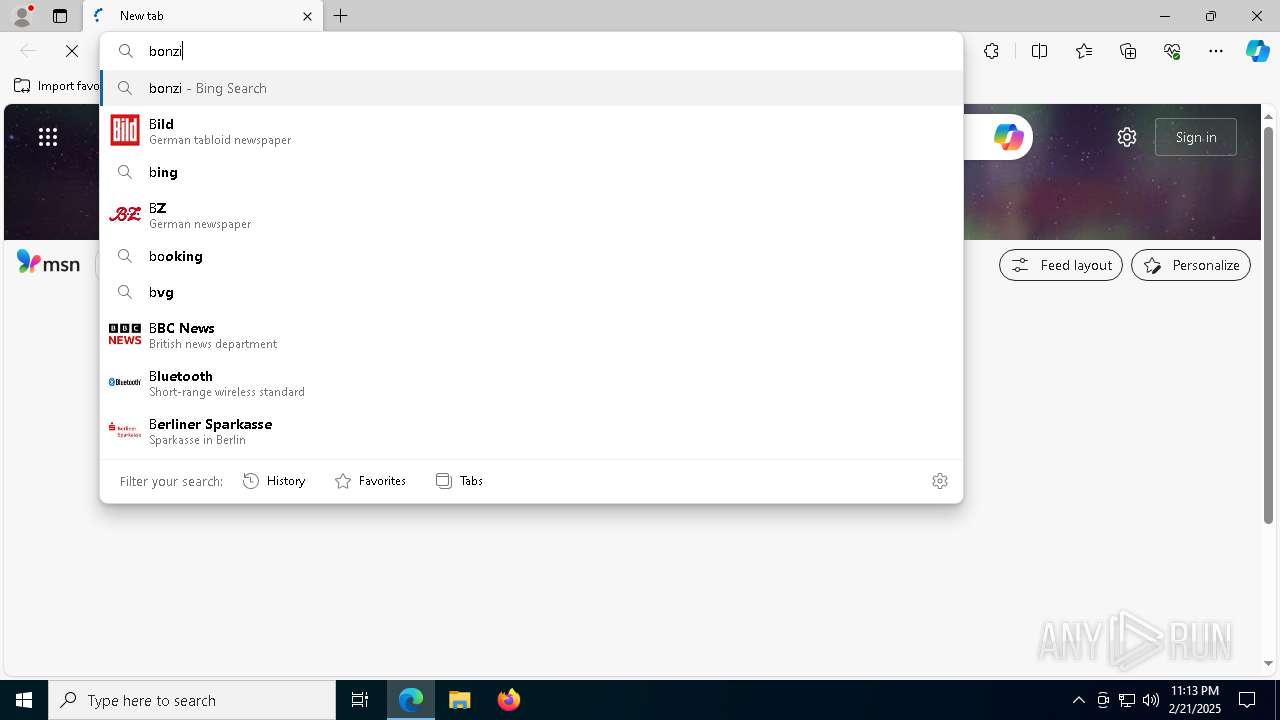
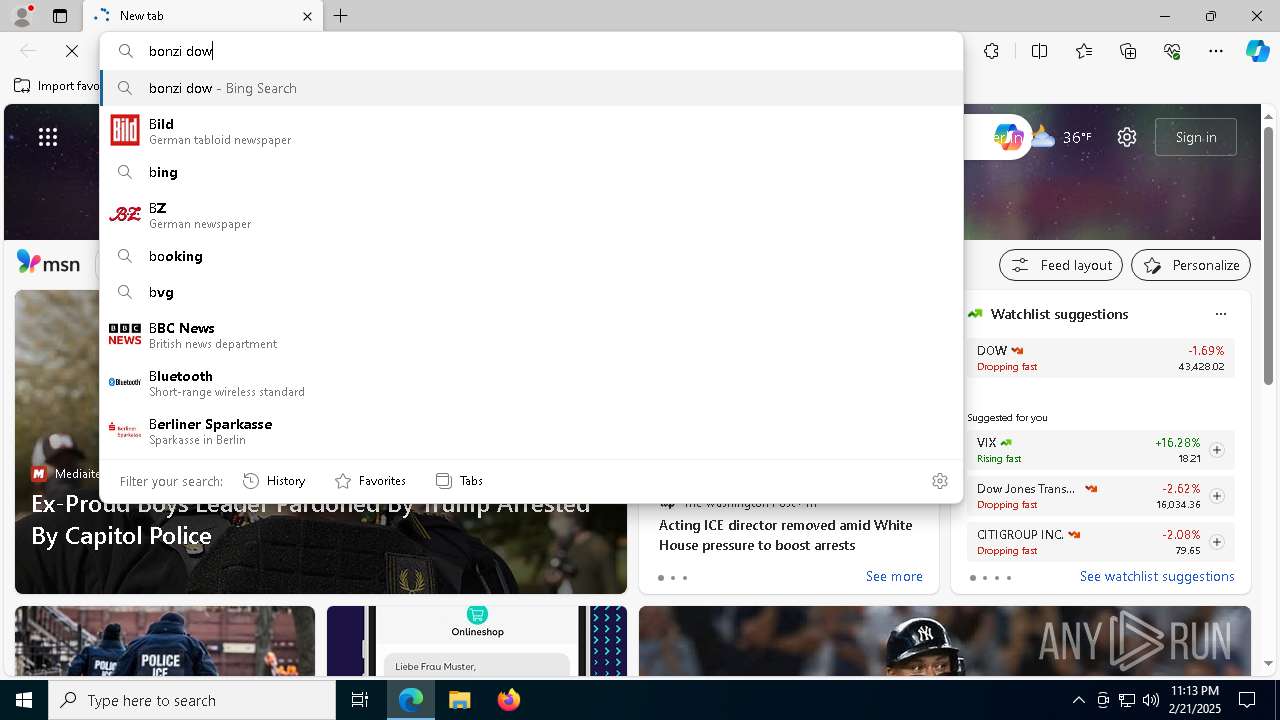
| URL: | https://tubebot.xyz/ |
| Full analysis: | https://app.any.run/tasks/26d71538-4125-4a43-8f6a-af9c0bbe1315 |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2025, 23:13:09 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E12153740EF9C318CBE190782EAEAFFD |
| SHA1: | 6CBB1E7C162FD963EF324F4BD2D1BB3E8A1EE8A8 |
| SHA256: | 9A6E3EDA807137ED110ED84476662EBAFE3C187AB3F6C85D46EE84F0E6EB2266 |
| SSDEEP: | 3:N8YfpF:2YfL |
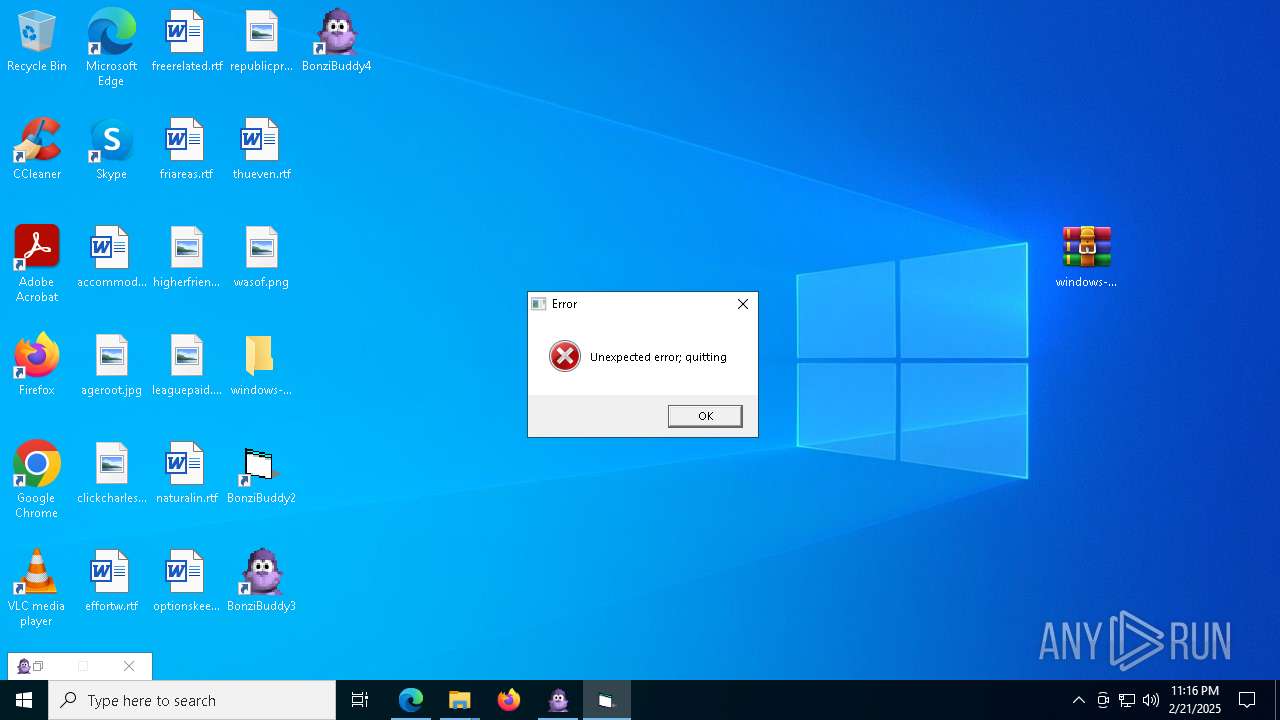
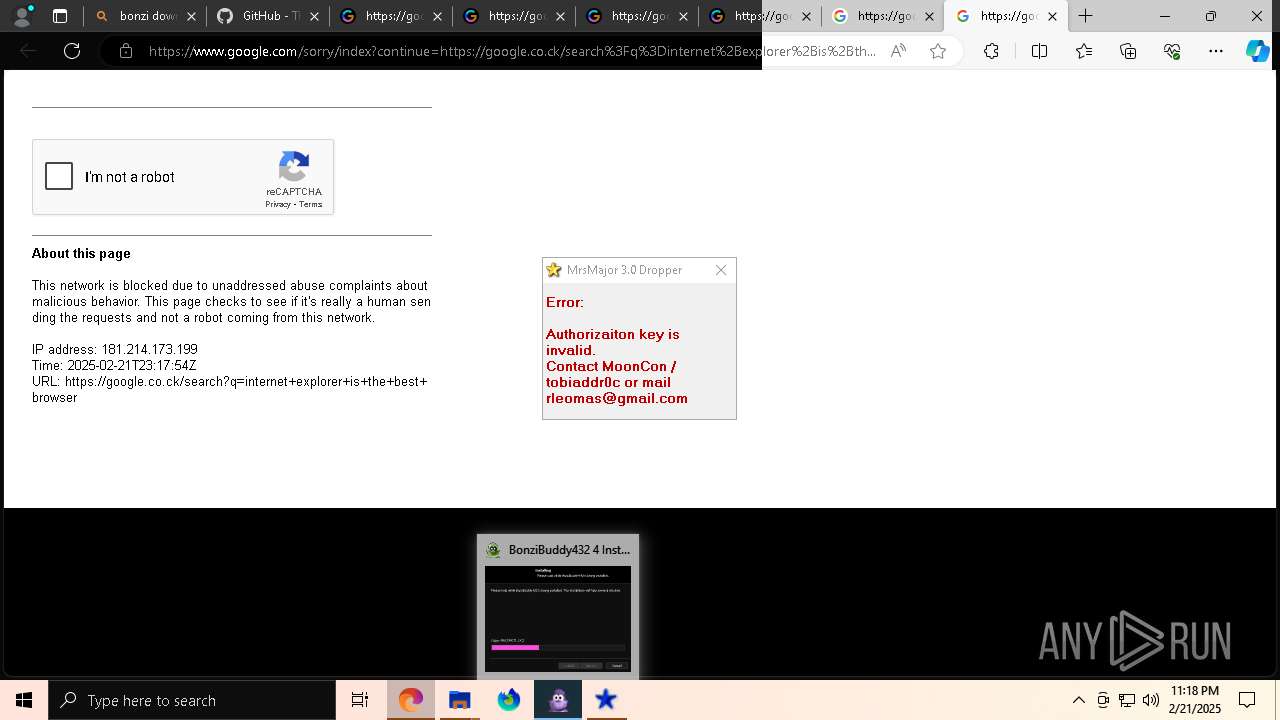
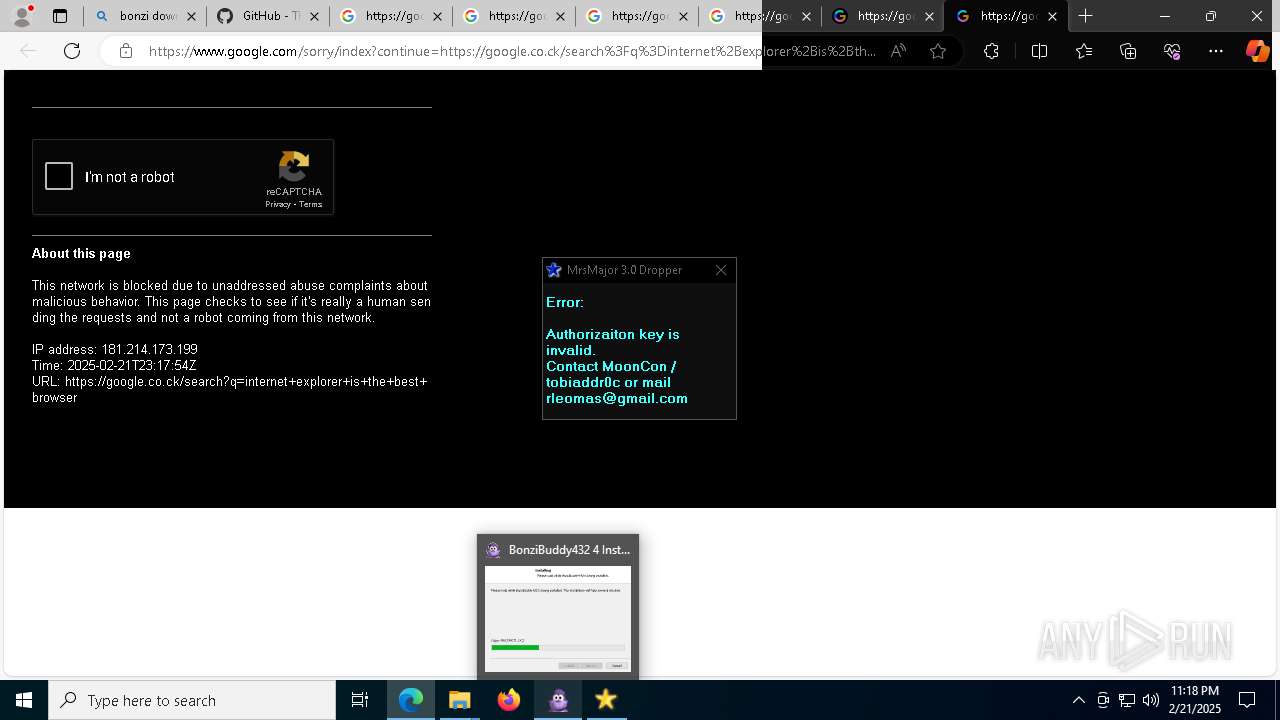
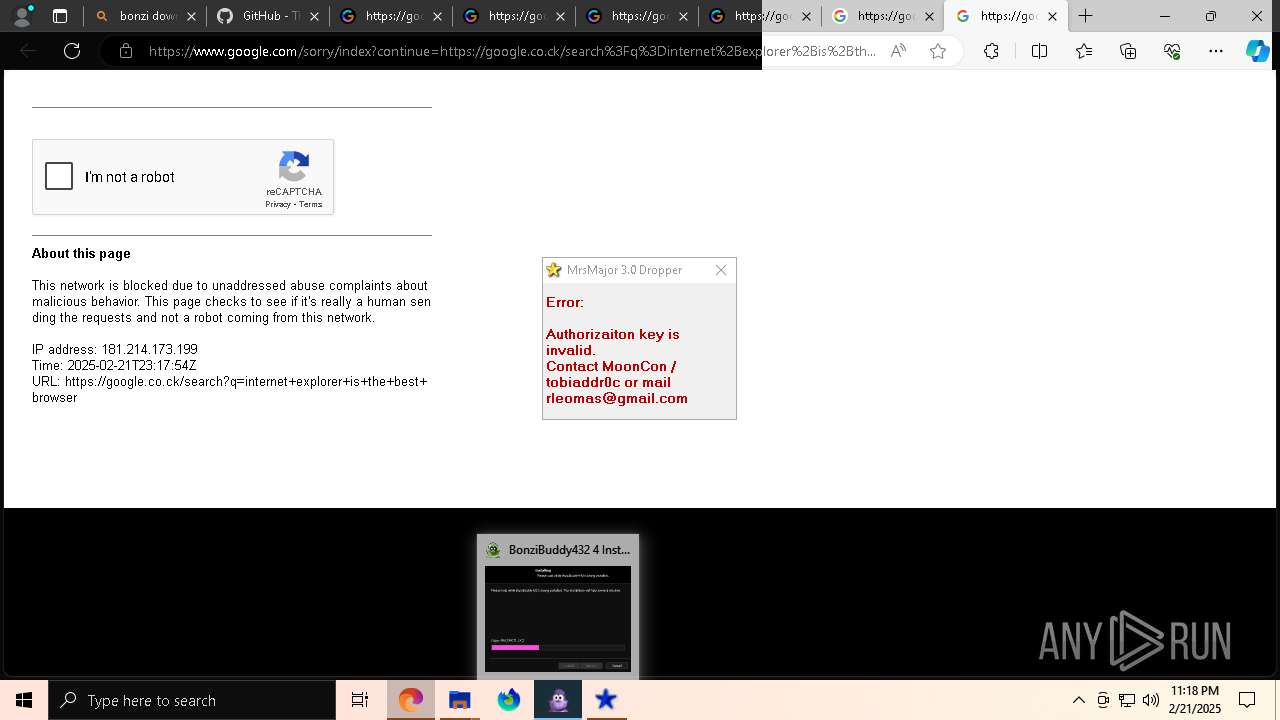
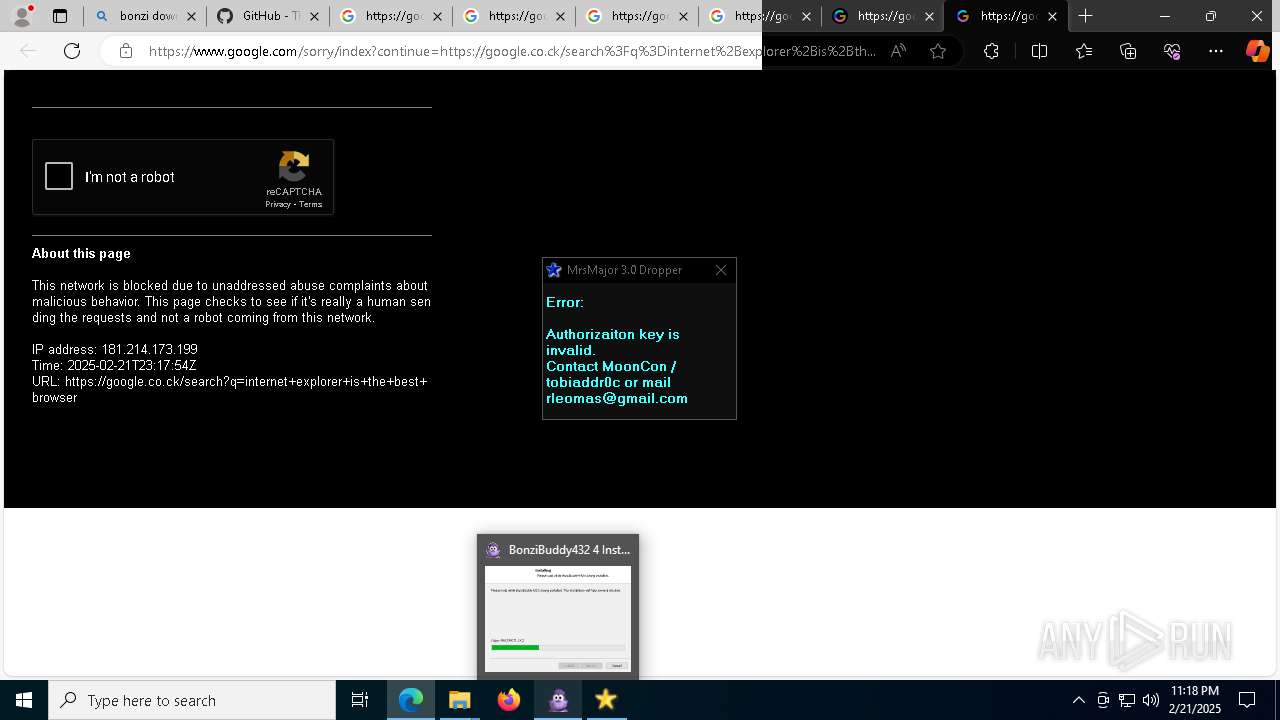
MALICIOUS
GENERIC has been found (auto)
- WinRAR.exe (PID: 7480)
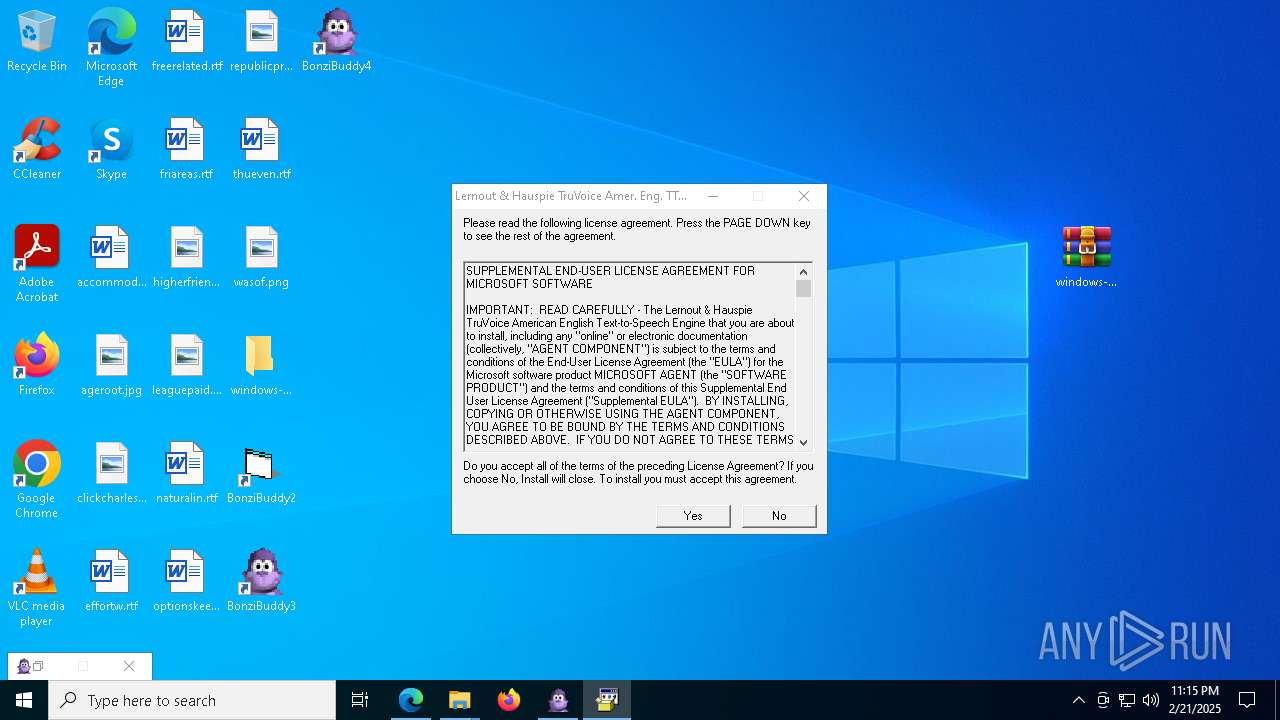
Executing a file with an untrusted certificate
- tv_enua.exe (PID: 4428)
- MSAGENT.EXE (PID: 4672)
Changes the autorun value in the registry
- tv_enua.exe (PID: 4428)
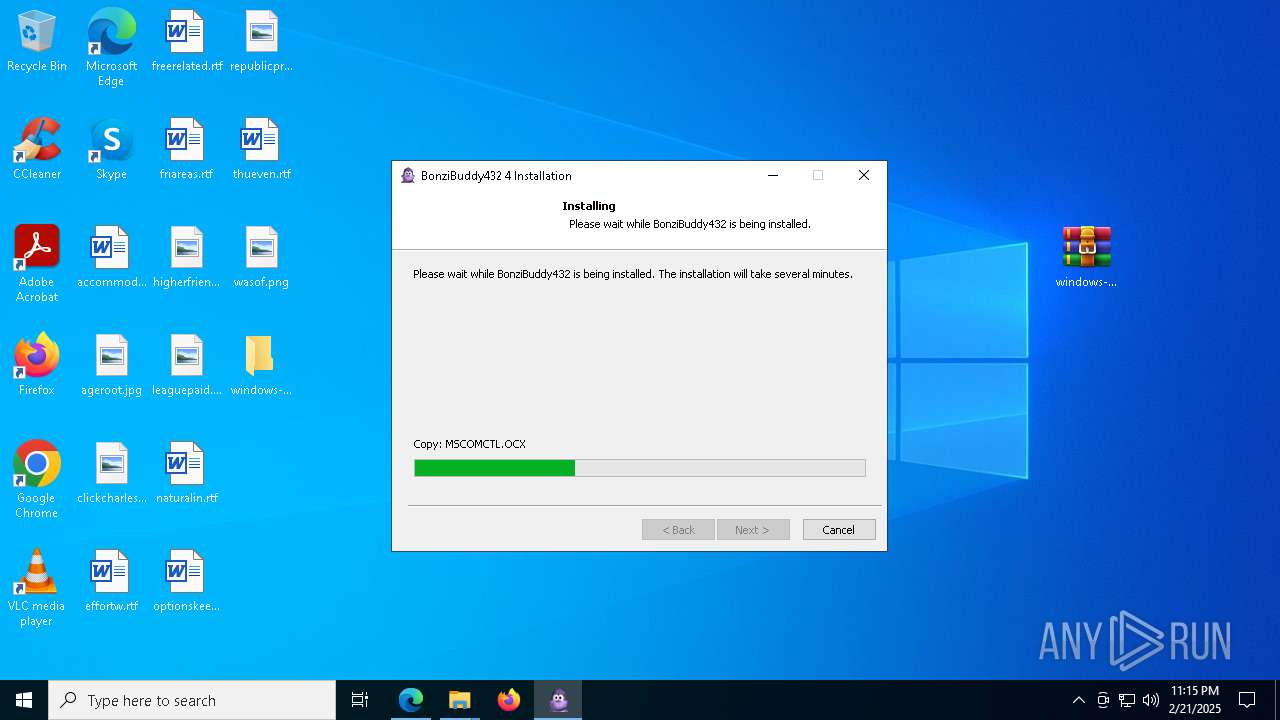
Registers / Runs the DLL via REGSVR32.EXE
- MSAGENT.EXE (PID: 4672)
- tv_enua.exe (PID: 4428)
Creates a new registry key or changes the value of an existing one (SCRIPT)
- wscript.exe (PID: 9016)
SUSPICIOUS
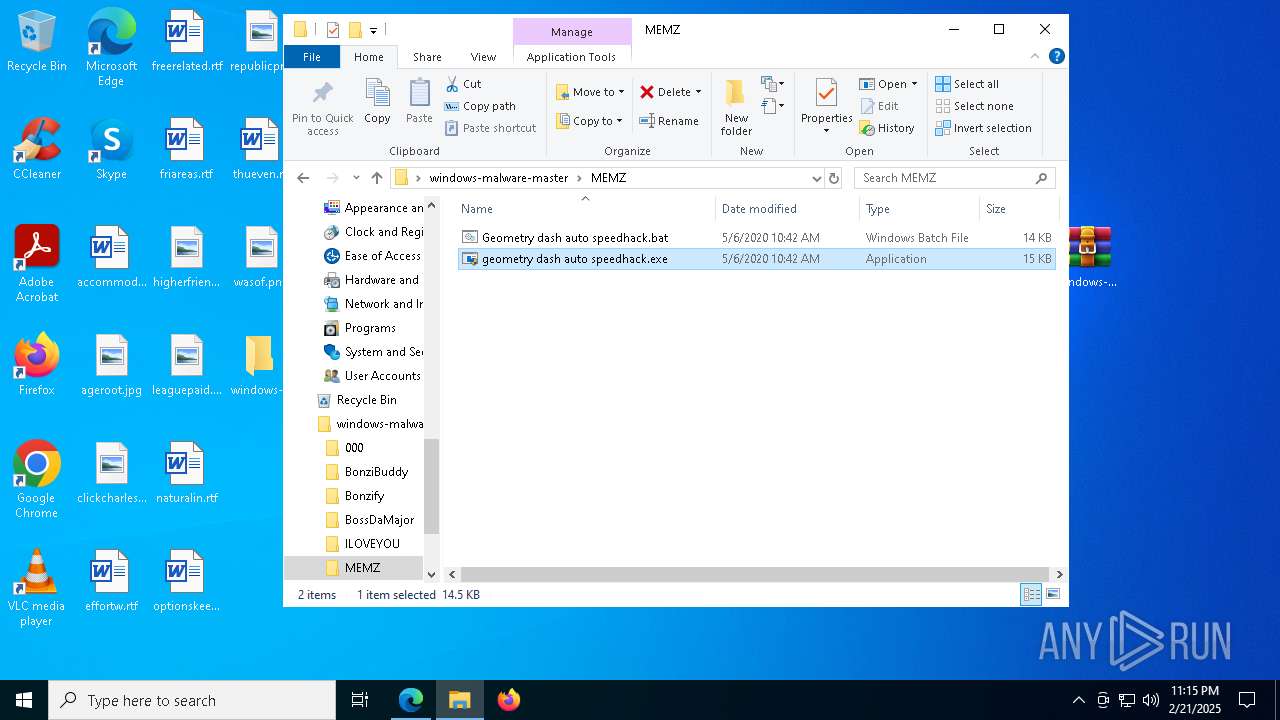
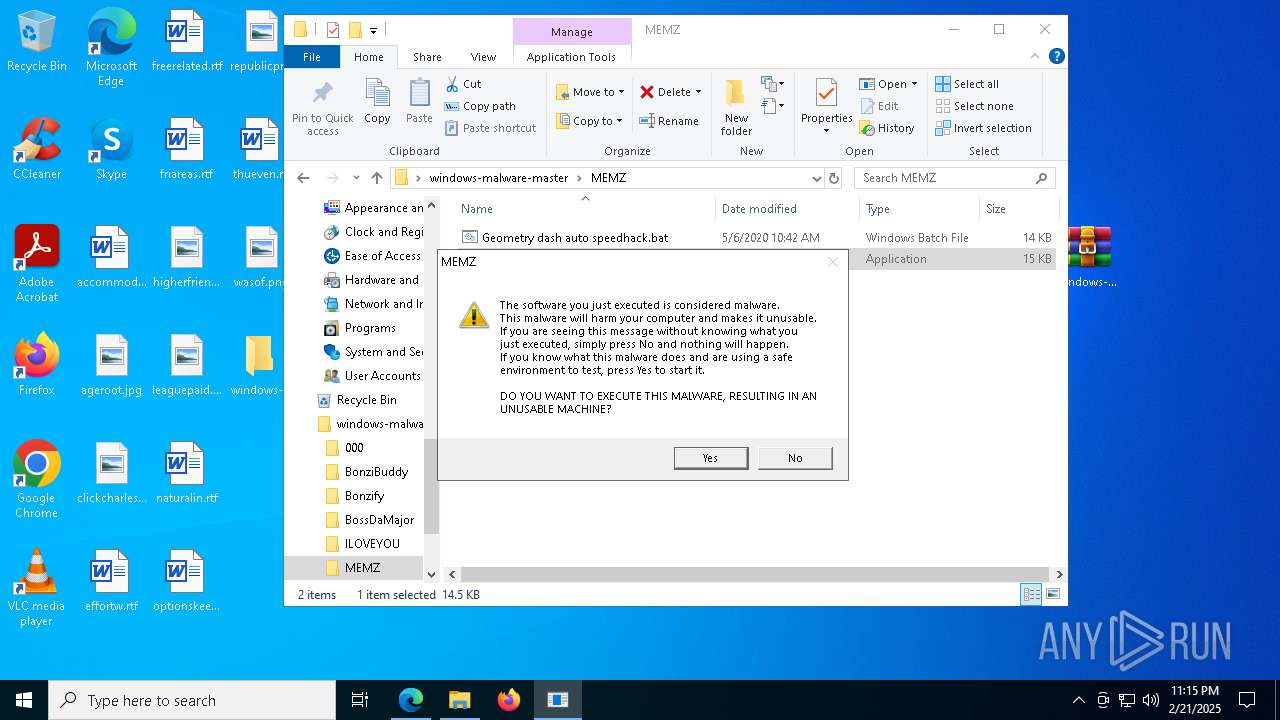
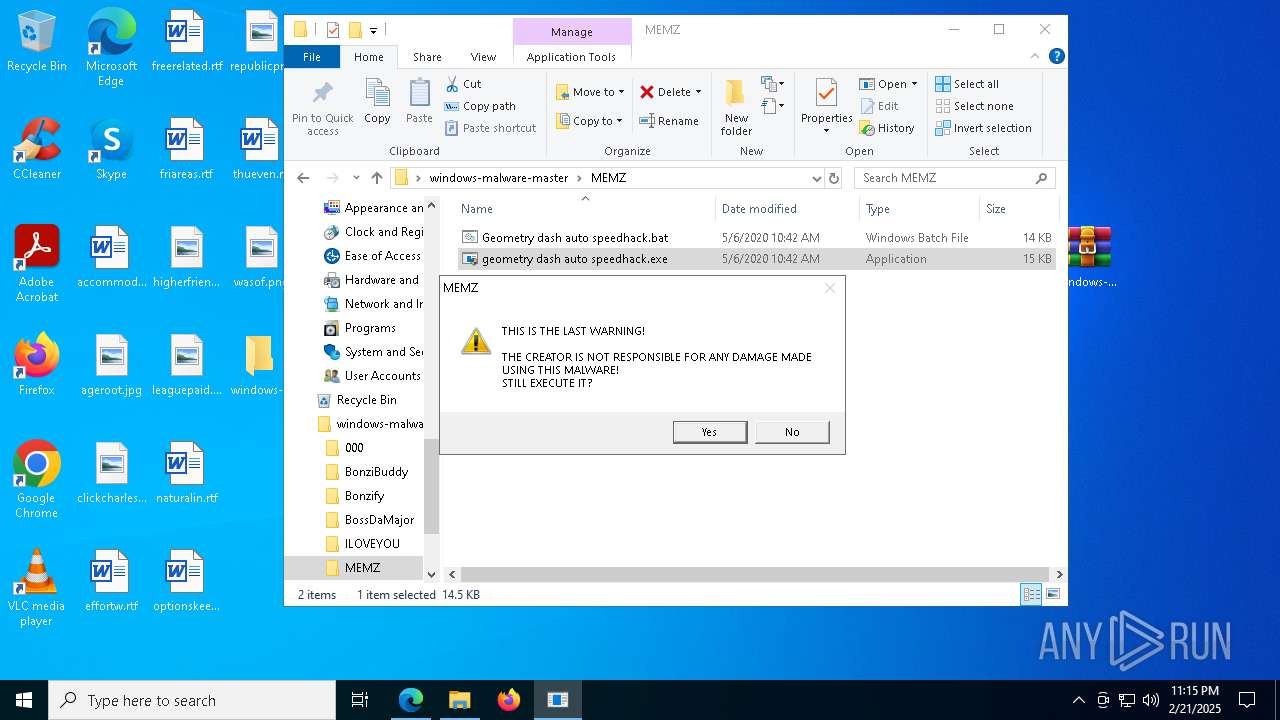
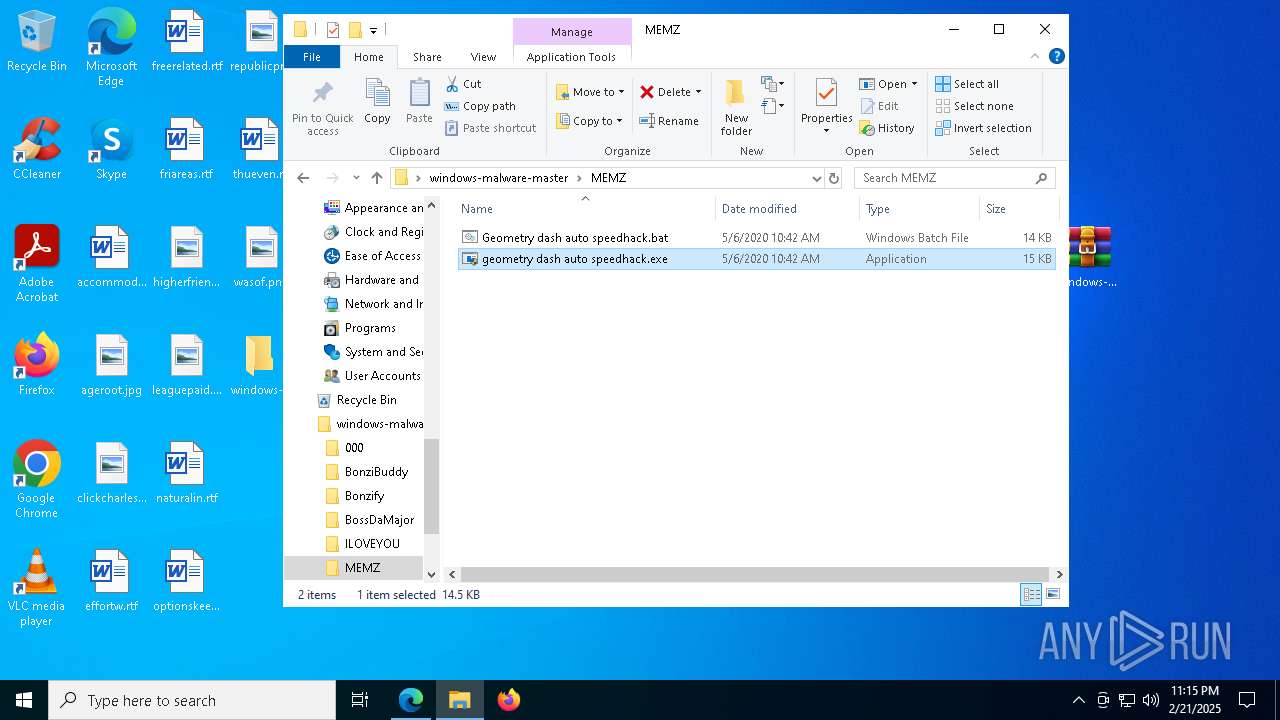
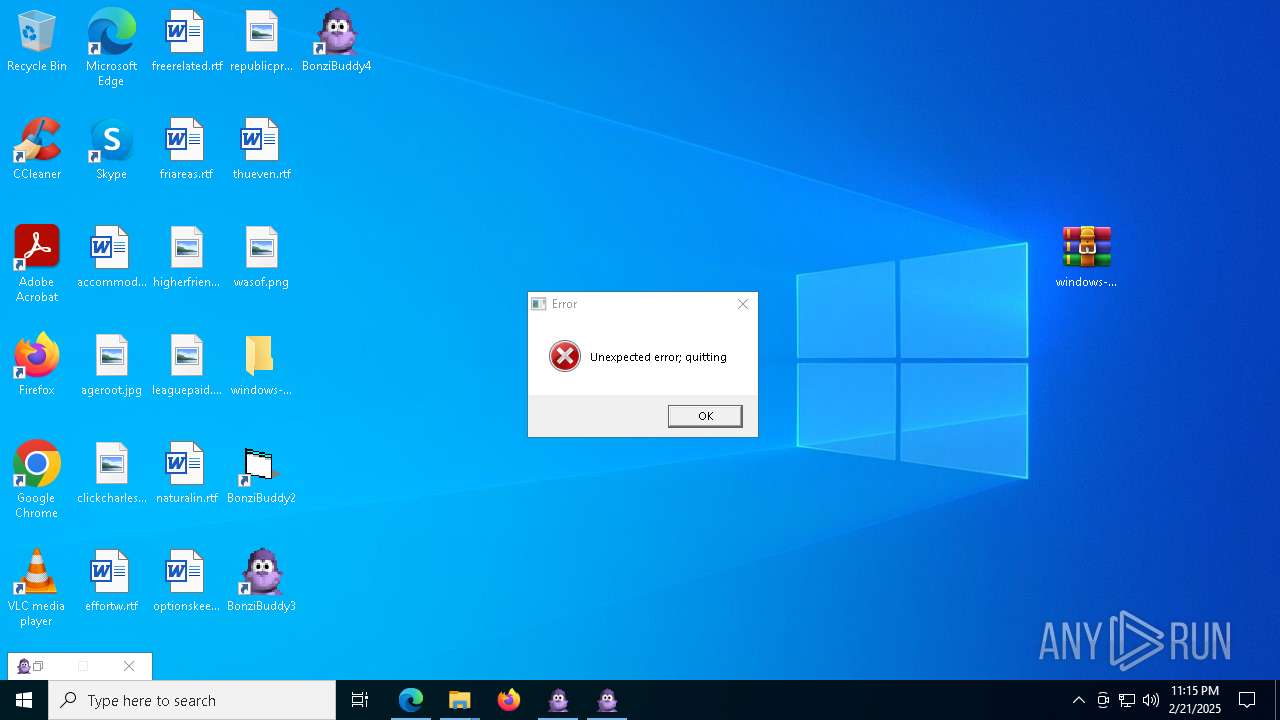
Application launched itself
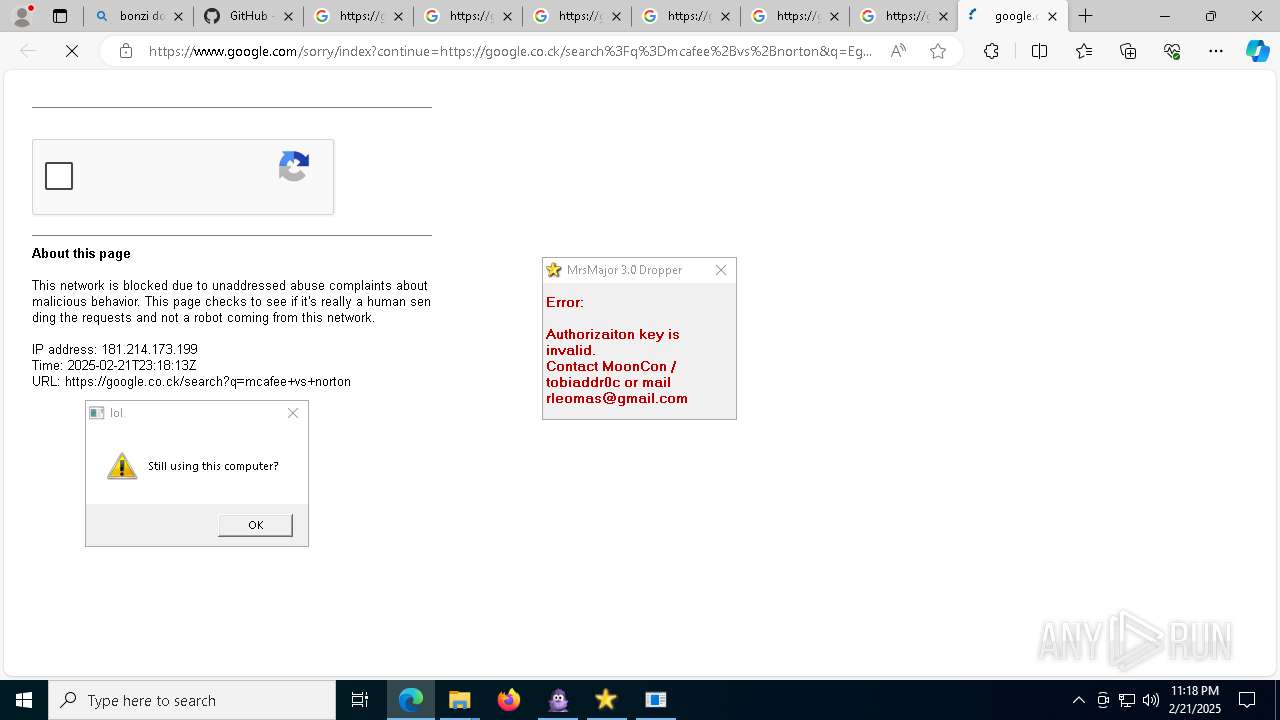
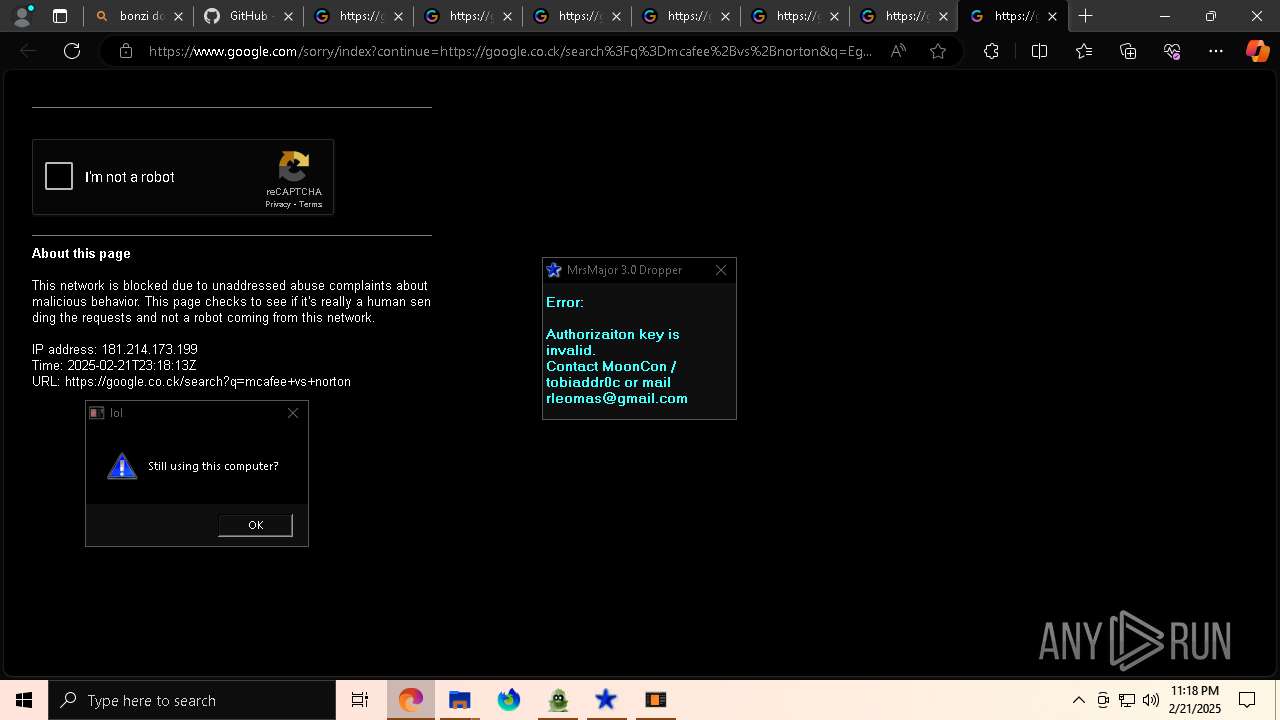
- geometry dash auto speedhack.exe (PID: 3812)
Reads security settings of Internet Explorer
- geometry dash auto speedhack.exe (PID: 3812)
- geometry dash auto speedhack.exe (PID: 5212)
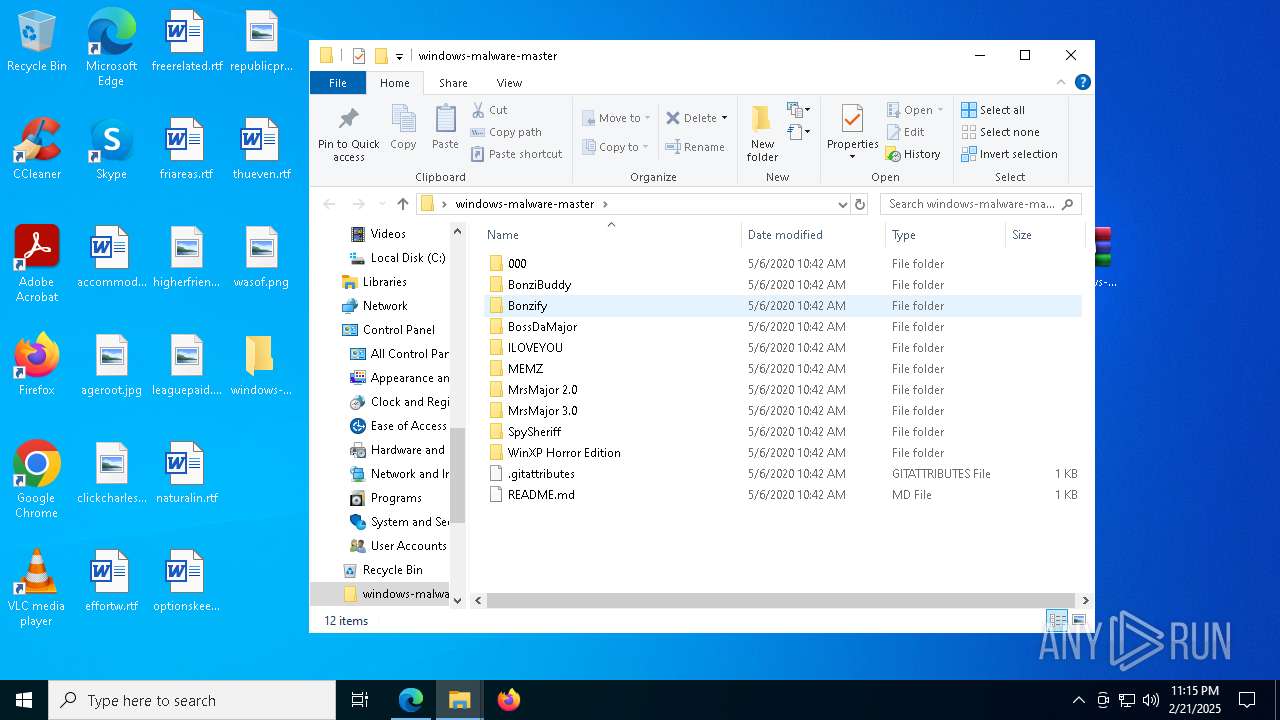
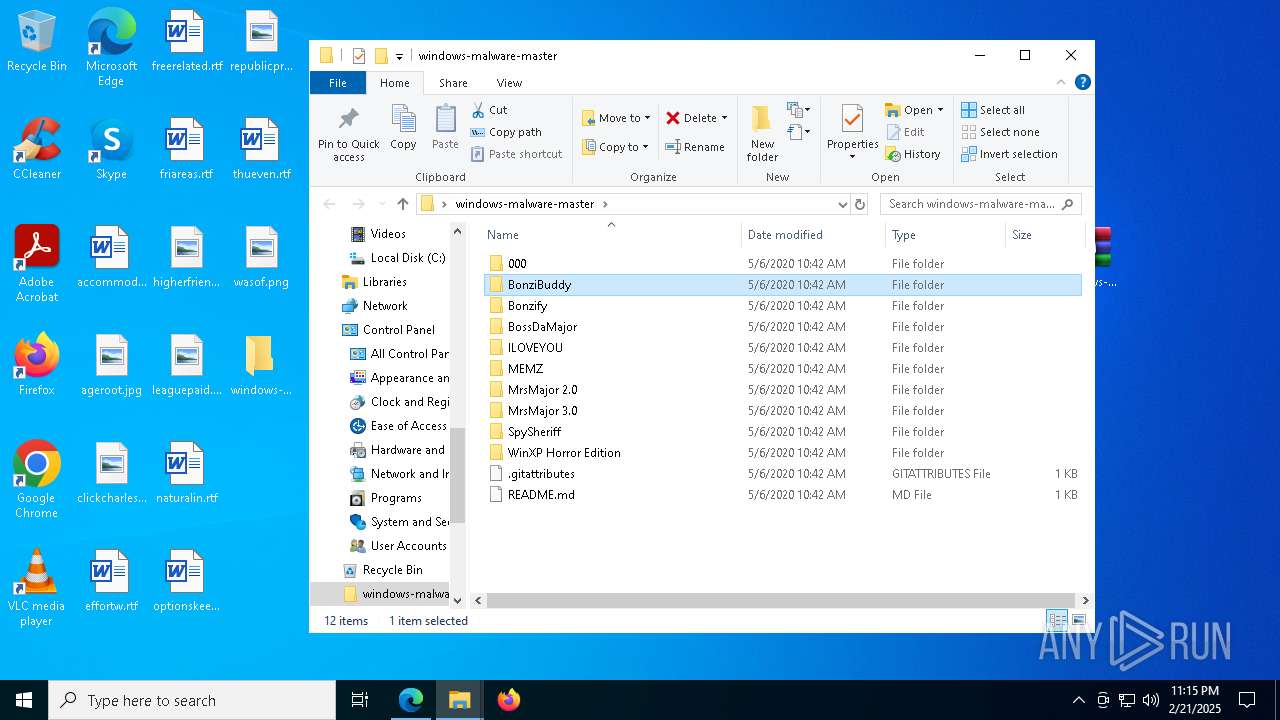
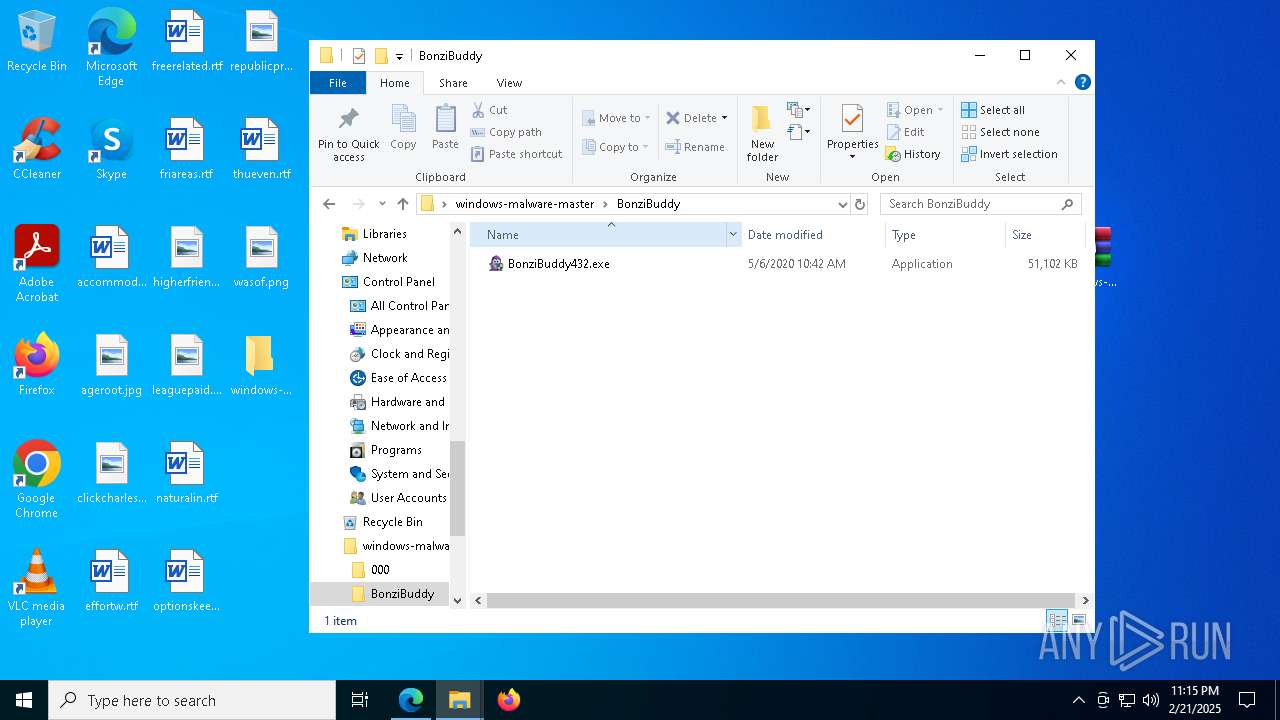
