WinRAR.exe | |||||||||||
User: admin Company: The Unknowns Integrity Level: MEDIUM Description: Unknown Logger Public V 1.4 Exit code: 0 Version: 1.4.0.0 Modules
| |||||||||||||||
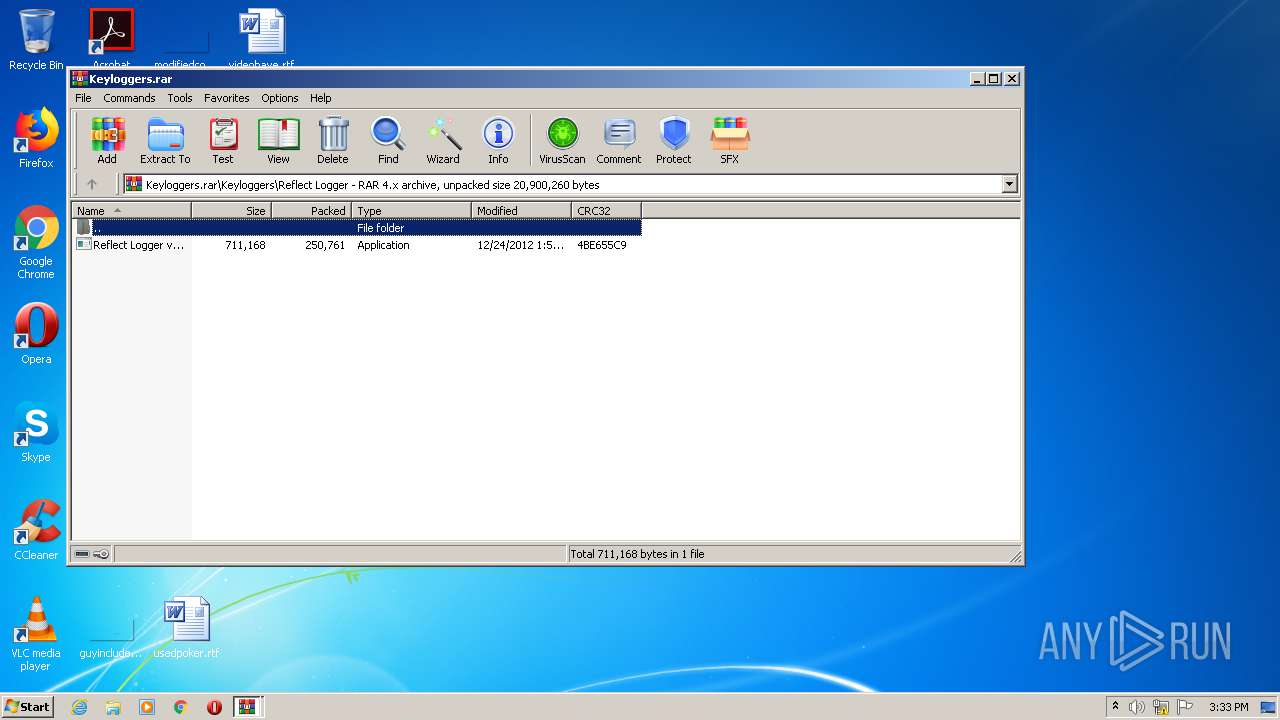
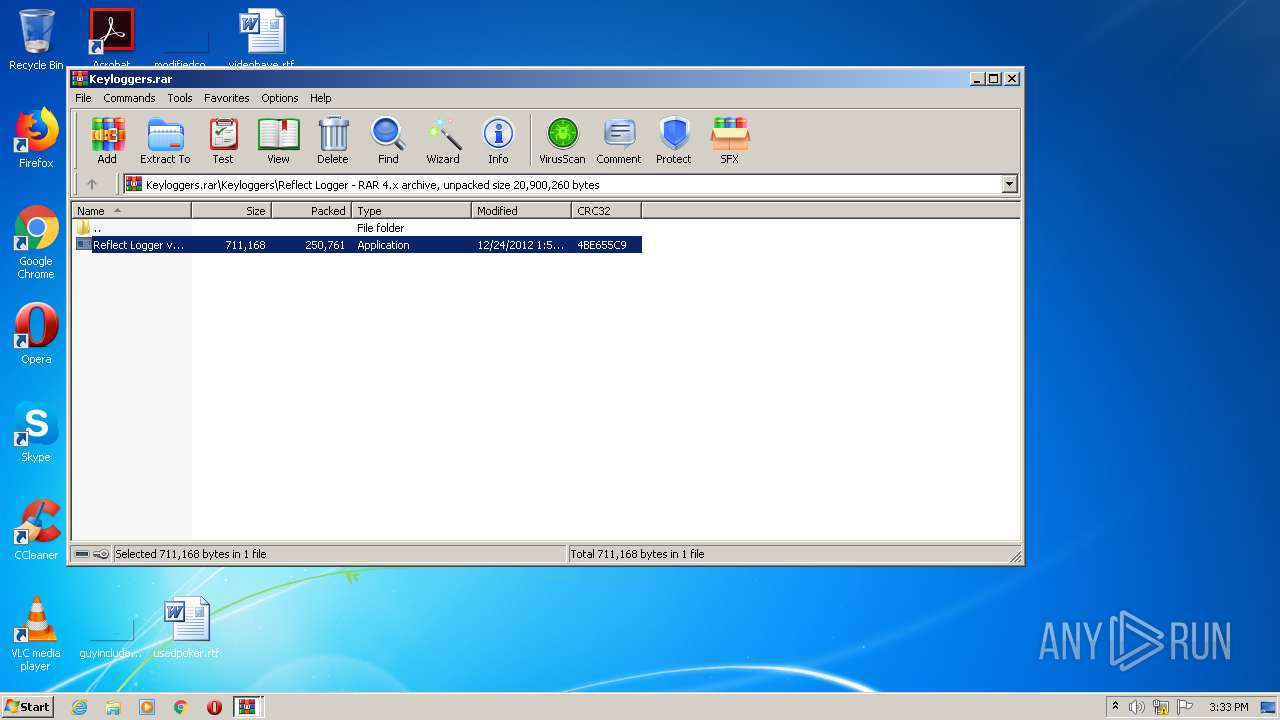
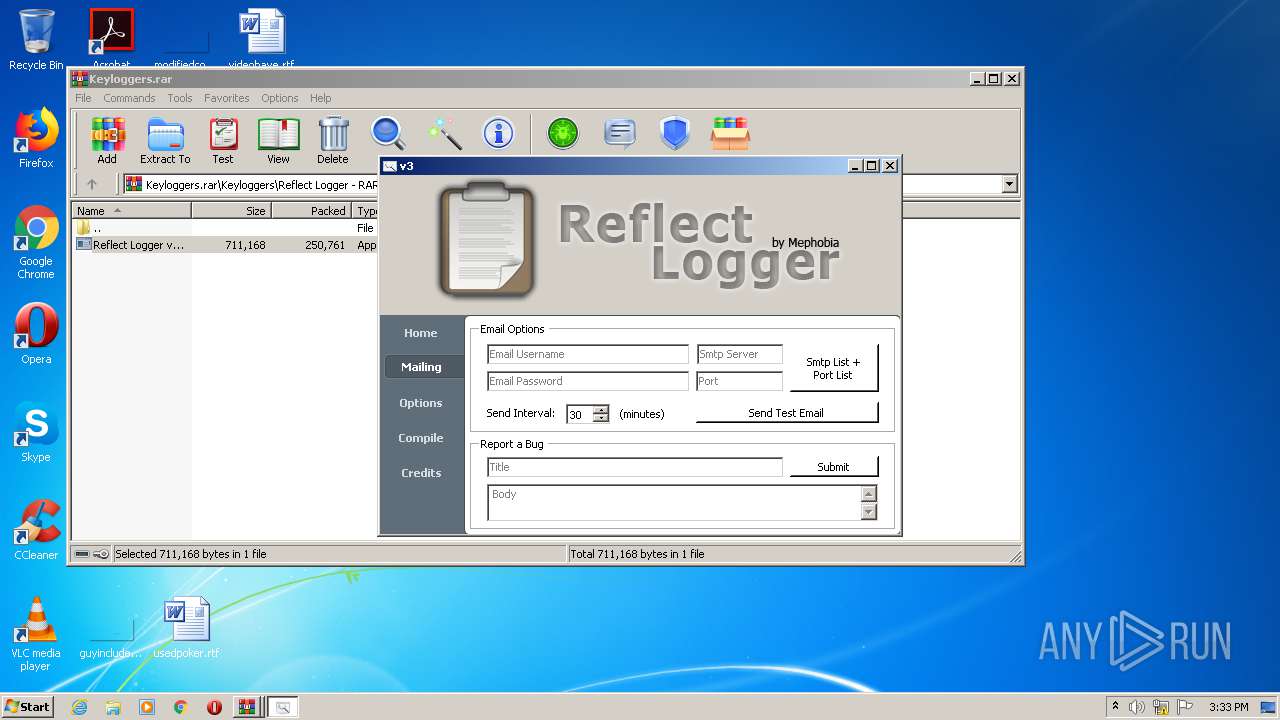
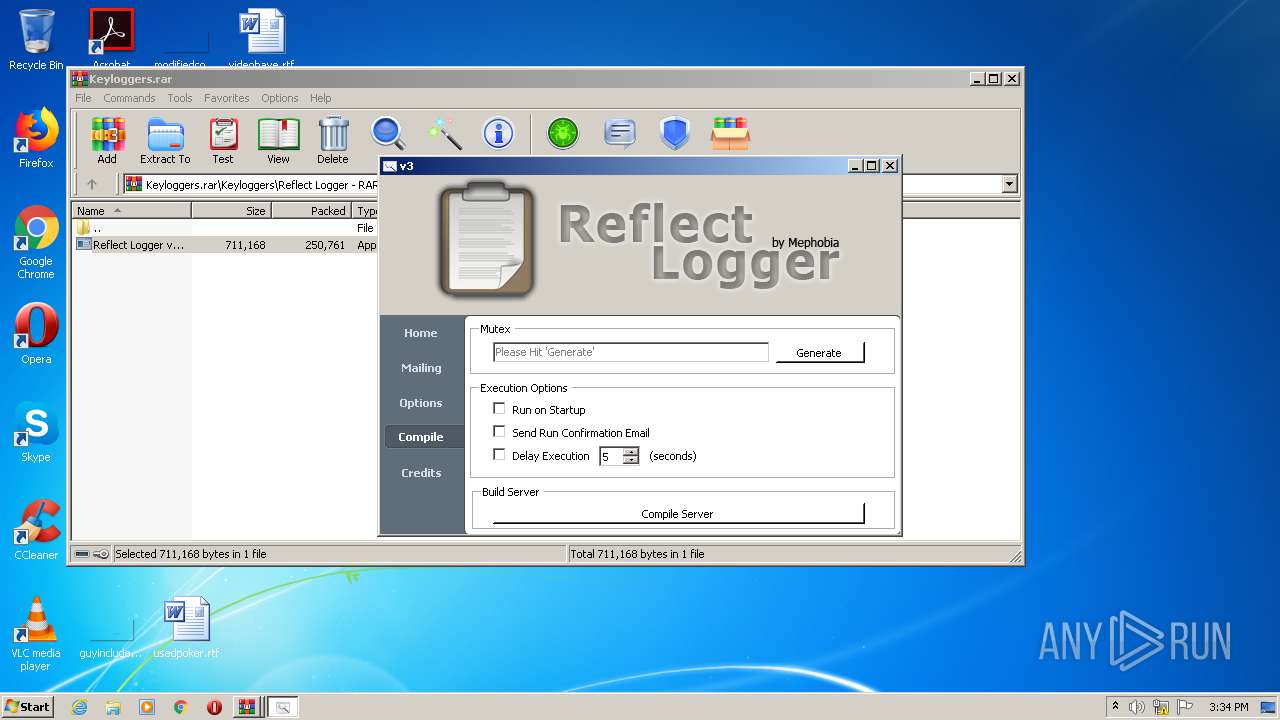
| 2740 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3012.16242\Keyloggers\Reflect Logger\Reflect Logger v3.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3012.16242\Keyloggers\Reflect Logger\Reflect Logger v3.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Mephobia HackForums Integrity Level: MEDIUM Description: Reflect Logger Exit code: 3221226540 Version: 2.0.0.0 Modules
