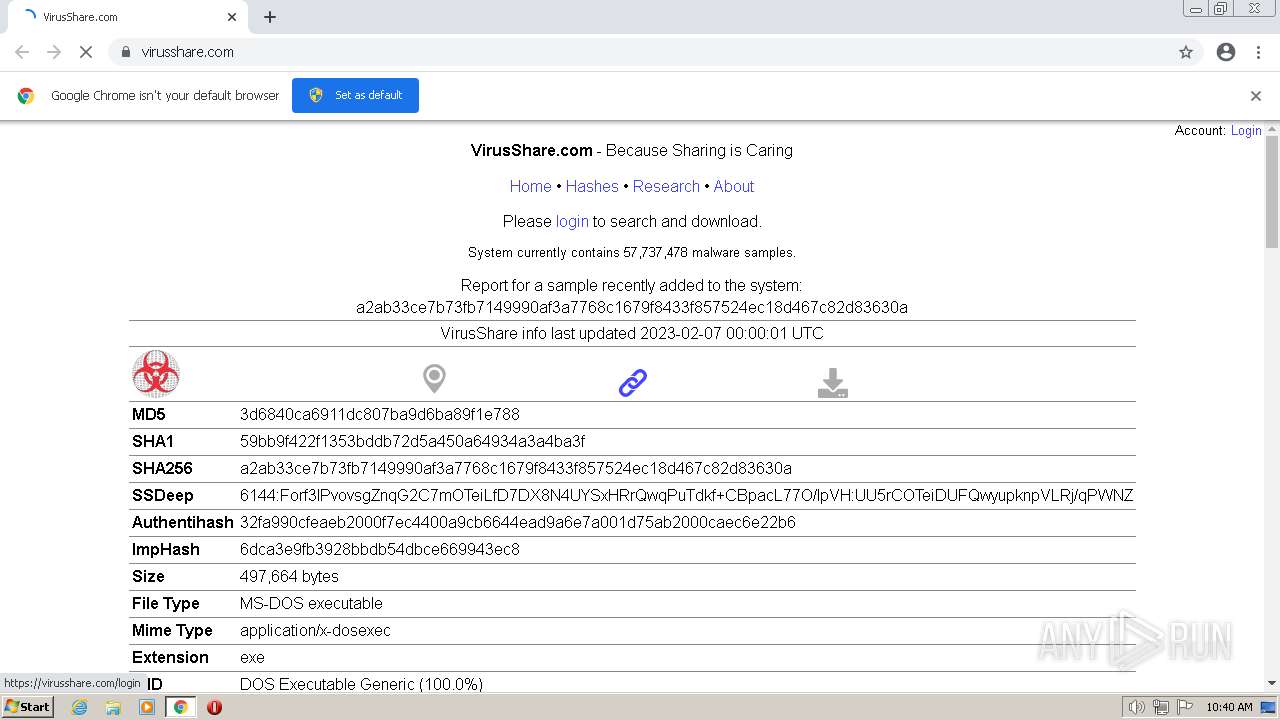
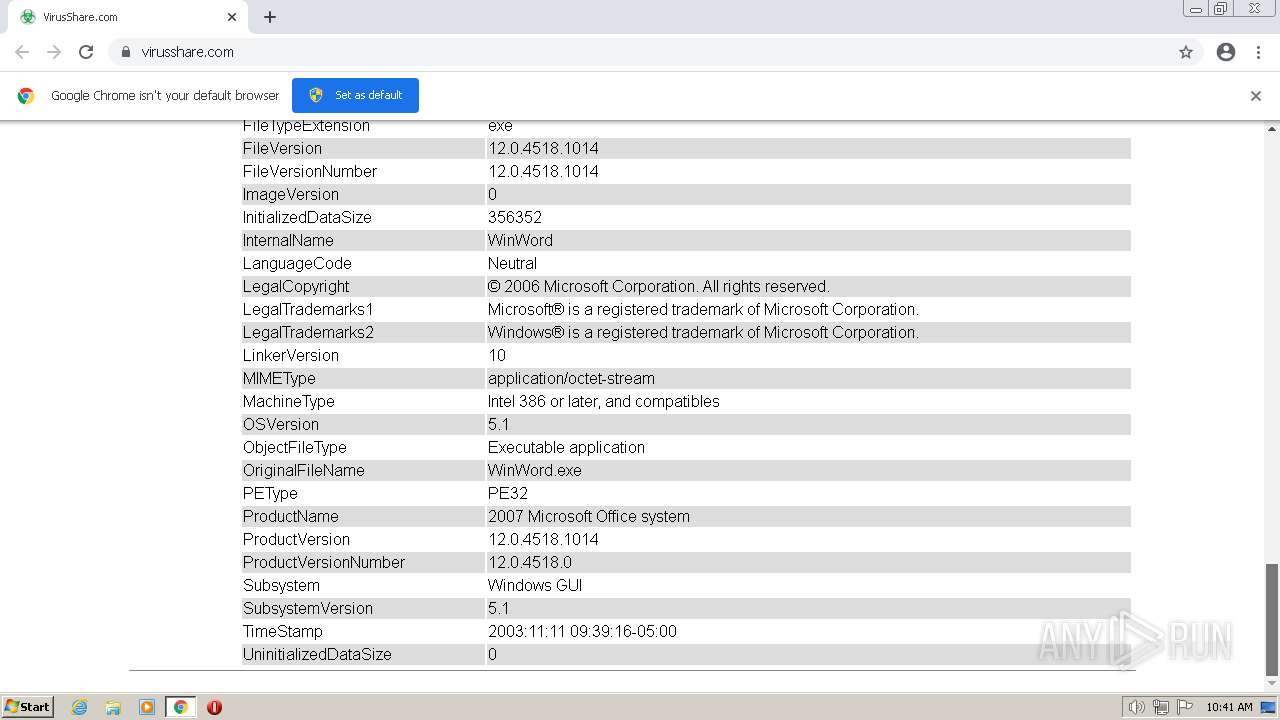
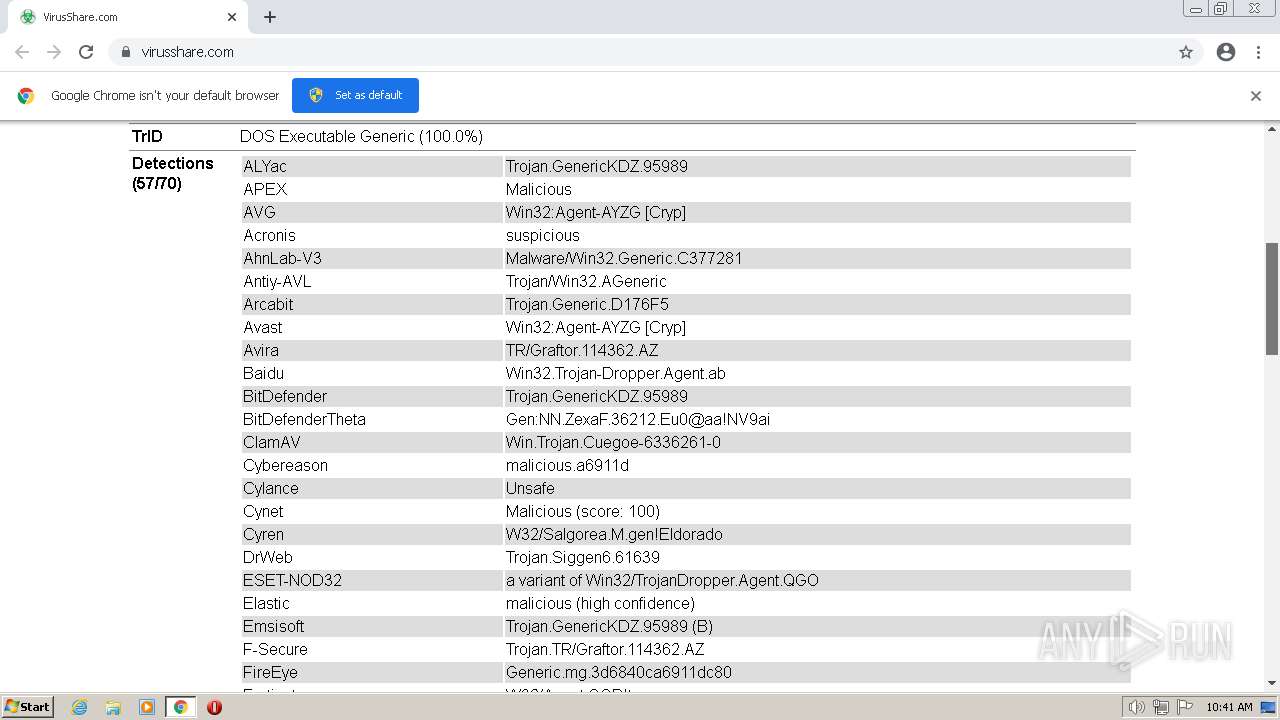
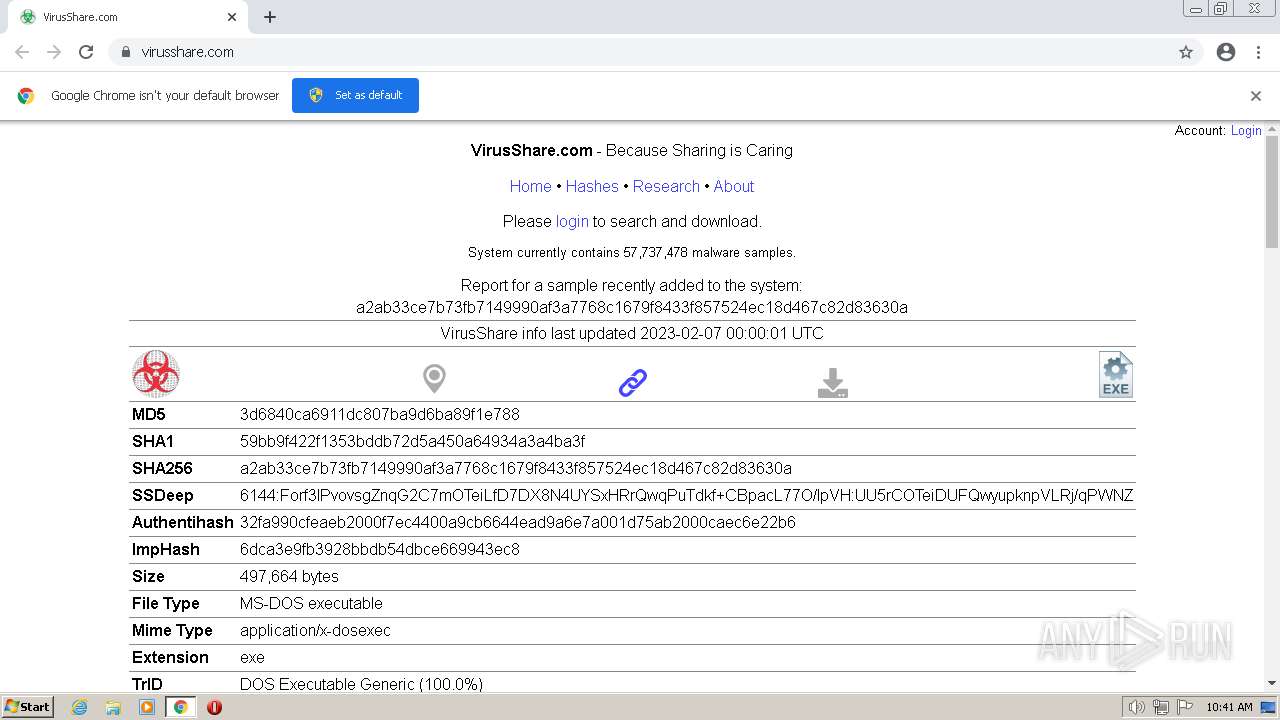
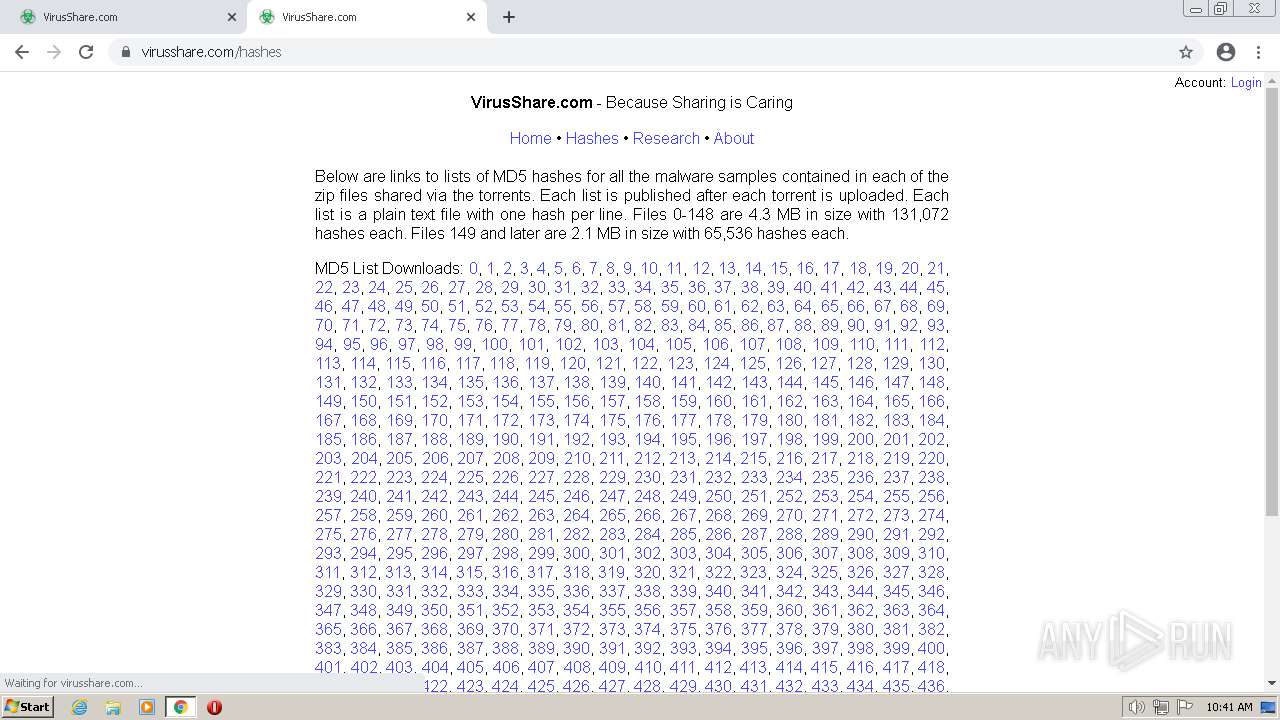
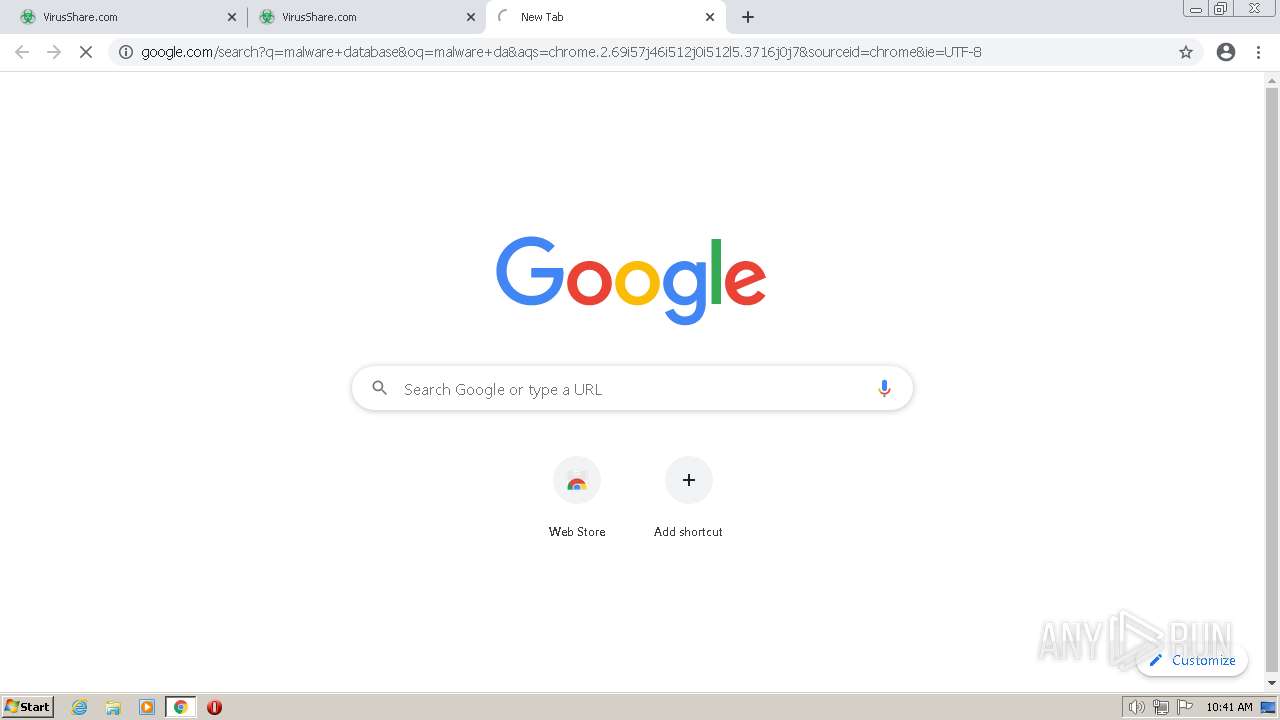
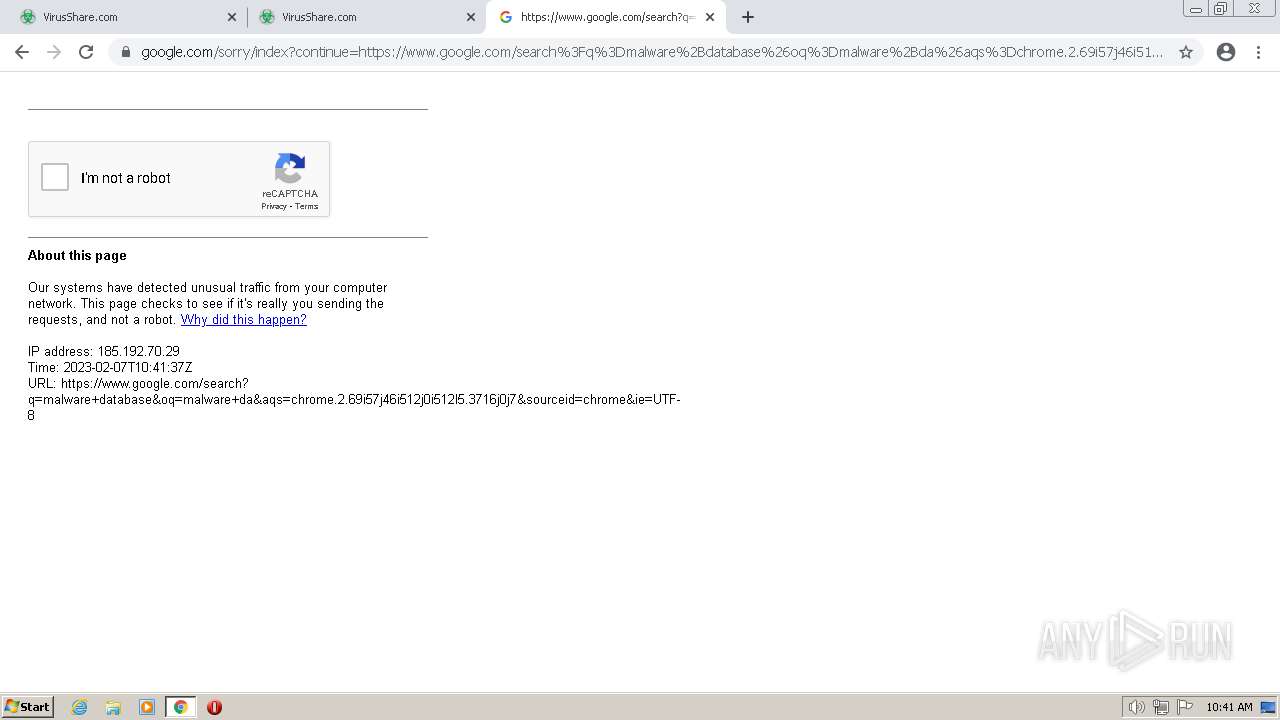
| URL: | https://virusshare.com/ |
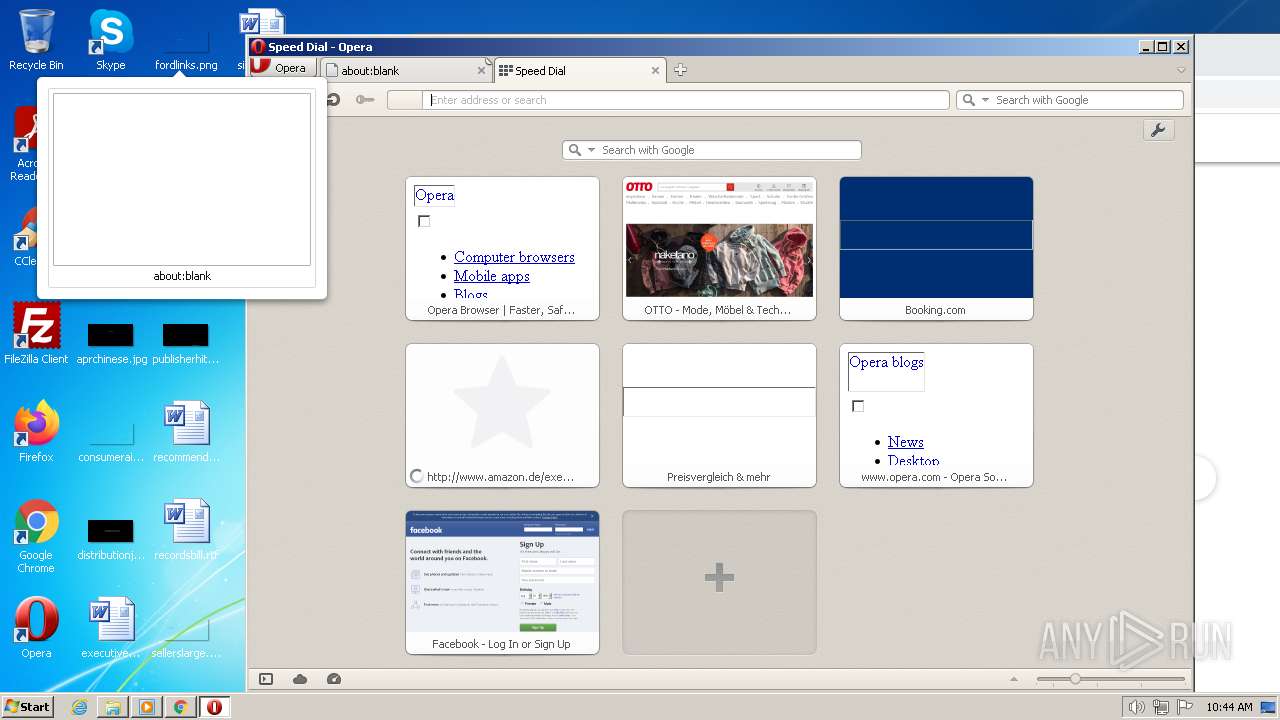
| Full analysis: | https://app.any.run/tasks/4b11c7a6-09ef-44bc-9aa0-8459ed5c806d |
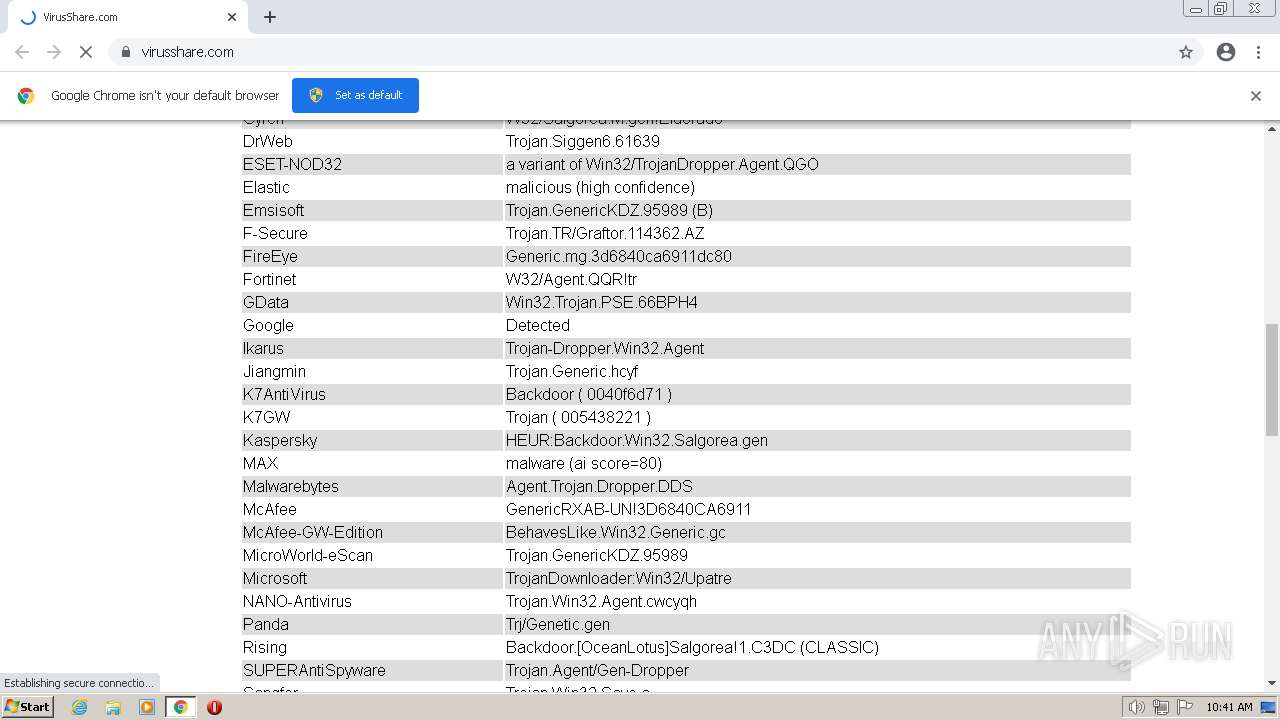
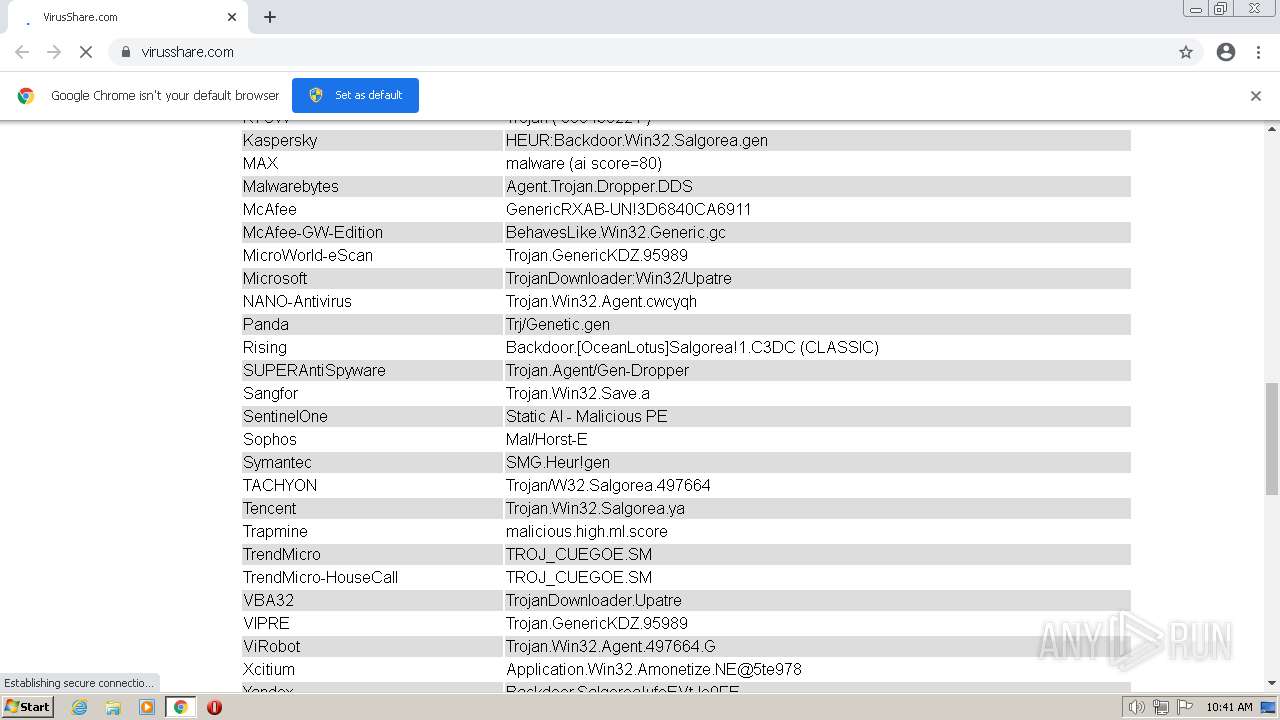
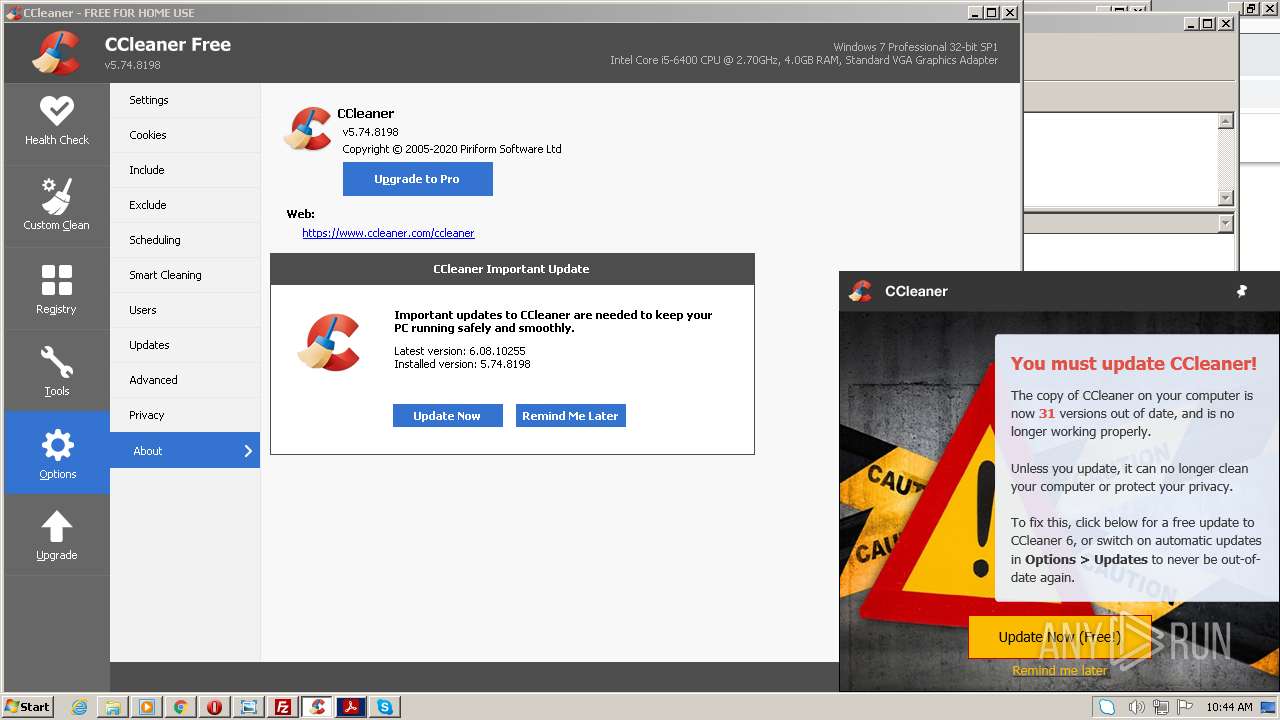
| Verdict: | Malicious activity |
| Analysis date: | February 07, 2023, 10:40:49 |
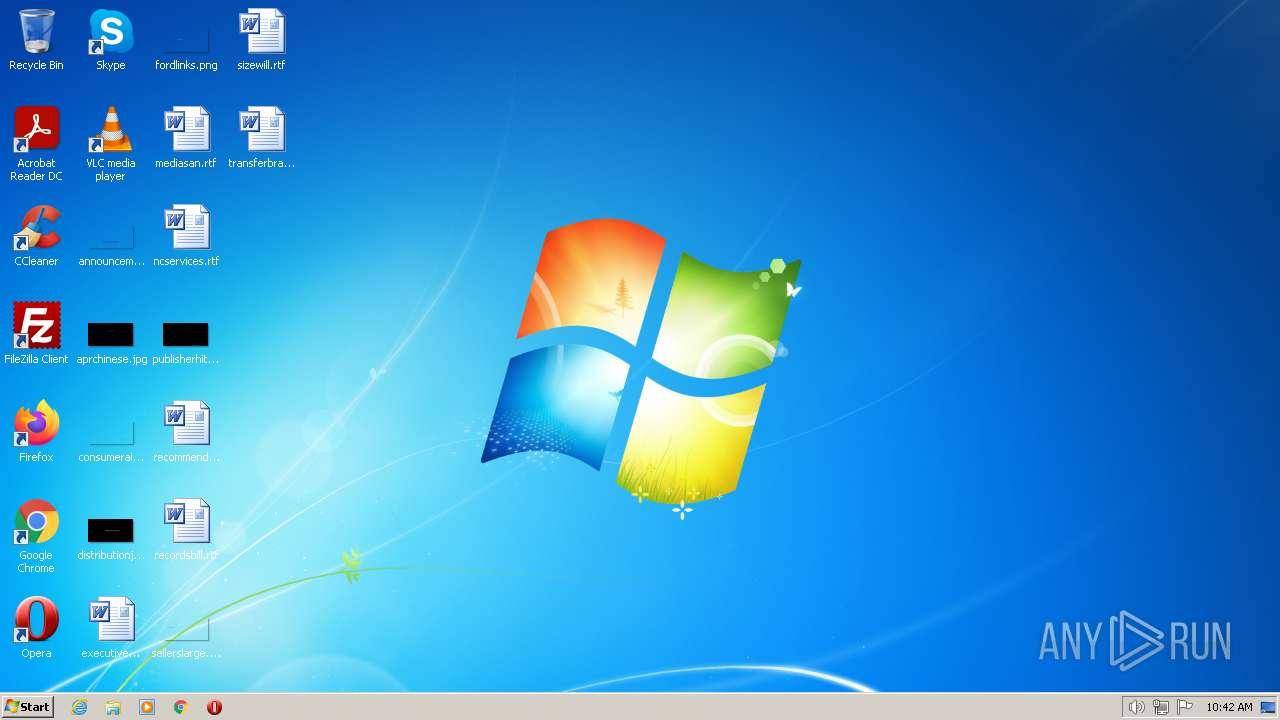
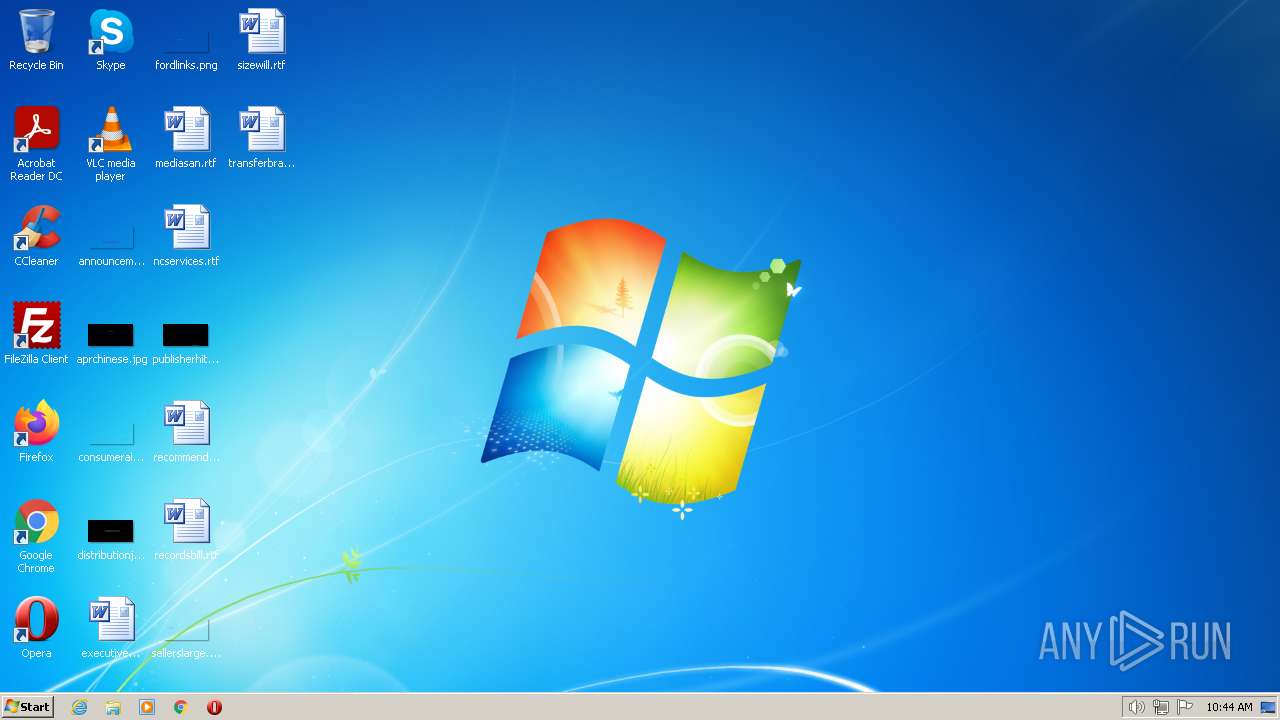
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 116F48AE056C33B3A0885898183BEF29 |
| SHA1: | 701C46668A234951DBB0AFD1CB53AF7CA7552C2F |
| SHA256: | 9A5AF9F5A9075402DDCD29F4250AB4655B57BDF2FFFA096872F297F661580765 |
| SSDEEP: | 3:N8Y0yK3:2YG |
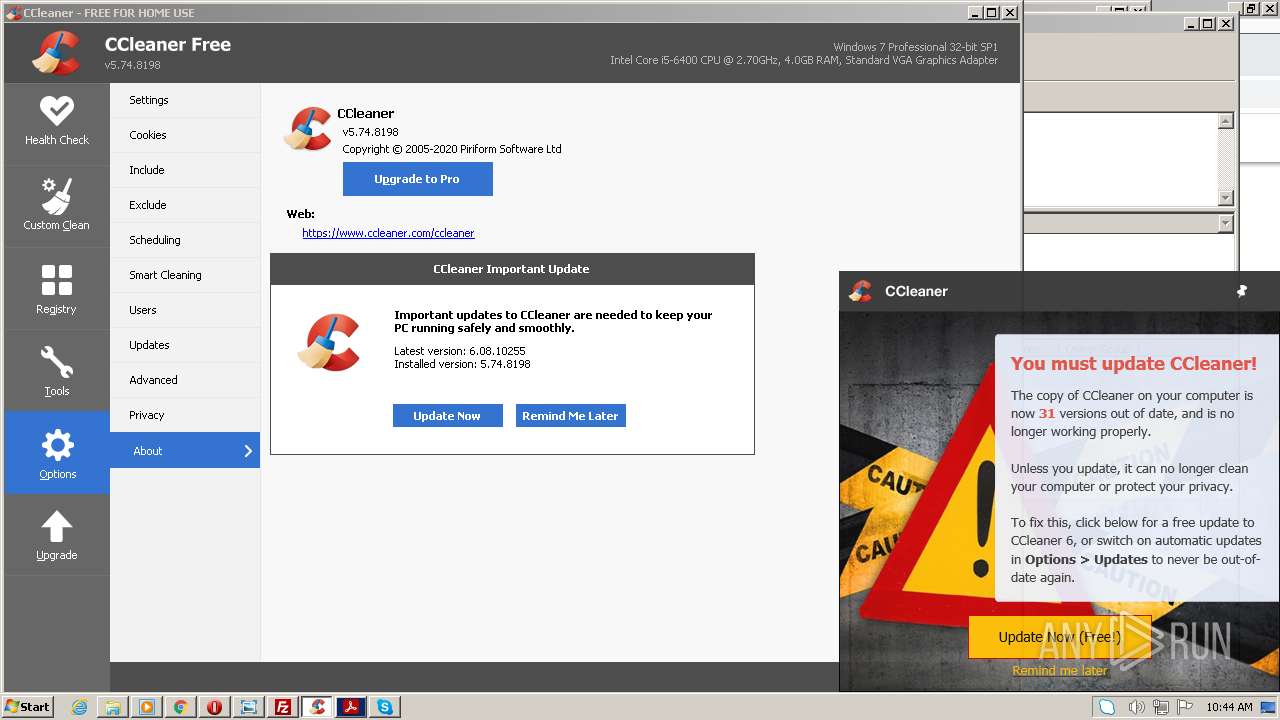
MALICIOUS
Drops the executable file immediately after the start
- CCleaner.exe (PID: 3980)
SUSPICIOUS
Application launched itself
- Skype.exe (PID: 3268)
- Skype.exe (PID: 3916)
- Skype.exe (PID: 5868)
Reads settings of System Certificates
- filezilla.exe (PID: 2280)
