analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
| File name: | dzrrodcq.exe |
| Full analysis: | https://app.any.run/tasks/37a12822-ce45-4154-b911-09a99e7cb027 |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 15:42:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6FD0E54DA73594E0F4CE673D71DCE035 |
| SHA1: | AF299F6CCB1B527A3928AF0DFCDD8A867719B1D2 |
| SHA256: | 9A578188E39E4A377798A555EC8578A1643360092C52364E56AEBFABAB078FBE |
| SSDEEP: | 12288:QIRZTEoH9MjgxD3OOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOu:nhEodMK |
MALICIOUS
Uses SVCHOST.EXE for hidden code execution
- qhpnxszn.exe (PID: 3752)
Application was dropped or rewritten from another process
- qhpnxszn.exe (PID: 3752)
TOFSEE was detected
- svchost.exe (PID: 1520)
SUSPICIOUS
Executed as Windows Service
- qhpnxszn.exe (PID: 3752)
Executable content was dropped or overwritten
- cmd.exe (PID: 2168)
- dzrrodcq.exe (PID: 2444)
Starts SC.EXE for service management
- dzrrodcq.exe (PID: 2444)
Starts CMD.EXE for commands execution
- dzrrodcq.exe (PID: 2444)
Uses NETSH.EXE for network configuration
- dzrrodcq.exe (PID: 2444)
Creates or modifies windows services
- svchost.exe (PID: 1520)
Creates files in the Windows directory
- svchost.exe (PID: 1520)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:04:21 06:43:38+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 87040 |
| InitializedDataSize: | 1922560 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1e04 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Apr-2018 04:43:38 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 21-Apr-2018 04:43:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000153AB | 0x00015400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.68234 |
.rdata | 0x00017000 | 0x00023962 | 0x00023A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.7948 |
.data | 0x0003B000 | 0x001AA5F0 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.666985 |
.sey | 0x001E6000 | 0x00000400 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rav | 0x001E7000 | 0x00000001 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.tls | 0x001E8000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.gfids | 0x001E9000 | 0x000000AC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.52941 |
.rsrc | 0x001EA000 | 0x00005928 | 0x00005A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.75197 |
.reloc | 0x001F0000 | 0x000011B4 | 0x009BF400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.56668 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 6.48695 | 4264 | UNKNOWN | Italian - Italy | RT_ICON |
14 | 3.24486 | 608 | UNKNOWN | UNKNOWN | RT_STRING |
15 | 3.30583 | 1866 | UNKNOWN | UNKNOWN | RT_STRING |
16 | 3.32747 | 1482 | UNKNOWN | UNKNOWN | RT_STRING |
17 | 3.31644 | 1570 | UNKNOWN | UNKNOWN | RT_STRING |
18 | 3.29979 | 1988 | UNKNOWN | UNKNOWN | RT_STRING |
19 | 3.29158 | 1980 | UNKNOWN | UNKNOWN | RT_STRING |
20 | 3.31493 | 1694 | UNKNOWN | UNKNOWN | RT_STRING |
21 | 3.229 | 1084 | UNKNOWN | UNKNOWN | RT_STRING |
116 | 1.7815 | 20 | UNKNOWN | Italian - Italy | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
USER32.dll |
Total processes
53
Monitored processes
11
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2444 | "C:\Users\admin\AppData\Local\Temp\dzrrodcq.exe" | C:\Users\admin\AppData\Local\Temp\dzrrodcq.exe | explorer.exe | |
User: admin Integrity Level: MEDIUM Exit code: 0 | ||||
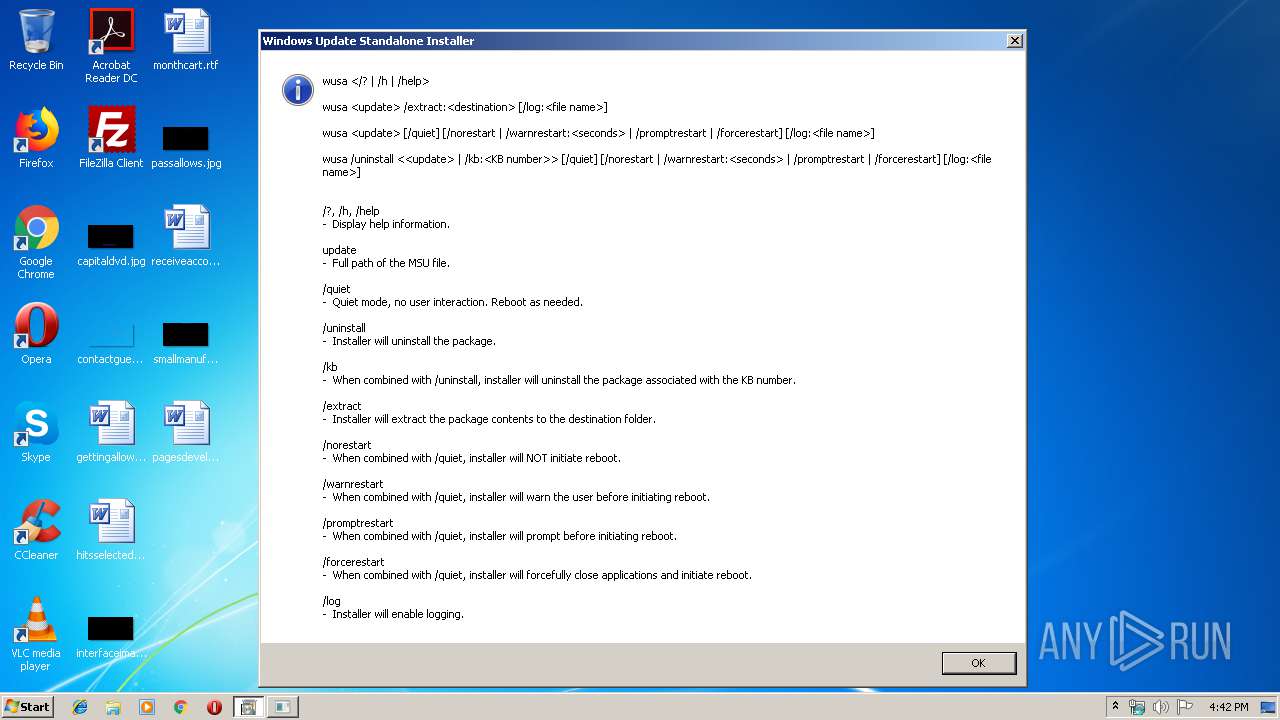
| 2372 | "C:\Windows\System32\wusa.exe" | C:\Windows\System32\wusa.exe | — | dzrrodcq.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Standalone Installer Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 3732 | "C:\Windows\System32\wusa.exe" | C:\Windows\System32\wusa.exe | dzrrodcq.exe | |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Standalone Installer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 1576 | cmd /C mkdir C:\Windows\system32\evyrpwnx\ | C:\Windows\system32\cmd.exe | dzrrodcq.exe | |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | ||||
| 2168 | cmd /C move /Y "C:\Users\admin\AppData\Local\Temp\qhpnxszn.exe" C:\Windows\system32\evyrpwnx\ | C:\Windows\system32\cmd.exe | dzrrodcq.exe | |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | ||||
| 4088 | sc create evyrpwnx binPath= "C:\Windows\system32\evyrpwnx\qhpnxszn.exe /d\"C:\Users\admin\AppData\Local\Temp\dzrrodcq.exe\"" type= own start= auto DisplayName= "wifi support" | C:\Windows\system32\sc.exe | dzrrodcq.exe | |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 1216 | sc description evyrpwnx "wifi internet conection" | C:\Windows\system32\sc.exe | dzrrodcq.exe | |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 2468 | sc start evyrpwnx | C:\Windows\system32\sc.exe | dzrrodcq.exe | |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 3752 | C:\Windows\system32\evyrpwnx\qhpnxszn.exe /d"C:\Users\admin\AppData\Local\Temp\dzrrodcq.exe" | C:\Windows\system32\evyrpwnx\qhpnxszn.exe | — | services.exe |
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 | ||||
| 1520 | svchost.exe | C:\Windows\system32\svchost.exe | qhpnxszn.exe | |
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
Total events
141
Read events
77
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1520 | svchost.exe | C:\Windows\system32\config\systemprofile:.repos | binary | |
MD5:B65DDBE6D680B044FA1FA65CCA53C54C | SHA256:D4535405C29CFB04EAAC0B41A0108860EF6452A8CFF092F4CD66E8C3B9C97A1C | |||
| 2444 | dzrrodcq.exe | C:\Users\admin\AppData\Local\Temp\qhpnxszn.exe | executable | |
MD5:28C33448A7F44509BCD15CD037630D4E | SHA256:5060367A323B847E776C71F3619B2F5642FC68A81024C298408433CF1ED7A2BC | |||
| 2168 | cmd.exe | C:\Windows\system32\evyrpwnx\qhpnxszn.exe | executable | |
MD5:28C33448A7F44509BCD15CD037630D4E | SHA256:5060367A323B847E776C71F3619B2F5642FC68A81024C298408433CF1ED7A2BC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
7
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1520 | svchost.exe | 40.112.72.205:80 | microsoft.com | Microsoft Corporation | IE | malicious |
1520 | svchost.exe | 104.47.53.36:25 | microsoft-com.mail.protection.outlook.com | Microsoft Corporation | US | unknown |
1520 | svchost.exe | 43.231.4.7:443 | — | Gigabit Hosting Sdn Bhd | MY | malicious |
1520 | svchost.exe | 98.136.96.77:25 | mta7.am0.yahoodns.net | Yahoo | US | unknown |
— | — | 173.194.202.26:25 | alt4.aspmx.l.google.com | Google Inc. | US | whitelisted |
1520 | svchost.exe | 85.114.134.88:484 | — | myLoc managed IT AG | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
microsoft.com |
| whitelisted |
microsoft-com.mail.protection.outlook.com |
| whitelisted |
yahoo.com |
| whitelisted |
mta7.am0.yahoodns.net |
| whitelisted |
google.com |
| whitelisted |
alt4.aspmx.l.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1520 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Tofsee.bot |
1520 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Tofsee.bot |