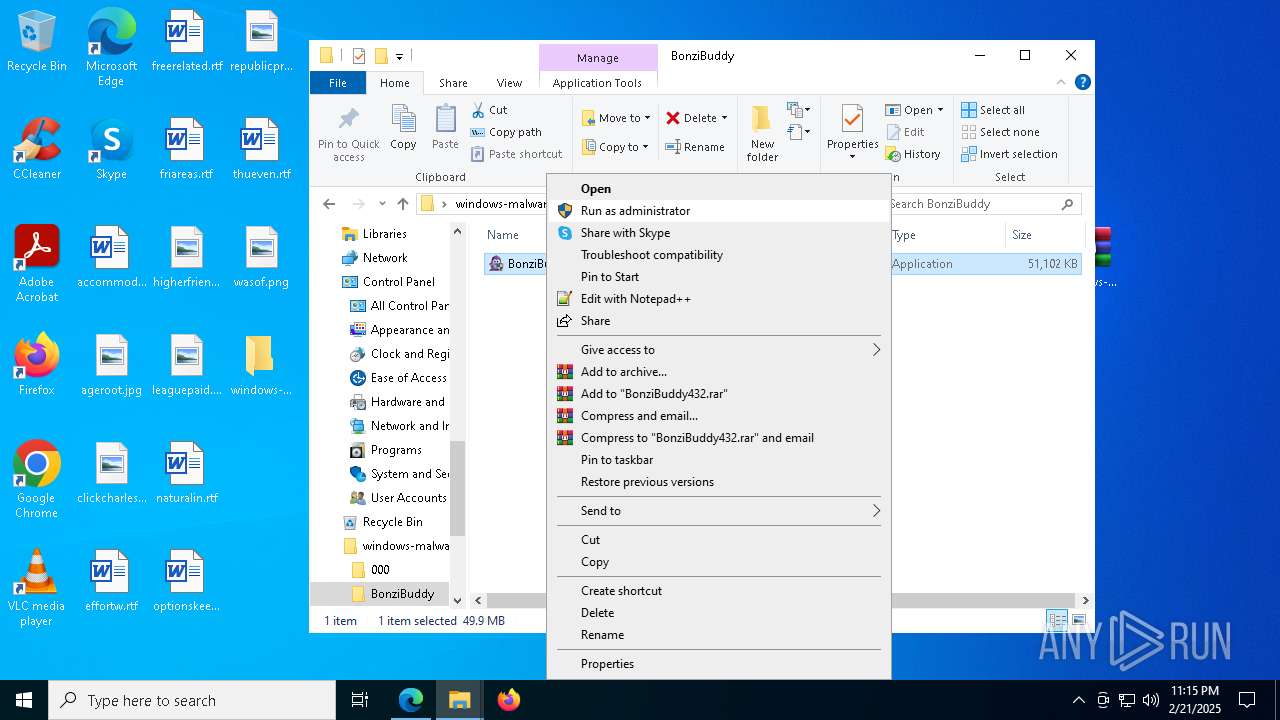
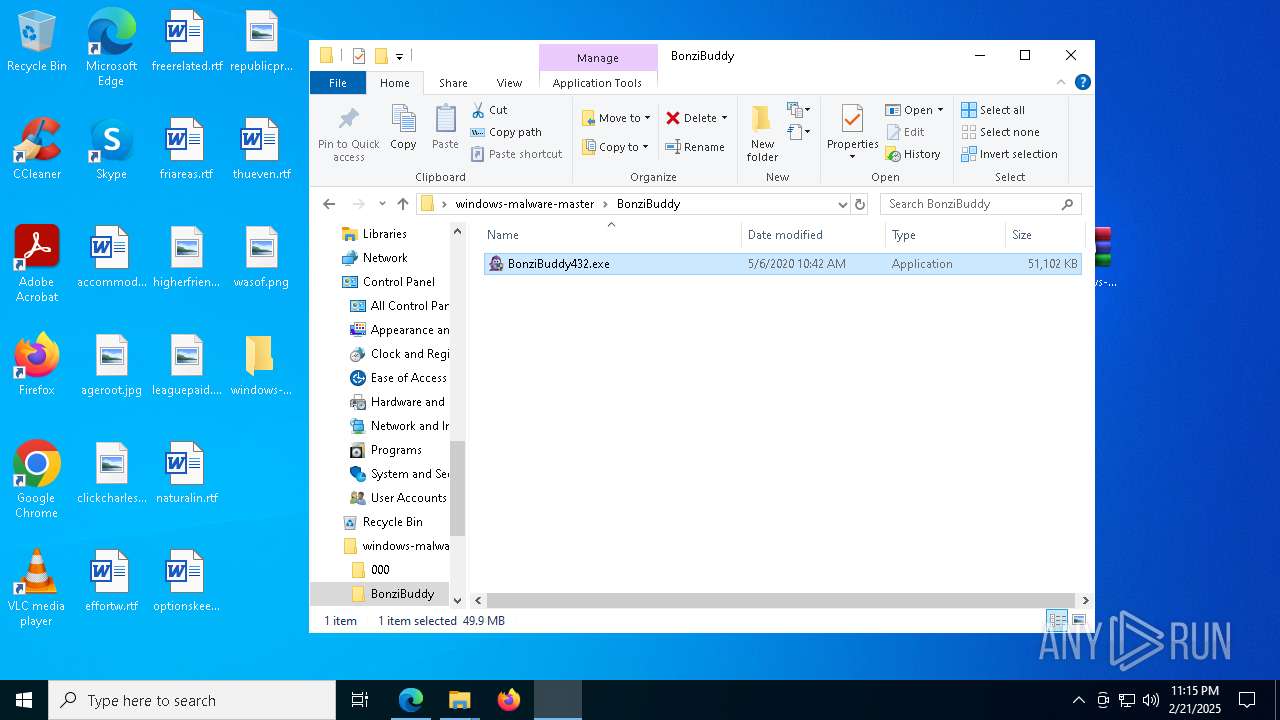
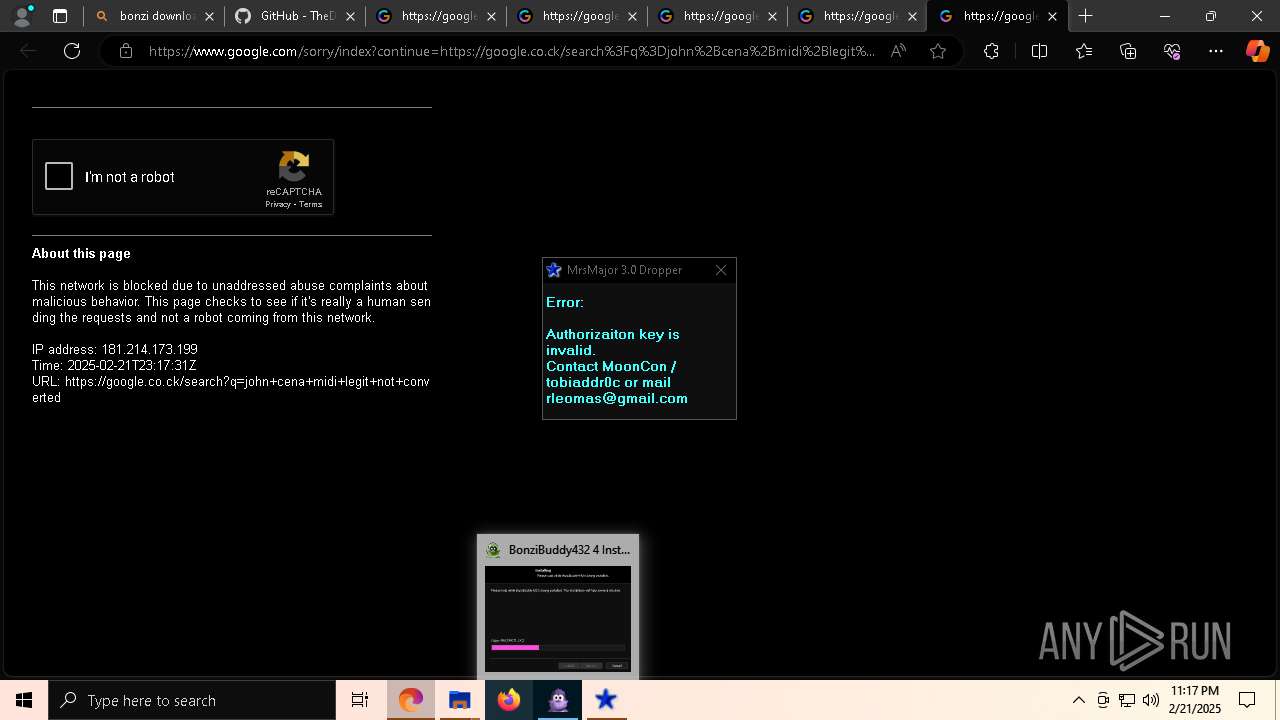
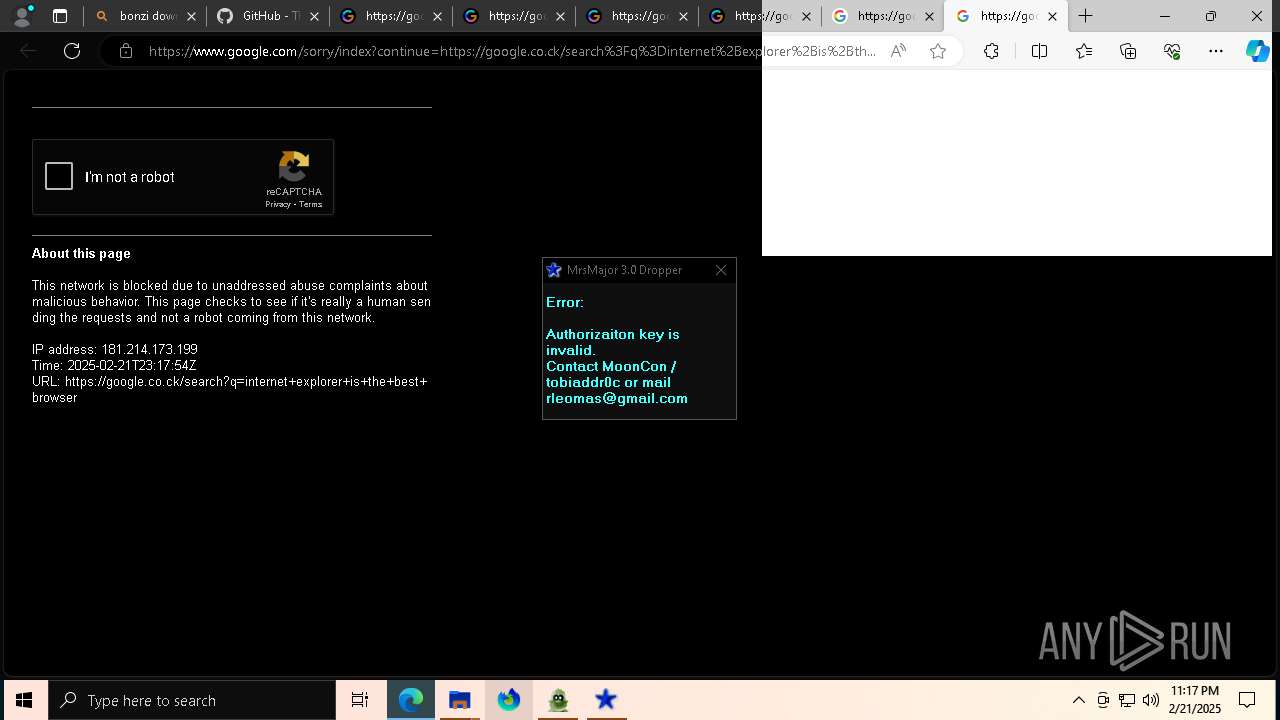
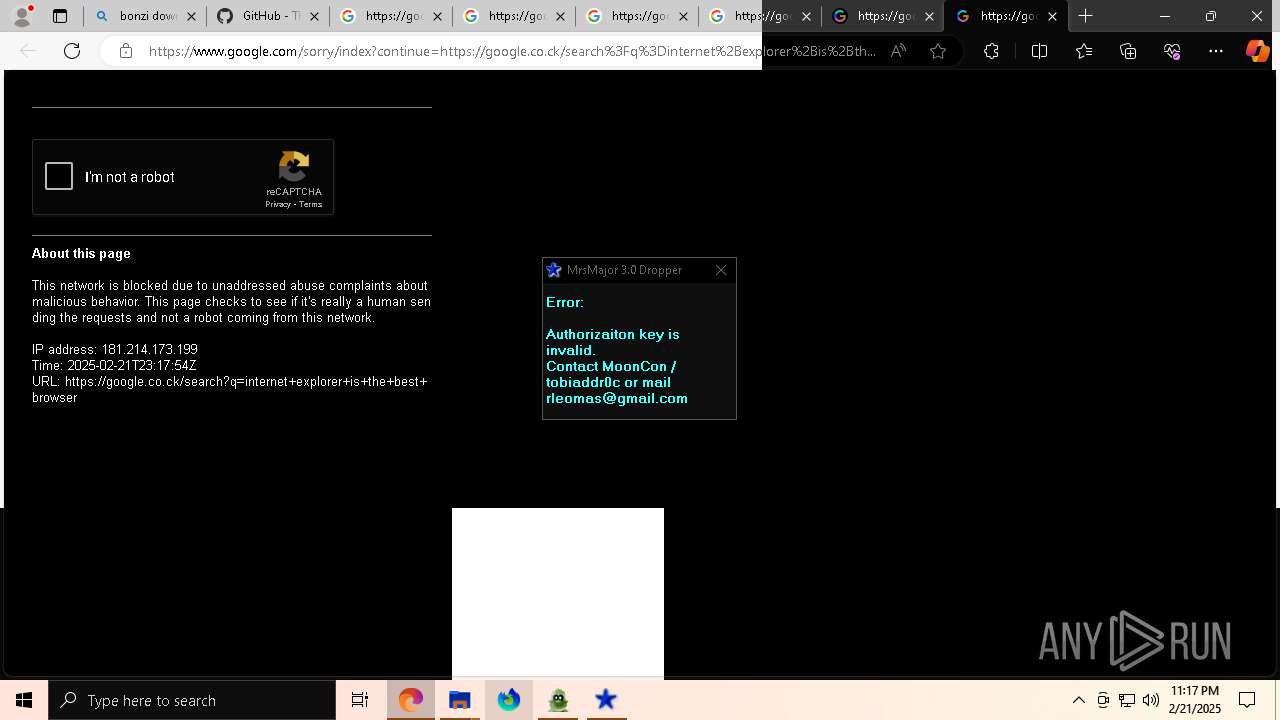
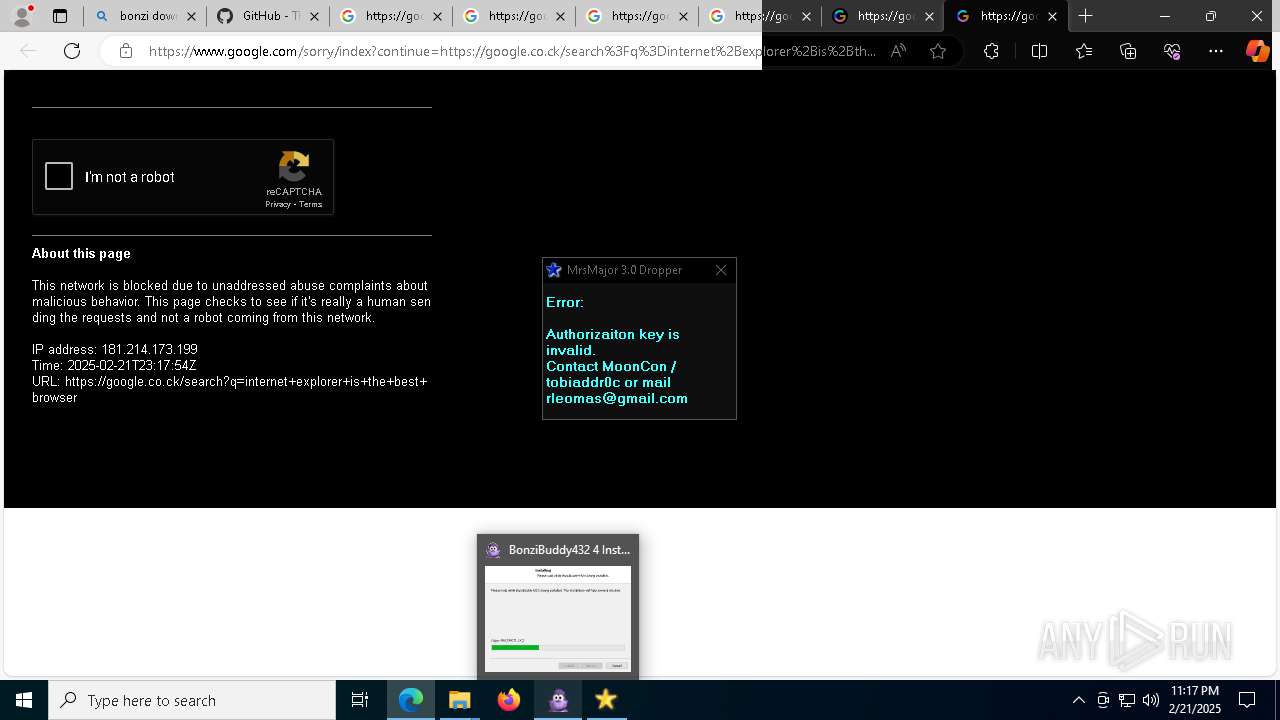
- BonziBuddy432.exe (PID: 7872)
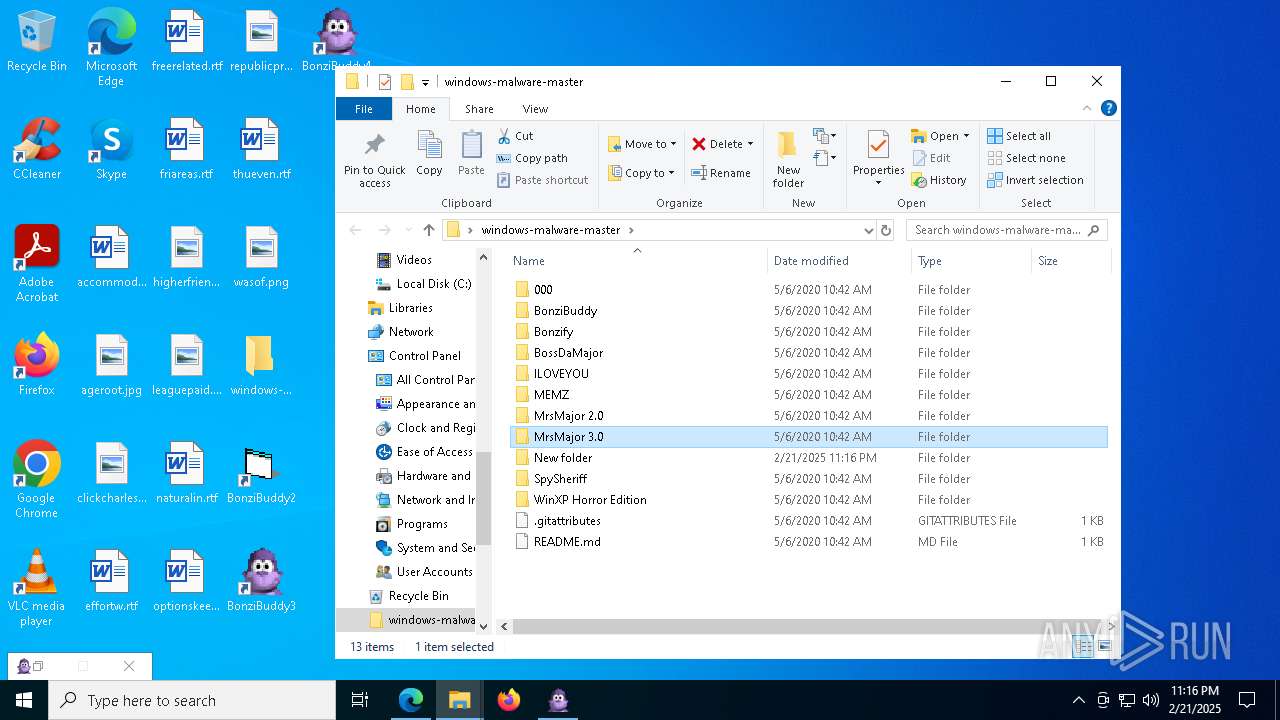
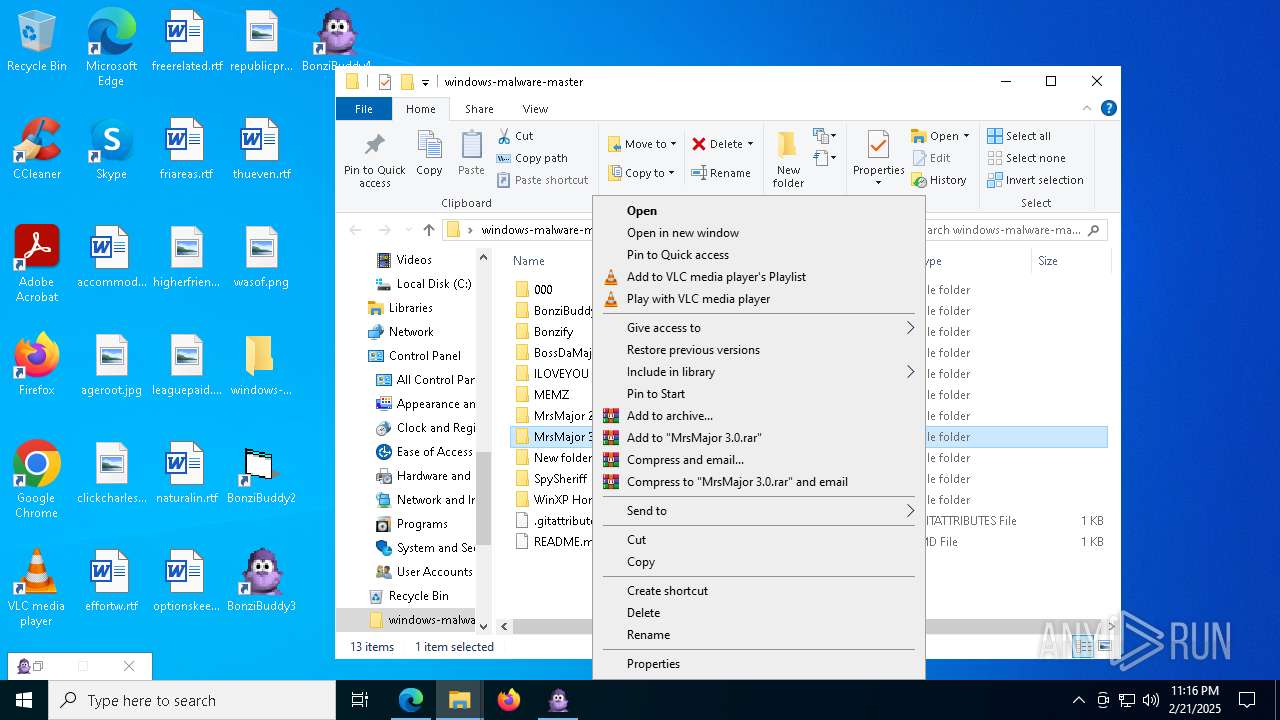
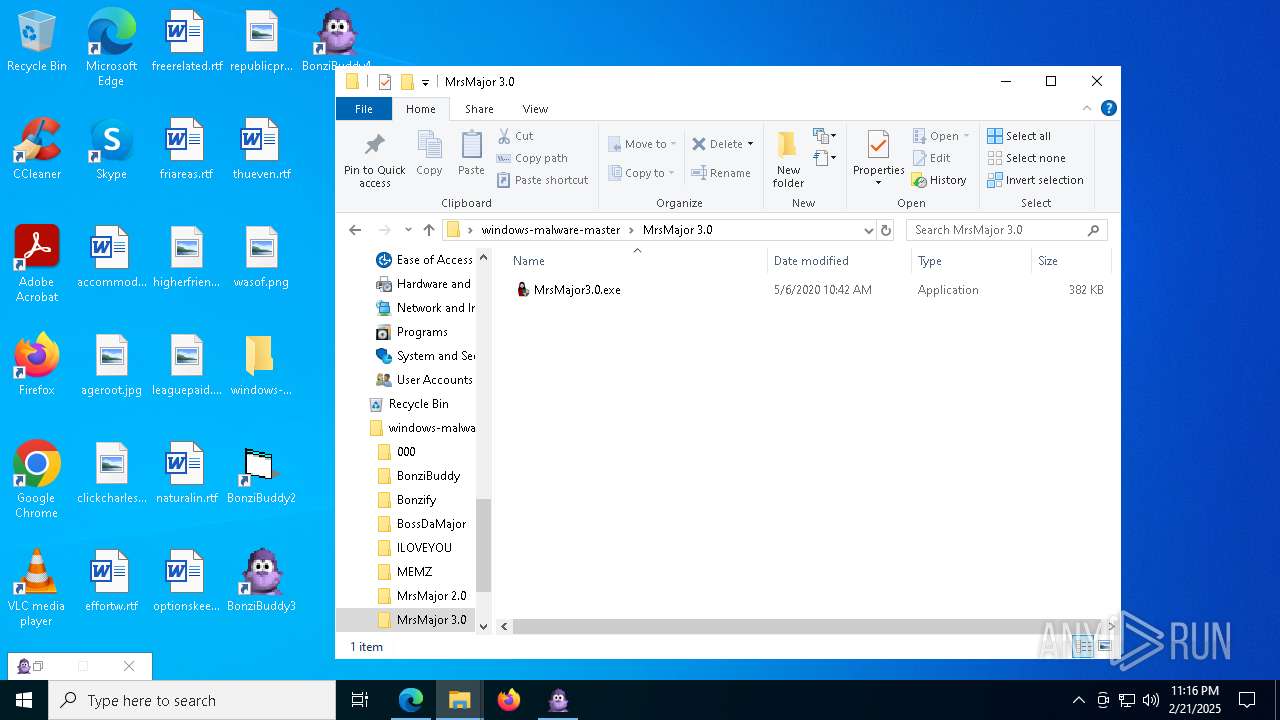
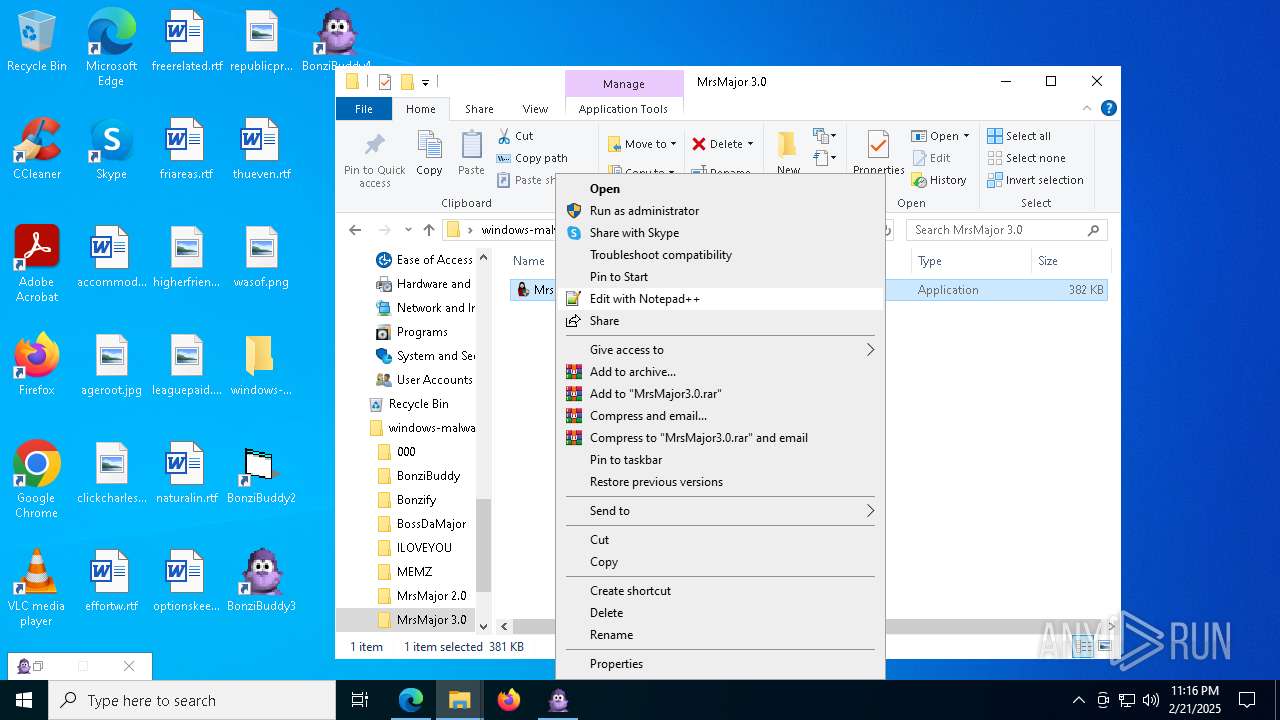
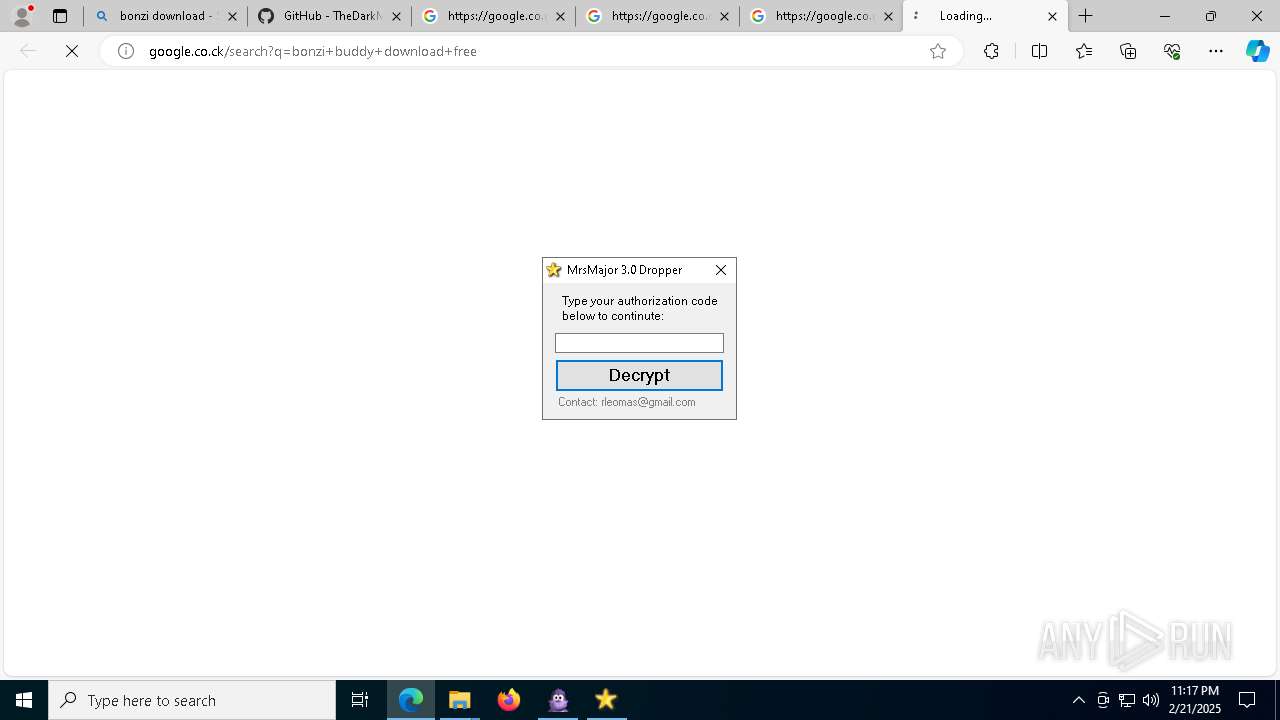
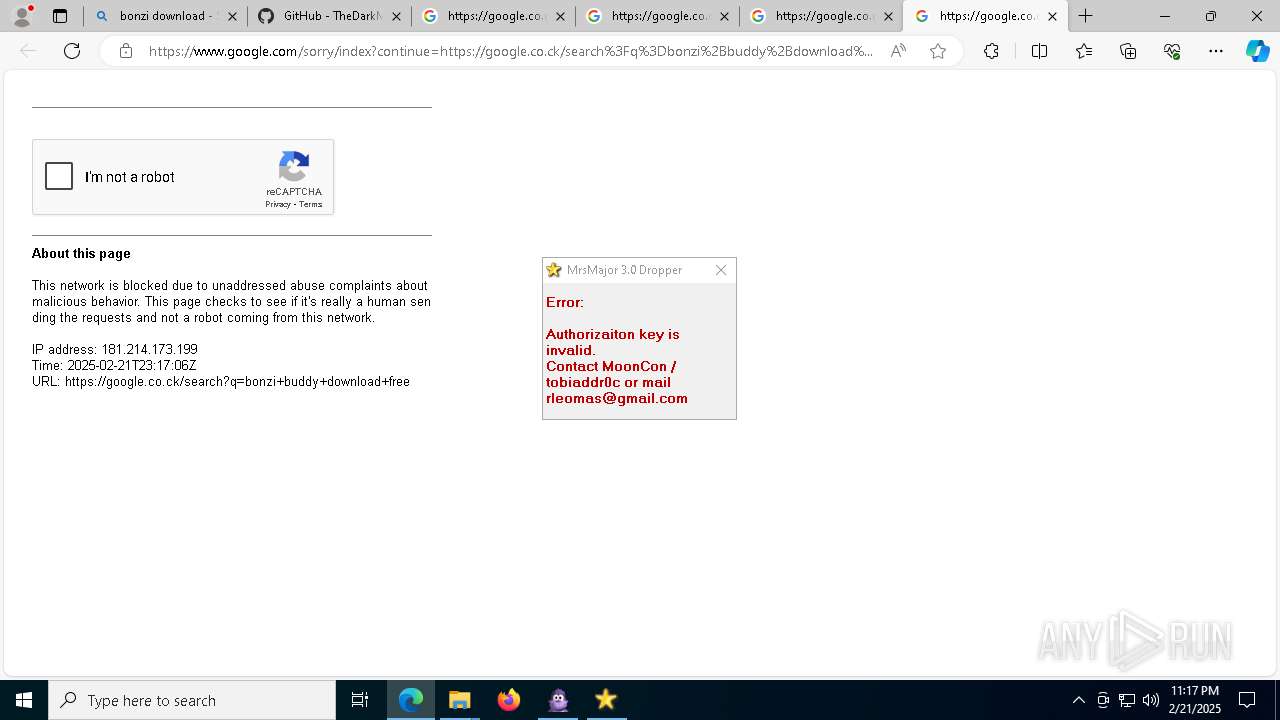
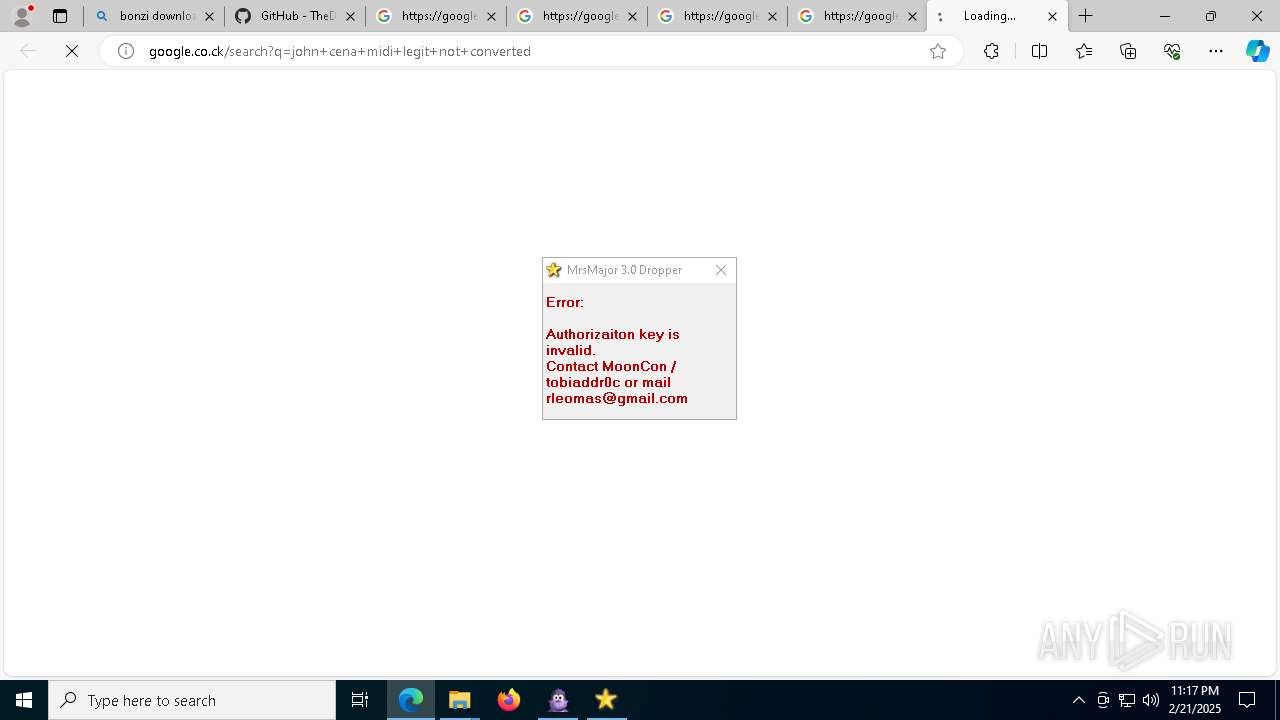
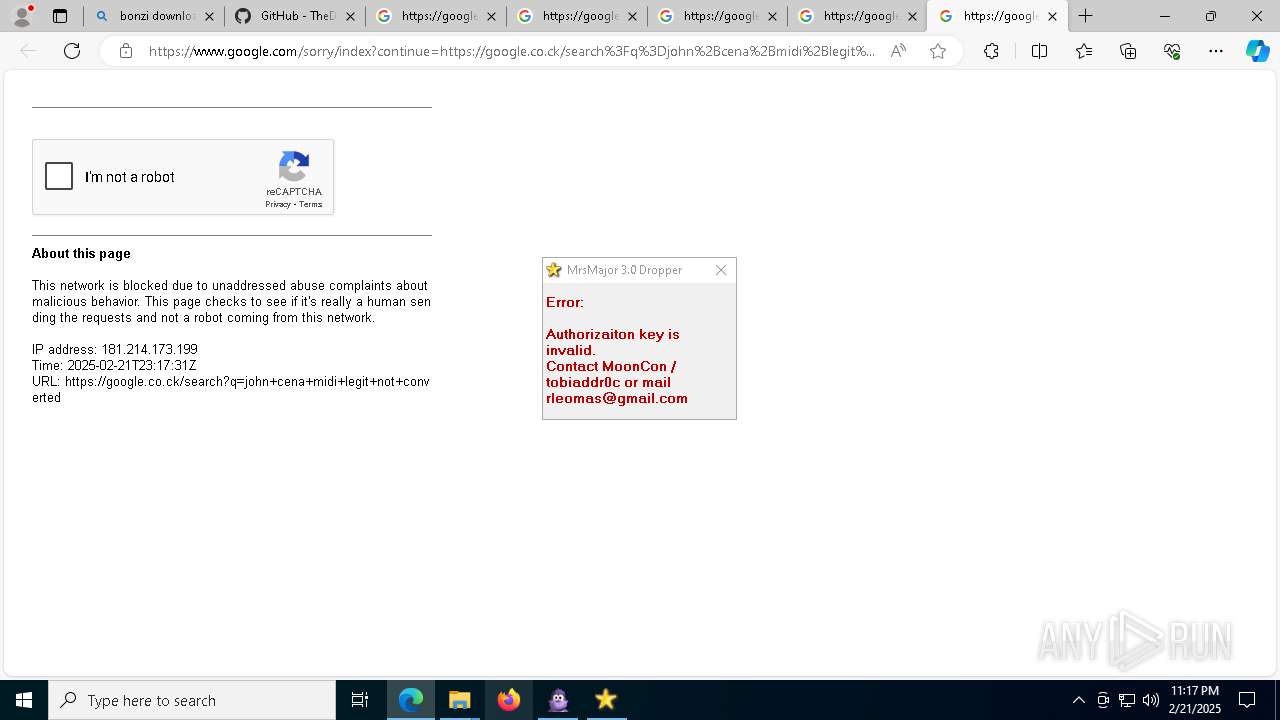
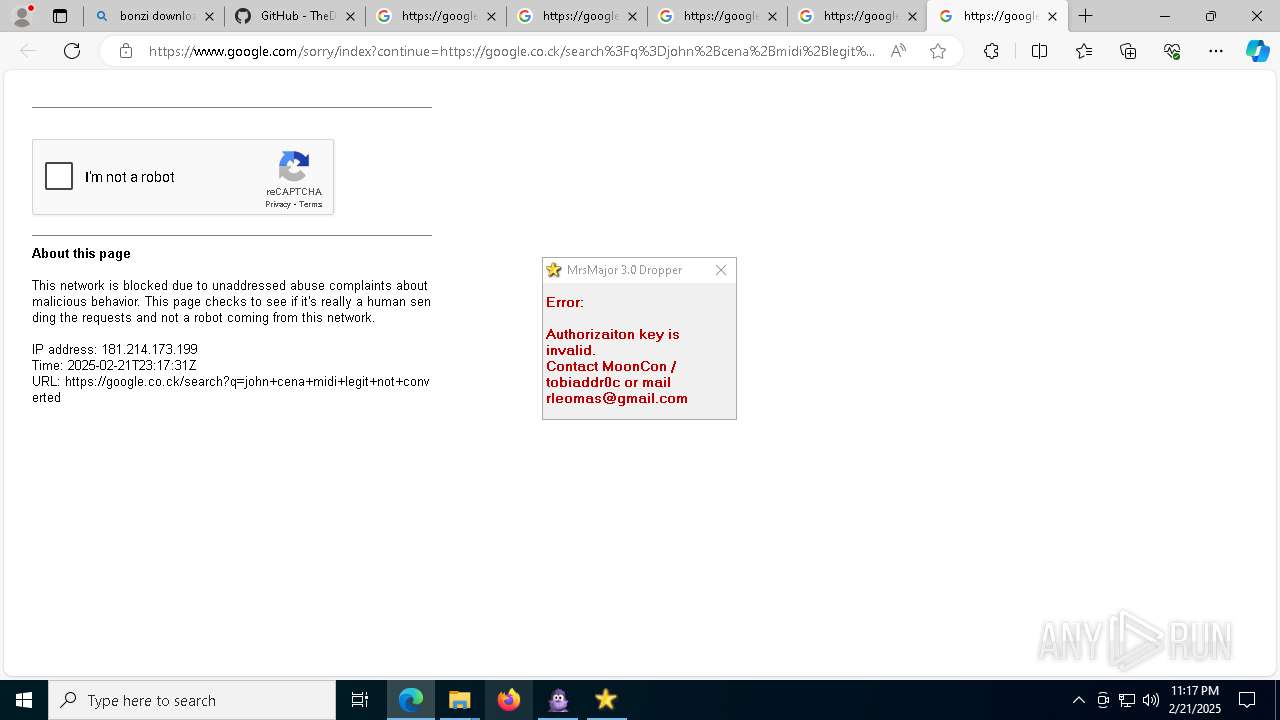
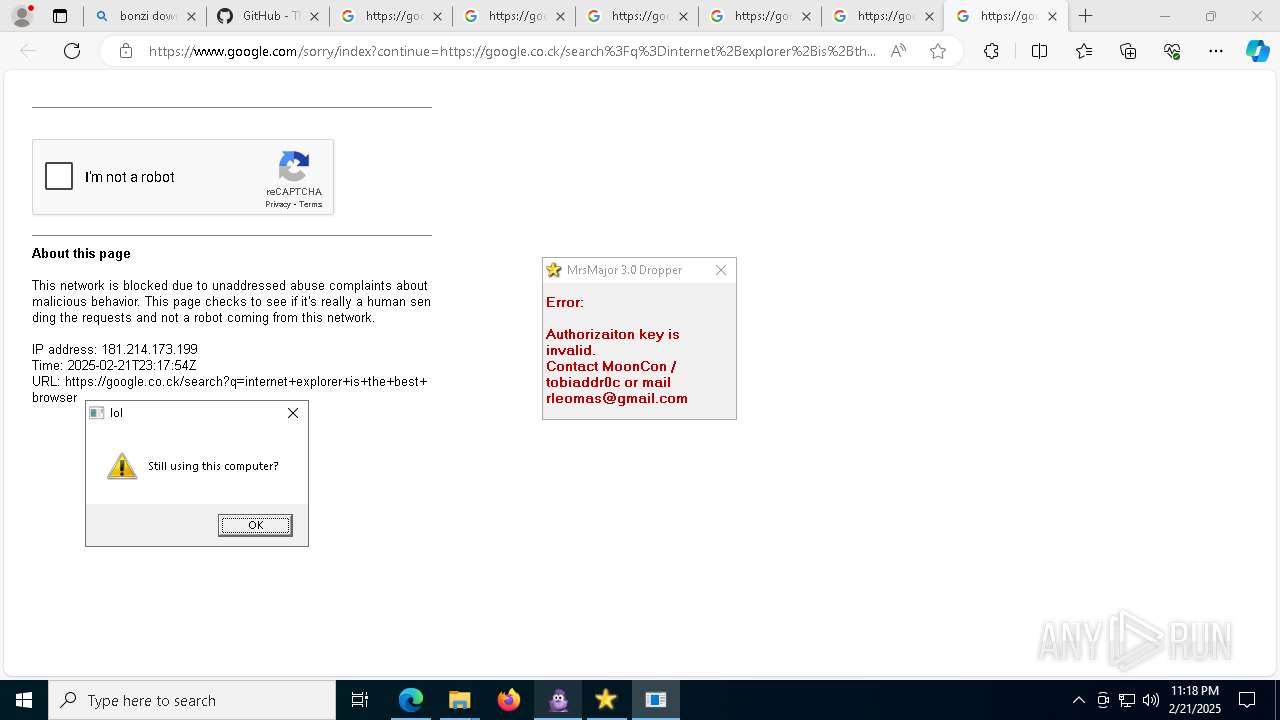
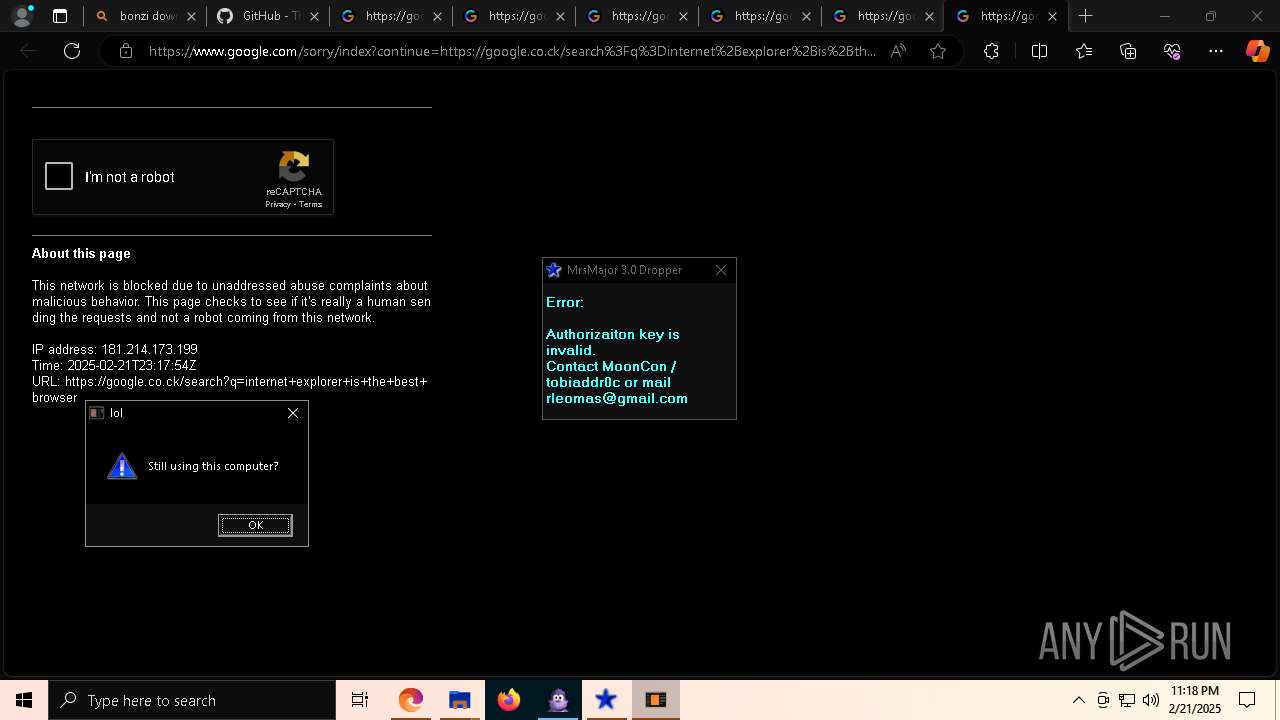
- MrsMajor3.0.exe (PID: 8964)
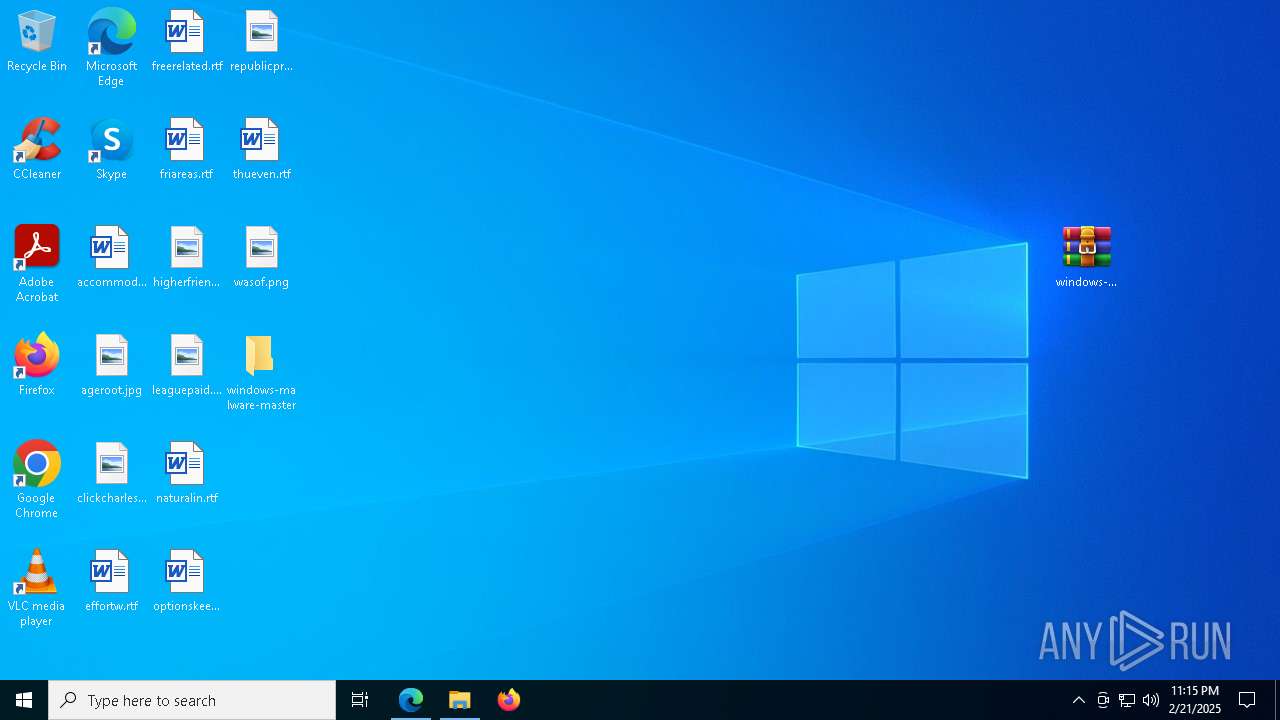
Creates file in the systems drive root
- geometry dash auto speedhack.exe (PID: 5212)
- notepad.exe (PID: 1192)
There is functionality for taking screenshot (YARA)
- geometry dash auto speedhack.exe (PID: 2744)
- geometry dash auto speedhack.exe (PID: 1292)
- geometry dash auto speedhack.exe (PID: 2904)
- geometry dash auto speedhack.exe (PID: 5212)
- geometry dash auto speedhack.exe (PID: 3780)
- geometry dash auto speedhack.exe (PID: 5836)
- BonziBuddy432.exe (PID: 7872)
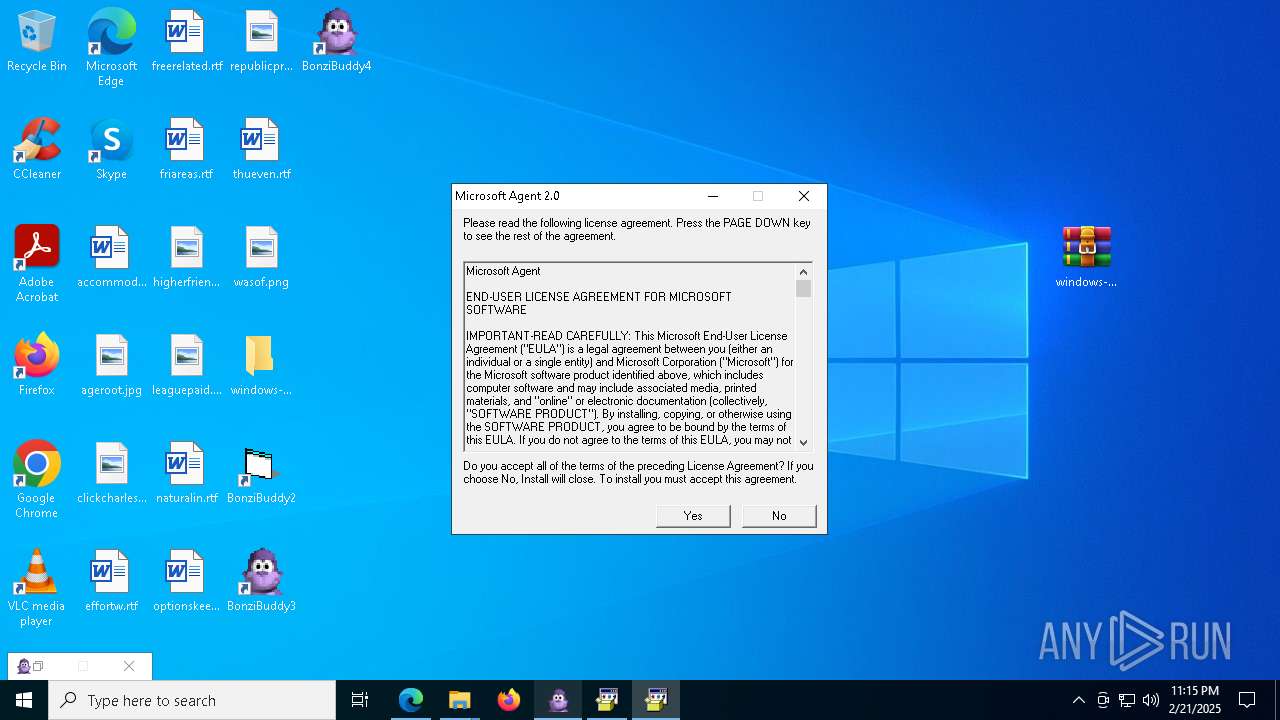
Executable content was dropped or overwritten
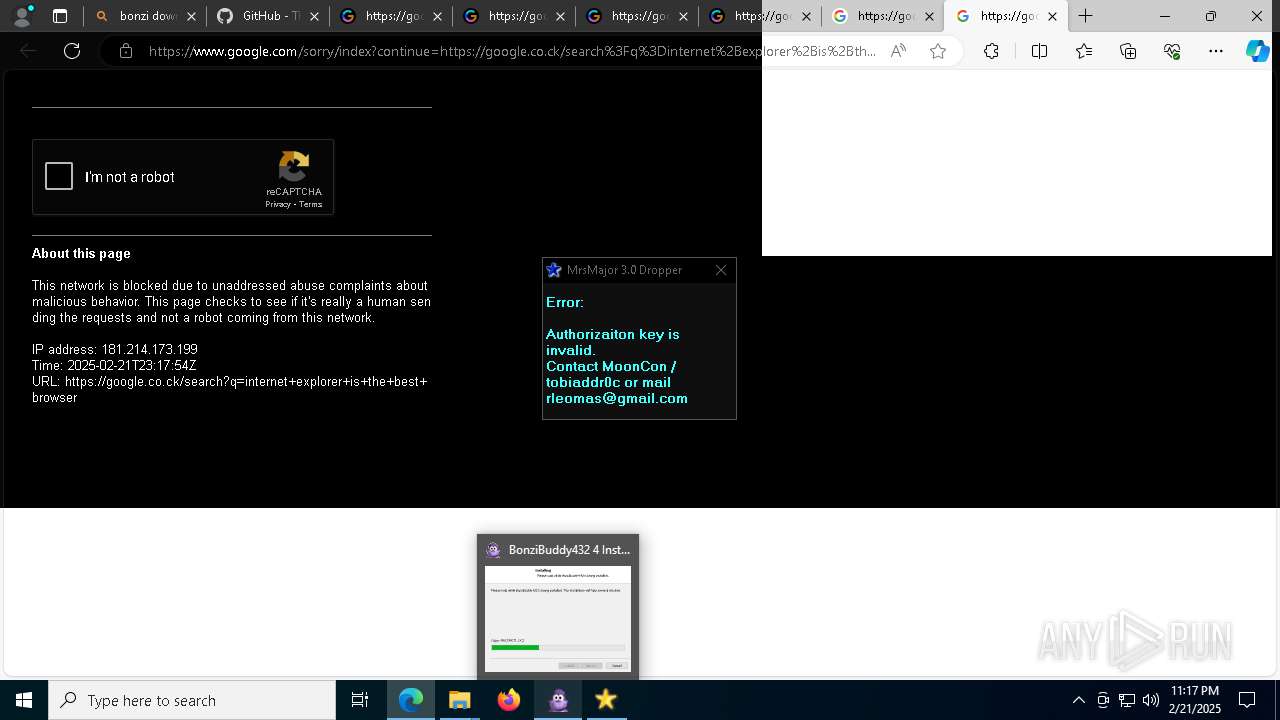
- BonziBuddy432.exe (PID: 7872)
- MSAGENT.EXE (PID: 4672)
- tv_enua.exe (PID: 4428)
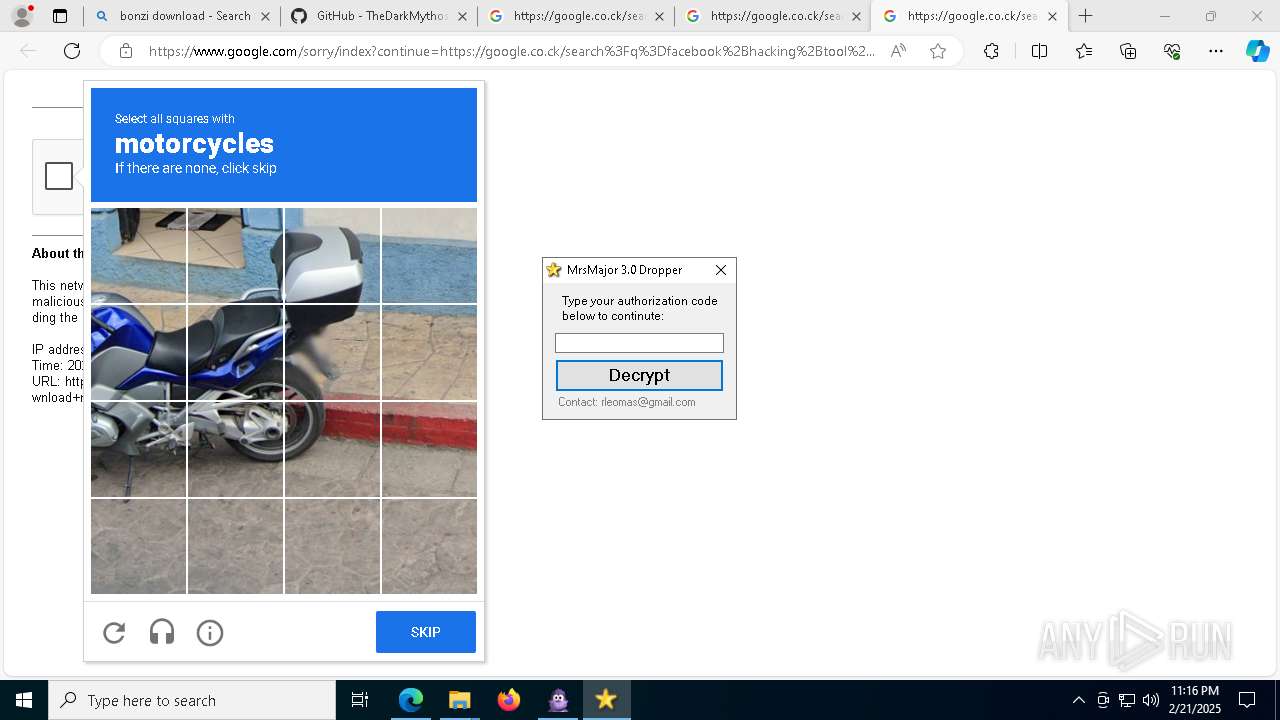
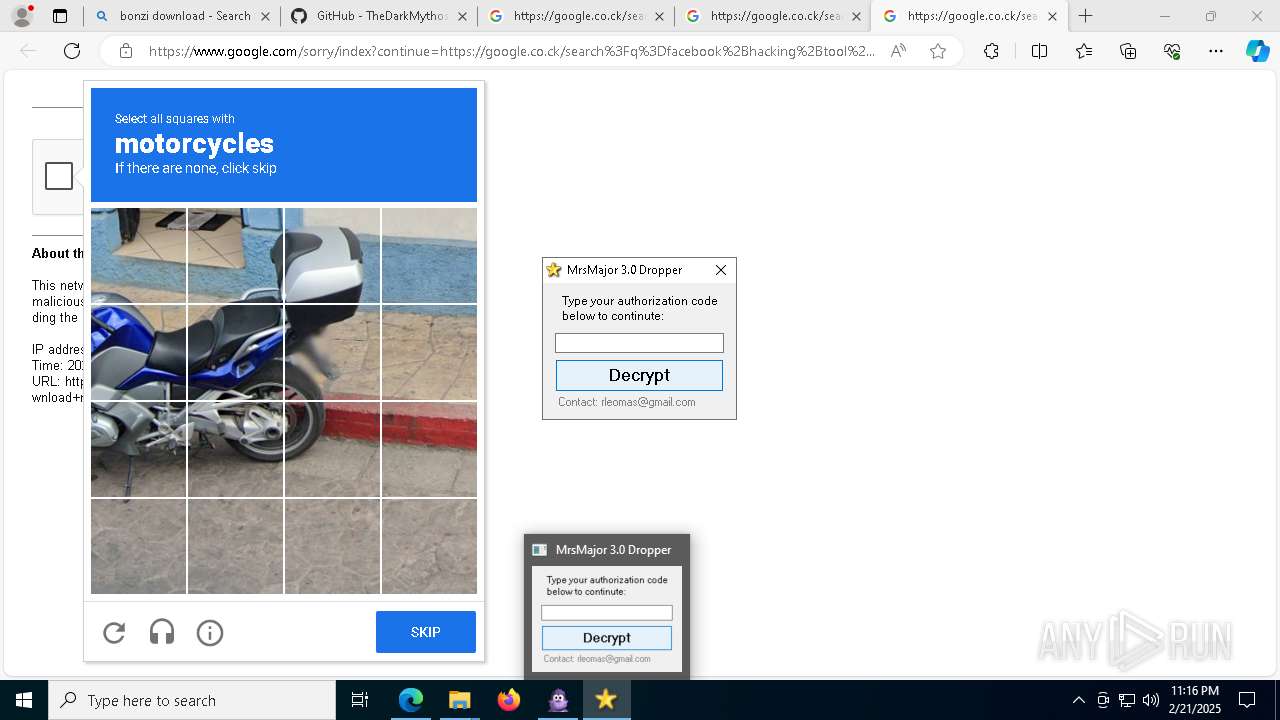
- MrsMajor3.0.exe (PID: 8964)
- eulascr.exe (PID: 7040)
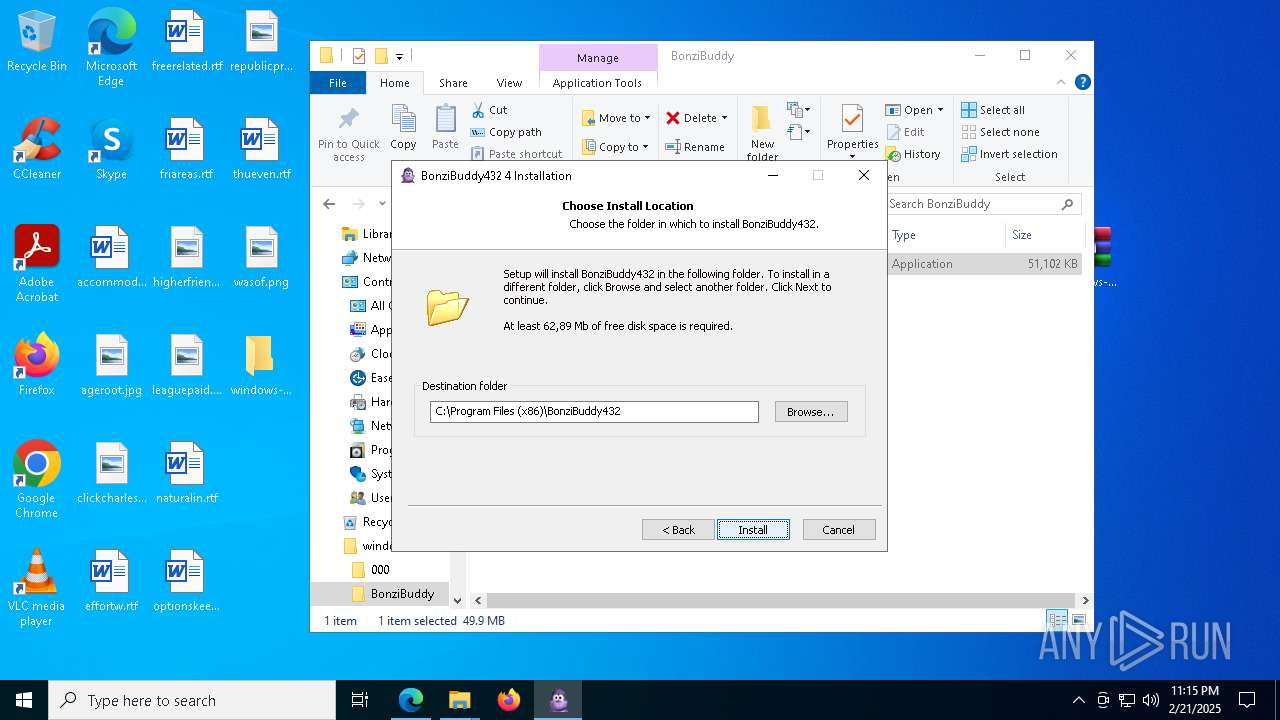
Creates a software uninstall entry
- BonziBuddy432.exe (PID: 7872)
- tv_enua.exe (PID: 4428)
Process drops legitimate windows executable
- BonziBuddy432.exe (PID: 7872)
