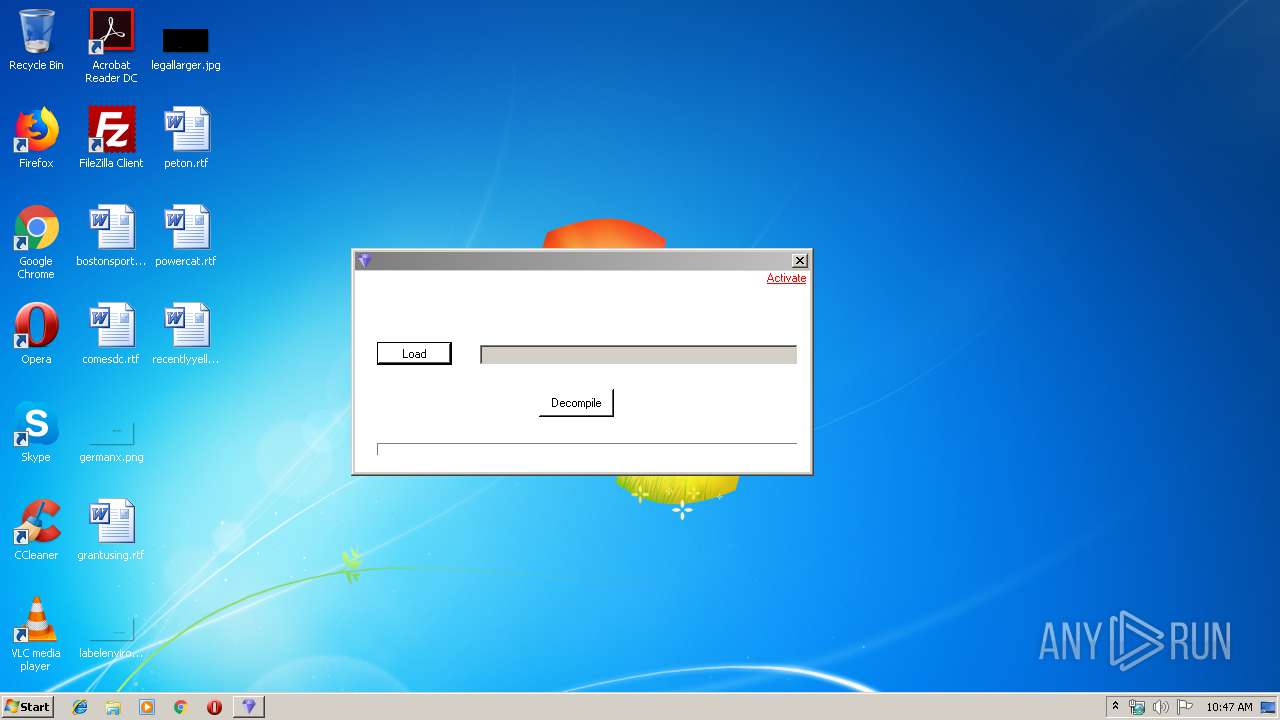
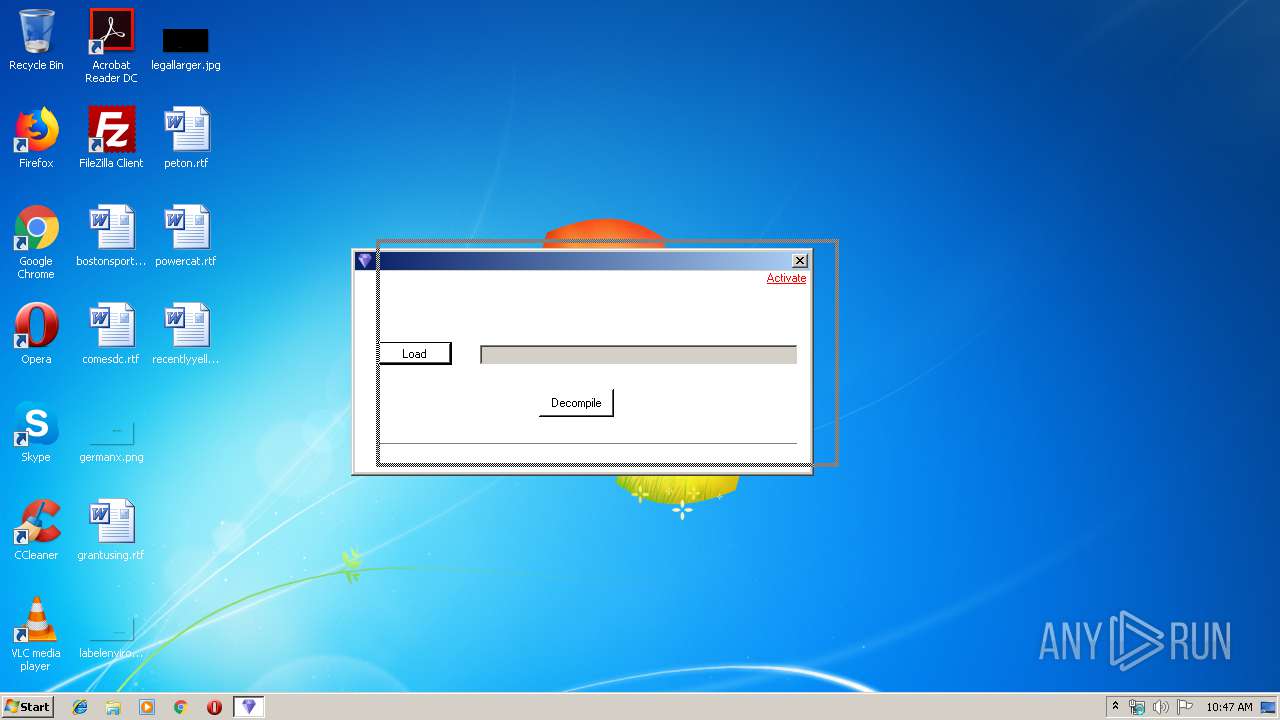
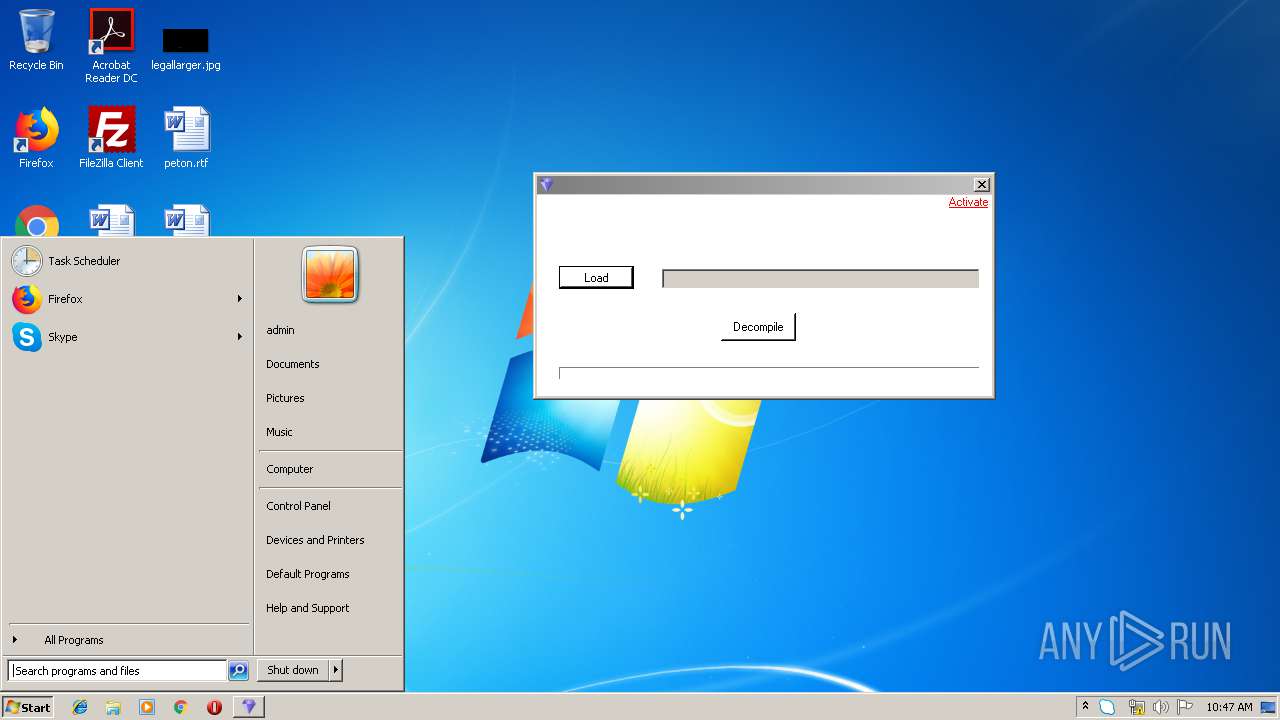
| File name: | archer ex4 to mq4 2019.exe |
| Full analysis: | https://app.any.run/tasks/df39c296-67c1-4bd0-9c28-b73efa14bf7b |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 09:46:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 3FC71DDB473F6EA79940D0B4FAFEA89A |
| SHA1: | 3A857695E25738FED54BE7A59B77FDB3419F9909 |
| SHA256: | 9A93BEBD4001F5C5C3F3C7245503B9CF03ABDA769C0B8E60377A1B1500B4AA1A |
| SSDEEP: | 3072:v4mSpdD61s4mSpdD61KgOarss4mSpFD61:k/W/zg6r |
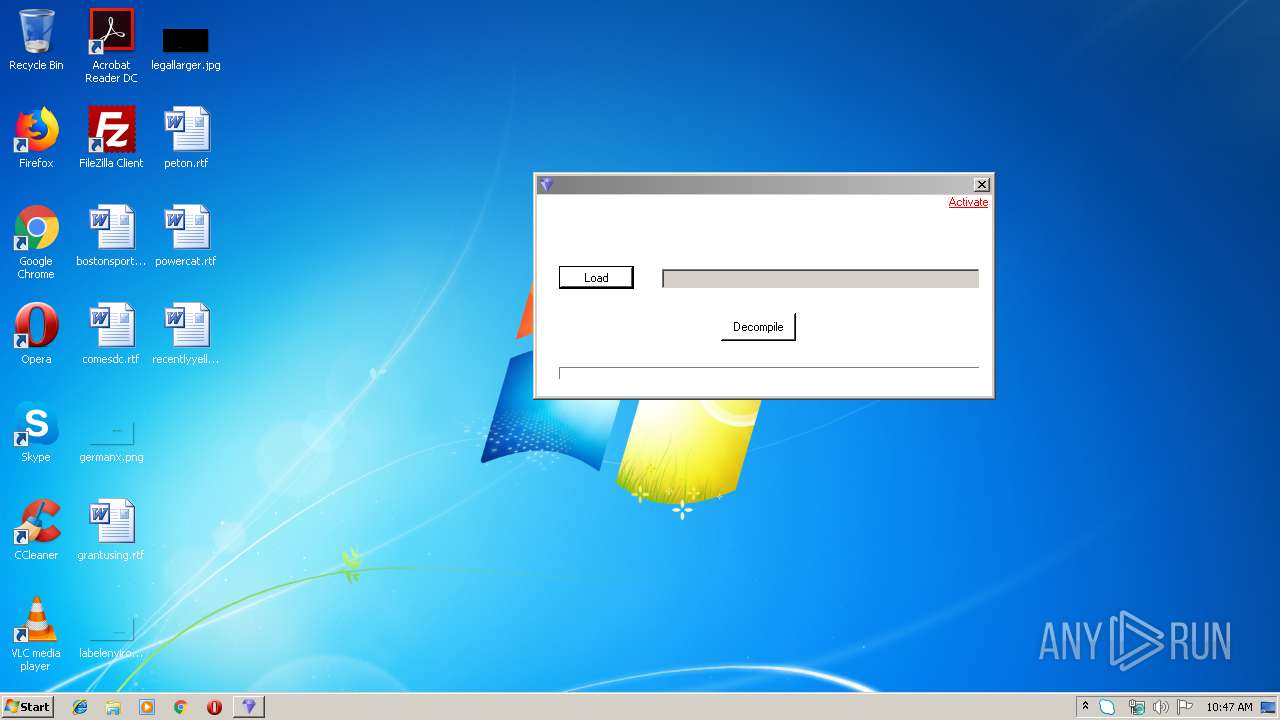
MALICIOUS
Changes the autorun value in the registry
- reg.exe (PID: 3884)
SUSPICIOUS
Creates files in the user directory
- Skype.exe (PID: 3672)
- Skype.exe (PID: 4088)
- Skype.exe (PID: 2556)
Uses REG.EXE to modify Windows registry
- Skype.exe (PID: 3672)
Reads CPU info
- Skype.exe (PID: 3672)
Modifies the open verb of a shell class
- Skype.exe (PID: 3672)
Application launched itself
- Skype.exe (PID: 4088)
- Skype.exe (PID: 2556)
- Skype.exe (PID: 3672)
INFO
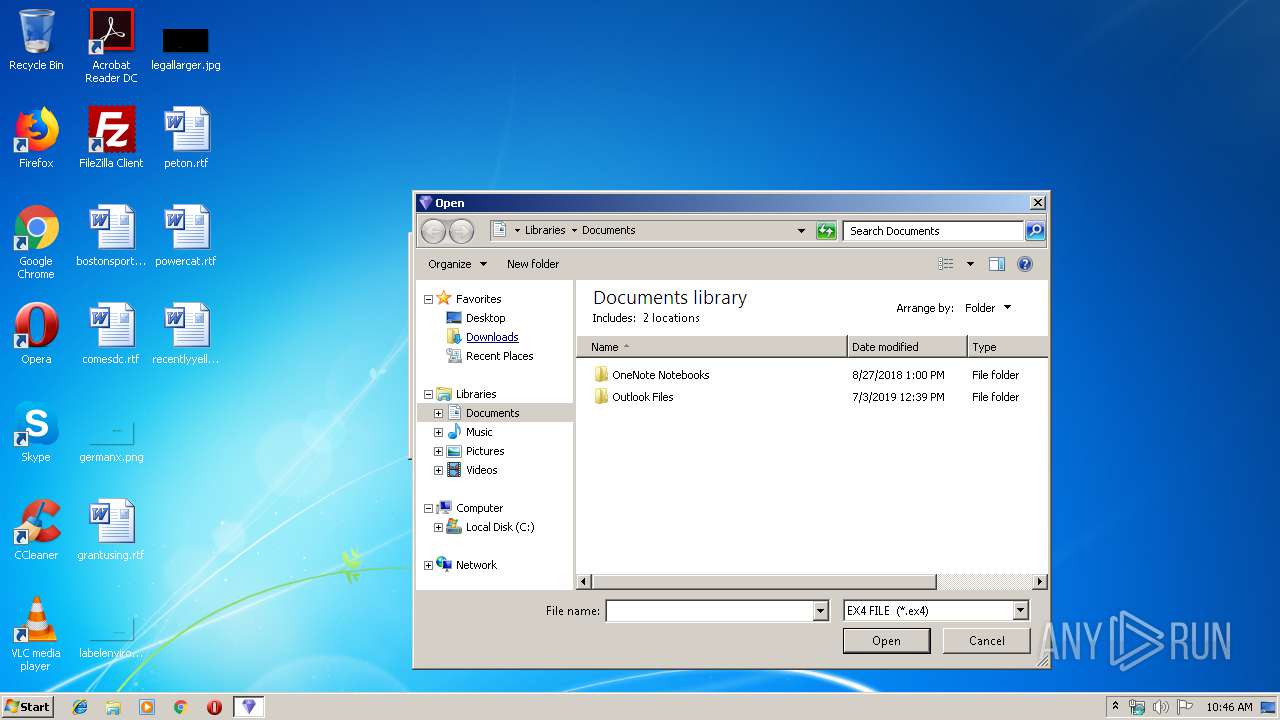
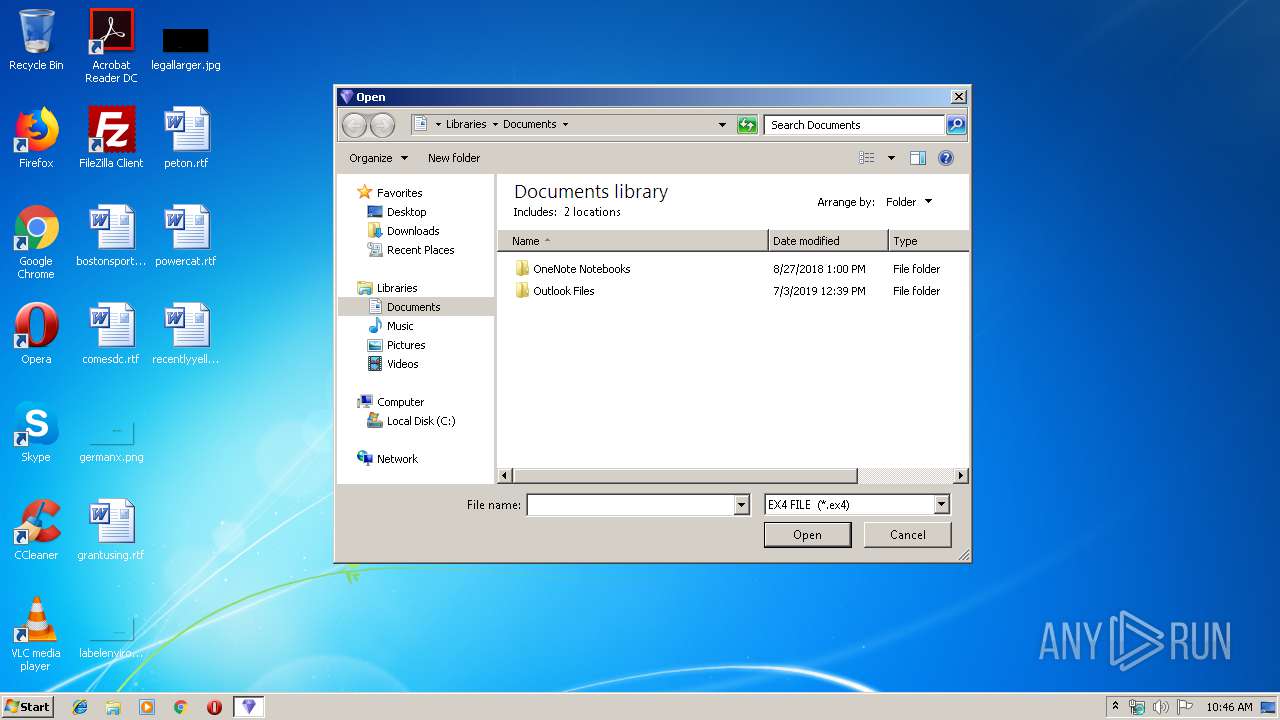
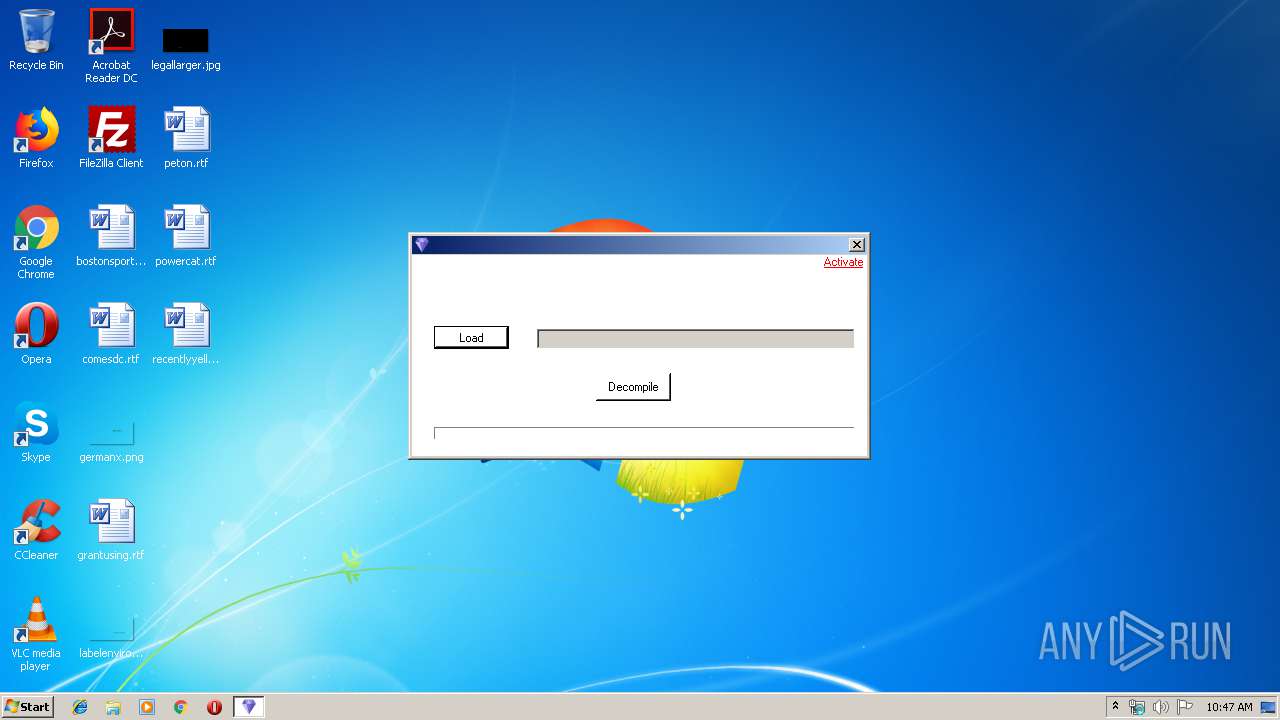
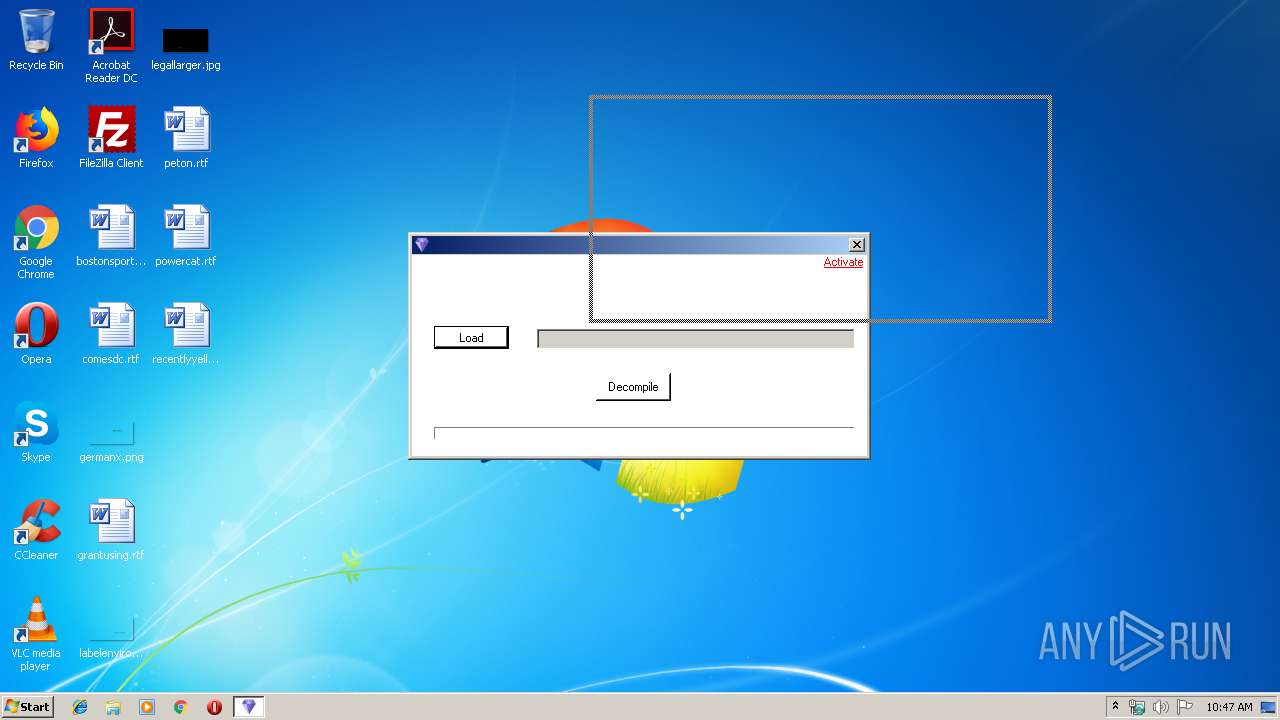
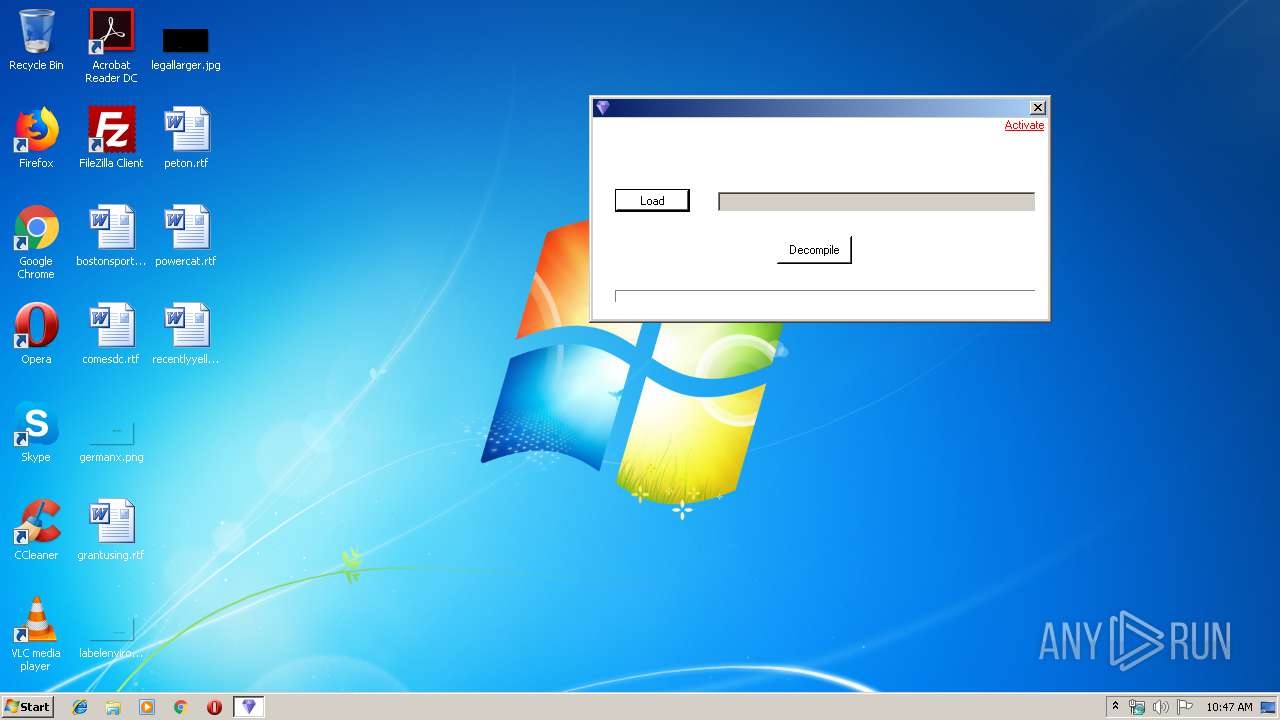
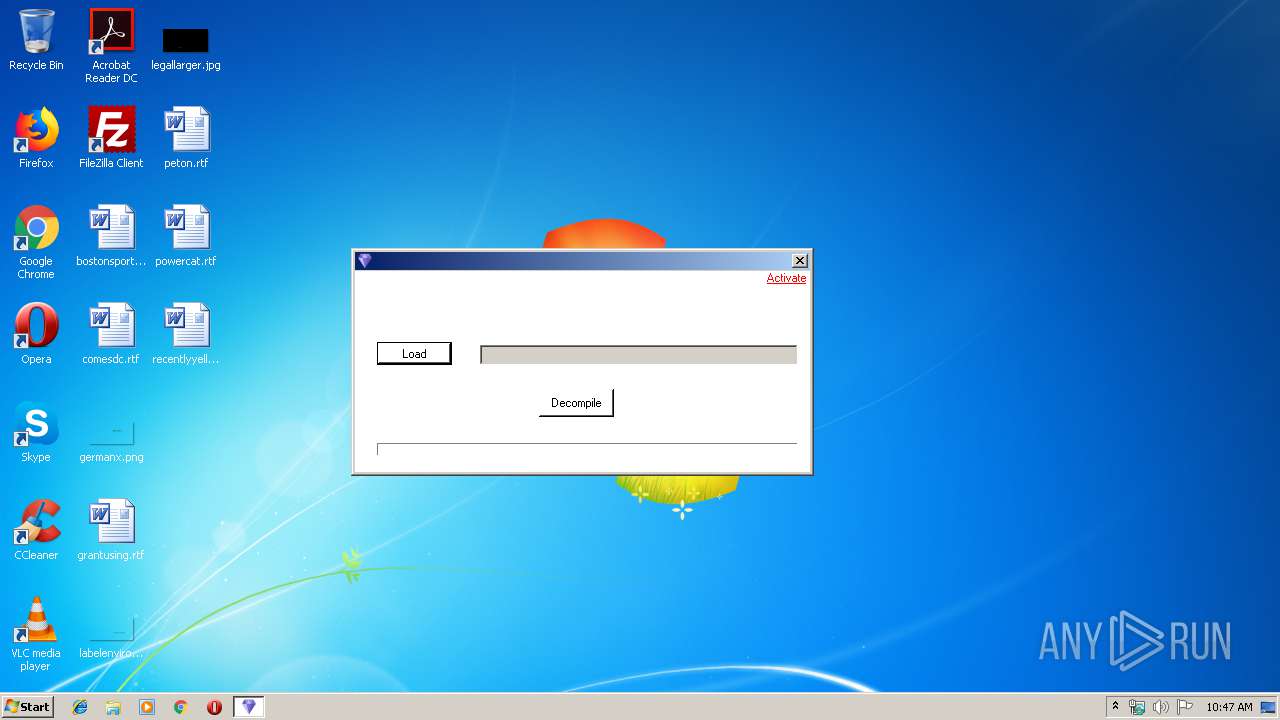
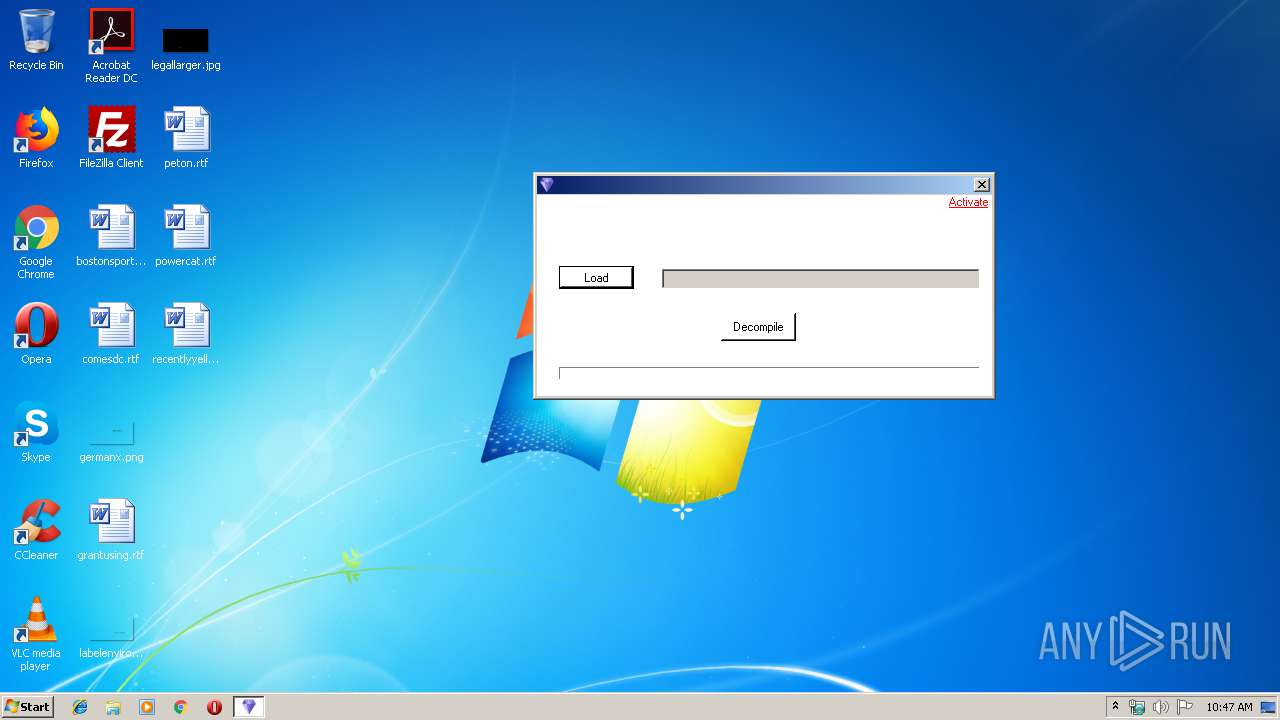
Manual execution by user
- Skype.exe (PID: 3672)
Reads settings of System Certificates
- Skype.exe (PID: 3672)
Dropped object may contain Bitcoin addresses
