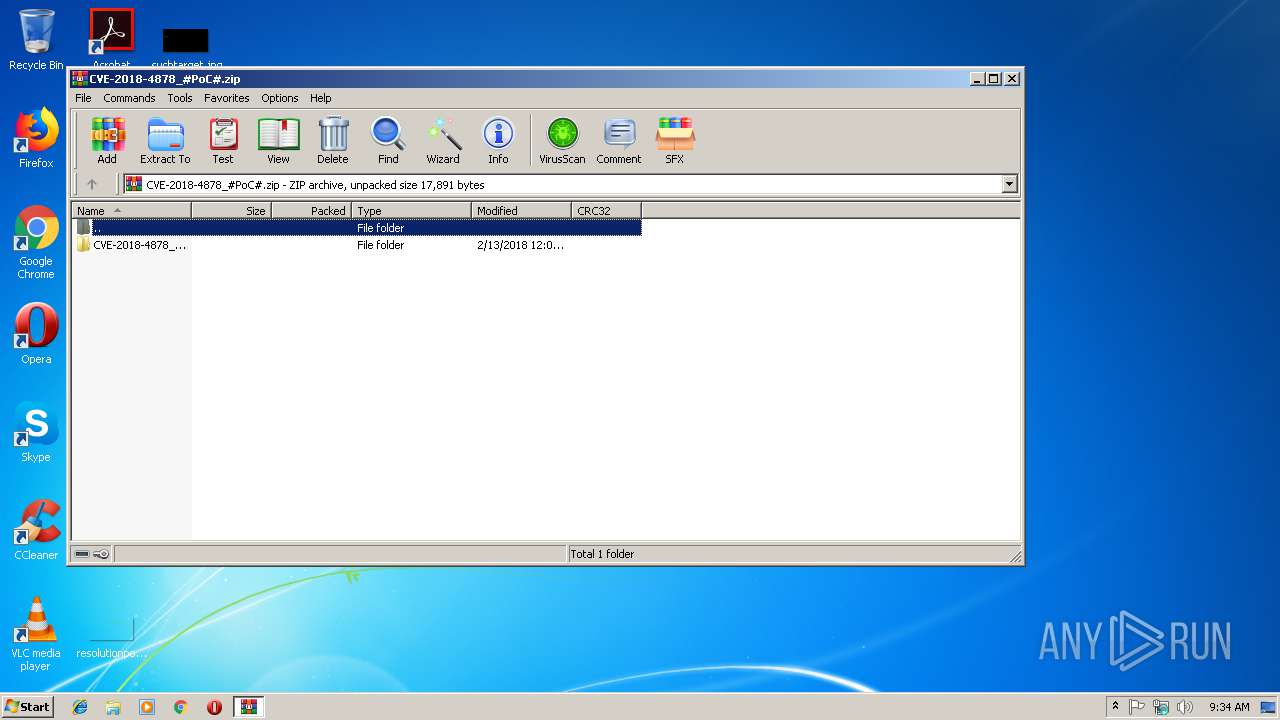
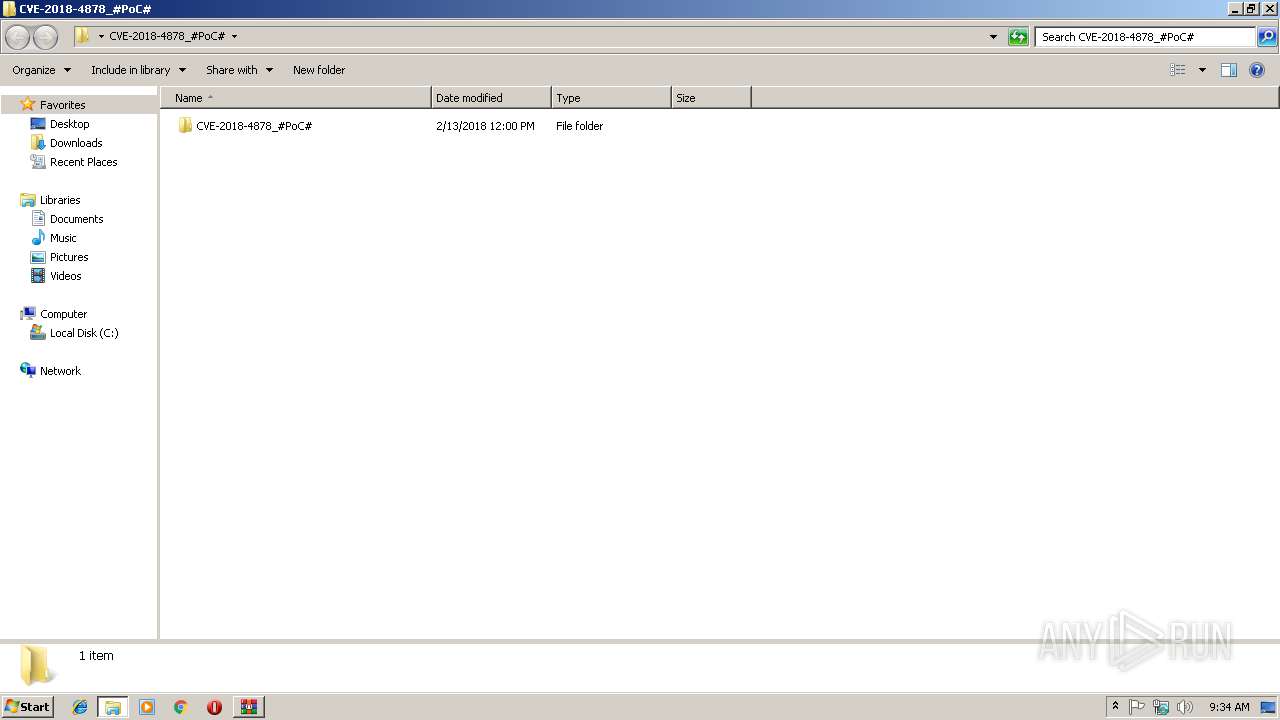
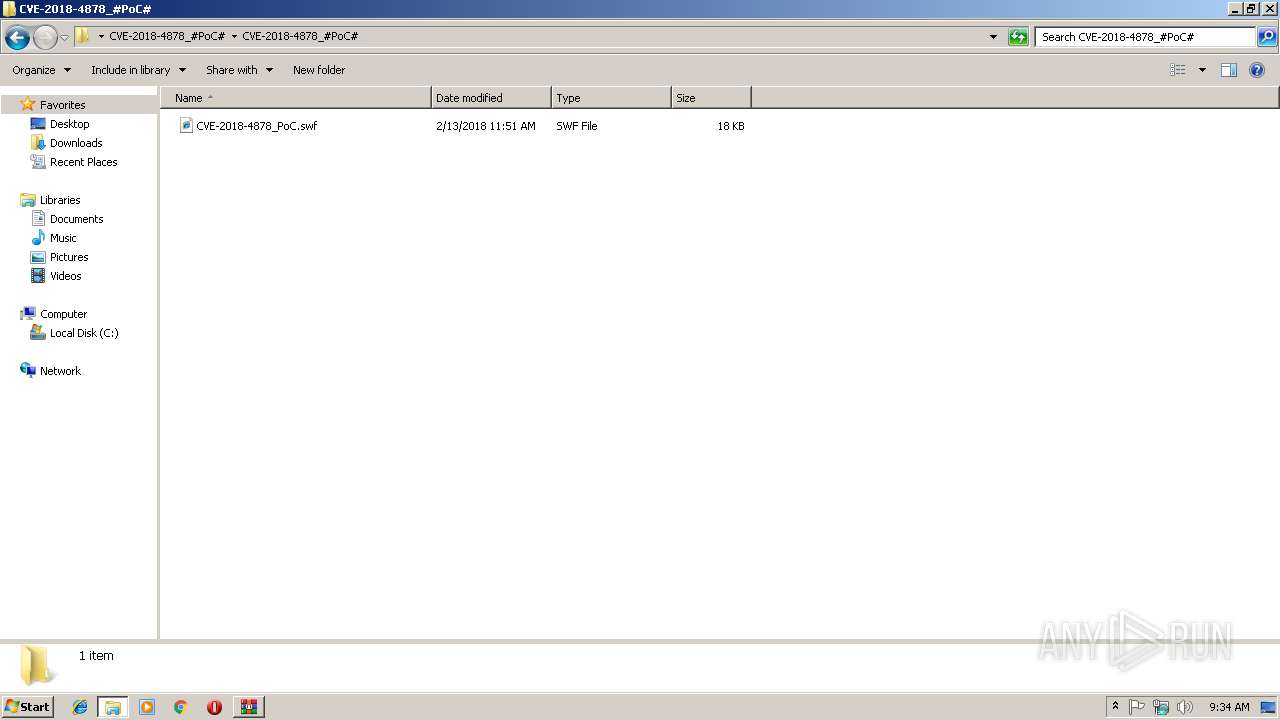
| File name: | CVE-2018-4878_#PoC#.zip |
| Full analysis: | https://app.any.run/tasks/2b0f6b57-2142-4c4a-993f-f5ae2fd89539 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2018, 09:33:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | ACFD127D82A01F89AFA94F3FFD836BEC |
| SHA1: | 4710F1B2B8C8784B60C00DD65ECEC7DEE912B58E |
| SHA256: | 9A5345FBE2991EA07F050ED5C5D086CF759E11E7C2ED2A2ACD90582238A50411 |
| SSDEEP: | 192:Vt4kQYLxoDsFVlJbm9p2stwhYManoCoLdkjJil08fGO+MNSeNLX2BZ7Ldxk:Vtm2UsFLJKPxManEwOvfG/MN3Ls6 |
MALICIOUS