Executes via Task Scheduler
- CCleaner.exe (PID: 3980)
Uses REG/REGEDIT.EXE to modify register
- Skype.exe (PID: 3268)
Executable content was dropped or overwritten
- CCleaner.exe (PID: 3980)
INFO
Application launched itself
- chrome.exe (PID: 860)
- chrome.exe (PID: 3792)
- chrome.exe (PID: 752)
- RdrCEF.exe (PID: 3828)
- AcroRd32.exe (PID: 116)
The process checks LSA protection
- chrome.exe (PID: 860)
- chrome.exe (PID: 3984)
- chrome.exe (PID: 3792)
- chrome.exe (PID: 3084)
- chrome.exe (PID: 1996)
- opera.exe (PID: 1852)
- chrome.exe (PID: 1416)
- chrome.exe (PID: 588)
- chrome.exe (PID: 3712)
- chrome.exe (PID: 3004)
- chrome.exe (PID: 2184)
- opera.exe (PID: 2852)
- opera.exe (PID: 3620)
- setup_wm.exe (PID: 4084)
- explorer.exe (PID: 3520)
- wmplayer.exe (PID: 1640)
- chrome.exe (PID: 752)
- chrome.exe (PID: 3644)
- DllHost.exe (PID: 2564)
- Skype.exe (PID: 3268)
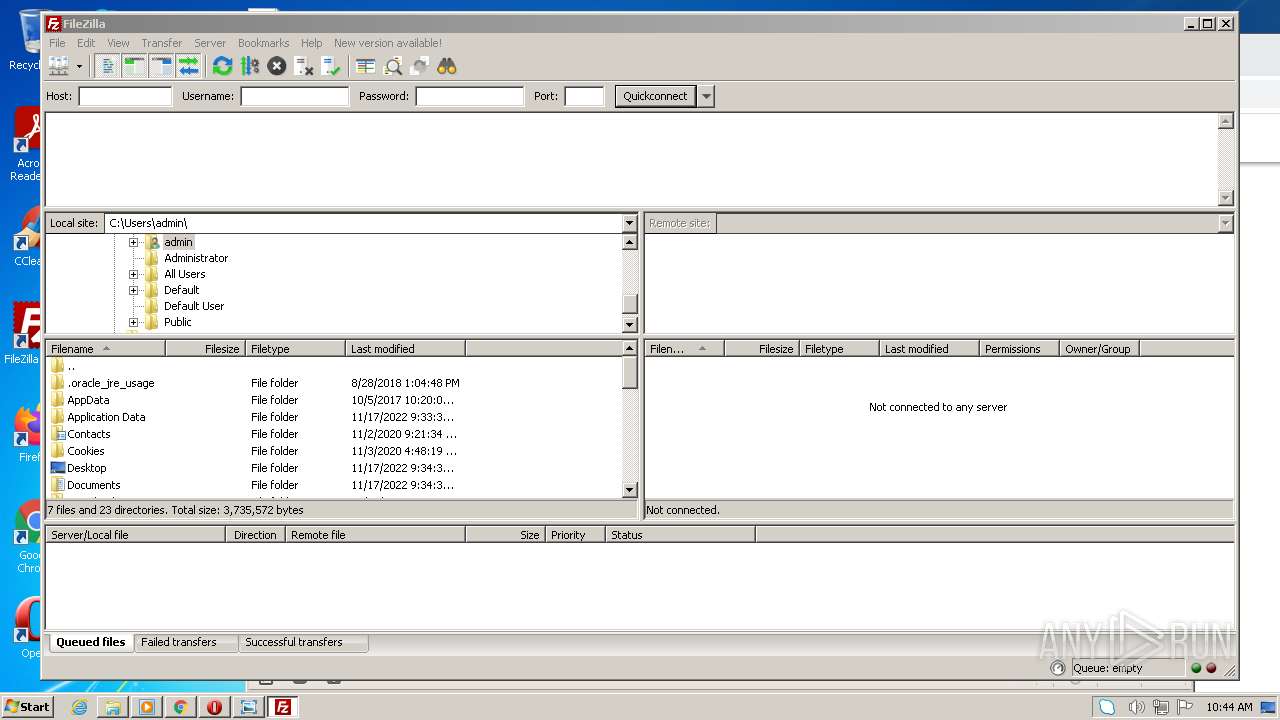
- filezilla.exe (PID: 2280)
Create files in a temporary directory
- chrome.exe (PID: 1416)
- chrome.exe (PID: 3792)
- setup_wm.exe (PID: 4084)
Manual execution by a user
- chrome.exe (PID: 3792)
- opera.exe (PID: 1852)
- opera.exe (PID: 3620)
- opera.exe (PID: 2852)
- wmplayer.exe (PID: 1640)
- chrome.exe (PID: 752)
- explorer.exe (PID: 3520)
