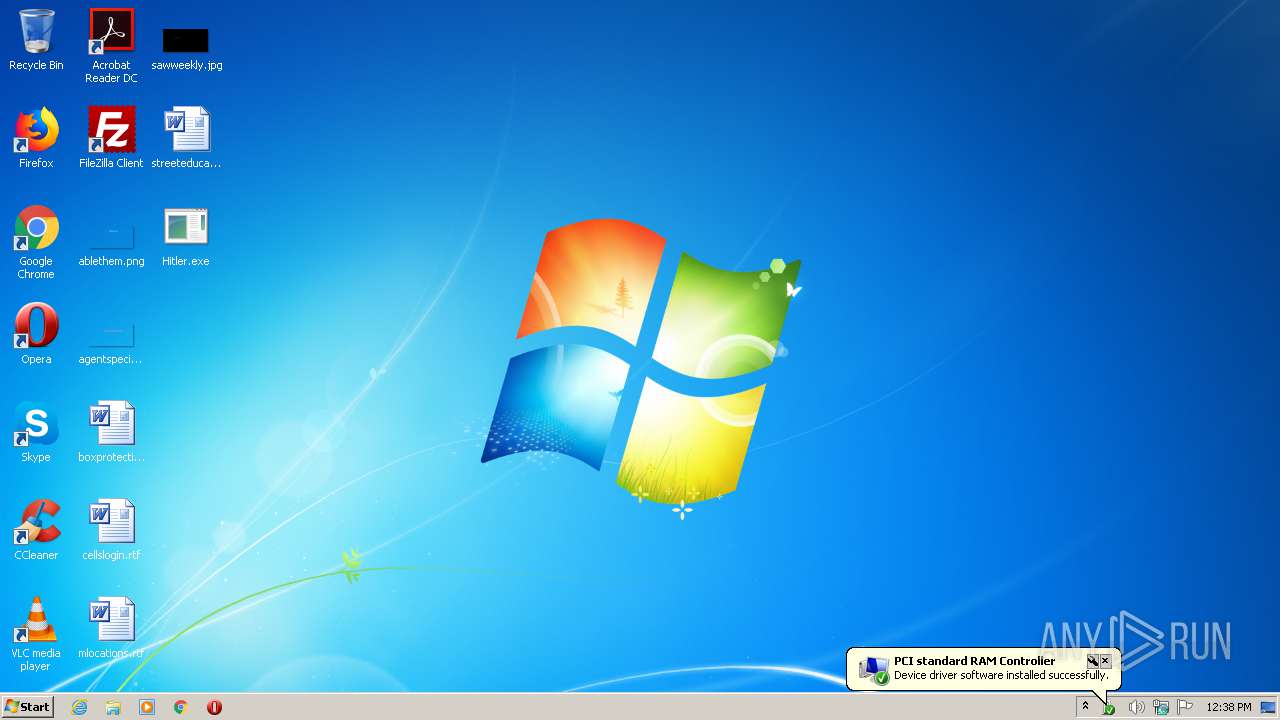
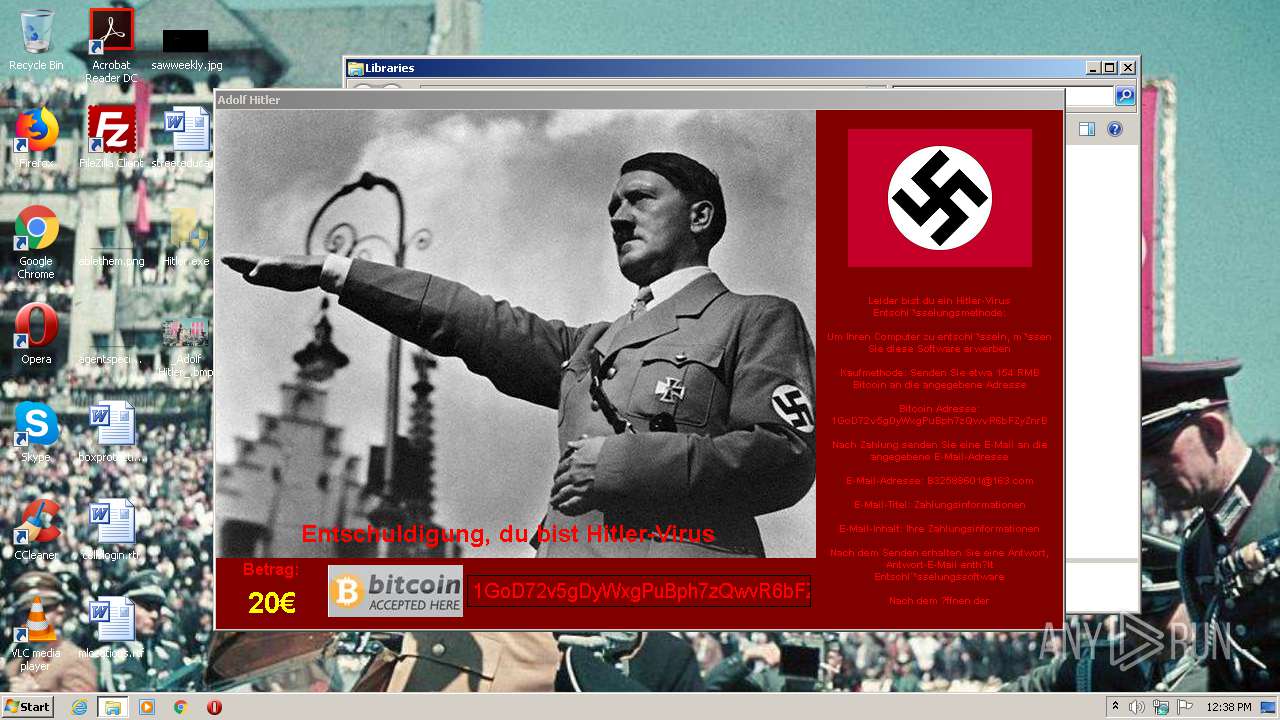
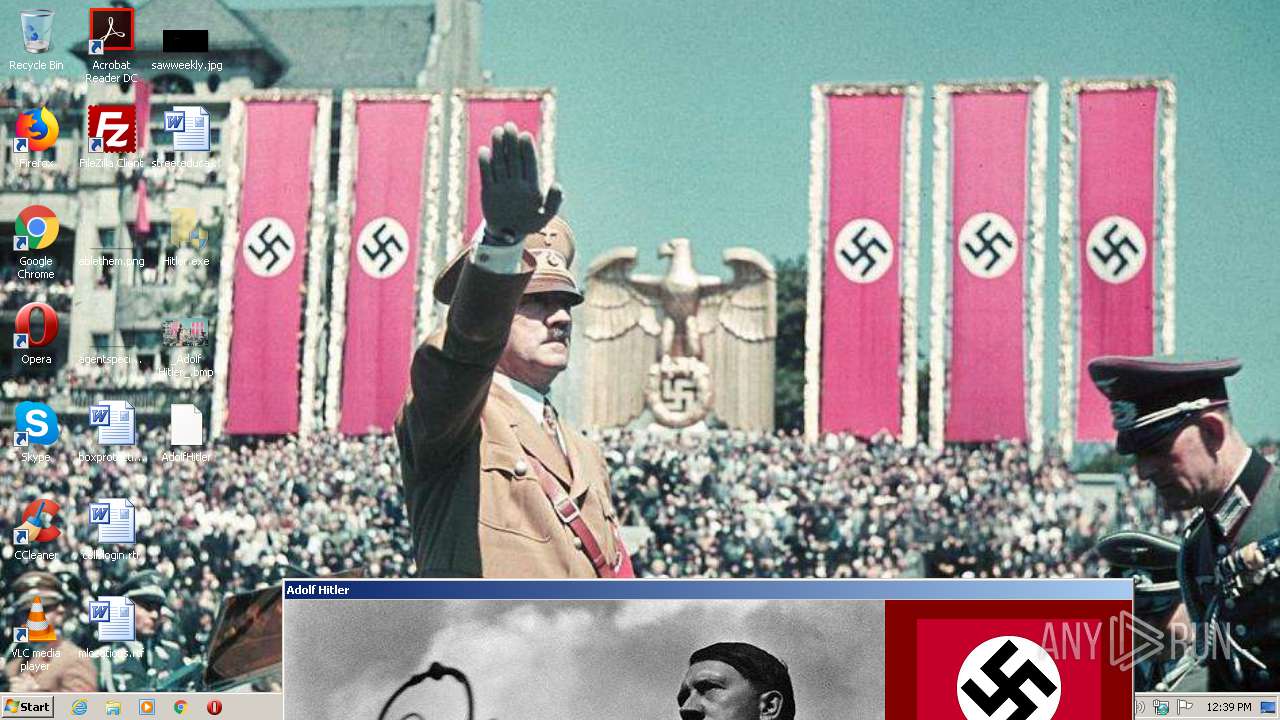
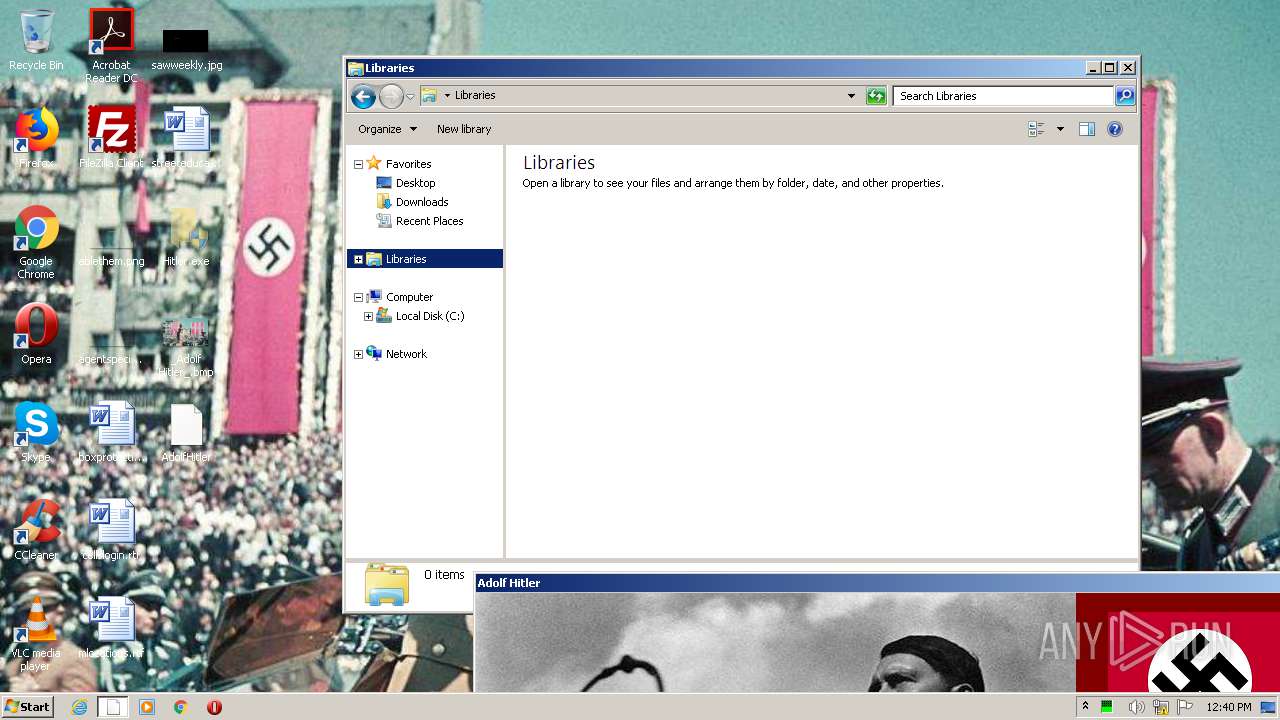
| File name: | Hitler.exe |
| Full analysis: | https://app.any.run/tasks/d9669d34-68a1-4745-8d3e-b1c73b66135c |
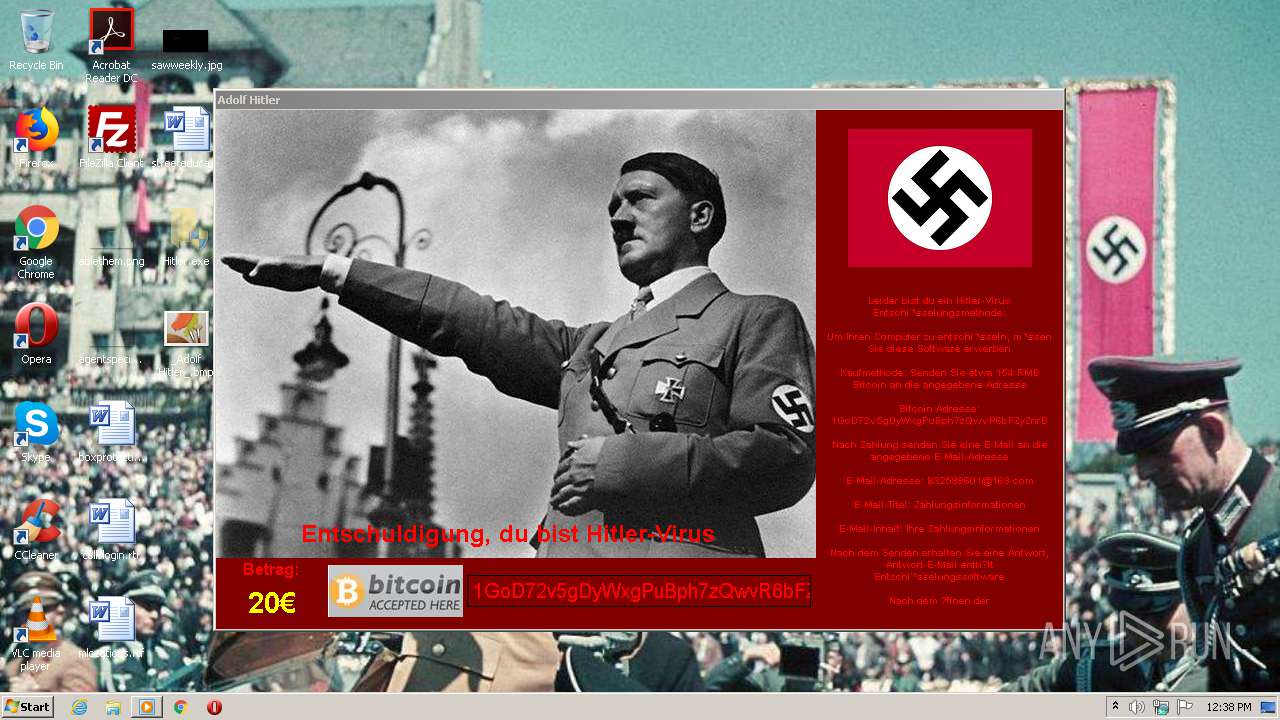
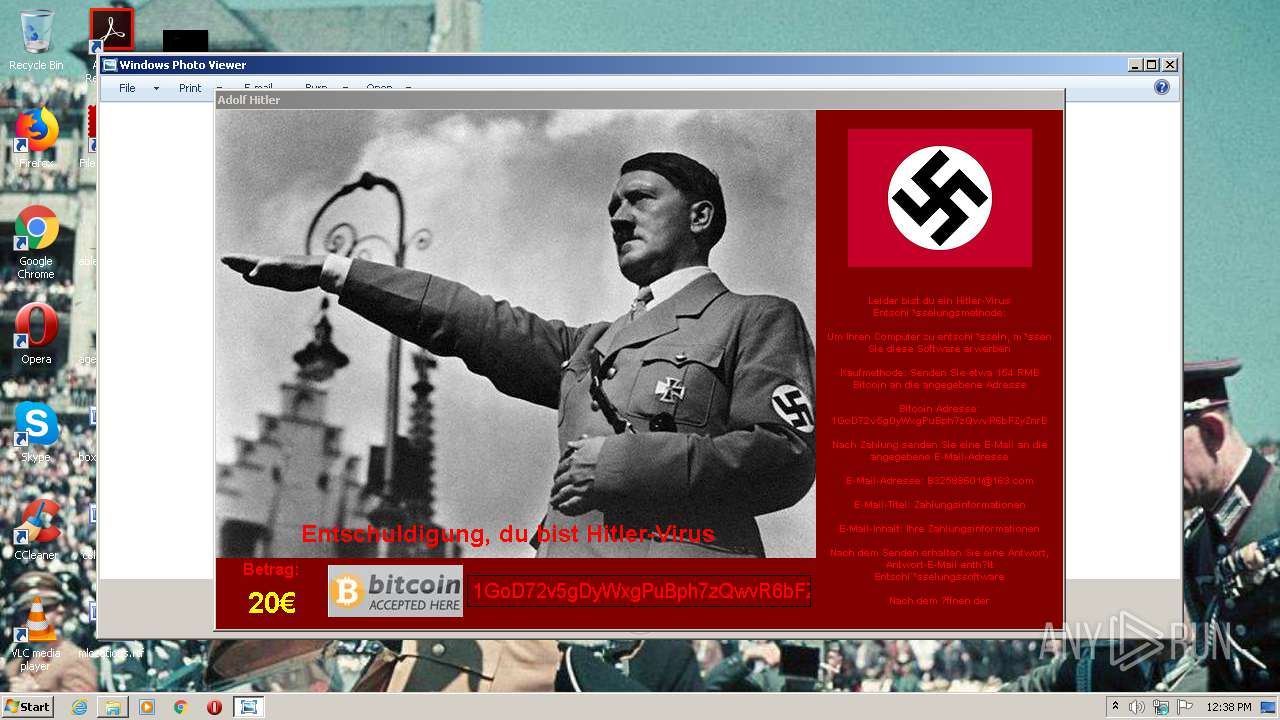
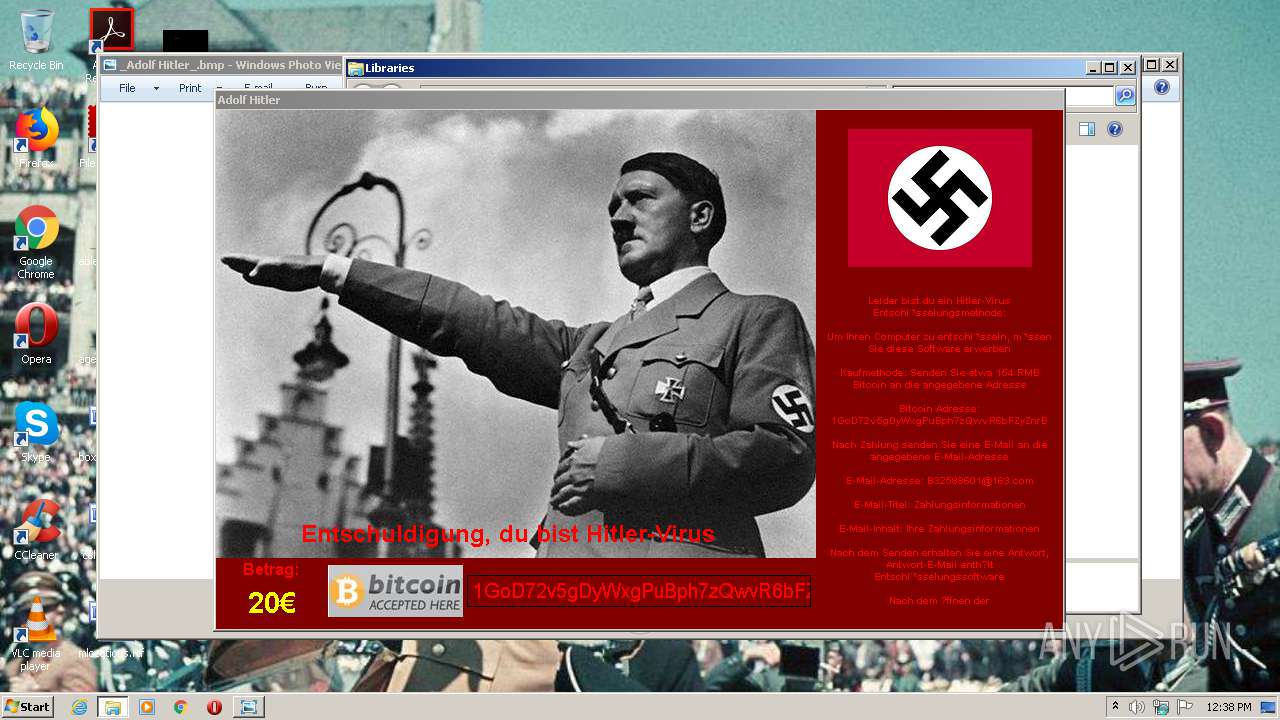
| Verdict: | Malicious activity |
| Analysis date: | August 24, 2020, 11:38:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | E64DBE09FC1805177D9058A40807E128 |
| SHA1: | FC15F43BE27987315C8BCF61FF392FF8AC3E394C |
| SHA256: | 9AE7D51B7C3E729D9FD0EB7B99811DE3270E7B37931FFF1F136EFEB50D276A4C |
| SSDEEP: | 98304:h8srYwCbFbLFVeGoXSKUa+sRlKSZt646FVbCJUpQdAahhGvLlhkmyNe4y4WNMvs:hh0b5eGoC0PRB6JPk6 |
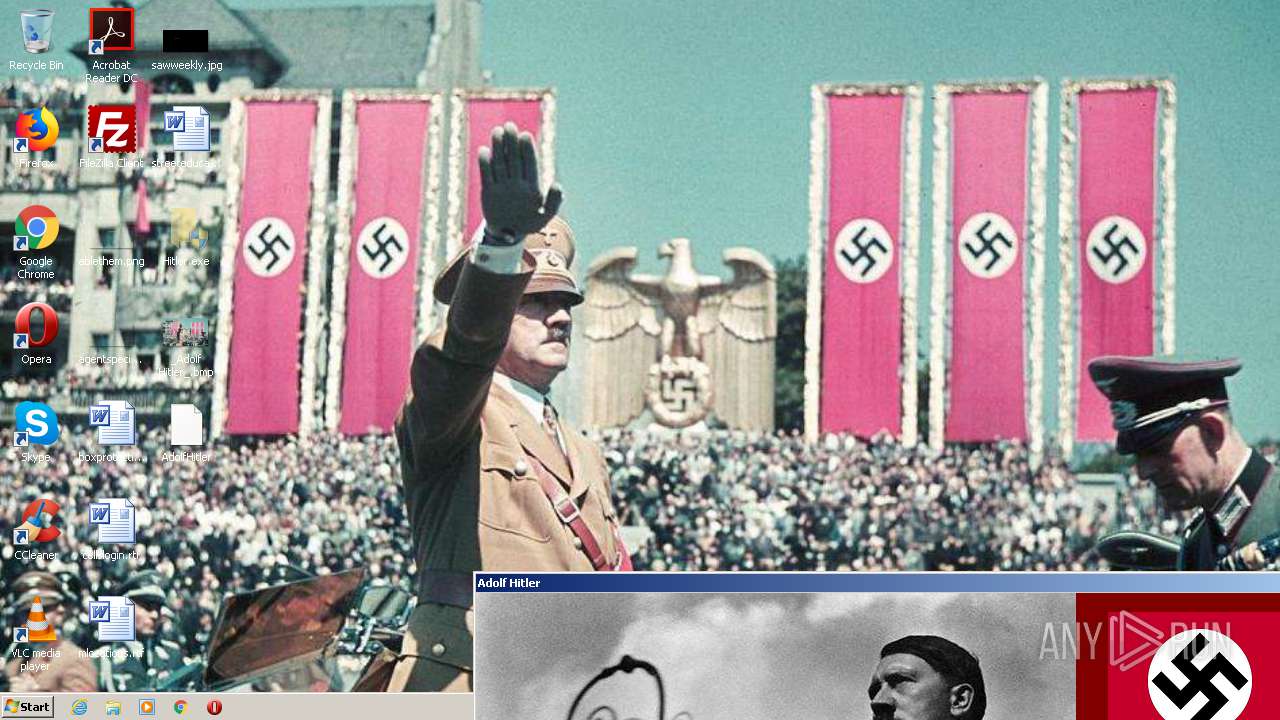
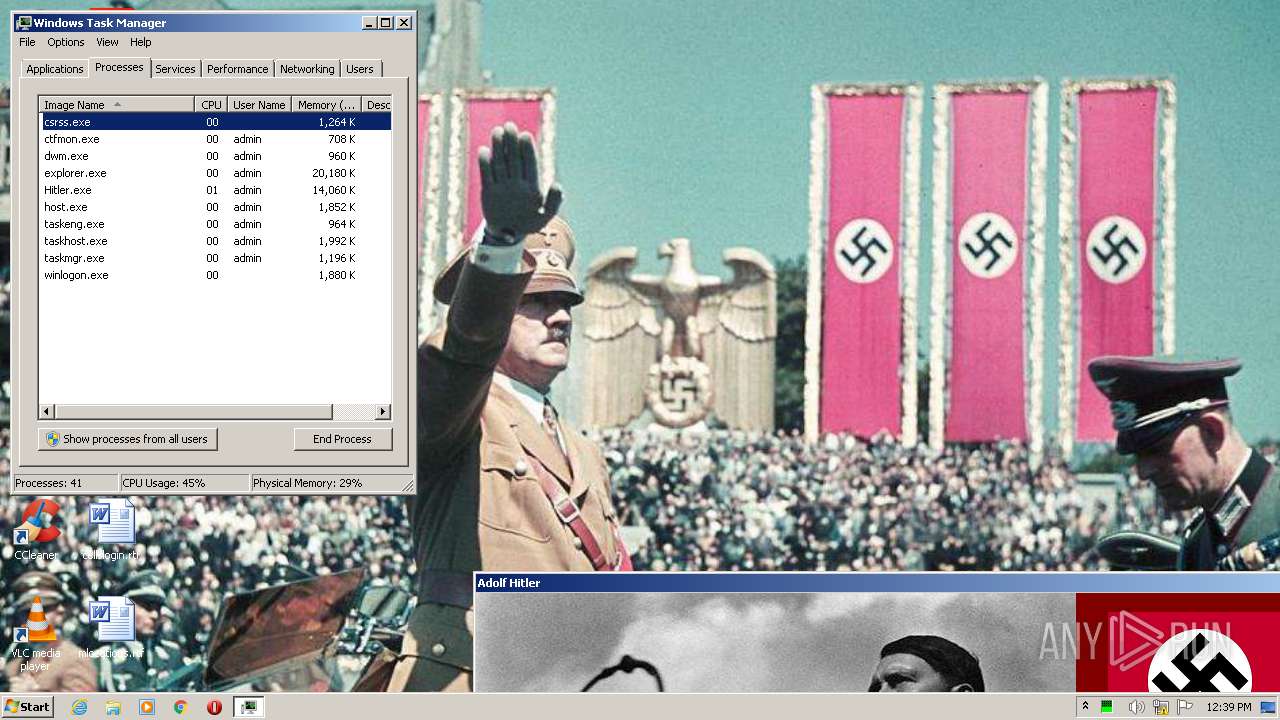
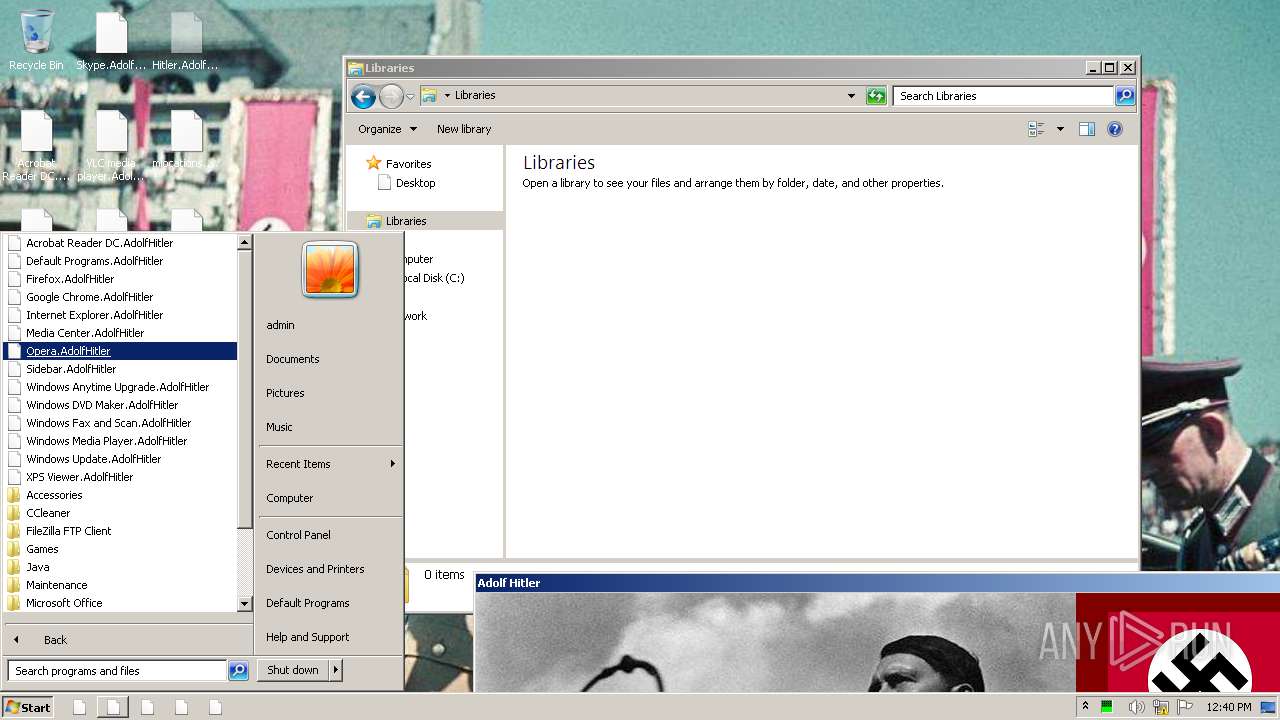
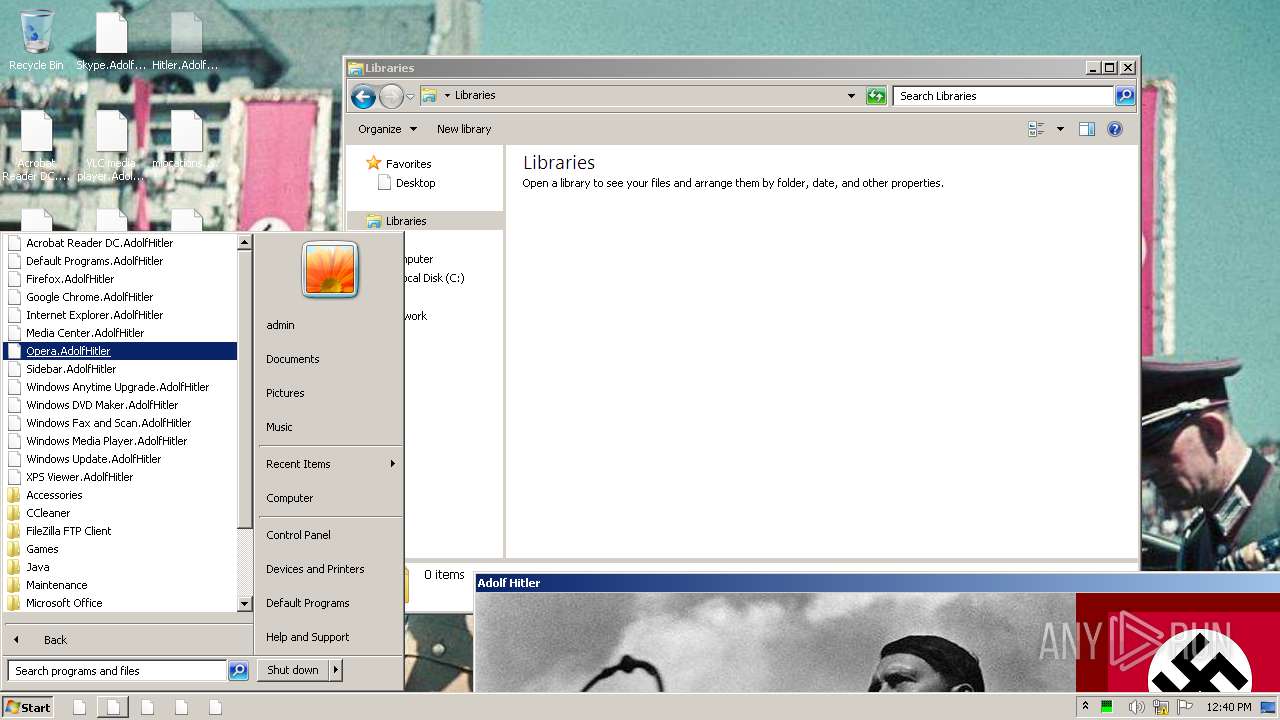
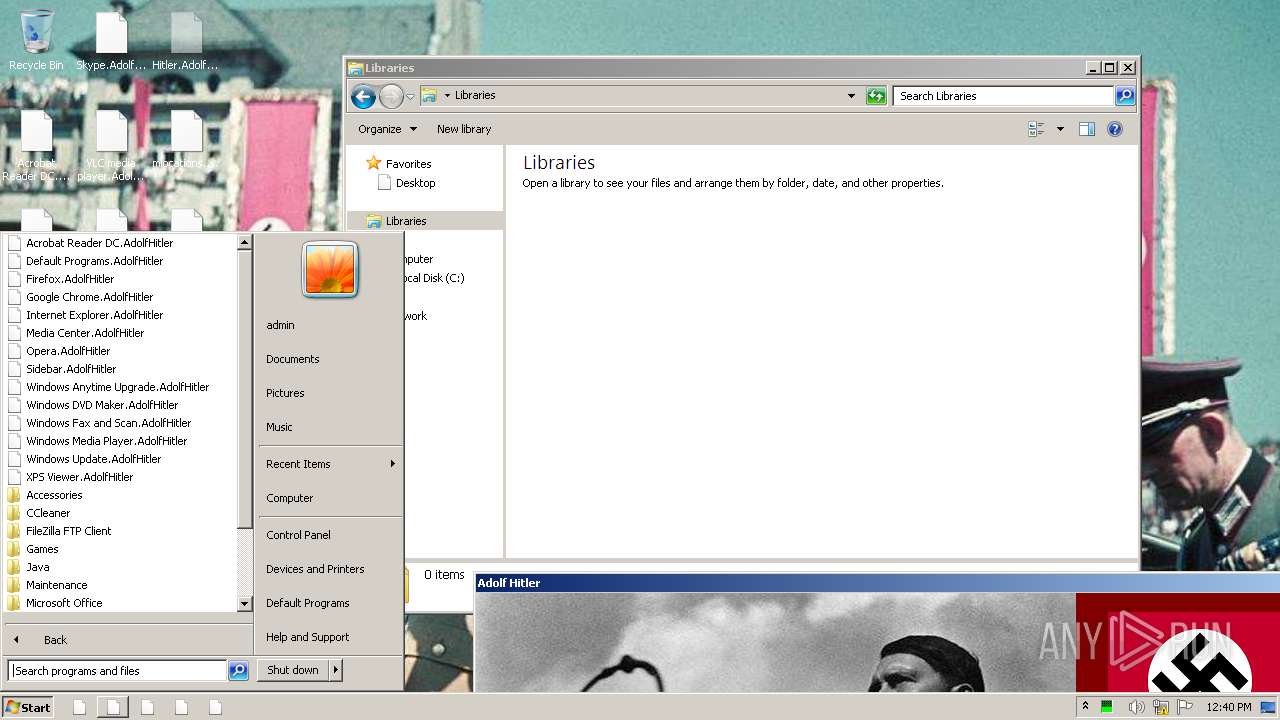
MALICIOUS
UAC/LUA settings modification