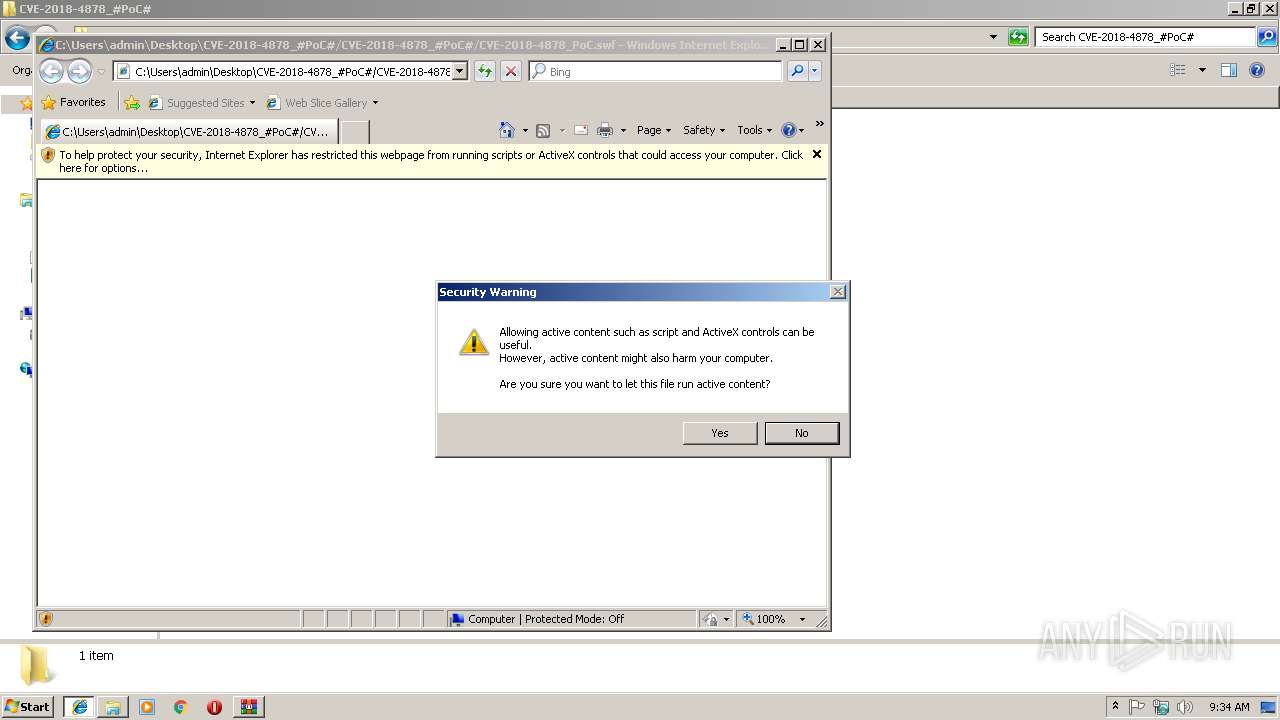
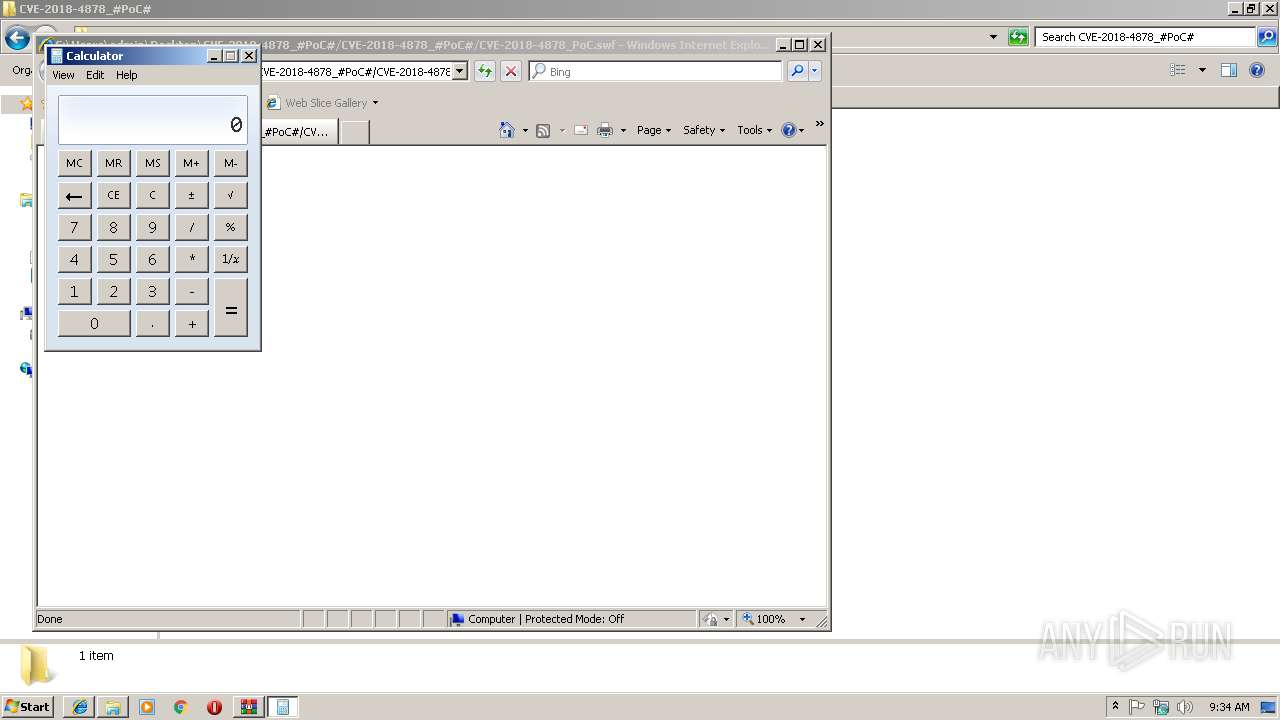
Runs app for hidden code execution
- iexplore.exe (PID: 3124)
Starts CMD.EXE for commands execution
- iexplore.exe (PID: 3124)
SUSPICIOUS
Starts Internet Explorer
- rundll32.exe (PID: 3060)
INFO
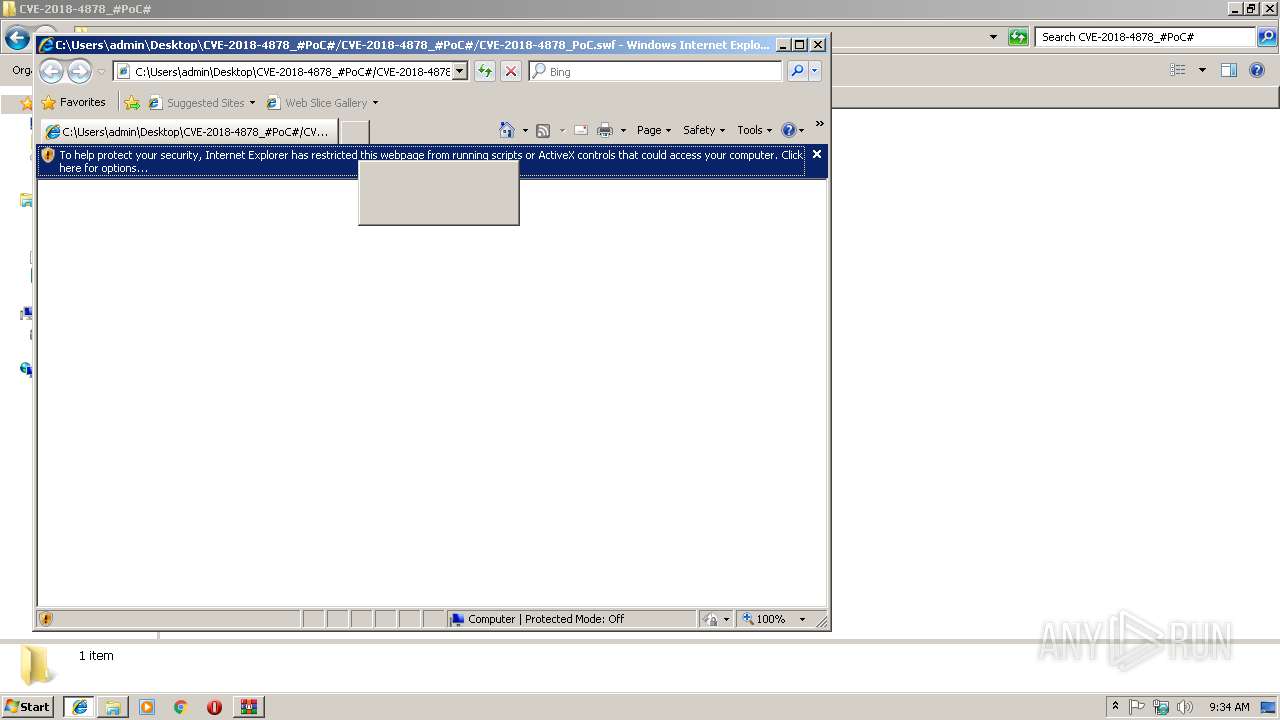
Reads internet explorer settings
- iexplore.exe (PID: 3124)
Application launched itself
- iexplore.exe (PID: 2944)
Changes internet zones settings
- iexplore.exe (PID: 2944)
Reads Internet Cache Settings
- iexplore.exe (PID: 3124)
Creates files in the user directory
