| File name: | 9a56d506889bc7c1904d4869a9e21e383a6f66eadc0dd71191cb74d3a2ed20b6.exe |
| Full analysis: | https://app.any.run/tasks/468850c8-3f68-4e4d-a033-e153427487ae |
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2024, 12:48:06 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | B4E634BAEECDE29B2599537D357F87A7 |
| SHA1: | 29CA3FD61D1563184E8C6353520AC2B0B82C81F5 |
| SHA256: | 9A56D506889BC7C1904D4869A9E21E383A6F66EADC0DD71191CB74D3A2ED20B6 |
| SSDEEP: | 3072:DLbR3VT8RiKvvCTbObUPTDvWyfLA+Sag8KGo:DLbfoRiKvvCHOQnvWyfLA+Sa6 |
MALICIOUS
Drops the executable file immediately after the start
- 9a56d506889bc7c1904d4869a9e21e383a6f66eadc0dd71191cb74d3a2ed20b6.exe (PID: 6216)
- powershell.exe (PID: 6388)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 6292)
Bypass execution policy to execute commands
- powershell.exe (PID: 6388)
SUSPICIOUS
Starts CMD.EXE for commands execution
- 9a56d506889bc7c1904d4869a9e21e383a6f66eadc0dd71191cb74d3a2ed20b6.exe (PID: 6216)
Executing commands from a ".bat" file
- 9a56d506889bc7c1904d4869a9e21e383a6f66eadc0dd71191cb74d3a2ed20b6.exe (PID: 6216)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6292)
The process executes Powershell scripts
- cmd.exe (PID: 6292)
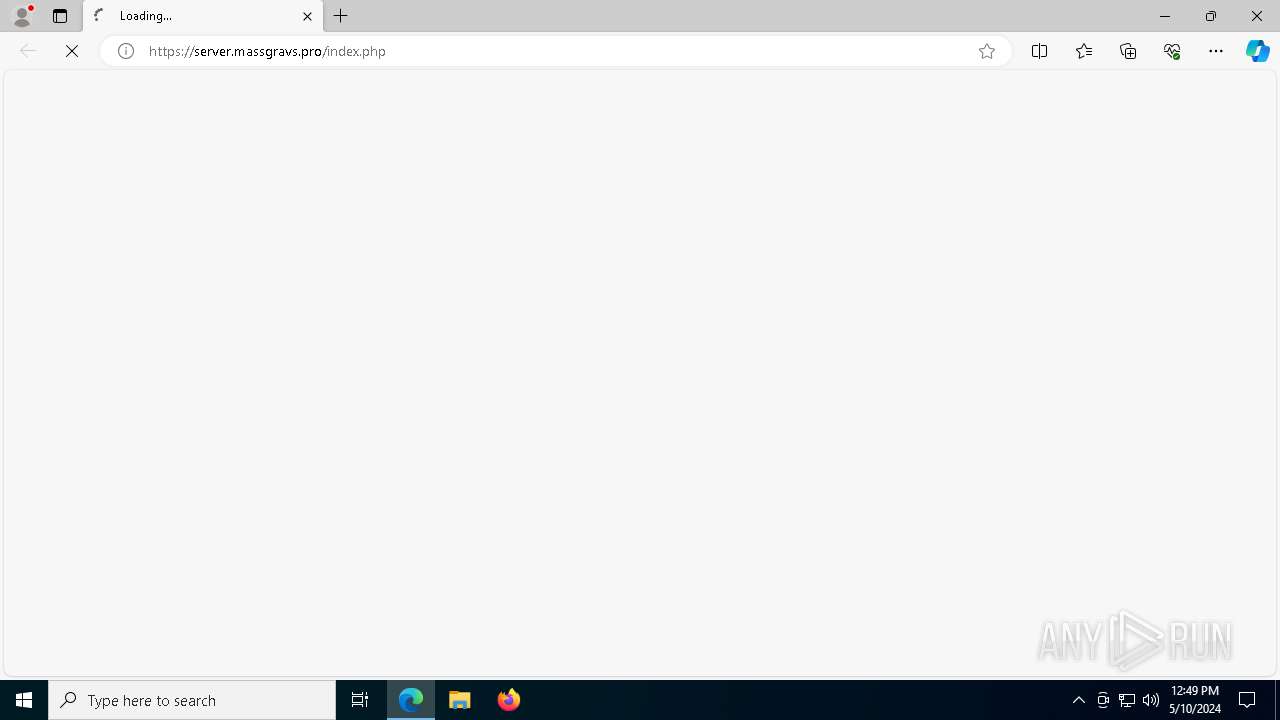
The Powershell connects to the Internet
- powershell.exe (PID: 6388)
Unusual connection from system programs
- powershell.exe (PID: 6388)
Executable content was dropped or overwritten
- powershell.exe (PID: 6388)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 6388)
INFO
Reads the machine GUID from the registry
- 9a56d506889bc7c1904d4869a9e21e383a6f66eadc0dd71191cb74d3a2ed20b6.exe (PID: 6216)
Reads the computer name
- 9a56d506889bc7c1904d4869a9e21e383a6f66eadc0dd71191cb74d3a2ed20b6.exe (PID: 6216)
- 5932464.exe (PID: 5712)
- identity_helper.exe (PID: 2684)
Checks supported languages
- 9a56d506889bc7c1904d4869a9e21e383a6f66eadc0dd71191cb74d3a2ed20b6.exe (PID: 6216)
- identity_helper.exe (PID: 2684)
- 5932464.exe (PID: 5712)
Create files in a temporary directory
- 9a56d506889bc7c1904d4869a9e21e383a6f66eadc0dd71191cb74d3a2ed20b6.exe (PID: 6216)
Gets or sets the time when the file was last written to (POWERSHELL)
- powershell.exe (PID: 6388)
Checks proxy server information
- powershell.exe (PID: 6388)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 6388)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6388)
- powershell.exe (PID: 6388)
Reads Microsoft Office registry keys
- msedge.exe (PID: 1572)
Application launched itself
- msedge.exe (PID: 1572)
Reads the software policy settings
- slui.exe (PID: 4628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (49.4) |
|---|---|---|
| .scr | | | Windows screen saver (23.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (11.7) |
| .exe | | | Win32 Executable (generic) (8) |
| .exe | | | Generic Win/DOS Executable (3.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2078:10:28 05:37:59+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 68096 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x127fe |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.768 |
| ProductVersionNumber: | 2.0.0.768 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Adobe Inc |
| FileDescription: | Adobe Download Manager |
| FileVersion: | 2.0.0.768s |
| InternalName: | Adobe Download Manager |
| LegalCopyright: | Copyright 2019 Adobe Inc. All rights reserved. |
| OriginalFileName: | Adobe Download Manager |
| ProductName: | Adobe Download Manager |
| ProductVersion: | 2.0.0.768s |
Total processes
166
Monitored processes
40
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4316 --field-trial-handle=2372,i,16889376360961763532,11423114351518337610,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1152 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1572 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://server.massgravs.pro/index.php | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1984 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3828 --field-trial-handle=2372,i,16889376360961763532,11423114351518337610,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2452 | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe -Embedding | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneDriveFile Co-Authoring Executable Exit code: 0 Version: 19.043.0304.0013 Modules
| |||||||||||||||
| 2684 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5988 --field-trial-handle=2372,i,16889376360961763532,11423114351518337610,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2916 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=6624 --field-trial-handle=2372,i,16889376360961763532,11423114351518337610,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3656 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5988 --field-trial-handle=2372,i,16889376360961763532,11423114351518337610,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4024 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3512 --field-trial-handle=2372,i,16889376360961763532,11423114351518337610,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5652 --field-trial-handle=2372,i,16889376360961763532,11423114351518337610,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
17 282
Read events
17 170
Write events
109
Delete events
3
Modification events
| (PID) Process: | (6388) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6388) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6388) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6388) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6388) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6388) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6388) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6388) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6388) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6388) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
3
Suspicious files
56
Text files
43
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6388 | powershell.exe | C:\5932464\Win5932464\chrome.exe | — | |
MD5:— | SHA256:— | |||
| 6388 | powershell.exe | C:\5932464\Win5932464\5932464.exe | — | |
MD5:— | SHA256:— | |||
| 1572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\abb8f205-a440-45c5-a15f-ecf0fc2de8df.tmp | — | |
MD5:— | SHA256:— | |||
| 6388 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ug2lz40b.xxu.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6388 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hlbvs2k3.2ny.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6216 | 9a56d506889bc7c1904d4869a9e21e383a6f66eadc0dd71191cb74d3a2ed20b6.exe | C:\Users\admin\AppData\Local\Temp\oculta.bat | text | |
MD5:B6A034D1E30E67525481785E15F3BE48 | SHA256:0176903485BD2A6D2D58E0F8259B49860CC87AD1782DE516B163063D0F021C1E | |||
| 6388 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:8B35E41A3D9E5A3F5F637C7C1FB845F2 | SHA256:3C1C49A4609CE11026FB579692011F42B1D4BC80869185500E9F1FC3C285E345 | |||
| 1572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Last Version | text | |
MD5:C7E2197BAE099B13BBB3ADEB1433487D | SHA256:3460EEAF45D581DD43A6E4E17AF8102DDAFF5AEAA88B10099527CF85211629E9 | |||
| 1572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF121342.TMP | — | |
MD5:— | SHA256:— | |||
| 1572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF121342.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
85
DNS requests
63
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5228 | svchost.exe | GET | 200 | 23.56.109.134:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
5228 | svchost.exe | GET | 200 | 23.61.152.46:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
4680 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | — | — | unknown |
5940 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
6388 | powershell.exe | GET | — | 103.117.141.64:80 | http://massgra.site/get/chrome.zip | unknown | — | — | unknown |
6576 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | unknown |
5860 | SIHClient.exe | GET | 200 | 23.61.152.46:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
6816 | svchost.exe | HEAD | 200 | 79.140.80.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/71fb6206-ed06-4b1d-9977-e1832c77726d?P1=1715379780&P2=404&P3=2&P4=c3RBclt5A3BN94ehQSZqcAGkufXYZZu576urXPIJ3k5iXxIaMo5xIgUIeTlf95zWXeTFCMmu22iK7Fv4tFf3fw%3d%3d | unknown | — | — | unknown |
5860 | SIHClient.exe | GET | 200 | 23.61.152.46:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4364 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
5228 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2308 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5140 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5228 | svchost.exe | 23.56.109.134:80 | crl.microsoft.com | Akamai International B.V. | FR | unknown |
5228 | svchost.exe | 23.61.152.46:80 | www.microsoft.com | AKAMAI-AS | BR | unknown |
4680 | SearchApp.exe | 2.16.197.40:443 | www.bing.com | Akamai International B.V. | BR | unknown |
5940 | svchost.exe | 20.190.160.22:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5940 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
r.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
massgra.site |
| unknown |
go.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6388 | powershell.exe | Potentially Bad Traffic | ET HUNTING Terse Request for Zip File (GET) |