| download: | /Da2dalus/The-MALWARE-Repo/raw/master/Ransomware/RedEye.exe |
| Full analysis: | https://app.any.run/tasks/41cdd63a-7bc9-4d84-b576-65b5594f3556 |
| Verdict: | Malicious activity |
| Analysis date: | April 11, 2024, 08:26:33 |
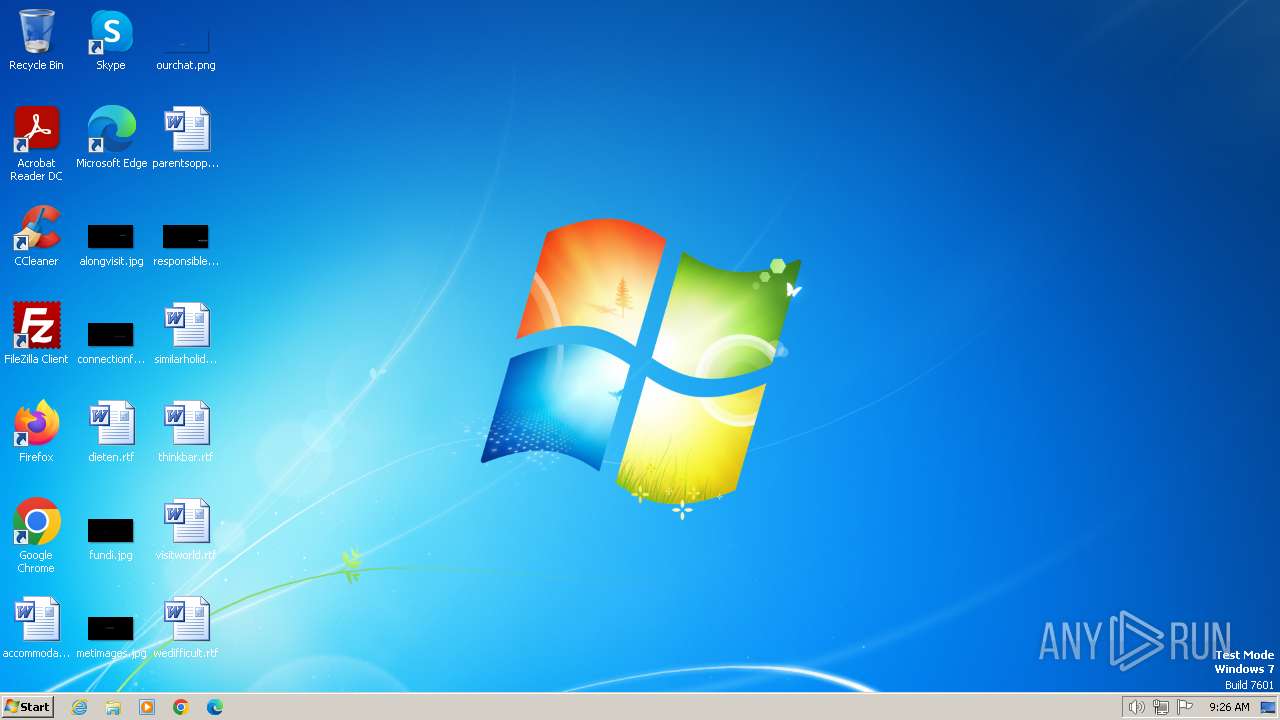
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | E9E5596B42F209CC058B55EDC2737A80 |
| SHA1: | F30232697B3F54E58AF08421DA697262C99EC48B |
| SHA256: | 9AC9F207060C28972EDE6284137698CE0769E3695C7AD98AB320605D23362305 |
| SSDEEP: | 196608:+ahZ5qN3wvdJBiAv1hXx7jeeDt9/wGoyIu+sTvDmQONhL/LslAVyq8rZyA+TXtTa:+w6NAvPAA/Xx3eeDtTD+GDONhL/AlAVm |
MALICIOUS
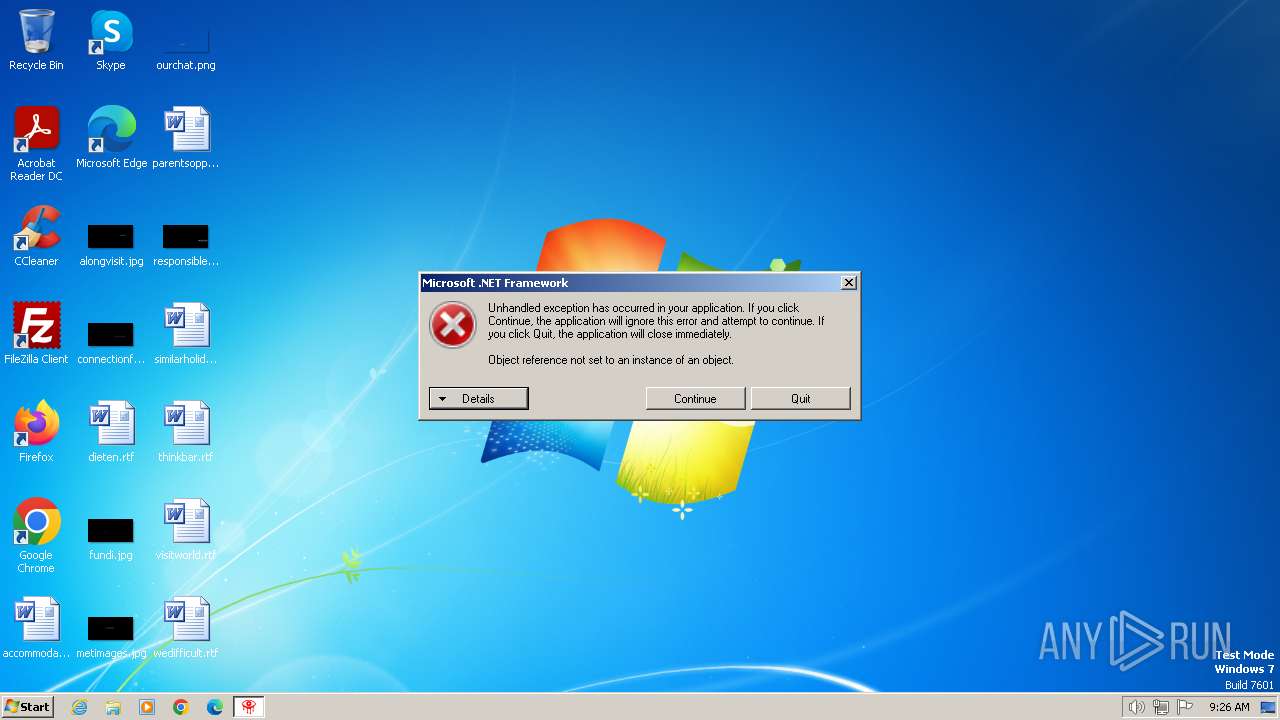
Drops the executable file immediately after the start
- RedEye.exe (PID: 2420)
Changes the autorun value in the registry
- RedEye.exe (PID: 2420)
SUSPICIOUS
Creates file in the systems drive root
- RedEye.exe (PID: 2420)
Executable content was dropped or overwritten
- RedEye.exe (PID: 2420)
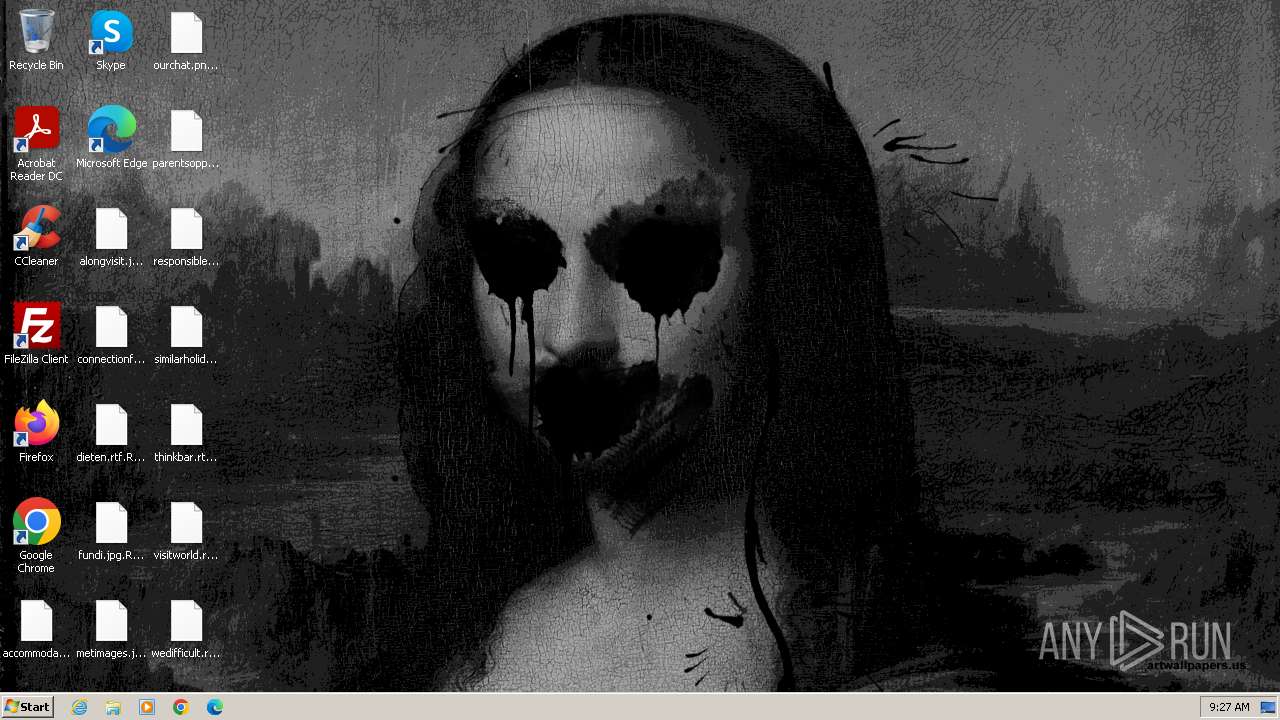
Changes the desktop background image
- RedEye.exe (PID: 2420)
Reads the Internet Settings
- RedEye.exe (PID: 2420)
- sipnotify.exe (PID: 1448)
Reads security settings of Internet Explorer
- RedEye.exe (PID: 2420)
The system shut down or reboot
- RedEye.exe (PID: 2420)
The process executes via Task Scheduler
- ctfmon.exe (PID: 1700)
- sipnotify.exe (PID: 1448)
Reads settings of System Certificates
- sipnotify.exe (PID: 1448)
INFO
Reads the machine GUID from the registry
- RedEye.exe (PID: 2420)
Reads the computer name
- RedEye.exe (PID: 2420)
- IMEKLMG.EXE (PID: 2052)
- IMEKLMG.EXE (PID: 340)
- wmpnscfg.exe (PID: 2360)
- wmpnscfg.exe (PID: 2480)
- wmpnscfg.exe (PID: 2404)
Checks supported languages