- Hitler.exe (PID: 3848)
Changes the autorun value in the registry
- Hitler.exe (PID: 3848)
Deletes shadow copies
- cmd.exe (PID: 2676)
Starts BCDEDIT.EXE to disable recovery
- cmd.exe (PID: 2676)
Loads the Task Scheduler COM API
- wbengine.exe (PID: 2904)
SUSPICIOUS
Starts CMD.EXE for commands execution
- Hitler.exe (PID: 3848)
Creates files in the Windows directory
- Hitler.exe (PID: 3848)
- wbadmin.exe (PID: 3844)
Executed via COM
- DllHost.exe (PID: 2428)
- vdsldr.exe (PID: 3956)
Uses ICACLS.EXE to modify access control list
- Hitler.exe (PID: 3848)
Reads Internet Cache Settings
- Hitler.exe (PID: 3848)
Executed as Windows Service
- wbengine.exe (PID: 2904)
- vds.exe (PID: 3512)
Low-level read access rights to disk partition
- wbengine.exe (PID: 2904)
- vds.exe (PID: 3512)
Creates files in the user directory
- Hitler.exe (PID: 3848)
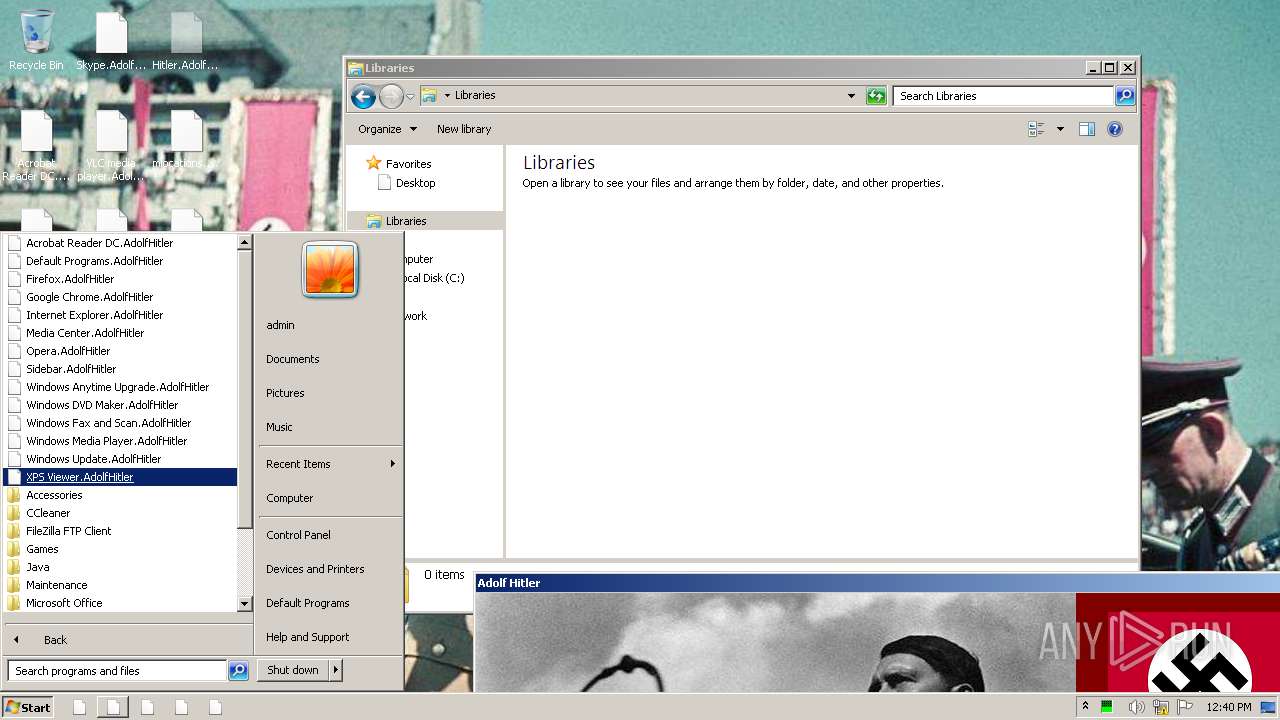
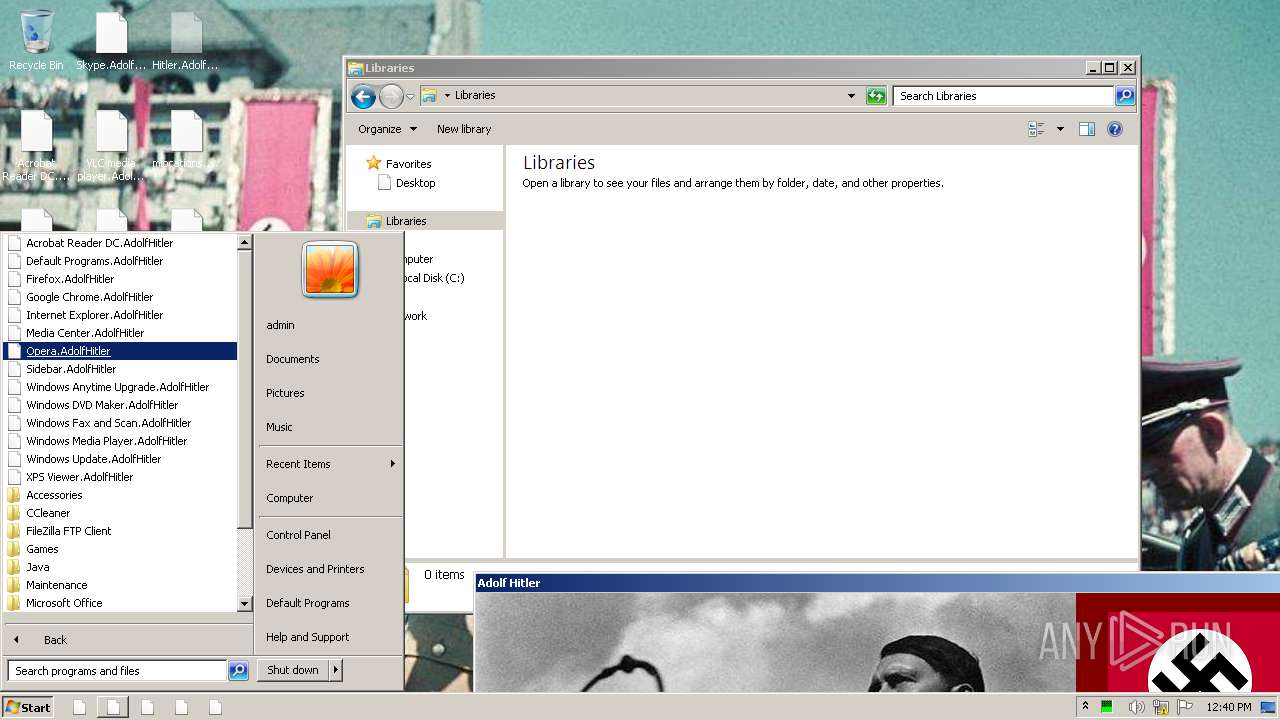
INFO
Manual execution by user
- explorer.exe (PID: 2496)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (33.3) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (32.6) |
| .scr | | | Windows screen saver (15.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.9) |
| .exe | | | Win32 Executable (generic) (5.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:11:05 05:11:25+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 3190784 |
| InitializedDataSize: | 335872 |
| UninitializedDataSize: | 1032192 |
| EntryPoint: | 0x407760 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Nov-2017 04:11:25 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 05-Nov-2017 04:11:25 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x000FC000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x000FD000 | 0x0030B000 | 0x0030AA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.63325 |
.rsrc | 0x00408000 | 0x00052000 | 0x00051E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.31127 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.02094 | 697 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 2.18858 | 296 | UNKNOWN | Chinese - PRC | RT_ICON |
3 | 3.09498 | 270376 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.17246 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 3.13037 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 3.22277 | 6760 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 3.19411 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 3.37649 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 3.47976 | 1720 | UNKNOWN | UNKNOWN | RT_ICON |
10 | 4.10875 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
OLEAUT32.dll |
RASAPI32.dll |
SHELL32.dll |
USER32.dll |
WININET.dll |
WINMM.dll |
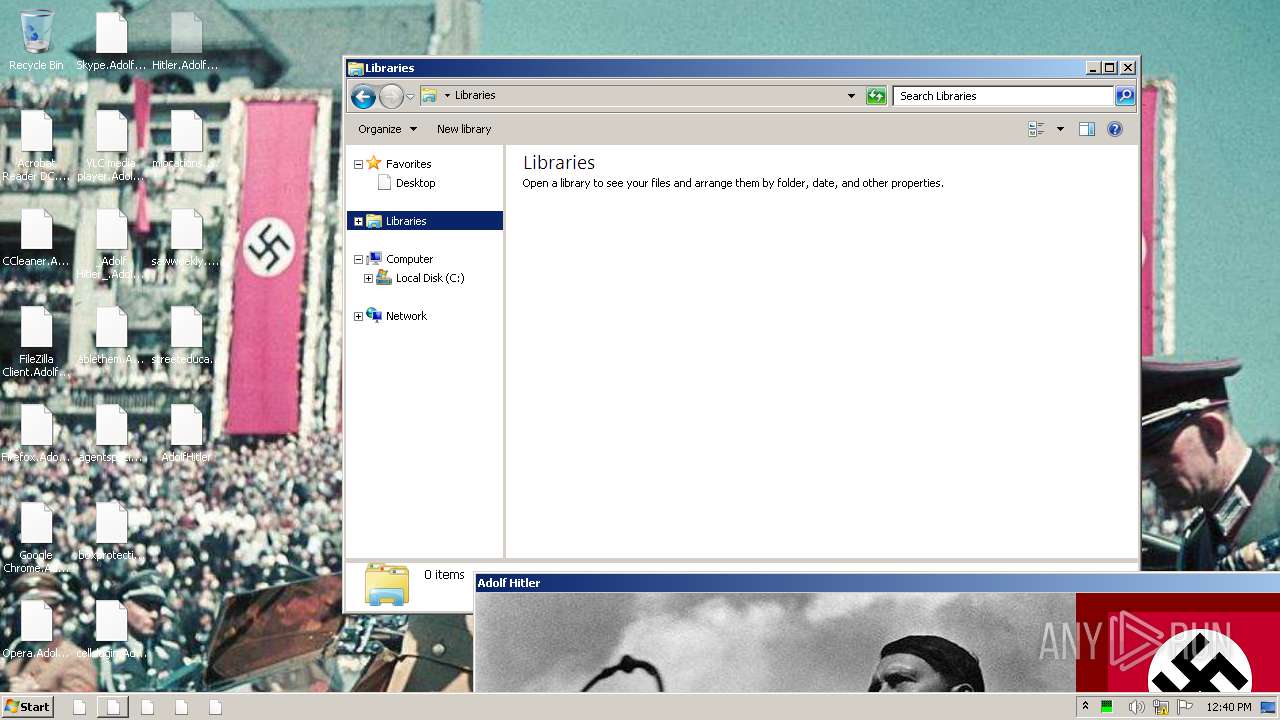
Total processes
62
Monitored processes
14
Malicious processes
2
Suspicious processes
1
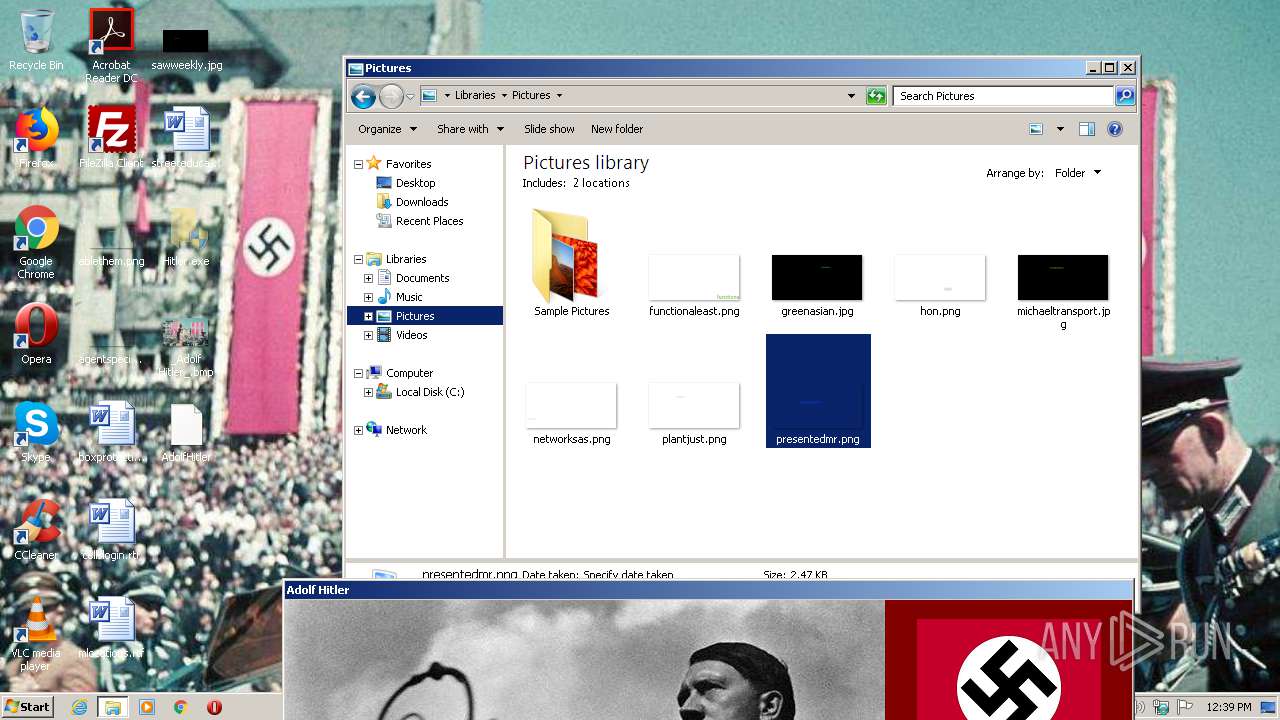
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 608 | wmic shadowcopy delete | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1452 | bcdedit /set {default} recoveryenabled no | C:\Windows\system32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1548 | "C:\Users\admin\Desktop\Hitler.exe" | C:\Users\admin\Desktop\Hitler.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2428 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2496 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2676 | cmd /c vssadmin delete shadow /all /quiet & wmic shadowcopy delete & bcdedit /set {default} boostatuspolicy ignoreallfailures & bcdedit /set {default} recoveryenabled no & wbadmin delete catalog -quiet | C:\Windows\system32\cmd.exe | — | Hitler.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2696 | bcdedit /set {default} boostatuspolicy ignoreallfailures | C:\Windows\system32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2824 | icacls . /grant Everyone:F /T /C /Q | C:\Windows\system32\icacls.exe | — | Hitler.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2904 | "C:\Windows\system32\wbengine.exe" | C:\Windows\system32\wbengine.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Block Level Backup Engine Service EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3024 | vssadmin delete shadow /all /quiet | C:\Windows\system32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
275
Read events
259
Write events
16
Delete events
0
Modification events
| (PID) Process: | (3848) Hitler.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (3848) Hitler.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Adolf Hitler |
Value: C:\Users\admin\Desktop\Hitler.exe | |||
| (PID) Process: | (3848) Hitler.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {FFE2A43C-56B9-4BF5-9A79-CC6D4285608A} {00000122-0000-0000-C000-000000000046} 0xFFFF |
Value: 0100000000000000CE14EB230B7AD601 | |||
| (PID) Process: | (3848) Hitler.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Hitler.exe | |||
| (PID) Process: | (2428) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
| (PID) Process: | (3848) Hitler.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3848) Hitler.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3848) Hitler.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3848) Hitler.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3848) Hitler.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
