| download: | domino.exe |
| Full analysis: | https://app.any.run/tasks/1f53edfd-8c67-439a-892c-faa885712621 |
| Verdict: | Suspicious activity |
| Analysis date: | July 20, 2020, 13:03:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 34F4AD30D314B15A4C614C6898365AB9 |
| SHA1: | F0115042CB40267C862227550CAB222D572ACFFF |
| SHA256: | 9ACC8EA064A8AE25AA316684158209036A532190E842DF273814B803712C026C |
| SSDEEP: | 98304:phtqXRbNOc7ZWrn54cdleJrsjwEPerA8+u0g+aoDnFh9:paOclun54cd0Jevo0aorj9 |
MALICIOUS
No malicious indicators.SUSPICIOUS
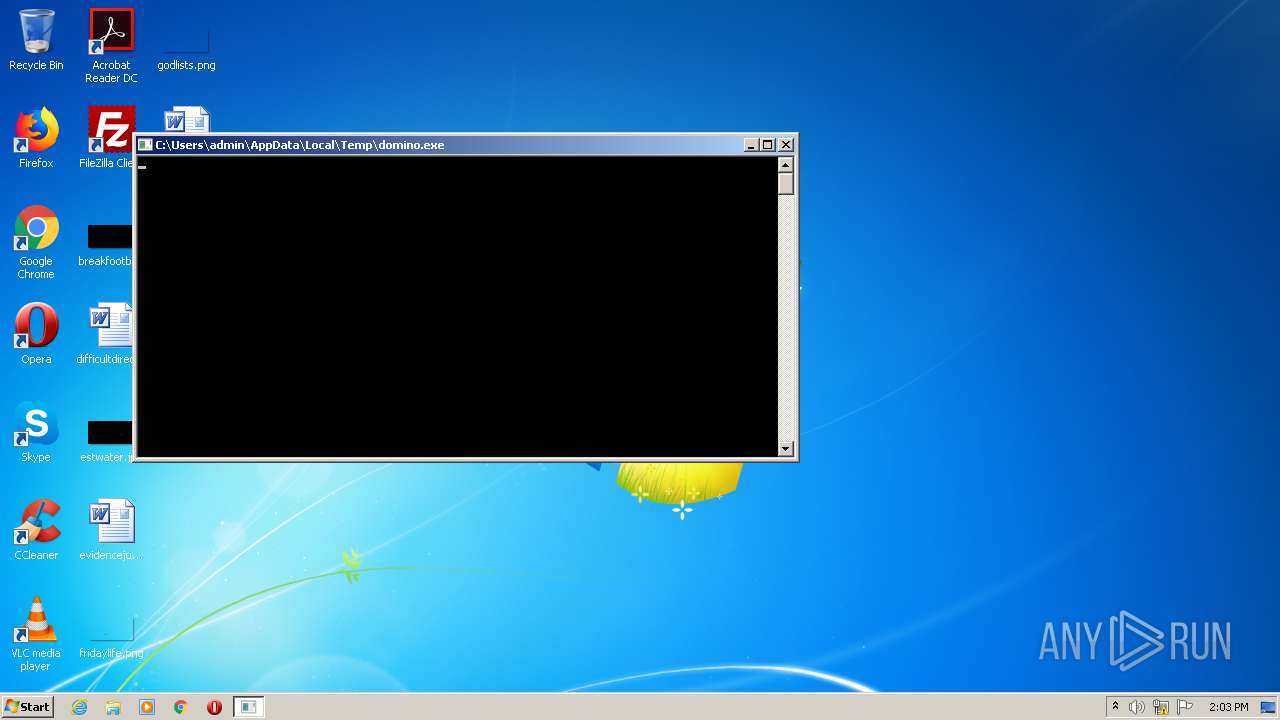
Application launched itself
- domino.exe (PID: 3248)
Starts CMD.EXE for self-deleting
- domino.exe (PID: 3248)
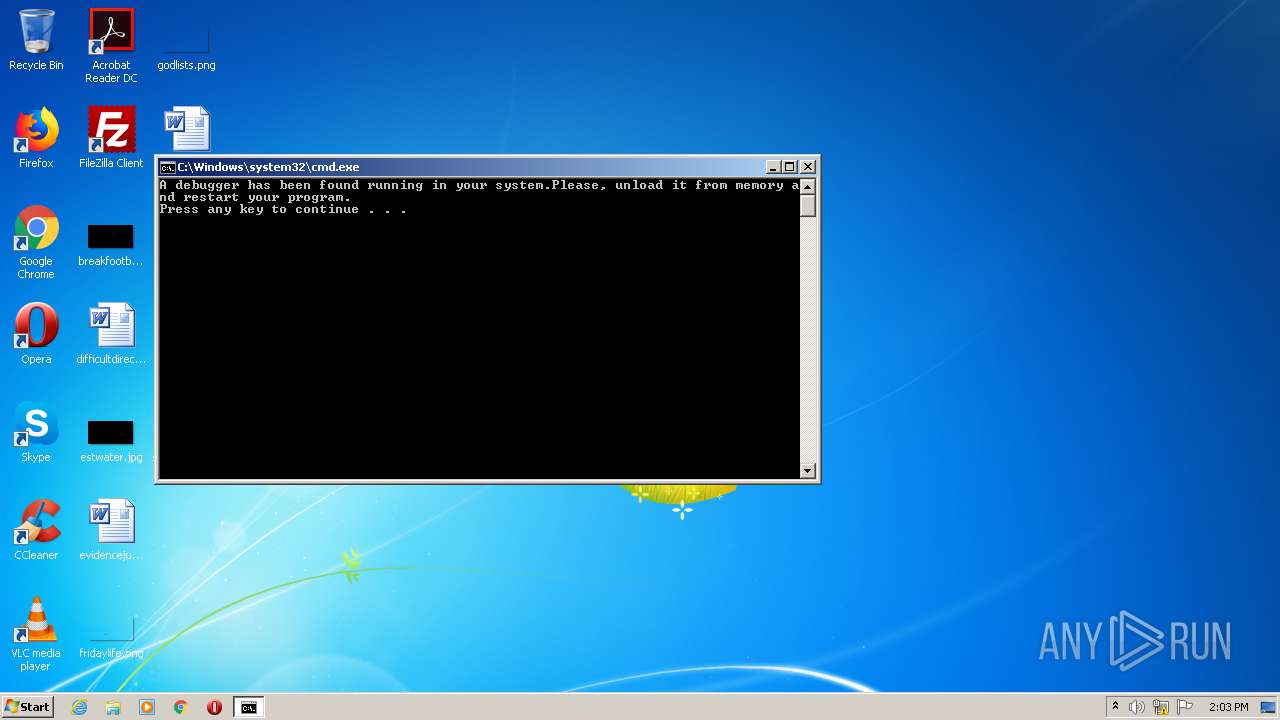
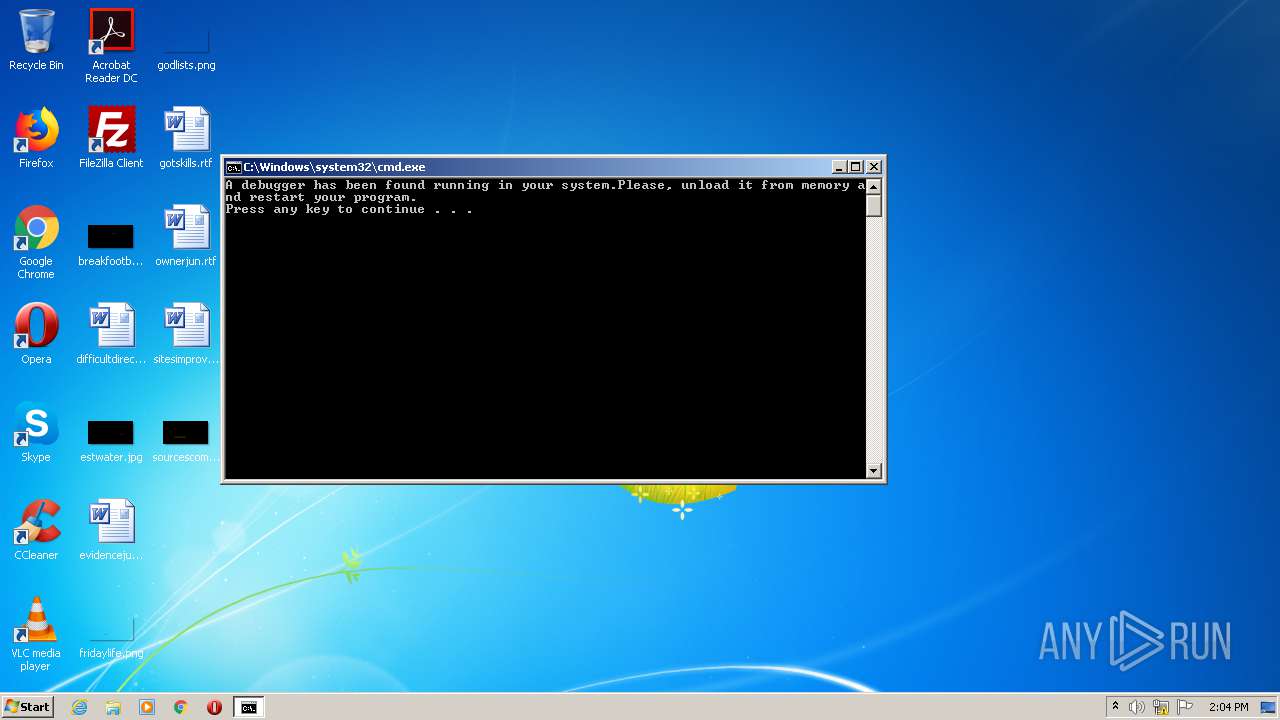
Starts CMD.EXE for commands execution
- domino.exe (PID: 3248)
INFO
Reads settings of System Certificates
- domino.exe (PID: 3248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2038:06:18 09:46:59+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 12288 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xbd0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | CrackMe_simple |
| FileVersion: | 1.0.0.0 |
| InternalName: | simple.exe |
| LegalCopyright: | Copyright © 2019 |
| LegalTrademarks: | - |
| OriginalFileName: | simple.exe |
| ProductName: | CrackMe_simple |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 13-May-1902 01:18:43 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | CrackMe_simple |
| FileVersion: | 1.0.0.0 |
| InternalName: | simple.exe |
| LegalCopyright: | Copyright © 2019 |
| LegalTrademarks: | - |
| OriginalFilename: | simple.exe |
| ProductName: | CrackMe_simple |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 13-May-1902 01:18:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x00002000 | 0x00004000 | 0x0000074C | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.86432 | |
\xb8\x05 | 0x00006000 | 0x000005B8 | 0x00000293 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.65104 |
\x0c | 0x00008000 | 0x0000000C | 0x00000035 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.53924 |
.imports | 0x0000A000 | 0x00002000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.05882 |
.rsrc | 0x0000C000 | 0x00002000 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.09994 |
WANNABE1 | 0x0000E000 | 0x0079E000 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.boot | 0x007AC000 | 0x00424000 | 0x00424000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.95407 |
.taggant | 0x00BD0000 | 0x00002200 | 0x00002014 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.83298 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
kernel32.dll |
mscoree.dll |
Total processes
40
Monitored processes
5
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2624 | "C:\Users\admin\AppData\Local\Temp\domino.exe" | C:\Users\admin\AppData\Local\Temp\domino.exe | — | domino.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: CrackMe_simple Exit code: 3221226324 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2700 | TIMEOUT 2 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3080 | cmd.exe /C TIMEOUT 2 > Nul & Del "C:\Users\admin\AppData\Local\Temp\domino.exe" | C:\Windows\system32\cmd.exe | — | domino.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3248 | "C:\Users\admin\AppData\Local\Temp\domino.exe" | C:\Users\admin\AppData\Local\Temp\domino.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: CrackMe_simple Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3352 | cmd.exe /C echo A debugger has been found running in your system.Please, unload it from memory and restart your program. && pause | C:\Windows\system32\cmd.exe | — | domino.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
35
Read events
20
Write events
15
Delete events
0
Modification events
| (PID) Process: | (3248) domino.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3248) domino.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (3248) domino.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
| (PID) Process: | (3248) domino.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dnsapi.dll,-103 |
Value: Domain Name System (DNS) Server Trust | |||
| (PID) Process: | (3248) domino.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-843 |
Value: BitLocker Drive Encryption | |||
| (PID) Process: | (3248) domino.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-844 |
Value: BitLocker Data Recovery Agent | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report