- tv_enua.exe (PID: 4428)
- MSAGENT.EXE (PID: 4672)
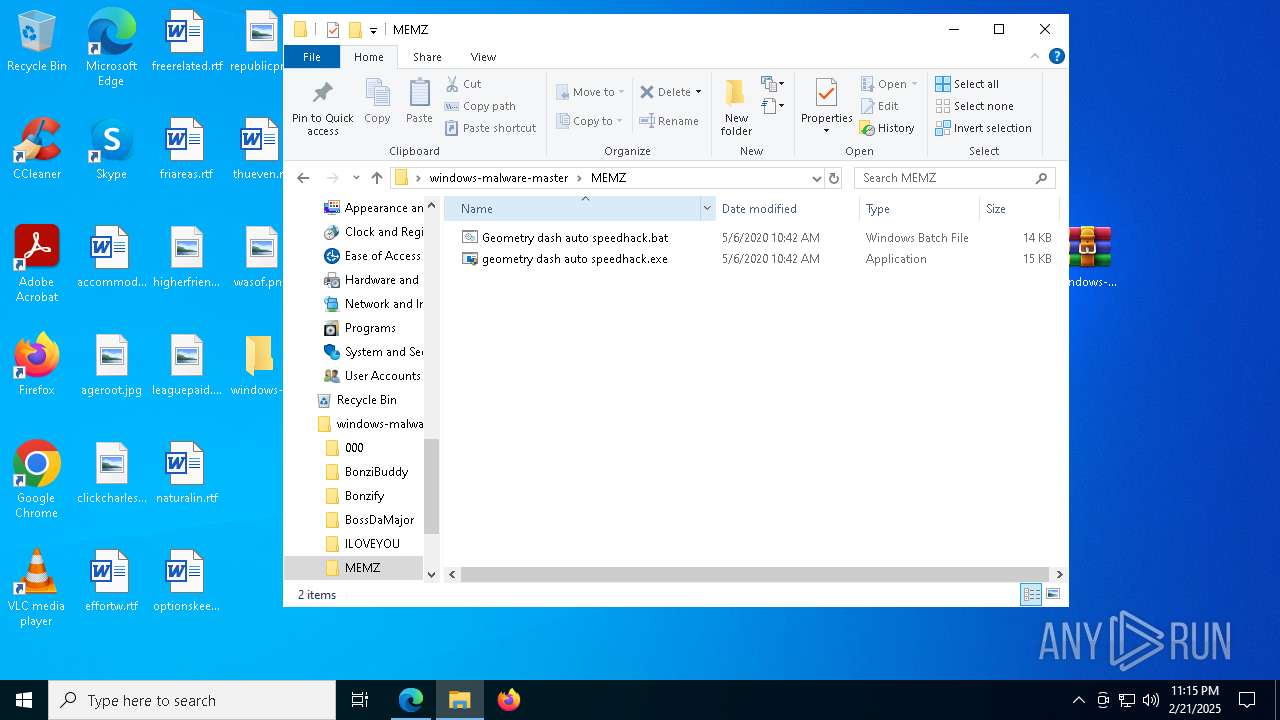
Executing commands from a ".bat" file
- BonziBuddy432.exe (PID: 7872)
Creates/Modifies COM task schedule object
- BonziBuddy432.exe (PID: 7872)
- regsvr32.exe (PID: 7460)
- regsvr32.exe (PID: 3488)
- regsvr32.exe (PID: 5316)
- regsvr32.exe (PID: 2396)
- regsvr32.exe (PID: 7352)
- regsvr32.exe (PID: 4840)
- regsvr32.exe (PID: 236)
- regsvr32.exe (PID: 7320)
- regsvr32.exe (PID: 1412)
Starts CMD.EXE for commands execution
- BonziBuddy432.exe (PID: 7872)
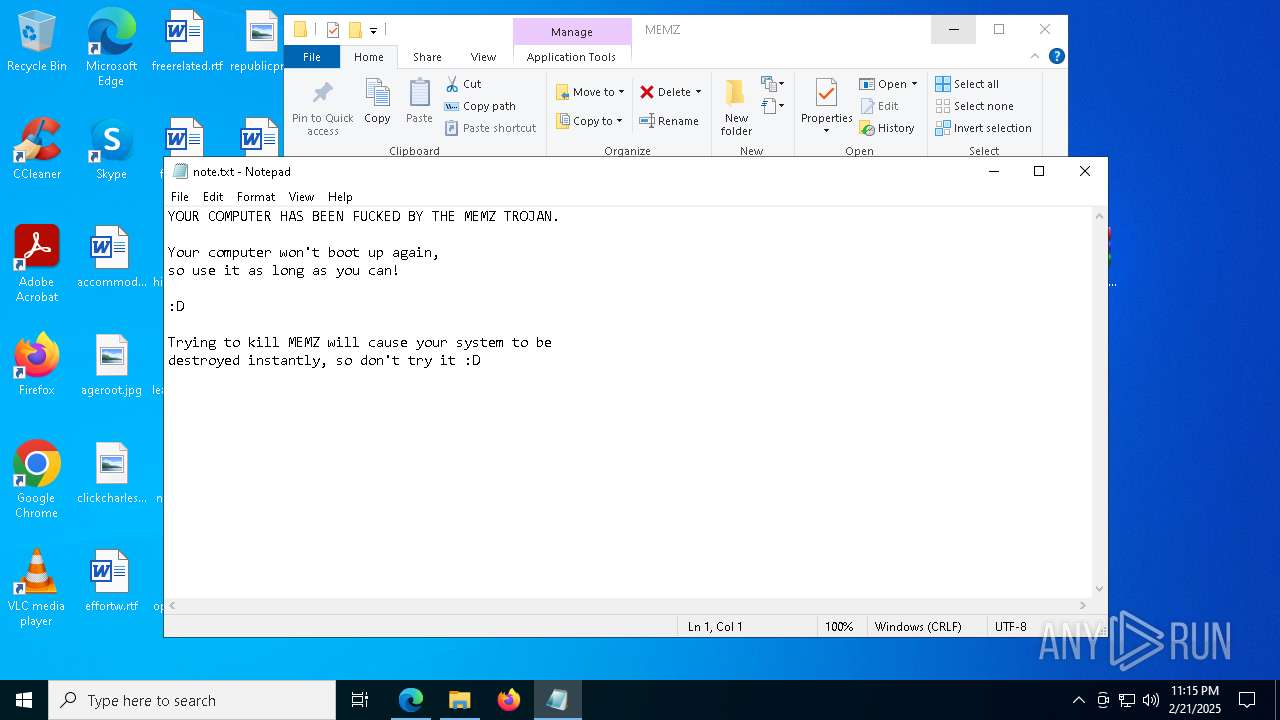
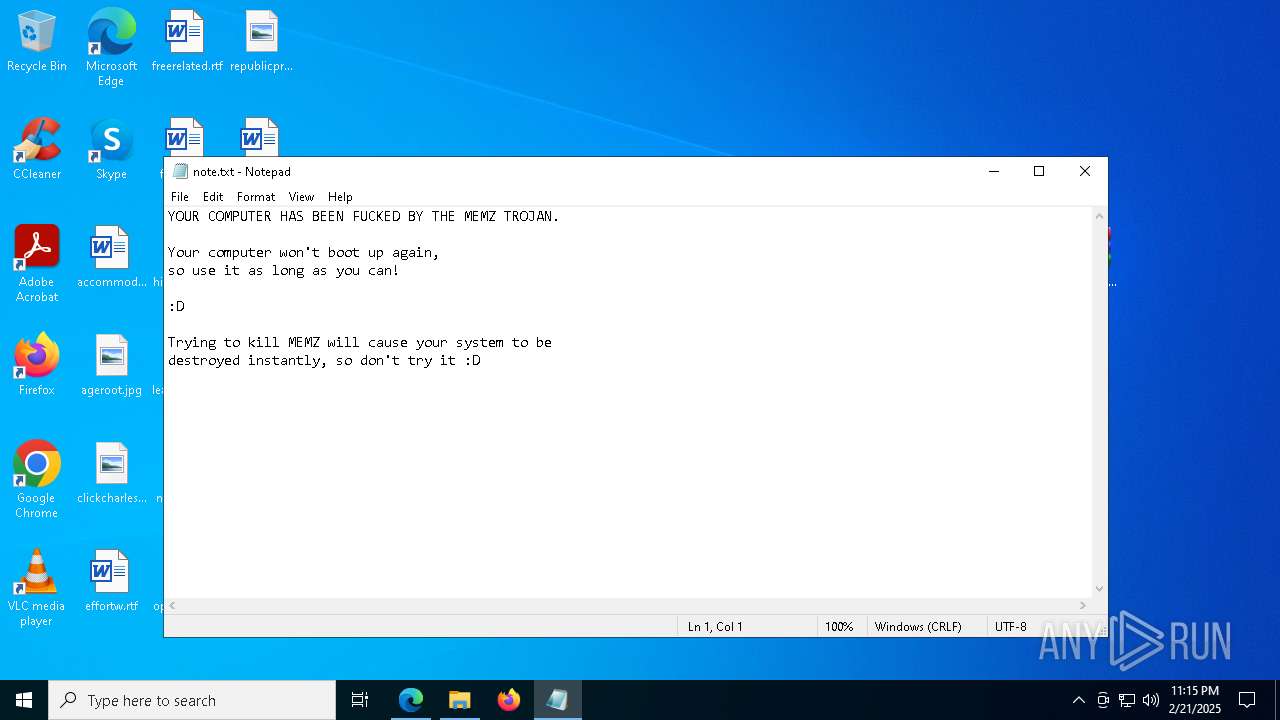
Start notepad (likely ransomware note)
- geometry dash auto speedhack.exe (PID: 5212)
Reads the date of Windows installation
- MrsMajor3.0.exe (PID: 8964)
Runs shell command (SCRIPT)
- wscript.exe (PID: 9016)
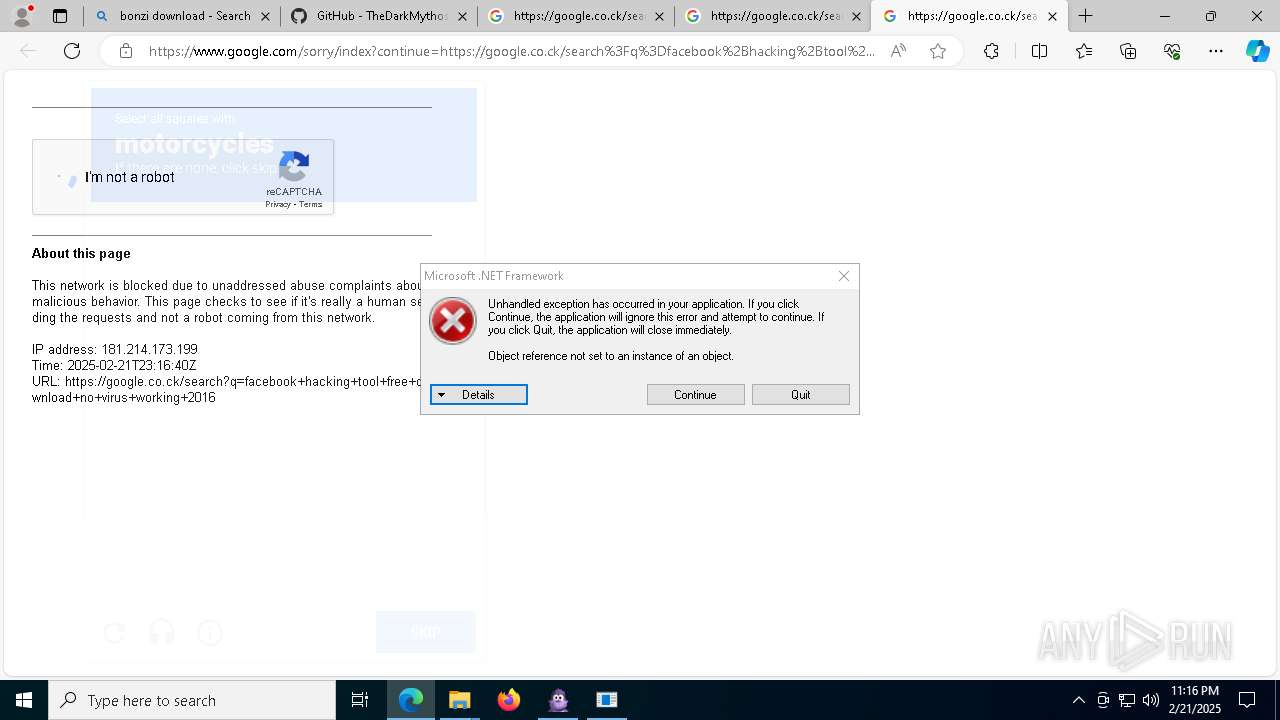
The process executes VB scripts
- MrsMajor3.0.exe (PID: 8964)
Runs WScript without displaying logo
- wscript.exe (PID: 9016)
INFO
Application launched itself
- msedge.exe (PID: 6332)
- firefox.exe (PID: 7652)
- firefox.exe (PID: 7992)
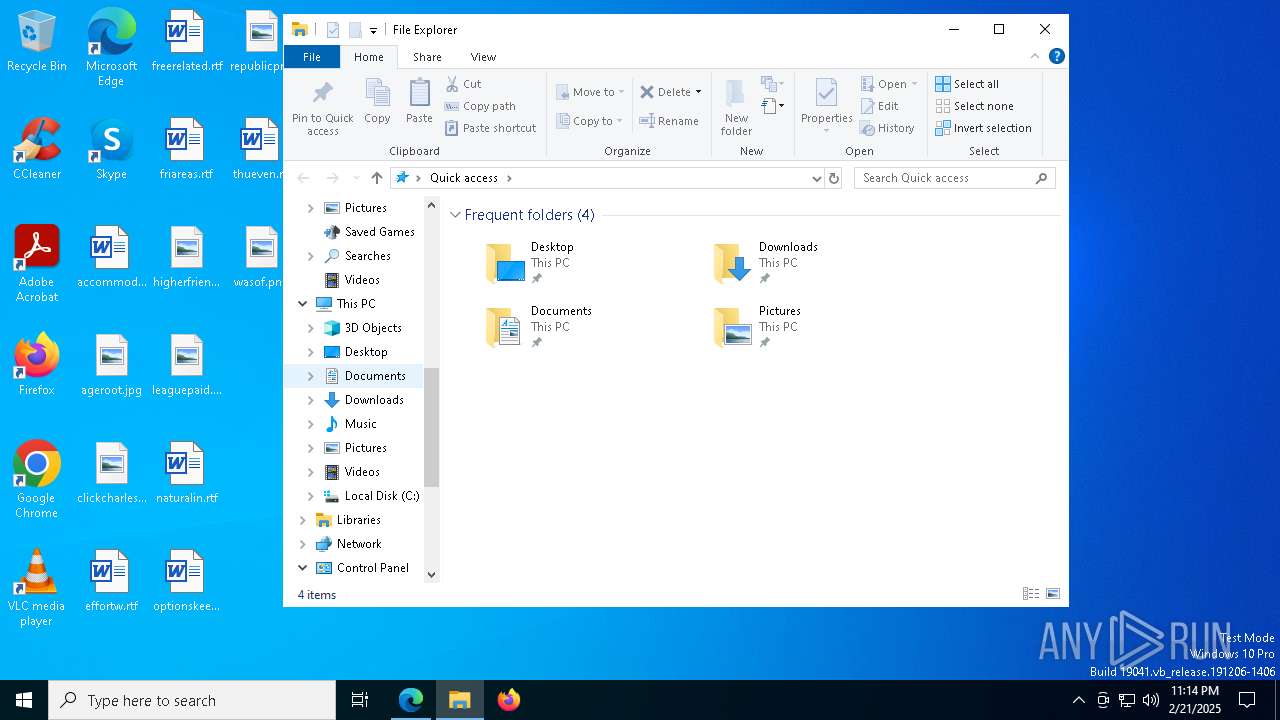
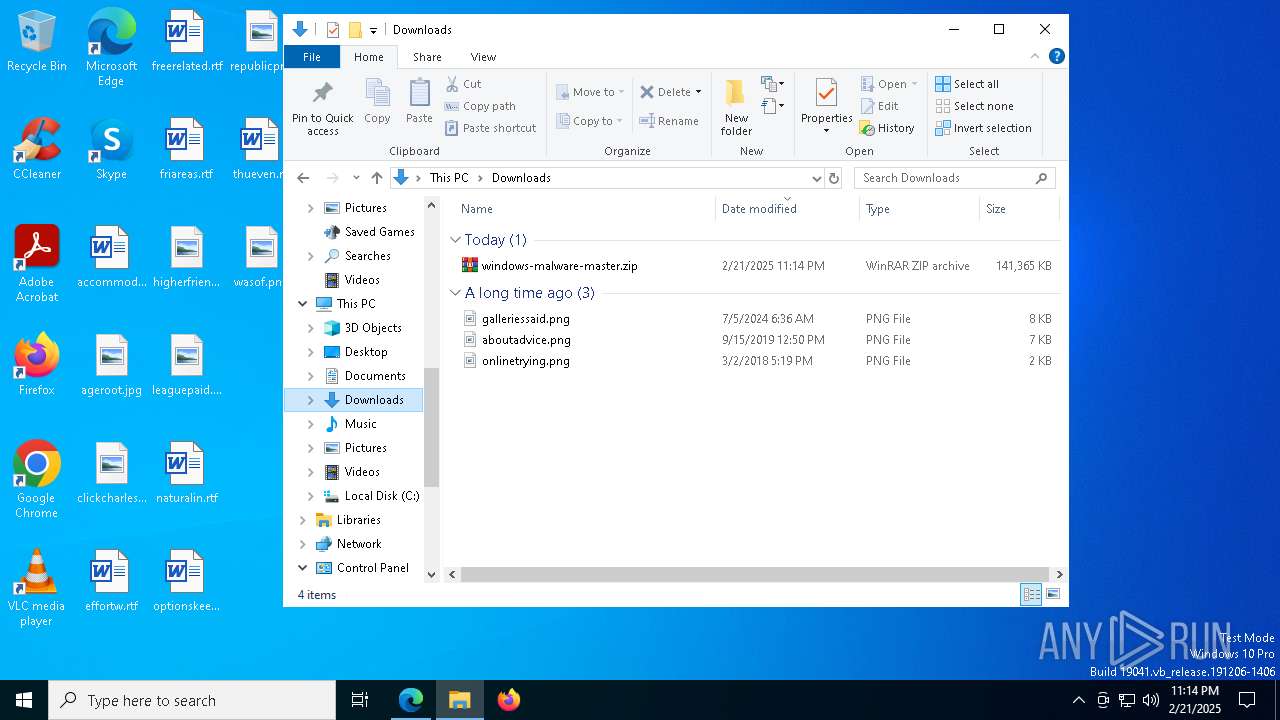
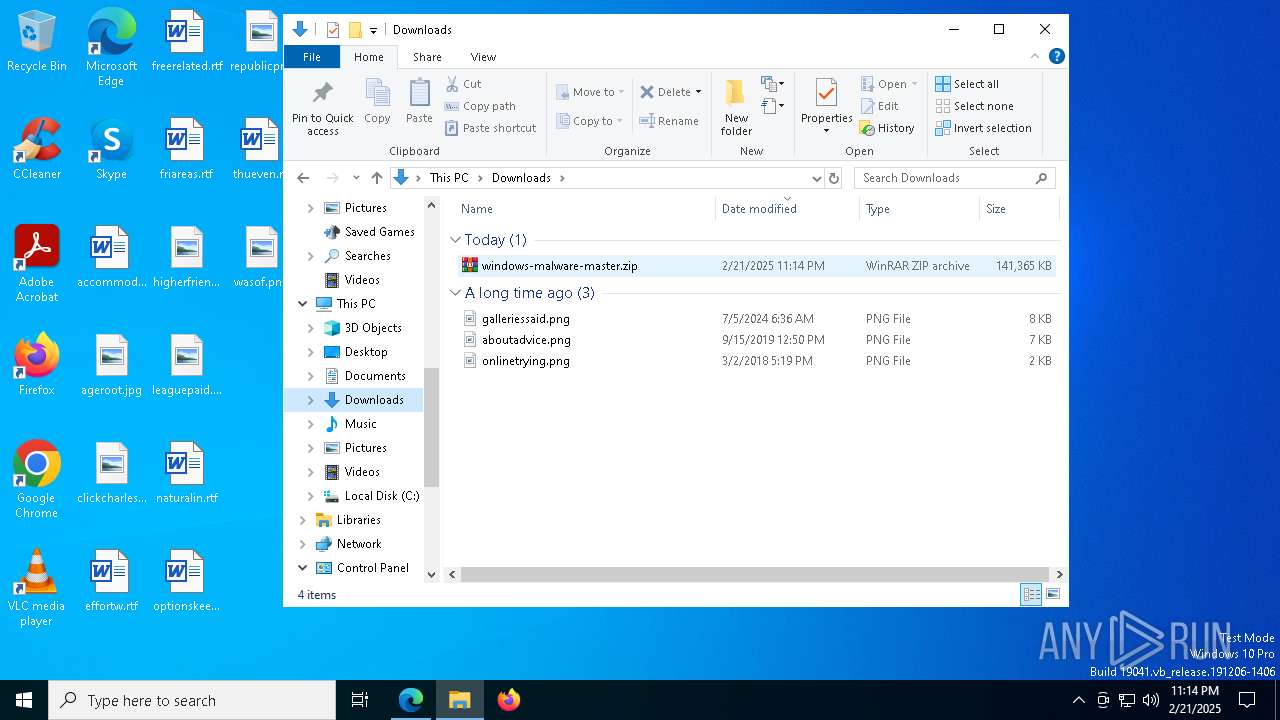
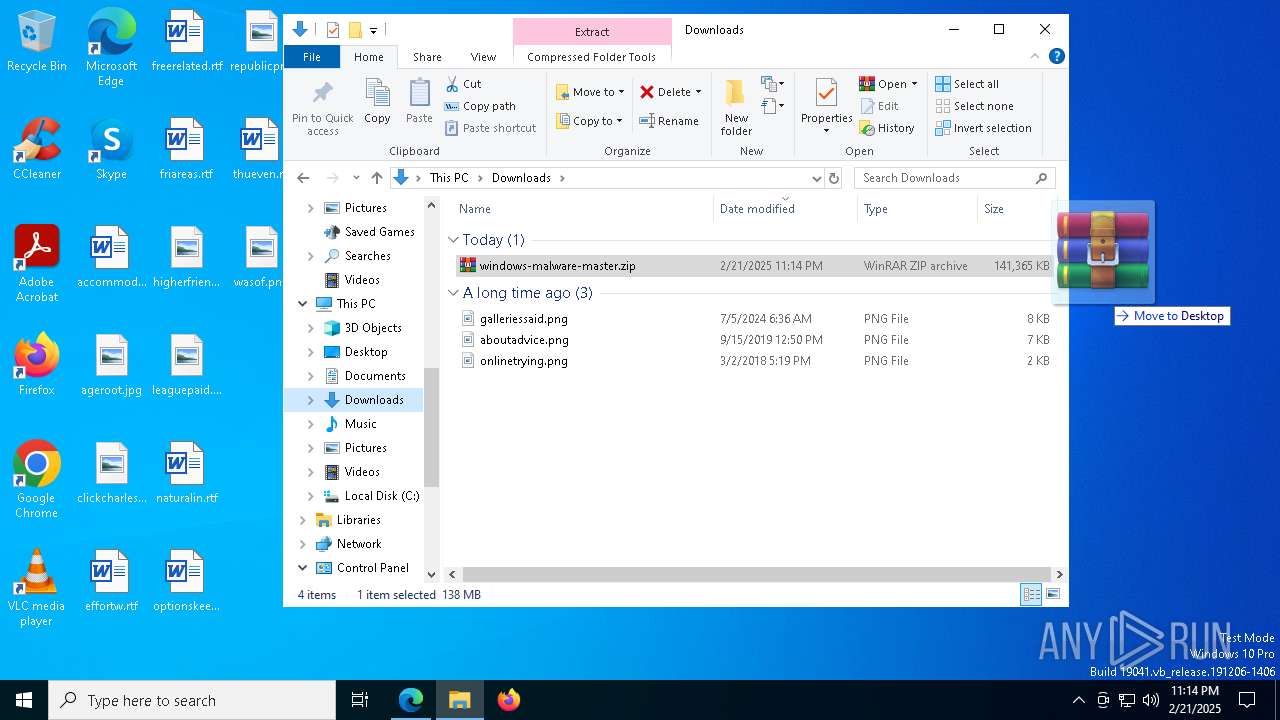
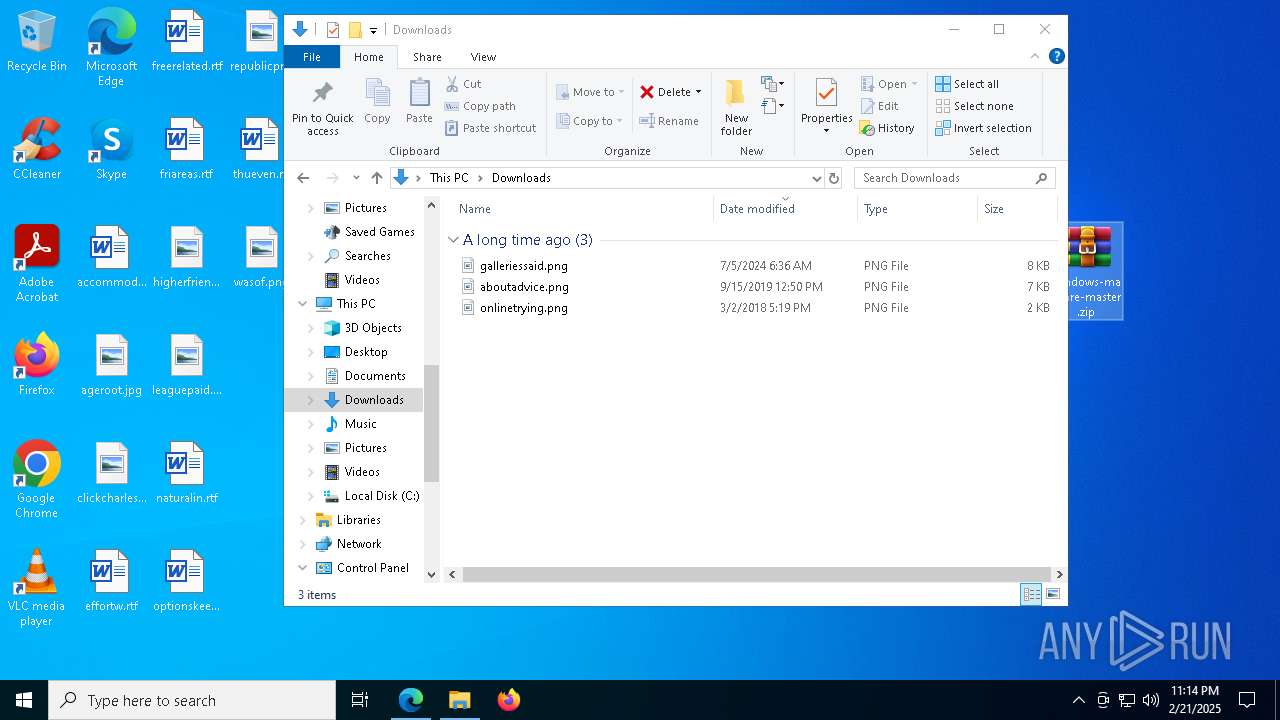
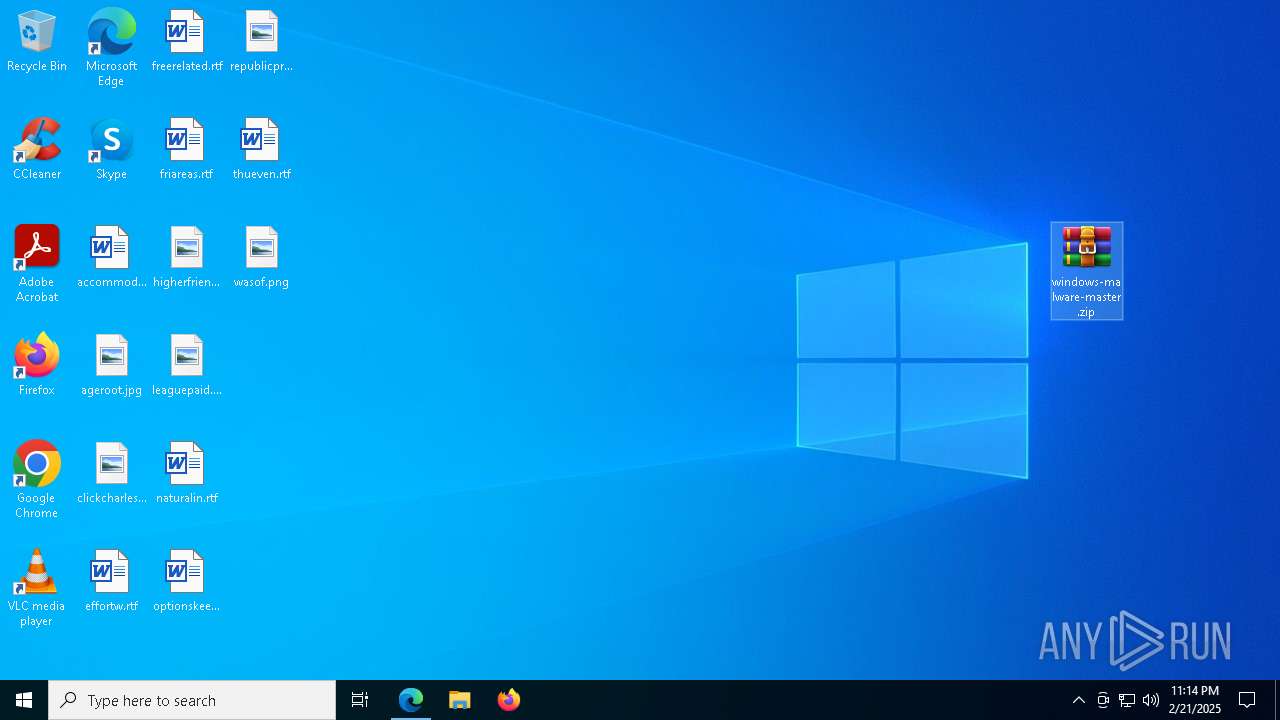
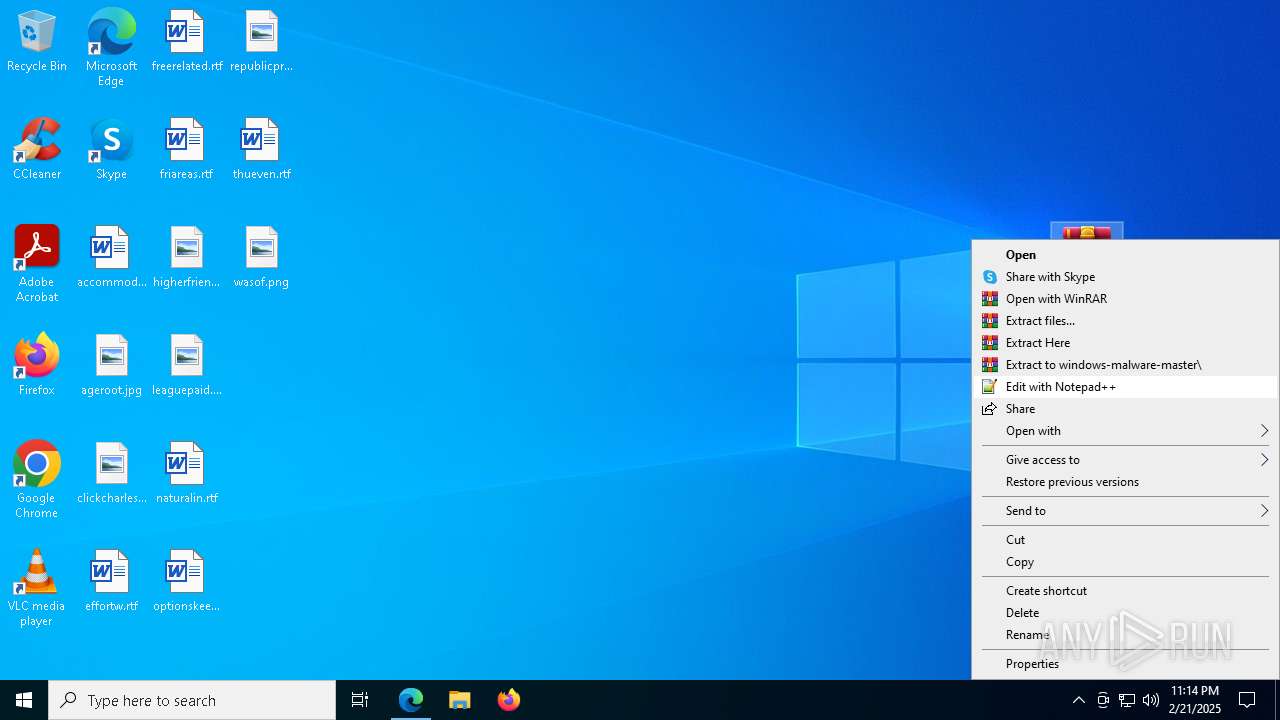
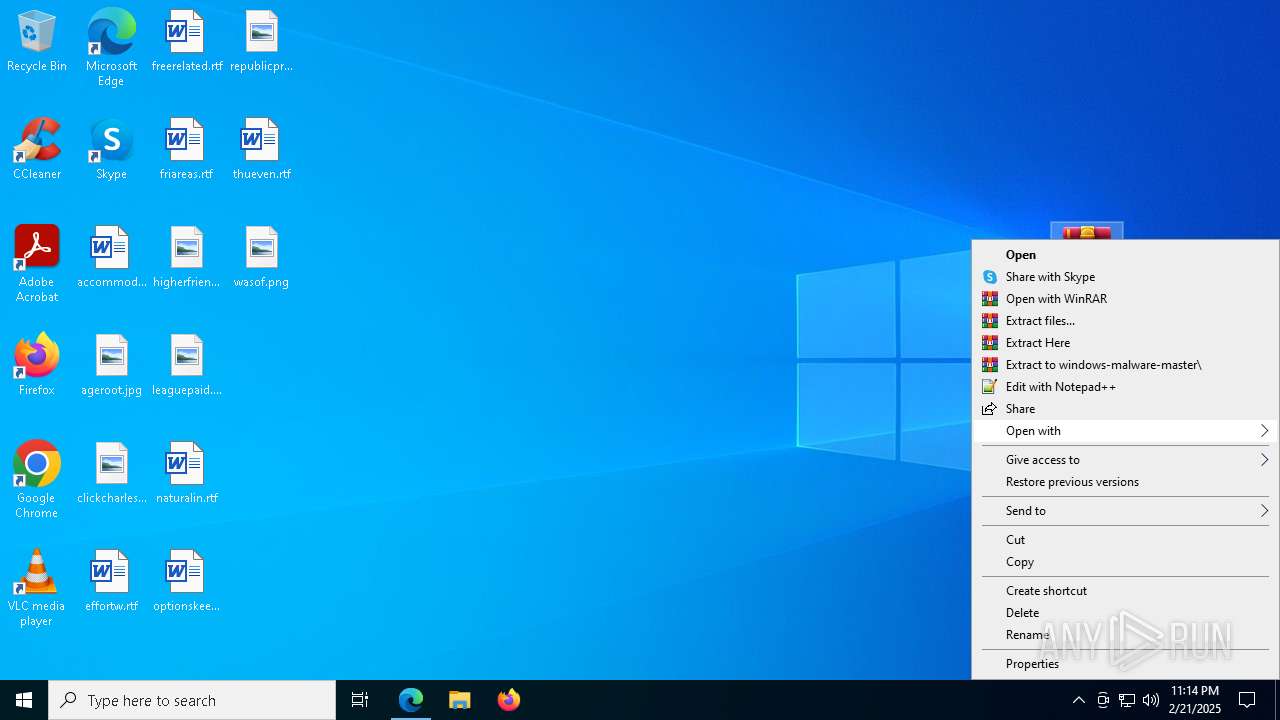
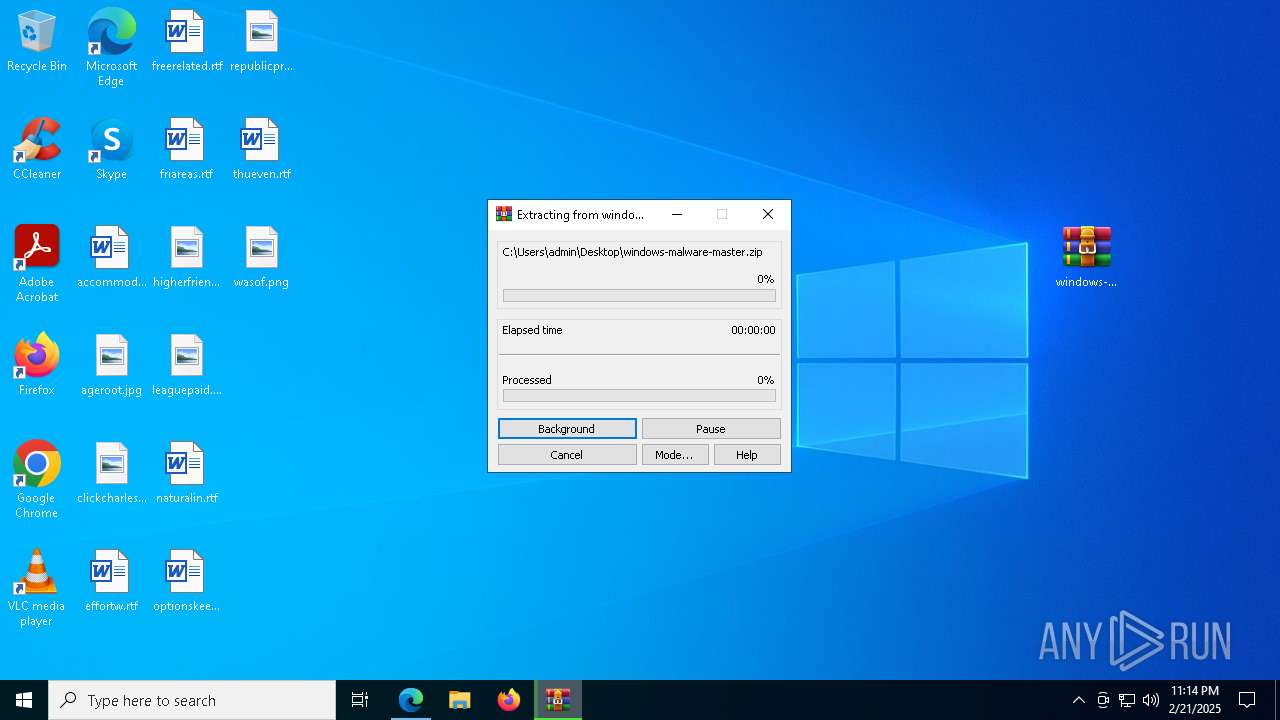
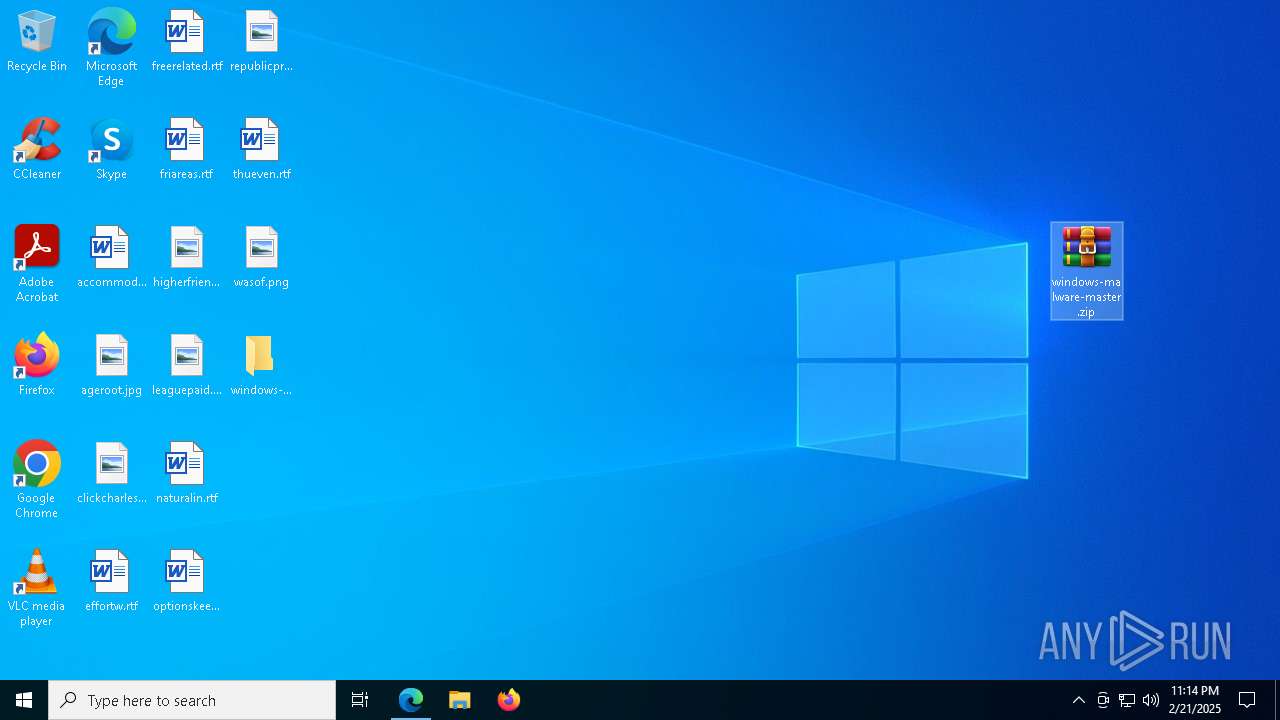
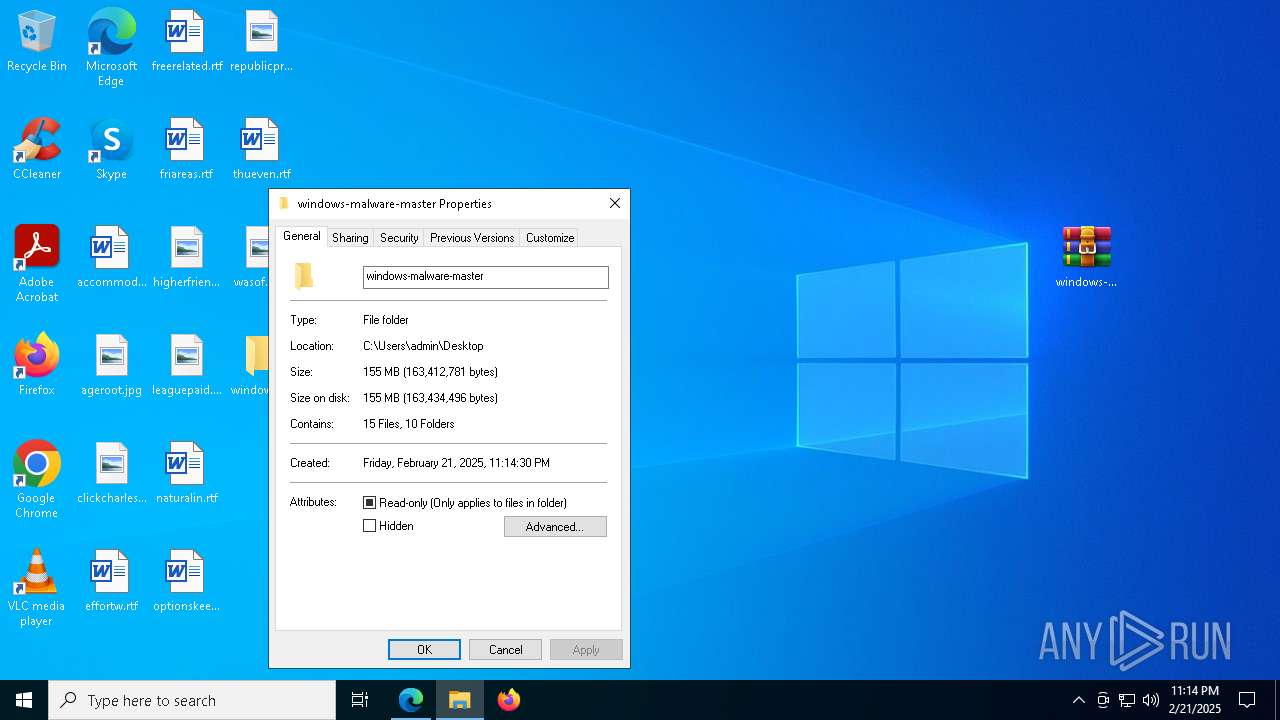
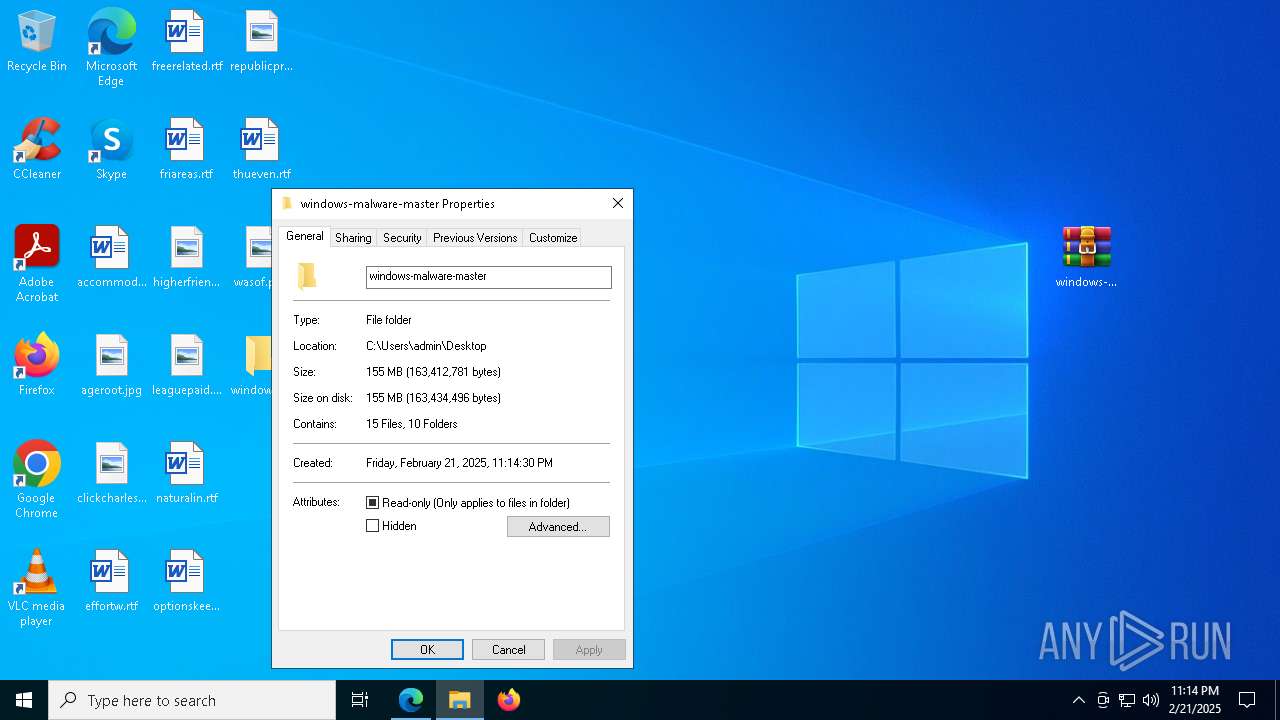
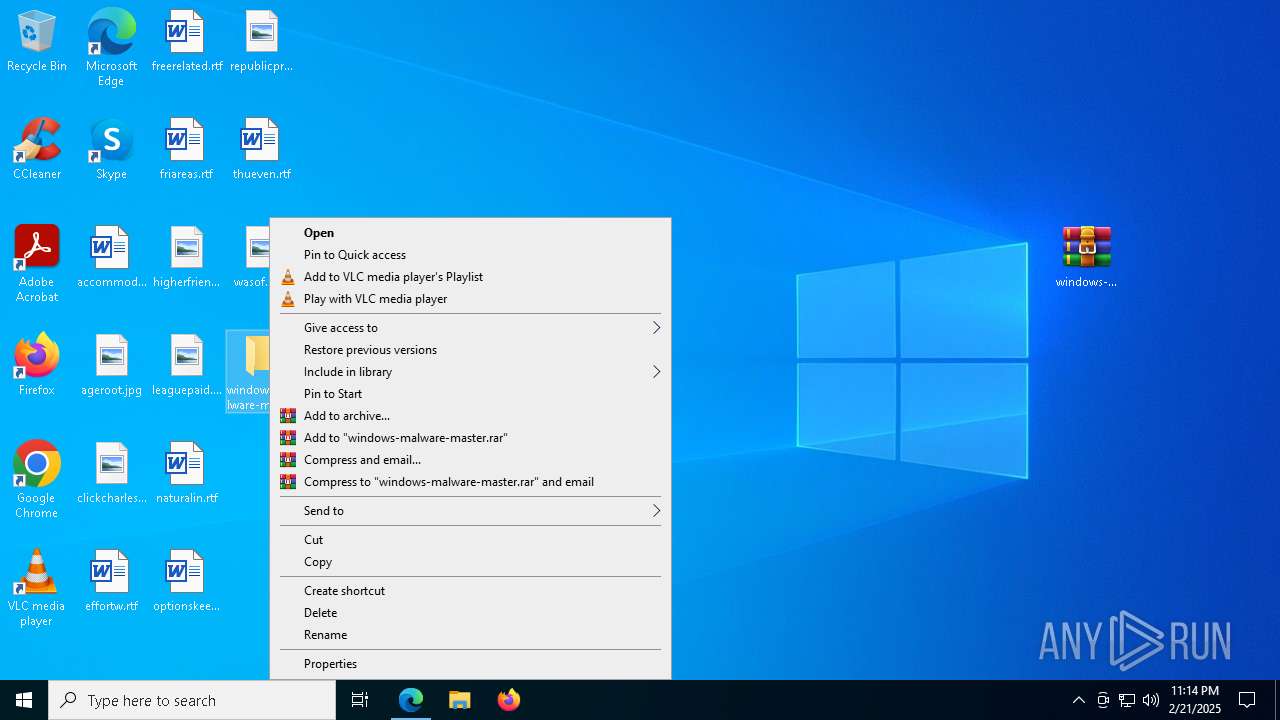
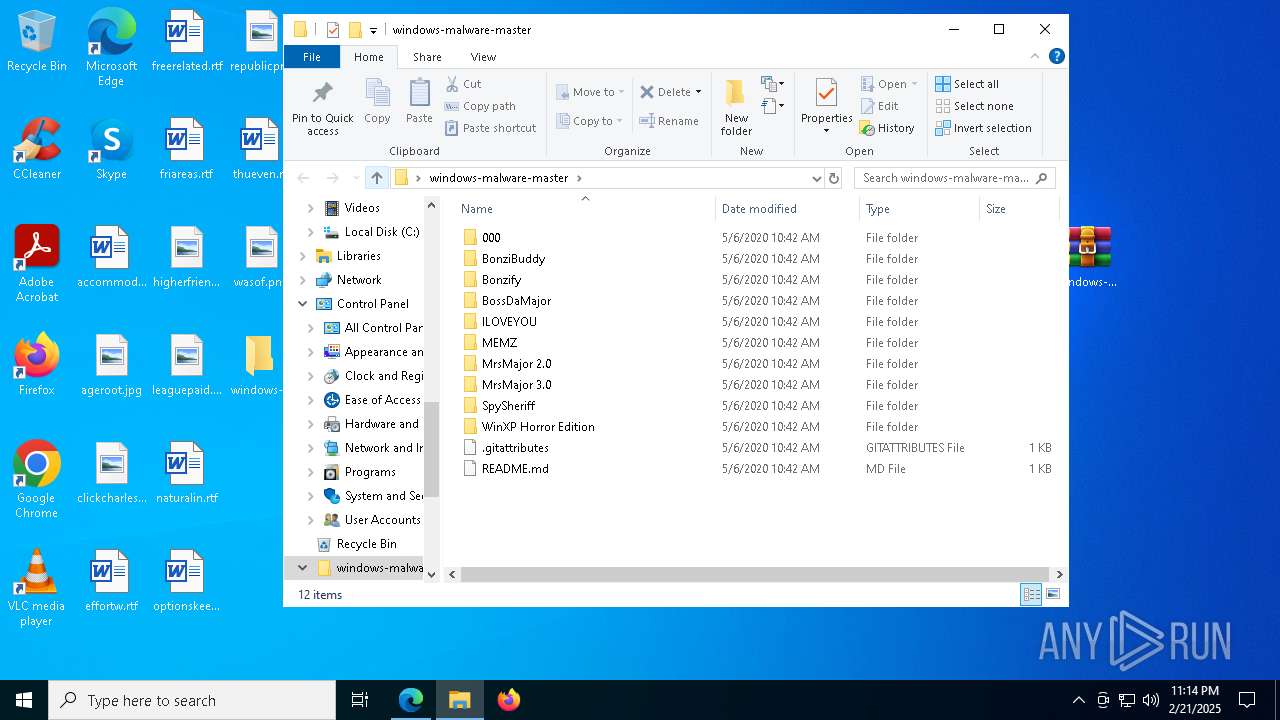
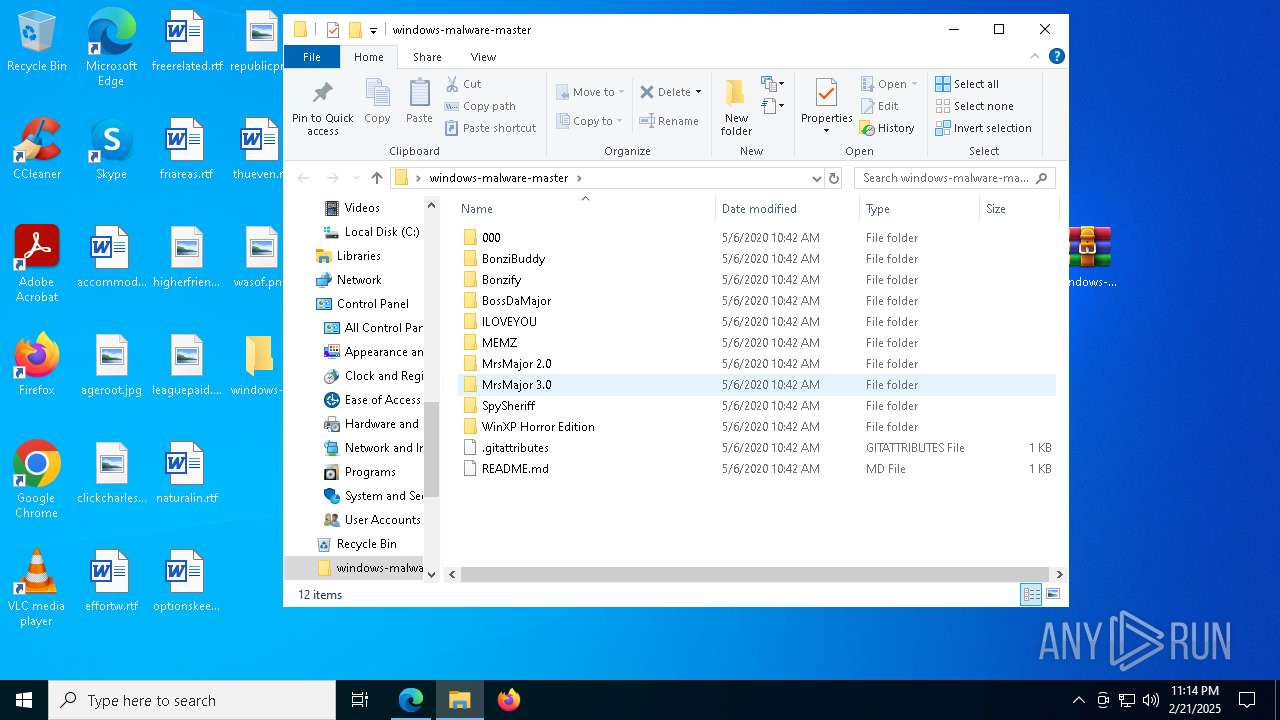
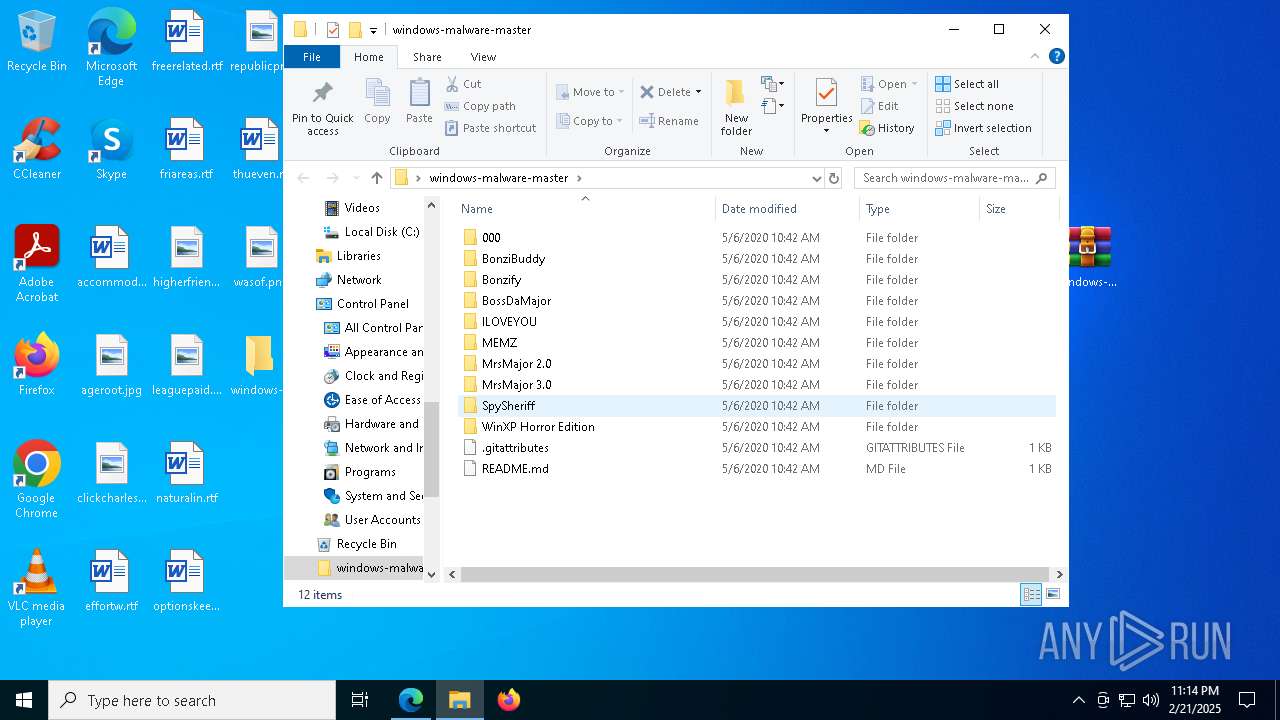
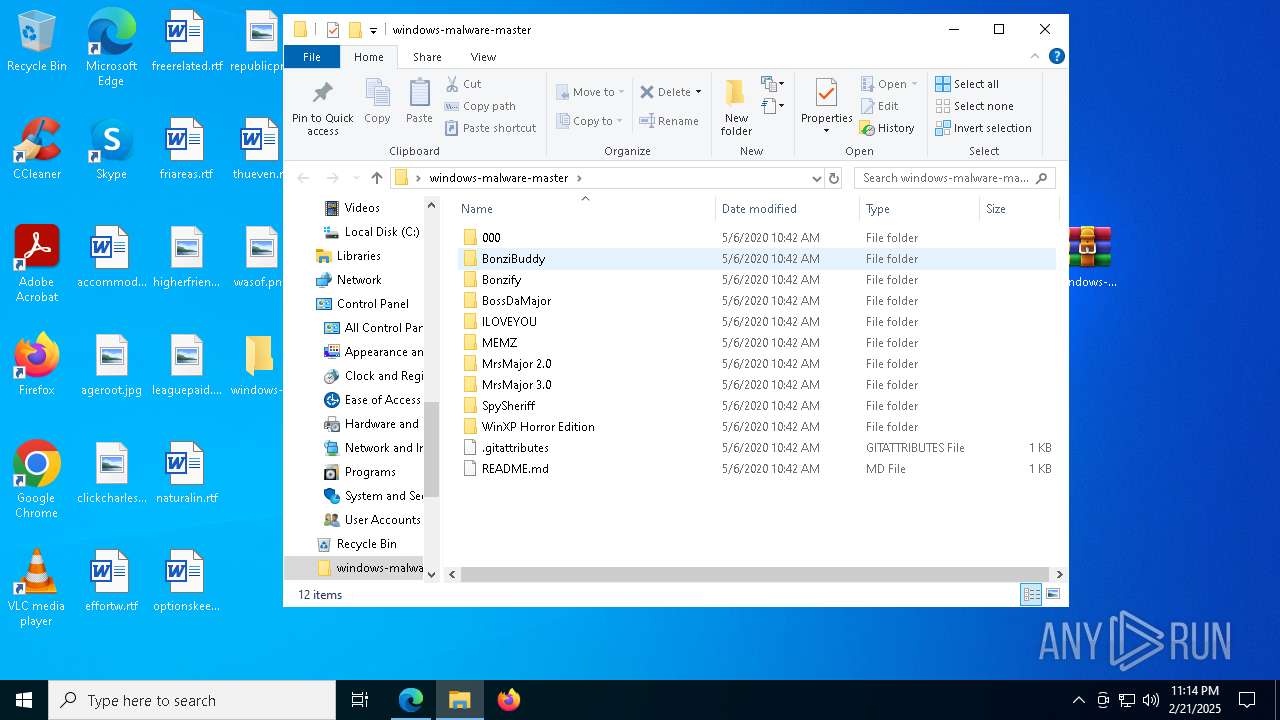
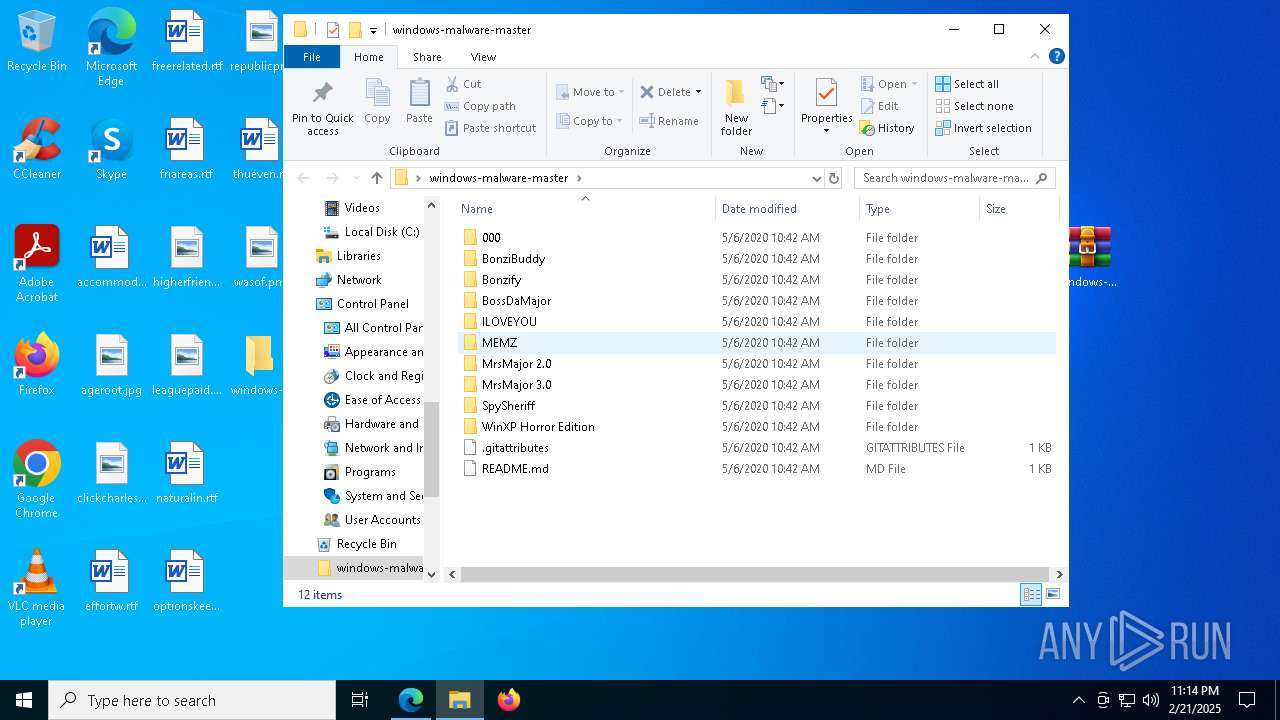
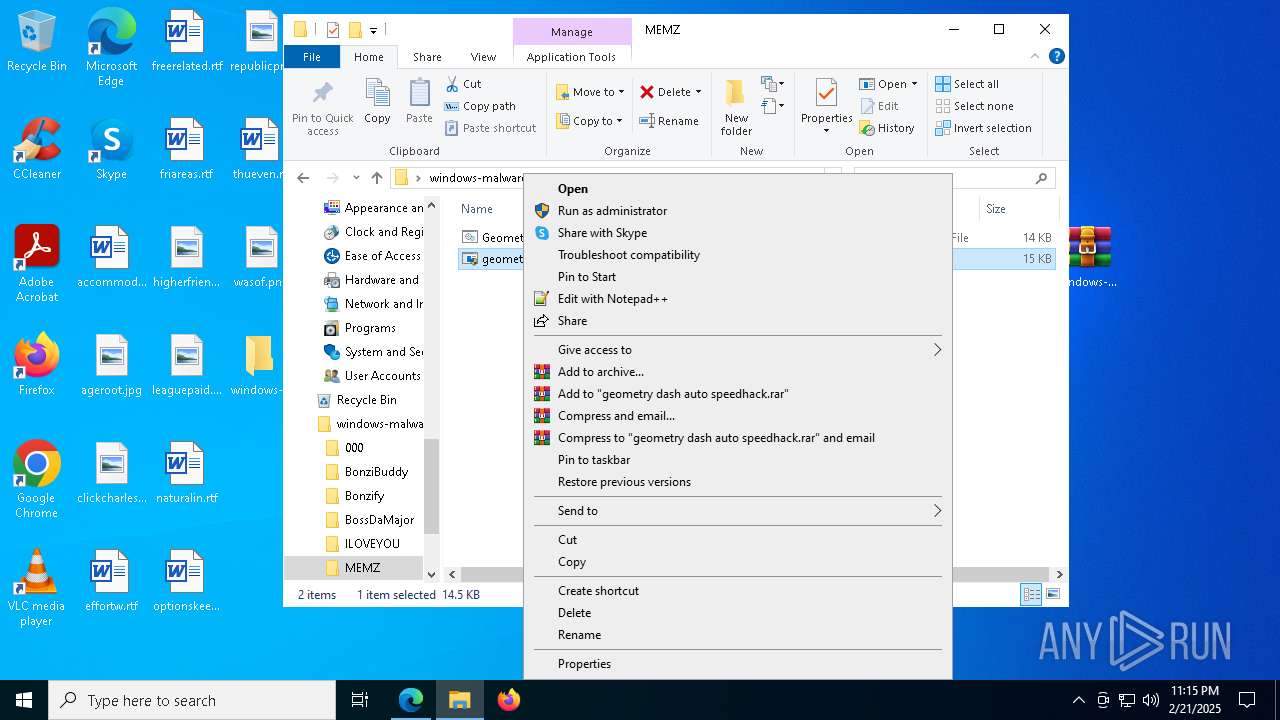
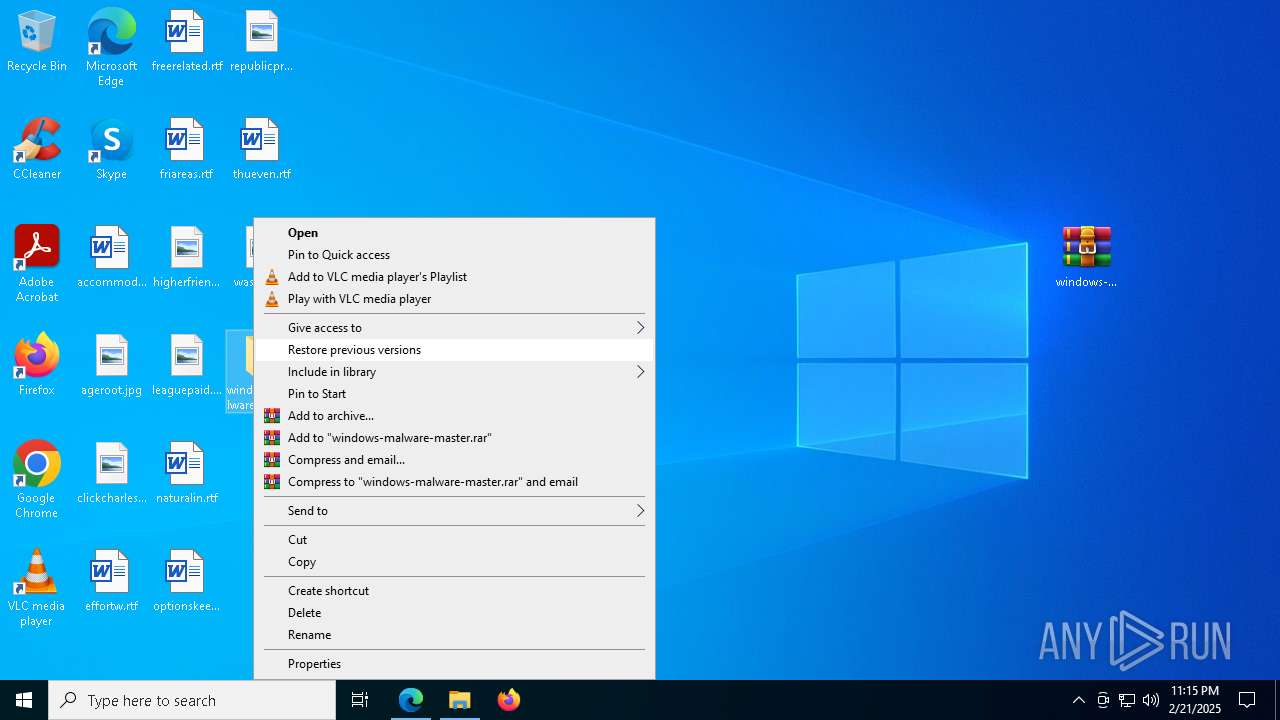
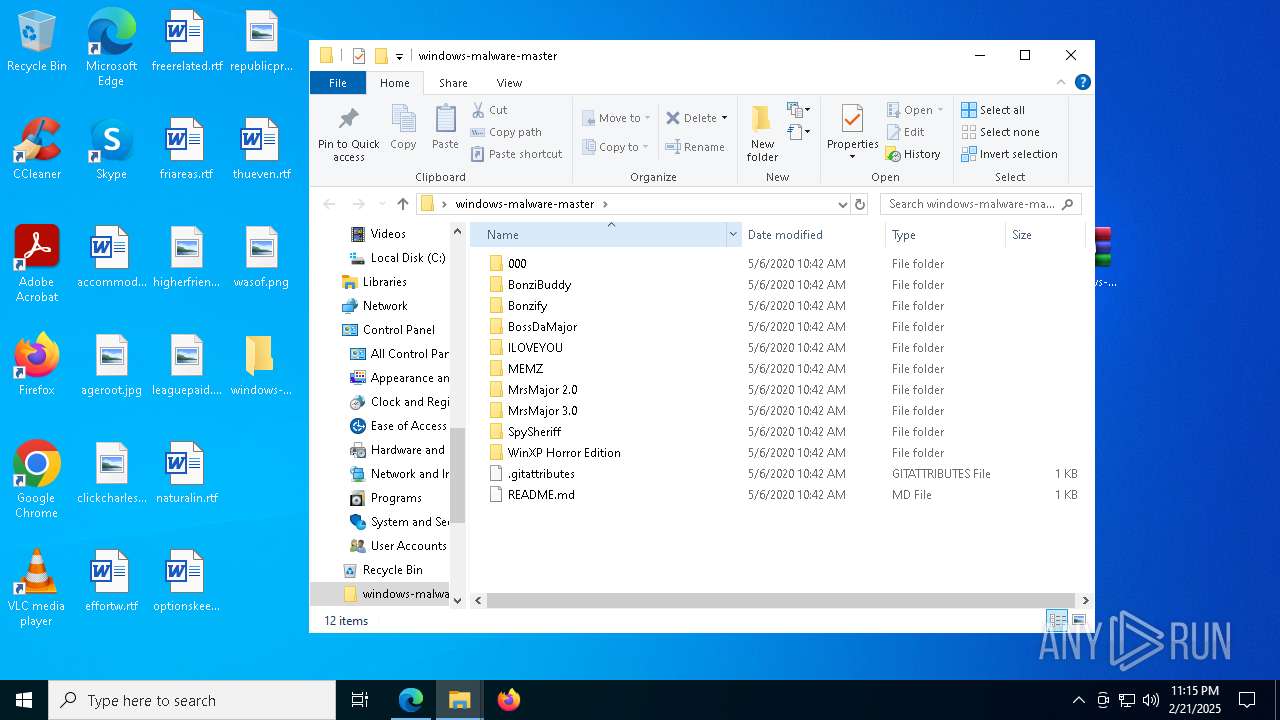
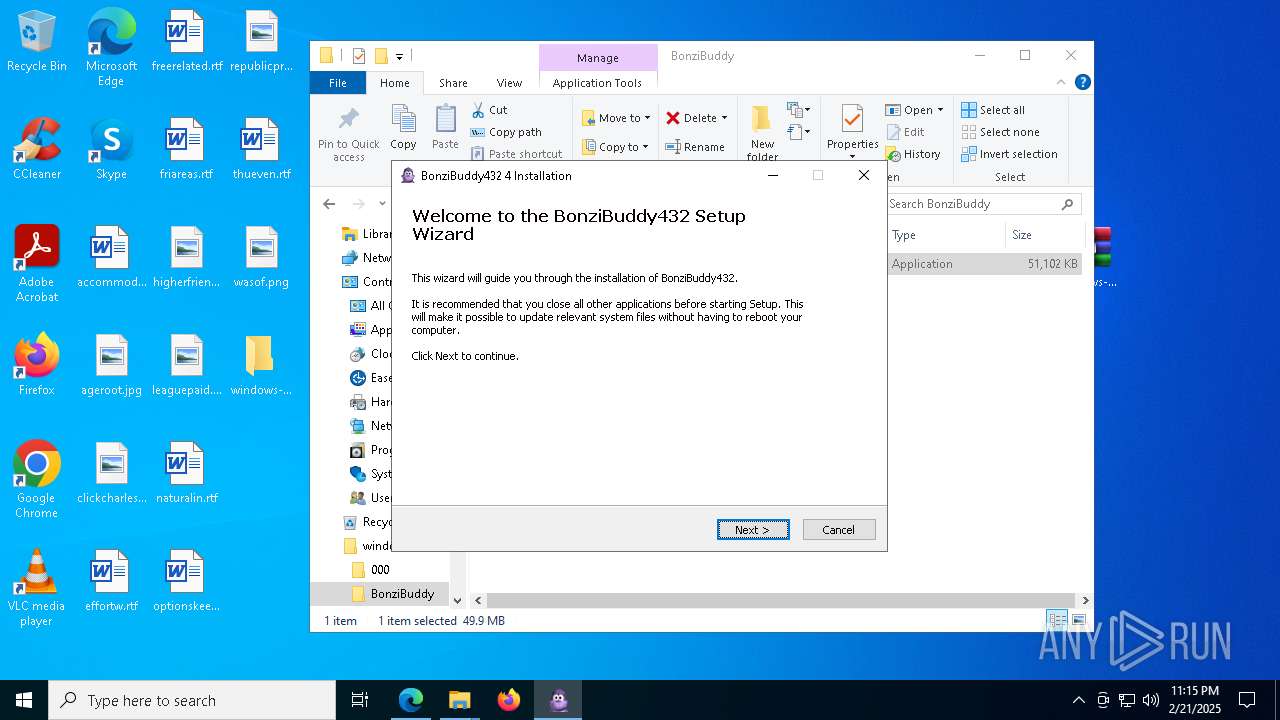
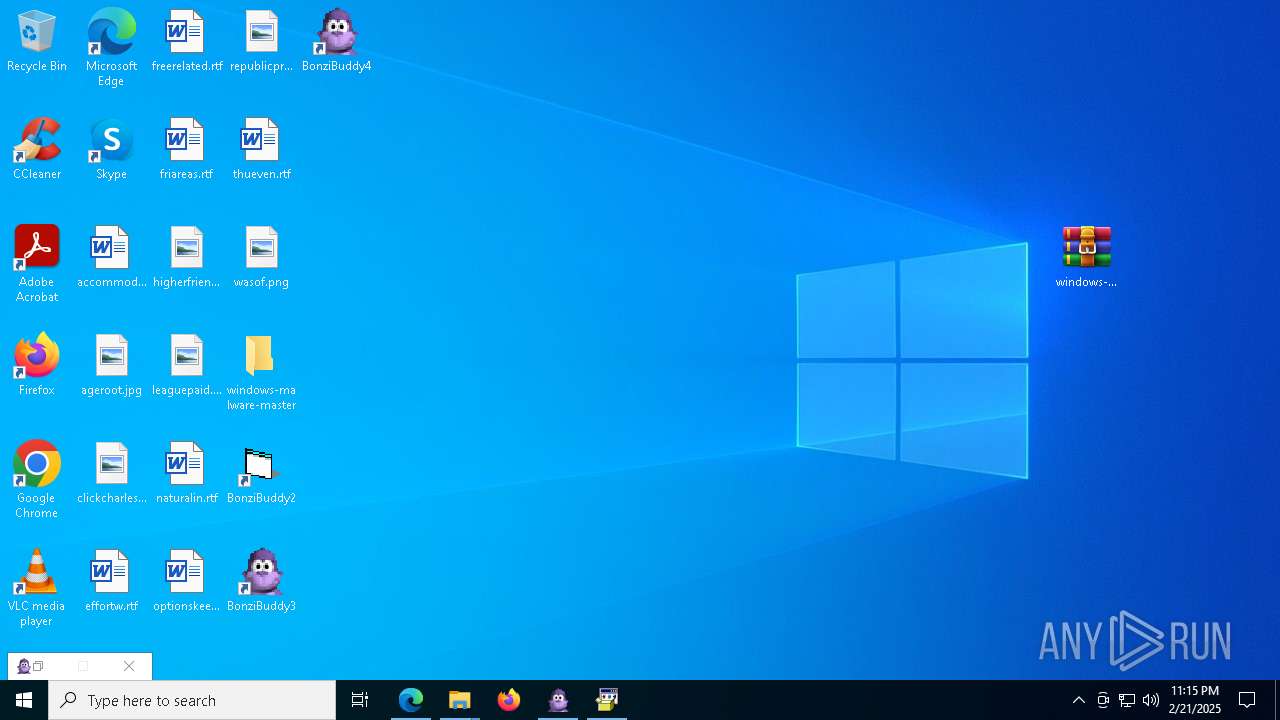
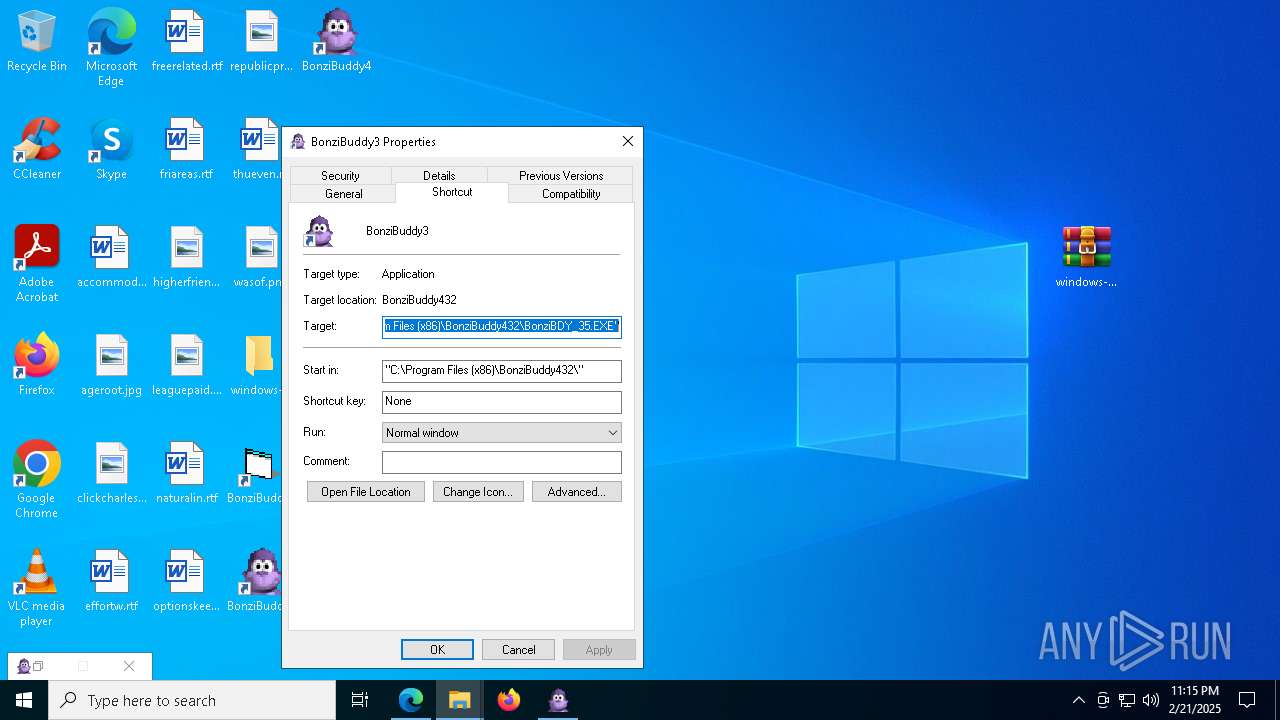
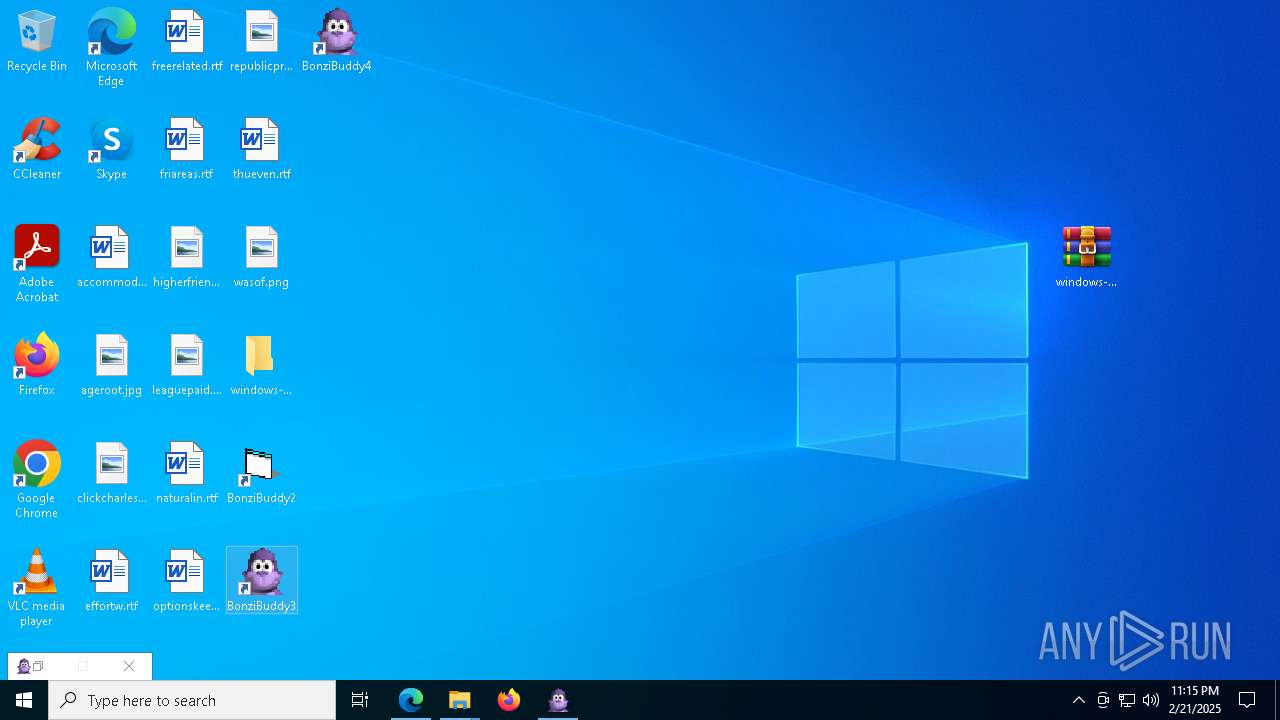
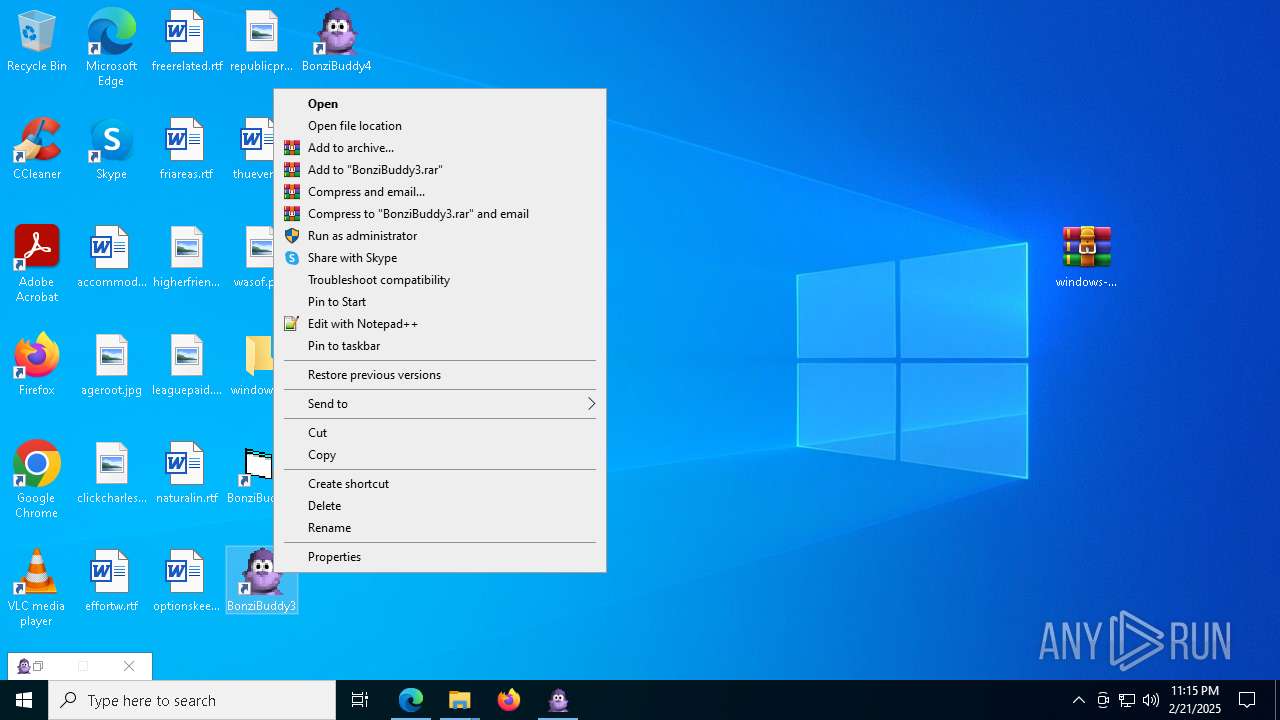
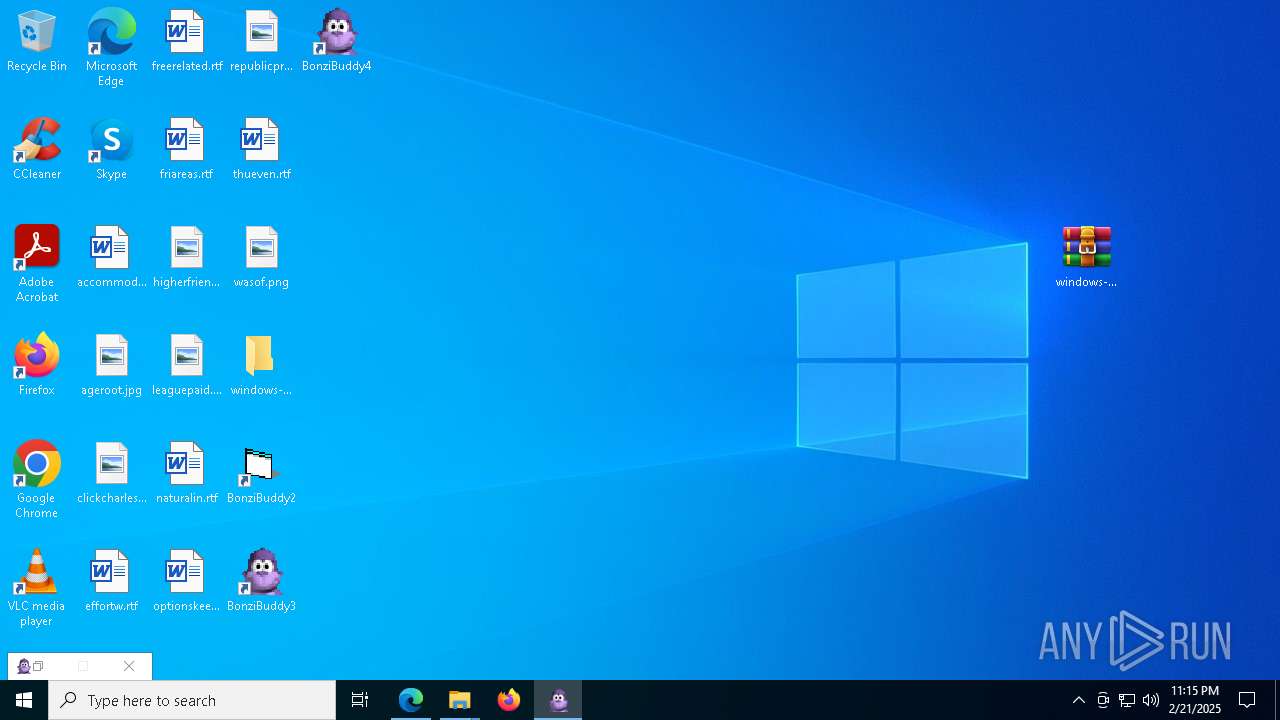
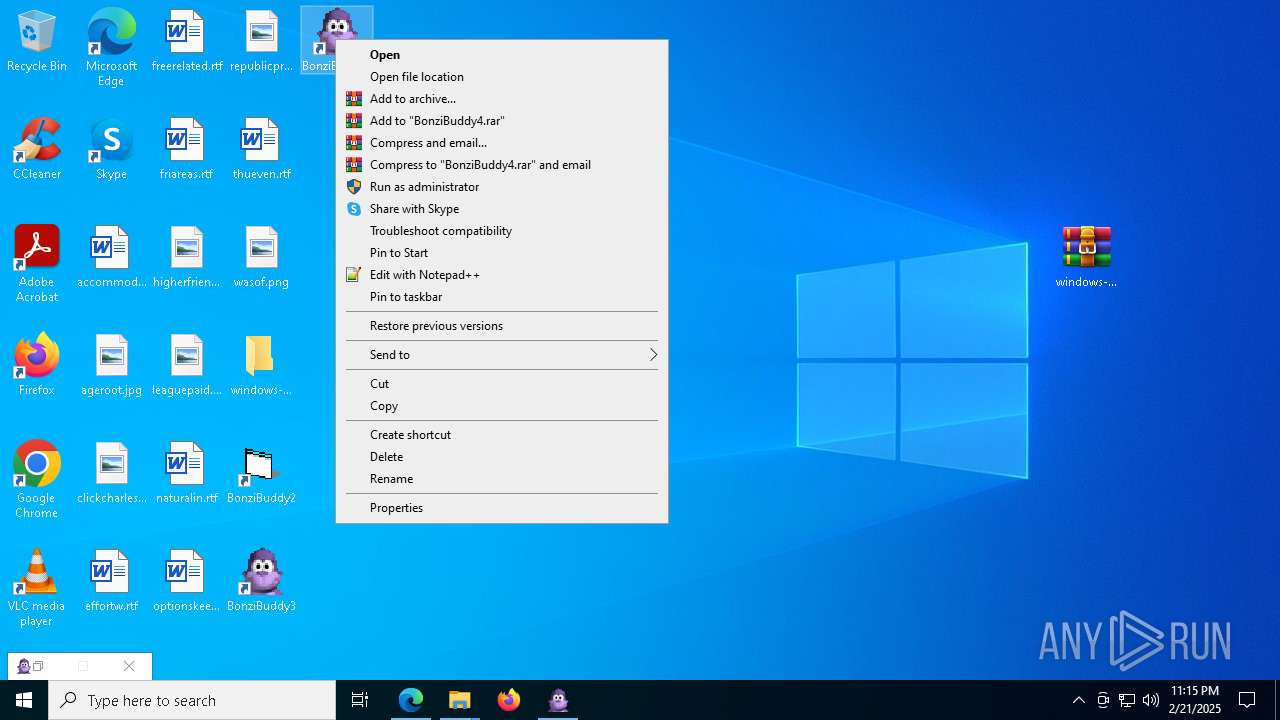
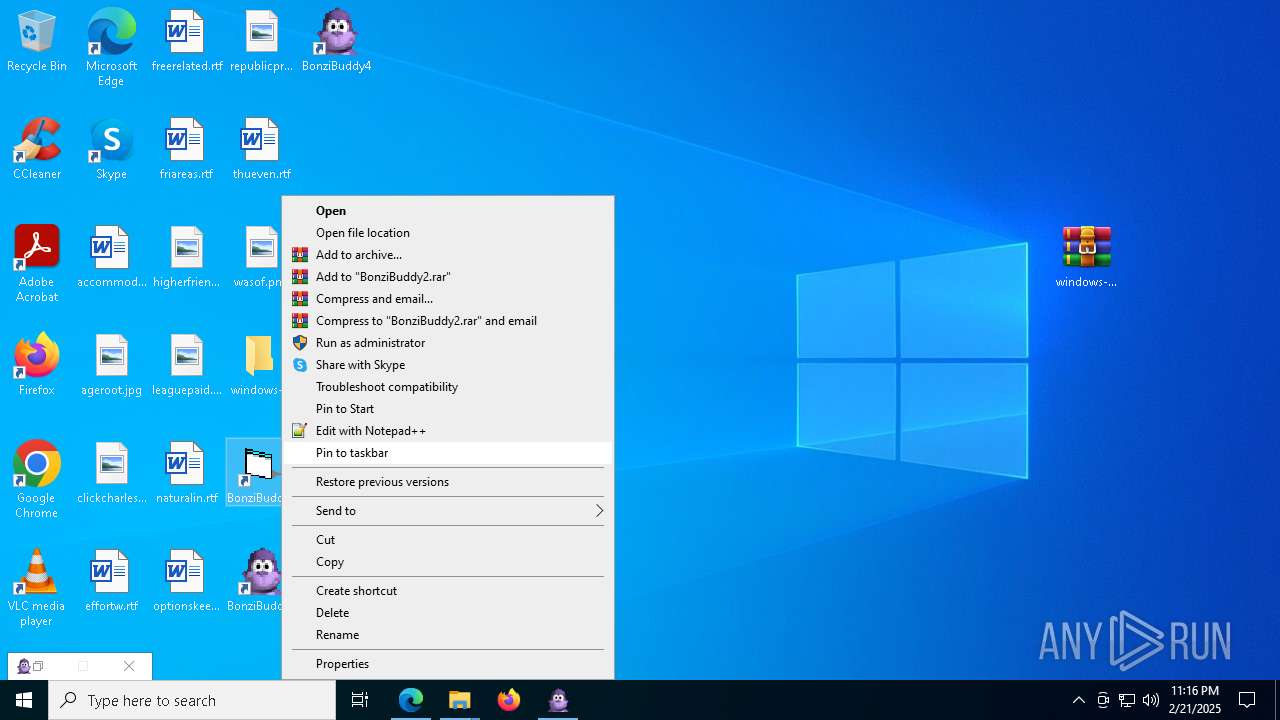
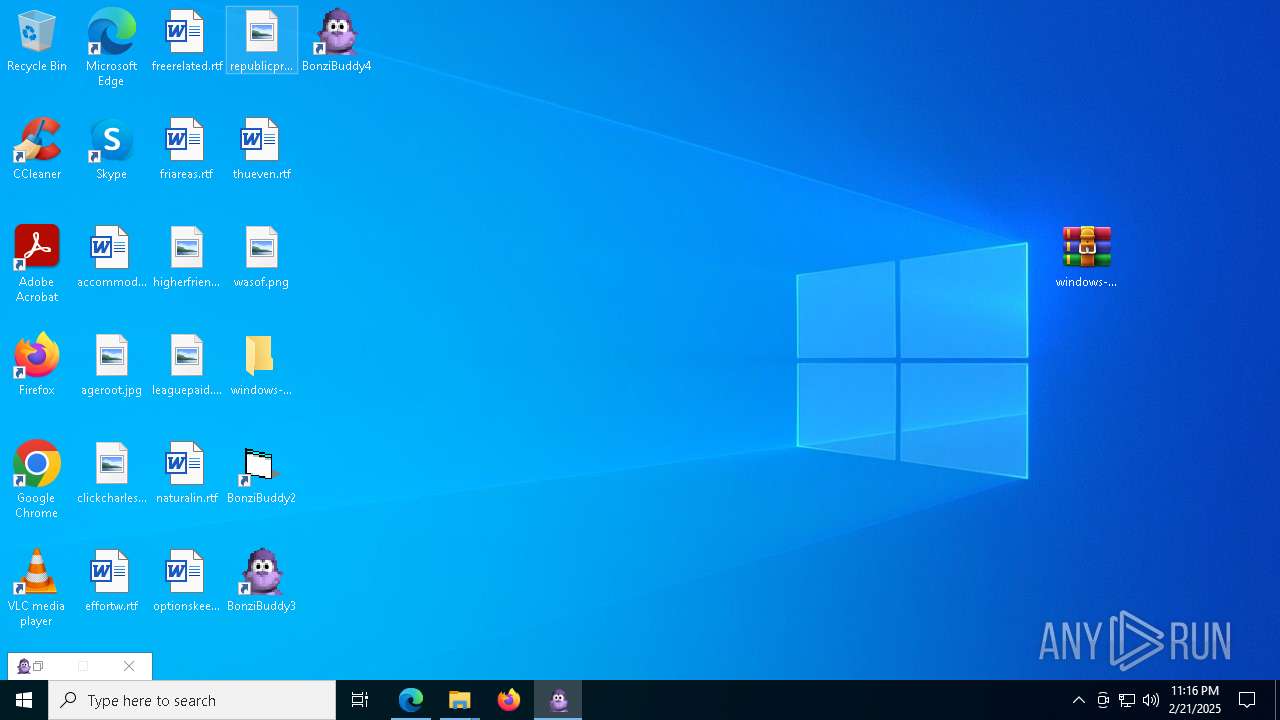
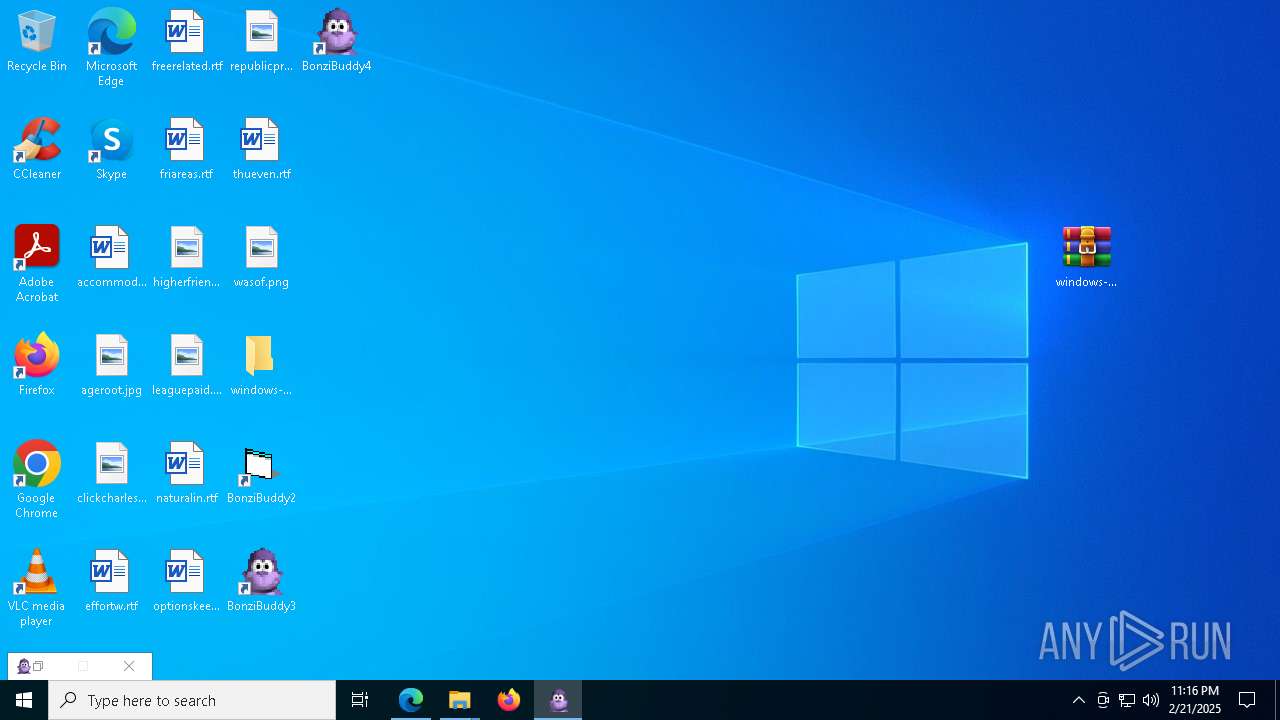
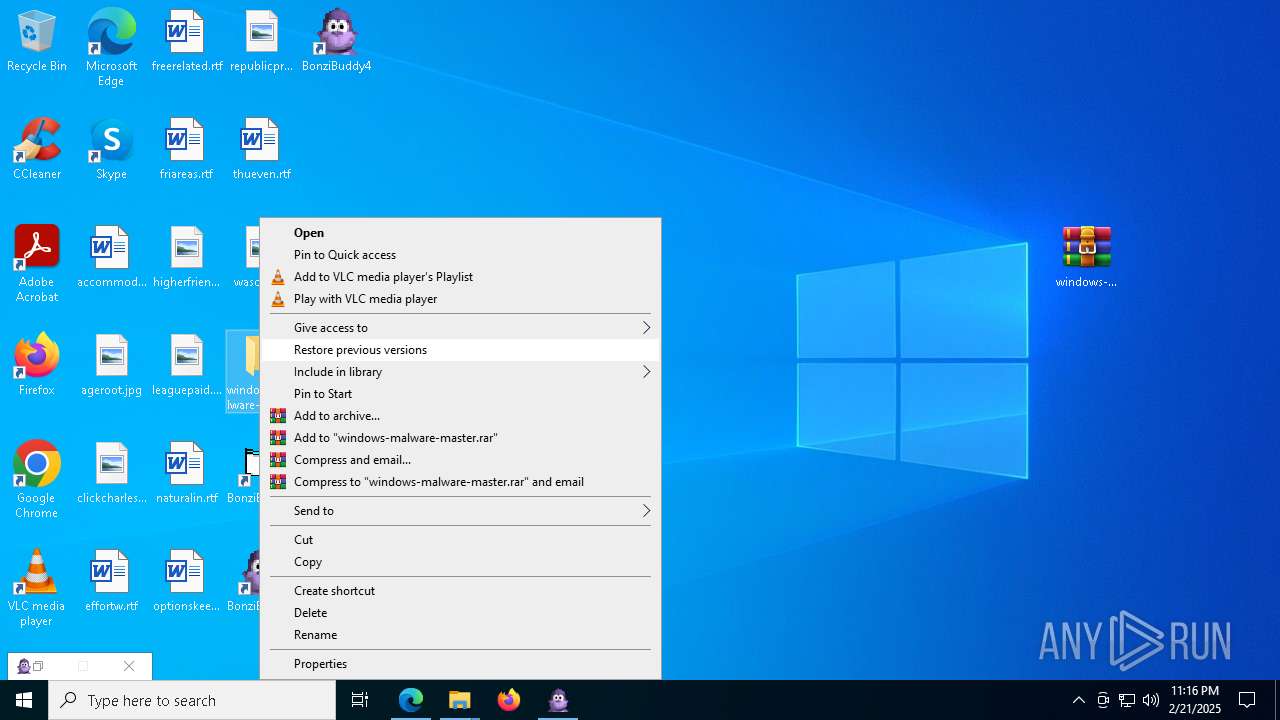
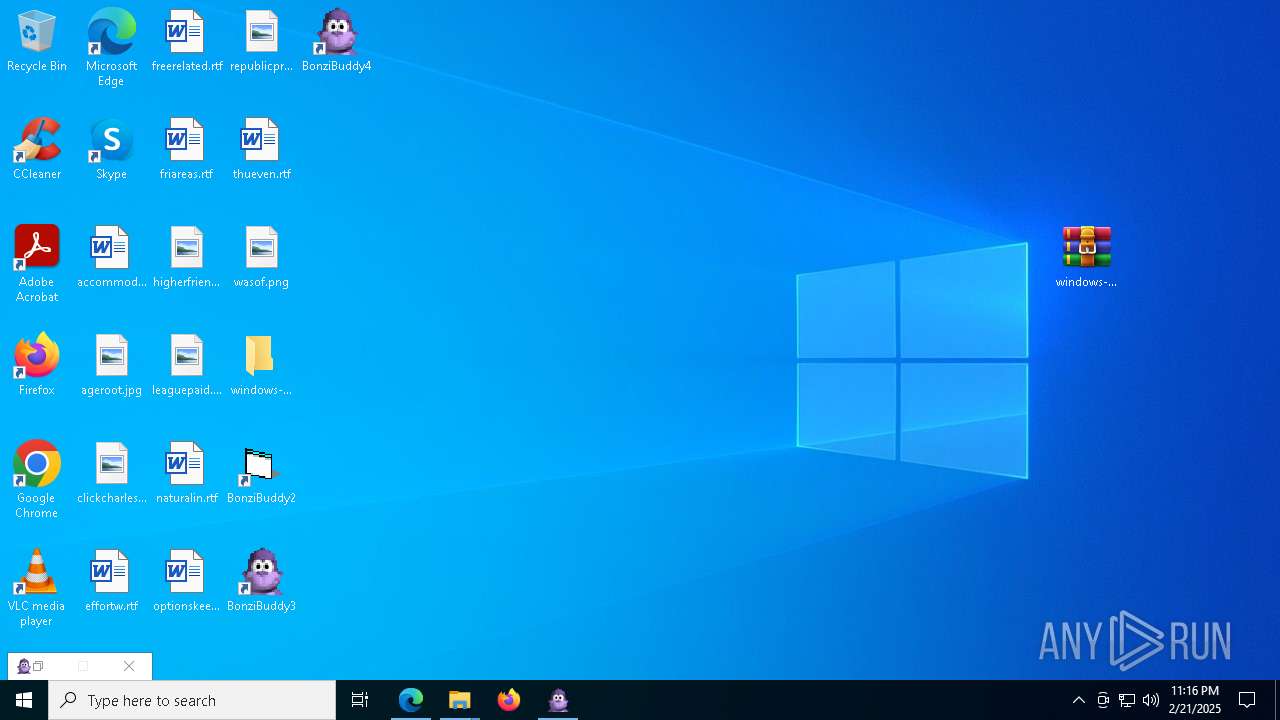
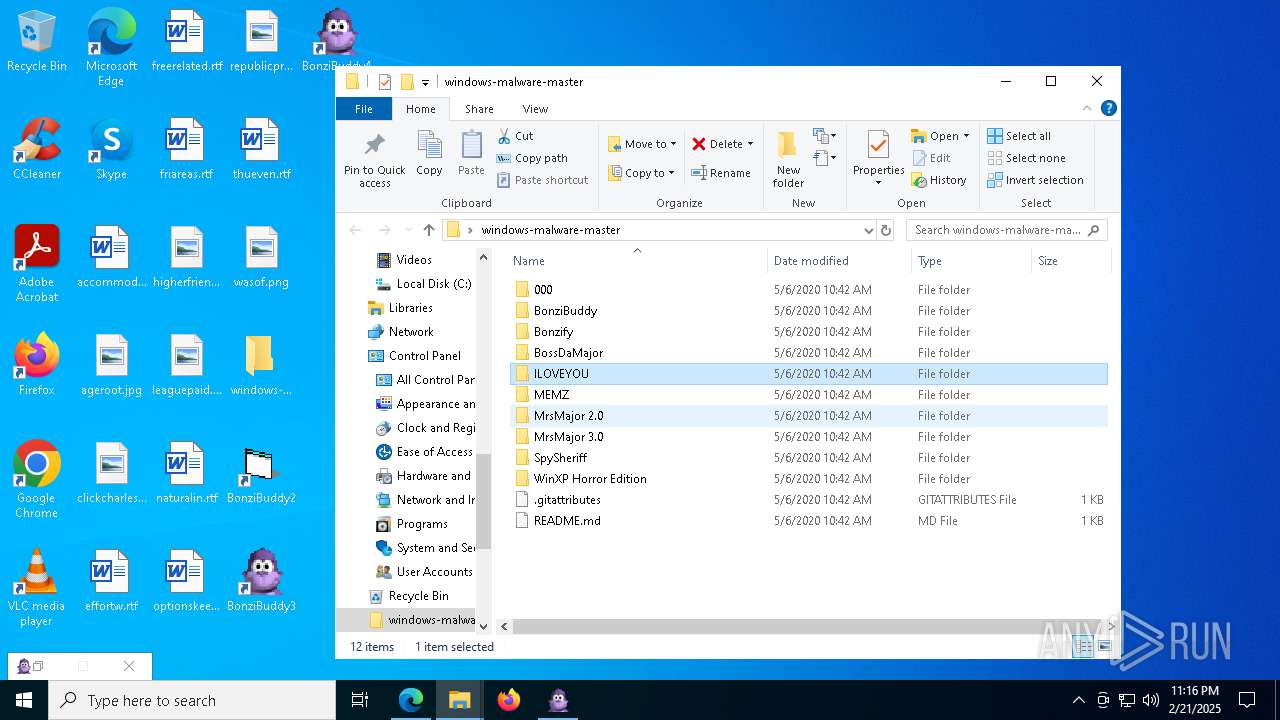
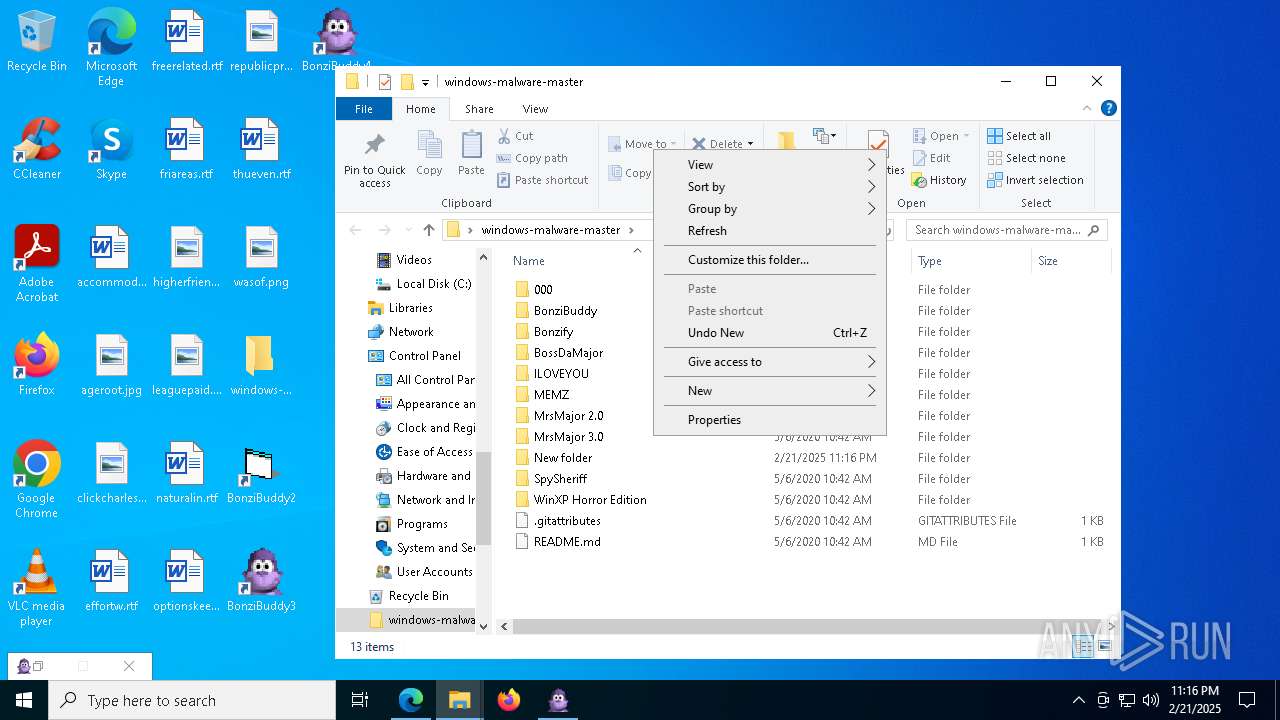
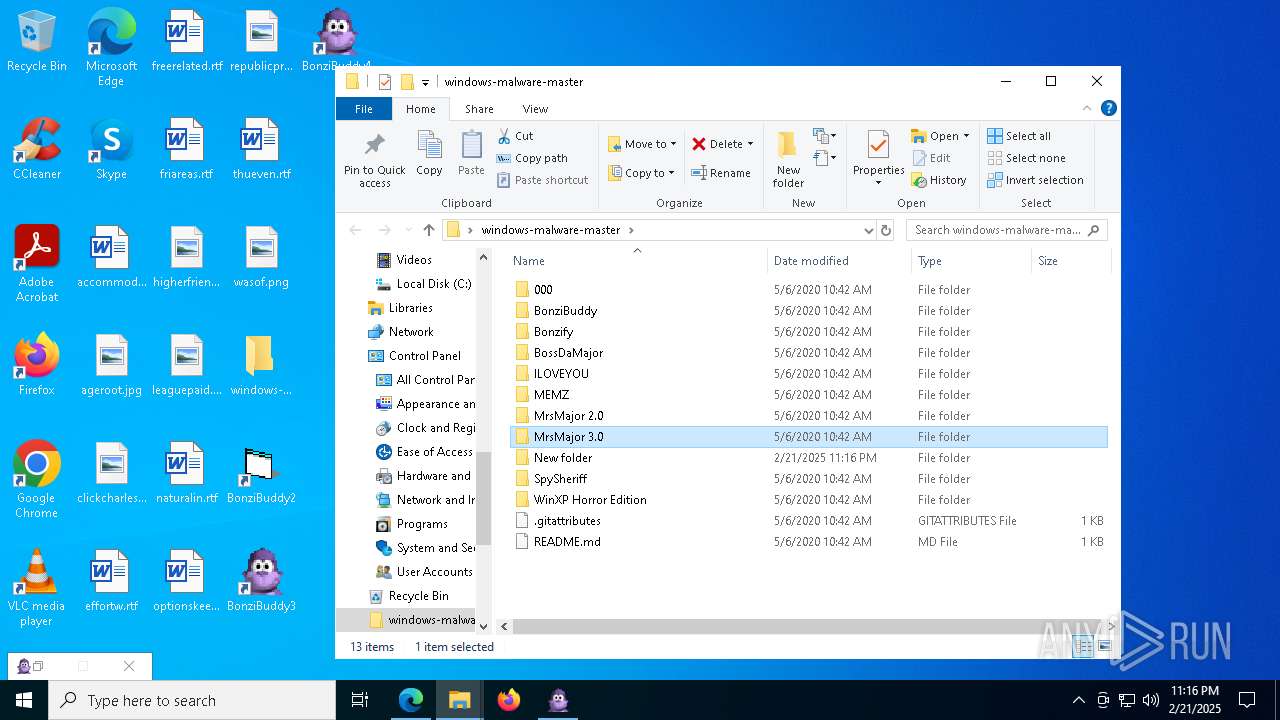
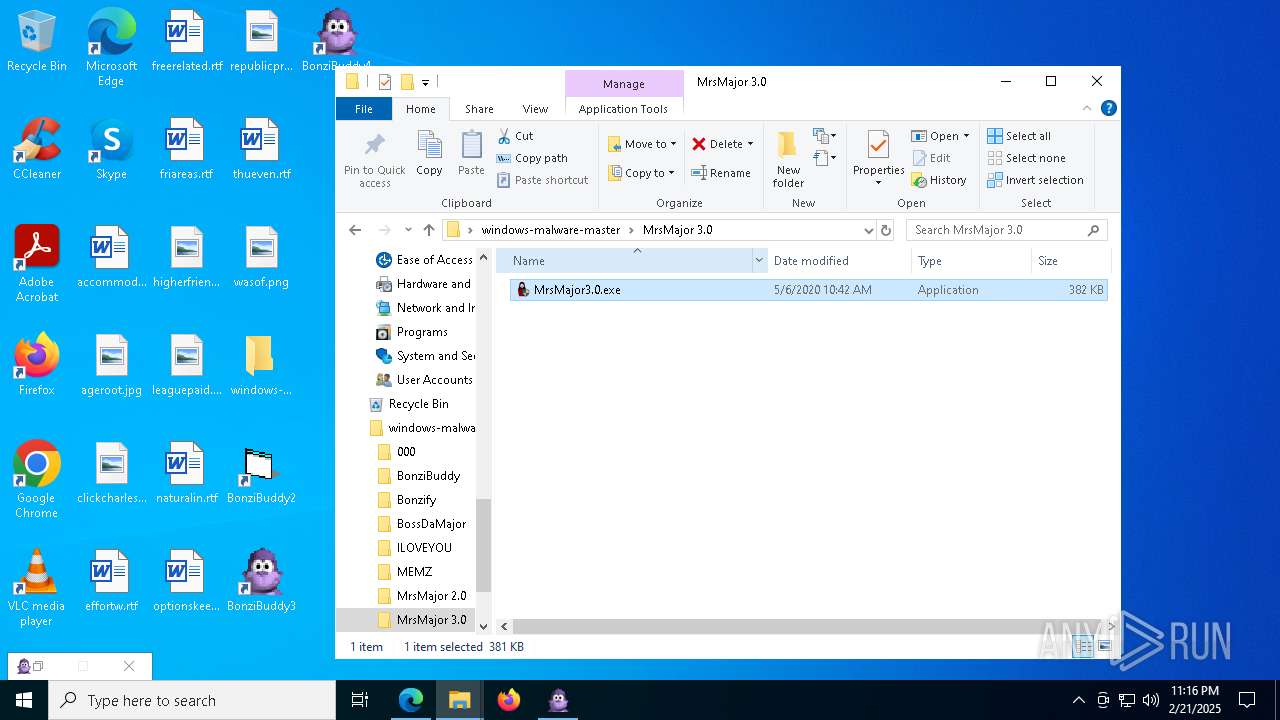
Manual execution by a user
- WinRAR.exe (PID: 7480)
- geometry dash auto speedhack.exe (PID: 3812)
- BonziBuddy432.exe (PID: 7872)
- BonziBDY_4.EXE (PID: 3848)
- BonziBDY_2.EXE (PID: 6076)
- firefox.exe (PID: 7652)
- MrsMajor3.0.exe (PID: 8964)
- BonziBDY_35.EXE (PID: 7428)
The sample compiled with english language support
- WinRAR.exe (PID: 7480)
- msedge.exe (PID: 6176)
- BonziBuddy432.exe (PID: 7872)
- MSAGENT.EXE (PID: 4672)
- tv_enua.exe (PID: 4428)
Checks supported languages
- geometry dash auto speedhack.exe (PID: 2744)
- geometry dash auto speedhack.exe (PID: 5836)
- geometry dash auto speedhack.exe (PID: 3780)
- geometry dash auto speedhack.exe (PID: 2904)
- geometry dash auto speedhack.exe (PID: 5212)
- geometry dash auto speedhack.exe (PID: 1292)
- identity_helper.exe (PID: 7392)
- geometry dash auto speedhack.exe (PID: 3812)
- BonziBuddy432.exe (PID: 7872)
- tv_enua.exe (PID: 4428)
- MSAGENT.EXE (PID: 4672)
- AgentSvr.exe (PID: 1344)
- BonziBDY_35.EXE (PID: 7428)
- BonziBDY_4.EXE (PID: 3848)
- BonziBDY_2.EXE (PID: 6076)
- MrsMajor3.0.exe (PID: 8964)
