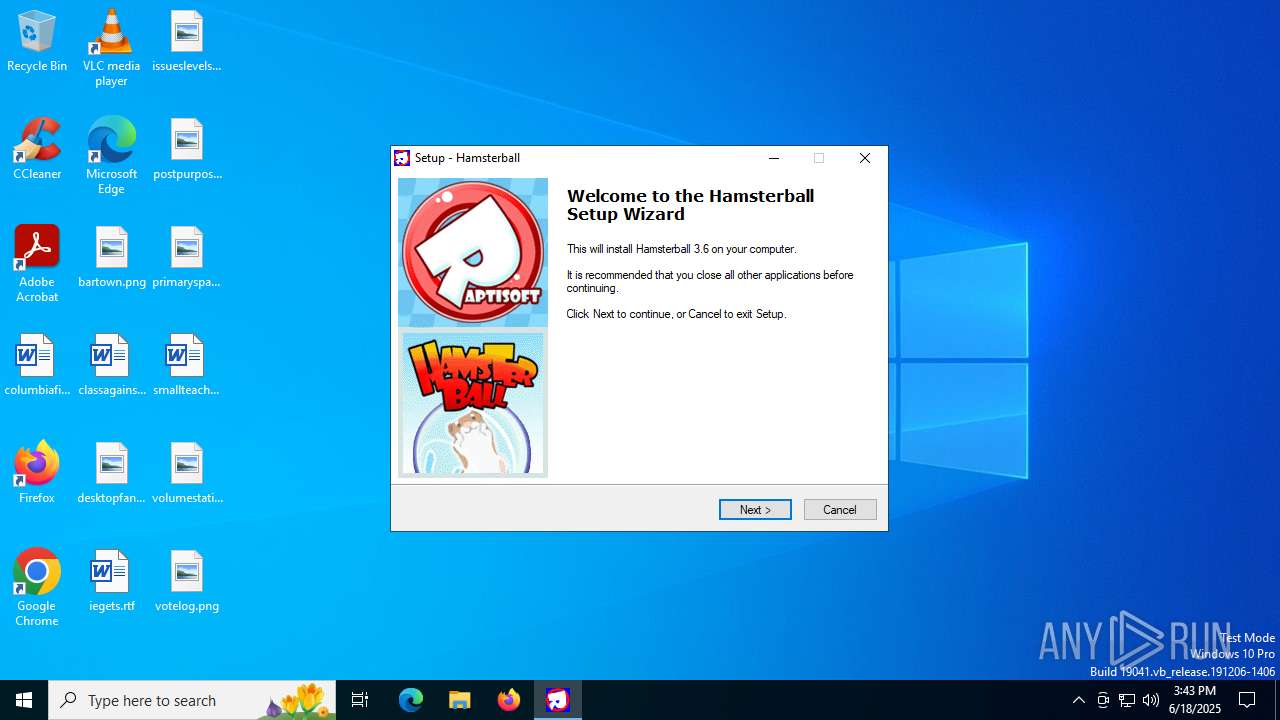
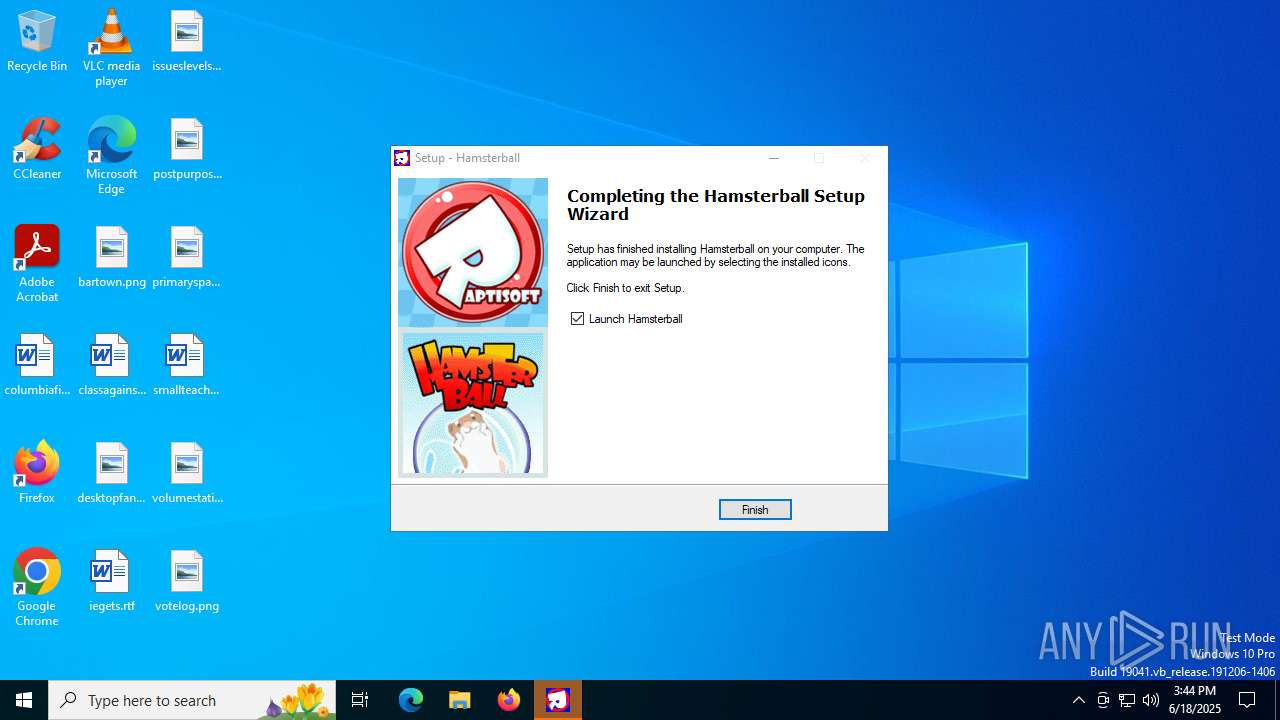
| download: | /download/hamsterball-v3.6.b-full-version/Setup.exe |
| Full analysis: | https://app.any.run/tasks/b75730e2-b6fa-4364-8859-16d83c14b70c |
| Verdict: | Malicious activity |
| Analysis date: | June 18, 2025, 15:43:17 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | 5DAB9600222E9FC33F758FCB402B2AB6 |
| SHA1: | C9B16A643857CCF30932D222C3145A0578C8663C |
| SHA256: | 9AED777534E345C174E0F09E6EEB5D7586648A134D256B44EB55337572D68C26 |
| SSDEEP: | 98304:EXrj4mectgIwJb06op9/auxjcsxgq2FRBQqPF7EkkJU4mBXHmw1mpDwKKM1fShof:NPjvRtVinO0Bz |
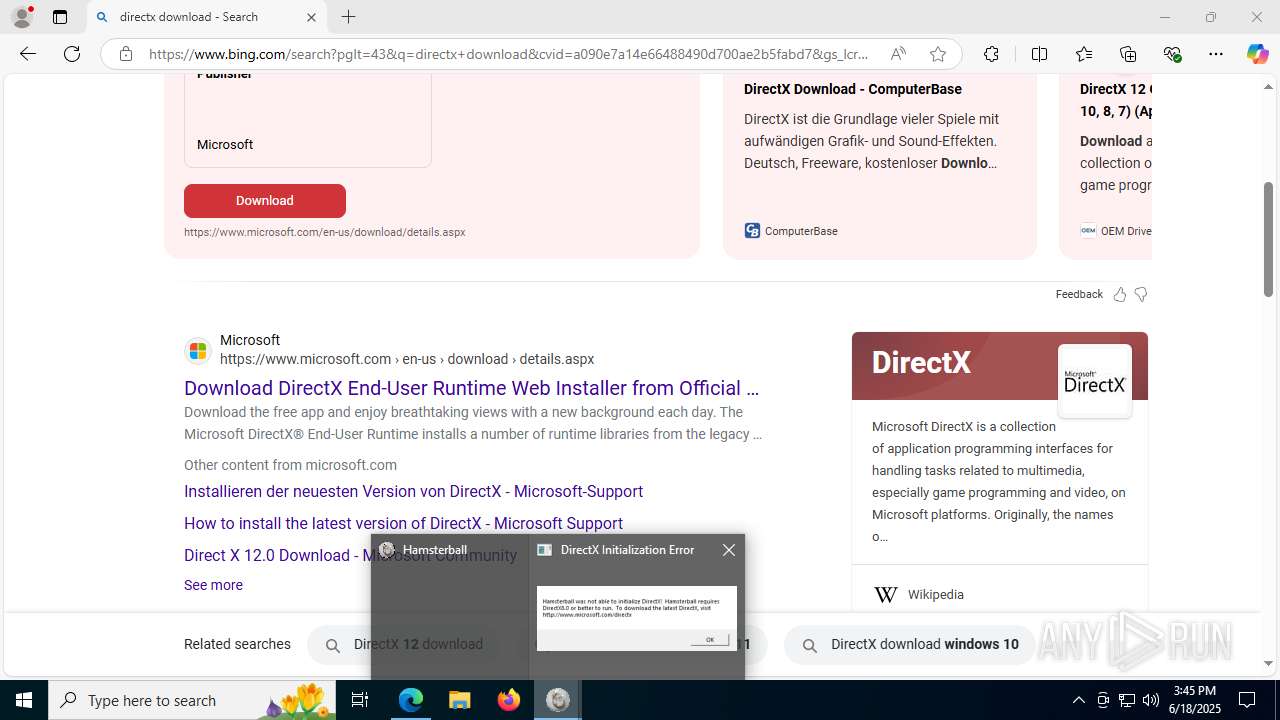
MALICIOUS
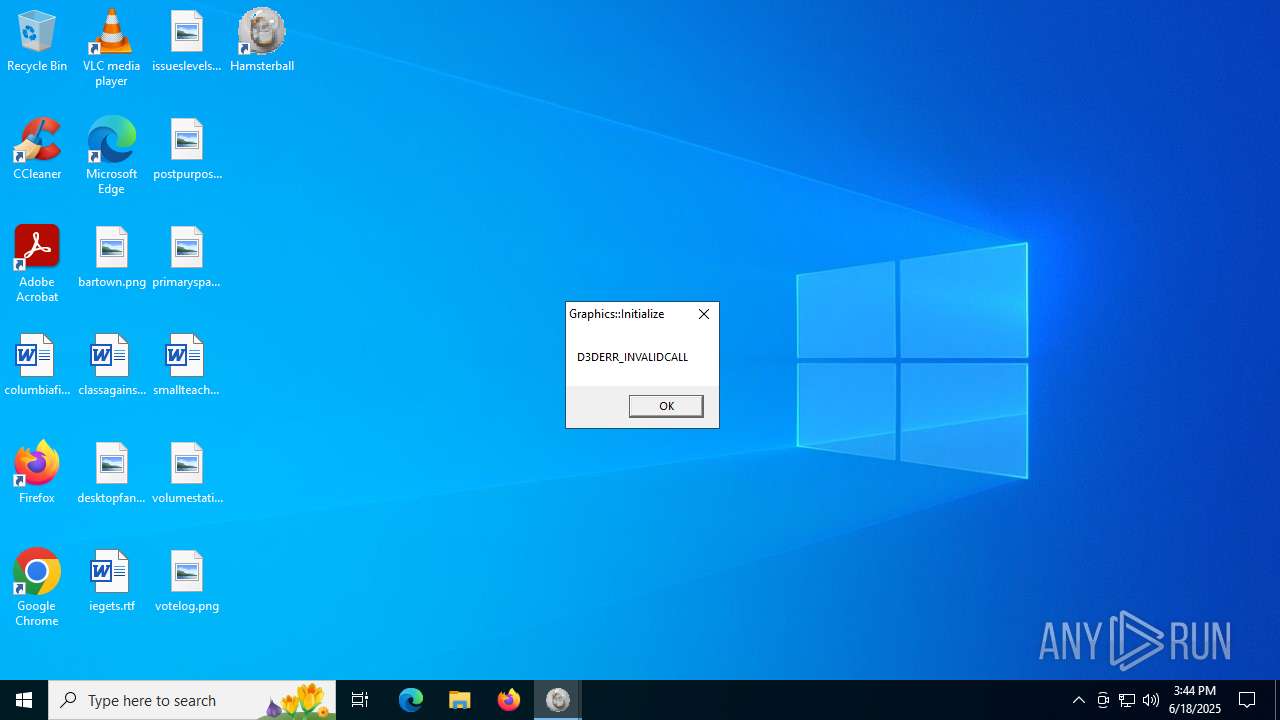
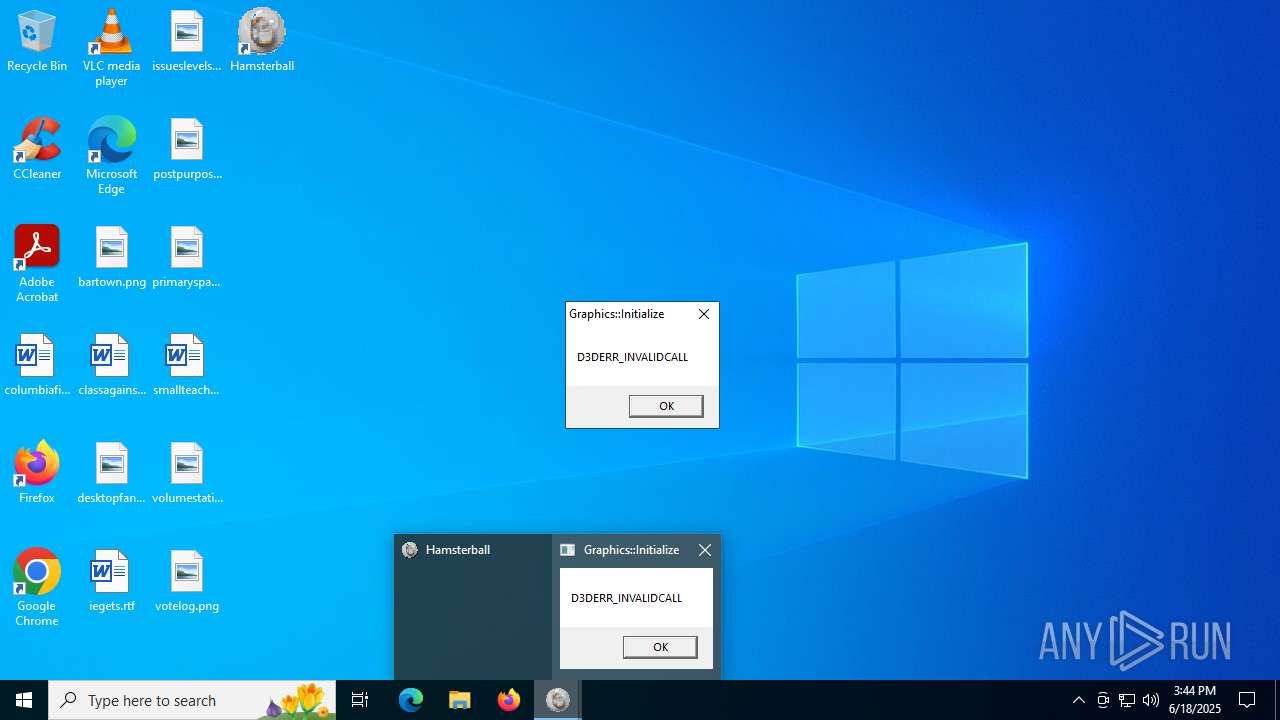
Application was injected by another process
- csrss.exe (PID: 608)
Runs injected code in another process
- Hamsterball.exe (PID: 5968)
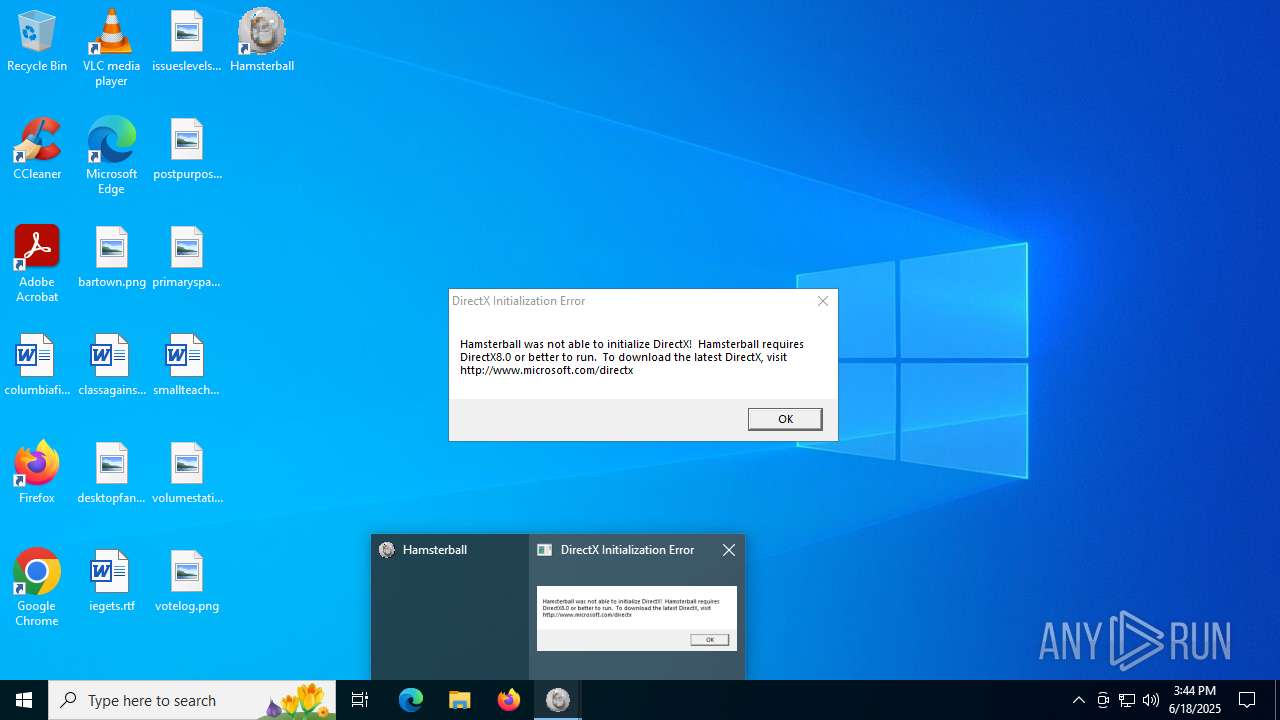
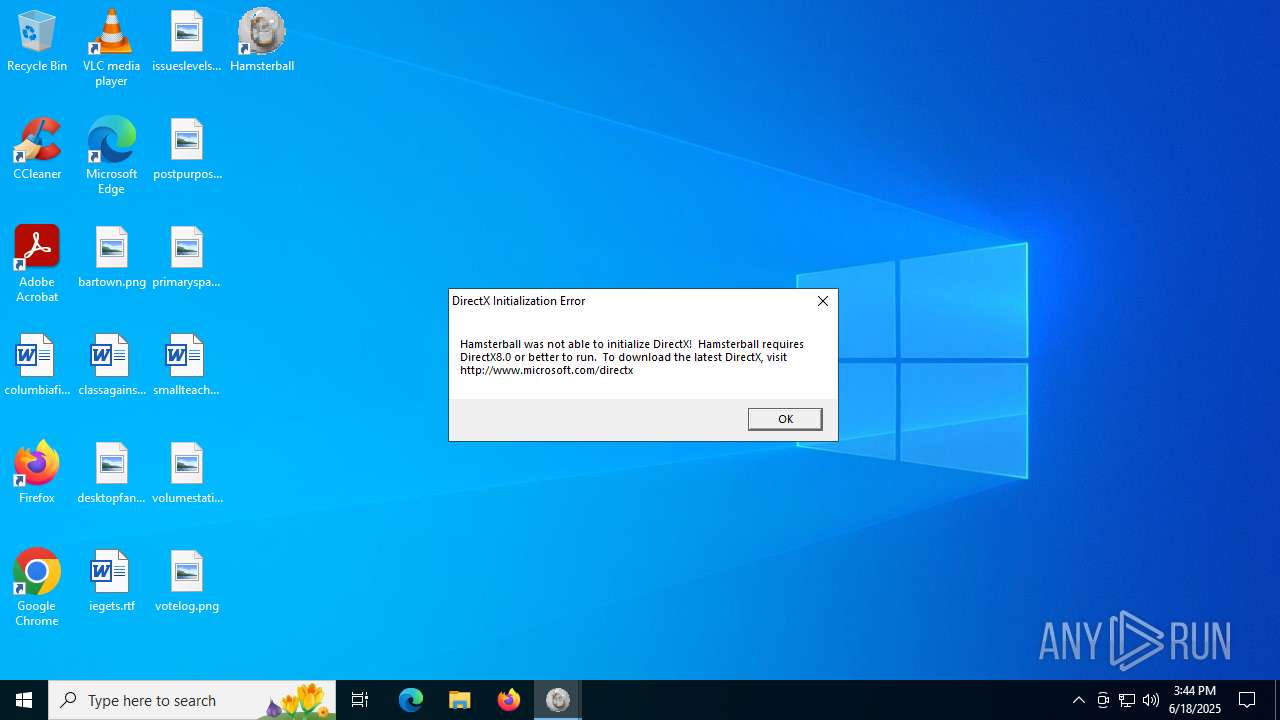
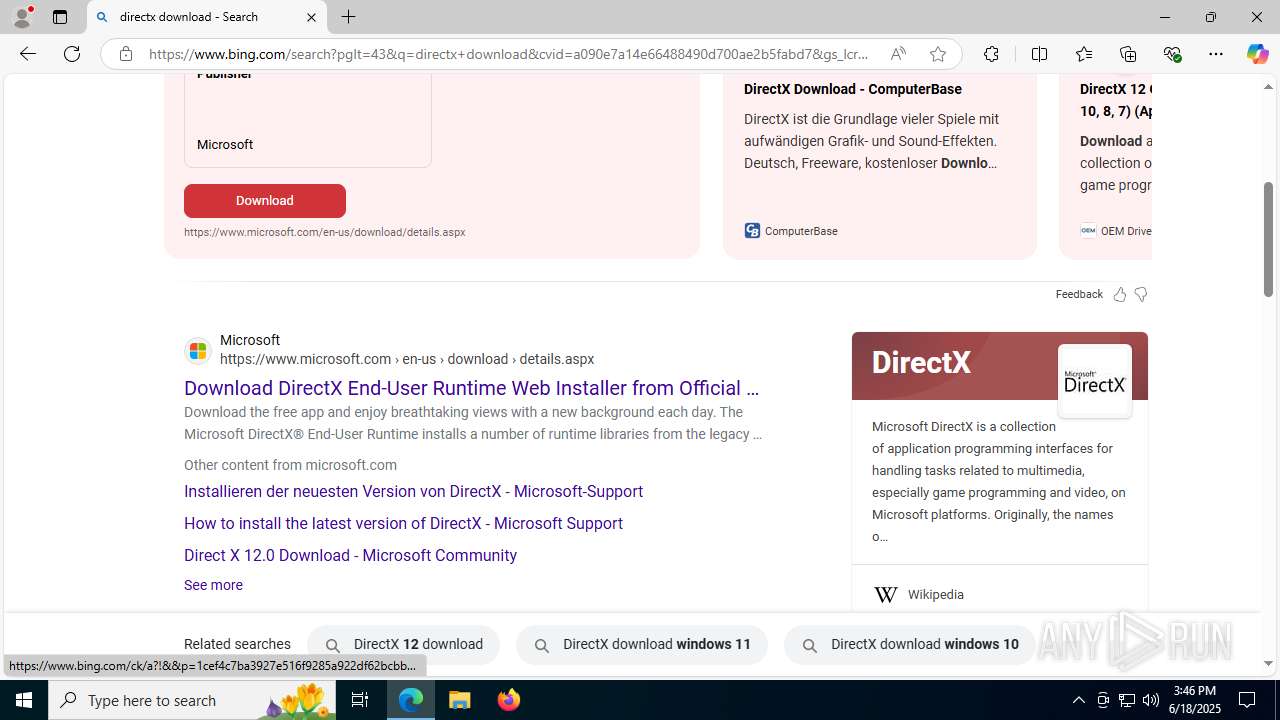
Changes the autorun value in the registry
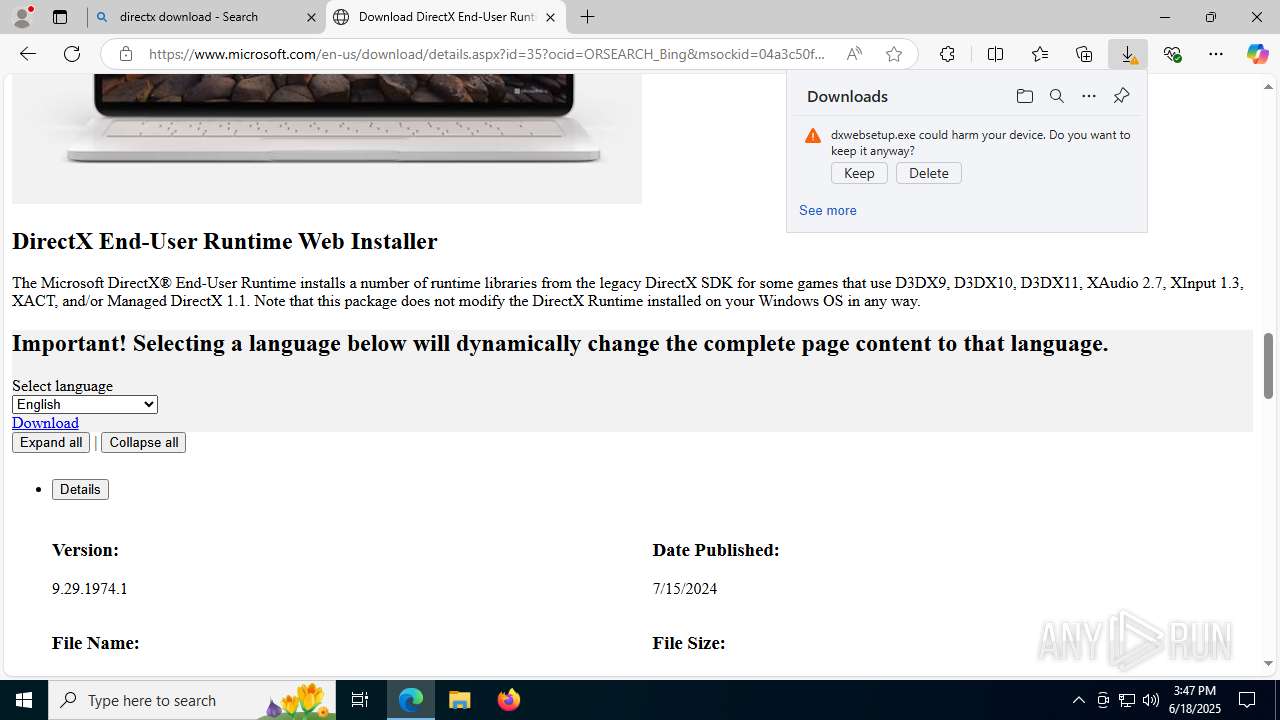
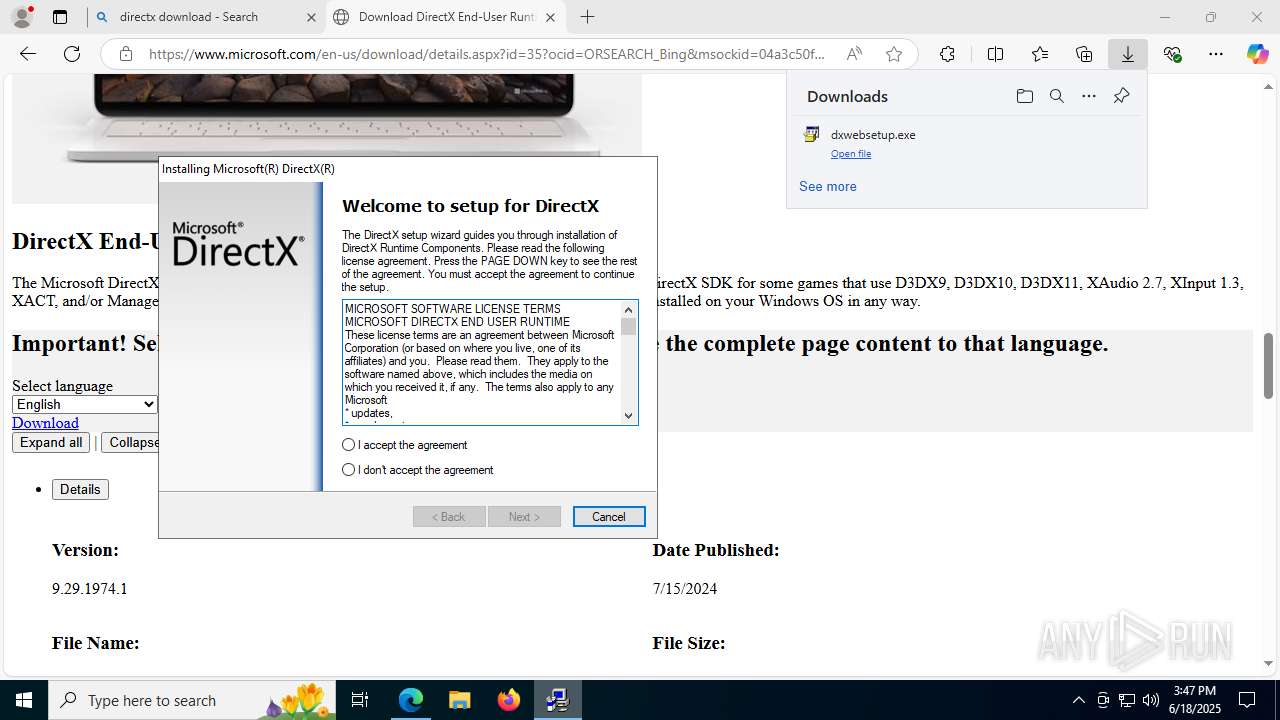
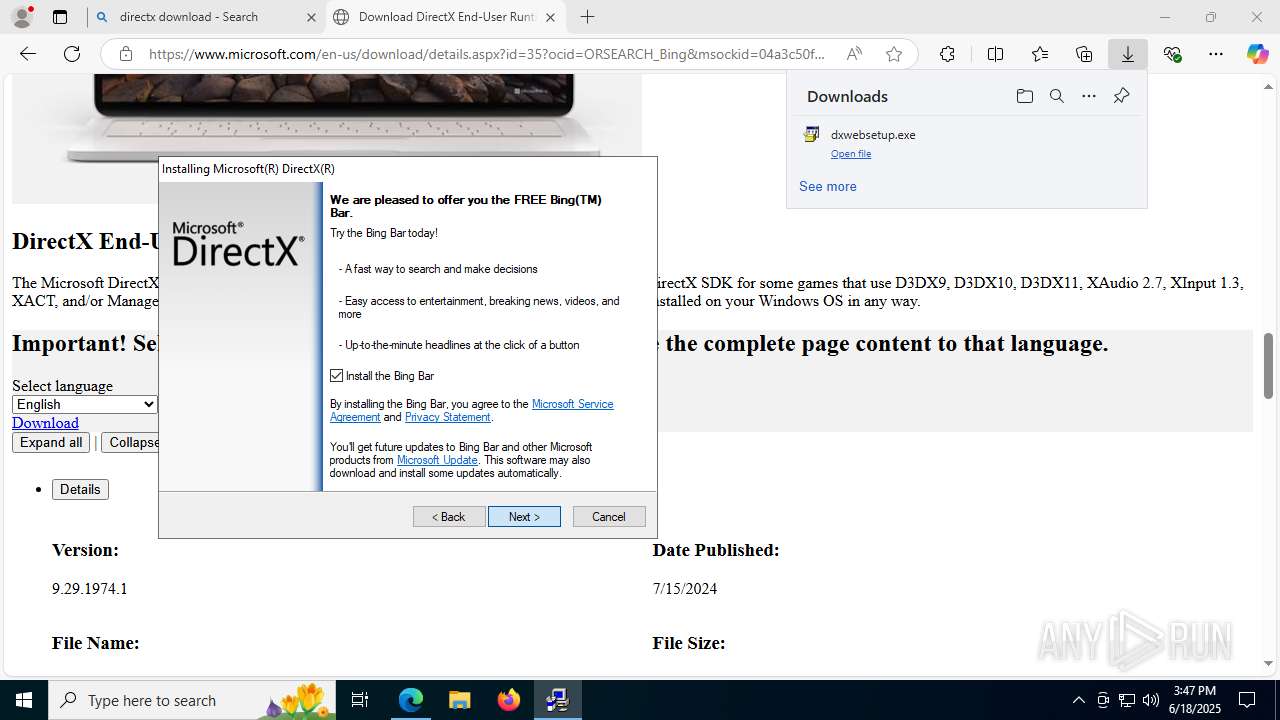
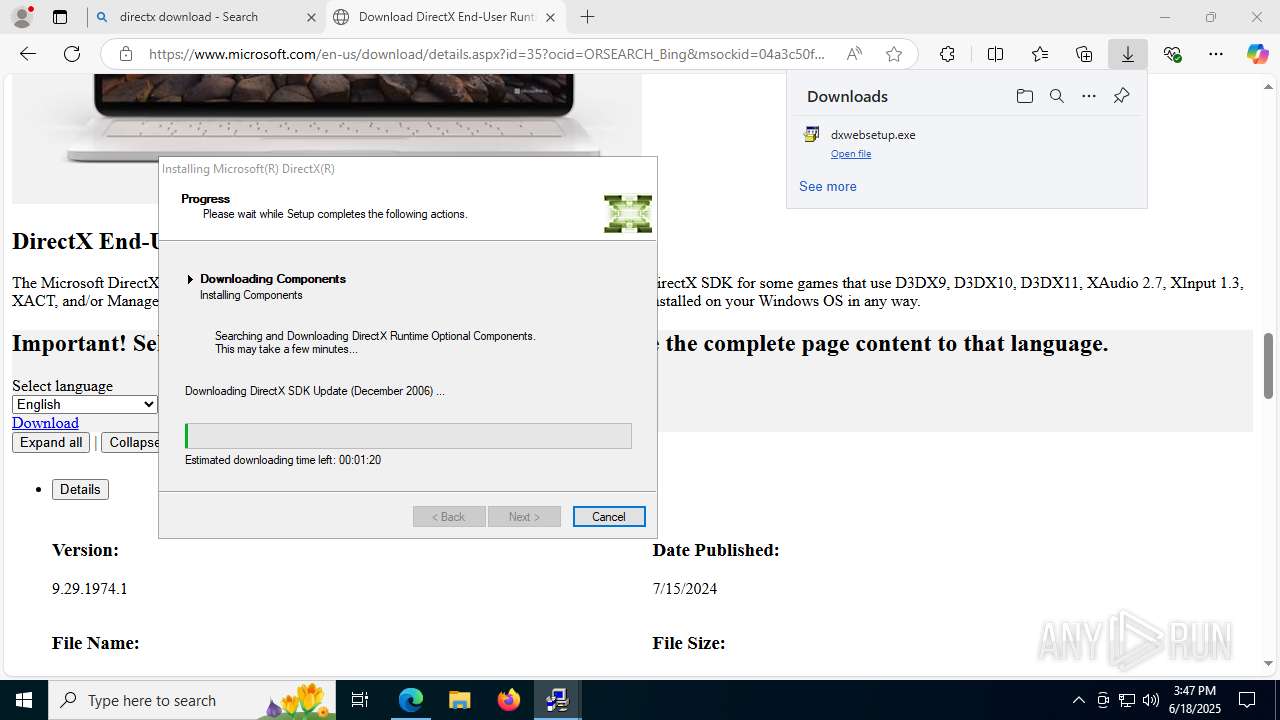
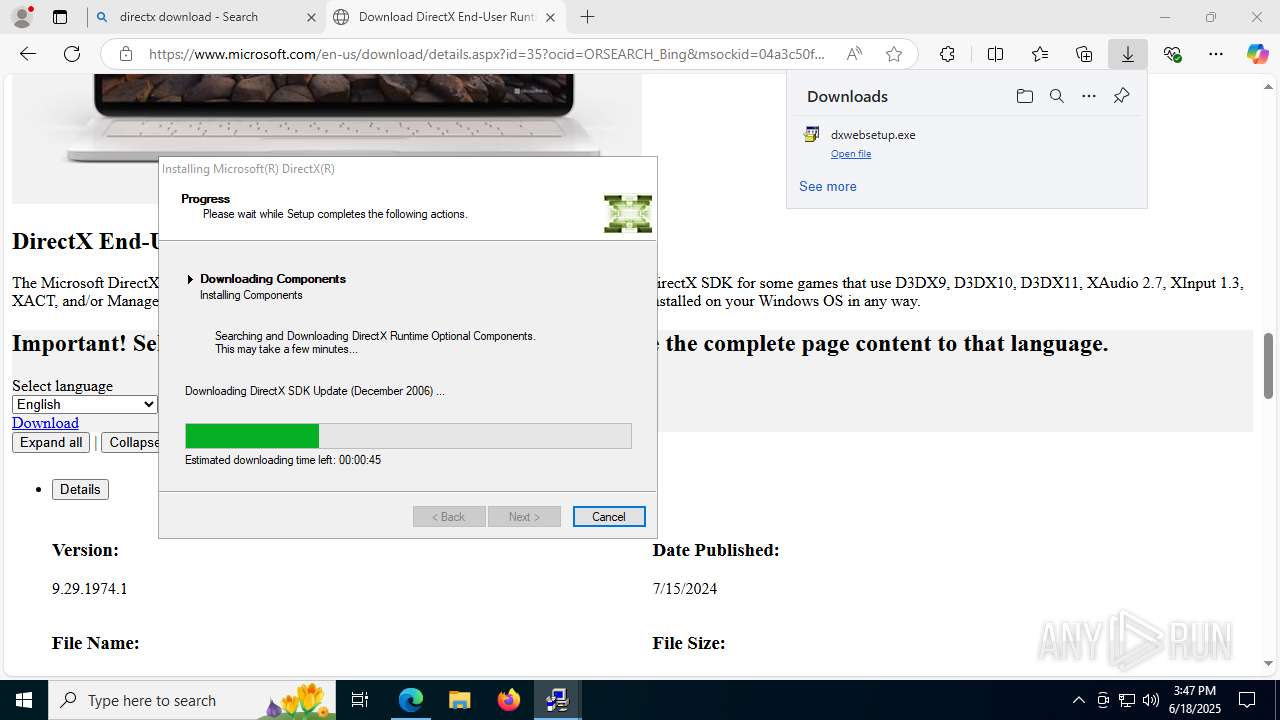
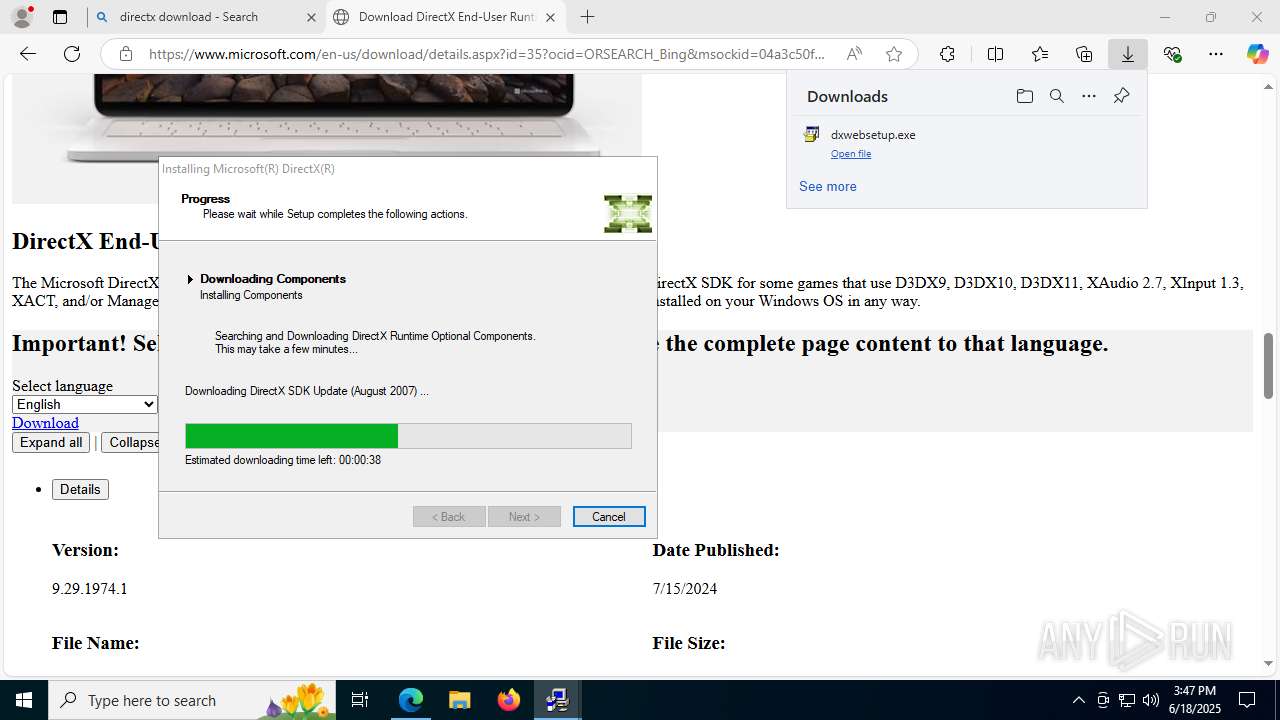
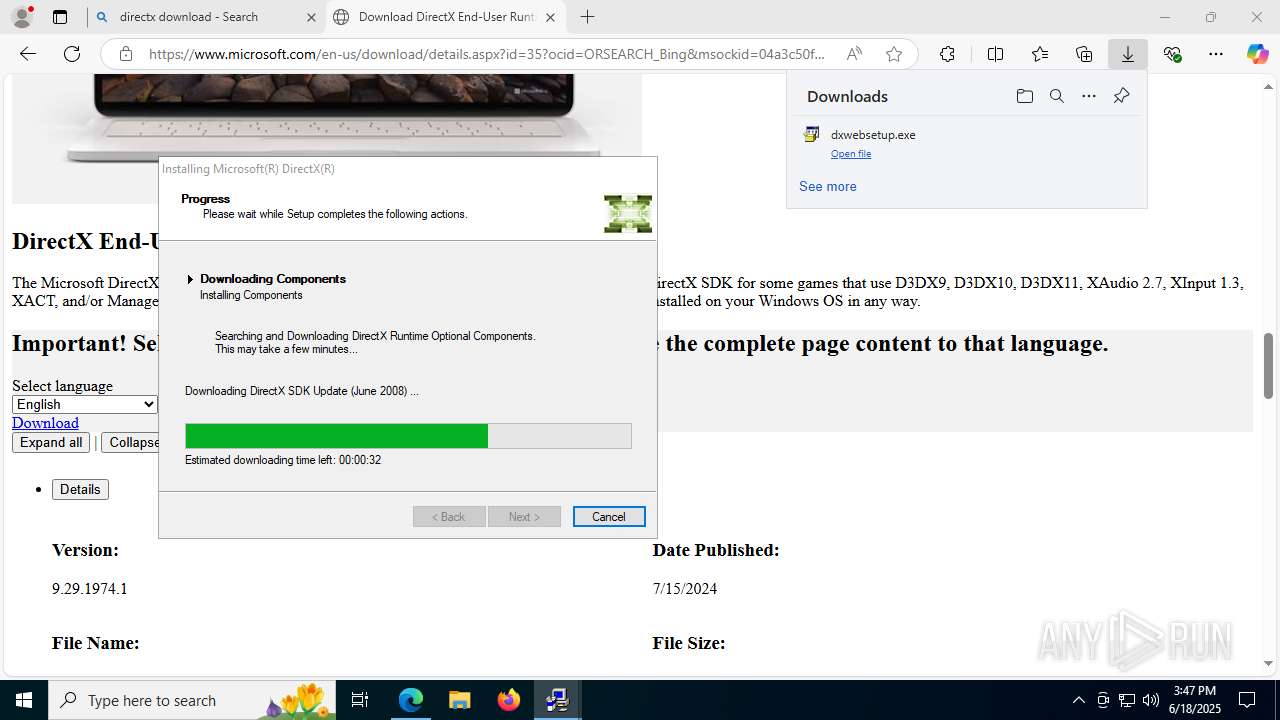
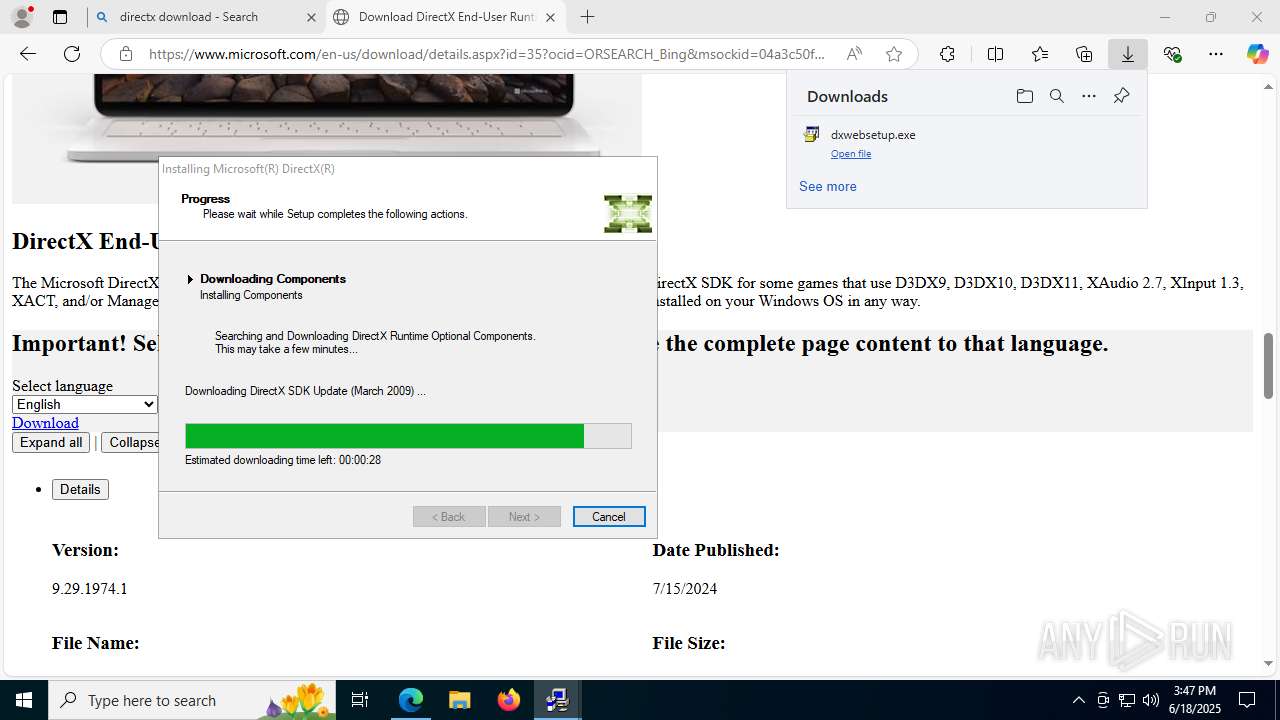
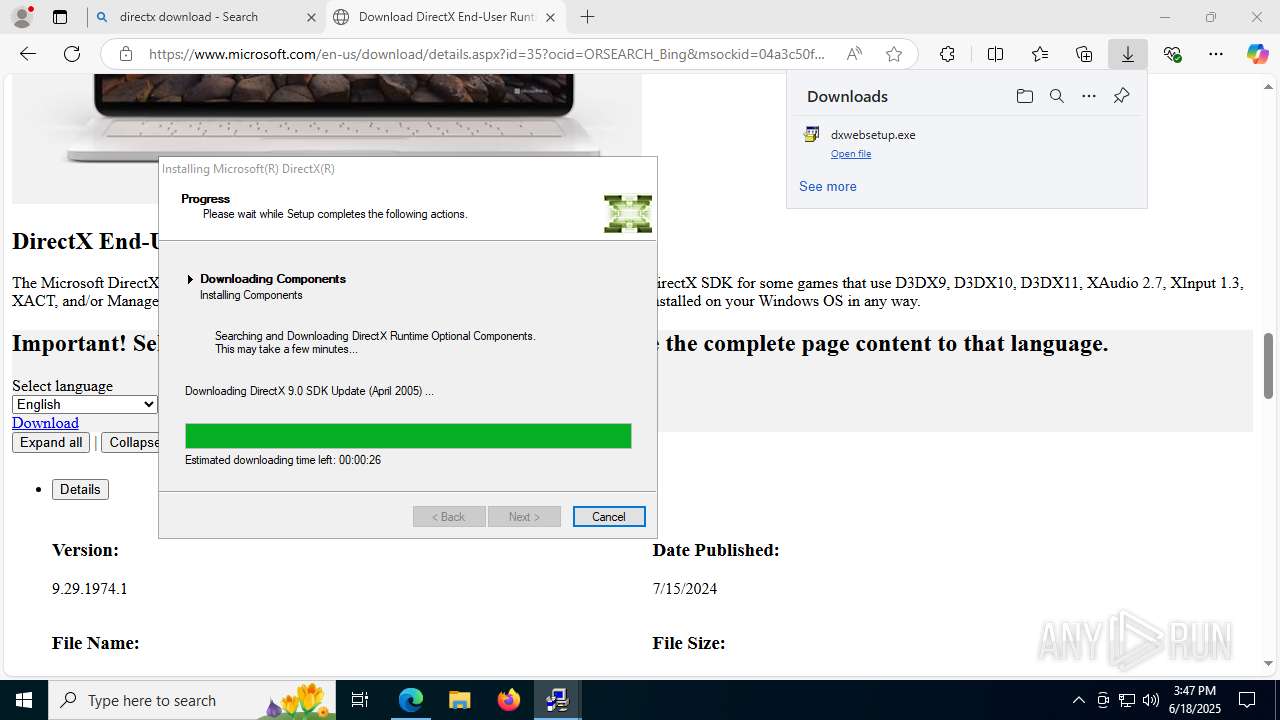
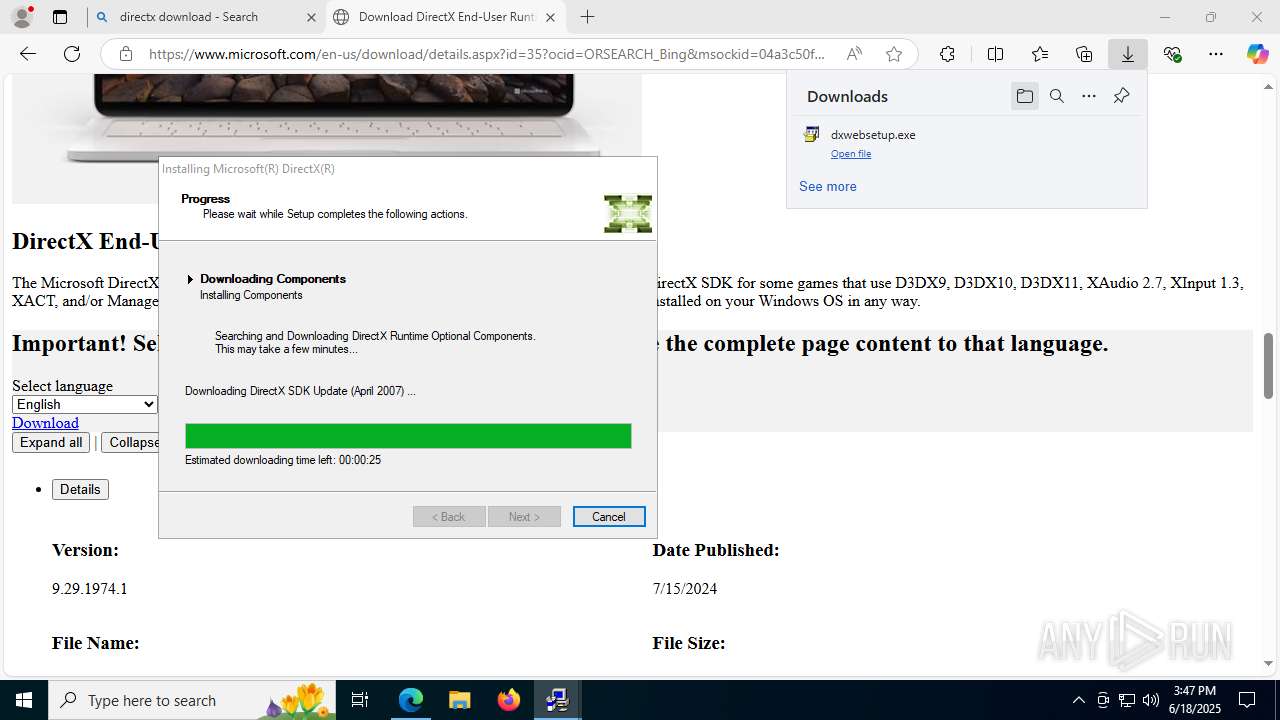
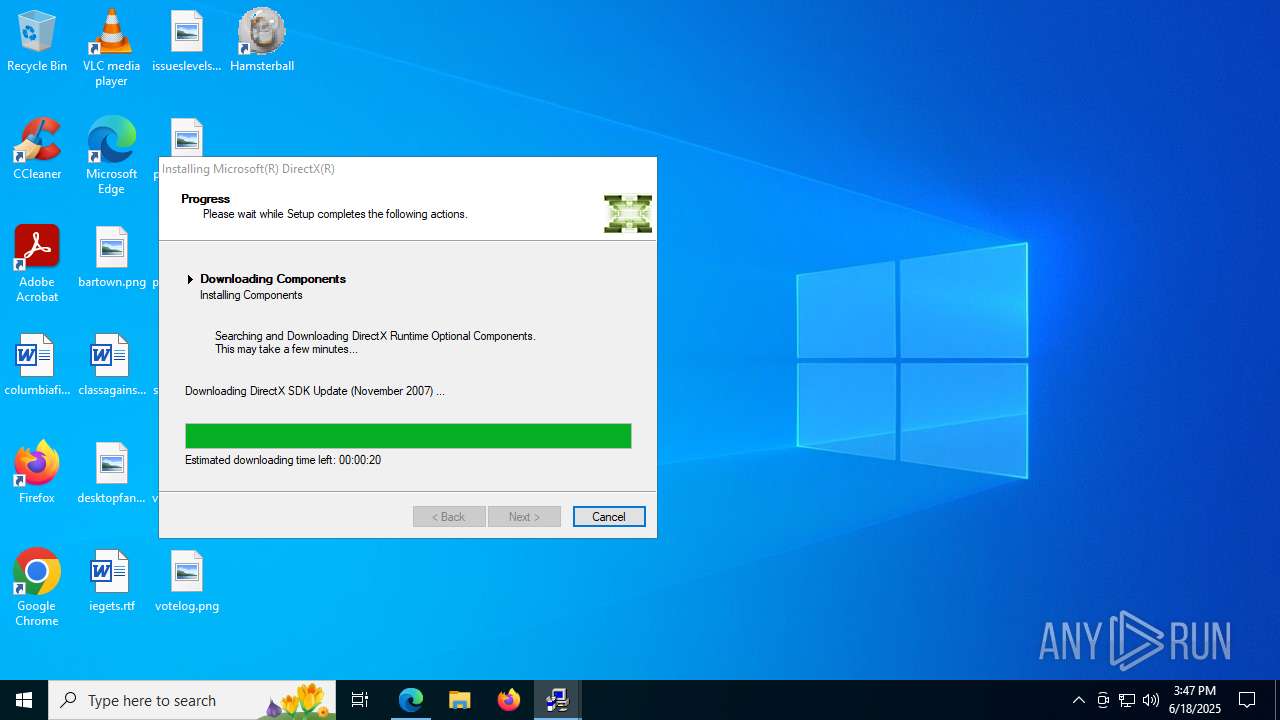
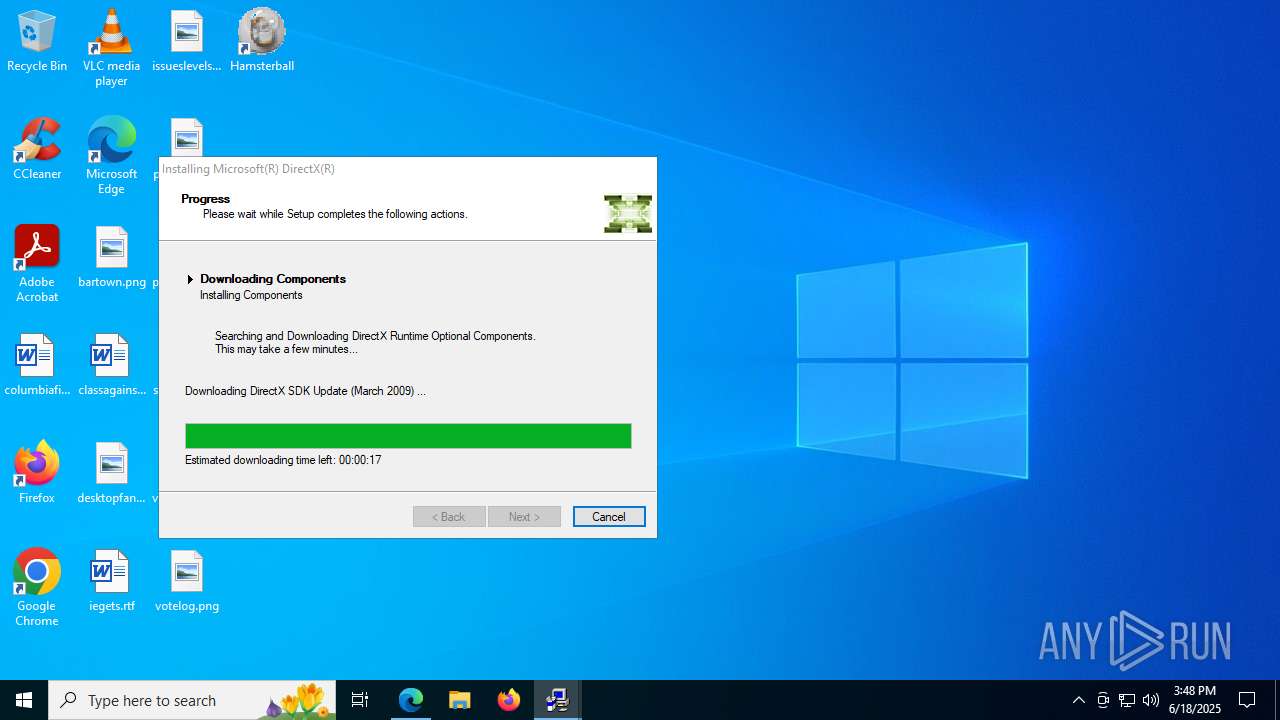
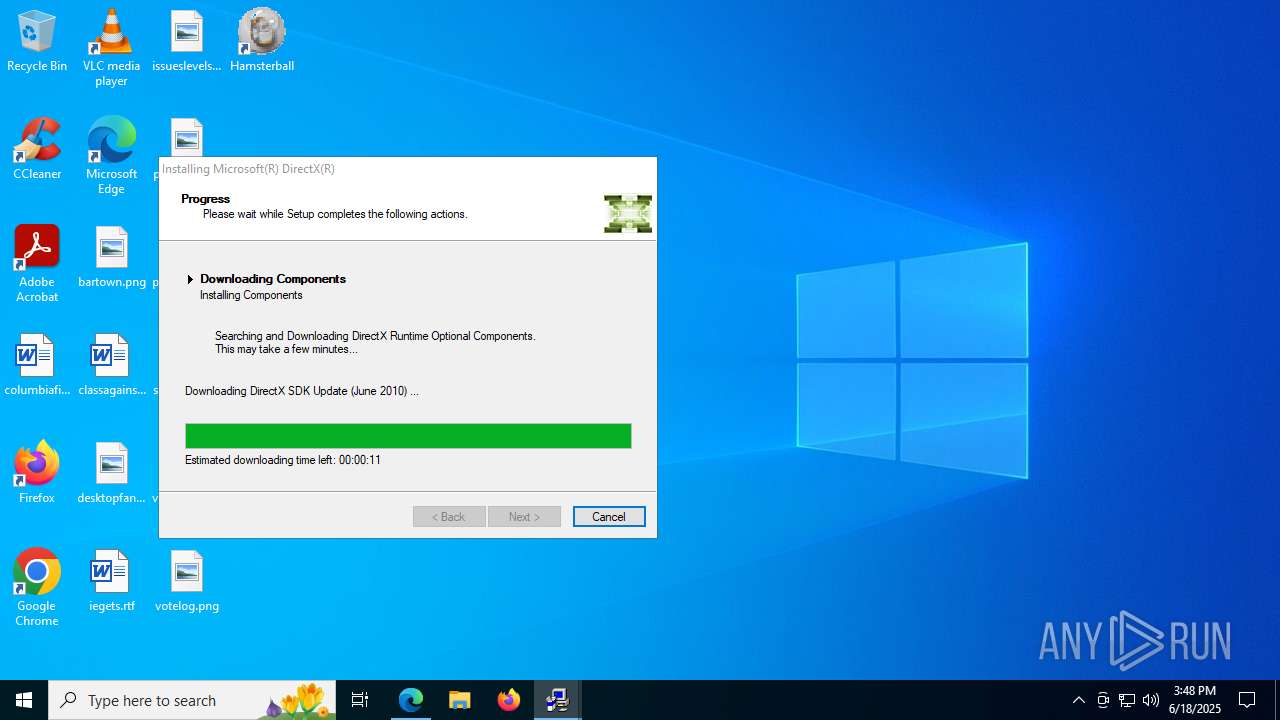
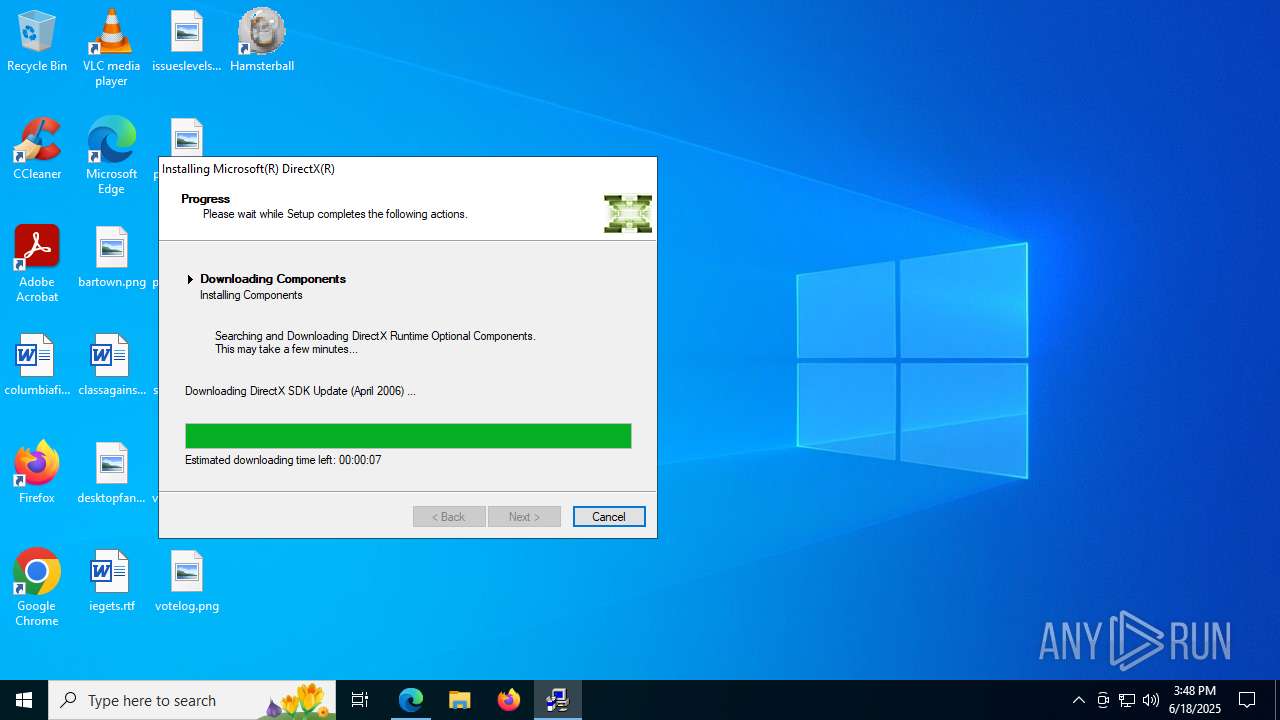
- dxwebsetup.exe (PID: 4476)
- dxwebsetup.exe (PID: 6148)