- filezilla.exe (PID: 2280)
- CCleaner.exe (PID: 3792)
- AcroRd32.exe (PID: 116)
- Skype.exe (PID: 3268)
Checks supported languages
- wmplayer.exe (PID: 1640)
- setup_wm.exe (PID: 4084)
- Skype.exe (PID: 3268)
- Skype.exe (PID: 2968)
- filezilla.exe (PID: 2280)
- CCleaner.exe (PID: 3792)
Reads Environment values
- setup_wm.exe (PID: 4084)
Process checks computer location settings
- setup_wm.exe (PID: 4084)
Reads the computer name
- setup_wm.exe (PID: 4084)
- wmplayer.exe (PID: 1640)
- Skype.exe (PID: 3268)
- Skype.exe (PID: 2968)
- filezilla.exe (PID: 2280)
Reads the machine GUID from the registry
- setup_wm.exe (PID: 4084)
- Skype.exe (PID: 3268)
- filezilla.exe (PID: 2280)
Checks proxy server information
- setup_wm.exe (PID: 4084)
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 2852)
- Skype.exe (PID: 3268)
Creates files or folders in the user directory
- filezilla.exe (PID: 2280)
Reads CPU info
- Skype.exe (PID: 3268)
Drops a file that was compiled in debug mode
- CCleaner.exe (PID: 3980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
134
Monitored processes
90
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 0 Version: 20.13.20064.405839 | |||||||||||||||
| 280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,5047478721120720488,8207302393837728031,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2816 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,5047478721120720488,8207302393837728031,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1024 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,5047478721120720488,8207302393837728031,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3724 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 560 | C:\Windows\system32\reg.exe QUERY HKCU\Software\Microsoft\Skype /v RestartForUpdate | C:\Windows\system32\reg.exe | — | Skype.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6debd988,0x6debd998,0x6debd9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1040,5047478721120720488,8207302393837728031,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3980 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,5047478721120720488,8207302393837728031,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1864 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1048,10888309381101801779,9450562151465442078,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1076 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
42 765
Read events
42 247
Write events
502
Delete events
16
Modification events
| (PID) Process: | (860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (860) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
4
Suspicious files
734
Text files
1 130
Unknown types
80
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-63E22AB8-35C.pma | — | |
MD5:— | SHA256:— | |||
| 860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\16fc68a3-70ea-46c6-8112-3c95e43fc325.tmp | text | |
MD5:— | SHA256:— | |||
| 860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF10c1267.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF10c1257.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old~RF10c1610.TMP | text | |
MD5:D0BA19096D6C8F8DE58312E8D938E893 | SHA256:AADE90A7B0984F3C719D528E4E6FAE3854E28B30363BDD4DF65037E69784A078 | |||
| 860 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
204
DNS requests
75
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | — | — | whitelisted |
2852 | opera.exe | GET | — | 185.26.182.109:80 | http://redir.opera.com/speeddials/amazon/ | unknown | — | — | whitelisted |
4084 | setup_wm.exe | GET | 302 | 2.21.20.148:80 | http://redir.metaservices.microsoft.com/redir/allservices/?sv=5&version=12.0.7601.17514&locale=409&userlocale=409&geoid=f4&parch=x86&arch=x86 | DE | — | — | whitelisted |
— | — | GET | 301 | 104.109.93.201:80 | http://www.ccleaner.com/auto?a=0&p=cc&v=5.74.8198&l=1033&lk=&mk=2W8P-6PRD-X4PA-EBG6-VP5T-5PPS-ZRBW-U6PP-HZ8S&o=6.1W3&au=0&mx=97B7721C4994E2556FF6A439510F665DF3233A637833016FDA6B2D652A6FC9CD&gd=19ce970b-f6c0-4a09-bae4-274b971730e0 | NL | — | — | whitelisted |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 5.78 Kb | whitelisted |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 10.2 Kb | whitelisted |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 8.67 Kb | whitelisted |
2852 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertGlobalRootG2.crl | US | der | 926 b | whitelisted |
2852 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 740 b | whitelisted |
2852 | opera.exe | GET | 400 | 82.145.216.15:80 | http://sitecheck2.opera.com/?host=redir.opera.com&hdn=H0WKpMbVXsif0I8OJoRVZA== | unknown | html | 150 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1416 | chrome.exe | 172.217.18.110:443 | clients2.google.com | GOOGLE | US | whitelisted |
1416 | chrome.exe | 172.217.16.193:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
1416 | chrome.exe | 172.217.18.3:443 | ssl.gstatic.com | GOOGLE | US | whitelisted |
1416 | chrome.exe | 142.250.74.196:443 | www.google.com | GOOGLE | US | whitelisted |
3004 | chrome.exe | 142.251.39.45:443 | accounts.google.com | GOOGLE | US | unknown |