| |||||||||||||||
| 3012 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Keyloggers.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3176 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3012.16242\Keyloggers\Reflect Logger\Reflect Logger v3.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3012.16242\Keyloggers\Reflect Logger\Reflect Logger v3.exe | WinRAR.exe | ||||||||||||
User: admin Company: Mephobia HackForums Integrity Level: HIGH Description: Reflect Logger Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
| 3364 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Keyloggers.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
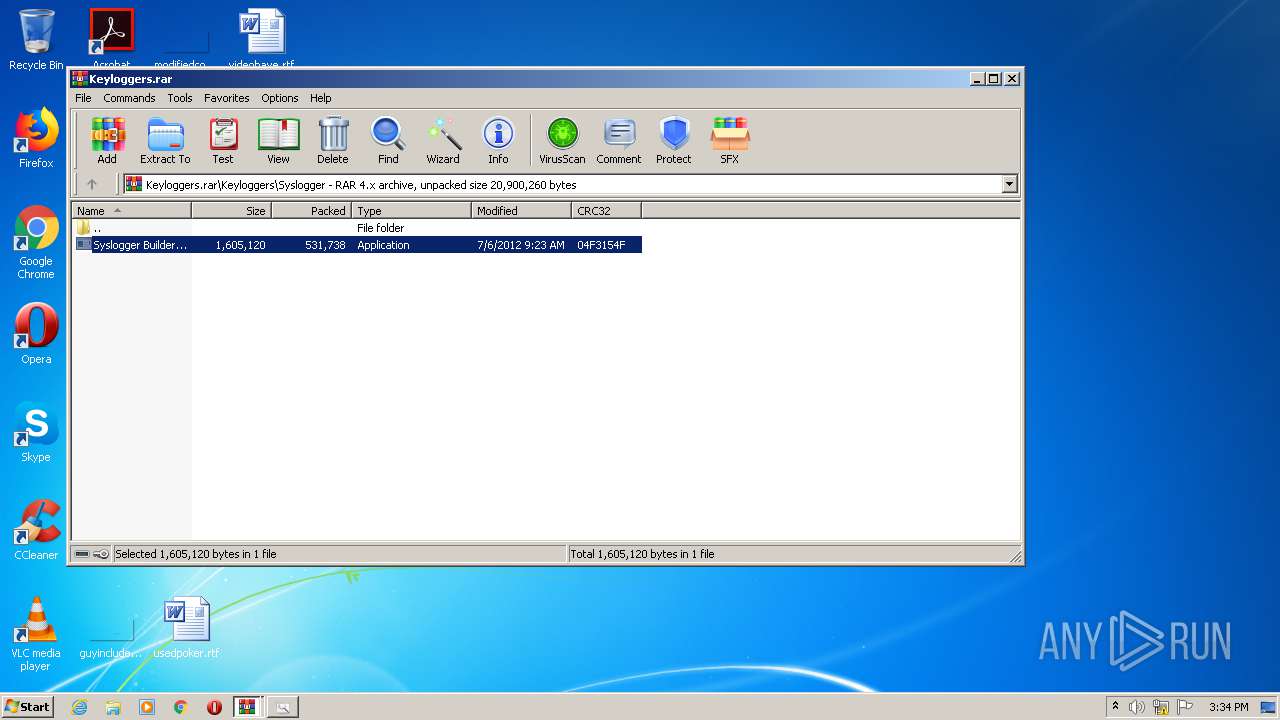
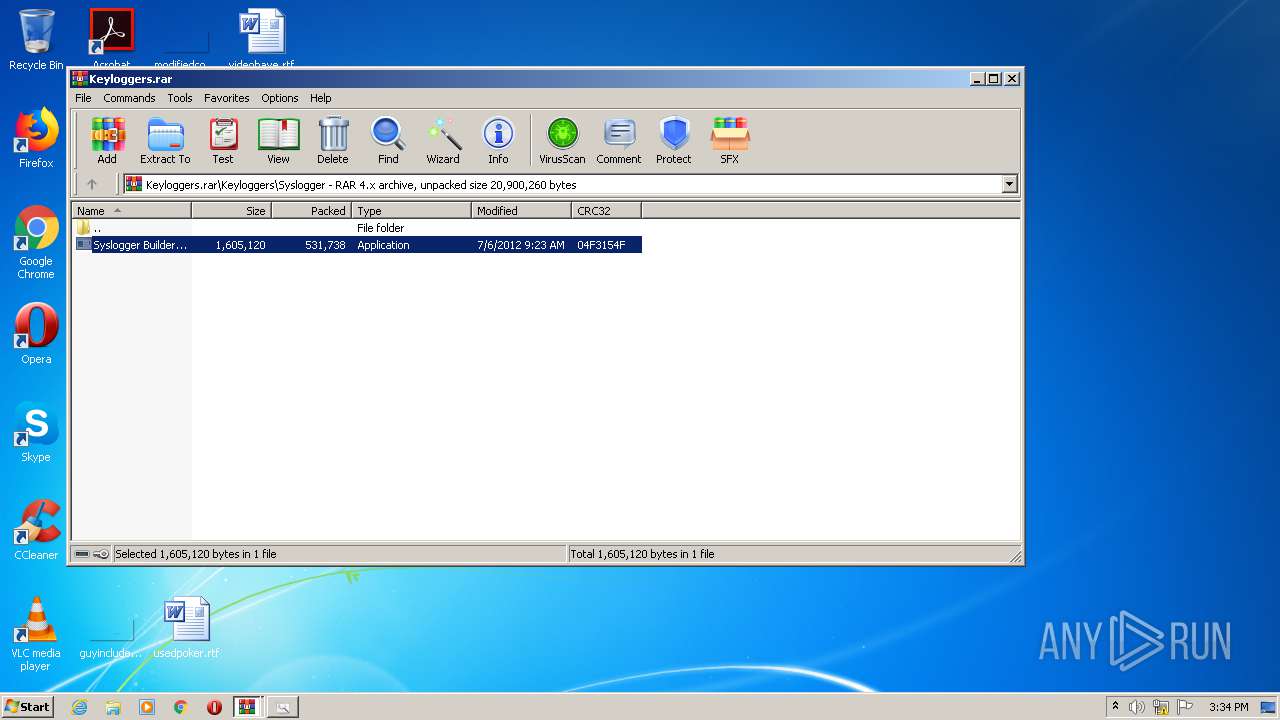
| 3452 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3012.18277\Keyloggers\Syslogger\Syslogger Builder.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3012.18277\Keyloggers\Syslogger\Syslogger Builder.exe | — | WinRAR.exe | |||||||||||
User: admin Company: E V O Integrity Level: MEDIUM Description: Syslogger Exit code: 0 Version: 1.0.2.0 Modules
| |||||||||||||||
Total events
760
Read events
740
Write events
20
Delete events
0
Modification events
| (PID) Process: | (3364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3364) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Keyloggers.rar | |||