SUSPICIOUS
Reads the Windows owner or organization settings
- is-CF62K.tmp (PID: 1232)
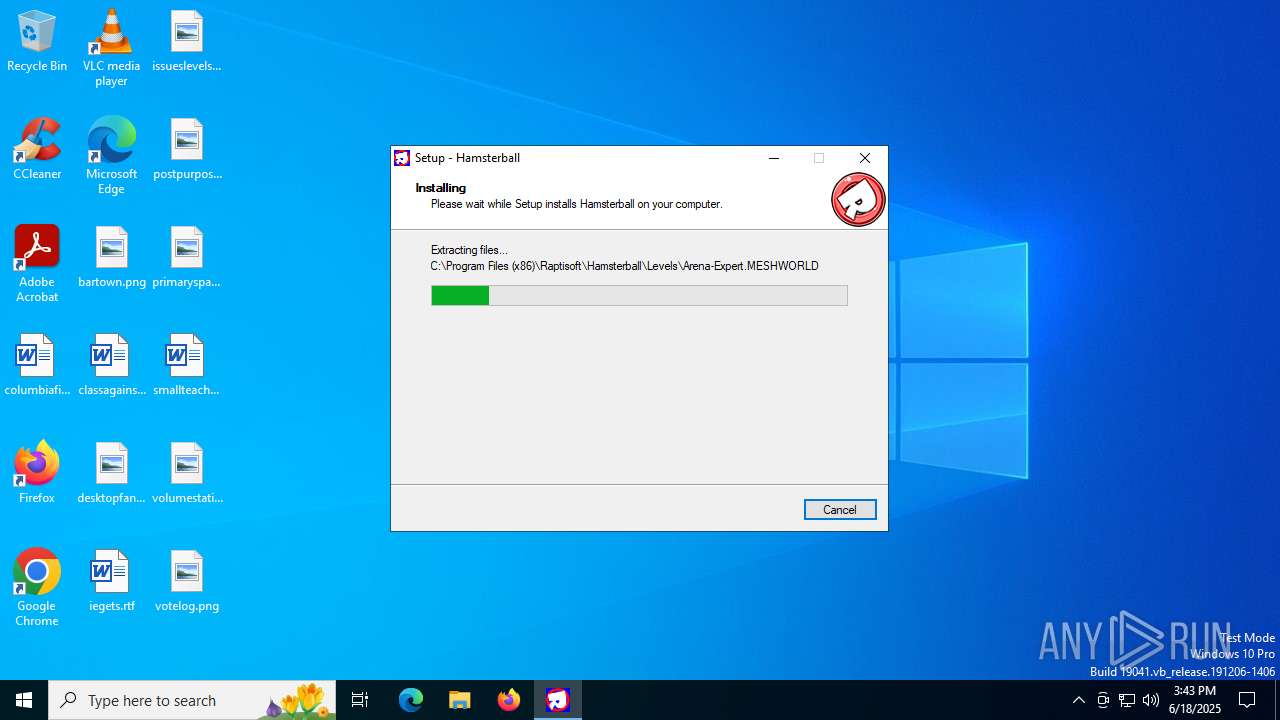
Executable content was dropped or overwritten
- Setup.exe (PID: 6536)
- is-CF62K.tmp (PID: 1232)
- dxwebsetup.exe (PID: 4476)
- dxwsetup.exe (PID: 1644)
- dxwebsetup.exe (PID: 6148)
There is functionality for taking screenshot (YARA)
- Hamsterball.exe (PID: 5968)
- Hamsterball.exe (PID: 5240)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 6172)
- dxwsetup.exe (PID: 1644)
Process drops legitimate windows executable
- msedge.exe (PID: 3052)
- msedge.exe (PID: 5724)
- dxwsetup.exe (PID: 1644)
- dxwebsetup.exe (PID: 4476)
- dxwebsetup.exe (PID: 6148)
Starts a Microsoft application from unusual location
- dxwsetup.exe (PID: 1644)
- dxwsetup.exe (PID: 6244)
Executes as Windows Service
- VSSVC.exe (PID: 1068)
Searches for installed software
- dllhost.exe (PID: 6512)
INFO
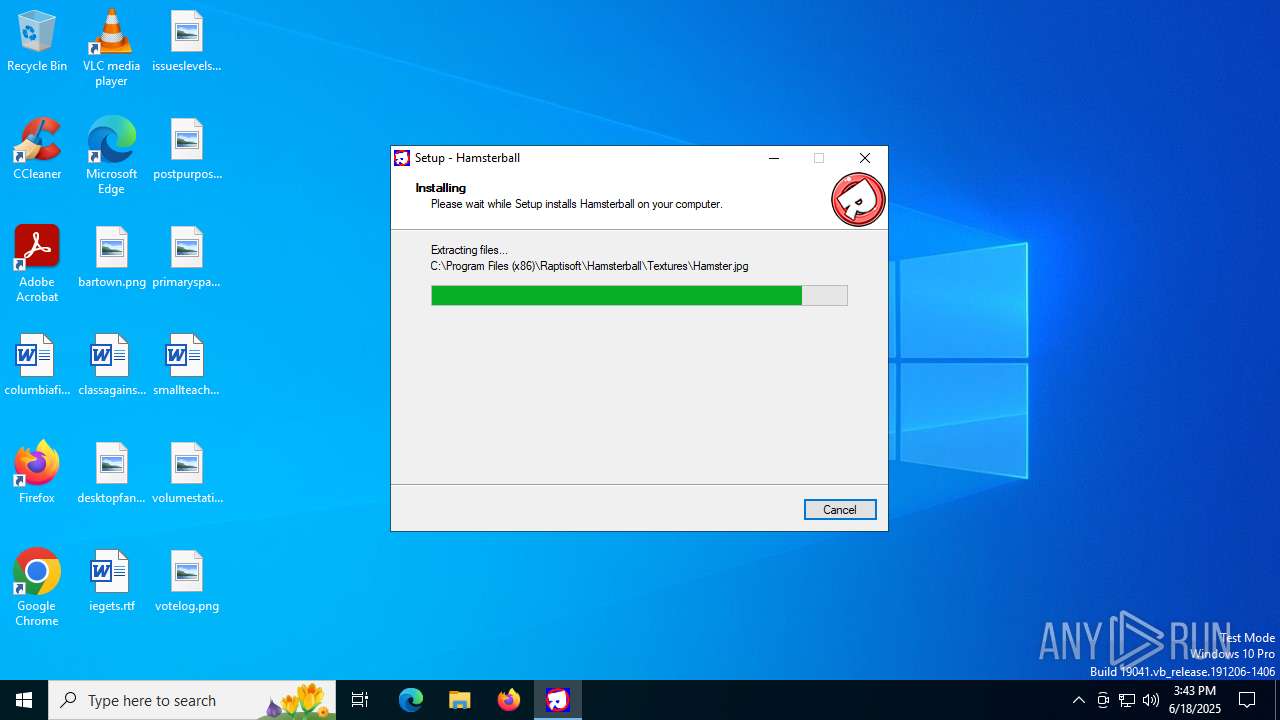
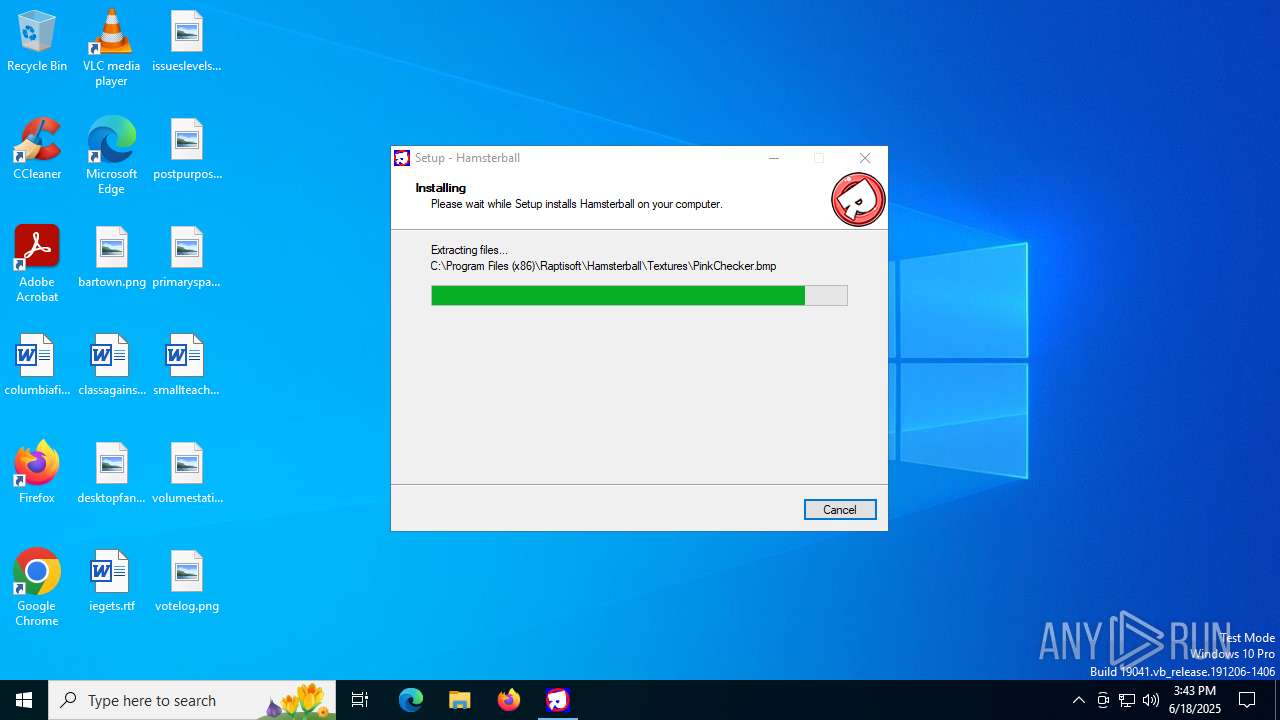
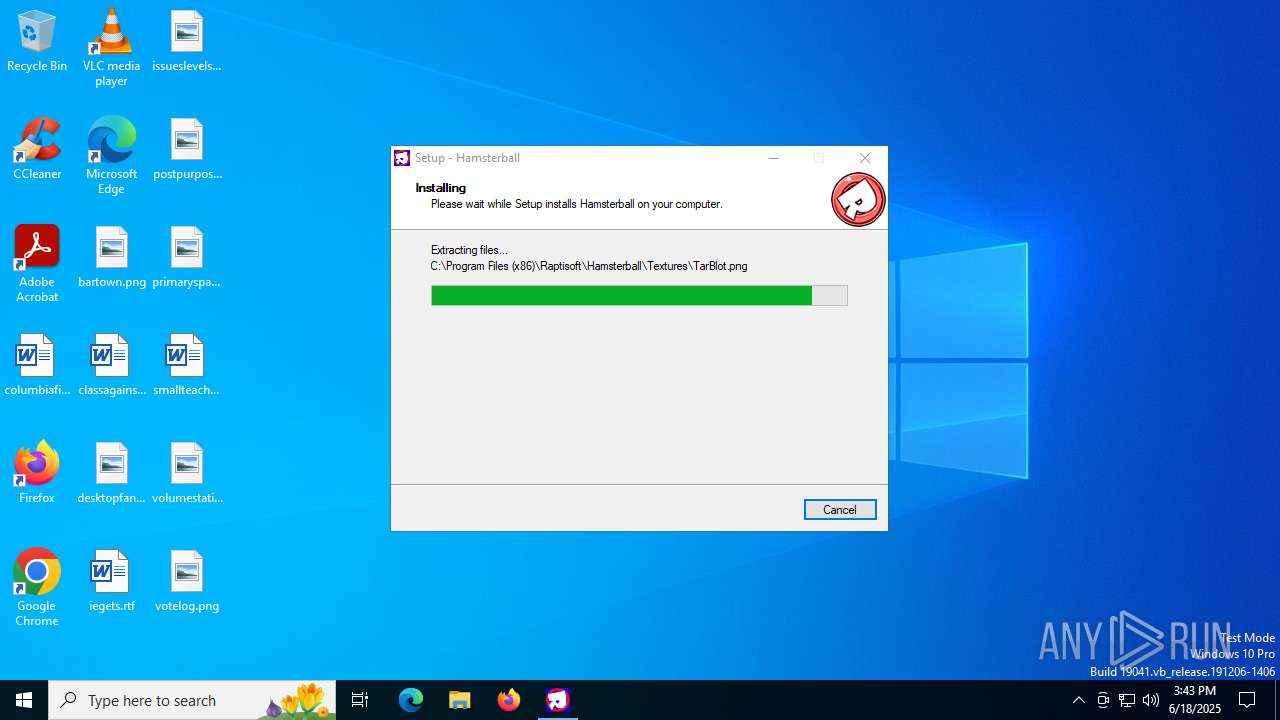
Creates files in the program directory
- is-CF62K.tmp (PID: 1232)
Create files in a temporary directory
- Setup.exe (PID: 6536)
- is-CF62K.tmp (PID: 1232)
- dxwebsetup.exe (PID: 6148)
- dxwebsetup.exe (PID: 4476)
- dxwsetup.exe (PID: 1644)
Compiled with Borland Delphi (YARA)
- is-CF62K.tmp (PID: 1232)
The sample compiled with english language support
- Setup.exe (PID: 6536)
- is-CF62K.tmp (PID: 1232)
- msedge.exe (PID: 3052)
- msedge.exe (PID: 5724)
- dxwebsetup.exe (PID: 4476)
- dxwsetup.exe (PID: 1644)
- dxwebsetup.exe (PID: 6148)
Checks supported languages
- Setup.exe (PID: 6536)
- is-CF62K.tmp (PID: 1232)
- Hamsterball.exe (PID: 5968)