- iexplore.exe (PID: 3124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:02:13 14:00:19 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | CVE-2018-4878_#PoC#/ |
Total processes
41
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
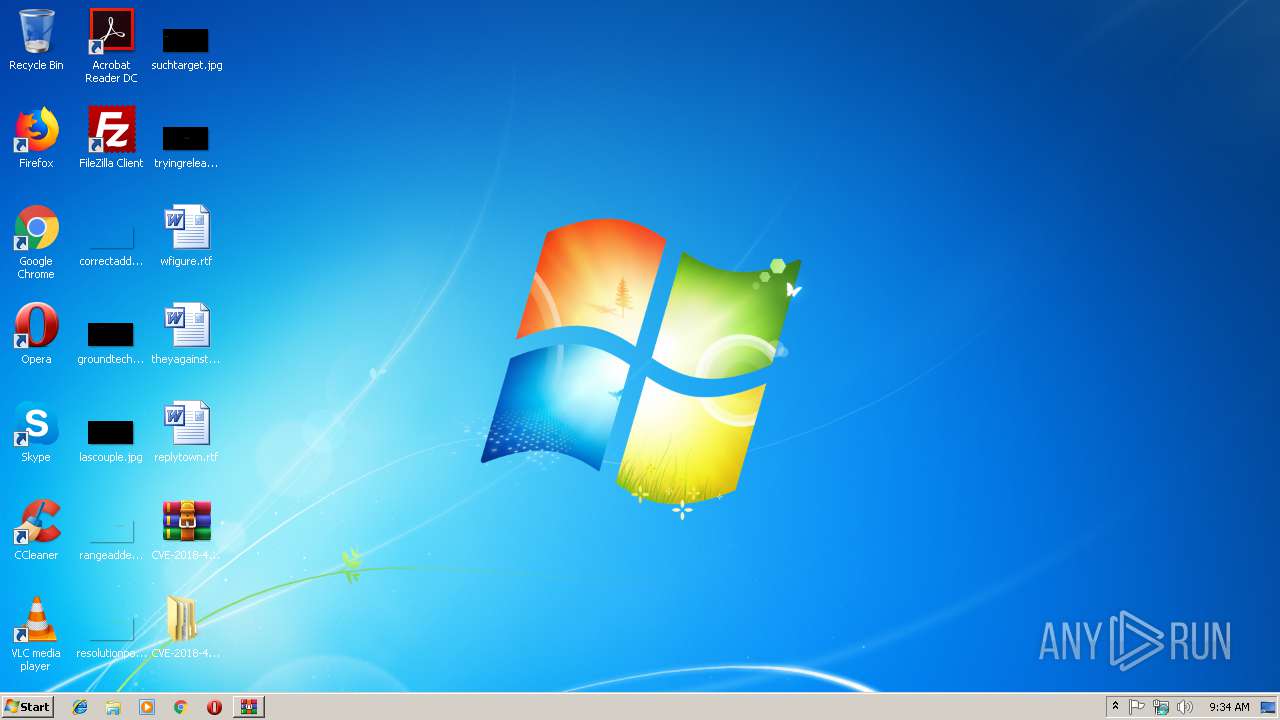
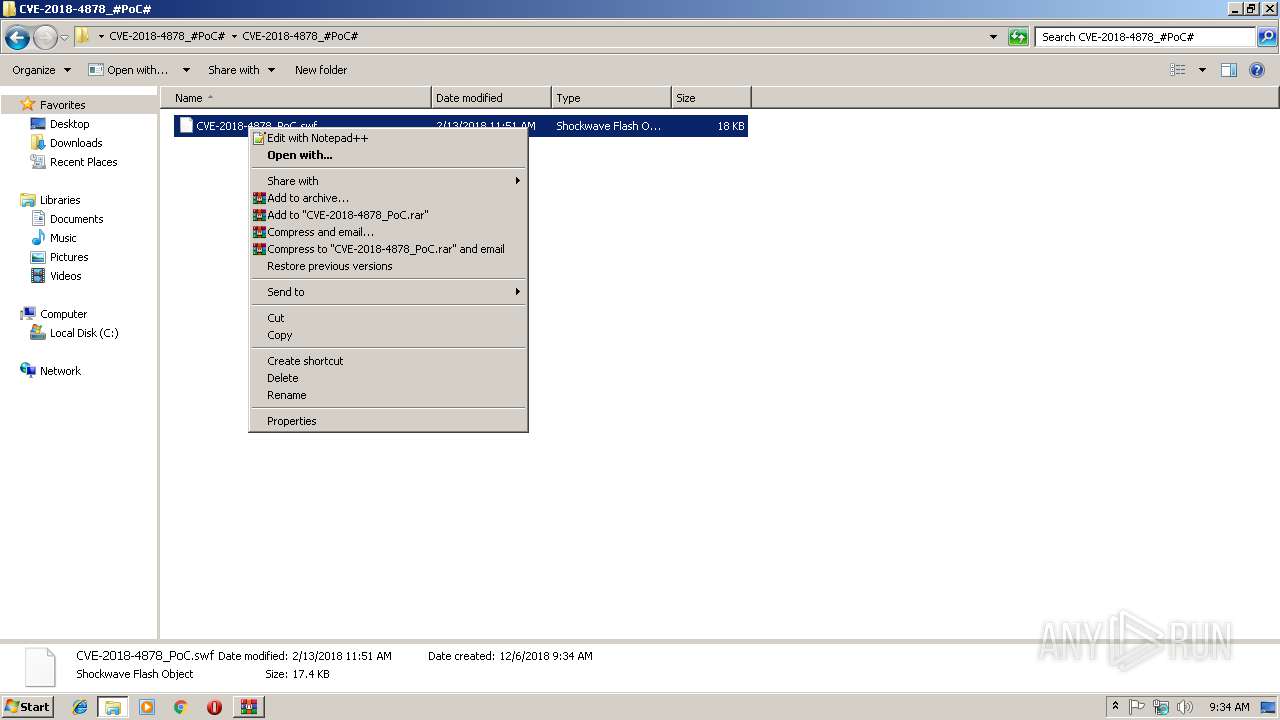
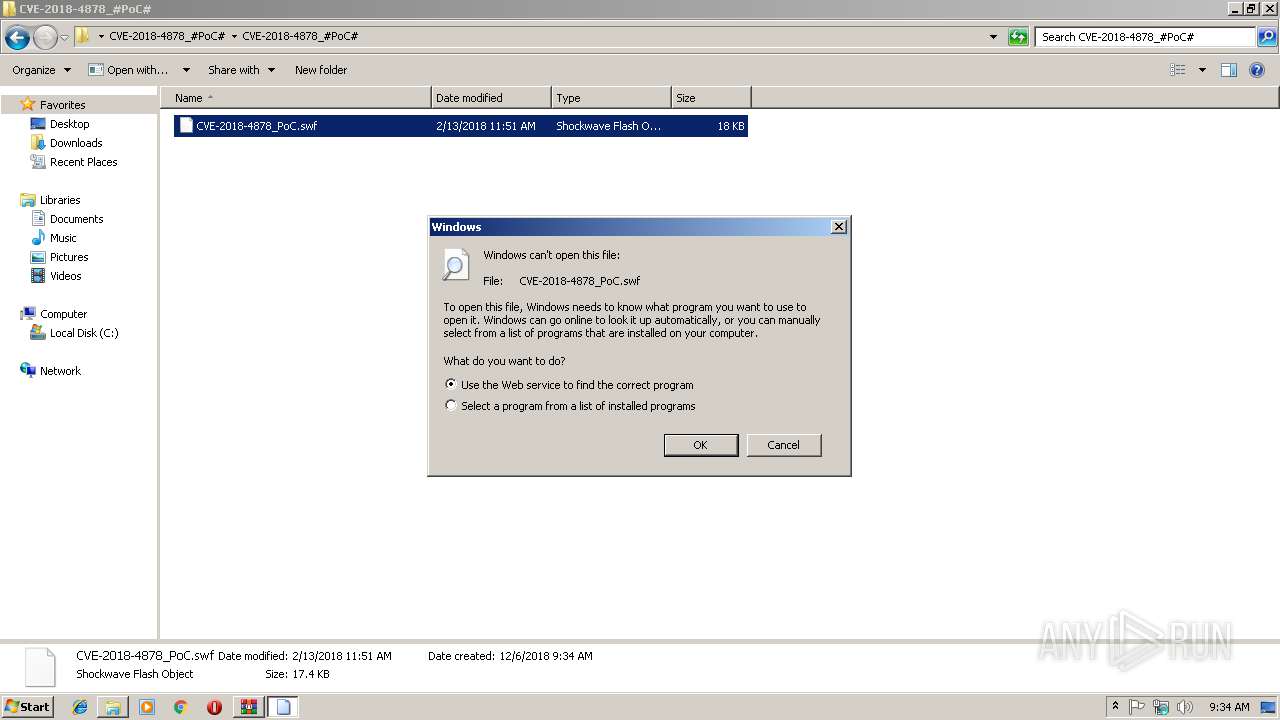
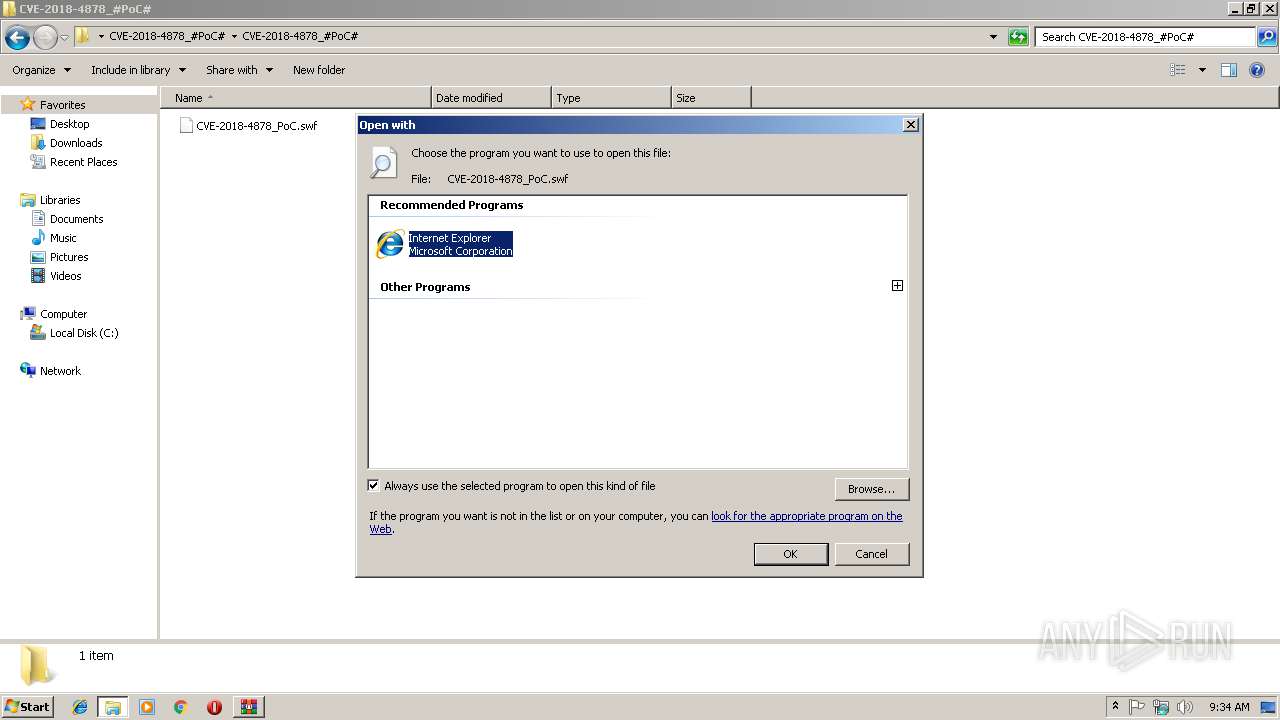
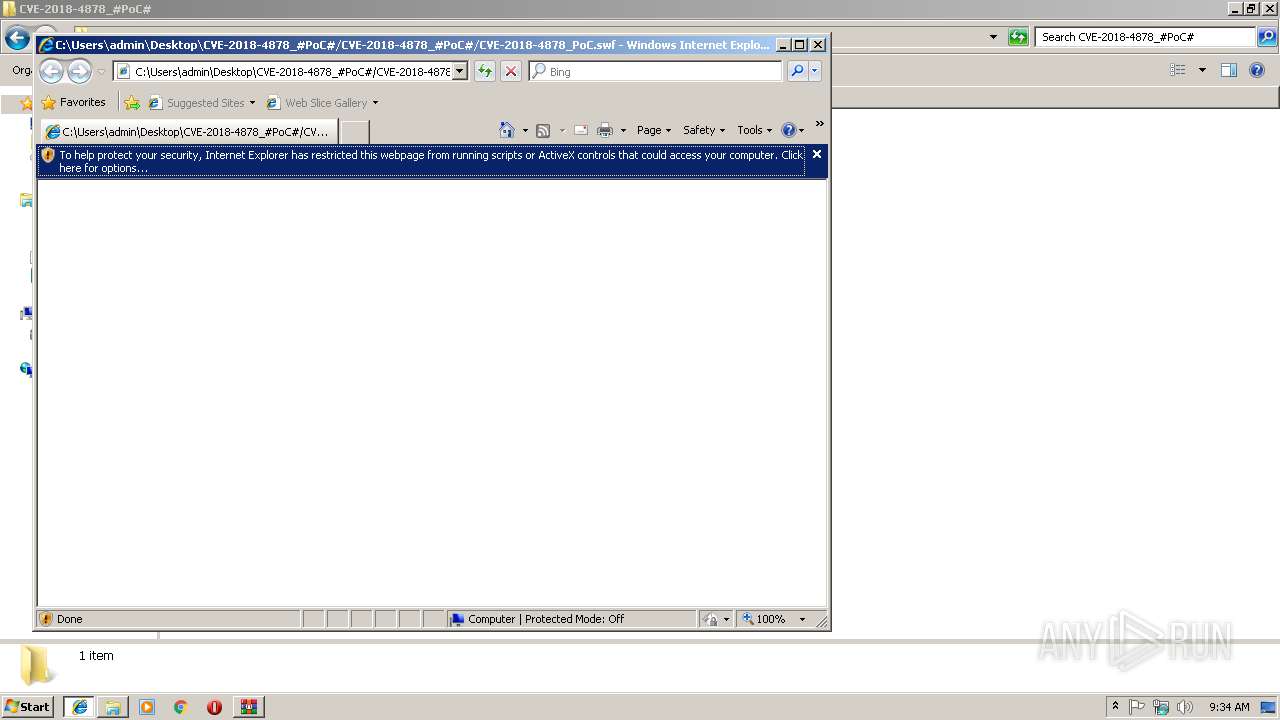
| 2944 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\Desktop\CVE-2018-4878_#PoC#\CVE-2018-4878_#PoC#\CVE-2018-4878_PoC.swf | C:\Program Files\Internet Explorer\iexplore.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3060 