- eulascr.exe (PID: 7040)
Reads the computer name
- geometry dash auto speedhack.exe (PID: 3812)
- identity_helper.exe (PID: 7392)
- geometry dash auto speedhack.exe (PID: 5212)
- BonziBuddy432.exe (PID: 7872)
- MSAGENT.EXE (PID: 4672)
- tv_enua.exe (PID: 4428)
- AgentSvr.exe (PID: 1344)
- BonziBDY_35.EXE (PID: 7428)
- BonziBDY_4.EXE (PID: 3848)
- BonziBDY_2.EXE (PID: 6076)
- MrsMajor3.0.exe (PID: 8964)
- eulascr.exe (PID: 7040)
Process checks computer location settings
- geometry dash auto speedhack.exe (PID: 3812)
- geometry dash auto speedhack.exe (PID: 5212)
- BonziBuddy432.exe (PID: 7872)
- MrsMajor3.0.exe (PID: 8964)
Reads Environment values
- identity_helper.exe (PID: 7392)
- eulascr.exe (PID: 7040)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7480)
- msedge.exe (PID: 6176)
Reads security settings of Internet Explorer
- notepad.exe (PID: 1192)
Create files in a temporary directory
- BonziBuddy432.exe (PID: 7872)
- MSAGENT.EXE (PID: 4672)
- tv_enua.exe (PID: 4428)
- MrsMajor3.0.exe (PID: 8964)
- eulascr.exe (PID: 7040)
Creates files in the program directory
- BonziBuddy432.exe (PID: 7872)
Reads the machine GUID from the registry
- geometry dash auto speedhack.exe (PID: 5212)
- eulascr.exe (PID: 7040)
Creates files or folders in the user directory
- BonziBuddy432.exe (PID: 7872)
Reads mouse settings
- BonziBuddy432.exe (PID: 7872)
Reads the software policy settings
- eulascr.exe (PID: 7040)
Checks proxy server information
- eulascr.exe (PID: 7040)
Disables trace logs
- eulascr.exe (PID: 7040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
287
Monitored processes
148
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 68 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=8856 --field-trial-handle=2288,i,13877141644145510995,5967589713384103423,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 236 | regsvr32 /s "C:\WINDOWS\msagent\AgentMPx.dll" | C:\Windows\SysWOW64\regsvr32.exe | — | MSAGENT.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=49 --mojo-platform-channel-handle=1480 --field-trial-handle=2288,i,13877141644145510995,5967589713384103423,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 448 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6704 --field-trial-handle=2288,i,13877141644145510995,5967589713384103423,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
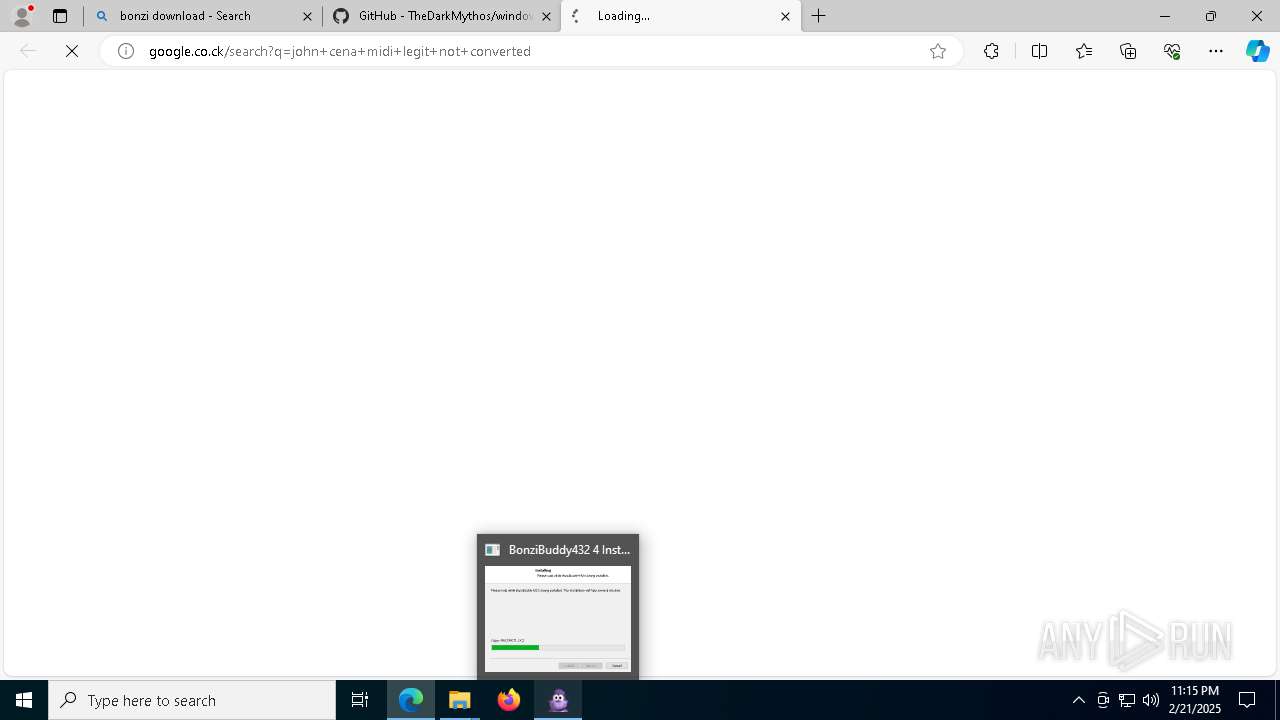
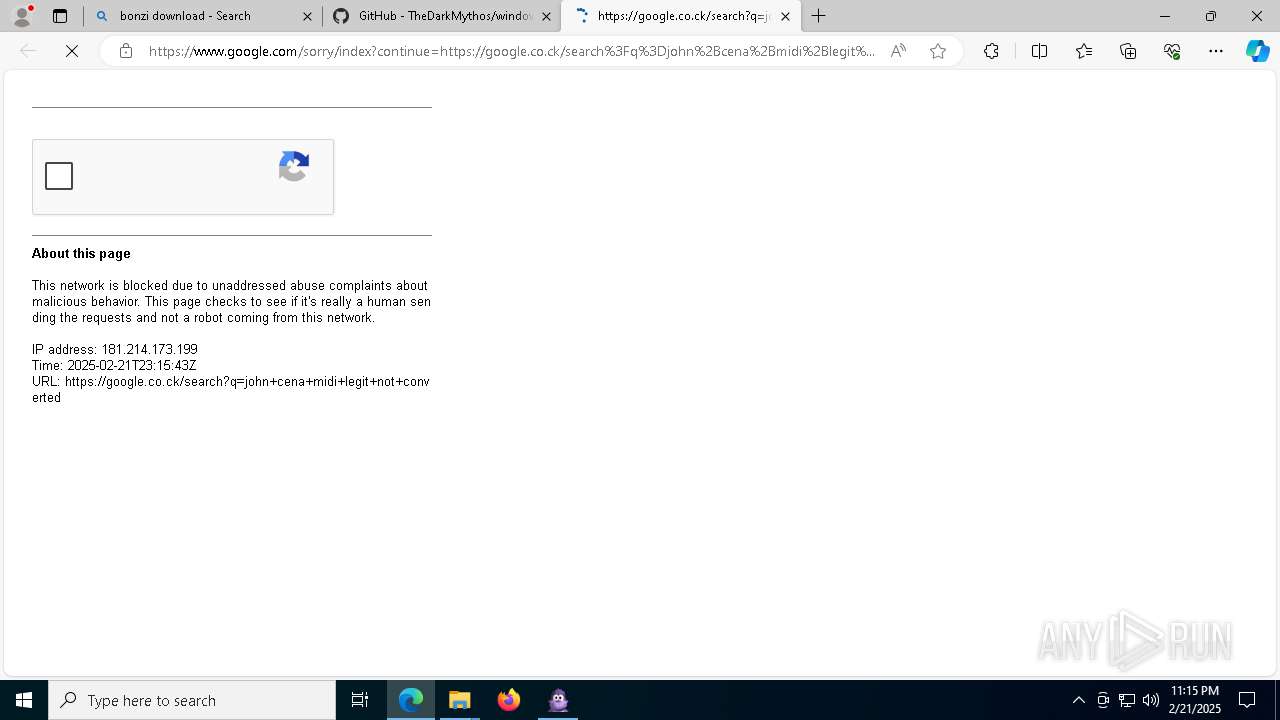
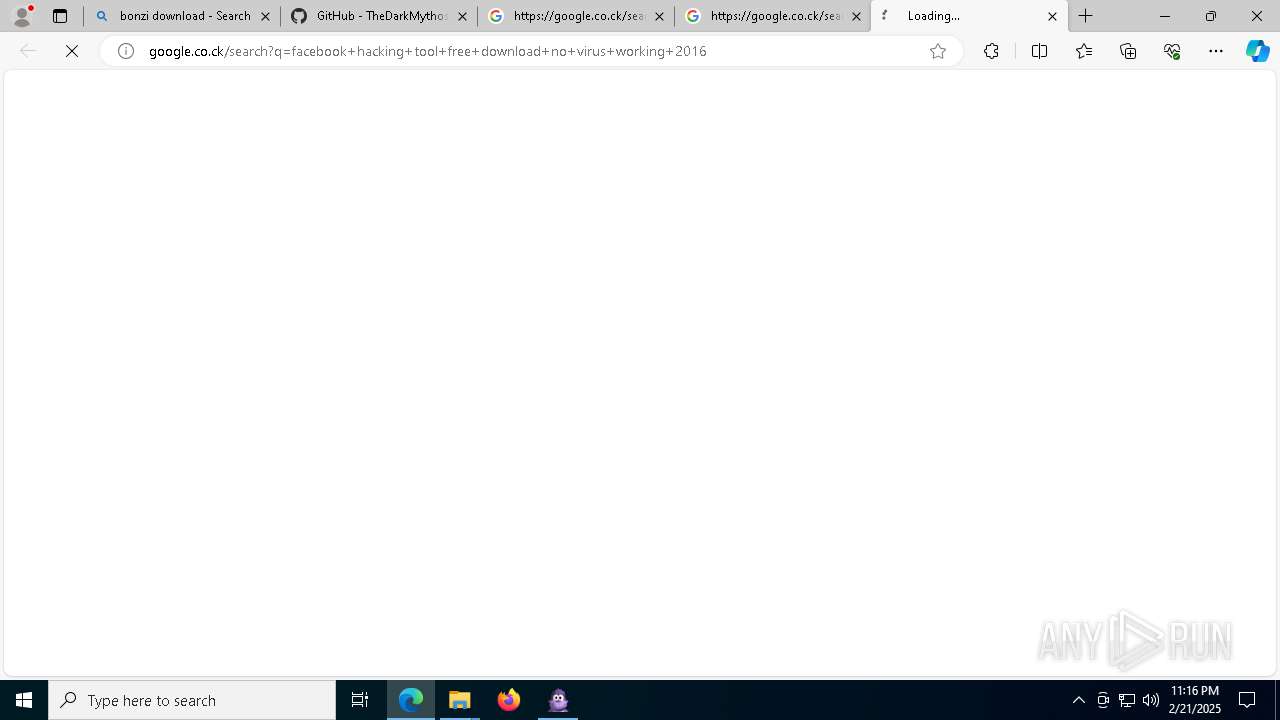
| 732 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument http://google.co.ck/search?q=minecraft+hax+download+no+virus | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | geometry dash auto speedhack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 936 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=8272 --field-trial-handle=2288,i,13877141644145510995,5967589713384103423,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1192 | "C:\Windows\System32\notepad.exe" \note.txt | C:\Windows\SysWOW64\notepad.exe | — | geometry dash auto speedhack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2900 -parentBuildID 20240213221259 -sandboxingKind 0 -prefsHandle 4896 -prefMapHandle 4892 -prefsLen 38103 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {9e8ceaef-a935-4f47-8e94-041fb25c7244} 7992 "\\.\pipe\gecko-crash-server-pipe.7992" 25a1289e110 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
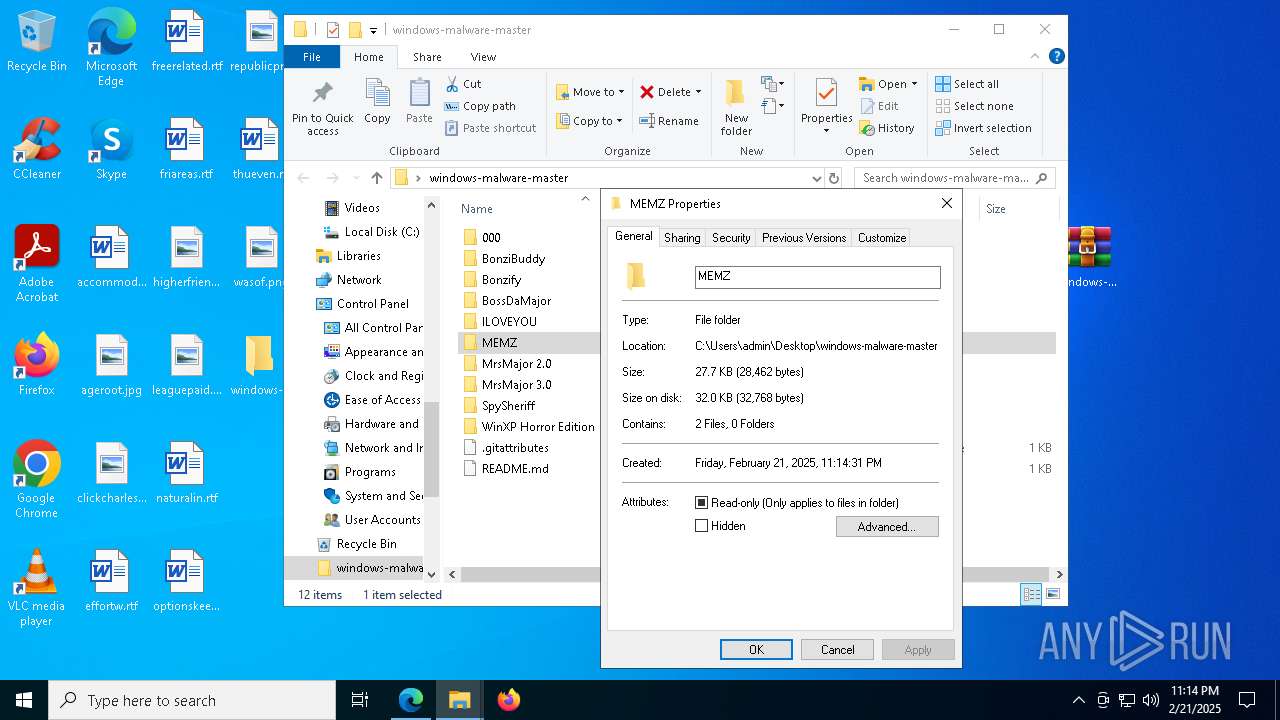
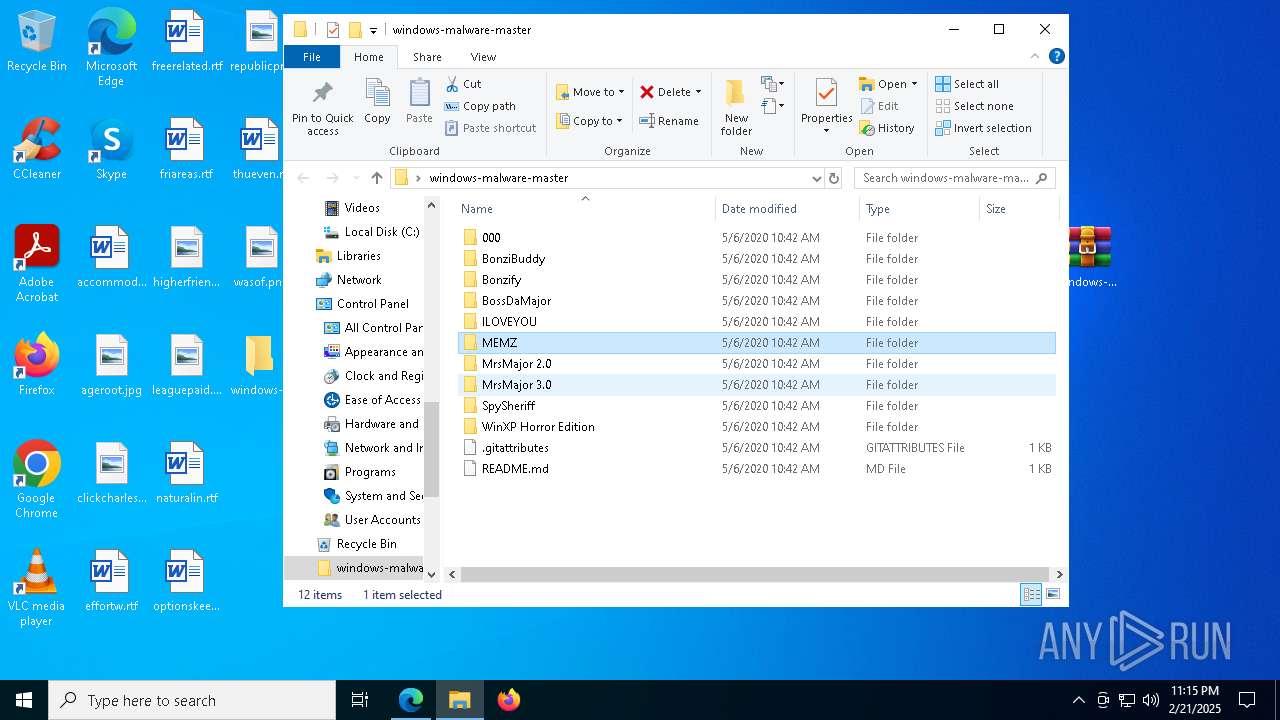
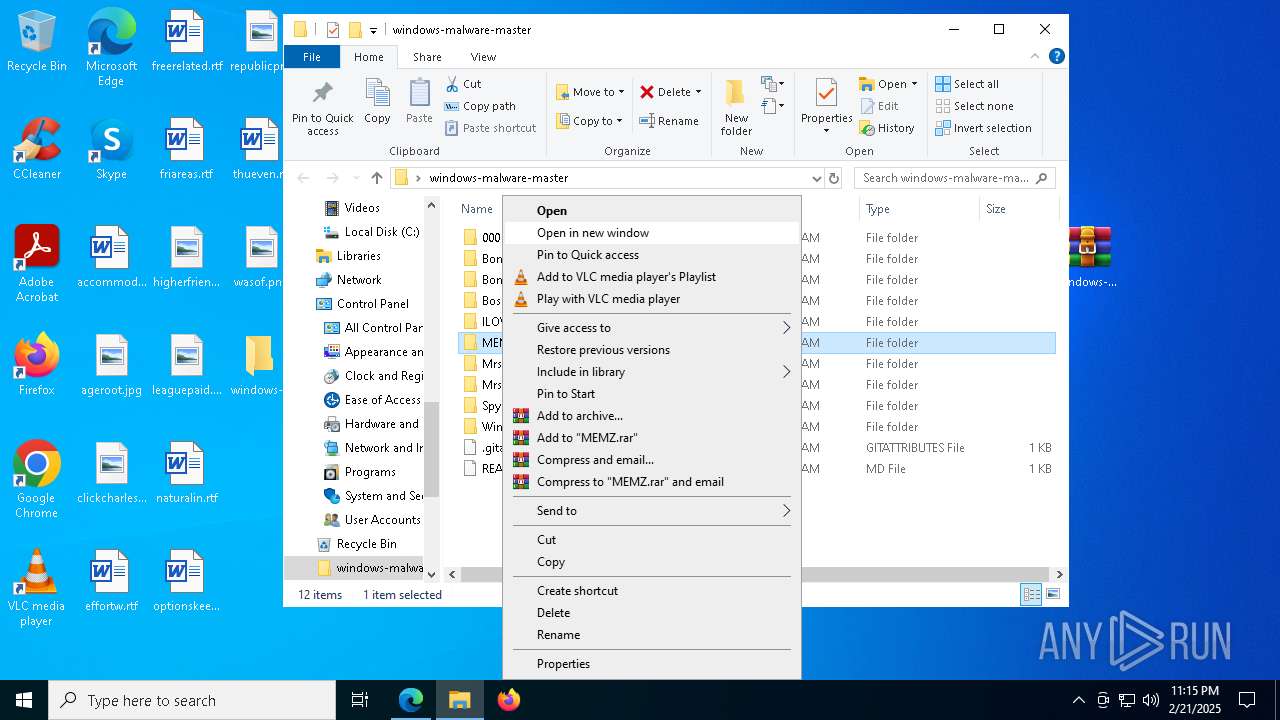
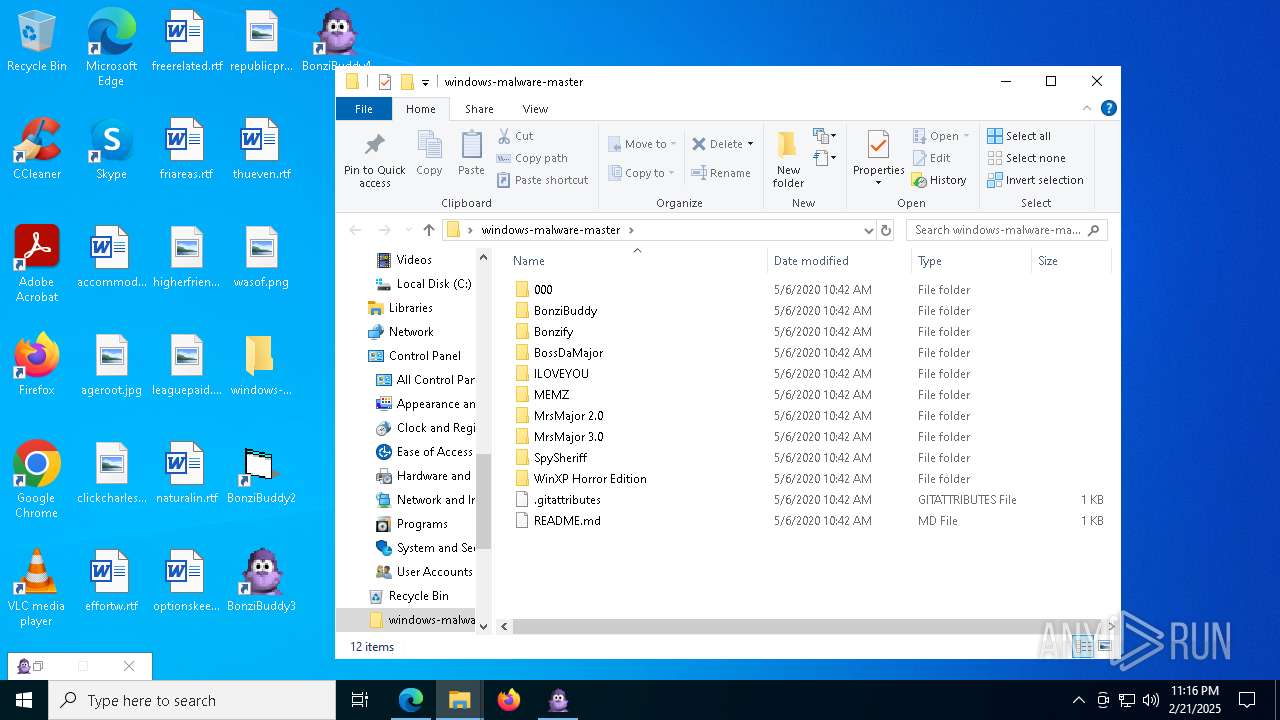
| 1292 | "C:\Users\admin\Desktop\windows-malware-master\MEMZ\geometry dash auto speedhack.exe" /watchdog | C:\Users\admin\Desktop\windows-malware-master\MEMZ\geometry dash auto speedhack.exe | — | geometry dash auto speedhack.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