- Hamsterball.exe (PID: 5240)
- identity_helper.exe (PID: 6336)
- ShellExperienceHost.exe (PID: 6172)
- dxwsetup.exe (PID: 1644)
- dxwebsetup.exe (PID: 6148)
- dxwsetup.exe (PID: 6244)
Detects InnoSetup installer (YARA)
- is-CF62K.tmp (PID: 1232)
- Setup.exe (PID: 6536)
Reads the computer name
- is-CF62K.tmp (PID: 1232)
- Hamsterball.exe (PID: 5968)
- Hamsterball.exe (PID: 5240)
- ShellExperienceHost.exe (PID: 6172)
- identity_helper.exe (PID: 6336)
- dxwsetup.exe (PID: 1644)
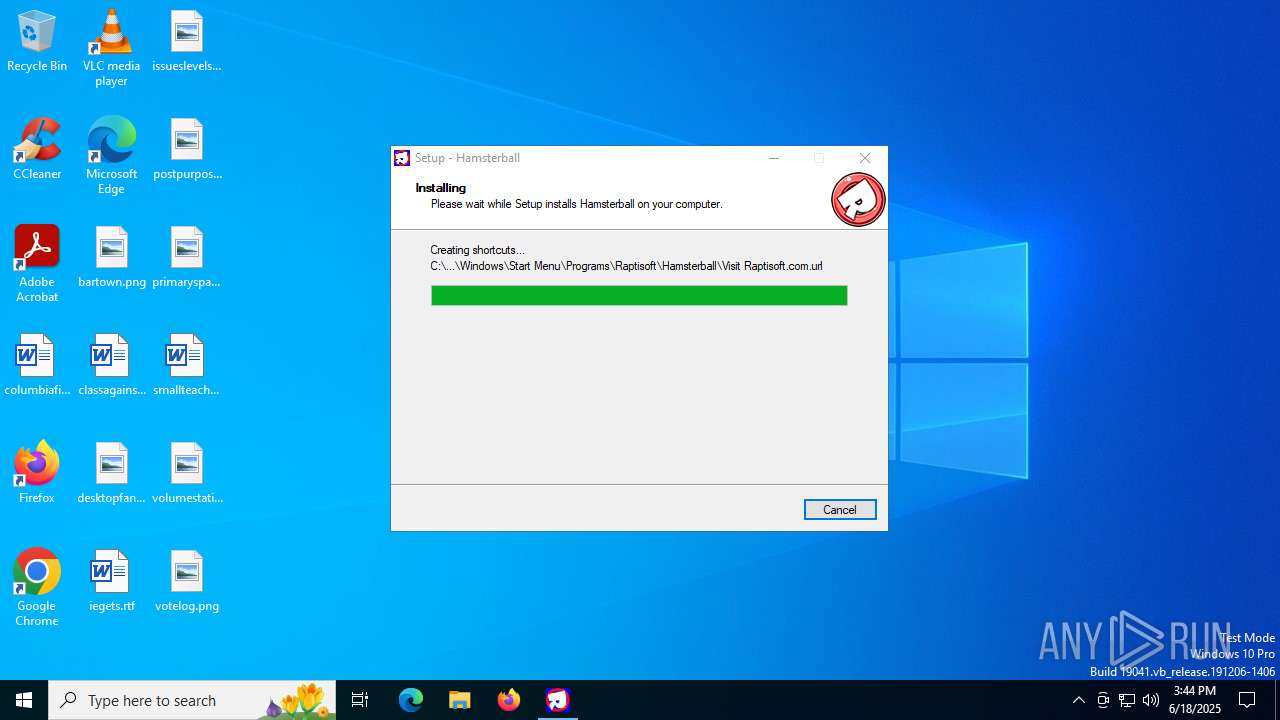
Creates a software uninstall entry
- is-CF62K.tmp (PID: 1232)
Manual execution by a user
- Hamsterball.exe (PID: 5240)
- msedge.exe (PID: 5724)
Reads the software policy settings
- slui.exe (PID: 2276)
- dxwsetup.exe (PID: 1644)
Checks proxy server information
- slui.exe (PID: 2276)
- dxwsetup.exe (PID: 1644)
Application launched itself
- msedge.exe (PID: 5724)
Reads Environment values
- identity_helper.exe (PID: 6336)
Executable content was dropped or overwritten
- msedge.exe (PID: 3052)
- msedge.exe (PID: 5724)
Launching a file from the Downloads directory
- msedge.exe (PID: 5724)
Launching a file from a Registry key
- dxwebsetup.exe (PID: 4476)
- dxwebsetup.exe (PID: 6148)
Creates files or folders in the user directory
- dxwsetup.exe (PID: 1644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable PowerBASIC/Win 9.x (51.2) |
|---|---|---|
| .exe | | | Inno Setup installer (37.9) |
| .exe | | | Win32 Executable Delphi generic (4.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (2.2) |
| .exe | | | Win32 Executable (generic) (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 36864 |