- RedEye.exe (PID: 2420)
- IMEKLMG.EXE (PID: 340)
- IMEKLMG.EXE (PID: 2052)
- wmpnscfg.exe (PID: 2360)
- wmpnscfg.exe (PID: 2404)
- wmpnscfg.exe (PID: 2480)
Manual execution by a user
- IMEKLMG.EXE (PID: 340)
- IMEKLMG.EXE (PID: 2052)
- RedEye.exe (PID: 2084)
- wmpnscfg.exe (PID: 2404)
- RedEye.exe (PID: 2072)
- wmpnscfg.exe (PID: 2360)
- wmpnscfg.exe (PID: 2480)
Process checks whether UAC notifications are on
- IMEKLMG.EXE (PID: 340)
- IMEKLMG.EXE (PID: 2052)
Reads security settings of Internet Explorer
- sipnotify.exe (PID: 1448)
Reads the software policy settings
- sipnotify.exe (PID: 1448)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:06:05 22:56:17+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 10989056 |
| InitializedDataSize: | 109568 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa7ccae |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Windows Update |
| CompanyName: | - |
| FileDescription: | Windows Update |
| FileVersion: | 1.0.0.0 |
| InternalName: | RedEye.exe |
| LegalCopyright: | Copyright © 2018 |
| LegalTrademarks: | Windows Update |
| OriginalFileName: | RedEye.exe |
| ProductName: | Windows Update |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
94
Monitored processes
12
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 340 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /JPN /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 1448 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