- Skype.exe (PID: 3672)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (55.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21) |
| .scr | | | Windows screen saver (9.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:03:13 18:29:26+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 368640 |
| InitializedDataSize: | 173568 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5befe |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
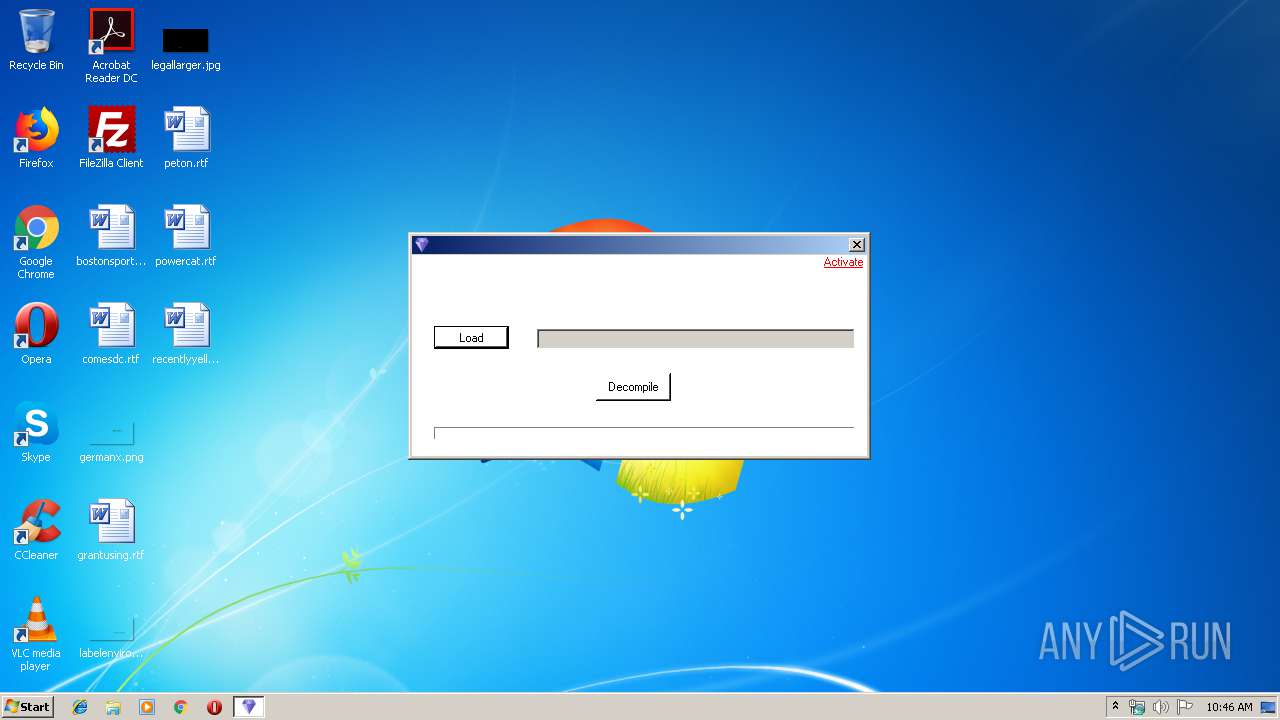
| FileDescription: | ex4 to mq4 2019 |
| FileVersion: | 1.0.0.0 |
| InternalName: | archer 2019.exe |
| LegalCopyright: | Copyright © 2019 |
| OriginalFileName: | archer 2019.exe |
| ProductName: | Archer Royston ex4 to mq4 |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Mar-2019 17:29:26 |
| Debug artifacts: |
|
| FileDescription: | ex4 to mq4 2019 |
| FileVersion: | 1.0.0.0 |
| InternalName: | archer 2019.exe |
| LegalCopyright: | Copyright © 2019 |
| OriginalFilename: | archer 2019.exe |
| ProductName: | Archer Royston ex4 to mq4 |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 13-Mar-2019 17:29:26 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00059F04 | 0x0005A000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.15635 |
.sdata | 0x0005C000 | 0x000000A4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.37929 |
.rsrc | 0x0005E000 | 0x0002A0B0 | 0x0002A200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.88016 |
.reloc | 0x0008A000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.3289 | 740 | UNKNOWN | UNKNOWN | RT_VERSION |
2 | 7.87708 | 8981 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 2.97912 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.51739 | 38056 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 3.50694 | 21640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 3.27185 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 3.84126 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 3.82279 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 4.43217 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
10 | 4.68448 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
mscoree.dll |
Total processes
46
Monitored processes
9
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 936 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | Skype.exe | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
| 2172 | C:\Windows\system32\reg.exe QUERY HKCU\Software\Microsoft\Skype /v RestartForUpdate | C:\Windows\system32\reg.exe | — | Skype.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2556 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --type=renderer --ms-disable-indexeddb-transaction-timeout --no-sandbox --service-pipe-token=0107DF61692AAEF600CF2D686083CD57 --lang=en-US --app-user-model-id=Microsoft.Skype.SkypeDesktop --app-path="C:\Program Files\Microsoft\Skype for Desktop\resources\app.asar" --node-integration=false --webview-tag=true --no-sandbox --preload="C:\Program Files\Microsoft\Skype for Desktop\resources\app.asar\Preload.js" --context-id=1 --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=0107DF61692AAEF600CF2D686083CD57 --renderer-client-id=4 --mojo-platform-channel-handle=2616 /prefetch:1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | — | Skype.exe | |||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
| 3568 | "C:\Users\admin\AppData\Local\Temp\archer ex4 to mq4 2019.exe" | C:\Users\admin\AppData\Local\Temp\archer ex4 to mq4 2019.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: ex4 to mq4 2019 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3656 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | Skype.exe | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 2 Version: 8.29.0.50 Modules
| |||||||||||||||
| 3672 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | explorer.exe | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
| 3884 | C:\Windows\system32\reg.exe ADD HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v "Skype for Desktop" /t REG_SZ /d "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" /f | C:\Windows\system32\reg.exe | Skype.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3948 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | Skype.exe | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 2 Version: 8.29.0.50 Modules
| |||||||||||||||
| 4088 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --type=renderer --ms-disable-indexeddb-transaction-timeout --no-sandbox --service-pipe-token=4EA8DD90806F4142E4B2DE8458B0A18F --lang=en-US --app-user-model-id=Microsoft.Skype.SkypeDesktop --app-path="C:\Program Files\Microsoft\Skype for Desktop\resources\app.asar" --node-integration=false --webview-tag=true --no-sandbox --preload="C:\Program Files\Microsoft\Skype for Desktop\resources\app.asar\Preload.js" --context-id=2 --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=4EA8DD90806F4142E4B2DE8458B0A18F --renderer-client-id=3 --mojo-platform-channel-handle=1536 /prefetch:1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | — | Skype.exe | |||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
Total events
700
Read events
658
Write events
41
Delete events
1
Modification events
| (PID) Process: | (3568) archer ex4 to mq4 2019.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3568) archer ex4 to mq4 2019.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0200000001000000000000000700000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3568) archer ex4 to mq4 2019.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (3568) archer ex4 to mq4 2019.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (3568) archer ex4 to mq4 2019.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (3568) archer ex4 to mq4 2019.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3568) archer ex4 to mq4 2019.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | 1 |
Value: 6100720063006800650072002000650078003400200074006F0020006D0071003400200032003000310039002E0065007800650000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000004D01000054000000CD03000034020000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (3568) archer ex4 to mq4 2019.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | delete value | Name: | 1 |
Value: 6100720063006800650072002000650078003400200074006F0020006D0071003400200032003000310039002E0065007800650000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000004D01000054000000CD03000034020000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (3568) archer ex4 to mq4 2019.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | 1 |
Value: 6100720063006800650072002000650078003400200074006F0020006D0071003400200032003000310039002E0065007800650000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000098010000E800000067030000CC010000000000000000000000000000000000004D01000054000000CD03000034020000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (3568) archer ex4 to mq4 2019.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0100000000000000FFFFFFFF | |||
Executable files
0
Suspicious files
5
Text files
16
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3672 | Skype.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\Y0STSPEZ61JPC7Z39QJQ.temp | — | |
MD5:— | SHA256:— | |||
| 4088 | Skype.exe | C:\Users\admin\AppData\Roaming\Microsoft\Skype for Desktop\skylib\slimcore-0-3819446762.blog | — | |
MD5:— | SHA256:— | |||
| 3672 | Skype.exe | C:\Users\admin\AppData\Roaming\Microsoft\Skype for Desktop\ecscache.json | text | |
MD5:— | SHA256:— | |||
| 3672 | Skype.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\b916037c1e115fe0.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3672 | Skype.exe | C:\Users\admin\AppData\Roaming\Microsoft\Skype for Desktop\IndexedDB\file__0.indexeddb.leveldb\000003.log | binary | |
MD5:— | SHA256:— | |||
| 3672 | Skype.exe | C:\Users\admin\AppData\Roaming\Microsoft\Skype for Desktop\Local Storage\leveldb\LOG.old~RF186d99.TMP | text | |