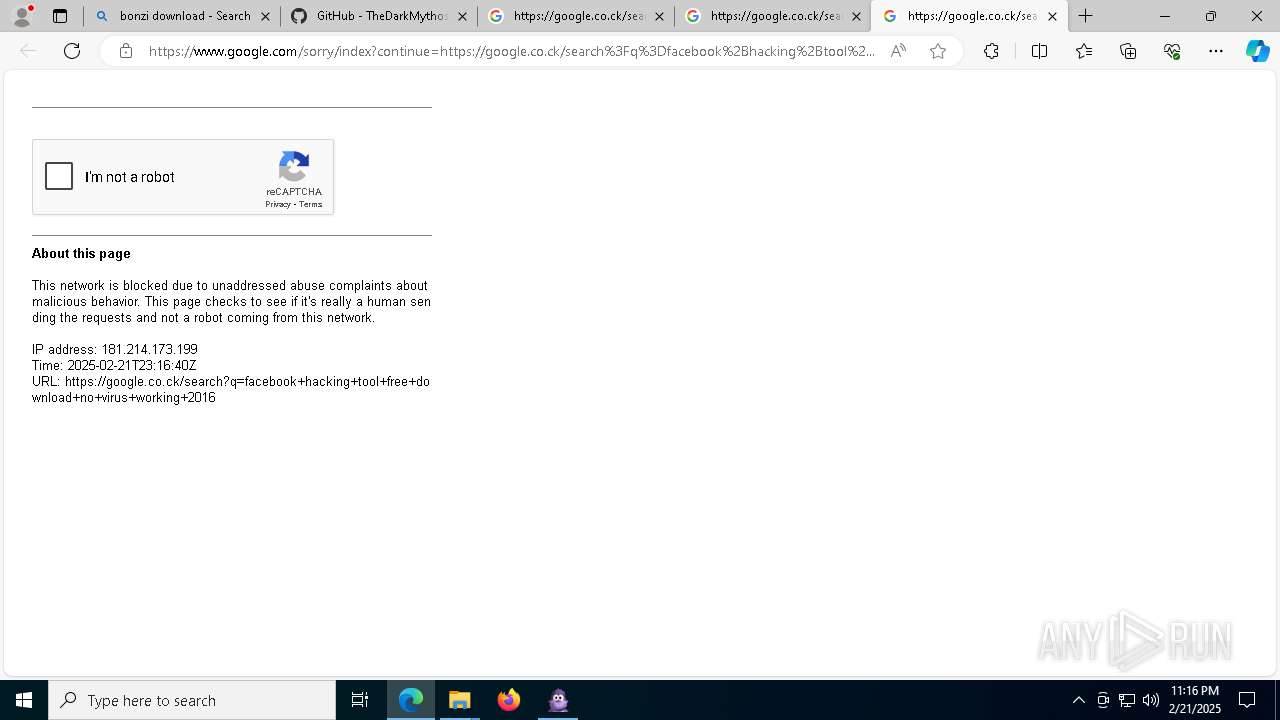
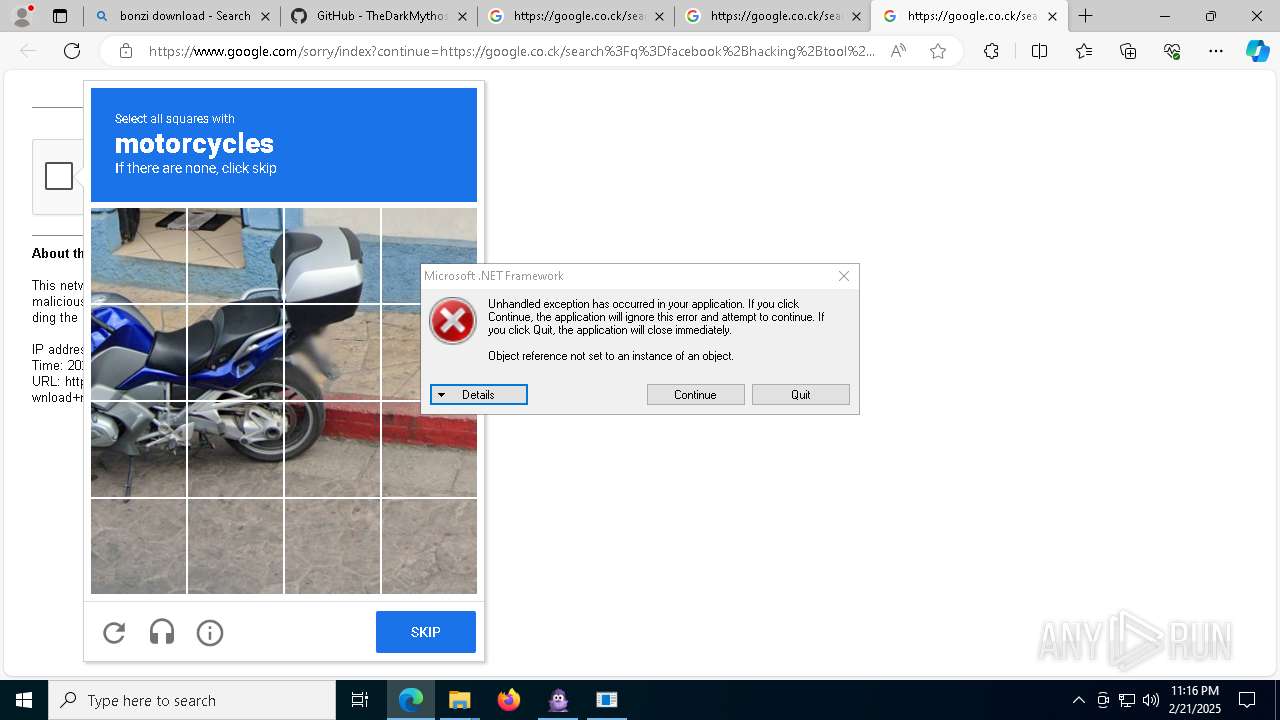
| 1296 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument http://google.co.ck/search?q=facebook+hacking+tool+free+download+no+virus+working+2016 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | geometry dash auto speedhack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
36 923
Read events
36 188
Write events
649
Delete events
86
Modification events
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 602D2E6B458D2F00 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 31393C6B458D2F00 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328416 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D0A22399-B2C1-4819-8073-F94D731BC888} | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328416 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {32A50FE3-05DA-4AF5-ABF8-ED1BA5DCB635} | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4E59736B458D2F00 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328416 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F5BDE8DC-A41E-46D1-A594-3FD1632FD183} | |||
Executable files
139
Suspicious files
1 043
Text files
260
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1388ea.TMP | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1388ea.TMP | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1388fa.TMP | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1388fa.TMP | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1388fa.TMP | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
86
TCP/UDP connections
212
DNS requests
225
