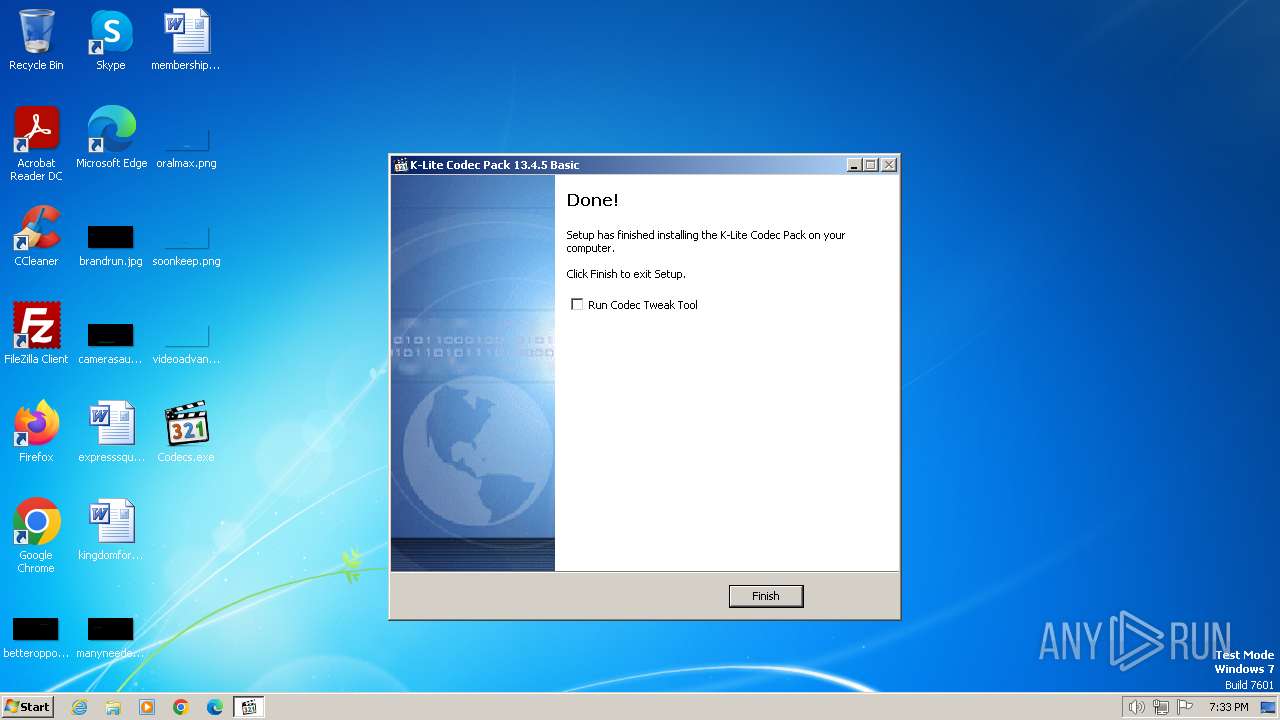
| File name: | Codecs.exe |
| Full analysis: | https://app.any.run/tasks/fa3141bd-6307-4176-b178-e194bf279cd1 |
| Verdict: | Malicious activity |
| Analysis date: | January 21, 2024, 19:32:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2432A0C854CD19453979E5F795C52A9D |
| SHA1: | 6DBE6F6A6BE246B068D76C796644D7EEE13BB604 |
| SHA256: | 9ABBCF17343D17D26757D27B05D4FEA8D7267BFC1357678363D6055B04001A01 |
| SSDEEP: | 98304:MgKj8v/Pbx2BFd/HvLP568yW3yB9vjYLsicgnz6BB4tbakgJbQ4eaktAM8BbvpI6:+n47nNn2sZ2AWqqU/oYJNLstp |
MALICIOUS
Drops the executable file immediately after the start
- Codecs.exe (PID: 2044)
- Codecs.exe (PID: 784)
- Codecs.tmp (PID: 1044)
Registers / Runs the DLL via REGSVR32.EXE
- Codecs.tmp (PID: 1044)
SUSPICIOUS
Executable content was dropped or overwritten
- Codecs.exe (PID: 784)
- Codecs.exe (PID: 2044)
- Codecs.tmp (PID: 1044)
Reads the Windows owner or organization settings
- Codecs.tmp (PID: 1044)
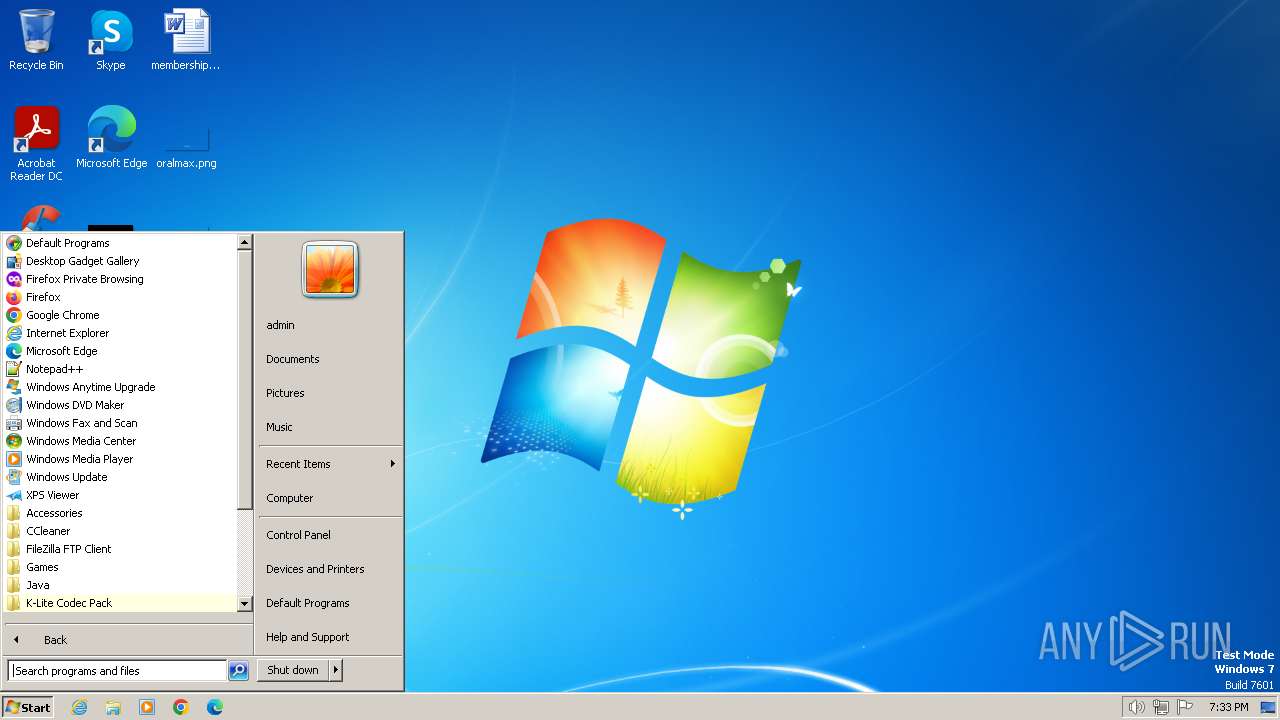
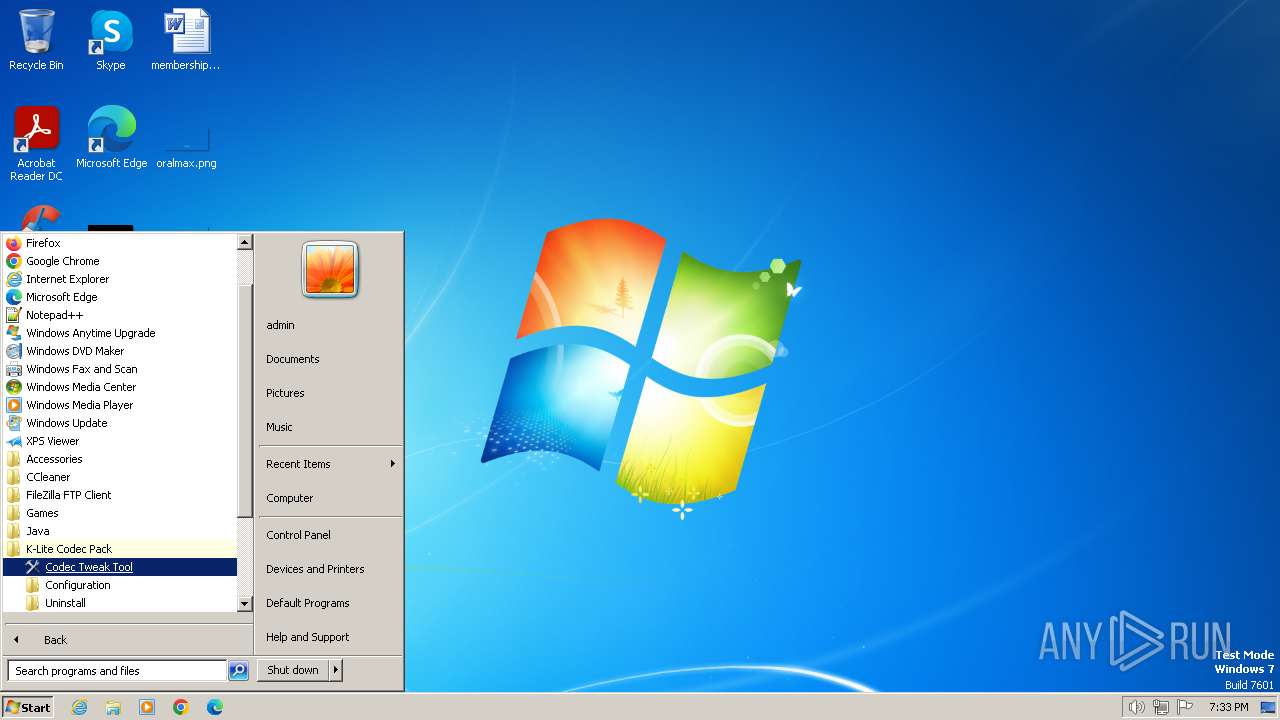
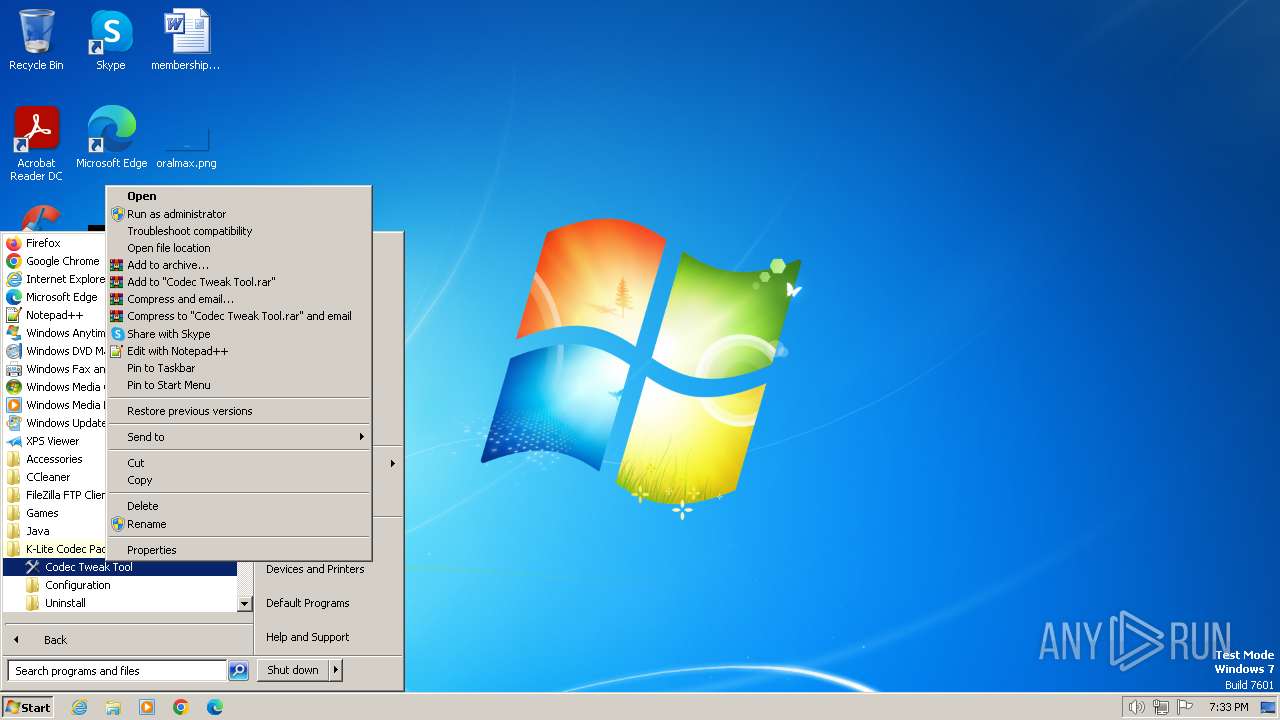
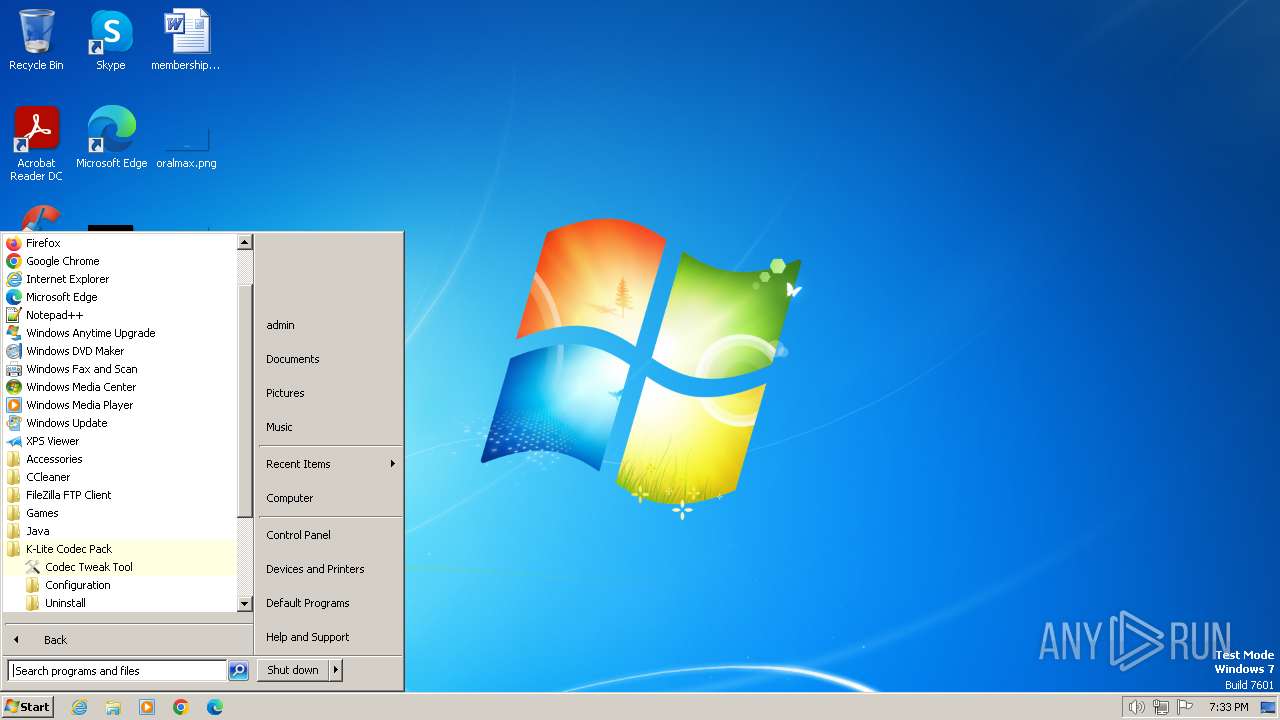
Searches for installed software
- Codecs.tmp (PID: 1044)
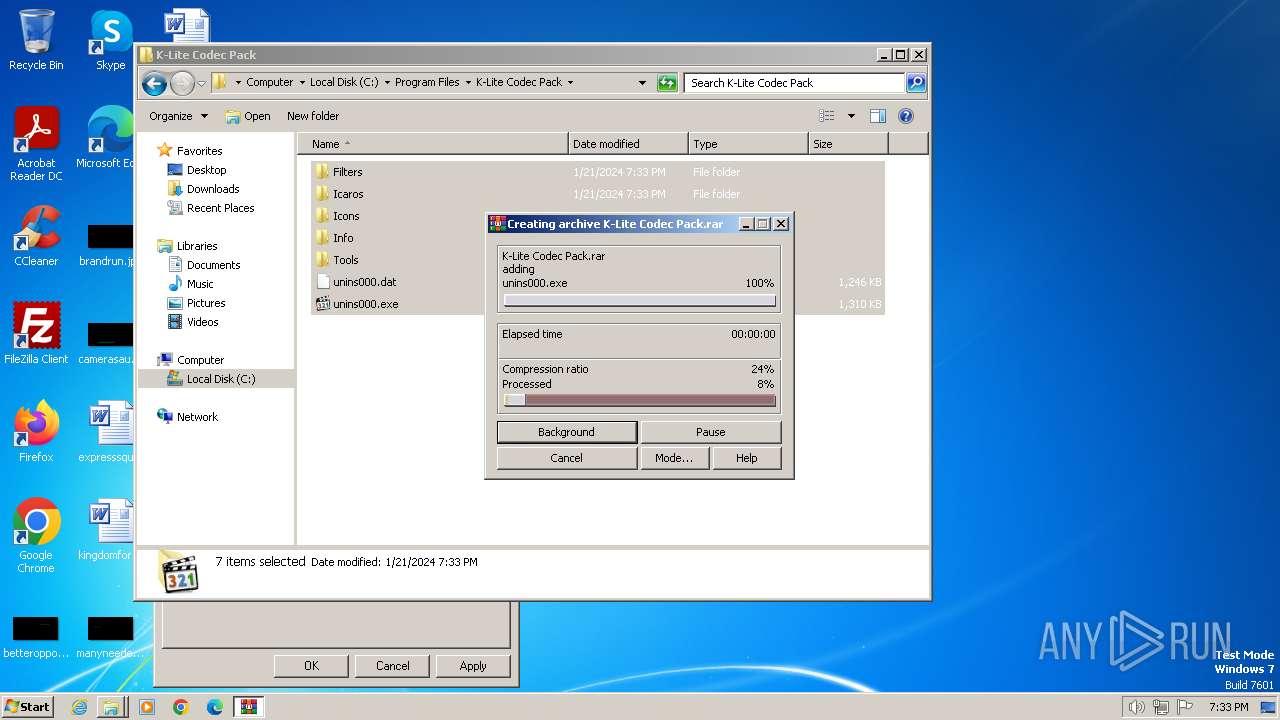
Application launched itself
- WinRAR.exe (PID: 2324)
INFO
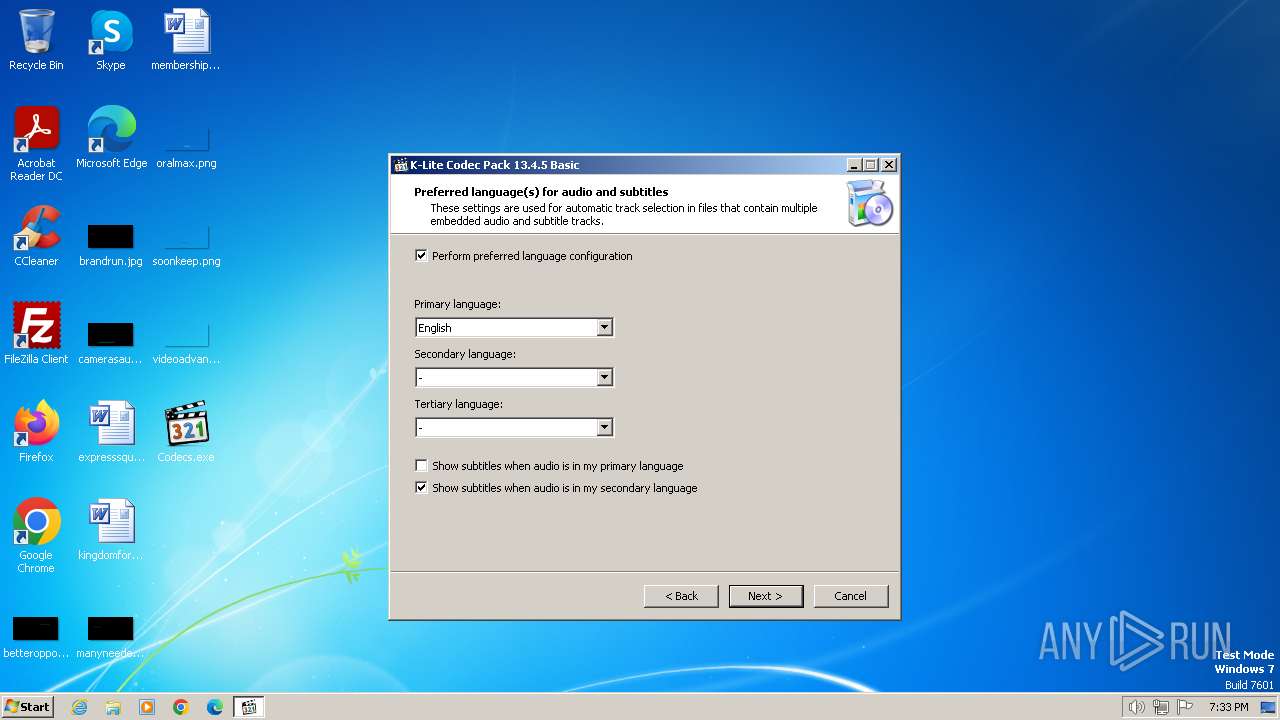
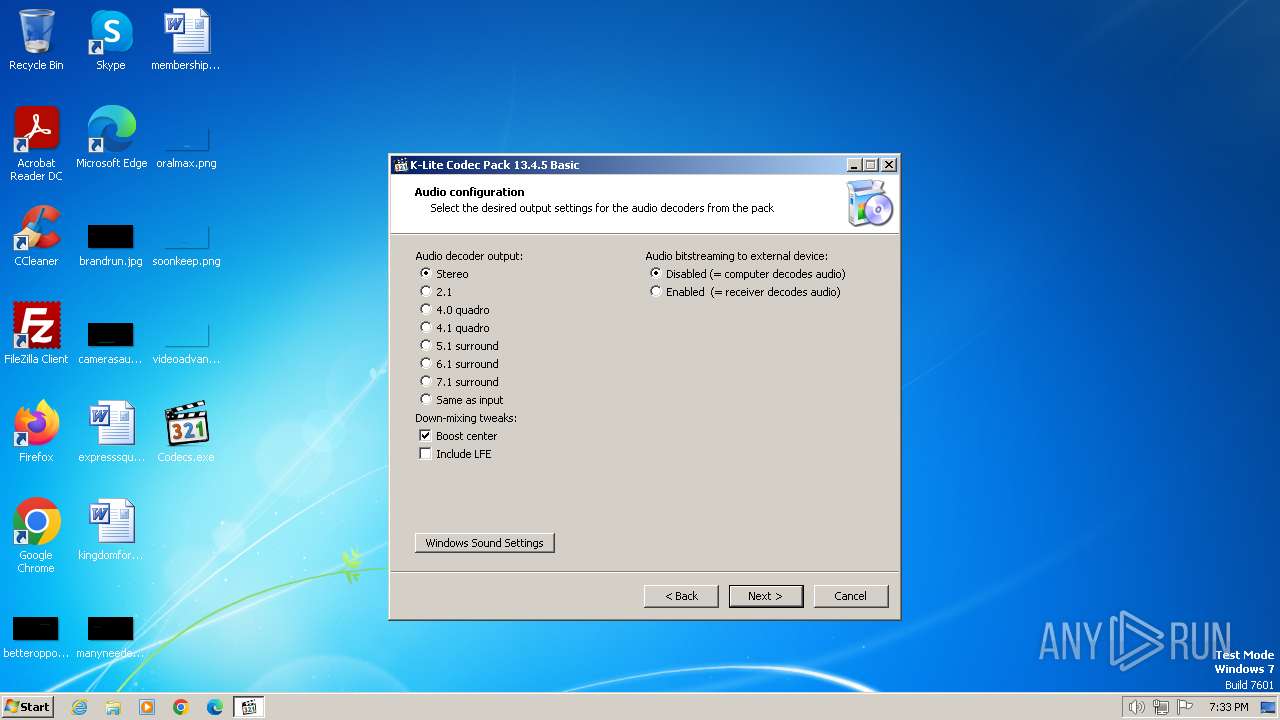
Checks supported languages
- Codecs.tmp (PID: 2036)
- Codecs.exe (PID: 784)
- Codecs.exe (PID: 2044)
- Codecs.tmp (PID: 1044)
- setacl_x86.exe (PID: 2300)
- setacl_x86.exe (PID: 2244)
- wmpnscfg.exe (PID: 3372)
Reads the computer name
- Codecs.tmp (PID: 2036)
- Codecs.tmp (PID: 1044)
- setacl_x86.exe (PID: 2300)
- setacl_x86.exe (PID: 2244)
- wmpnscfg.exe (PID: 3372)
Create files in a temporary directory
- Codecs.exe (PID: 784)
- Codecs.exe (PID: 2044)
- Codecs.tmp (PID: 1044)
Reads CPU info
- Codecs.tmp (PID: 1044)
Process checks computer location settings
- Codecs.tmp (PID: 1044)
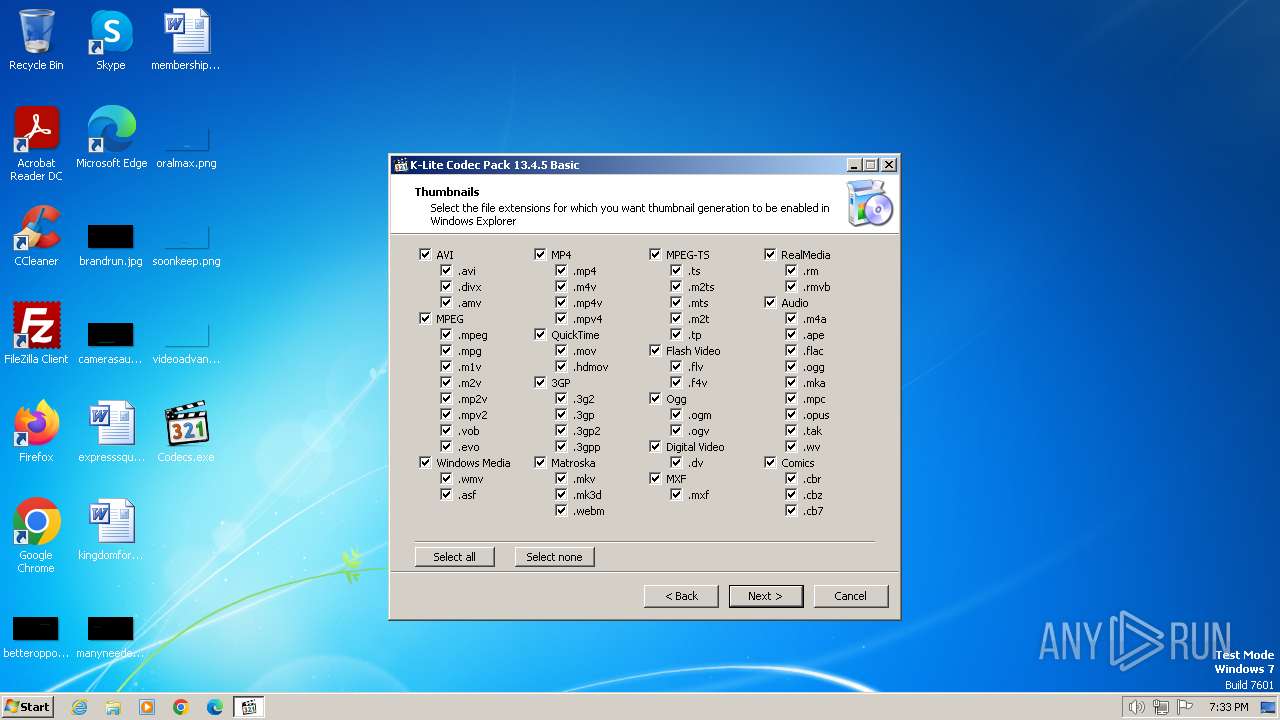
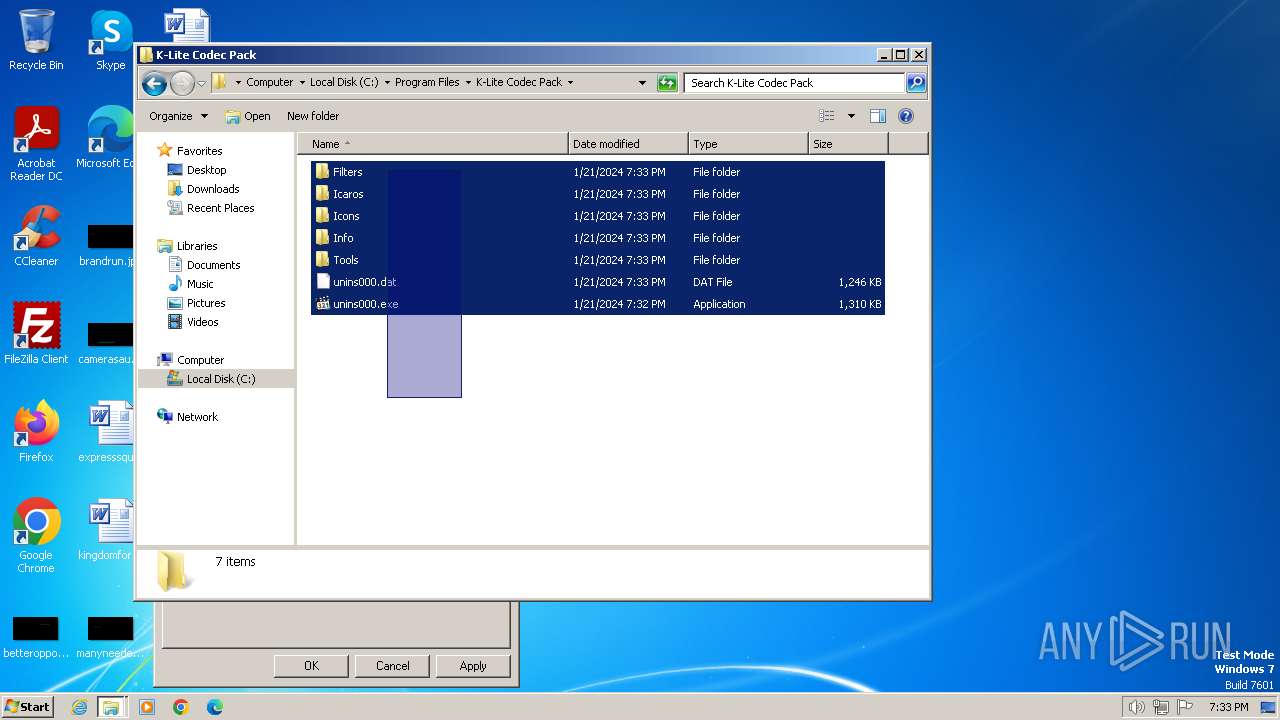
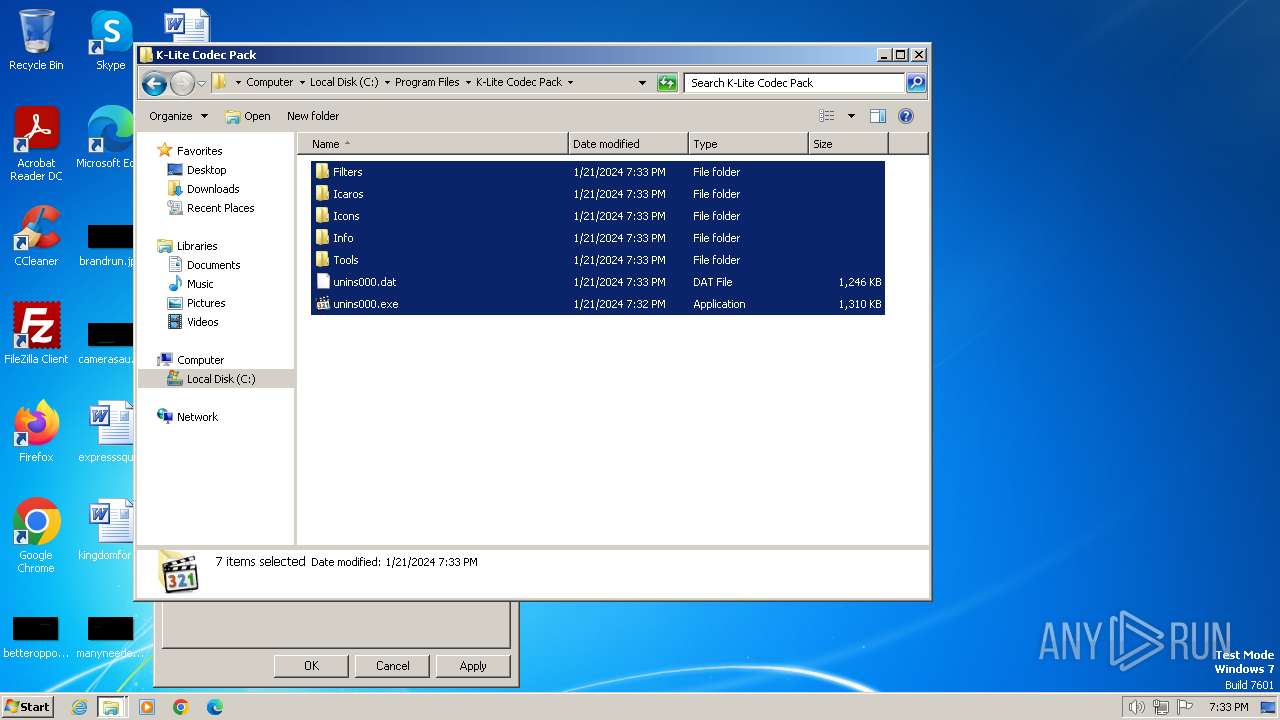
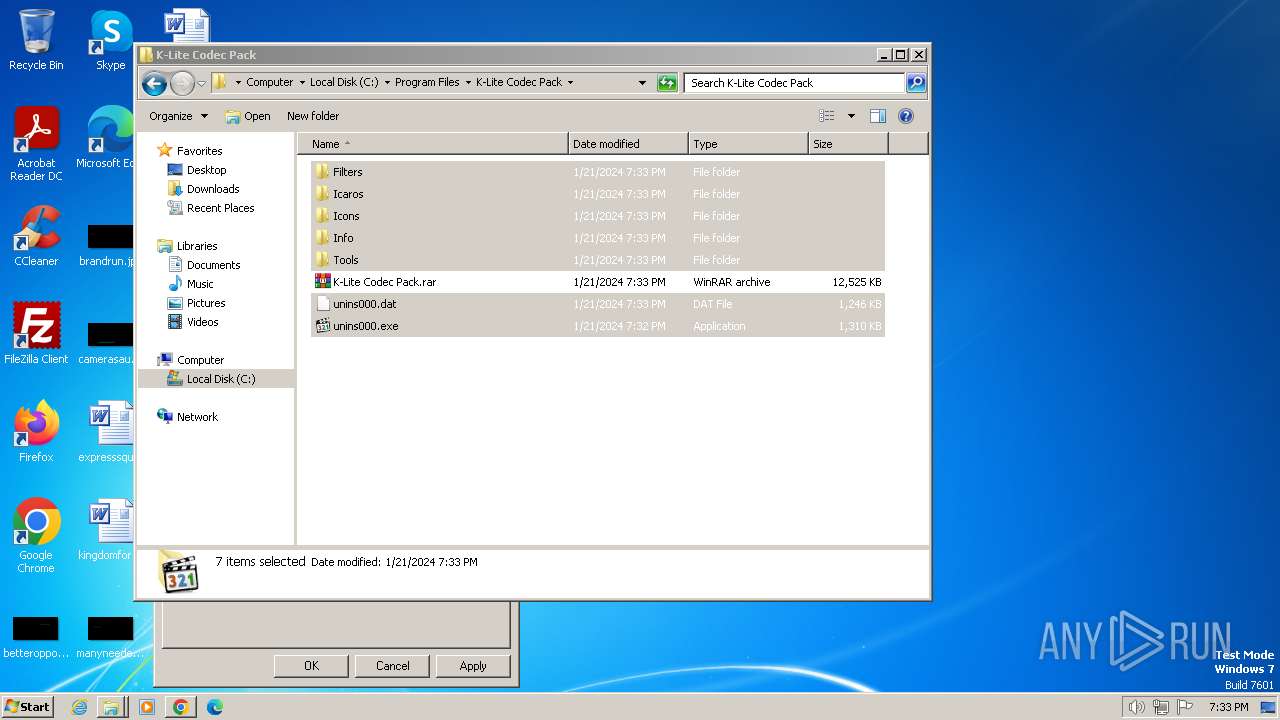
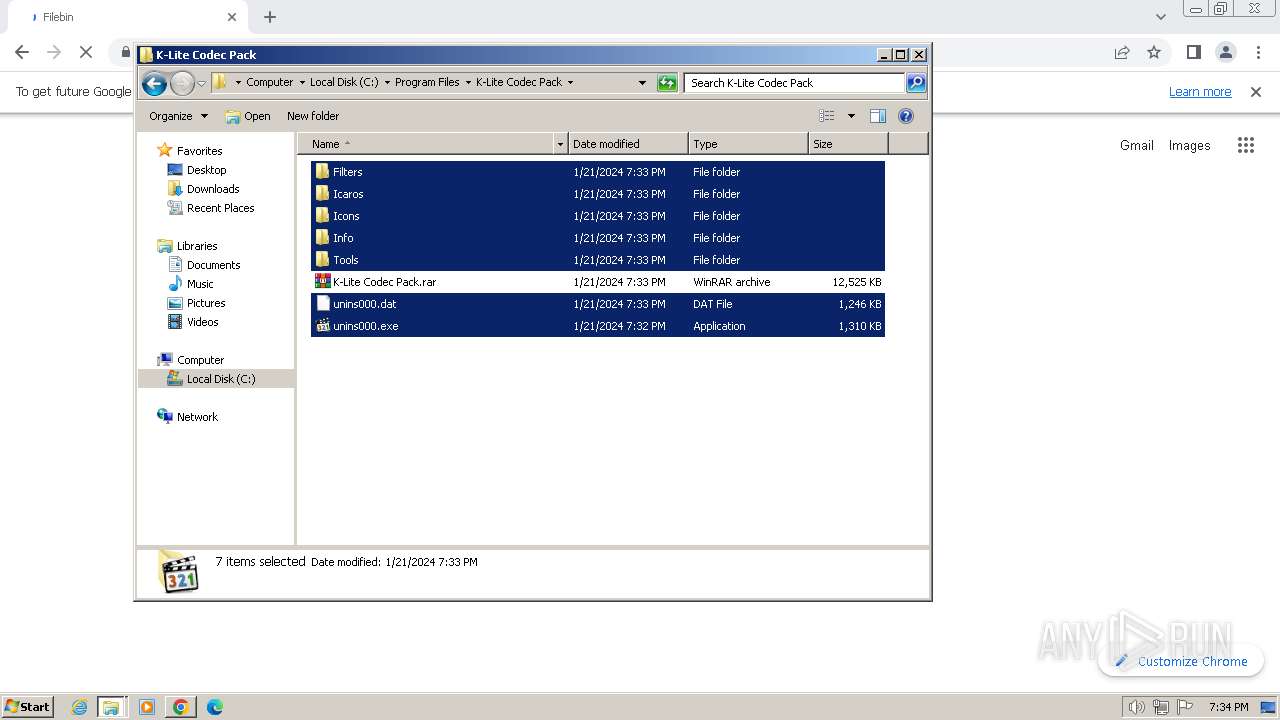
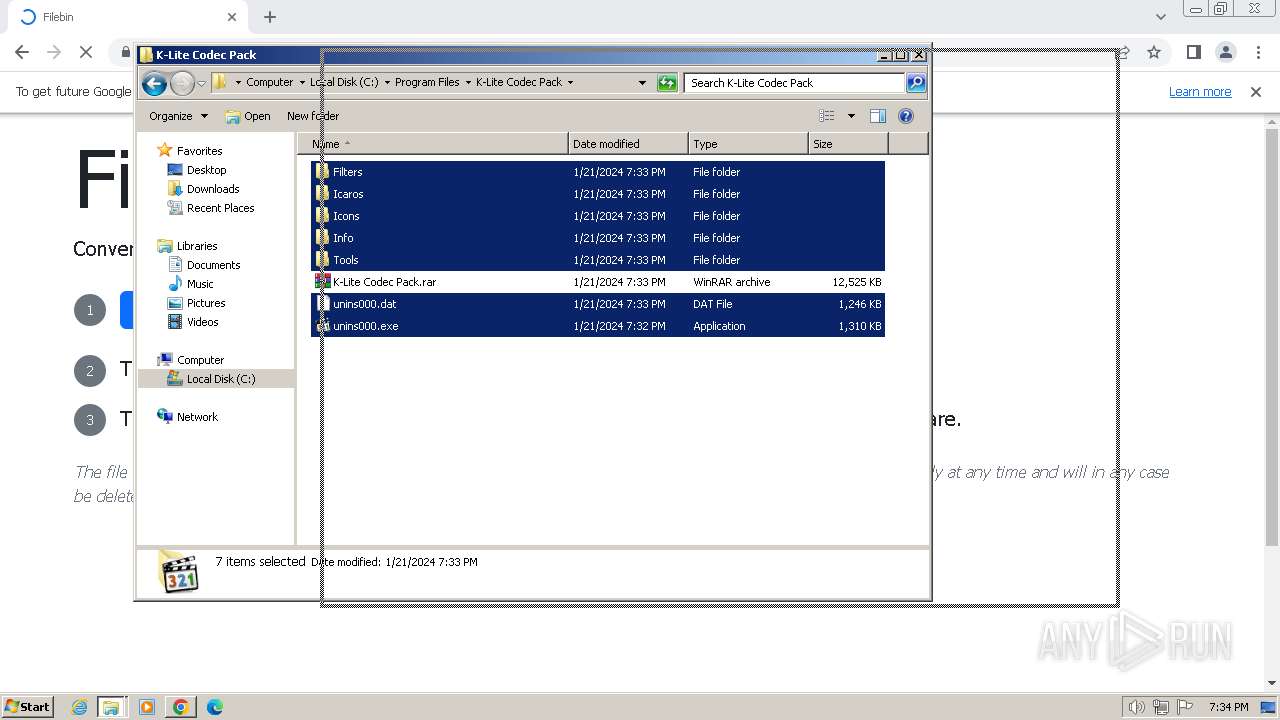
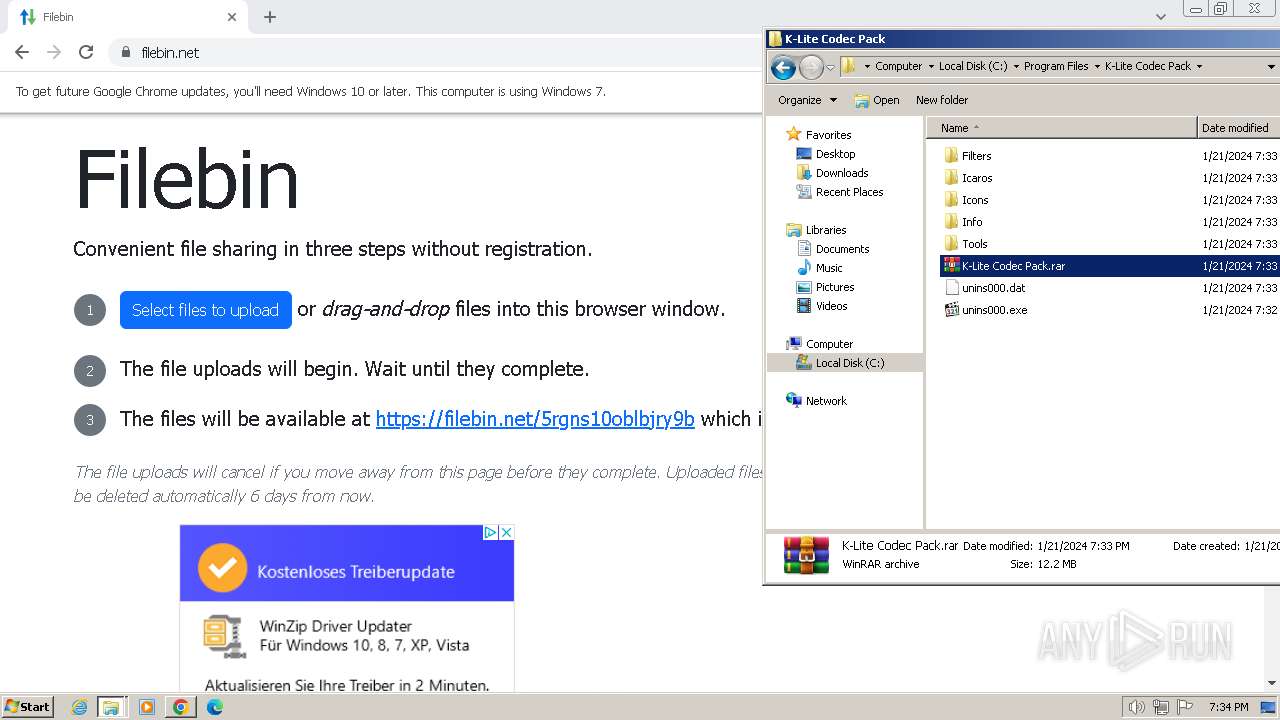
Creates files in the program directory
- Codecs.tmp (PID: 1044)
- regsvr32.exe (PID: 1544)
- WinRAR.exe (PID: 1992)
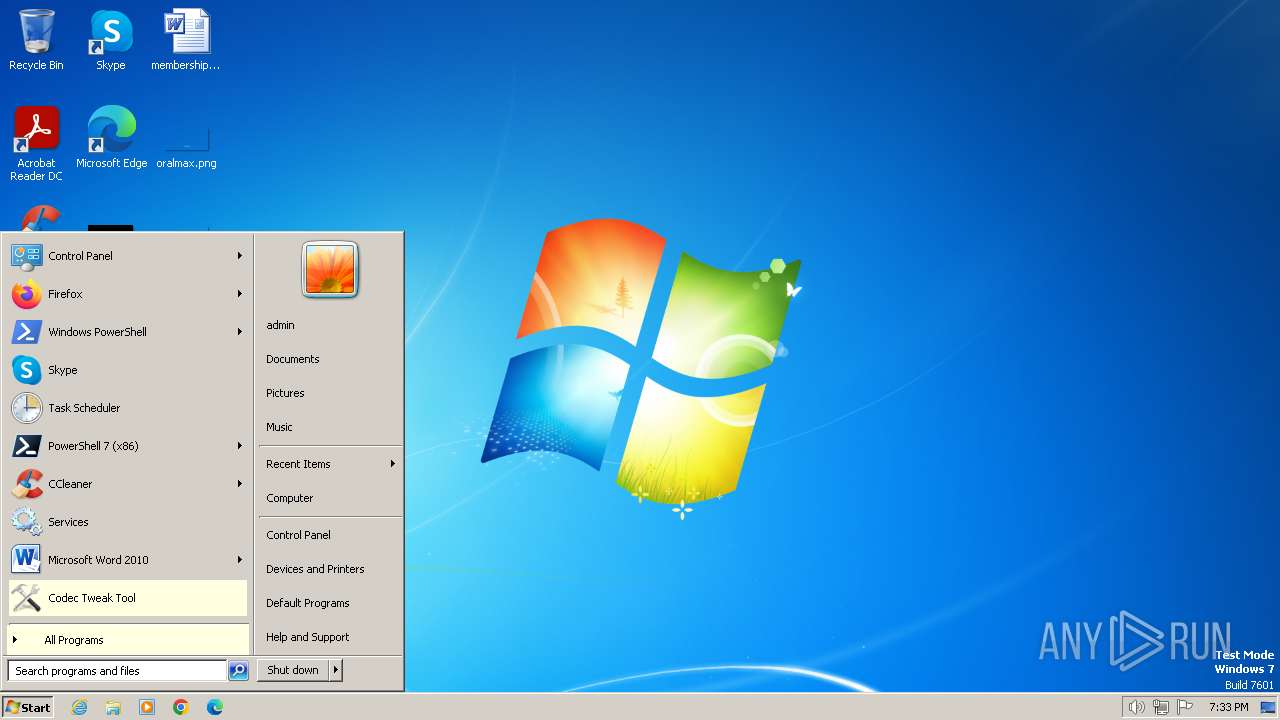
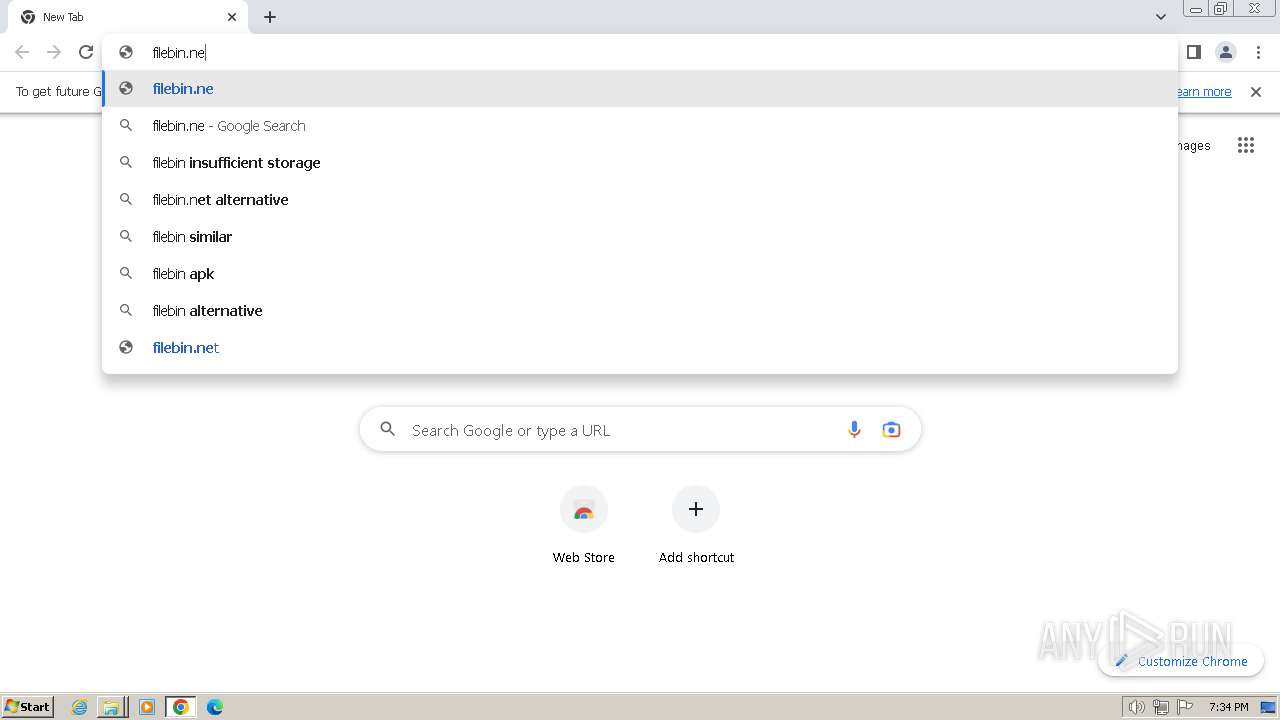
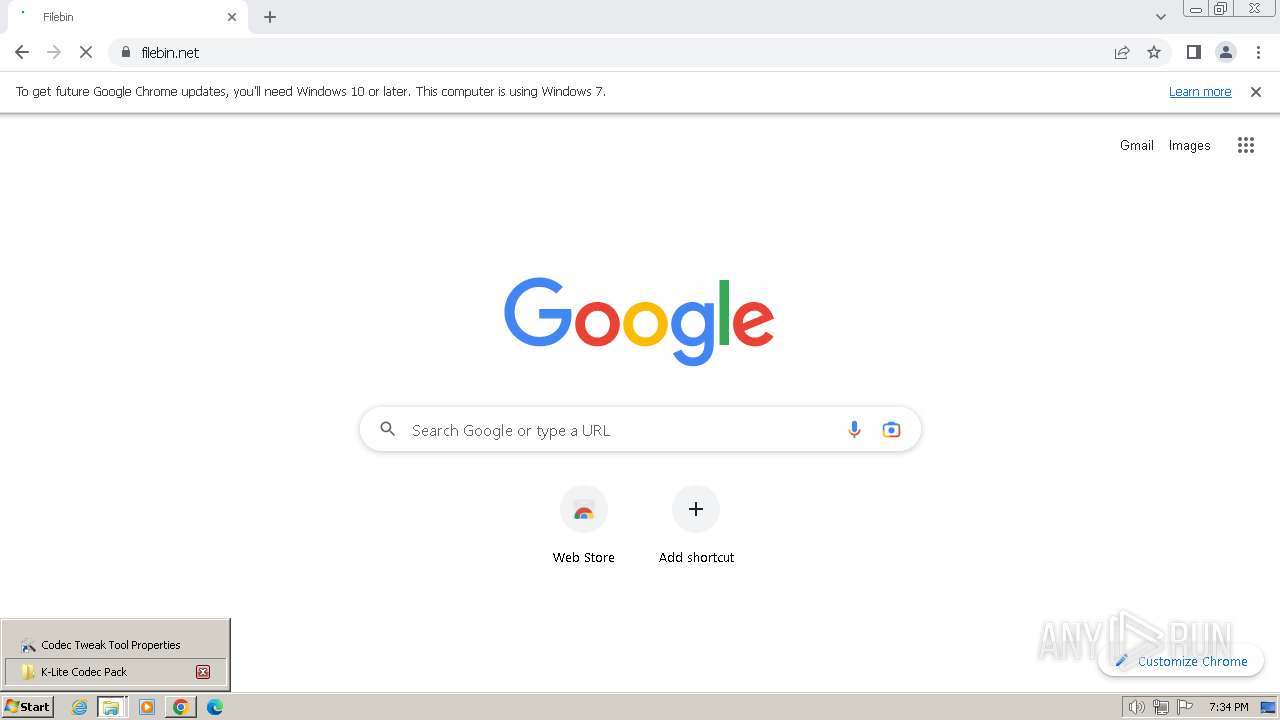
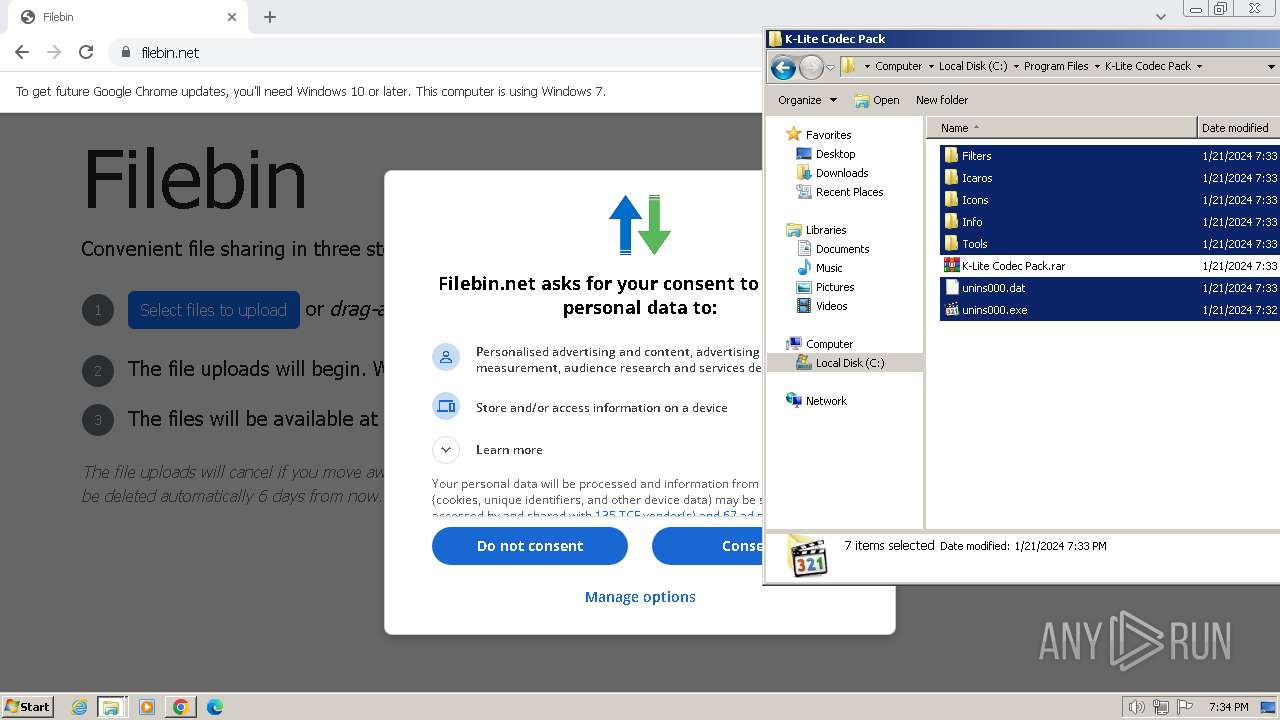
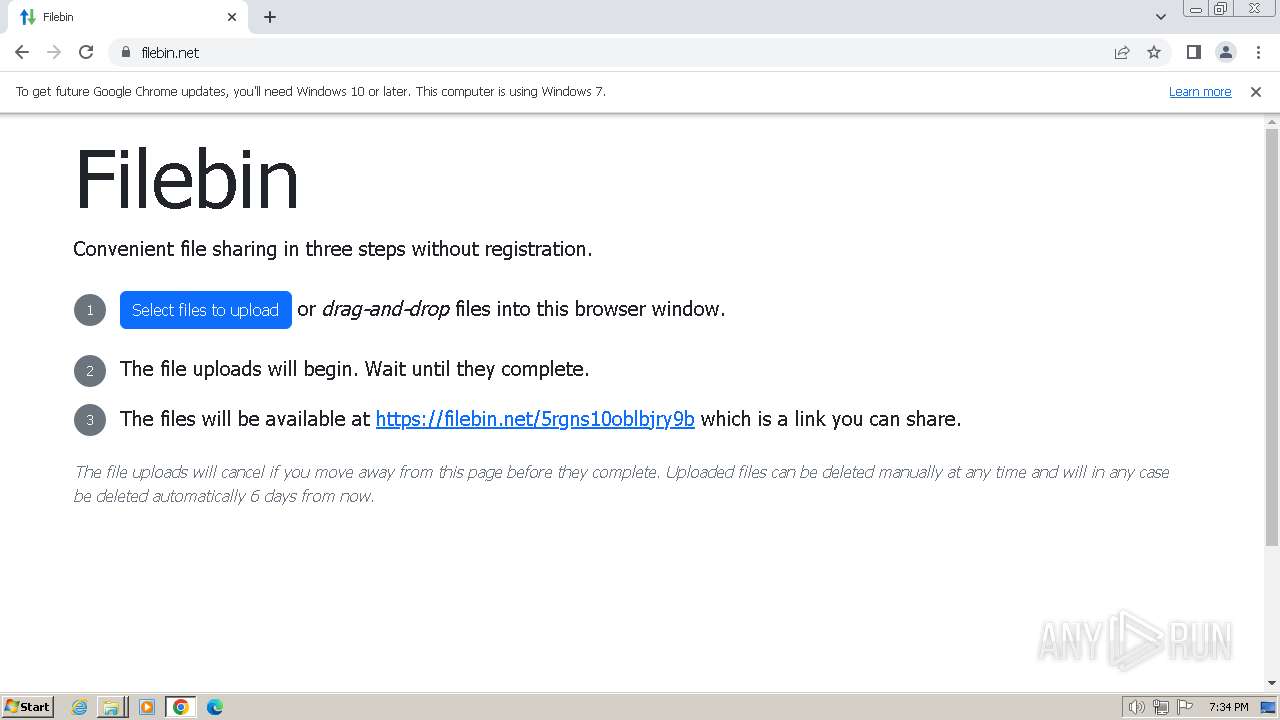
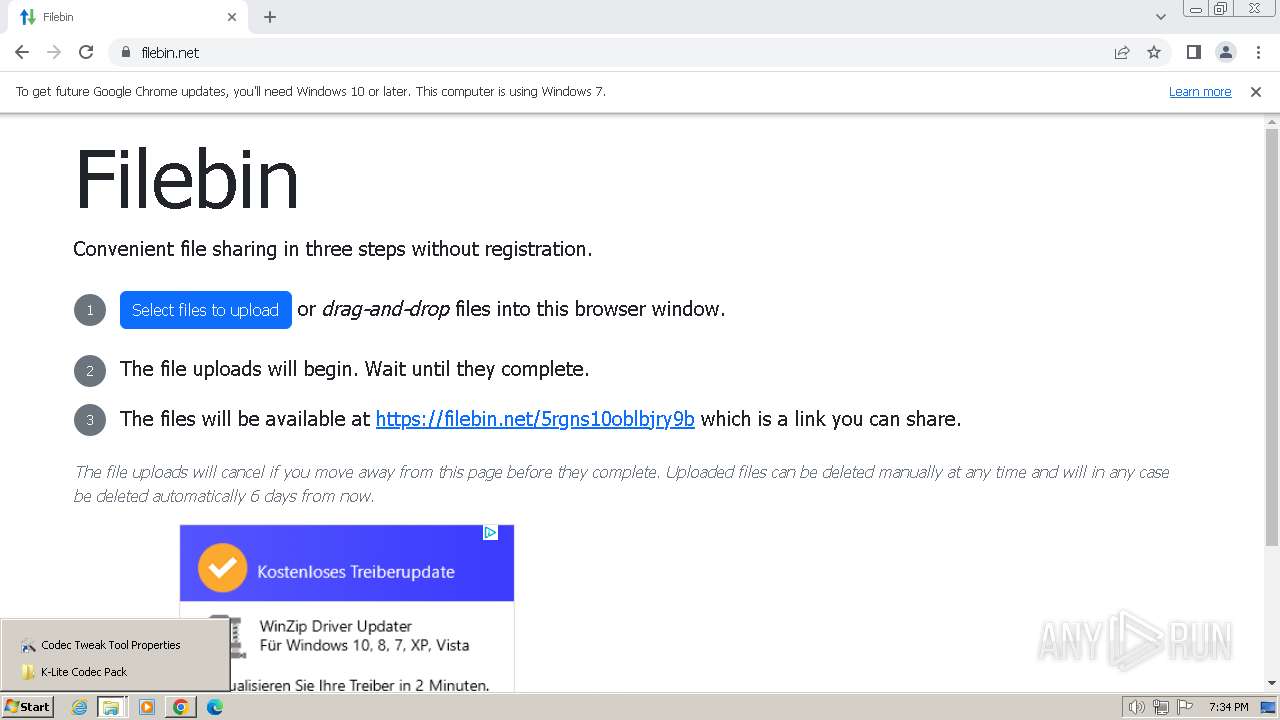
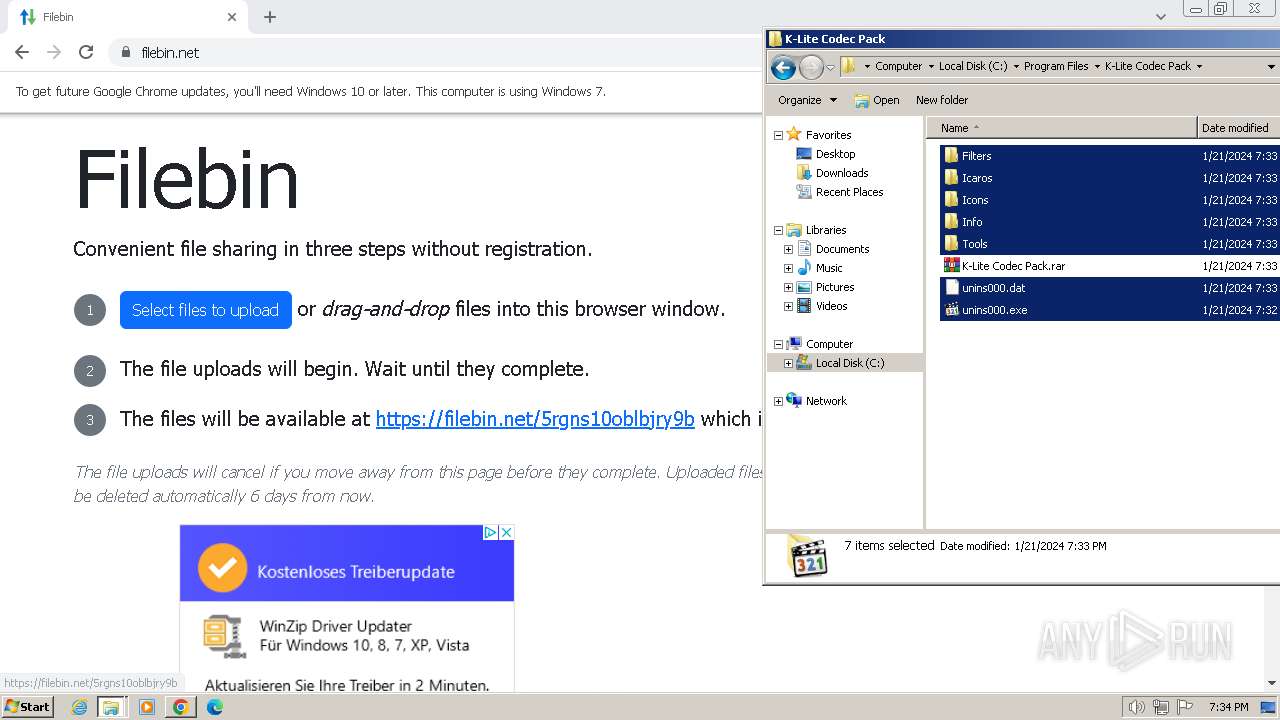
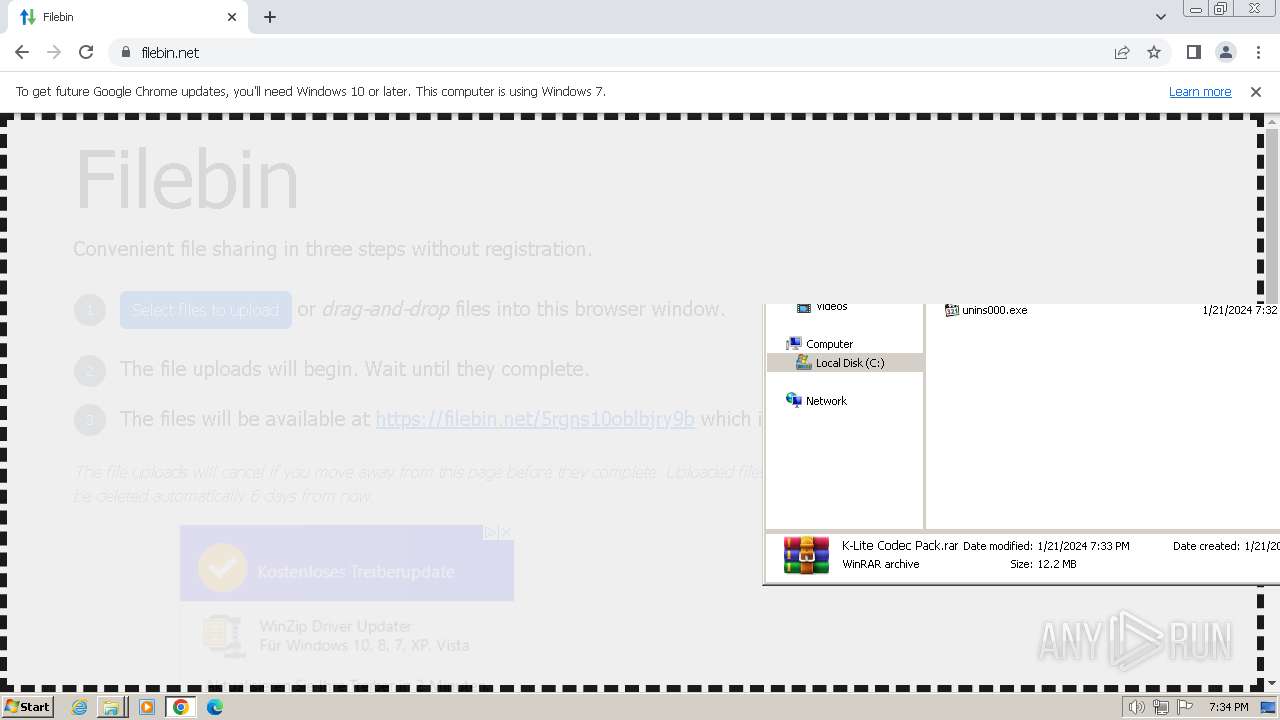
Manual execution by a user
- WinRAR.exe (PID: 2324)