| 1700 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /KOR /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 2072 | "C:\Users\admin\AppData\Local\Temp\RedEye.exe" | C:\Users\admin\AppData\Local\Temp\RedEye.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Windows Update Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2084 | "C:\Users\admin\AppData\Local\Temp\RedEye.exe" | C:\Users\admin\AppData\Local\Temp\RedEye.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Windows Update Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2360 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2404 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2420 | "C:\Users\admin\AppData\Local\Temp\RedEye.exe" | C:\Users\admin\AppData\Local\Temp\RedEye.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Windows Update Exit code: 1073807364 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 525
Read events
5 478
Write events
34
Delete events
13
Modification events
| (PID) Process: | (2420) RedEye.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | WallPaper |
Value: C:\redeyebmp.bmp | |||
| (PID) Process: | (2420) RedEye.exe | Key: | HKEY_CURRENT_USER\Software\ShortCutInfection |
| Operation: | write | Name: | Mr.Wolf |
Value: True | |||
| (PID) Process: | (2420) RedEye.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Windows Update |
Value: C:\Users\admin\AppData\Local\Temp\RedEye.exe | |||
| (PID) Process: | (2420) RedEye.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Windows Update |
Value: C:\Users\admin\AppData\Local\Temp\RedEye.exe | |||
| (PID) Process: | (2420) RedEye.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2420) RedEye.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2420) RedEye.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2420) RedEye.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1700) ctfmon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | internat.exe |