| InitializedDataSize: | 16896 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x98d8 |
| OSVersion: | 1 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | This installation was built with Inno Setup: http://www.innosetup.com |
| CompanyName: | Raptisoft |
| FileDescription: | Hamsterball Setup |
| FileVersion: | |
| LegalCopyright: |
Total processes
212
Monitored processes
59
Malicious processes
4
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 416 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2692,i,4723646839483390270,2535251780028985676,262144 --variations-seed-version --mojo-platform-channel-handle=2508 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 592 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=6532,i,4723646839483390270,2535251780028985676,262144 --variations-seed-version --mojo-platform-channel-handle=5676 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 592 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=6240,i,4723646839483390270,2535251780028985676,262144 --variations-seed-version --mojo-platform-channel-handle=8072 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 608 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,20480,768 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\System32\csrss.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 648 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2428,i,4723646839483390270,2535251780028985676,262144 --variations-seed-version --mojo-platform-channel-handle=2432 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1068 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1204 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc437af208,0x7ffc437af214,0x7ffc437af220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1232 | "C:\Users\admin\AppData\Local\Temp\is-J5RTU.tmp\is-CF62K.tmp" /SL4 $90230 "C:\Users\admin\AppData\Local\Temp\Setup.exe" 6618604 54784 | C:\Users\admin\AppData\Local\Temp\is-J5RTU.tmp\is-CF62K.tmp | Setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.44.0.0 Modules
| |||||||||||||||
| 1644 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\dxwsetup.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\dxwsetup.exe | dxwebsetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DirectX Setup Version: 4.9.0.0904 Modules
| |||||||||||||||
| 1728 | "C:\Users\admin\Downloads\dxwebsetup.exe" | C:\Users\admin\Downloads\dxwebsetup.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: DirectX 9.0 Web setup Exit code: 3221226540 Version: 9.29.1974.0 Modules
| |||||||||||||||
Total events
13 892
Read events
13 739
Write events
143
Delete events
10
Modification events
| (PID) Process: | (1232) is-CF62K.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Hamsterball_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.1.9 | |||
| (PID) Process: | (1232) is-CF62K.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Hamsterball_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files (x86)\Raptisoft\Hamsterball | |||
| (PID) Process: | (1232) is-CF62K.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Hamsterball_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files (x86)\Raptisoft\Hamsterball\ | |||
| (PID) Process: | (1232) is-CF62K.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Hamsterball_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Raptisoft\Hamsterball | |||
