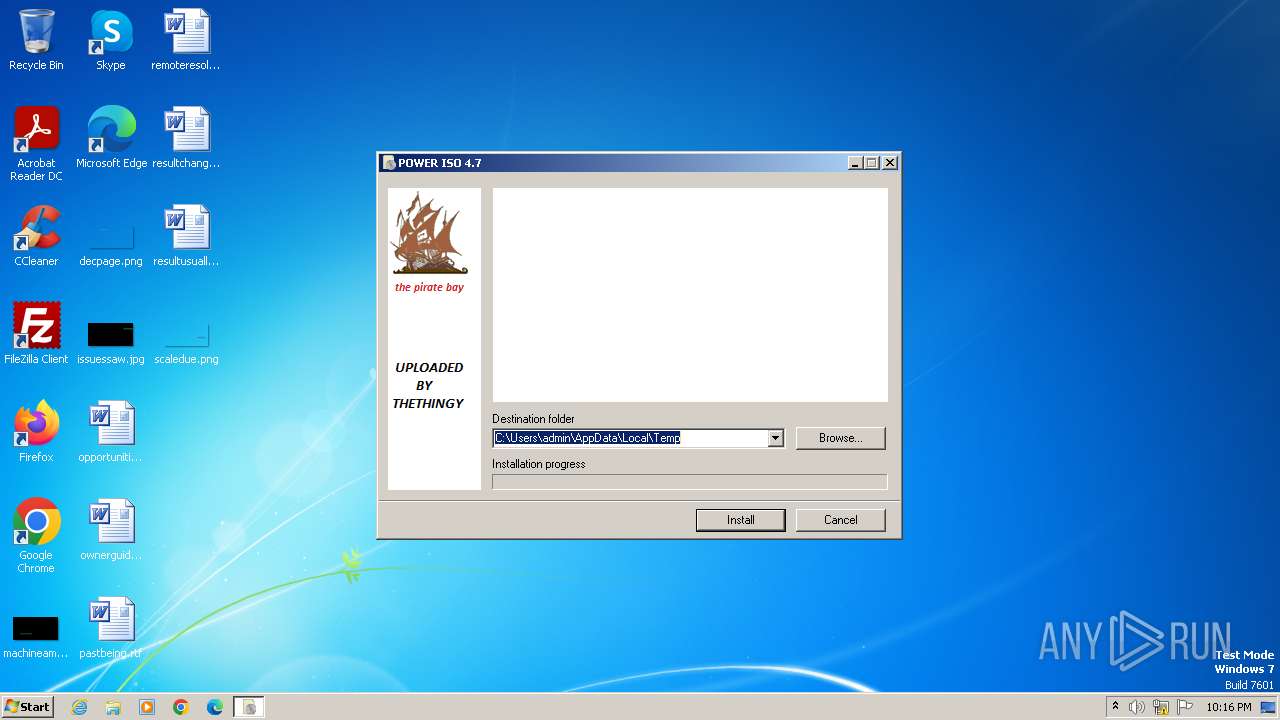
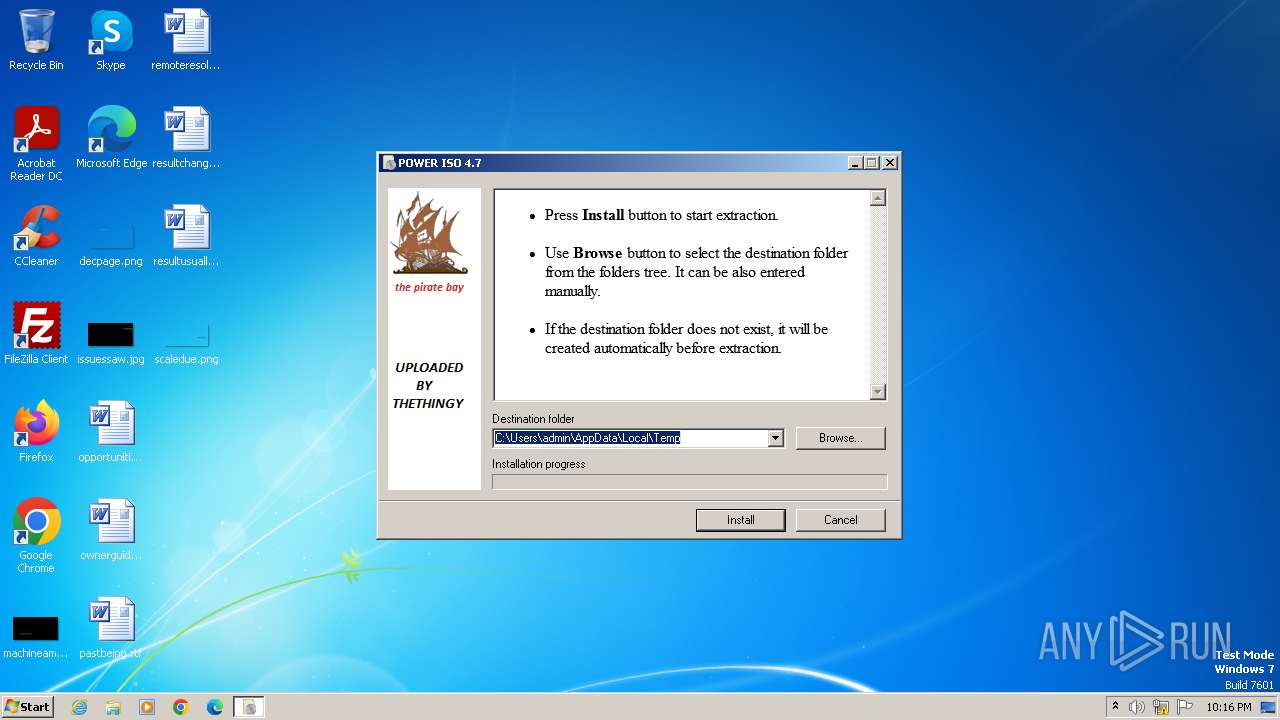
| File name: | POWER ISO 4.7.exe |
| Full analysis: | https://app.any.run/tasks/42cf9f49-5fe1-446f-af4d-e67bfc3a80c0 |
| Verdict: | Malicious activity |
| Analysis date: | June 06, 2024, 21:16:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | A69365FF2809EB091744C813EBFFD7D7 |
| SHA1: | 26F8ABC0DC561FB142647E87D4720839F48A880D |
| SHA256: | 9ADDB074CC376C56AB25AE93E2CBB073EBE6B7084E866A5142B066A9F2C44A58 |
| SSDEEP: | 98304:Y+NA0T/t1UVkq73IDe78Rf/pIZTCs7m8SLhXANp/wh8nnhv+U6scPnBS3g1JeYqT:Q+LPI |
MALICIOUS
Drops the executable file immediately after the start
- POWER ISO 4.7.exe (PID: 3976)
SUSPICIOUS
Reads Microsoft Outlook installation path
- POWER ISO 4.7.exe (PID: 3976)
Reads security settings of Internet Explorer
- POWER ISO 4.7.exe (PID: 3976)
Reads Internet Explorer settings
- POWER ISO 4.7.exe (PID: 3976)
Reads the Internet Settings
- POWER ISO 4.7.exe (PID: 3976)
Executable content was dropped or overwritten
- POWER ISO 4.7.exe (PID: 3976)
INFO
Checks supported languages
- POWER ISO 4.7.exe (PID: 3976)
Reads the computer name
- POWER ISO 4.7.exe (PID: 3976)
Checks proxy server information
- POWER ISO 4.7.exe (PID: 3976)
Reads the machine GUID from the registry
- POWER ISO 4.7.exe (PID: 3976)
Create files in a temporary directory
- POWER ISO 4.7.exe (PID: 3976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:02:10 13:09:37+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 67584 |
| InitializedDataSize: | 182784 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa785 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
32