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\CVE-2018-4878_#PoC#\CVE-2018-4878_#PoC#\CVE-2018-4878_PoC.swf | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3124 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2944 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3392 | C:\Windows\System32\cmd.exe | C:\Windows\System32\cmd.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1278912021 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
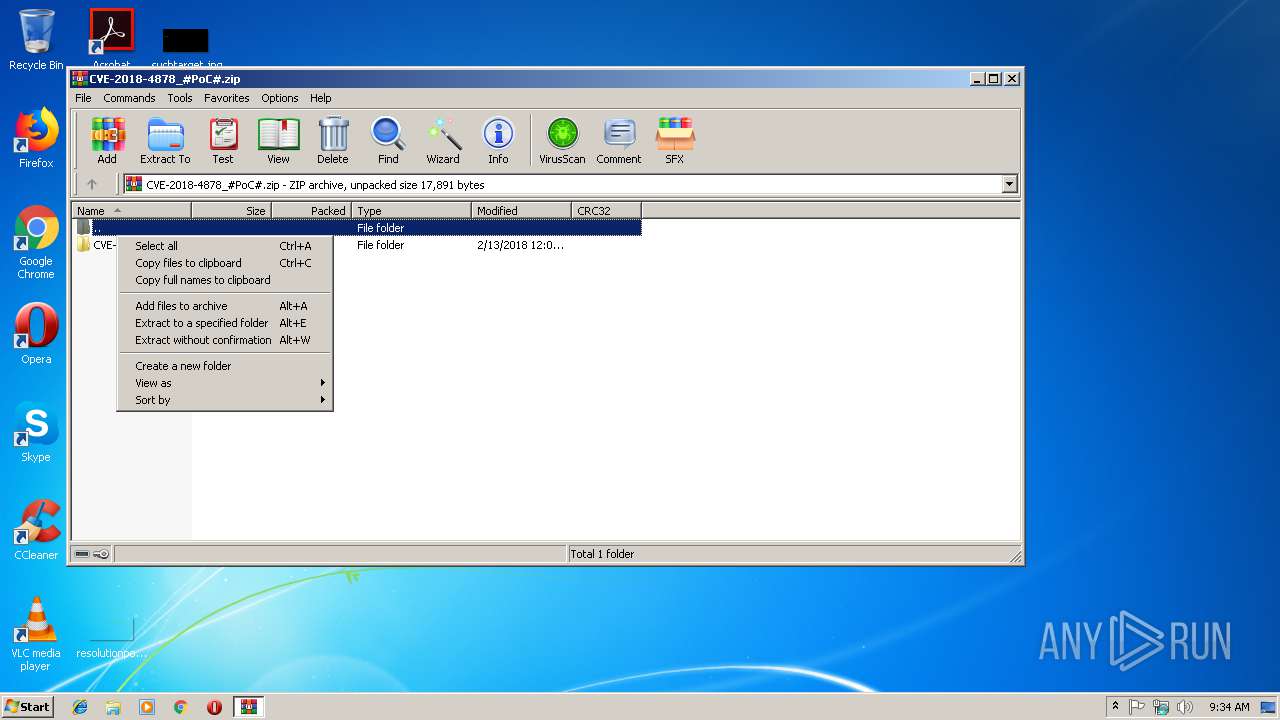
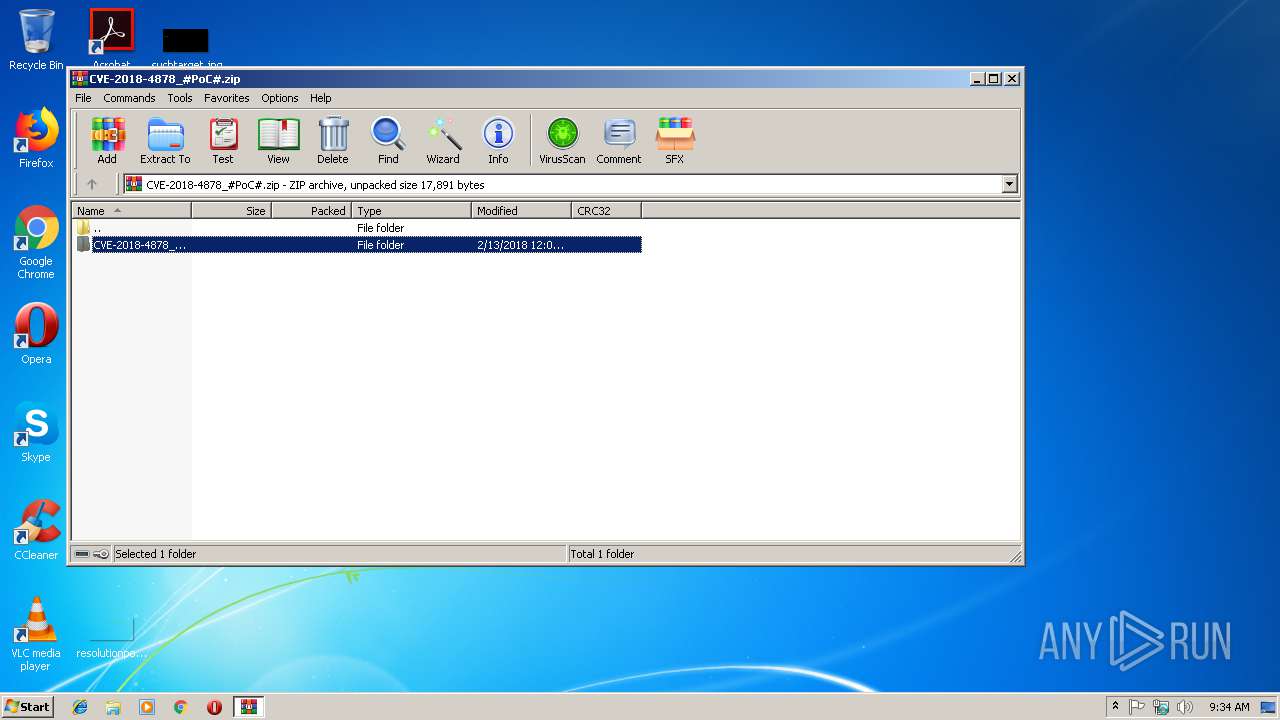
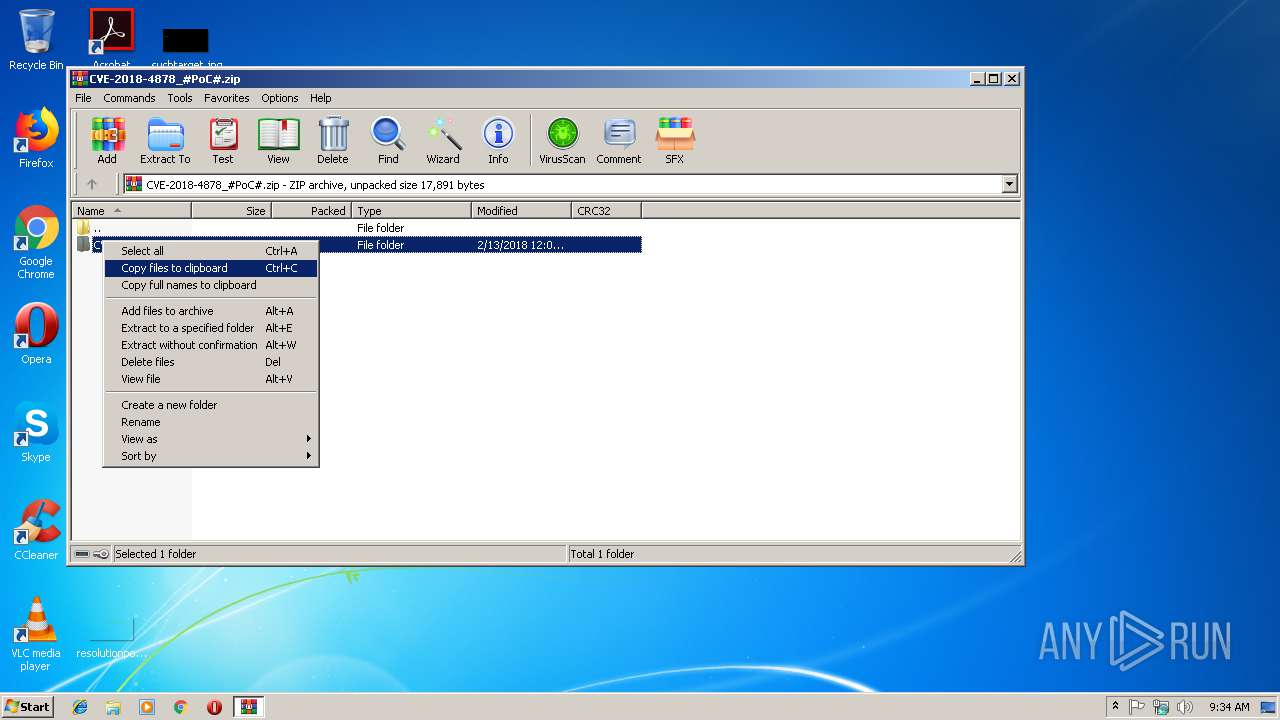
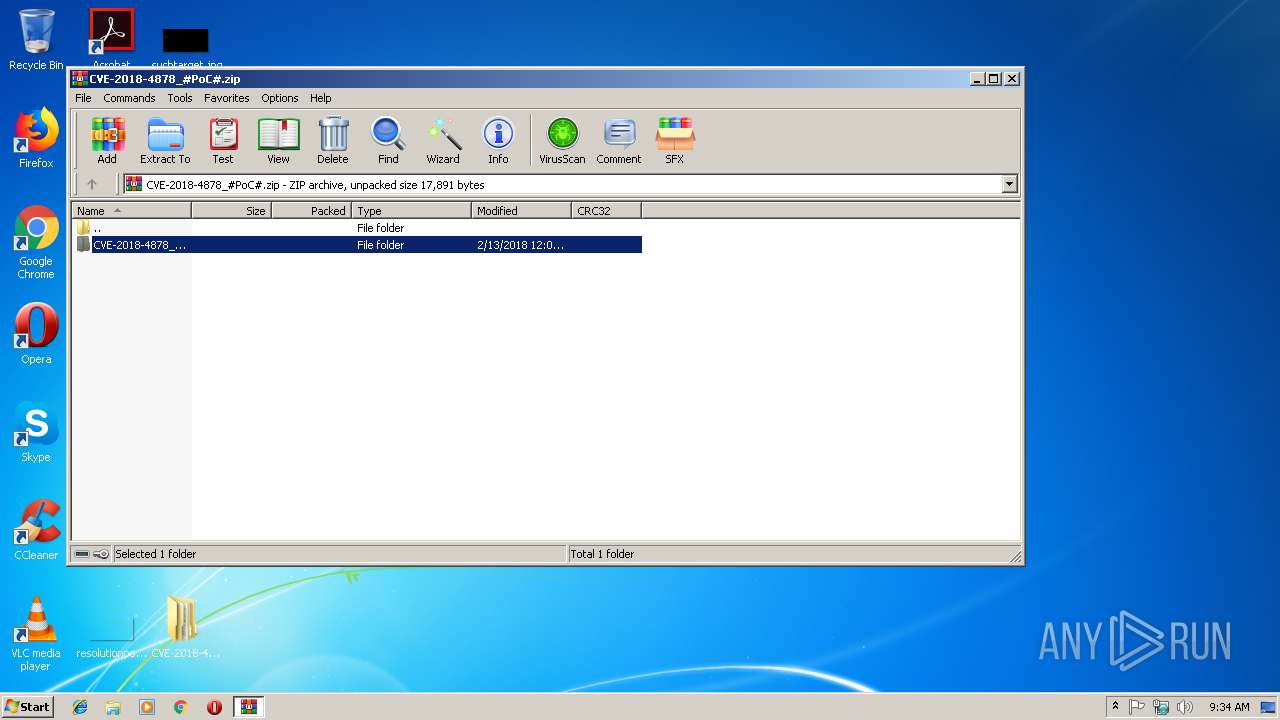