- wmpnscfg.exe (PID: 3372)
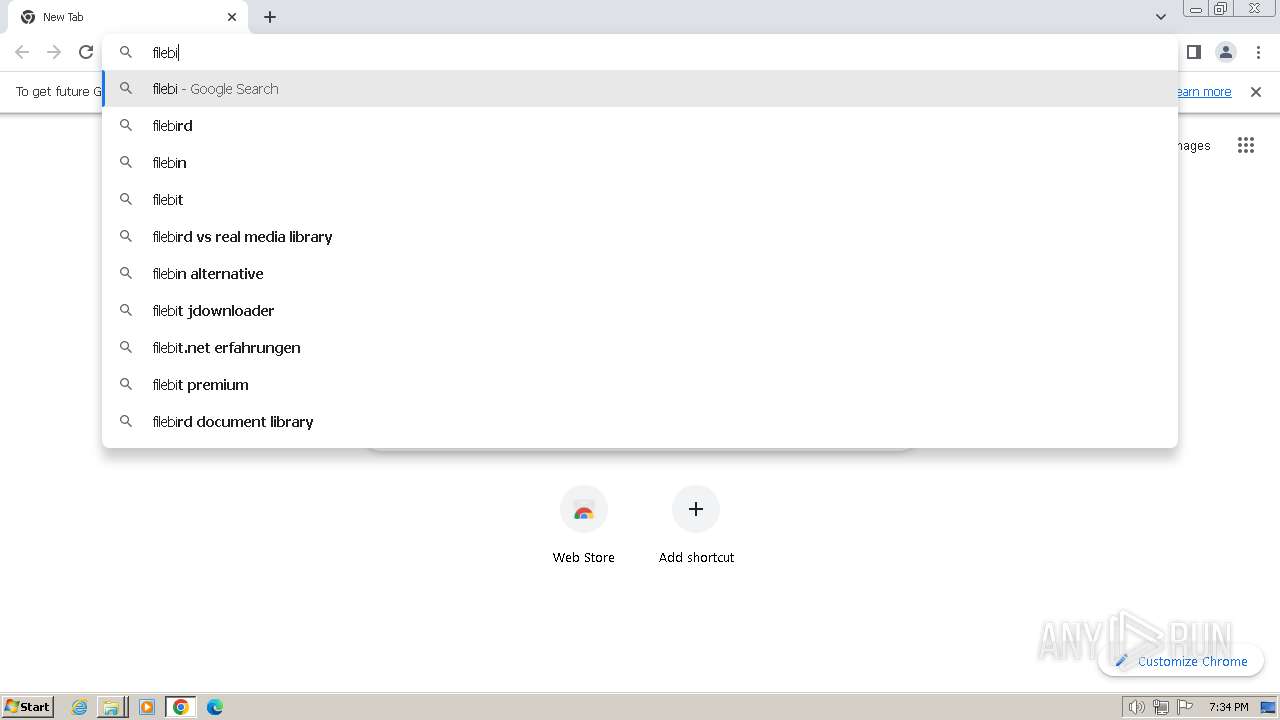
- chrome.exe (PID: 2548)
Application launched itself
- chrome.exe (PID: 2548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:06 16:39:04+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 191488 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x117dc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 13.4.5.0 |
| ProductVersionNumber: | 13.4.5.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
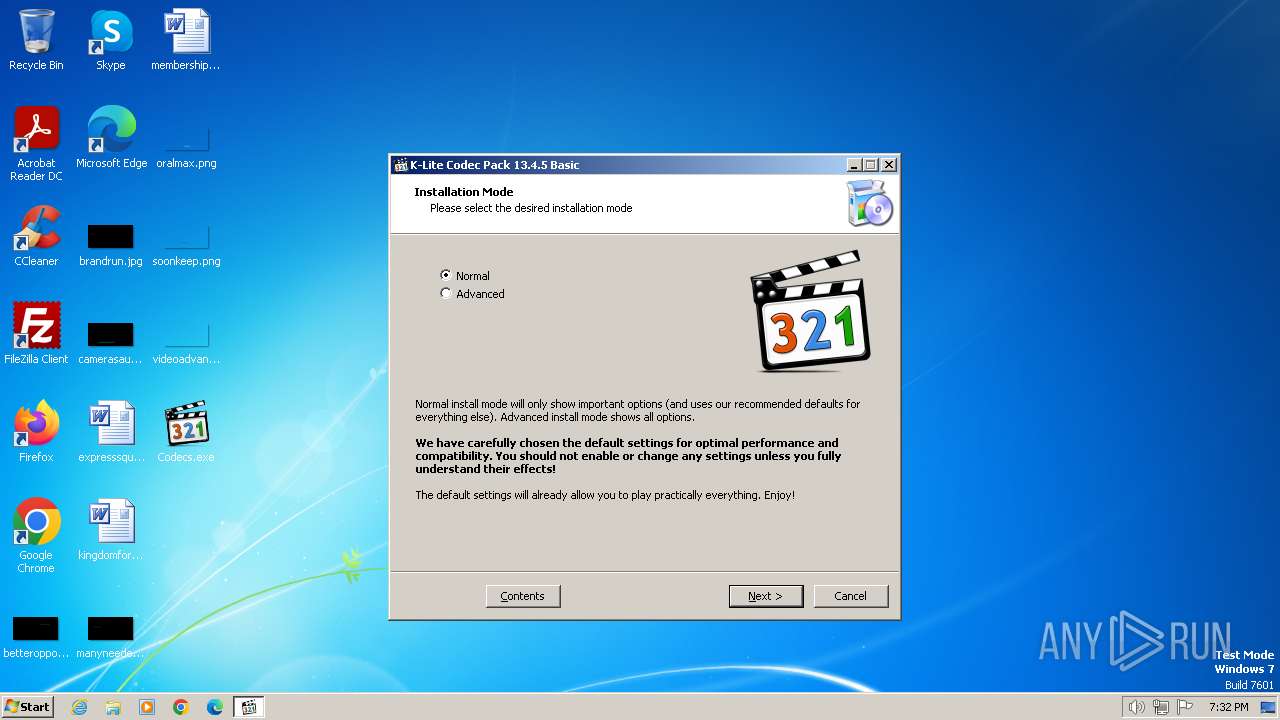
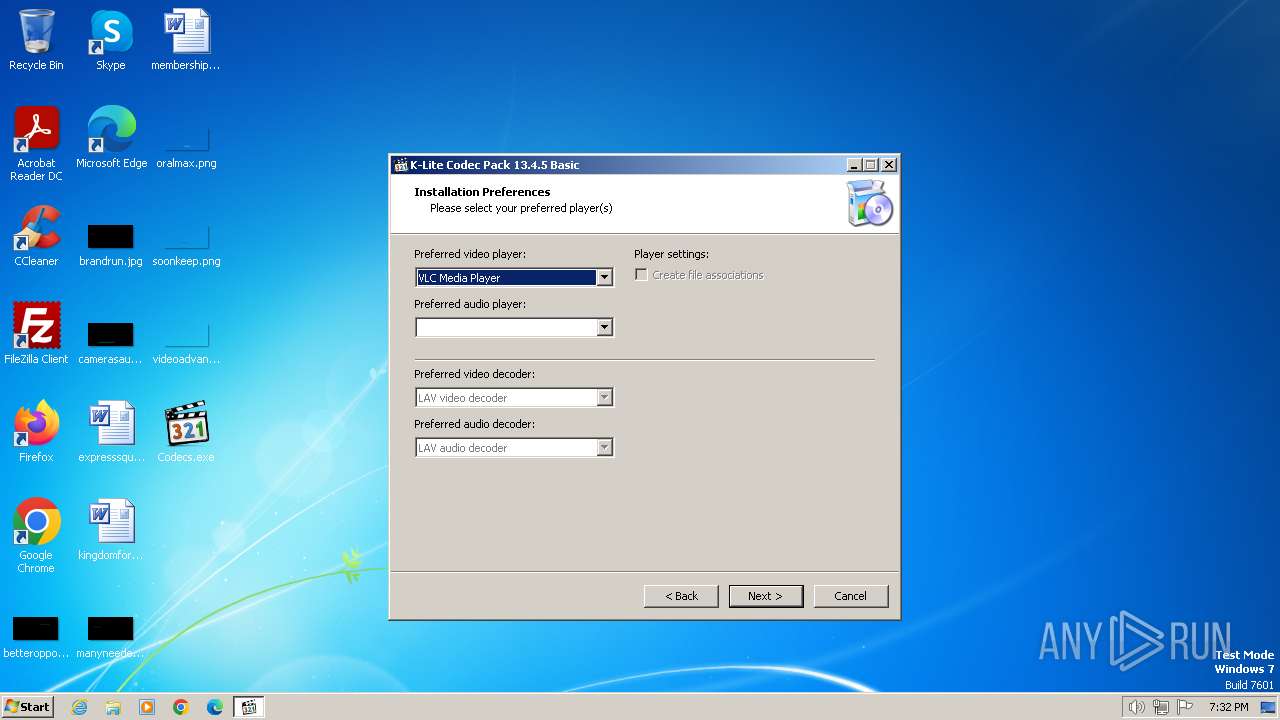
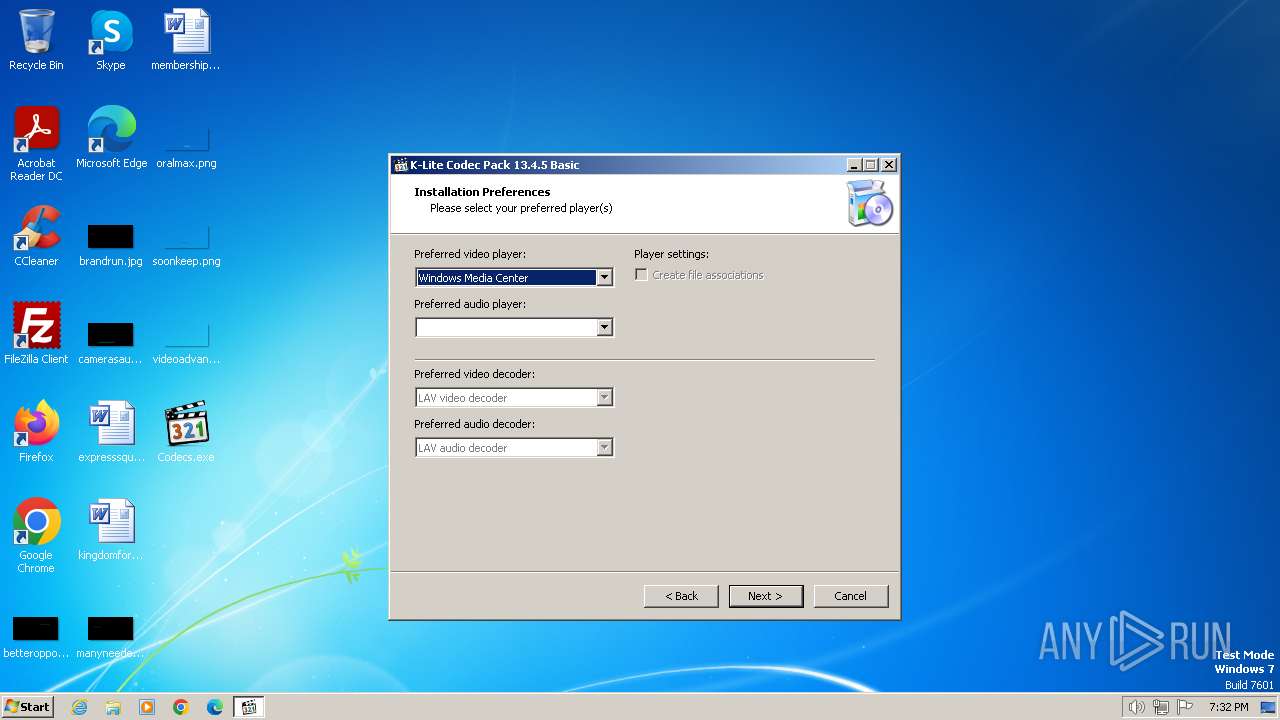
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | KLCP |
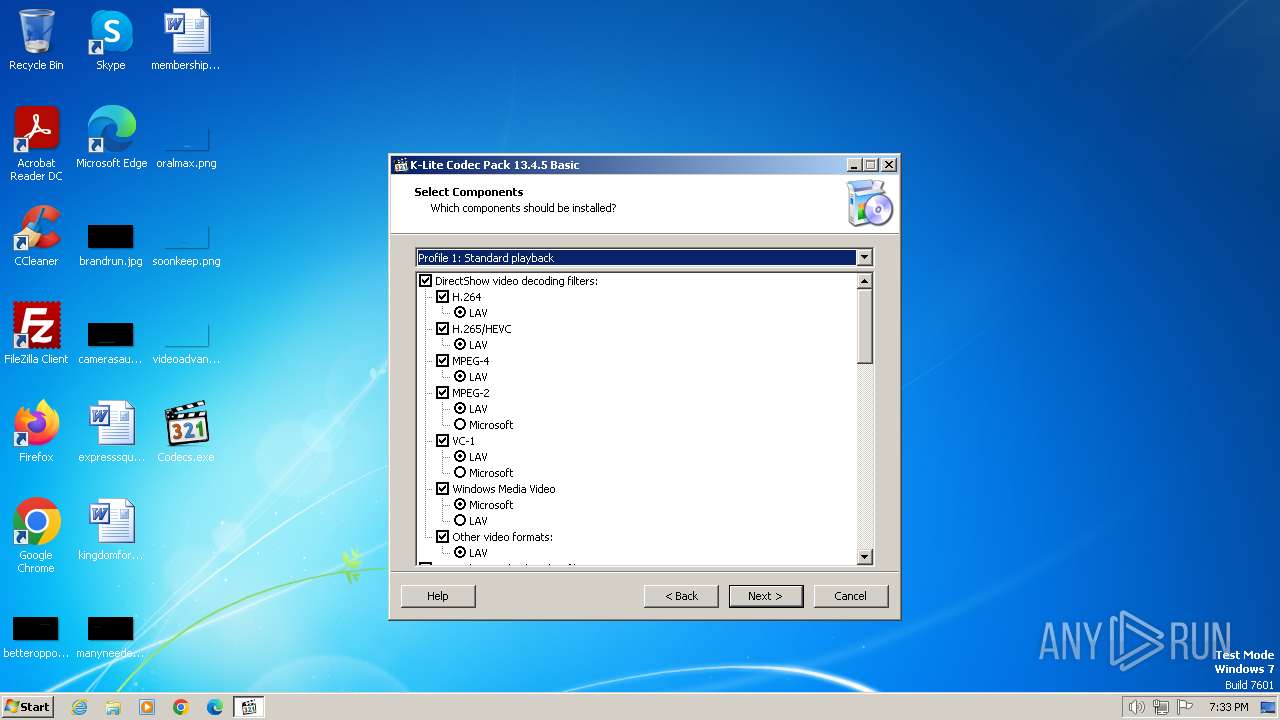
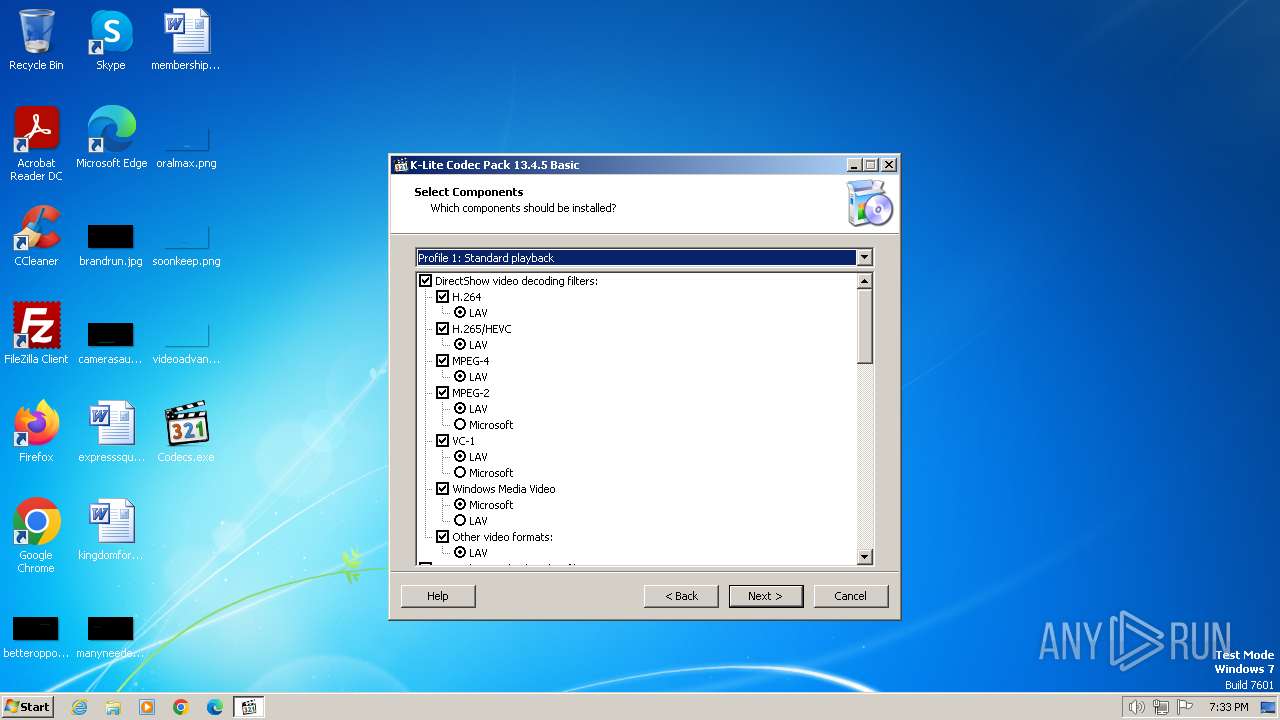
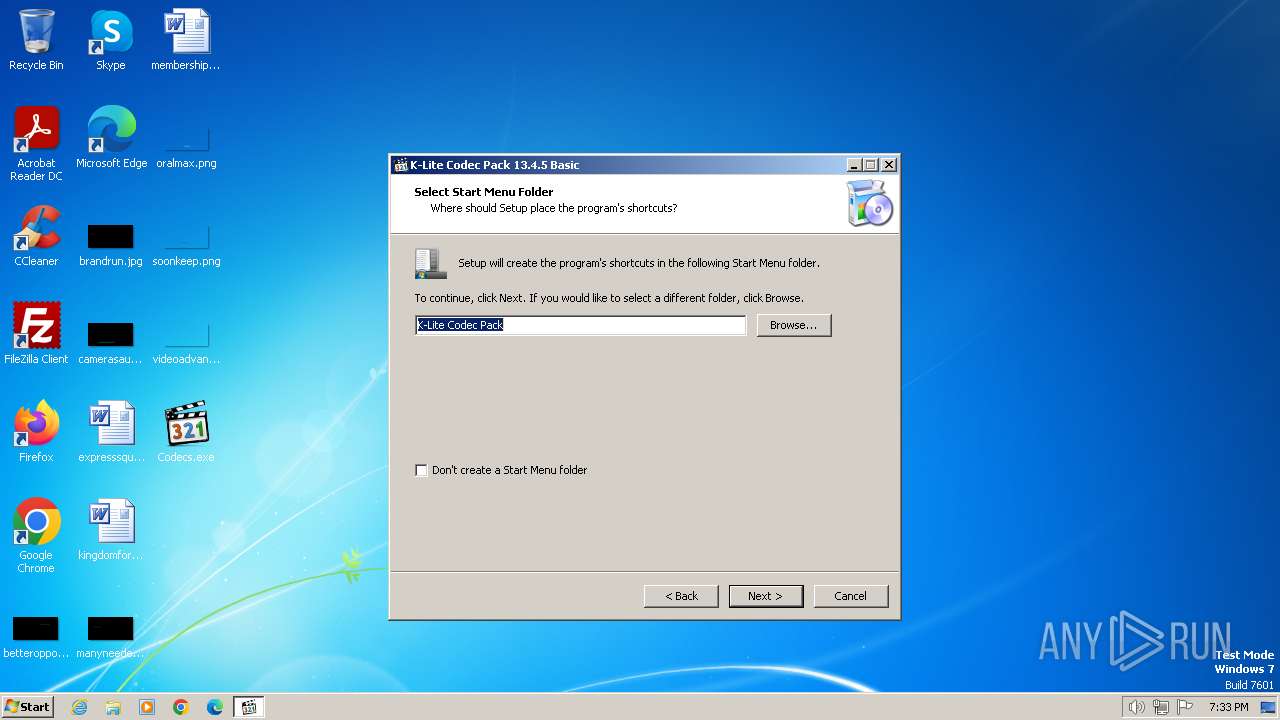
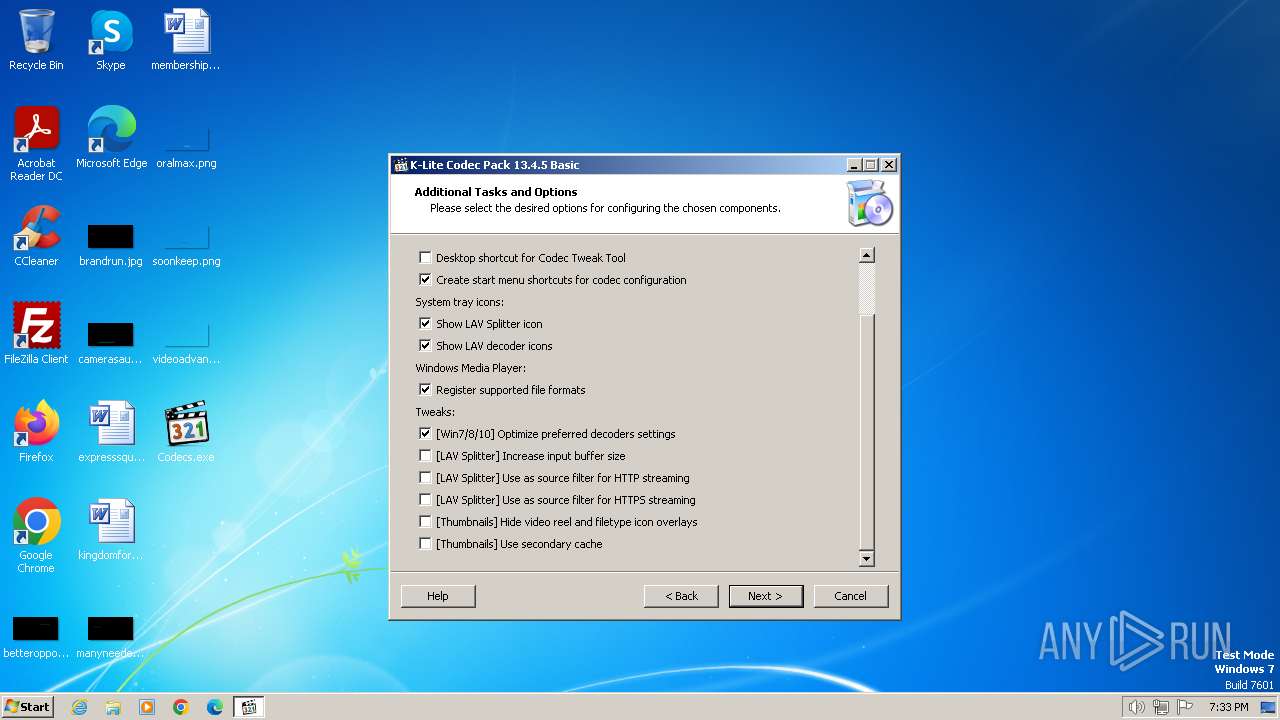
| FileDescription: | K-Lite Codec Pack Setup |
| FileVersion: | 13.4.5.0 |
| LegalCopyright: | |
| ProductName: | K-Lite Codec Pack |
| ProductVersion: | 13.4.5 |
Total processes
80
Monitored processes
34
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 784 | "C:\Users\admin\Desktop\Codecs.exe" /SPAWNWND=$401B2 /NOTIFYWND=$301AA | C:\Users\admin\Desktop\Codecs.exe | Codecs.tmp | ||||||||||||
User: admin Company: KLCP Integrity Level: HIGH Description: K-Lite Codec Pack Setup Exit code: 0 Version: 13.4.5.0 Modules