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3976 | "C:\Users\admin\AppData\Local\Temp\POWER ISO 4.7.exe" | C:\Users\admin\AppData\Local\Temp\POWER ISO 4.7.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
956
Read events
937
Write events
13
Delete events
6
Modification events
| (PID) Process: | (3976) POWER ISO 4.7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3976) POWER ISO 4.7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (3976) POWER ISO 4.7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
| (PID) Process: | (3976) POWER ISO 4.7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoConfigURL |
Value: | |||
| (PID) Process: | (3976) POWER ISO 4.7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoDetect |
Value: | |||
| (PID) Process: | (3976) POWER ISO 4.7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005D010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3976) POWER ISO 4.7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3976) POWER ISO 4.7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3976) POWER ISO 4.7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3976) POWER ISO 4.7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3976 | POWER ISO 4.7.exe | C:\Users\admin\AppData\Local\Temp\POWER ISO 4.7\PowerISO47.exe | executable | |
MD5:A38F725A0367F27E37BF2D01193FD8C7 | SHA256:64DA7BAF8AC5F781E019ED2EBC3D2F830013CB103B71C29A59913A40E53C42CB | |||
| 3976 | POWER ISO 4.7.exe | C:\Users\admin\AppData\Local\Temp\POWER ISO 4.7\SERIALS.txt | text | |
MD5:8034106DB483F480882DF4797CB224ED | SHA256:55B3E438411F29CCB3D3907C6D7F4F3D766CCFB0DA3E167138DF699263239D0F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |