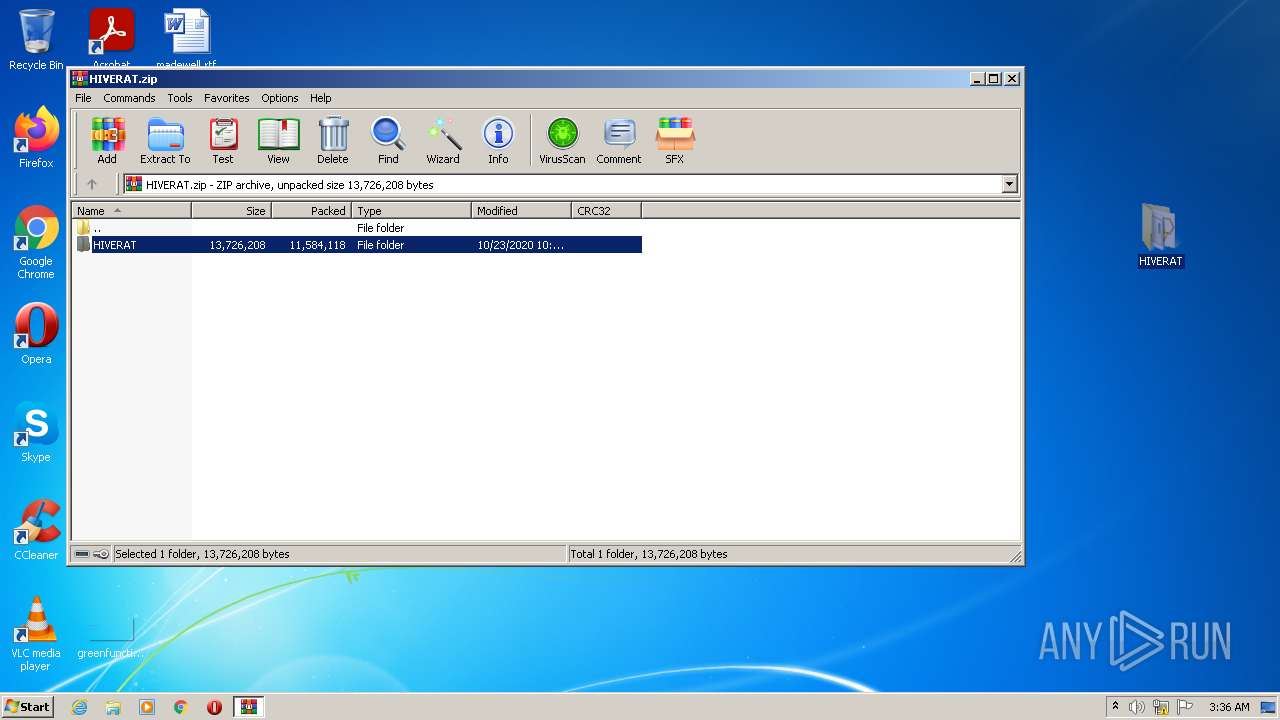
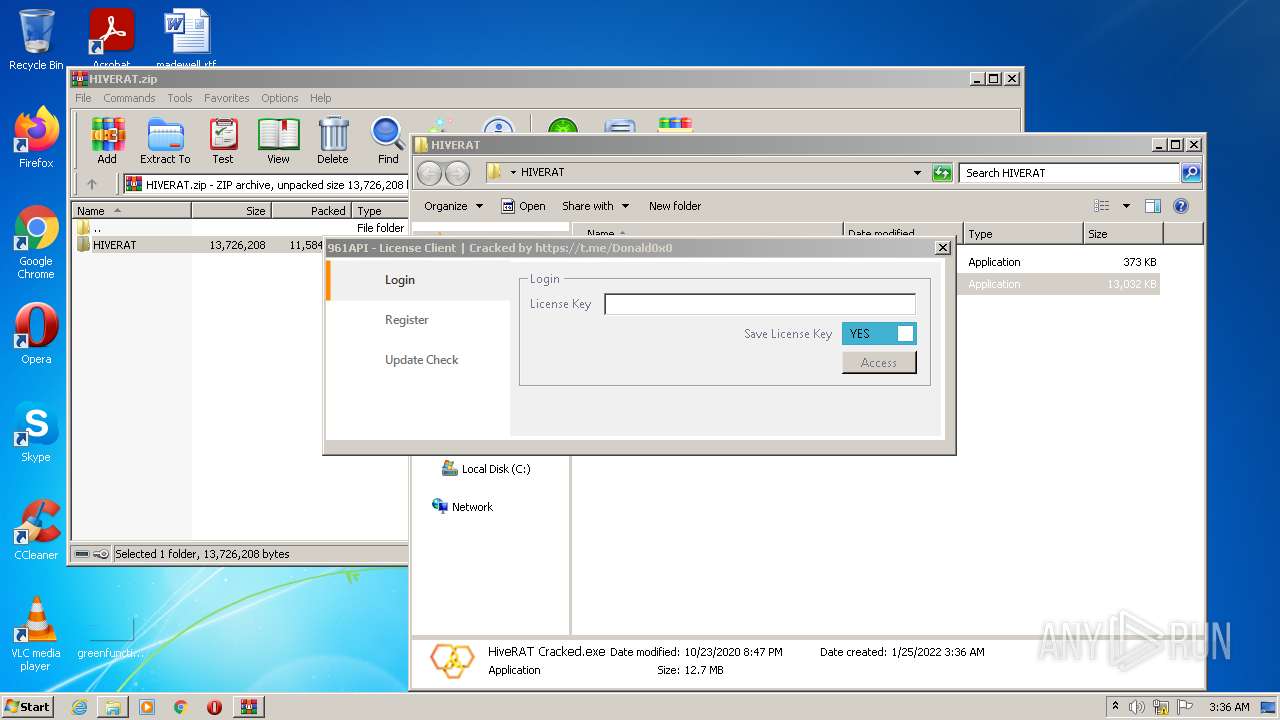
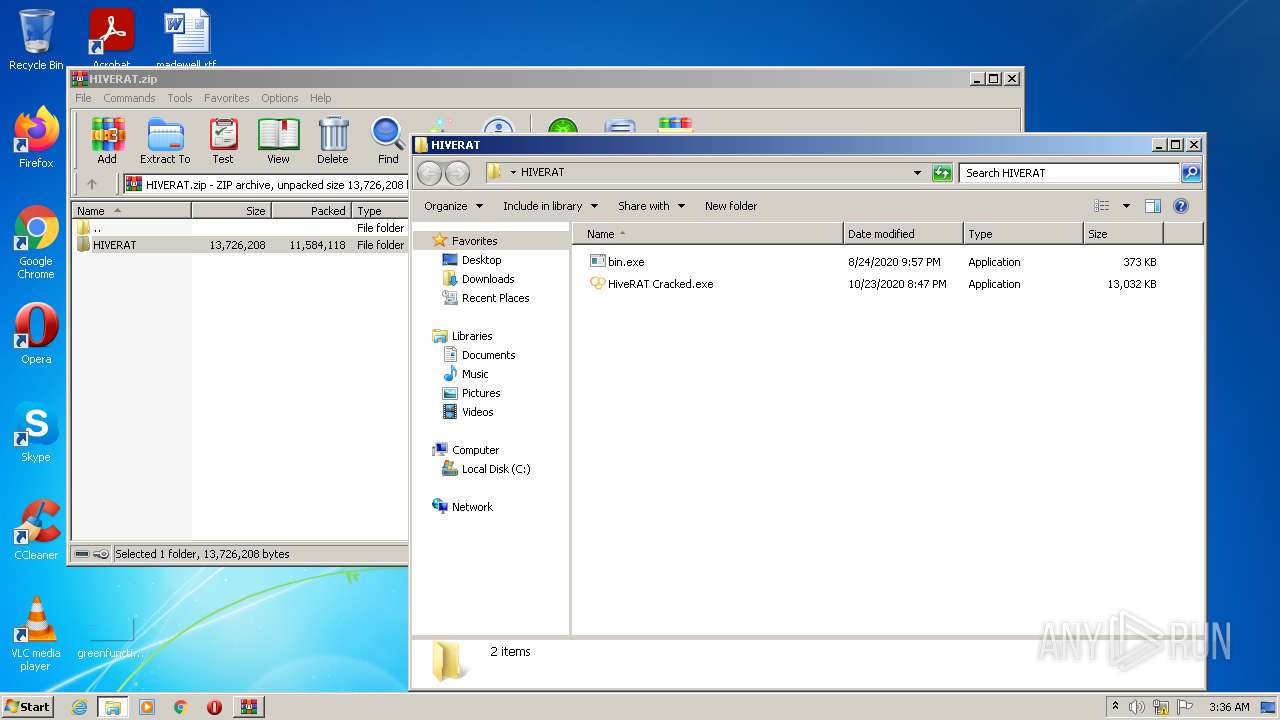
| File name: | HIVERAT.zip |
| Full analysis: | https://app.any.run/tasks/1c005db8-baca-465f-8713-16e2b6dd8c72 |
| Verdict: | Malicious activity |
| Analysis date: | January 25, 2022, 03:35:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | BCB9B2D8BB954E760C21FA69A36392AF |
| SHA1: | 783F1940F3E74343867F73C0CB95EB7F631A8E56 |