| (PID) Process: | (1232) is-CF62K.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Hamsterball_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (1232) is-CF62K.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Hamsterball_is1 |
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: desktopicon | |||
| (PID) Process: | (1232) is-CF62K.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Hamsterball_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Tasks |
Value: | |||
| (PID) Process: | (1232) is-CF62K.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Hamsterball_is1 |
| Operation: | write | Name: | DisplayName |
Value: Hamsterball 3.6 | |||
| (PID) Process: | (1232) is-CF62K.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Hamsterball_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files (x86)\Raptisoft\Hamsterball\unins000.exe" | |||
| (PID) Process: | (1232) is-CF62K.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Hamsterball_is1 |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Program Files (x86)\Raptisoft\Hamsterball\unins000.exe" /SILENT | |||
Executable files
28
Suspicious files
1 223
Text files
660
Unknown types
253
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1232 | is-CF62K.tmp | C:\Users\admin\AppData\Local\Temp\is-VOG13.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 1232 | is-CF62K.tmp | C:\Users\admin\AppData\Local\Temp\is-VOG13.tmp\_isetup\_RegDLL.tmp | executable | |
MD5:C594B792B9C556EA62A30DE541D2FB03 | SHA256:5DCC1E0A197922907BCA2C4369F778BD07EE4B1BBBDF633E987A028A314D548E | |||
| 1232 | is-CF62K.tmp | C:\Users\admin\AppData\Local\Temp\is-VOG13.tmp\_isetup\_setup64.tmp | executable | |