| 3536 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\CVE-2018-4878_#PoC#.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3856 | calc | C:\Windows\System32\calc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Calculator Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
887
Read events
744
Write events
143
Delete events
0
Modification events
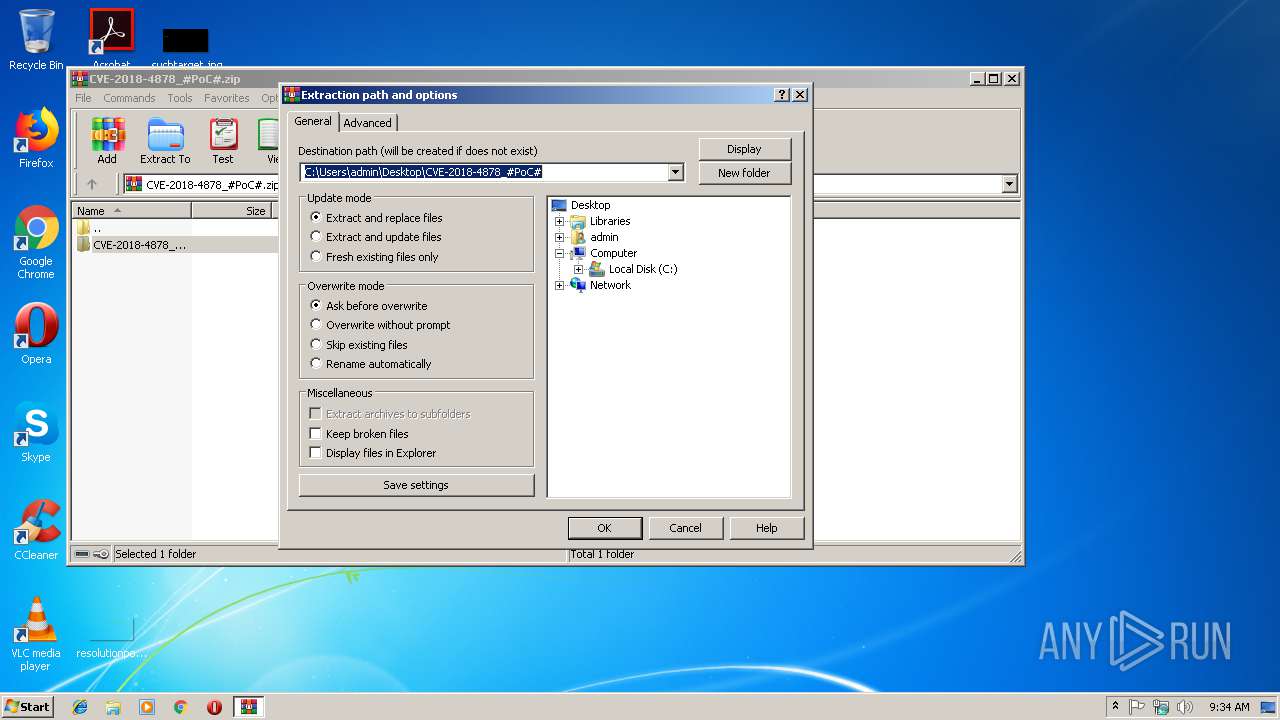
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\CVE-2018-4878_#PoC#.zip | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\CVE-2018-4878_#PoC# | |||
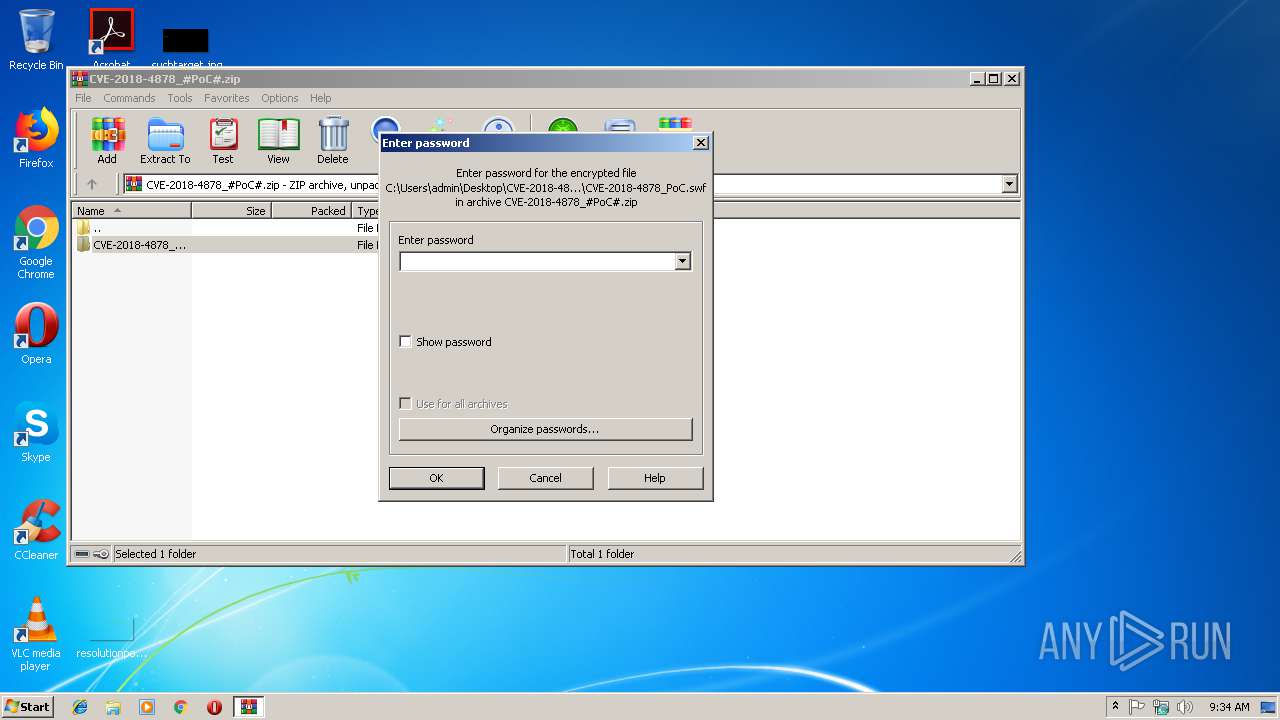
| (PID) Process: | (3536) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
36