| SHA256: | 9AC083A901D2EDEEB7EFE08957946B771E06D34527021D6457F13D793884A9D7 |
| SSDEEP: | 196608:I36IF7334ptz4nmBSJn8kZEpklv3YPNelQNd3ZTeXj6X0WOLfL8nQX5mABks4xFp:IX7gtzCmBS10pioEIpTezrWE4QJmEbje |
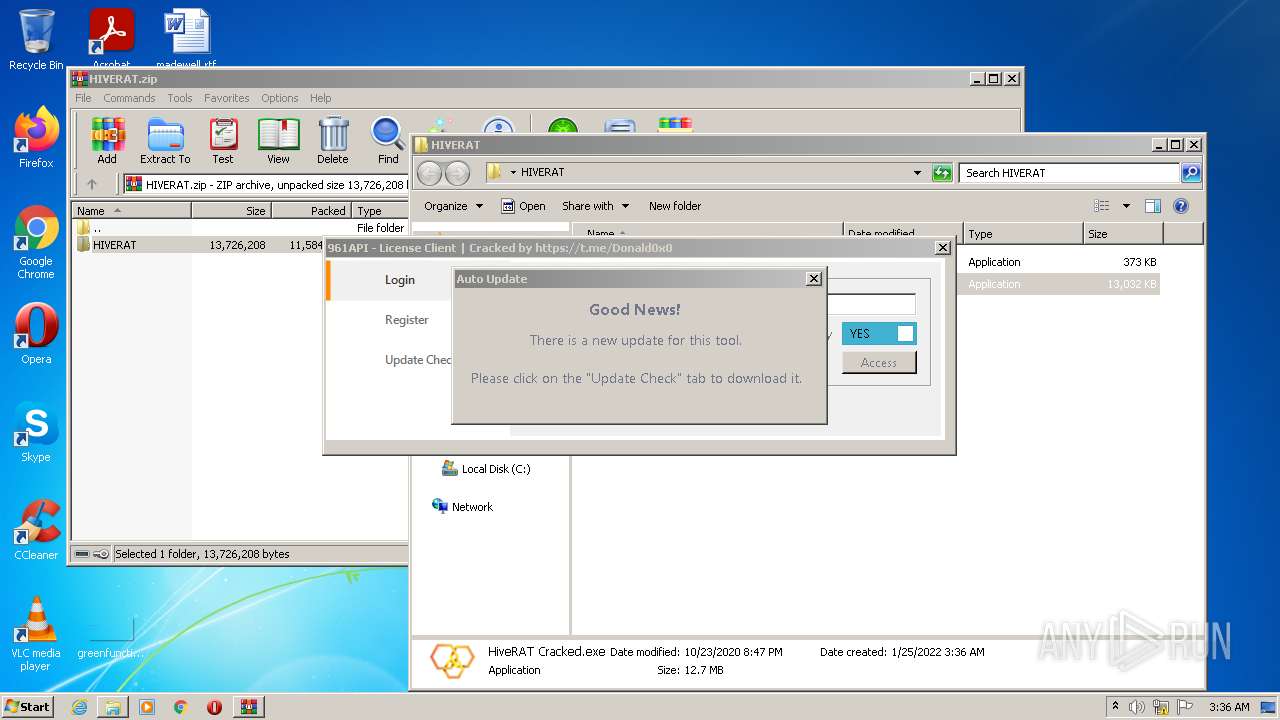
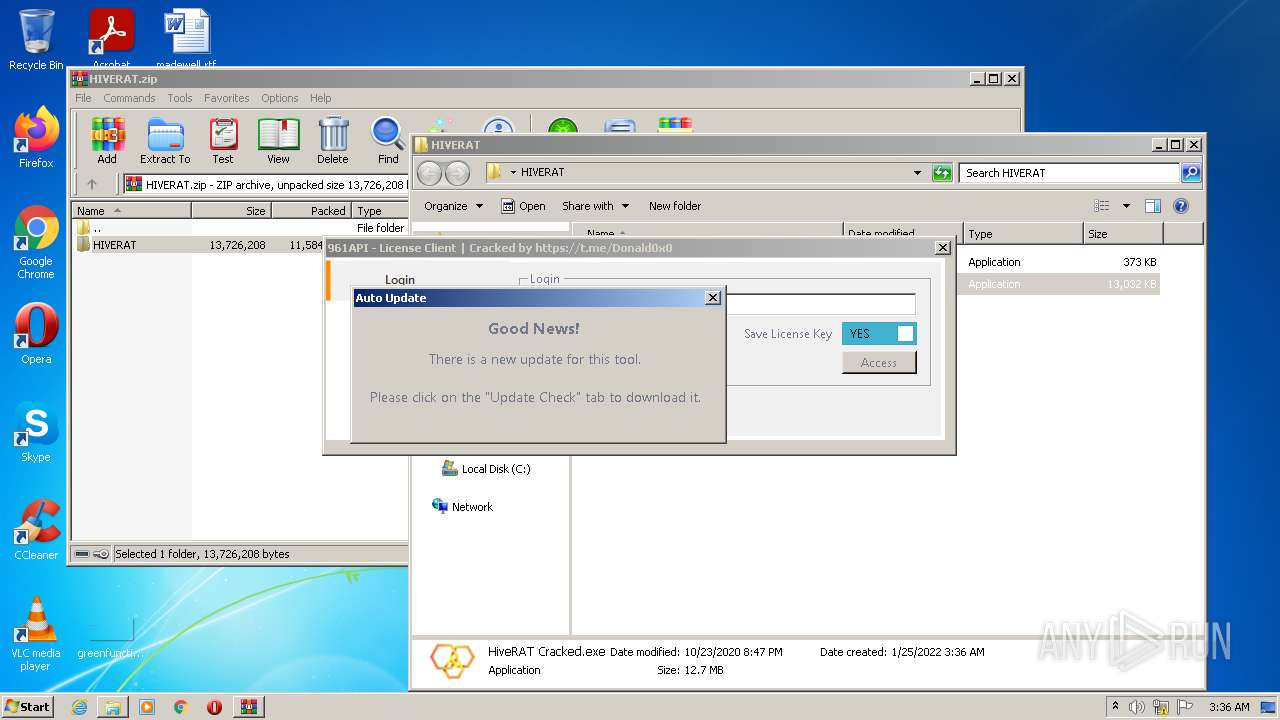
MALICIOUS
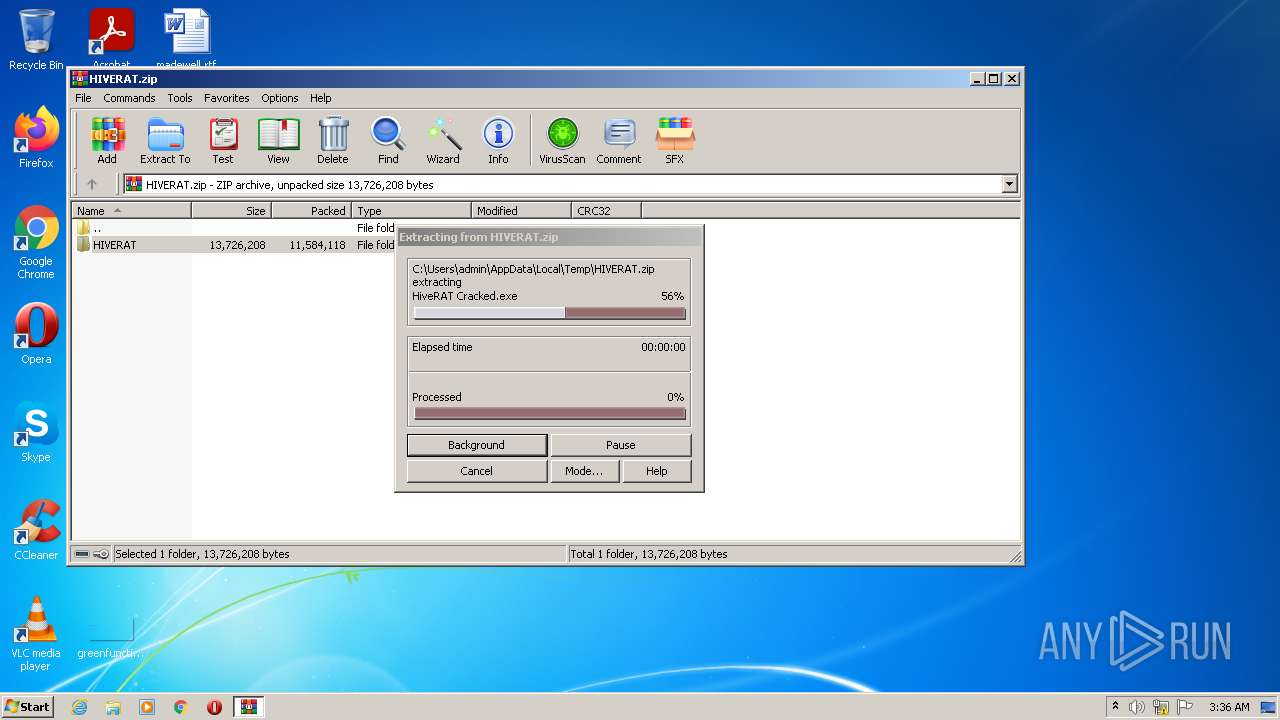
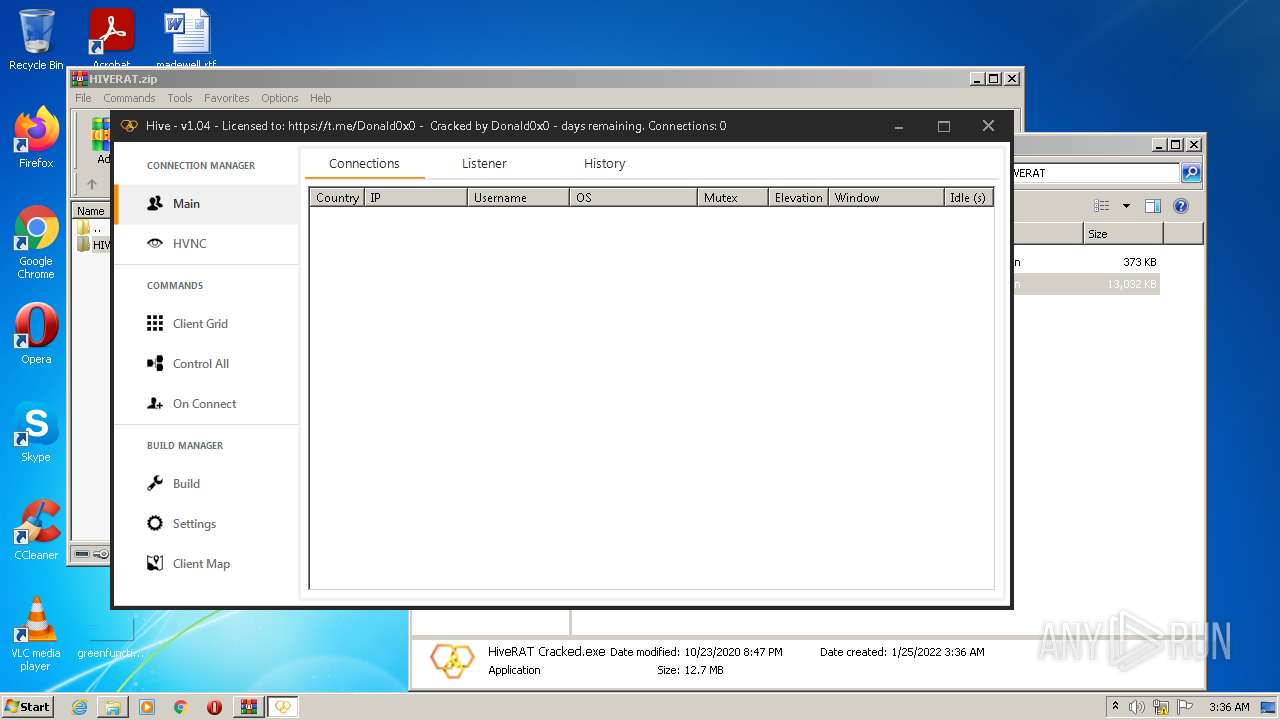
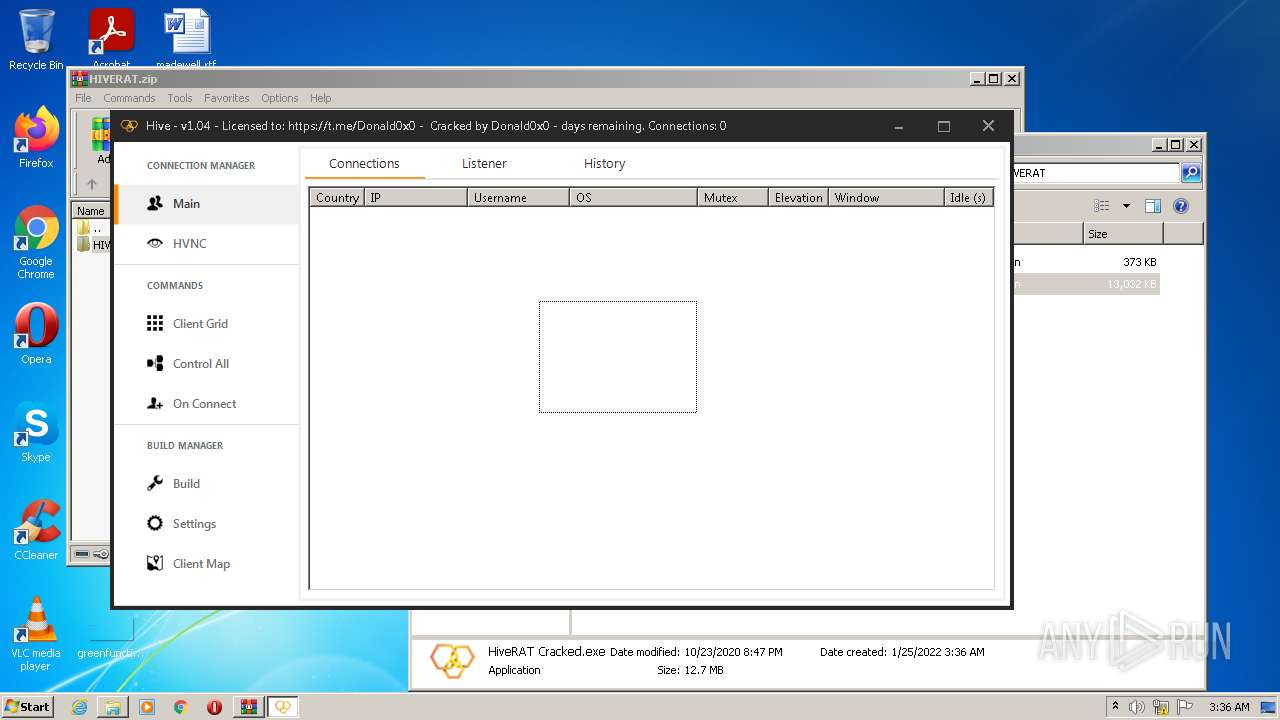