| |||||||||||||||
| 848 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\K-Lite Codec Pack\Filters\LAV\LAVSplitter.ax" | C:\Windows\System32\regsvr32.exe | — | Codecs.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1044 | "C:\Users\admin\AppData\Local\Temp\is-LUEMU.tmp\Codecs.tmp" /SL5="$400E6,15753090,259072,C:\Users\admin\Desktop\Codecs.exe" /SPAWNWND=$401B2 /NOTIFYWND=$301AA | C:\Users\admin\AppData\Local\Temp\is-LUEMU.tmp\Codecs.tmp | Codecs.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3944 --field-trial-handle=1156,i,17488514057297614776,2997174802798771067,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --mojo-platform-channel-handle=3976 --field-trial-handle=1156,i,17488514057297614776,2997174802798771067,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=4088 --field-trial-handle=1156,i,17488514057297614776,2997174802798771067,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1544 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\K-Lite Codec Pack\Icaros\32-bit\IcarosPropertyHandler.dll" | C:\Windows\System32\regsvr32.exe | — | Codecs.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1732 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\K-Lite Codec Pack\Filters\LAV\LAVVideo.ax" | C:\Windows\System32\regsvr32.exe | — | Codecs.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1796 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\K-Lite Codec Pack\Filters\LAV\LAVAudio.ax" | C:\Windows\System32\regsvr32.exe | — | Codecs.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1824 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\K-Lite Codec Pack\Filters\DirectVobSub\vsfilter.dll" | C:\Windows\System32\regsvr32.exe | — | Codecs.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 271
Read events
4 094
Write events
155
Delete events
22
Modification events
| (PID) Process: | (1044) Codecs.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Explorer.EXE | |||
| (PID) Process: | (1044) Codecs.tmp | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MediaResources\DirectSound\Speaker Configuration |
| Operation: | write | Name: | Speaker Configuration |
Value: 4 | |||
| (PID) Process: | (1044) Codecs.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFilesHash |
Value: F3C8A420BFCBA16BFCC779BE6FB2AA78EBB8DAFC582BB48B47DE4245EF73D6C9 | |||
| (PID) Process: | (1044) Codecs.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFiles0000 |
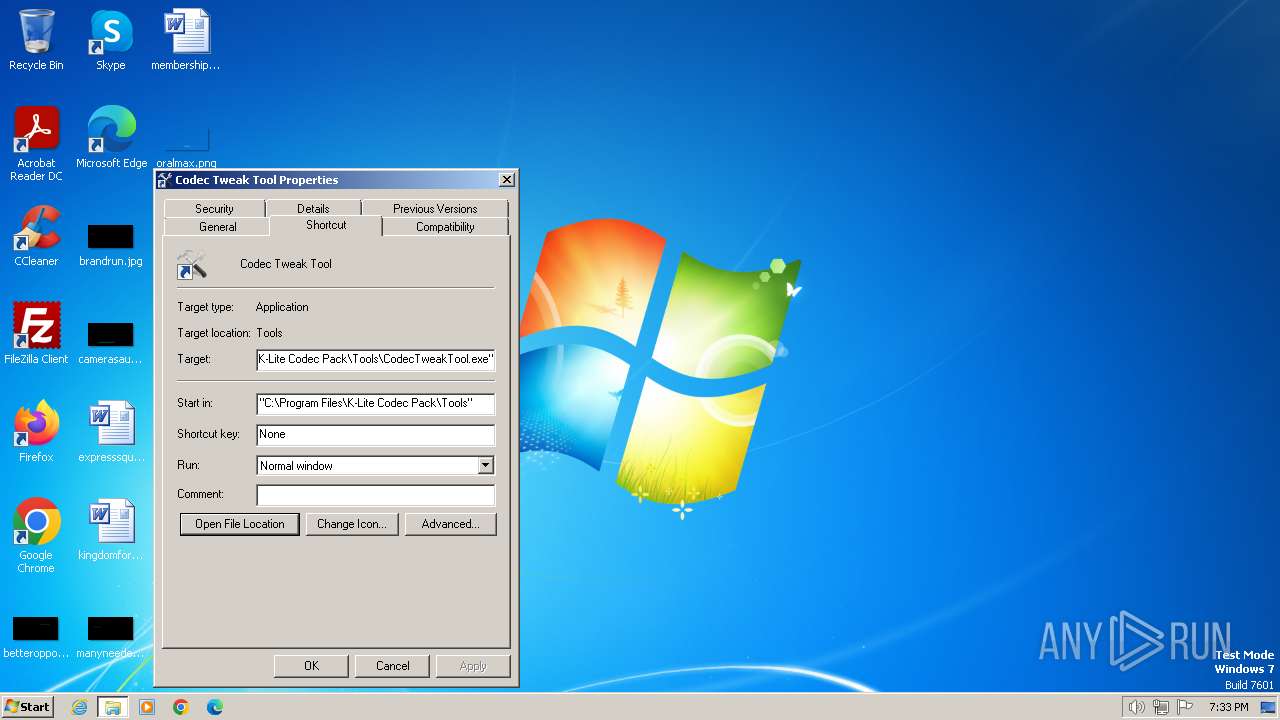
Value: C:\Program Files\K-Lite Codec Pack\Tools\CodecTweakTool.exe | |||
| (PID) Process: | (1044) Codecs.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (1044) Codecs.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | SessionHash |
Value: C0F6F08078A14A17CBFD39CA240B432474DF8D2C34BD3322AF2786FC8C1B74AD | |||
| (PID) Process: | (1044) Codecs.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Owner |
Value: 14040000924AAE97A04CDA01 | |||
| (PID) Process: | (1044) Codecs.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1044) Codecs.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFilesHash |
Value: EECFDB0C9DC8D1660776DA6F07ECA4F66E8D76CA21FA68DF8EEE920C54A0CF3B | |||
| (PID) Process: | (1044) Codecs.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFiles0000 |
Value: C:\Program Files\K-Lite Codec Pack\Filters\LAV\LAVAudio.ax | |||
Executable files
49
Suspicious files
118
Text files
69
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
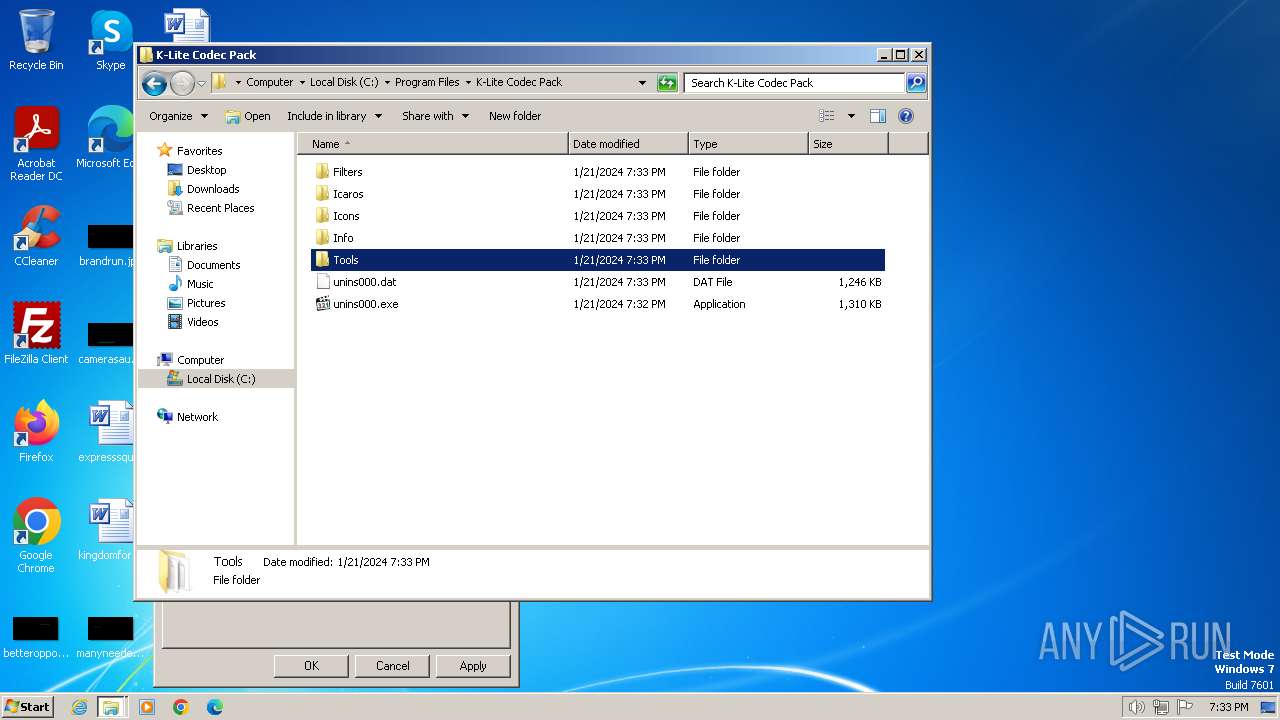
| 1044 | Codecs.tmp | C:\Program Files\K-Lite Codec Pack\unins000.exe | executable | |
MD5:93FB82357AB0F109C21FAB3B85C1992C | SHA256:01A560507A5794B9146C99528456F9D51E573CC9AE388D891049F3489621D93B | |||
| 1044 | Codecs.tmp | C:\Users\admin\AppData\Local\Temp\is-RIMBA.tmp\klcp_detect2.dll | executable | |
MD5:67C7C8EC61094D0D5E59E7CAC8A39808 | SHA256:D72E5D2A5368DD9CE70C7ECCFC0D637BAA433B571E2466BCA696D7E23F4DFEB4 | |||
| 784 | Codecs.exe | C:\Users\admin\AppData\Local\Temp\is-LUEMU.tmp\Codecs.tmp | executable | |
MD5:0F85F217FA49597D023DE2251EB01AFE | SHA256:59BB2F266EC5A0180BF7060C0C8CE3559E3A688EF86924EA0BC0DE10CBAE2915 | |||
| 1044 | Codecs.tmp | C:\Users\admin\AppData\Local\Temp\is-RIMBA.tmp\_isetup\_iscrypt.dll | executable | |
MD5:A69559718AB506675E907FE49DEB71E9 | SHA256:2F6294F9AA09F59A574B5DCD33BE54E16B39377984F3D5658CDA44950FA0F8FC | |||
| 1044 | Codecs.tmp | C:\Program Files\K-Lite Codec Pack\Info\is-L83J9.tmp | text | |
MD5:F30768139453DAFD29080EFCE5D8996B | SHA256:79FC3A43EEF9FD4D1DEBC3854E25ECA954445986D0A532672A2F278D84C3C093 | |||
| 1044 | Codecs.tmp | C:\Users\admin\AppData\Local\Temp\is-RIMBA.tmp\klcp_detect.dll | executable | |
MD5:D66F5CB867234099E717109F4B8A2888 | SHA256:EE0A1551A72599042683084CA88782ABBF8F26C9484FB448035058E80D08A5E3 | |||
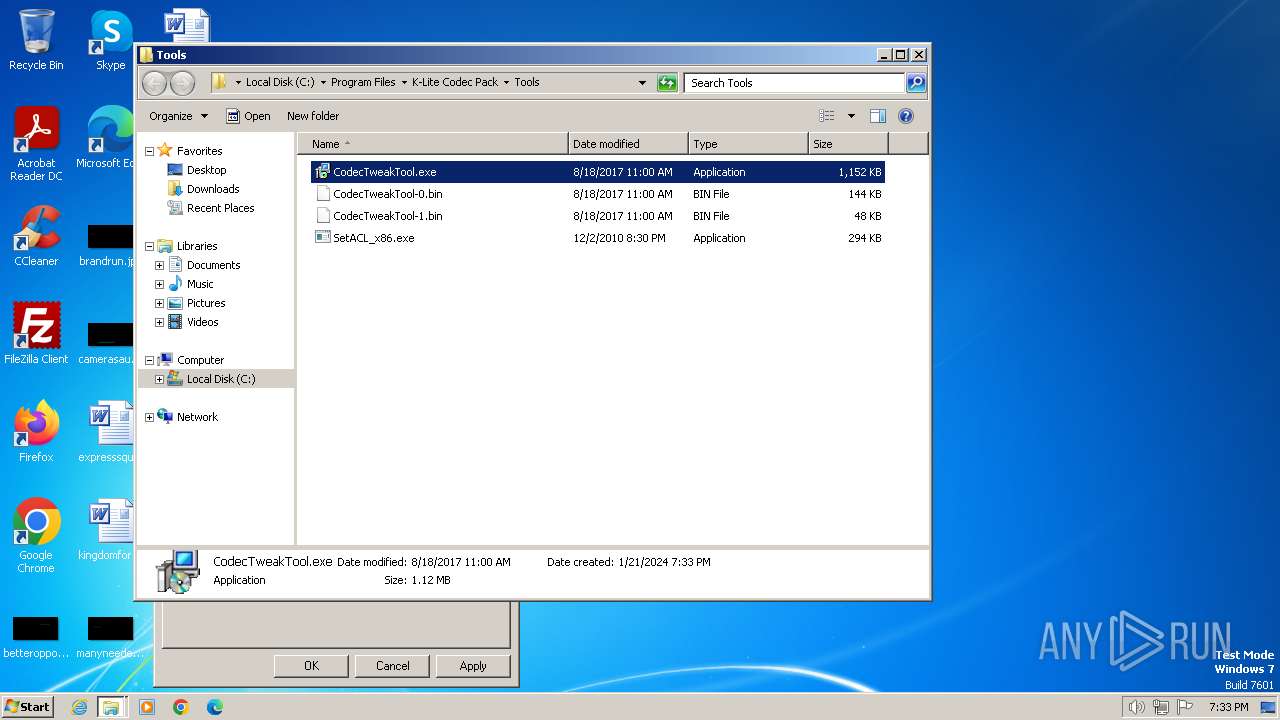
| 1044 | Codecs.tmp | C:\Program Files\K-Lite Codec Pack\Tools\is-CSQL3.tmp | binary | |
MD5:102E6E1E7D7E8281619A0DF652C9228C | SHA256:D5BB04DEC4F09C8FBAE338142B87DF62780EBEC7F78DA7194A8BB5332BCB70F0 | |||
| 1044 | Codecs.tmp | C:\Program Files\K-Lite Codec Pack\Tools\CodecTweakTool-0.bin | binary | |
MD5:102E6E1E7D7E8281619A0DF652C9228C | SHA256:D5BB04DEC4F09C8FBAE338142B87DF62780EBEC7F78DA7194A8BB5332BCB70F0 | |||
| 1044 | Codecs.tmp | C:\Program Files\K-Lite Codec Pack\Tools\is-QAHNJ.tmp | binary | |
MD5:BFC586B3F628C230147B4FE01EF64E3B | SHA256:B89C4981B34259048085E030DA4962F0B90BE3A51BF048A674ED9FA86C733040 | |||
| 1044 | Codecs.tmp | C:\Program Files\K-Lite Codec Pack\Tools\CodecTweakTool-1.bin | binary | |
MD5:BFC586B3F628C230147B4FE01EF64E3B | SHA256:B89C4981B34259048085E030DA4962F0B90BE3A51BF048A674ED9FA86C733040 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
49
DNS requests
55
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | US | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | US | binary | 5.56 Kb | unknown |
856 | svchost.exe | GET | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | US | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2548 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2968 | chrome.exe | 108.177.127.84:443 | accounts.google.com | GOOGLE | US | unknown |
2968 | chrome.exe | 172.217.169.164:443 | www.google.com | GOOGLE | US | whitelisted |
2968 | chrome.exe | 142.250.186.67:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
2968 | chrome.exe | 142.250.181.227:443 | update.googleapis.com | GOOGLE | US | whitelisted |
2548 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
2968 | chrome.exe | 142.250.185.99:443 | www.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
lh5.googleusercontent.com |
| whitelisted |
apis.google.com |
| whitelisted |
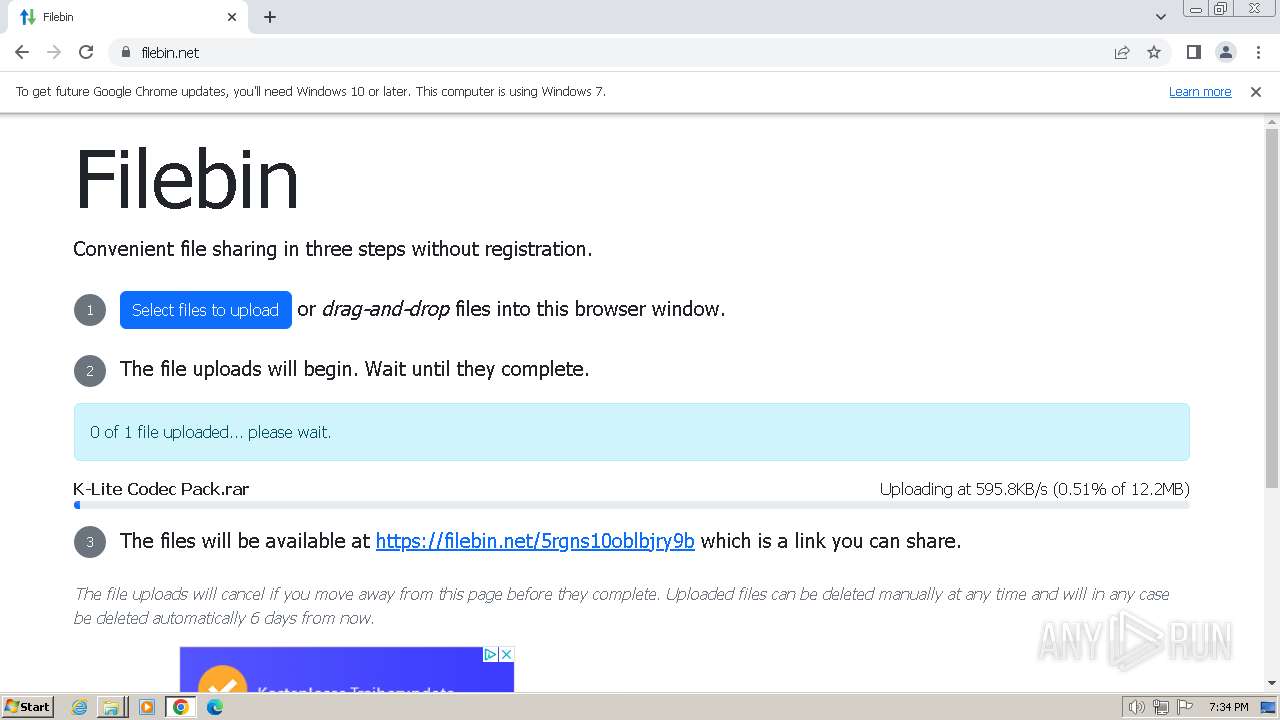
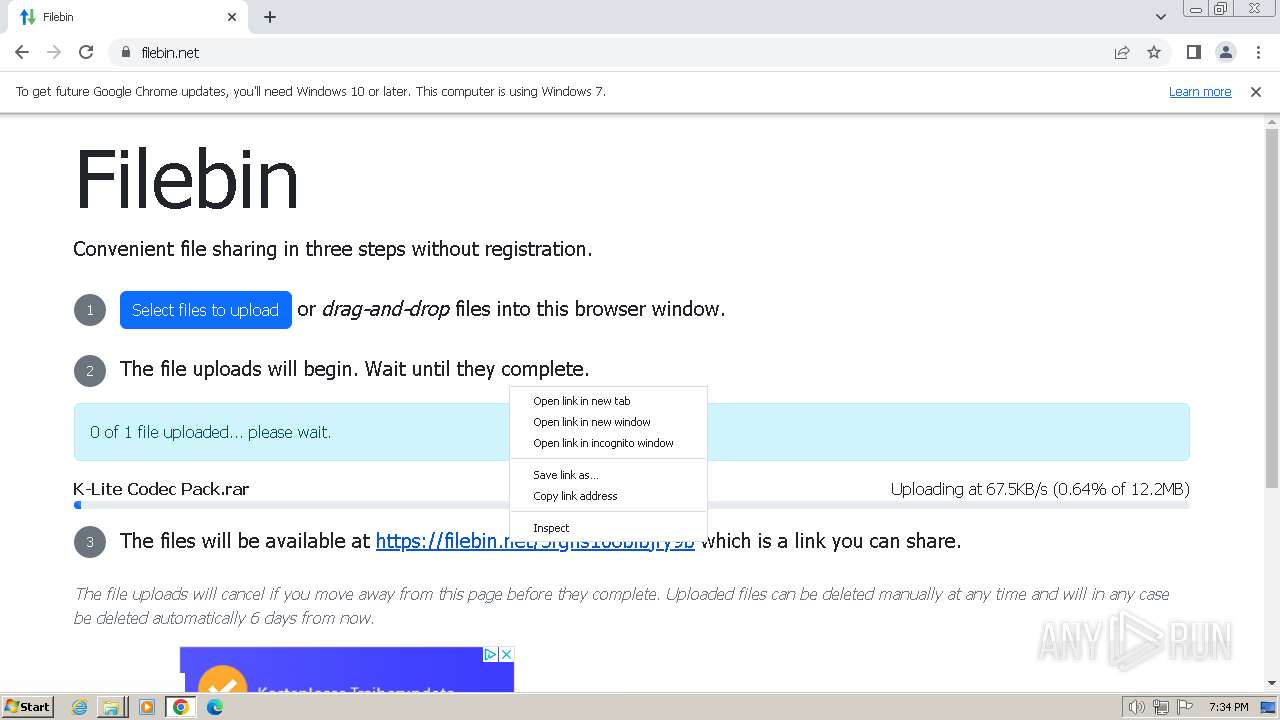
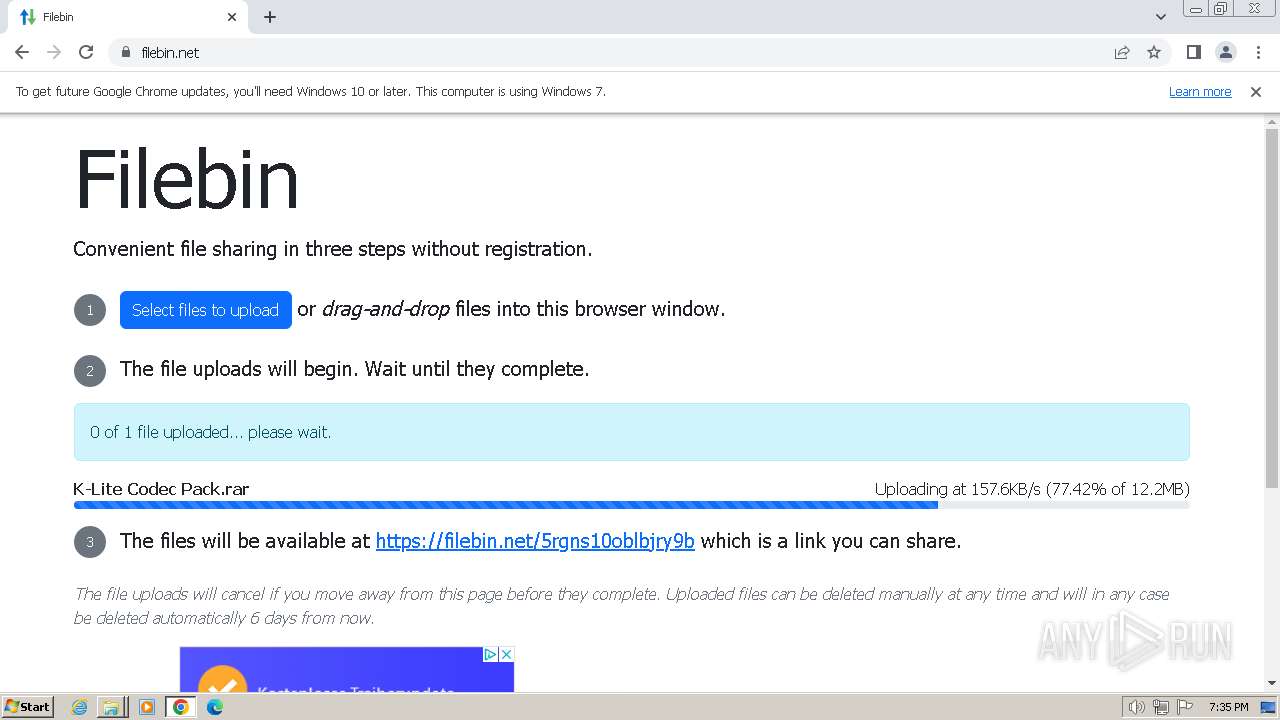
filebin.net |
| unknown |
pagead2.googlesyndication.com |
| whitelisted |