MD5:AA879BAA50DCCA58AD6CD14A92814695 | SHA256:7C4BCD92059137479EC4863A202D8E6EEA878EF1E45AC6C9E503498EA4977B8A | |||
| 6536 | Setup.exe | C:\Users\admin\AppData\Local\Temp\is-J5RTU.tmp\is-CF62K.tmp | executable | |
MD5:554131C651E5A5F9C8052ECE46E22905 | SHA256:F21D4EEE932389E77C1D008AF13D3B774F2552782CEF22AD4BA05F9BE4A8D5A6 | |||
| 1232 | is-CF62K.tmp | C:\Program Files (x86)\Raptisoft\Hamsterball\esellerateengine.dll | executable | |
MD5:7615A3BE9EAFC8ED4C0EE24103001703 | SHA256:0B718055667856D0FF0174C314AD0CC818F461713B9FC46F355193C69872949B | |||
| 1232 | is-CF62K.tmp | C:\Program Files (x86)\Raptisoft\Hamsterball\RaceData.xml | text | |
MD5:0AA40DE6DFE8BCE67DC29E9C5984F33F | SHA256:EE26D3E63B523B03F26D977B980BB920723902910439FAD0BB78D910FC43FD2A | |||
| 1232 | is-CF62K.tmp | C:\Program Files (x86)\Raptisoft\Hamsterball\is-JV0UN.tmp | executable | |
MD5:37A8C71FEEE5E71CB309E3B97DC3960F | SHA256:A51FCF190F7480A43AC92D34285A4477922DA731531047F1B27AC73FE0BF8DA0 | |||
| 1232 | is-CF62K.tmp | C:\Program Files (x86)\Raptisoft\Hamsterball\Hamsterball.exe | executable | |
MD5:37A8C71FEEE5E71CB309E3B97DC3960F | SHA256:A51FCF190F7480A43AC92D34285A4477922DA731531047F1B27AC73FE0BF8DA0 | |||
| 1232 | is-CF62K.tmp | C:\Program Files (x86)\Raptisoft\Hamsterball\is-J9N5H.tmp | text | |
MD5:0AA40DE6DFE8BCE67DC29E9C5984F33F | SHA256:EE26D3E63B523B03F26D977B980BB920723902910439FAD0BB78D910FC43FD2A | |||
| 1232 | is-CF62K.tmp | C:\Program Files (x86)\Raptisoft\Hamsterball\is-QHDSF.tmp | text | |
MD5:E6CC5EBD708D24DB9C41BADF7BE77B73 | SHA256:C8875F43B372D8549744128C384D73298B7D4A5307F44652EEF066646EF56A49 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
184
TCP/UDP connections
173
