| File name: | 9a52d1615be6f25a1ae7b93238cb8c70c27466ce73ed4f135c3e9695ac0ea502_visualizePend278609.bin |
| Full analysis: | https://app.any.run/tasks/53e66eef-380c-43cb-be39-817bd2e464d0 |
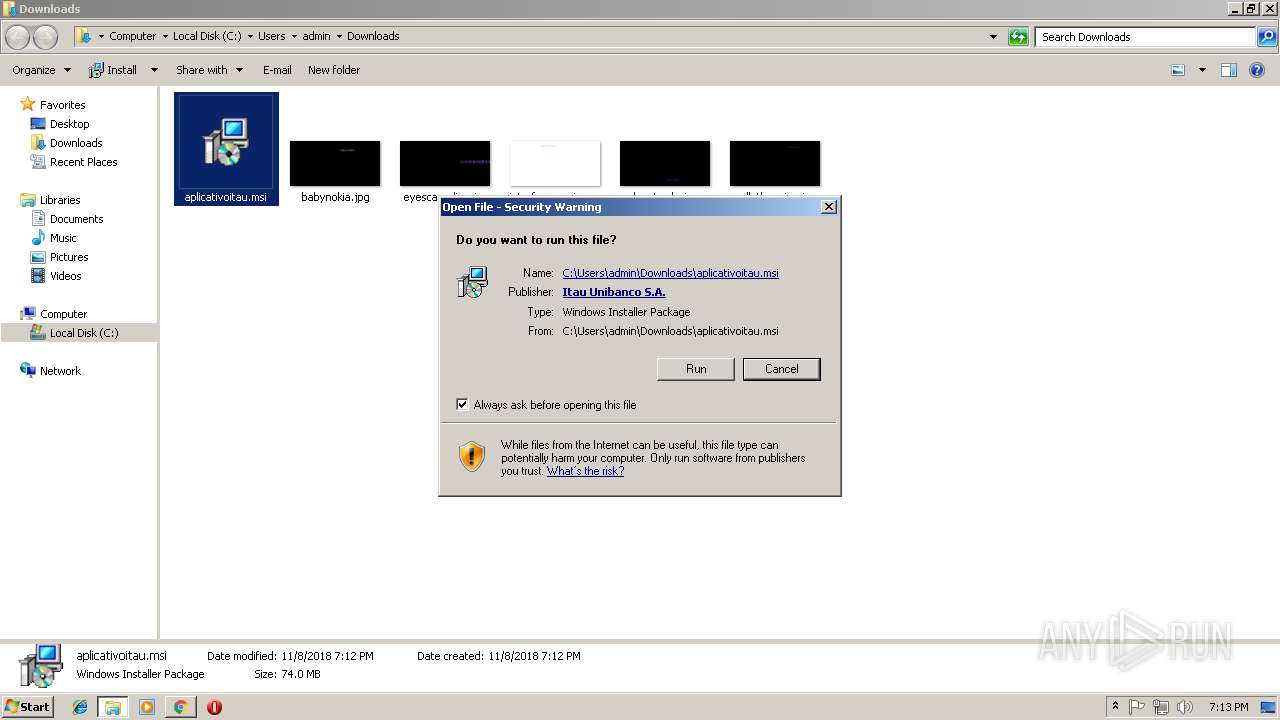