MD5:7F39B22308B34B4138A09991EC4D41C5 | SHA256:31C4D714AFBFAB8D23AE08F061F6A5F1E46A26B0AB20795EAC7D2134A55CCEB6 | |||
| 3672 | Skype.exe | C:\Users\admin\AppData\Roaming\Microsoft\Skype for Desktop\Local Storage\leveldb\LOG.old | text | |
MD5:7F39B22308B34B4138A09991EC4D41C5 | SHA256:31C4D714AFBFAB8D23AE08F061F6A5F1E46A26B0AB20795EAC7D2134A55CCEB6 | |||
| 3672 | Skype.exe | C:\Users\admin\AppData\Roaming\Microsoft\Skype for Desktop\Cache\f_000005 | compressed | |
MD5:— | SHA256:— | |||
| 3948 | Skype.exe | C:\Users\admin\AppData\Local\Temp\skype-preview Crashes\operation_log.txt | text | |
MD5:— | SHA256:— | |||
| 2556 | Skype.exe | C:\Users\admin\AppData\Roaming\Microsoft\Skype for Desktop\skylib\slimcore-1-2147483647.blog | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
7
DNS requests
7
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3672 | Skype.exe | 13.90.95.57:443 | get.skype.com | Microsoft Corporation | US | whitelisted |
3672 | Skype.exe | 13.107.3.128:443 | a.config.skype.com | Microsoft Corporation | US | whitelisted |
3672 | Skype.exe | 52.114.128.9:443 | pipe.skype.com | Microsoft Corporation | US | whitelisted |
3672 | Skype.exe | 2.18.233.81:443 | download.skype.com | Akamai International B.V. | — | whitelisted |
3672 | Skype.exe | 172.217.18.106:443 | www.googleapis.com | Google Inc. | US | whitelisted |
3672 | Skype.exe | 40.79.33.178:443 | avatar.skype.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
get.skype.com |
| whitelisted |
a.config.skype.com |
| whitelisted |
pipe.skype.com |
| whitelisted |
download.skype.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
avatar.skype.com |
| whitelisted |
config.edge.skype.com |
| malicious |
Threats
Process | Message |
|---|---|
Skype.exe | [936:2924:0717/104724.772:VERBOSE1:crash_service_main.cc(78)] Session start. cmdline is [--reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1]
|
Skype.exe | [936:2924:0717/104724.772:VERBOSE1:crash_service.cc(145)] window handle is 000301E0
|
Skype.exe | [936:2924:0717/104724.772:VERBOSE1:crash_service.cc(300)] pipe name is \\.\pipe\skype-preview Crash Service
dumps at C:\Users\admin\AppData\Local\Temp\skype-preview Crashes
|
Skype.exe | [936:2924:0717/104724.772:VERBOSE1:crash_service.cc(304)] checkpoint is C:\Users\admin\AppData\Local\Temp\skype-preview Crashes\crash_checkpoint.txt
server is https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload
maximum 128 reports/day
reporter is electron-crash-service
|
Skype.exe | [936:2924:0717/104724.772:VERBOSE1:crash_service_main.cc(94)] Ready to process crash requests
|
Skype.exe | [936:2668:0717/104724.772:VERBOSE1:crash_service.cc(333)] client start. pid = 3672
|
Skype.exe | [936:2668:0717/104726.582:VERBOSE1:crash_service.cc(333)] client start. pid = 4088
|
Skype.exe | [3656:3644:0717/104726.757:VERBOSE1:crash_service_main.cc(78)] Session start. cmdline is [--reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1]
|
Skype.exe | [3656:3644:0717/104726.758:VERBOSE1:crash_service.cc(145)] window handle is 00050172
|
Skype.exe | [3656:3644:0717/104726.758:VERBOSE1:crash_service.cc(300)] pipe name is \\.\pipe\skype-preview Crash Service
dumps at C:\Users\admin\AppData\Local\Temp\skype-preview Crashes
|