DNS requests
196
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4520 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4520 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7020 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5600 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750792706&P2=404&P3=2&P4=PsAUMRVvlawz96v2wEHlw6j%2bmXNltljPCzTO3iZrgaA3aJstpJjMv9SzXlFch%2bL97RmvUC5g%2bl3AJCFwNfKY3w%3d%3d | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
3052 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:WBzai-S4WrhawHZacbmAqOOg116mjiPUNnk-_G4tJQI&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
5600 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750792706&P2=404&P3=2&P4=PsAUMRVvlawz96v2wEHlw6j%2bmXNltljPCzTO3iZrgaA3aJstpJjMv9SzXlFch%2bL97RmvUC5g%2bl3AJCFwNfKY3w%3d%3d | unknown | — | — | whitelisted |
5600 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750792706&P2=404&P3=2&P4=PsAUMRVvlawz96v2wEHlw6j%2bmXNltljPCzTO3iZrgaA3aJstpJjMv9SzXlFch%2bL97RmvUC5g%2bl3AJCFwNfKY3w%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3396 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4520 | SIHClient.exe | 20.109.210.53:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4520 | SIHClient.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
Threats
Process | Message |
|---|---|
dxwsetup.exe | DLL_PROCESS_ATTACH |
dxwsetup.exe | DLL_PROCESS_DETACH |
dxwsetup.exe | DLL_PROCESS_DETACH |
dxwsetup.exe | Invalid parameter passed to C runtime function.
|
dxwsetup.exe | DLL_PROCESS_ATTACH |
dxwsetup.exe | Invalid parameter passed to C runtime function.
|
dxwsetup.exe | DLL_PROCESS_ATTACH |
dxwsetup.exe | DLL_PROCESS_ATTACH |