— | — | 172.217.16.195:443 | www.gstatic.com | GOOGLE | US | whitelisted |
1416 | chrome.exe | 142.250.186.170:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
1416 | chrome.exe | 172.217.16.195:443 | www.gstatic.com | GOOGLE | US | whitelisted |
1416 | chrome.exe | 142.250.186.174:443 | encrypted-tbn0.gstatic.com | GOOGLE | US | whitelisted |
1416 | chrome.exe | 216.58.212.163:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
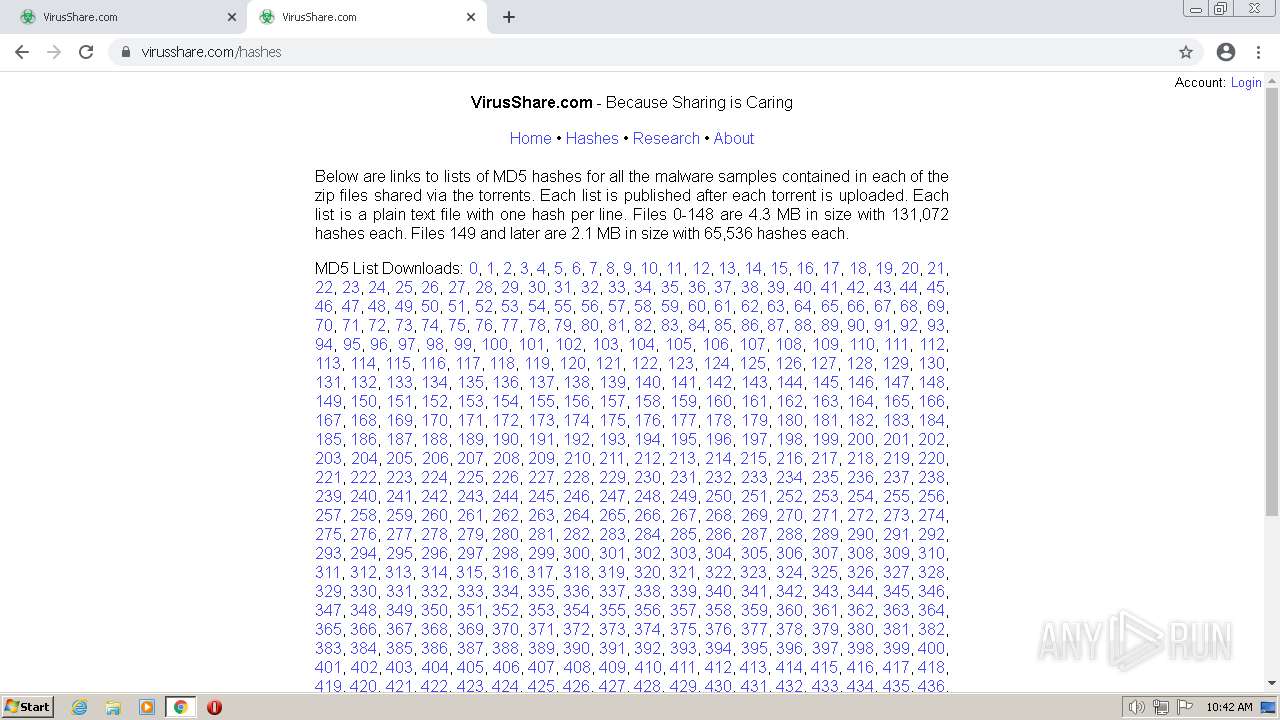
virusshare.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
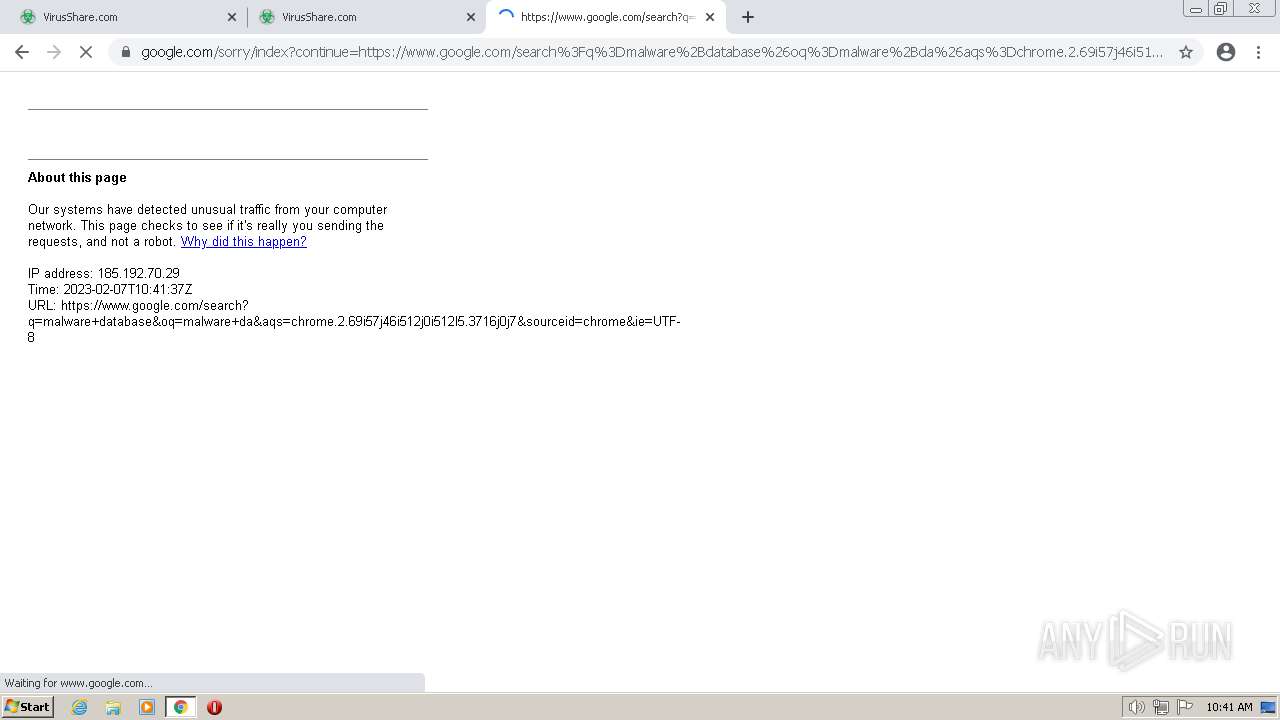
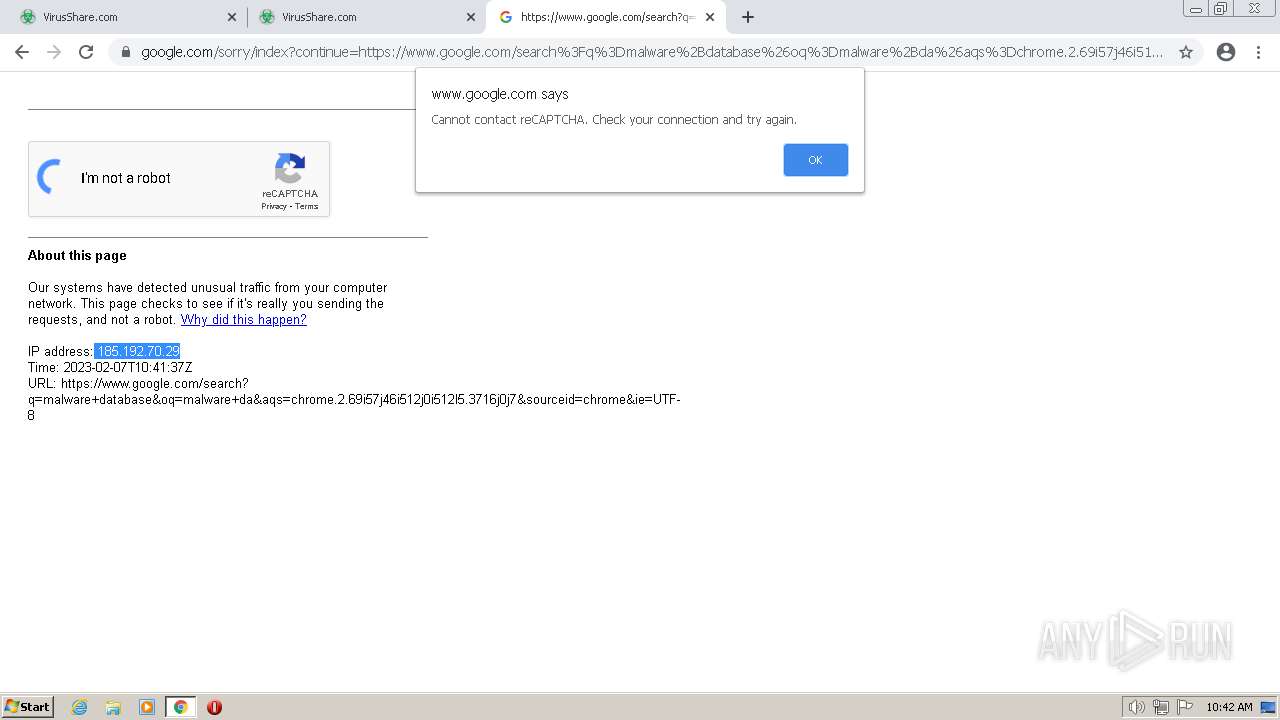
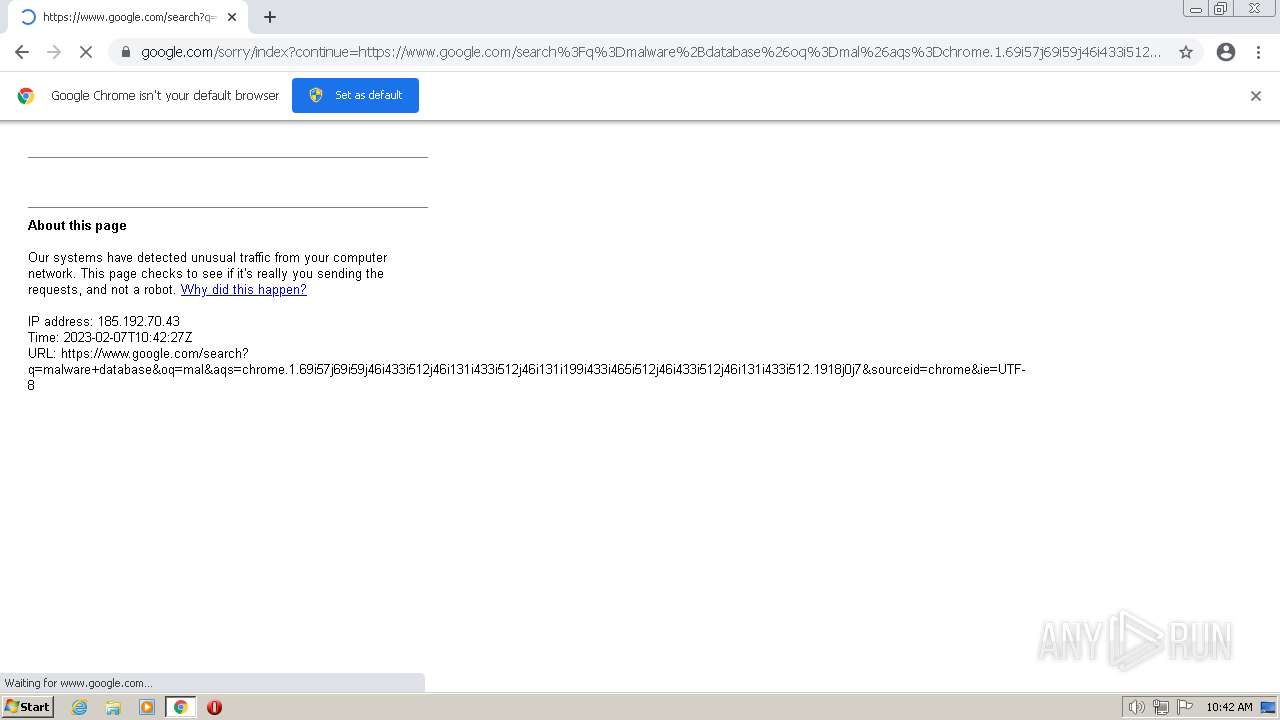
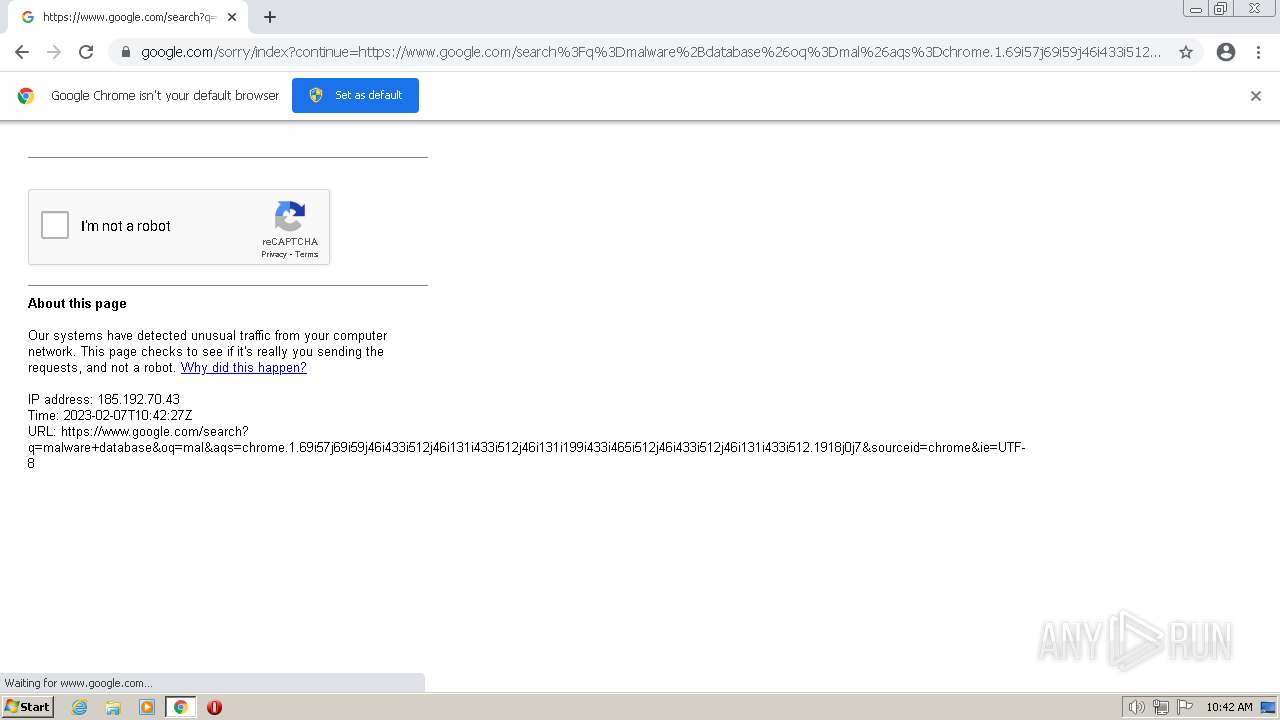
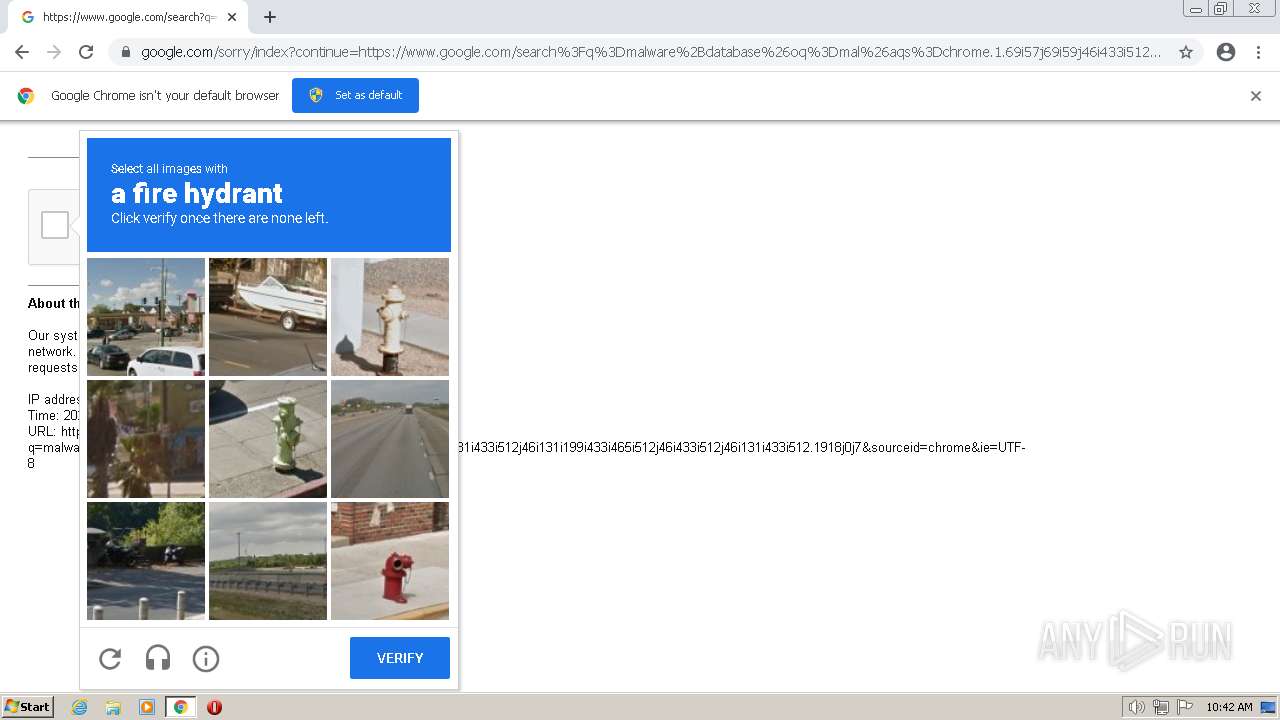
www.google.com |
| malicious |
encrypted-tbn0.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
Process | Message |
|---|---|
Skype.exe | [2968:2720:0207/104420.298:VERBOSE1:crash_service_main.cc(78)] Session start. cmdline is [--reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1]
|
Skype.exe | [2968:2720:0207/104420.298:VERBOSE1:crash_service_main.cc(78)] Session start. cmdline is [--reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1]
|
Skype.exe | [2968:2720:0207/104420.313:VERBOSE1:crash_service.cc(300)] pipe name is \\.\pipe\skype-preview Crash Service