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2944 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2944 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3124 | iexplore.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sxx | — | |
MD5:— | SHA256:— | |||
| 3536 | WinRAR.exe | C:\Users\admin\Desktop\CVE-2018-4878_#PoC#\CVE-2018-4878_#PoC#\CVE-2018-4878_PoC.swf | swf | |
MD5:— | SHA256:— | |||
| 3124 | iexplore.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sol | sol | |
MD5:— | SHA256:— | |||
| 3124 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\crossdomain[1].xml | xml | |
MD5:— | SHA256:— | |||
| 3124 | iexplore.exe | C:\Users\admin\AppData\Roaming\Adobe\Flash Player\APSPrivateData2\0\drm-ax-win-x86\GlobalStateStore.gs.lkg | der | |
MD5:— | SHA256:— | |||
| 3124 | iexplore.exe | C:\Users\admin\AppData\Roaming\Adobe\Flash Player\APSPrivateData2\0\drm-ax-win-x86\CertStore.dat.lkg | cat | |
MD5:— | SHA256:— | |||
| 2944 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[3].png | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
| 3124 | iexplore.exe | C:\Users\admin\AppData\Roaming\Adobe\Flash Player\APSPrivateData2\0\drm-ax-win-x86\MiscGlobalDataStore.mgd.lkg | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
2
DNS requests
2
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3124 | iexplore.exe | POST | 200 | 52.4.148.166:80 | http://individualization.adobe.com/flashaccess/i15n/v5 | US | cat | 9.54 Kb | whitelisted |
3124 | iexplore.exe | GET | 200 | 52.4.148.166:80 | http://individualization.adobe.com/crossdomain.xml | US | xml | 286 b | whitelisted |
2944 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2944 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3124 | iexplore.exe | 52.4.148.166:80 | individualization.adobe.com | Amazon.com, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
individualization.adobe.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3124 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Outdated Flash Version M1 |