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2018, 19:11:44 |
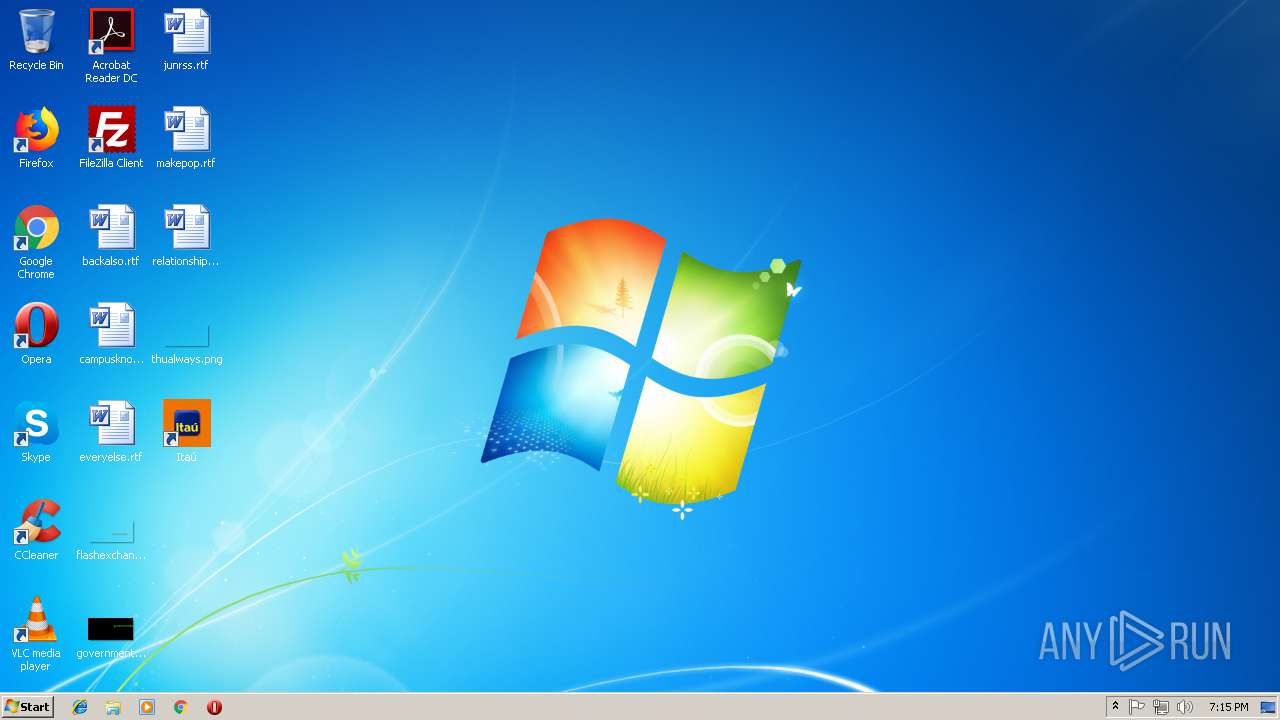
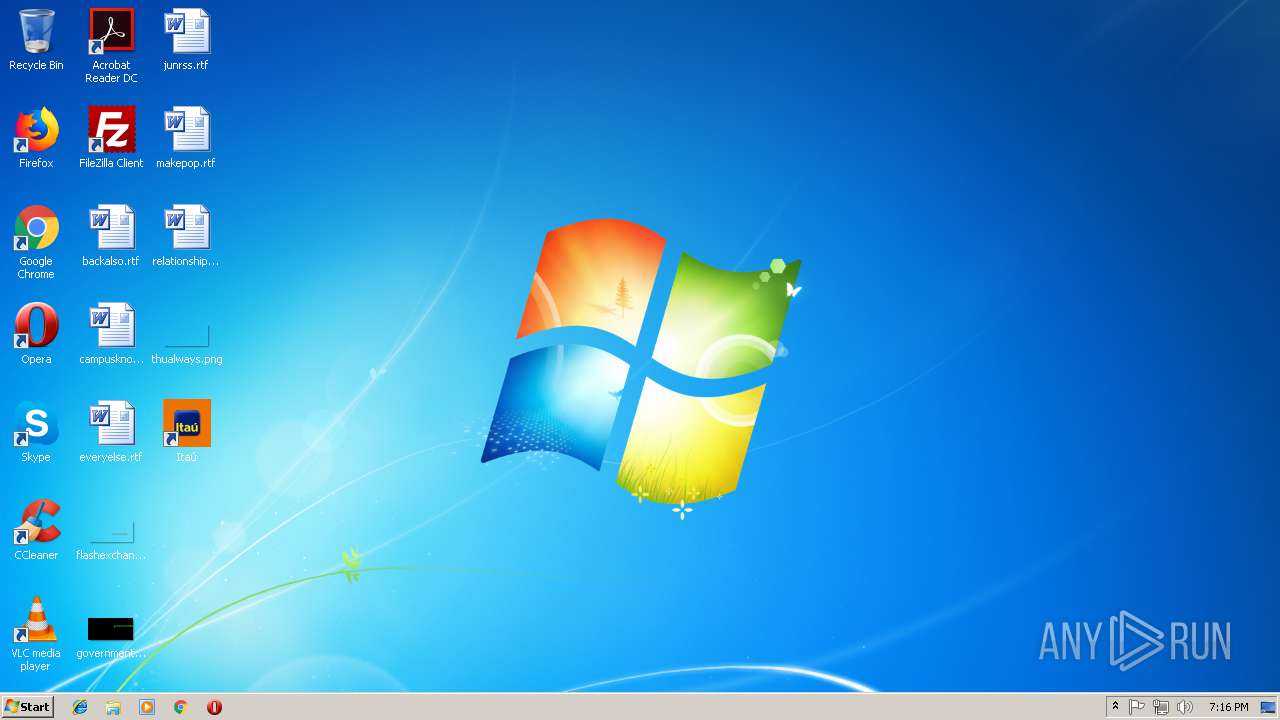
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