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6652 | msedge.exe | GET | 304 | 104.76.201.34:80 | http://x1.i.lencr.org/ | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5576 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4932 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6ca9004c-2afd-40c0-a9b1-4fec460952e5?P1=1740586912&P2=404&P3=2&P4=IezT1%2bpAIS%2fSblfWaW5SV8bIdnwri3YwIkihu00sn3FaHNiqtkal9CzBAVryWfhGraFFCdUqBtPYr23yozmdTg%3d%3d | unknown | — | — | whitelisted |
5892 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4932 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6ca9004c-2afd-40c0-a9b1-4fec460952e5?P1=1740586912&P2=404&P3=2&P4=IezT1%2bpAIS%2fSblfWaW5SV8bIdnwri3YwIkihu00sn3FaHNiqtkal9CzBAVryWfhGraFFCdUqBtPYr23yozmdTg%3d%3d | unknown | — | — | whitelisted |
4932 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/6ca9004c-2afd-40c0-a9b1-4fec460952e5?P1=1740586912&P2=404&P3=2&P4=IezT1%2bpAIS%2fSblfWaW5SV8bIdnwri3YwIkihu00sn3FaHNiqtkal9CzBAVryWfhGraFFCdUqBtPYr23yozmdTg%3d%3d | unknown | — | — | whitelisted |
6652 | msedge.exe | GET | 304 | 104.76.201.34:80 | http://r3.i.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5892 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5064 | SearchApp.exe | 184.86.251.9:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
6652 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6332 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6652 | msedge.exe | 188.114.96.3:443 | tubebot.xyz | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
tubebot.xyz |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6652 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
6652 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
6652 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
6652 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
6652 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6652 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |