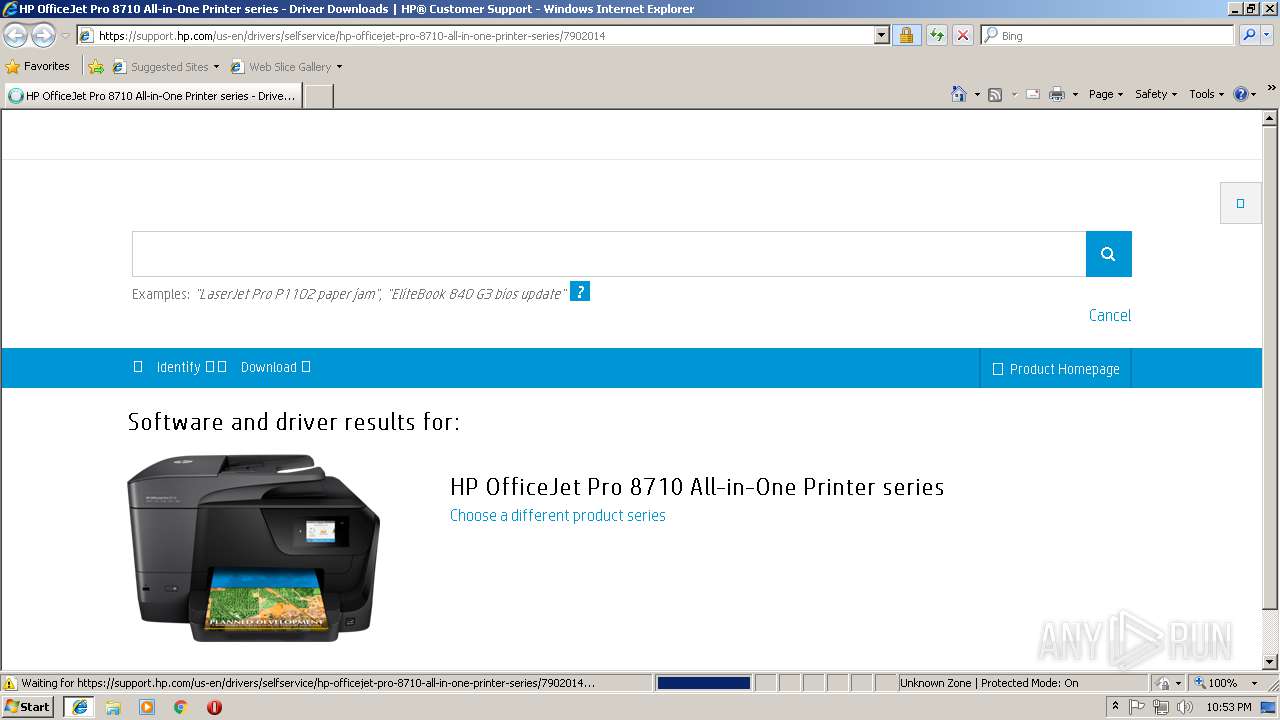
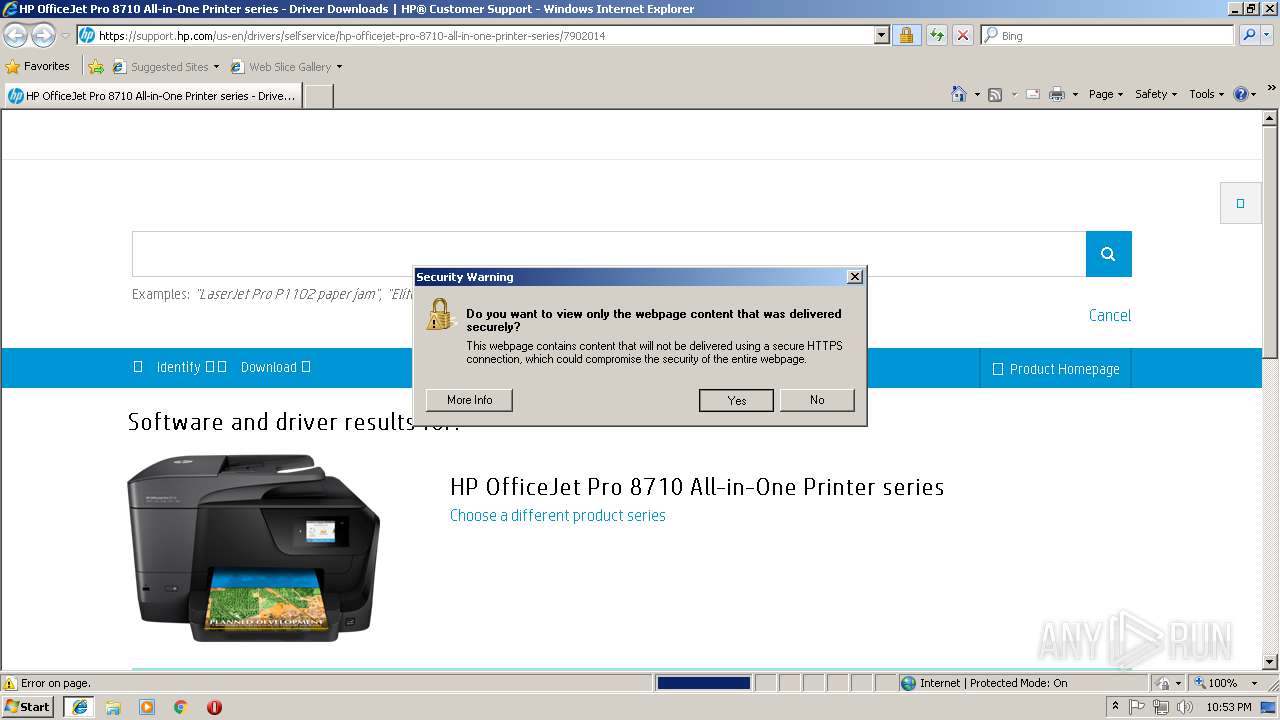
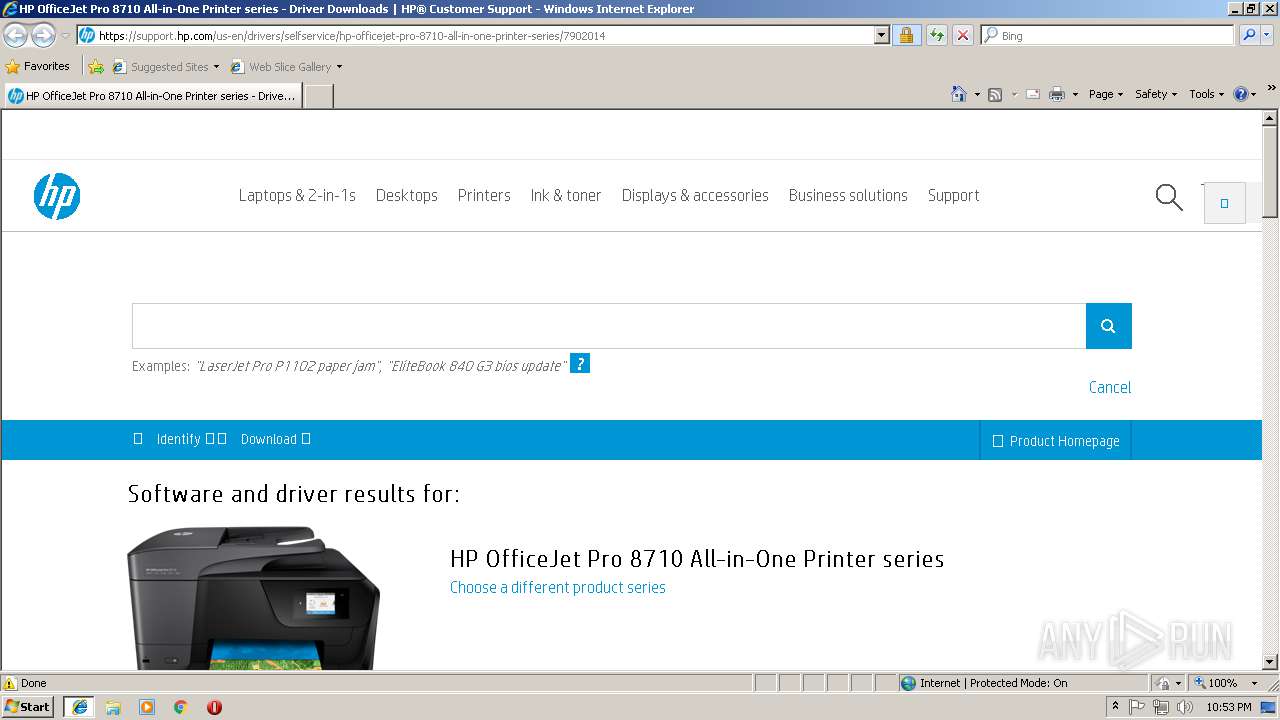
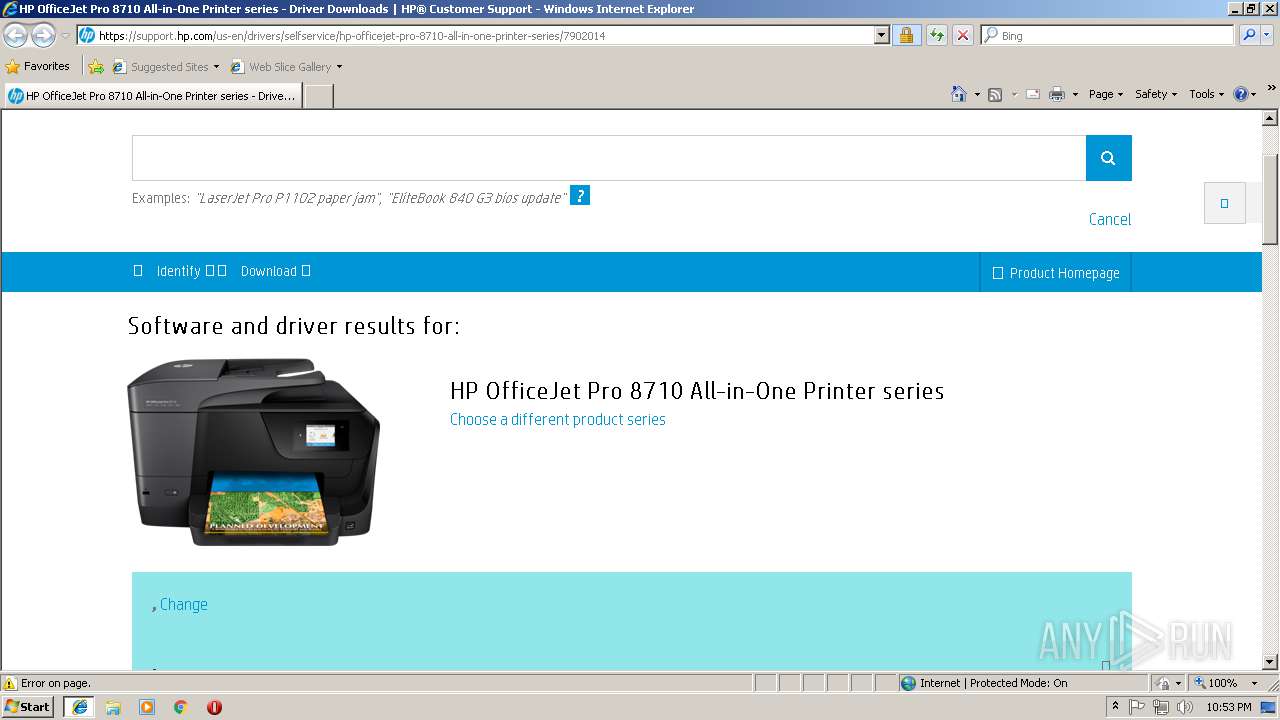
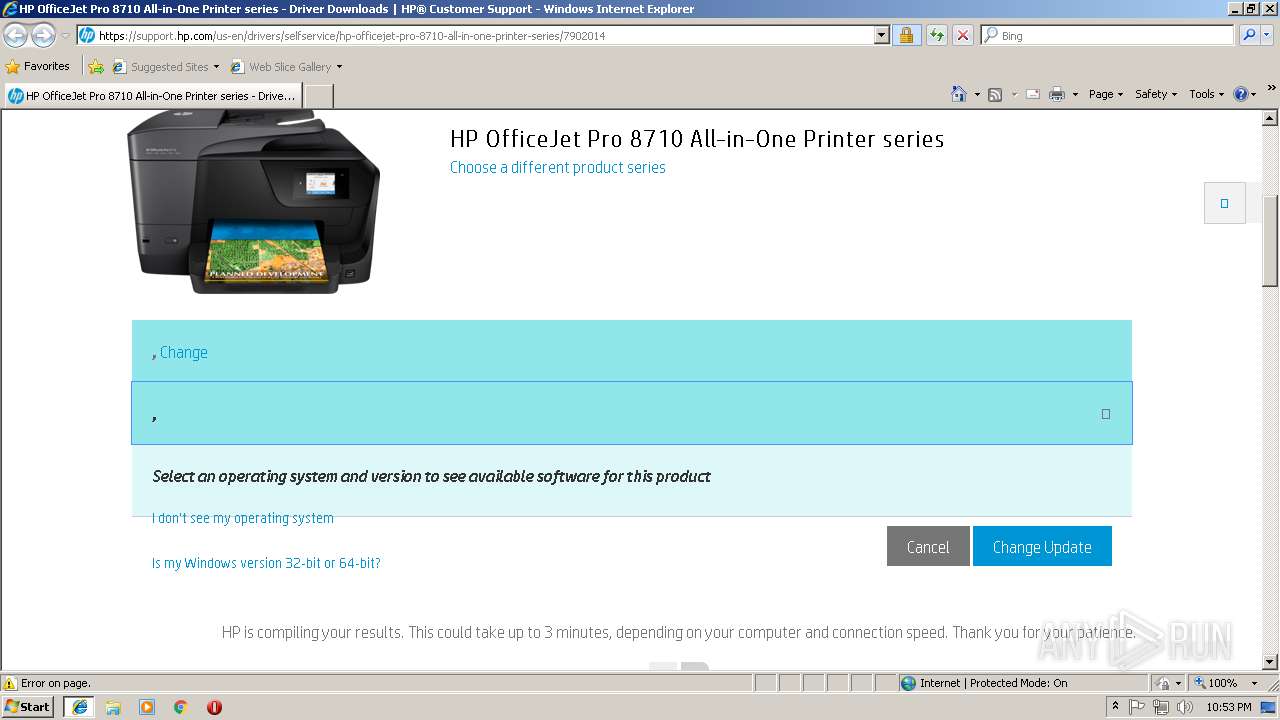
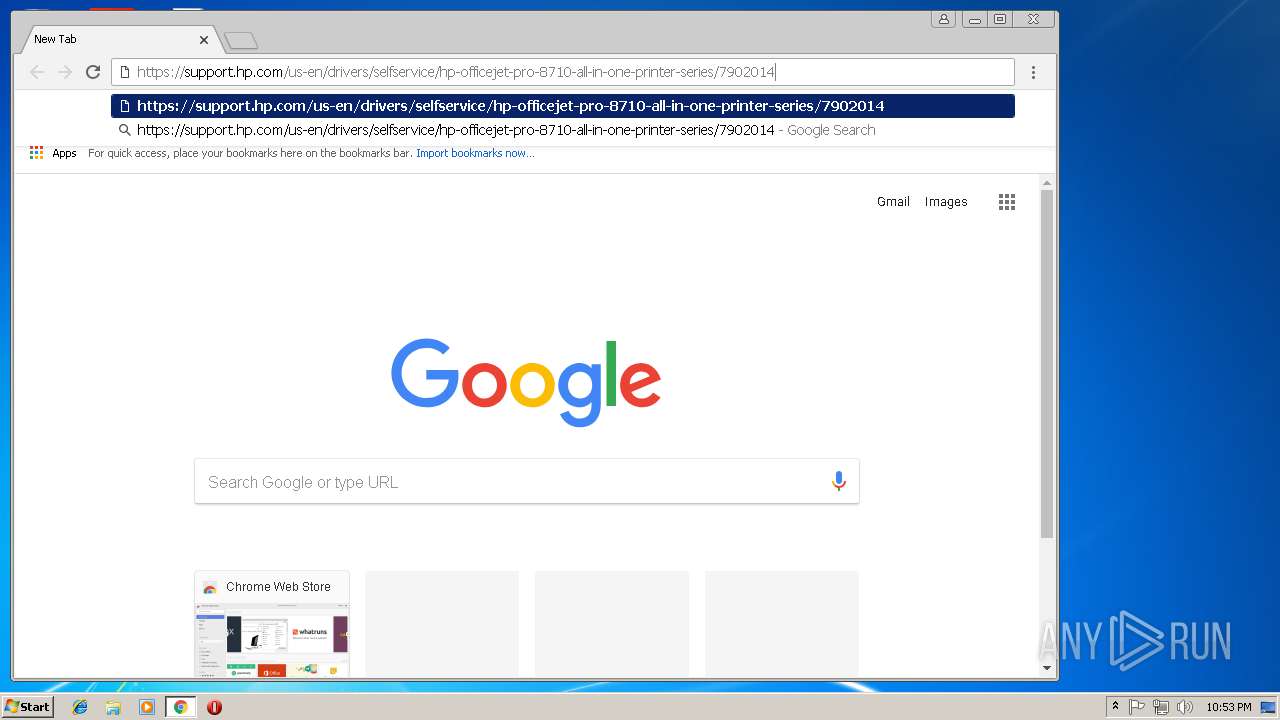
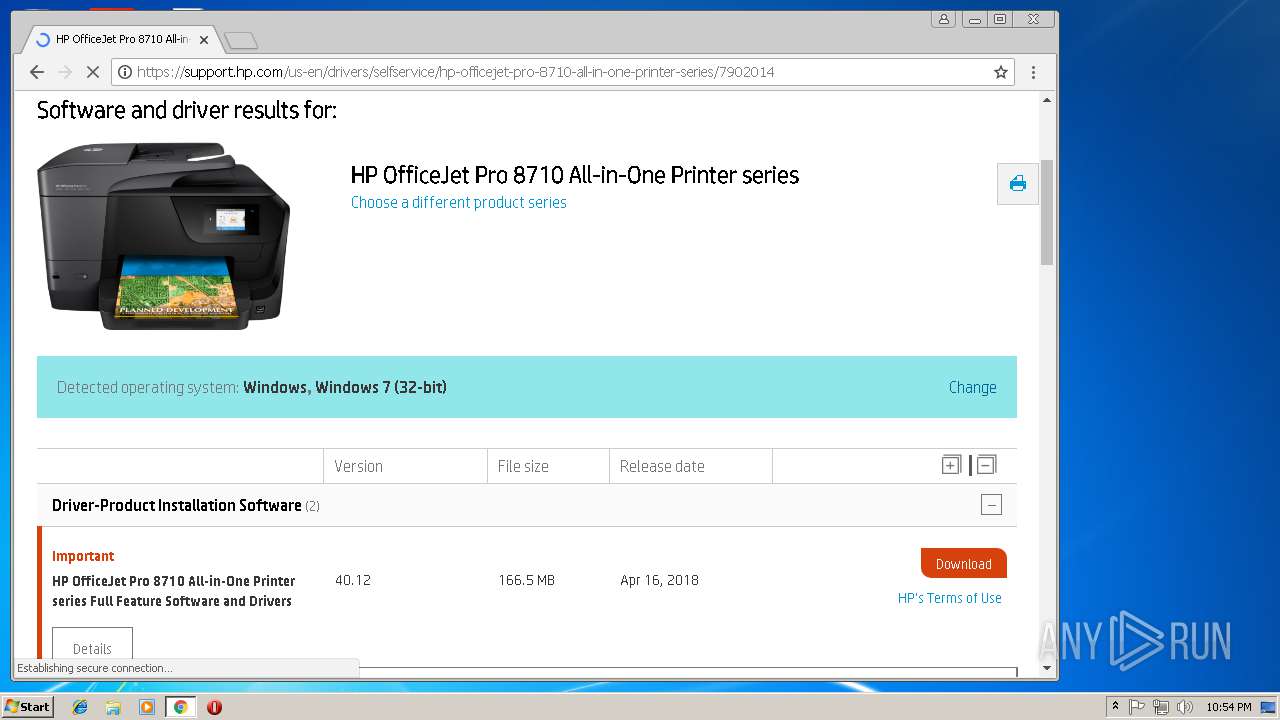
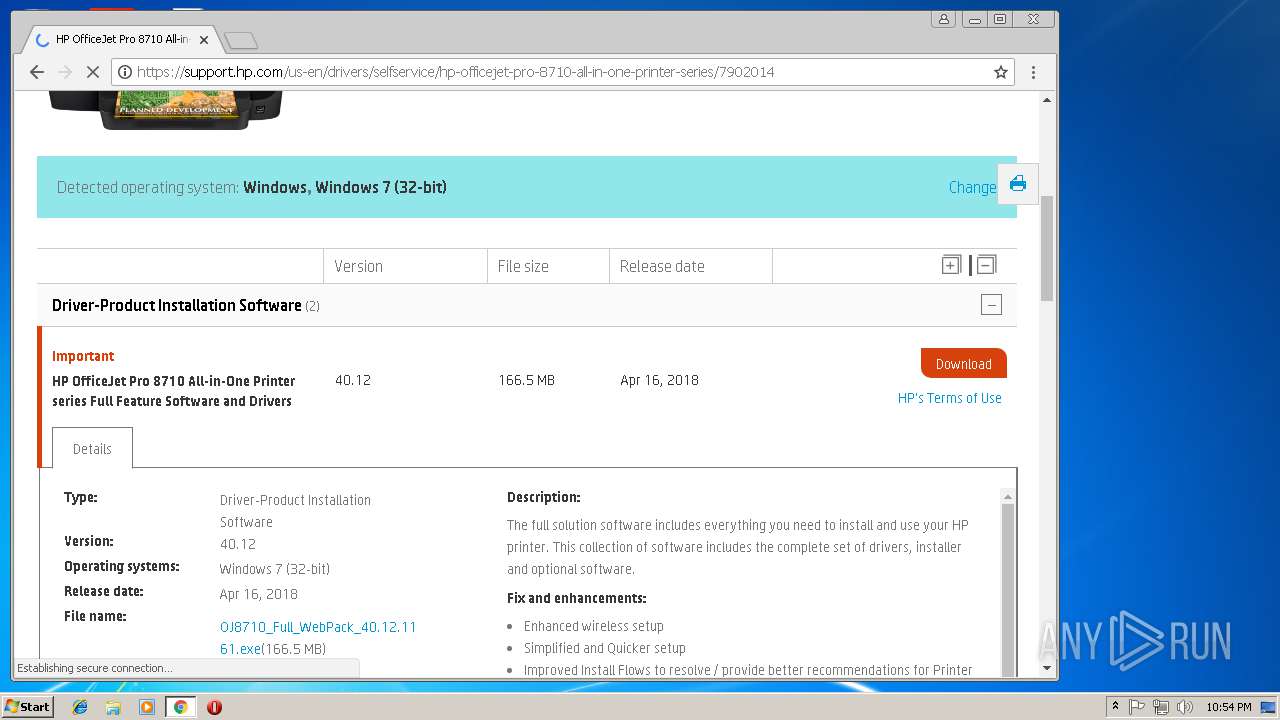
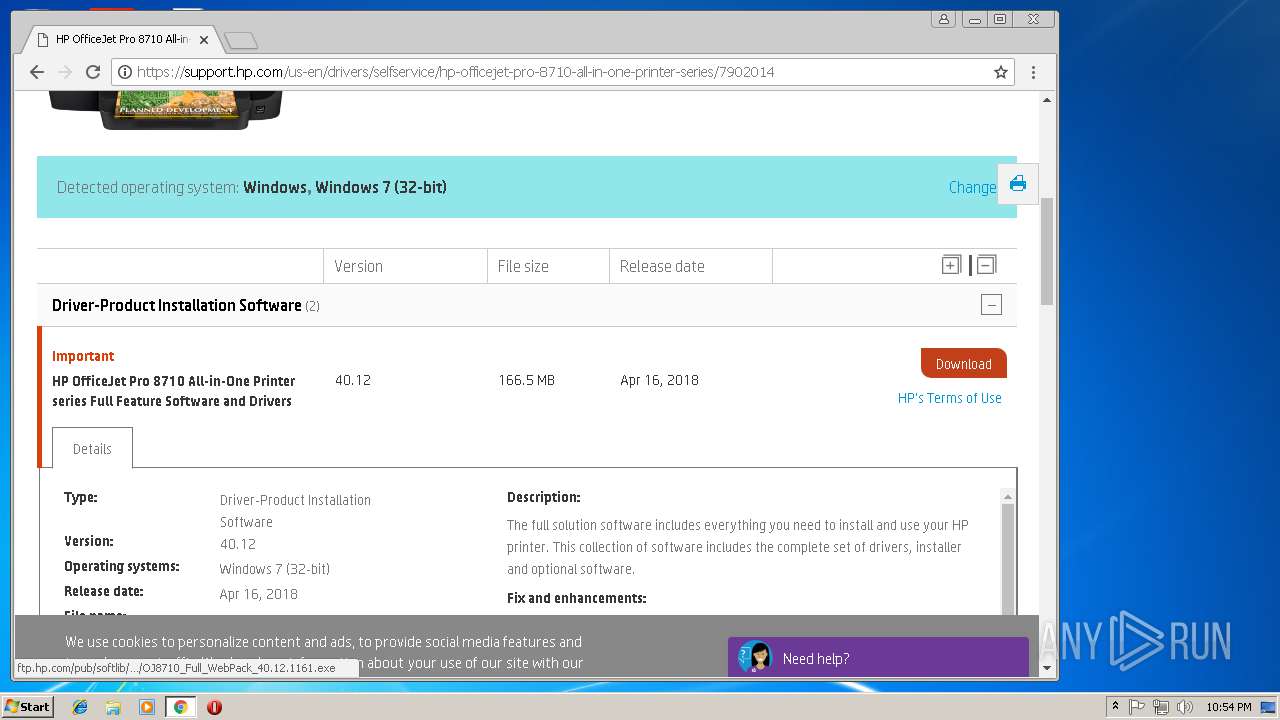
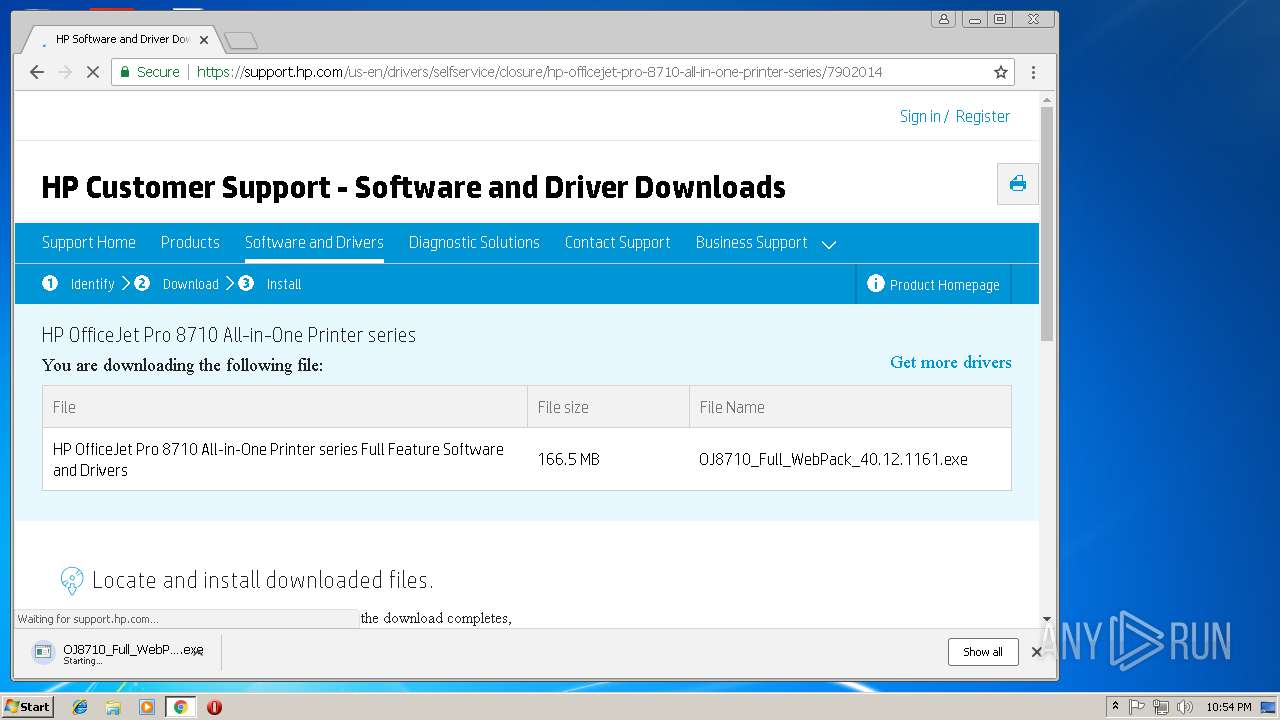
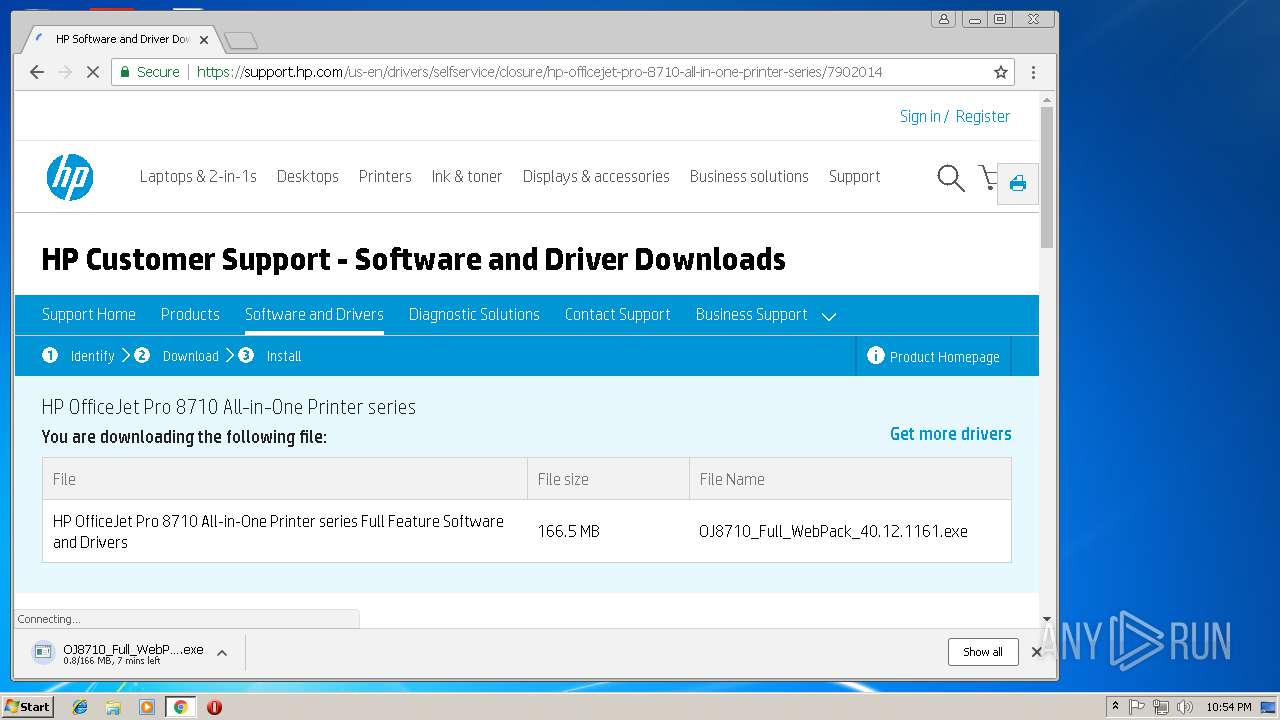
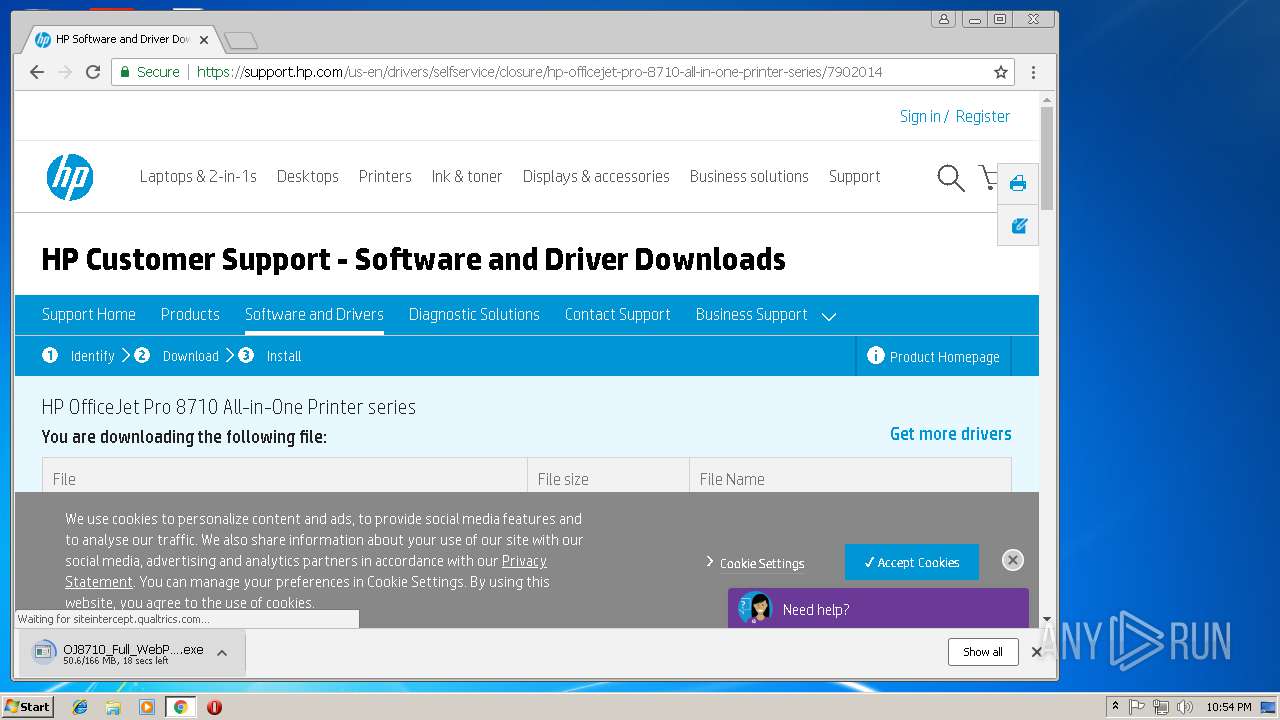
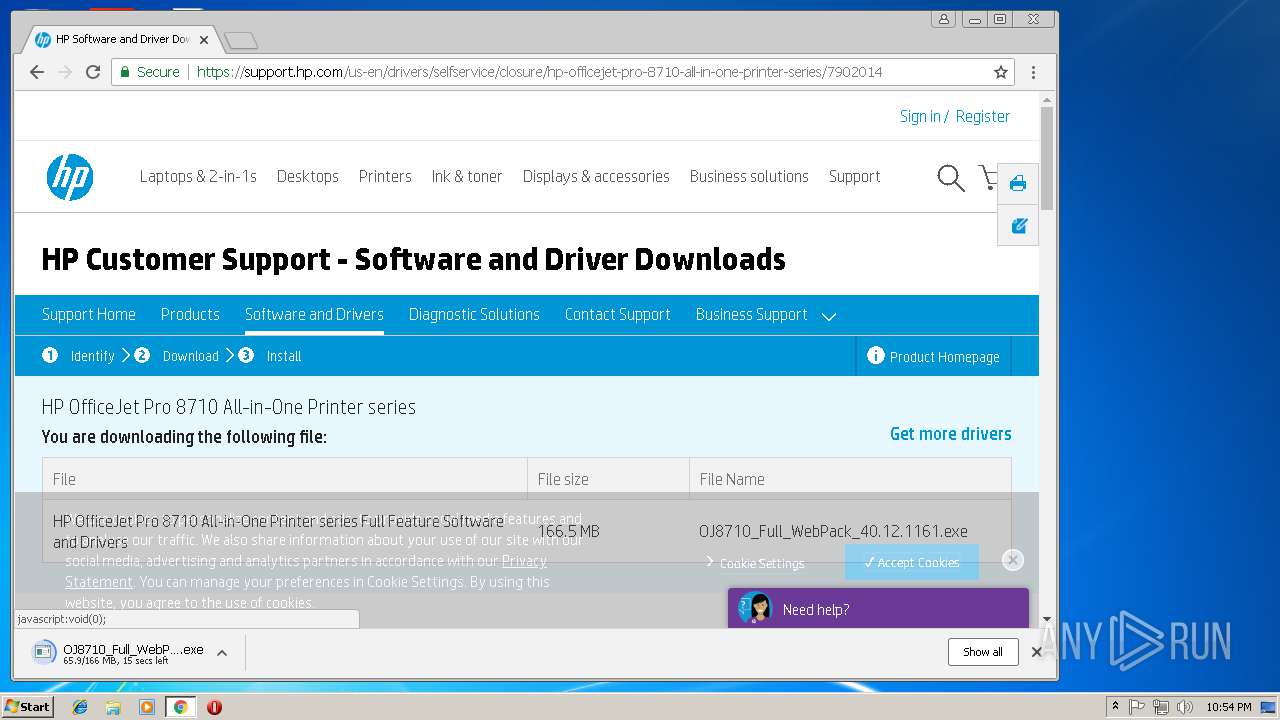
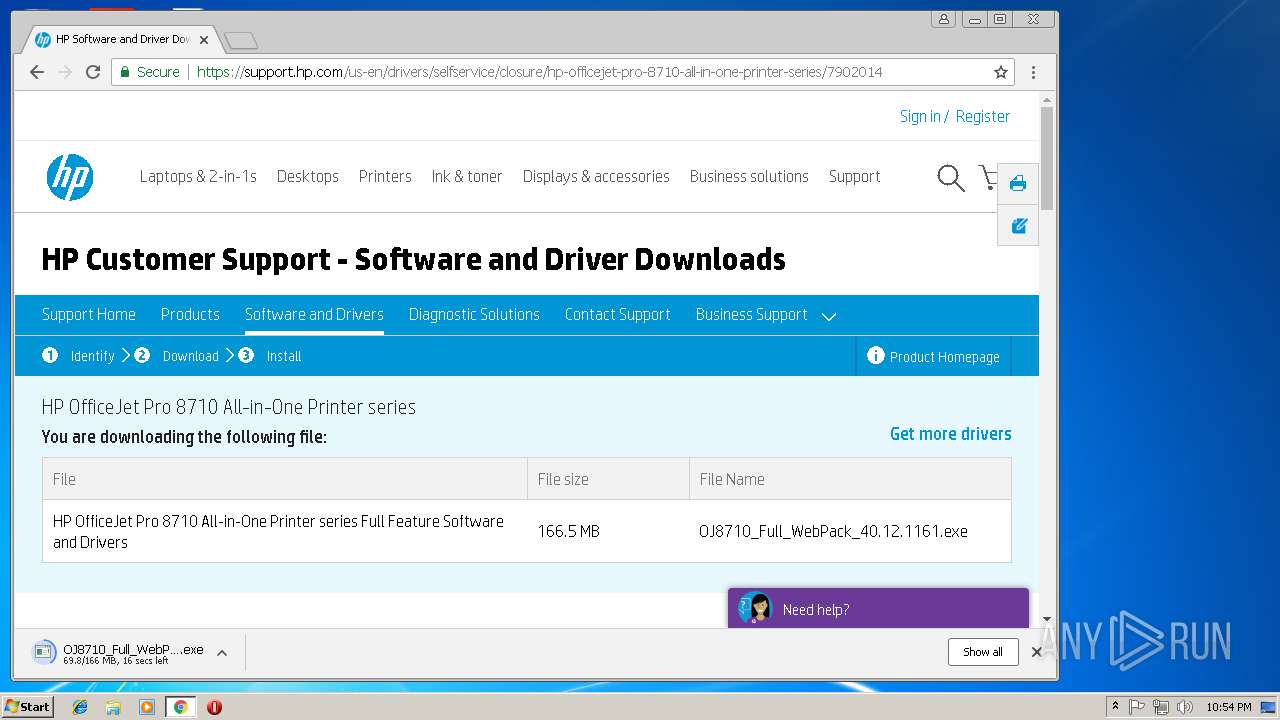
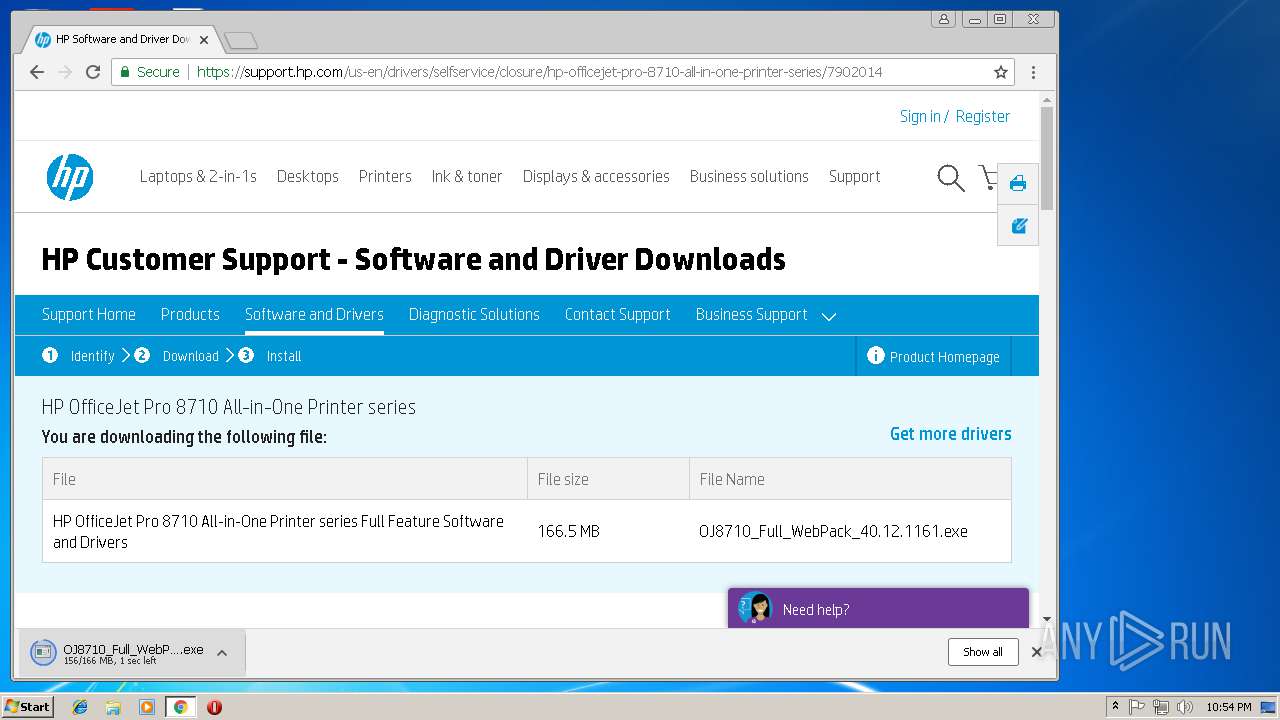
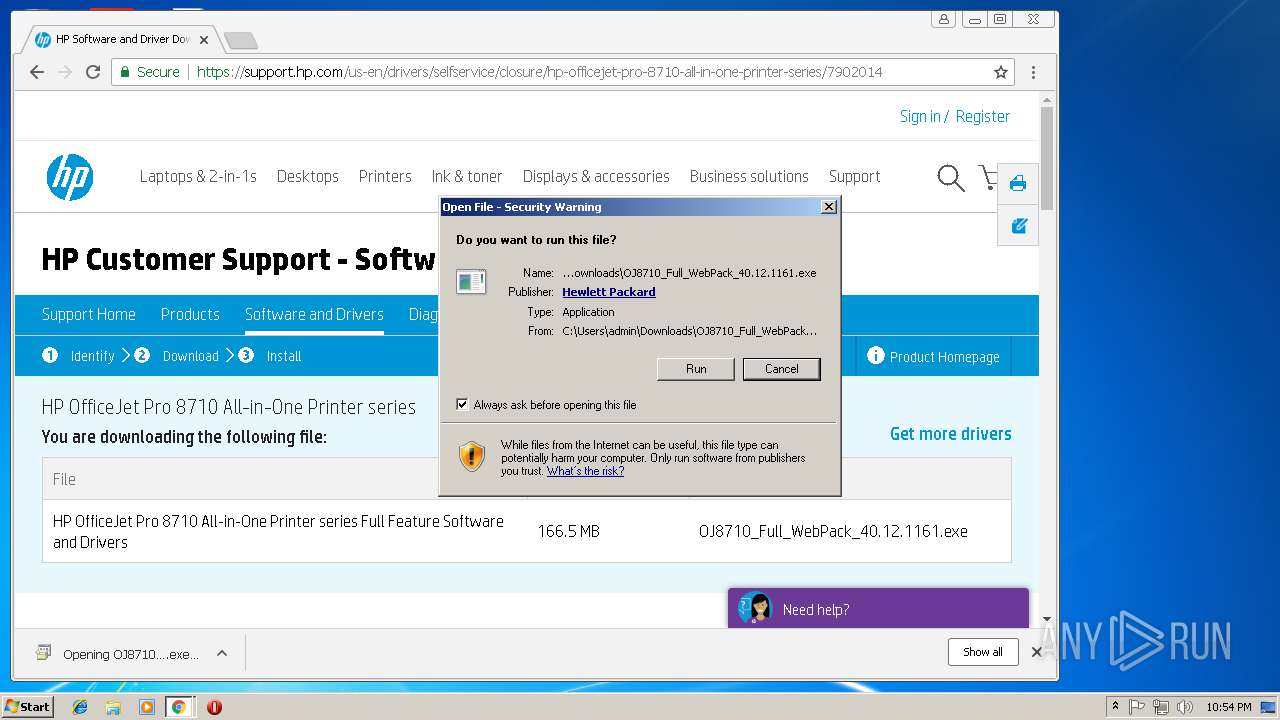
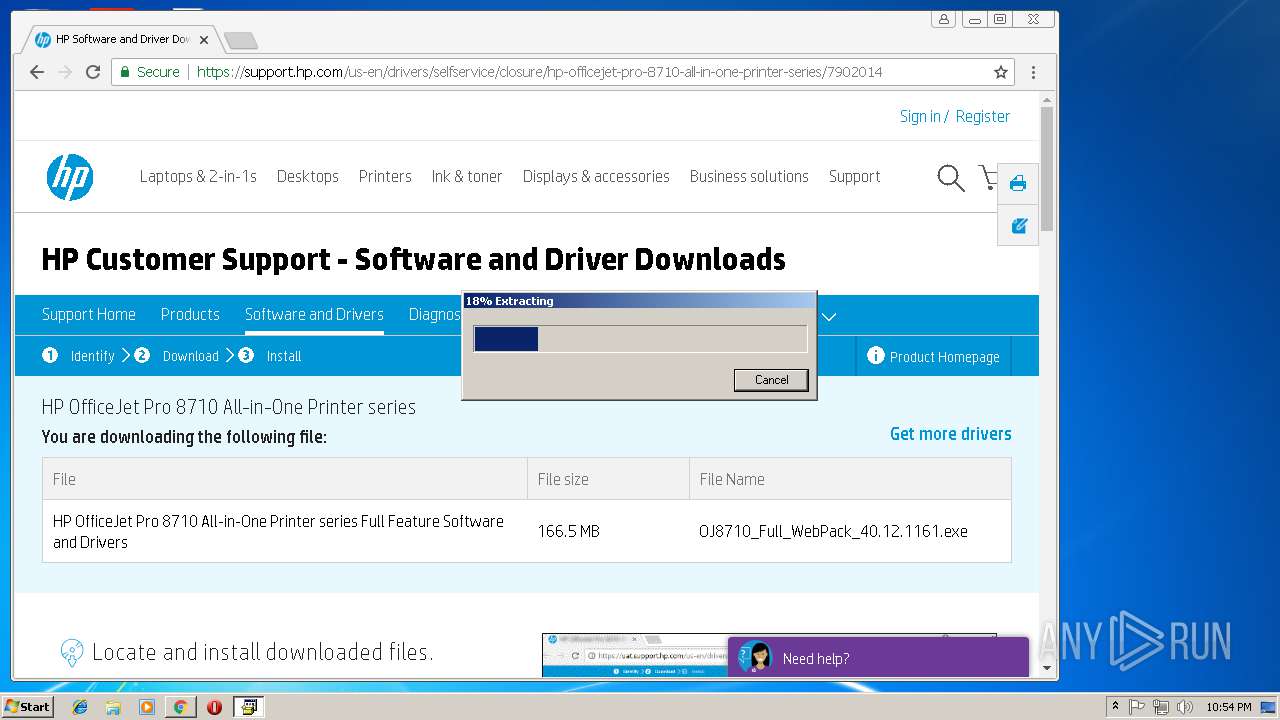
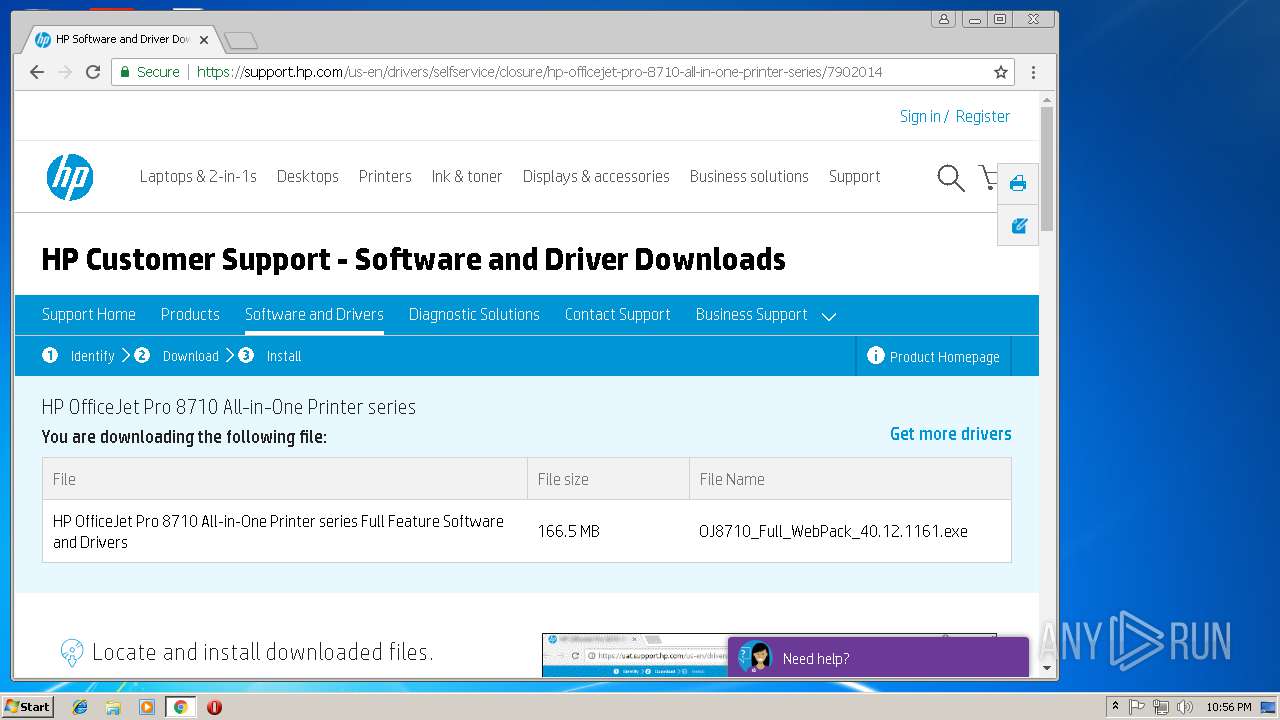
| URL: | https://support.hp.com/us-en/drivers/selfservice/hp-officejet-pro-8710-all-in-one-printer-series/7902014 |
| Full analysis: | https://app.any.run/tasks/1c90a358-8ed8-476f-b70d-447ca798d7ca |
| Verdict: | Malicious activity |
| Analysis date: | September 28, 2018, 21:52:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3439197DC328685629D35ACB45673AFF |
| SHA1: | 7C6861970A5AAAAD8FF49DF8A87202CDE8BA02BB |
| SHA256: | 9ABAF7E939961DE4810C26FF25D18DA3B660F7ACD5761AD7336BDB3435074406 |
| SSDEEP: | 3:N8dCBLNgrA+hGoVVIPK6JJIxXLgIWoNvI:2wBL6hGoAy6CMrT |
MALICIOUS
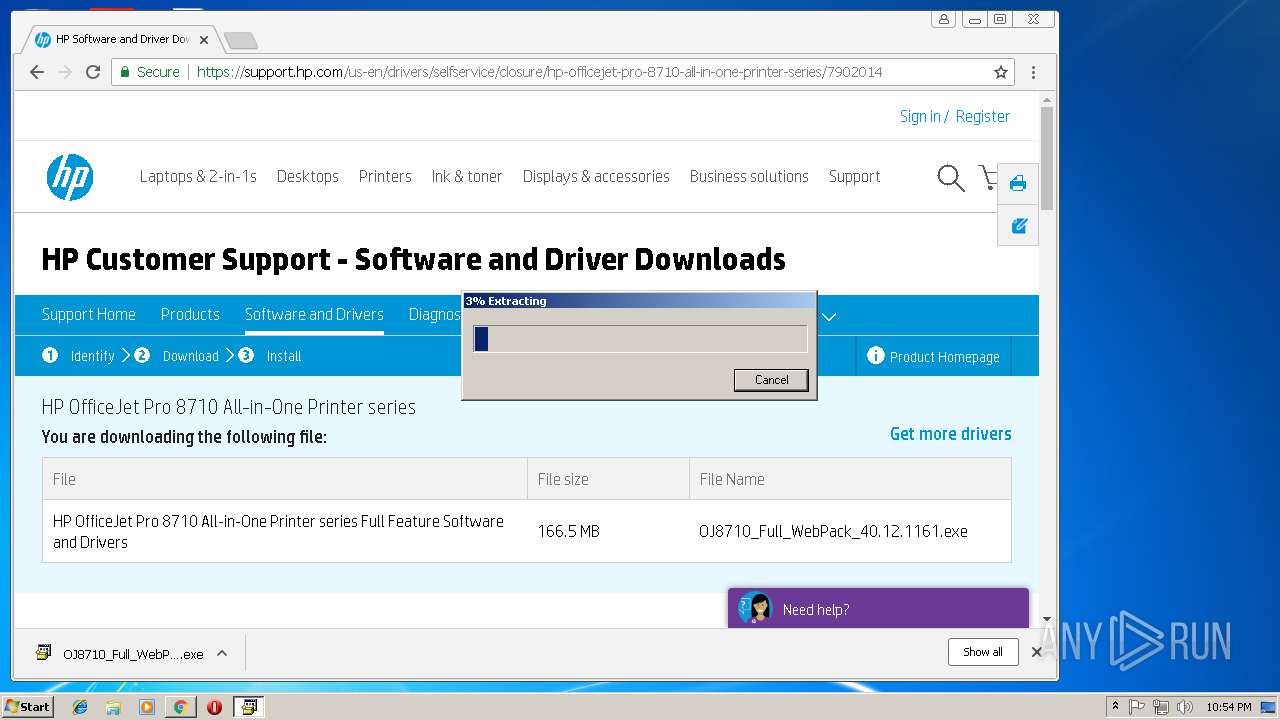
Application was dropped or rewritten from another process
- OJ8710_Full_WebPack_40.12.1161.exe (PID: 1428)
- HP-DQEX5.exe (PID: 1720)
- HP-DQEX5.exe (PID: 2920)
- Setup.exe (PID: 360)
- DeviceSetup.exe (PID: 3684)
- FaxPrinterUtility.exe (PID: 2412)
- HPScan.exe (PID: 3172)
- HPNETW~1.EXE (PID: 1772)
- HPNETW~1.EXE (PID: 3264)
Changes settings of System certificates
- HP-DQEX5.exe (PID: 2920)
Loads dropped or rewritten executable
- spoolsv.exe (PID: 1208)
- HPScan.exe (PID: 3172)
- wmiprvse.exe (PID: 3860)
- HP-DQEX5.exe (PID: 2920)
SUSPICIOUS
Adds / modifies Windows certificates
- HP-DQEX5.exe (PID: 2920)
Executable content was dropped or overwritten
- OJ8710_Full_WebPack_40.12.1161.exe (PID: 1428)
- chrome.exe (PID: 3336)
- msiexec.exe (PID: 2360)
- DrvInst.exe (PID: 2888)
- FaxPrinterUtility.exe (PID: 2412)
- MsiExec.exe (PID: 2268)
- spoolsv.exe (PID: 1208)
Creates files in the Windows directory
- msiexec.exe (PID: 2360)
- DrvInst.exe (PID: 2288)
- DrvInst.exe (PID: 2888)
- MsiExec.exe (PID: 2268)
- spoolsv.exe (PID: 1208)
- FaxPrinterUtility.exe (PID: 2412)
- DrvInst.exe (PID: 2488)
- wmiprvse.exe (PID: 3860)
- DrvInst.exe (PID: 3624)
Reads Internet Cache Settings
- HP-DQEX5.exe (PID: 2920)
Creates files in the program directory
- HP-DQEX5.exe (PID: 2920)
Creates files in the driver directory
- DrvInst.exe (PID: 2288)
- DrvInst.exe (PID: 2888)
- DrvInst.exe (PID: 3624)
- DrvInst.exe (PID: 2488)