Application was dropped or rewritten from another process
- HiveRAT Cracked.exe (PID: 1296)
- bin.exe (PID: 4080)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 3644)
- bin.exe (PID: 4080)
- HiveRAT Cracked.exe (PID: 1296)
Reads the computer name
- WinRAR.exe (PID: 3644)
- HiveRAT Cracked.exe (PID: 1296)
- bin.exe (PID: 4080)
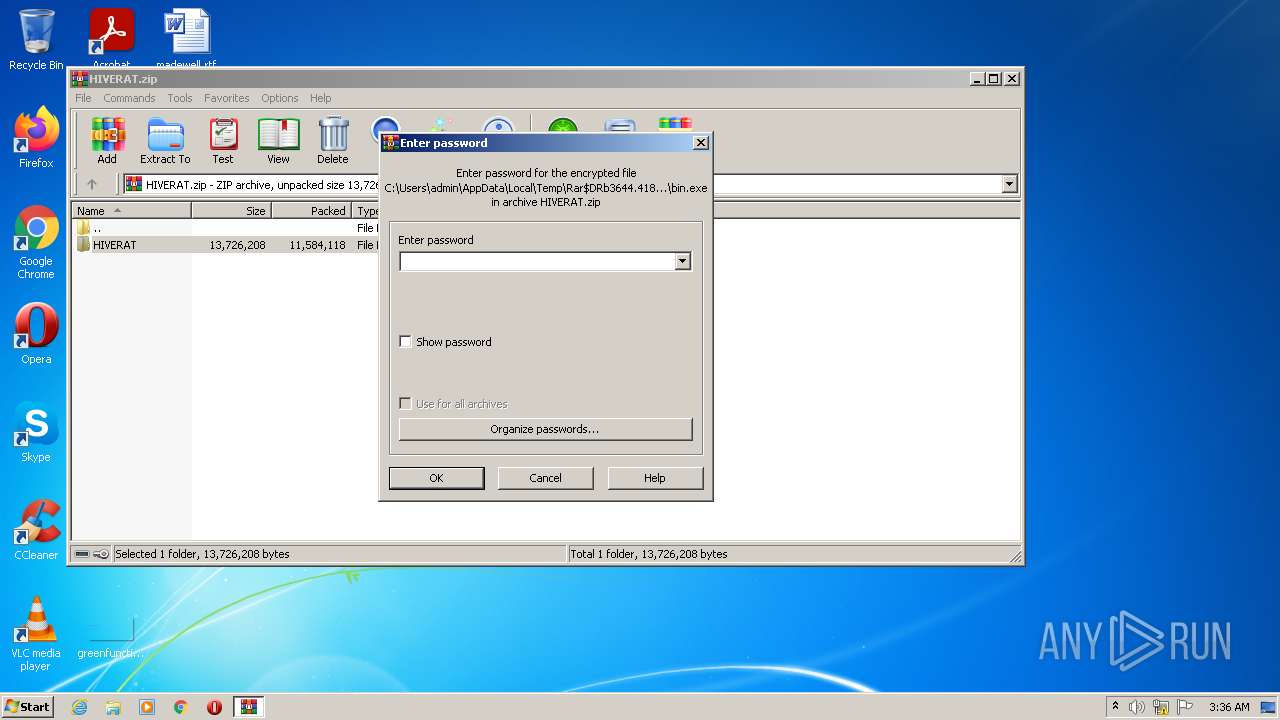
Drops a file with a compile date too recent