0
Suspicious files
20 452
Text files
12
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3848 | Hitler.exe | C:\autoexec.bat | — | |
MD5:— | SHA256:— | |||
| 3848 | Hitler.exe | C:\config.sys | — | |
MD5:— | SHA256:— | |||
| 3848 | Hitler.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccessMUI.msi | — | |
MD5:— | SHA256:— | |||
| 3848 | Hitler.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccLR.cab | — | |
MD5:— | SHA256:— | |||
| 3848 | Hitler.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\branding.xml | — | |
MD5:— | SHA256:— | |||
| 3848 | Hitler.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\Setup.xml | — | |
MD5:— | SHA256:— | |||
| 3848 | Hitler.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\AccessMUI.msi | — | |
MD5:— | SHA256:— | |||
| 3848 | Hitler.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\AccLR.cab | — | |
MD5:— | SHA256:— | |||
| 3848 | Hitler.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\branding.xml | — | |
MD5:— | SHA256:— | |||
| 3848 | Hitler.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\Setup.xml | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
5
DNS requests
5
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 120.41.45.83:80 | http://top.ip138.com/ | CN | html | 5.32 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3848 | Hitler.exe | 103.235.46.39:80 | www.baidu.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | HK | unknown |
3848 | Hitler.exe | 163.171.128.148:80 | www.ip138.com | — | US | malicious |
— | — | 120.41.45.83:80 | top.ip138.com | Xiamen | CN | unknown |
3848 | Hitler.exe | 123.126.97.5:25 | smtp.163.com | China Unicom Beijing Province Network | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.baidu.com |
| whitelisted |
smtp.163.com |
| shared |
www.ip138.com |
| suspicious |
top.ip138.com |
| malicious |
2020.ip138.com |
| unknown |
Threats
1 ETPRO signatures available at the full report