Value: | |||
| (PID) Process: | (340) IMEKLMG.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\IMEJP\14.0 |
| Operation: | write | Name: | SetPreload |
Value: 1 | |||
Executable files
1
Suspicious files
0
Text files
7
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2420 | RedEye.exe | C:\redeyebmp.bmp | — | |
MD5:— | SHA256:— | |||
| 2420 | RedEye.exe | C:\windows.exe | executable | |
MD5:— | SHA256:— | |||
| 2420 | RedEye.exe | C:\autorun.inf | ini | |
MD5:— | SHA256:— | |||
| 2420 | RedEye.exe | C:\Users\admin\Documents\hostdescribed.rtf.RedEye | — | |
MD5:— | SHA256:— | |||
| 2420 | RedEye.exe | C:\Users\admin\Documents\ifcoming.rtf.RedEye | — | |
MD5:— | SHA256:— | |||
| 2420 | RedEye.exe | C:\Users\admin\Documents\setgreater.rtf.RedEye | — | |
MD5:— | SHA256:— | |||
| 2420 | RedEye.exe | C:\Users\admin\Documents\sourcesamateur.rtf.RedEye | — | |
MD5:— | SHA256:— | |||
| 2420 | RedEye.exe | C:\Users\admin\Documents\toysmight.rtf.RedEye | — | |
MD5:— | SHA256:— | |||
| 2420 | RedEye.exe | C:\Users\admin\Pictures\createdfact.png.RedEye | — | |
MD5:— | SHA256:— | |||
| 2420 | RedEye.exe | C:\Users\admin\Pictures\organizationscale.jpg.RedEye | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
8
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1448 | sipnotify.exe | HEAD | 200 | 104.102.39.173:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133573012346710000 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1100 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1448 | sipnotify.exe | 104.102.39.173:80 | query.prod.cms.rt.microsoft.com | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
query.prod.cms.rt.microsoft.com |
| whitelisted |