- WinRAR.exe (PID: 3644)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3644)
Reads Environment values
- HiveRAT Cracked.exe (PID: 1296)
INFO
Manual execution by user
- HiveRAT Cracked.exe (PID: 1296)
- bin.exe (PID: 4080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
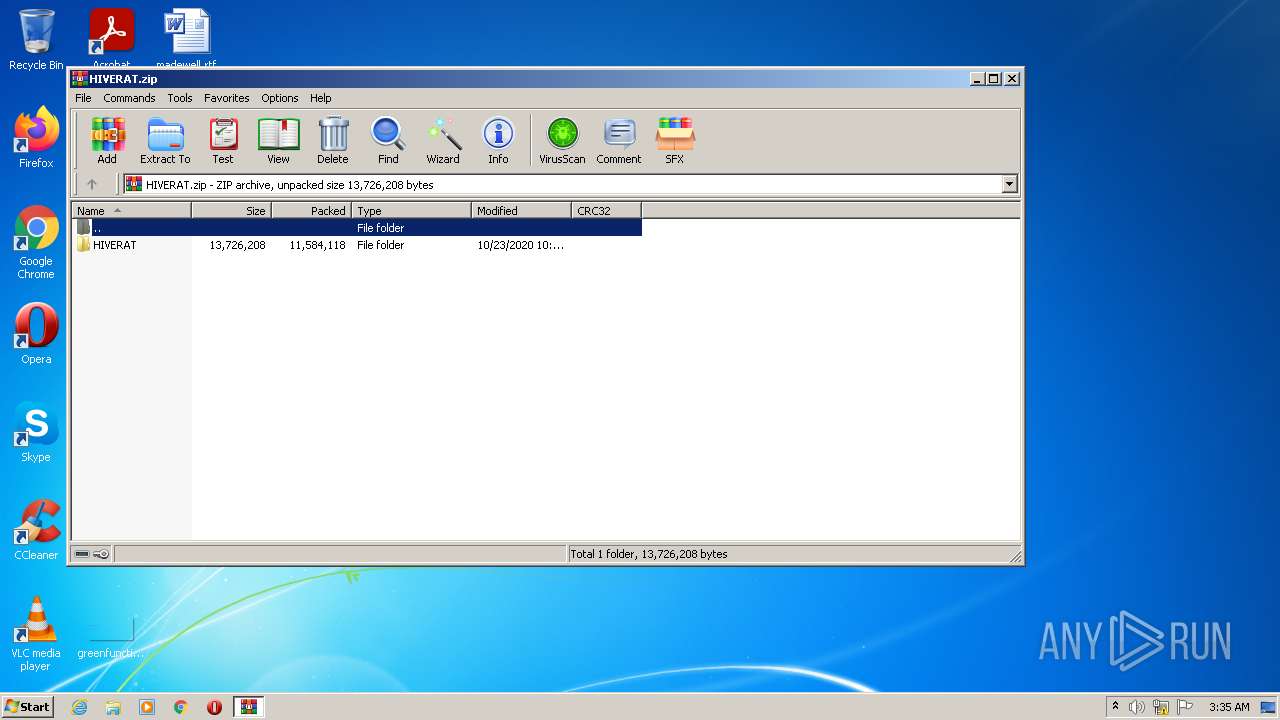
ZIP
| ZipFileName: | HIVERAT/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | - |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2020:10:23 23:40:09 |
| ZipCompression: | None |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 10 |
Total processes
38
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1296 | "C:\Users\admin\Desktop\HIVERAT\HiveRAT Cracked.exe" | C:\Users\admin\Desktop\HIVERAT\HiveRAT Cracked.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: Hive Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3644 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\HIVERAT.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 4080 | "C:\Users\admin\Desktop\HIVERAT\bin.exe" | C:\Users\admin\Desktop\HIVERAT\bin.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.4.4.0 Modules
| |||||||||||||||
Total events
1 561
Read events
1 539
Write events
22
Delete events
0
Modification events
| (PID) Process: | (3644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3644) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\HIVERAT.zip | |||
| (PID) Process: | (3644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3644) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
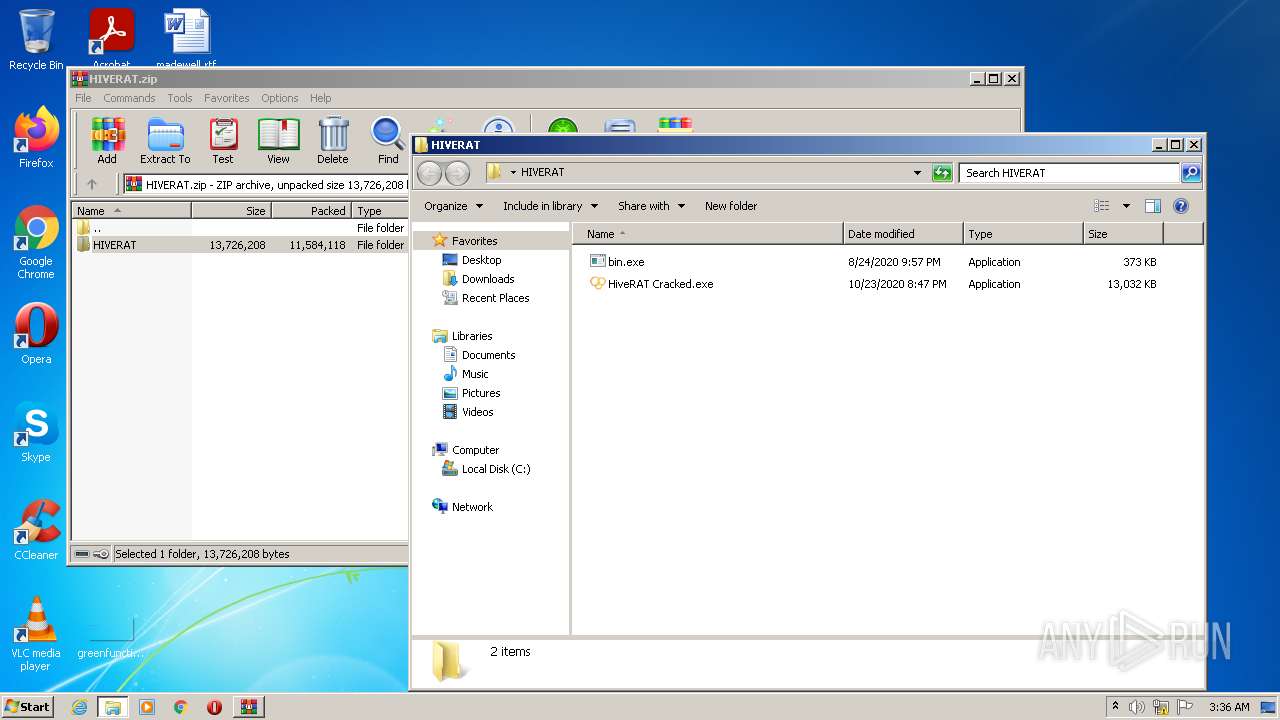
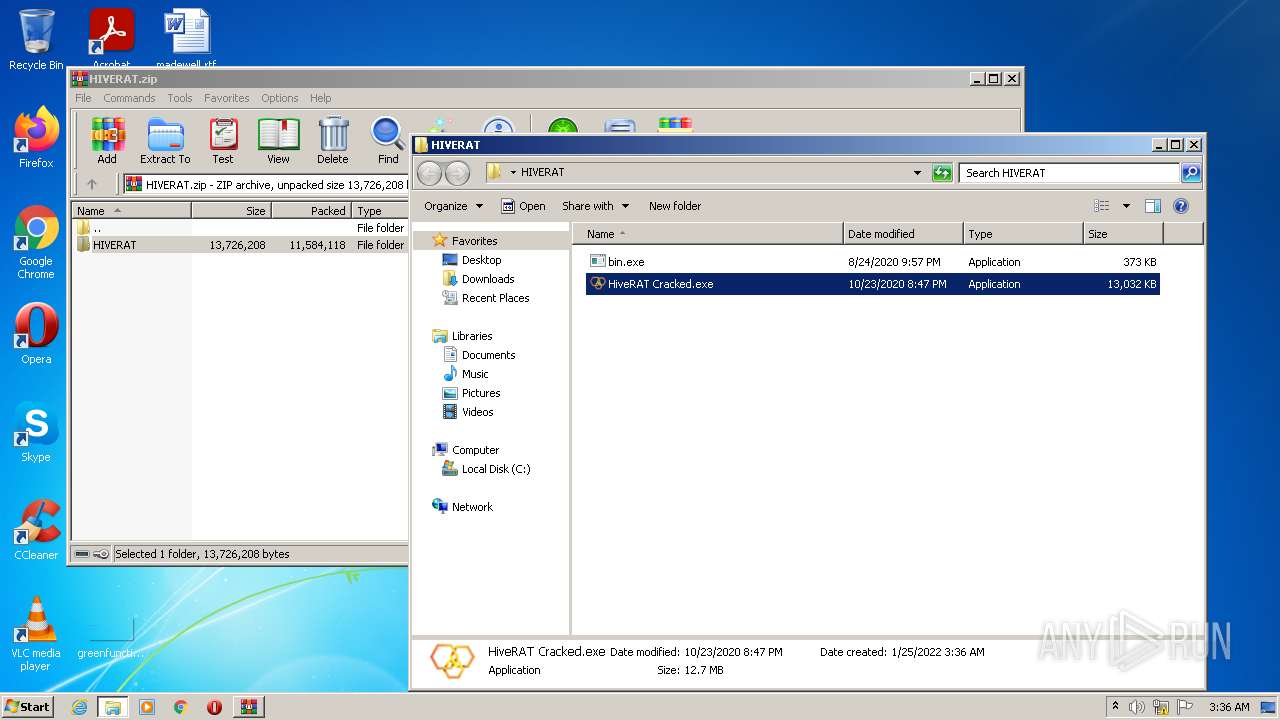
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3644 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3644.41829\HIVERAT\HiveRAT Cracked.exe | executable | |
MD5:BD6F5B20F969EFC6E3214407BB434067 | SHA256:EF6C4CF2C8F9E911D34220D59B0D89E4775397E8CA8EDF8DA82E879DFE8CBA62 | |||
| 3644 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3644.41829\HIVERAT\bin.exe | executable | |
MD5:D9E247DF13E357C75A900EB0EEE162B0 | SHA256:7FE99EF31EEA4B782B70873523F7735757B51E6ED9E1841364066764883786CB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report