| (PID) Process: | (3364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3364) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
Executable files
66
Suspicious files
0
Text files
21
Unknown types
3
Dropped files
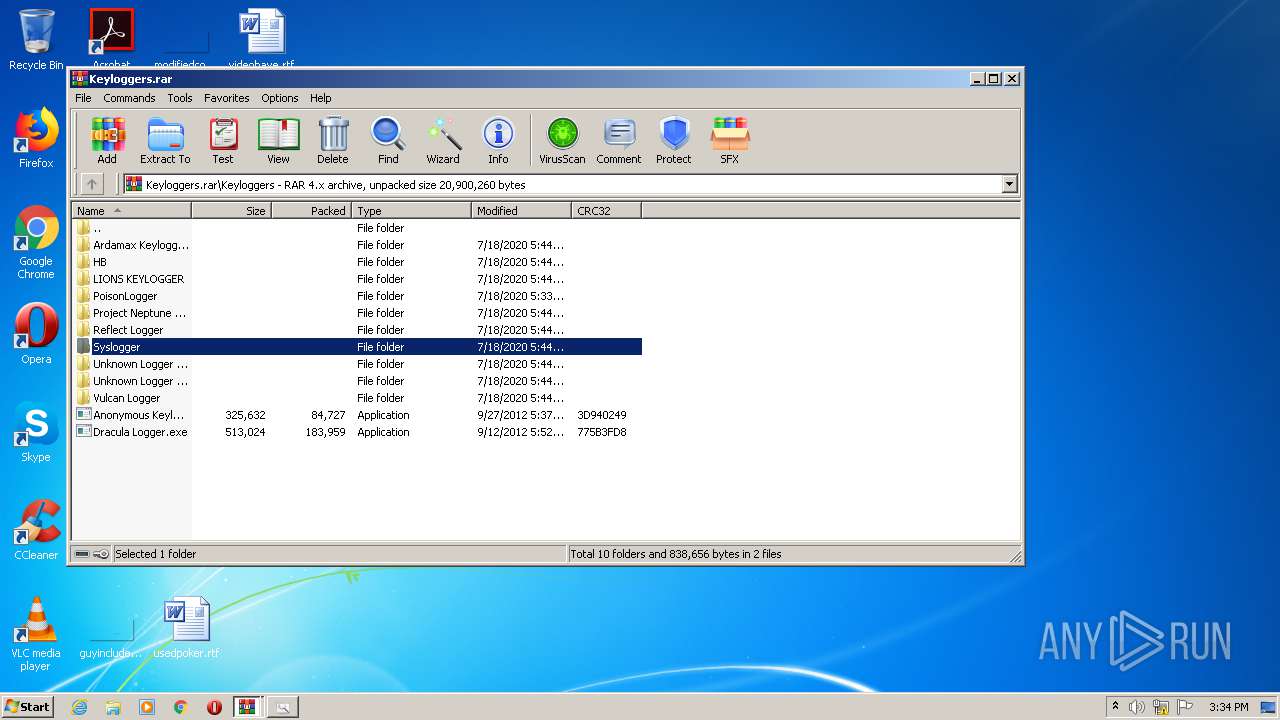
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3012.16242\Keyloggers\Ardamax Keylogger 4.0 by [[Plunderthesecurity.in]]\install_akl.exe | executable | |
MD5:— | SHA256:— | |||
| 3012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3012.16242\Keyloggers\HB\HB Builder.exe | executable | |
MD5:— | SHA256:— | |||
| 3012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3012.16242\Keyloggers\LIONS KEYLOGGER\LIONS KEYLOGGER PÚBLICO.exe | executable | |
MD5:— | SHA256:— | |||
| 3012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3012.16242\Keyloggers\Ardamax Keylogger 4.0 by [[Plunderthesecurity.in]]\Patch\Serial.txt | text | |
MD5:— | SHA256:— | |||
| 3012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3012.16242\Keyloggers\HB\HBStub.exe | executable | |
MD5:— | SHA256:— | |||
| 3012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3012.16242\Keyloggers\Dracula Logger.exe | executable | |
MD5:F51A2895A0AEE4F6290DE37AC8A2042F | SHA256:0BFAD1FFAD03842B90FA7790F838EE78AA3AB10093CD041F6F8F0037219954A1 | |||
| 3012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3012.16242\Keyloggers\Reflect Logger\Reflect Logger v3.exe | executable | |
MD5:— | SHA256:— | |||
| 3012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3012.16242\Keyloggers\PoisonLogger\server.exe | executable | |
MD5:— | SHA256:— | |||
| 3012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3012.16242\Keyloggers\LIONS KEYLOGGER\Stub.dll | executable | |
MD5:— | SHA256:— | |||
| 3012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3012.16242\Keyloggers\Anonymous Keylogger.exe | executable | |
MD5:70F7FDD57CD561A114AC03E1F50649FE | SHA256:9F08561DE1EB32642A366D27532450C7908D1F1FADD1667FDF49187B584F5E69 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report