dumps at C:\Users\admin\AppData\Local\Temp\skype-preview Crashes
|
Skype.exe | [2968:2720:0207/104420.313:VERBOSE1:crash_service.cc(145)] window handle is 00040224
|
Skype.exe | [2968:2720:0207/104420.313:VERBOSE1:crash_service_main.cc(94)] Ready to process crash requests
|
Skype.exe | [2968:2324:0207/104420.313:VERBOSE1:crash_service.cc(333)] client start. pid = 3268
|
Skype.exe | [2968:2720:0207/104420.313:VERBOSE1:crash_service.cc(304)] checkpoint is C:\Users\admin\AppData\Local\Temp\skype-preview Crashes\crash_checkpoint.txt
server is https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload
maximum 128 reports/day
reporter is electron-crash-service
|
Skype.exe | [2968:2720:0207/104420.313:VERBOSE1:crash_service.cc(145)] window handle is 00040224
|
Skype.exe | [2968:2720:0207/104420.313:VERBOSE1:crash_service.cc(304)] checkpoint is C:\Users\admin\AppData\Local\Temp\skype-preview Crashes\crash_checkpoint.txt
server is https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload
maximum 128 reports/day
reporter is electron-crash-service
|
Skype.exe | [2968:2720:0207/104420.313:VERBOSE1:crash_service.cc(300)] pipe name is \\.\pipe\skype-preview Crash Service
dumps at C:\Users\admin\AppData\Local\Temp\skype-preview Crashes
|