Removes files from Windows directory
- DrvInst.exe (PID: 2288)
- DrvInst.exe (PID: 2888)
- DrvInst.exe (PID: 3624)
- DrvInst.exe (PID: 2488)
- spoolsv.exe (PID: 1208)
- FaxPrinterUtility.exe (PID: 2412)
Changes IE settings (feature browser emulation)
- msiexec.exe (PID: 2360)
INFO
Application launched itself
- iexplore.exe (PID: 2748)
- msiexec.exe (PID: 2360)
- chrome.exe (PID: 3336)
Reads internet explorer settings
- iexplore.exe (PID: 1152)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 1152)
- OJ8710_Full_WebPack_40.12.1161.exe (PID: 1428)
- msiexec.exe (PID: 2360)
- MsiExec.exe (PID: 2268)
Creates files in the user directory
- iexplore.exe (PID: 1152)
- iexplore.exe (PID: 2748)
Reads settings of System Certificates
- chrome.exe (PID: 3336)
- HP-DQEX5.exe (PID: 2920)
- iexplore.exe (PID: 2748)
- DeviceSetup.exe (PID: 3684)
Reads Internet Cache Settings
- iexplore.exe (PID: 1152)
- chrome.exe (PID: 3336)
Changes settings of System certificates
- chrome.exe (PID: 3336)
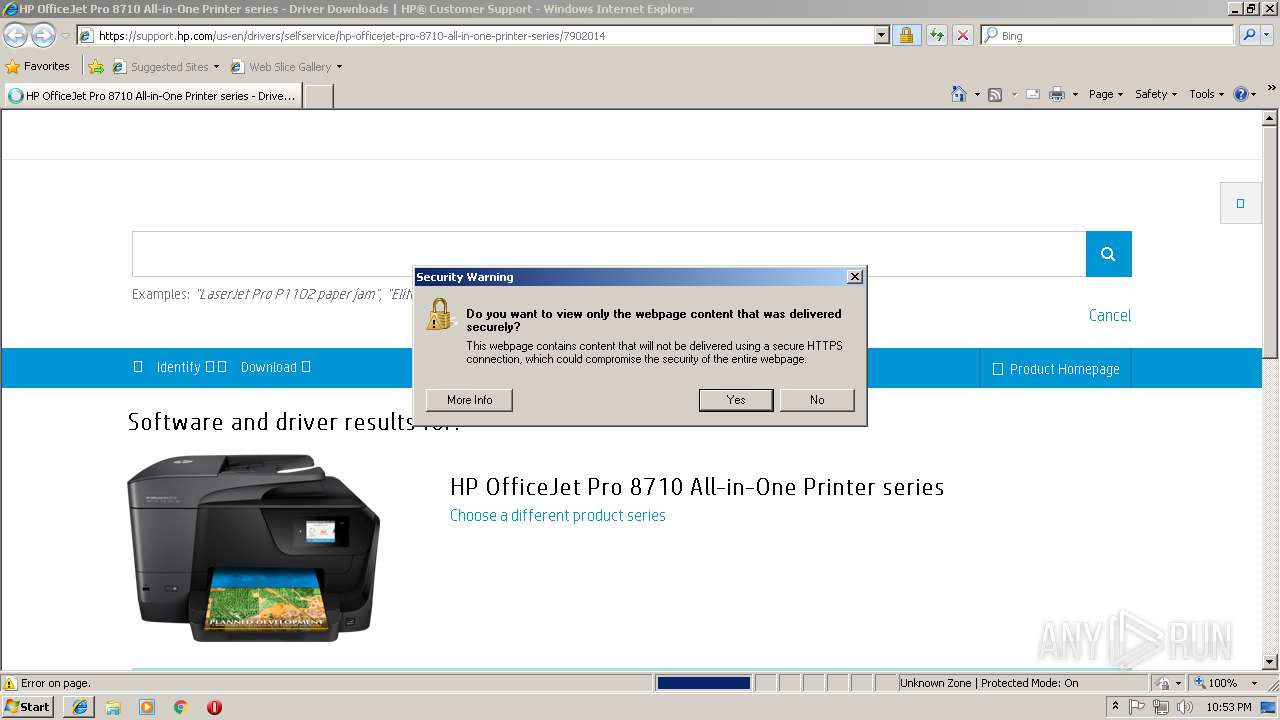
Changes internet zones settings
- iexplore.exe (PID: 2748)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2280)
- MsiExec.exe (PID: 2268)
Creates files in the program directory
- MsiExec.exe (PID: 2268)
- msiexec.exe (PID: 2360)
Creates a software uninstall entry
- msiexec.exe (PID: 2360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
79
Monitored processes
40
Malicious processes
9
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | "C:\Users\admin\AppData\Local\Temp\7zS39D9\Setup.exe" /webpack | C:\Users\admin\AppData\Local\Temp\7zS39D9\Setup.exe | — | OJ8710_Full_WebPack_40.12.1161.exe | |||||||||||
User: admin Company: HP Inc. Integrity Level: MEDIUM Description: SetupLauncher.exe Exit code: 0 Version: 040.012.1161.1896 Modules
| |||||||||||||||
| 544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=888,6411200431736039351,11084462334903377515,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=AF4429DD76FC78CE77ED5A29123EBEA3 --mojo-platform-channel-handle=876 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=888,6411200431736039351,11084462334903377515,131072 --enable-features=PasswordImport --service-pipe-token=16A17462A503D023554E547FE1102A61 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16A17462A503D023554E547FE1102A61 --renderer-client-id=3 --mojo-platform-channel-handle=2076 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=888,6411200431736039351,11084462334903377515,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=A40FBFAA23E293F133BBD081F8E5D576 --mojo-platform-channel-handle=2664 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2748 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1208 | C:\Windows\System32\spoolsv.exe | C:\Windows\System32\spoolsv.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Spooler SubSystem App Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=888,6411200431736039351,11084462334903377515,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=099FA033FD46C90F43277B86ADA00FFB --mojo-platform-channel-handle=4360 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1428 | "C:\Users\admin\Downloads\OJ8710_Full_WebPack_40.12.1161.exe" | C:\Users\admin\Downloads\OJ8710_Full_WebPack_40.12.1161.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=888,6411200431736039351,11084462334903377515,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=A3E8C893C8AF2C64CF847DDA9679BFA3 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=A3E8C893C8AF2C64CF847DDA9679BFA3 --renderer-client-id=16 --mojo-platform-channel-handle=5548 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1720 | "C:\Users\admin\AppData\Local\Temp\7zS39D9\HP-DQEX5.exe" /user "PC\admin" /webpack | C:\Users\admin\AppData\Local\Temp\7zS39D9\HP-DQEX5.exe | — | Setup.exe | |||||||||||
User: admin Company: HP Inc. Integrity Level: MEDIUM Description: HP-DQEX5.exe Exit code: 3221226540 Version: 040.012.1161.1896 Modules
| |||||||||||||||
Total events
5 338
Read events
2 817
Write events
2 465
Delete events
56
Modification events
| (PID) Process: | (2748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000068000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {C37D72D9-C368-11E8-BFAB-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (2748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E207090005001C001500340011007D00 | |||
Executable files
218
Suspicious files
463
Text files
897
Unknown types
157
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2748 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\D2YPIJ90\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2748 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\7902014[1].txt | — | |
MD5:— | SHA256:— | |||
| 1152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\ra_collection[1].txt | text | |
MD5:— | SHA256:— | |||
| 1152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\mashup_ra_collection[1].txt | text | |
MD5:— | SHA256:— | |||
| 1152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\mashup_ra_collection[2].txt | text | |
MD5:— | SHA256:— | |||
| 1152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 1152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\10425806409[1].js | html | |
MD5:— | SHA256:— | |||
| 1152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U2ZG9DE0\themesOverride[1].css | text | |
MD5:— | SHA256:— | |||
| 1152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\stylesheet[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
154
DNS requests
74
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3336 | chrome.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
3336 | chrome.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
3336 | chrome.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
3336 | chrome.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 53.8 Kb | whitelisted |
3336 | chrome.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 53.8 Kb | whitelisted |
3336 | chrome.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 53.8 Kb | whitelisted |
3336 | chrome.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 53.8 Kb | whitelisted |
3336 | chrome.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 53.8 Kb | whitelisted |
3336 | chrome.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
3336 | chrome.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2748 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1152 | iexplore.exe | 209.197.3.15:443 | netdna.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
1152 | iexplore.exe | 23.67.131.110:443 | support.hp.com | Akamai International B.V. | NL | whitelisted |
1152 | iexplore.exe | 34.230.106.70:443 | nexus.ensighten.com | Amazon.com, Inc. | US | unknown |
1152 | iexplore.exe | 23.45.97.153:443 | ssl-product-images.www8-hp.com | Akamai International B.V. | NL | whitelisted |
1152 | iexplore.exe | 104.19.197.151:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | shared |
1152 | iexplore.exe | 2.19.34.83:443 | cdn.optimizely.com | Akamai International B.V. | — | whitelisted |
1152 | iexplore.exe | 74.125.71.82:443 | html5shiv.googlecode.com | Google Inc. | US | whitelisted |
1152 | iexplore.exe | 104.108.65.2:443 | ssl.www8.hp.com | Akamai Technologies, Inc. | NL | whitelisted |
1152 | iexplore.exe | 104.108.65.2:80 | ssl.www8.hp.com | Akamai Technologies, Inc. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
support.hp.com |
| whitelisted |
cdn.optimizely.com |
| whitelisted |
html5shiv.googlecode.com |
| whitelisted |
netdna.bootstrapcdn.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
ssl.www8.hp.com |
| whitelisted |
nexus.ensighten.com |
| whitelisted |
ssl-product-images.www8-hp.com |
| unknown |
www8.hp.com |
| whitelisted |
Threats
Process | Message |
|---|---|
spoolsv.exe | 2018/09/28 22:55:33 [1208] {tid: 0x0A70} (++) |
spoolsv.exe | Module File Name: C:\Windows\System32\spoolsv.exe (317440 bytes) |
spoolsv.exe | |
spoolsv.exe | 2018/09/28 22:55:33 [1208] {tid: 0x0A70} (++) |
spoolsv.exe | Command Line: C:\Windows\System32\spoolsv.exe |
spoolsv.exe | |
spoolsv.exe | 2018/09/28 22:55:33 [1208] {tid: 0x0A70} (++) |
spoolsv.exe | File Version: 6.1.7600.16385 (win7_rtm.090713-1255) |
spoolsv.exe | |
spoolsv.exe | 2018/09/28 22:55:33 [1208] {tid: 0x0A70} (++) |