DFD15589266A3551F4FBADB844B3872B |
| SHA1: | F44266D8EE26BEB0CBBC75F8DEC33C4E2522981D |
| SHA256: | 9A52D1615BE6F25A1AE7B93238CB8C70C27466CE73ED4F135C3E9695AC0EA502 |
| SSDEEP: | 49152:bbPiQ4fS5Z8t4sLspB7E1xCJ2erYUcY1mwTdTPg:bbPRutaZ2jYzg |
MALICIOUS
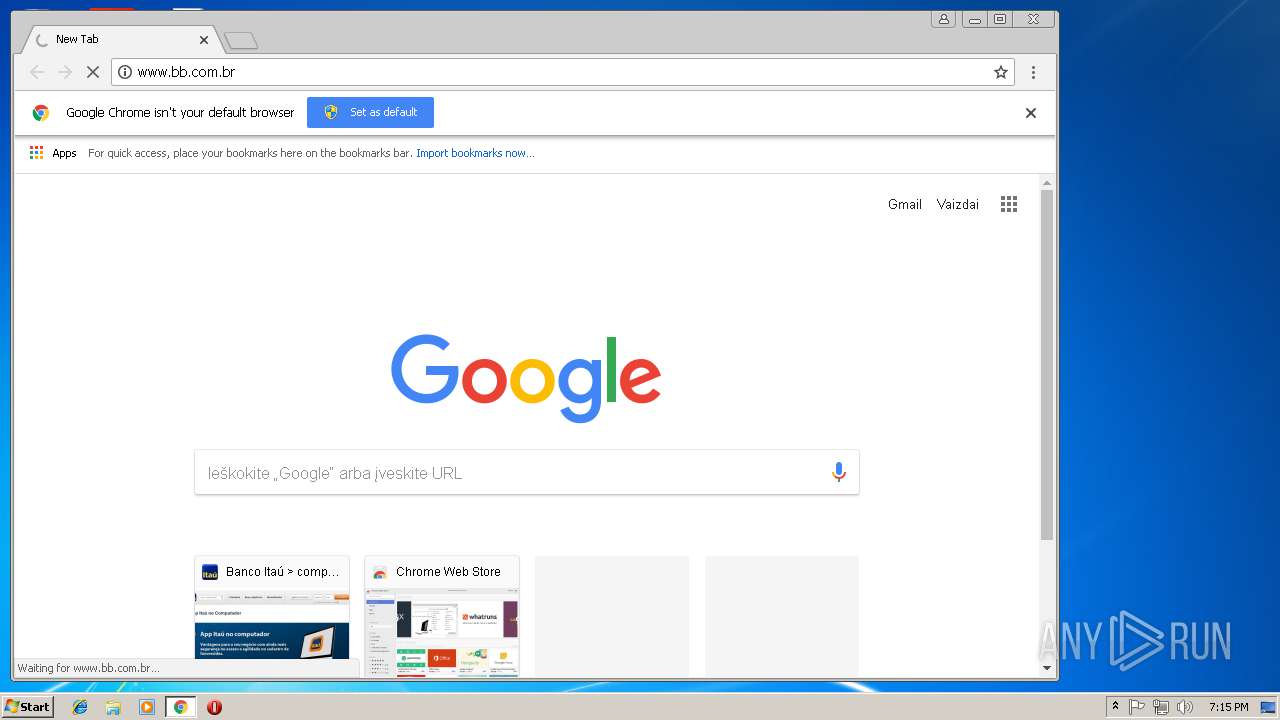
LatentBot was detected
- msIO5Xbiogs.exe (PID: 1824)
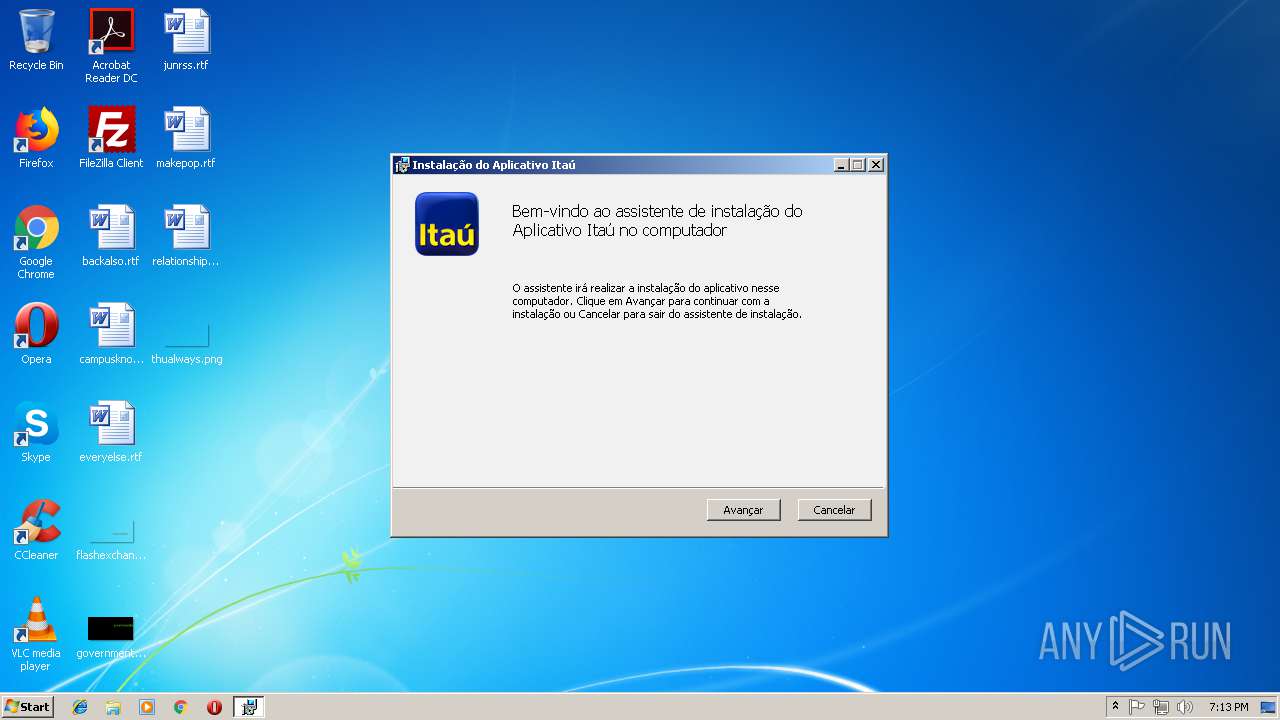
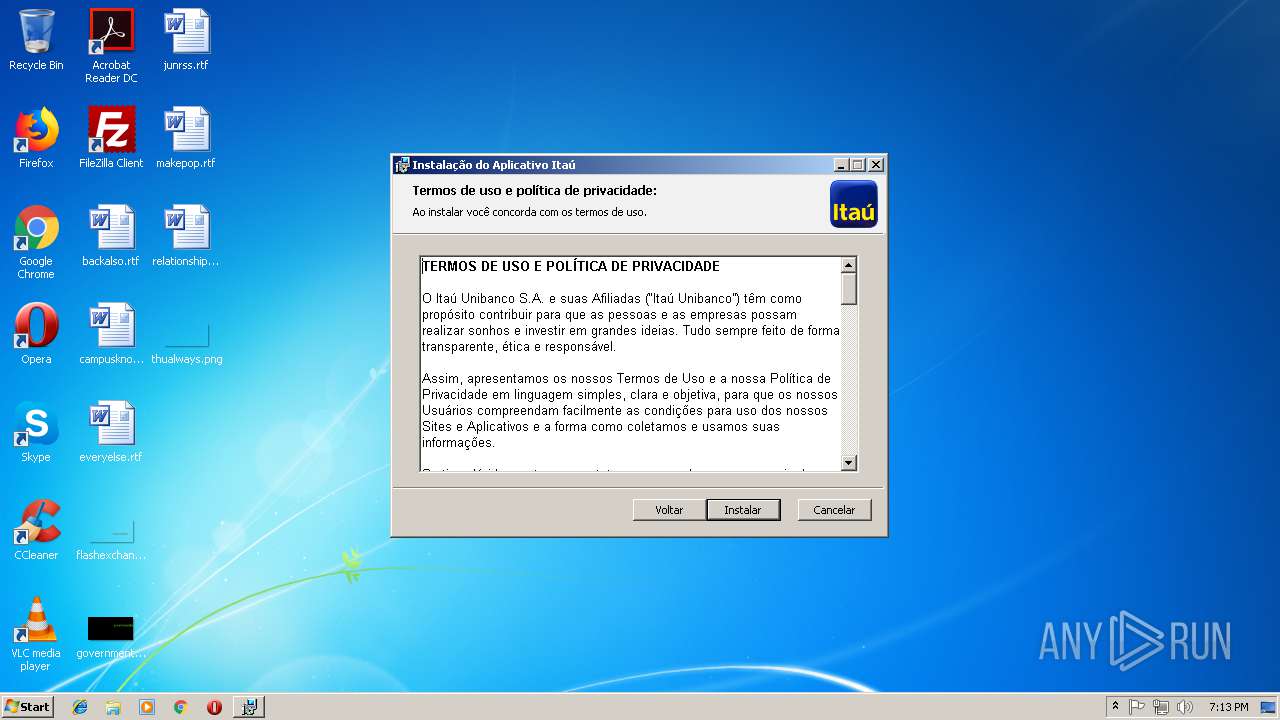
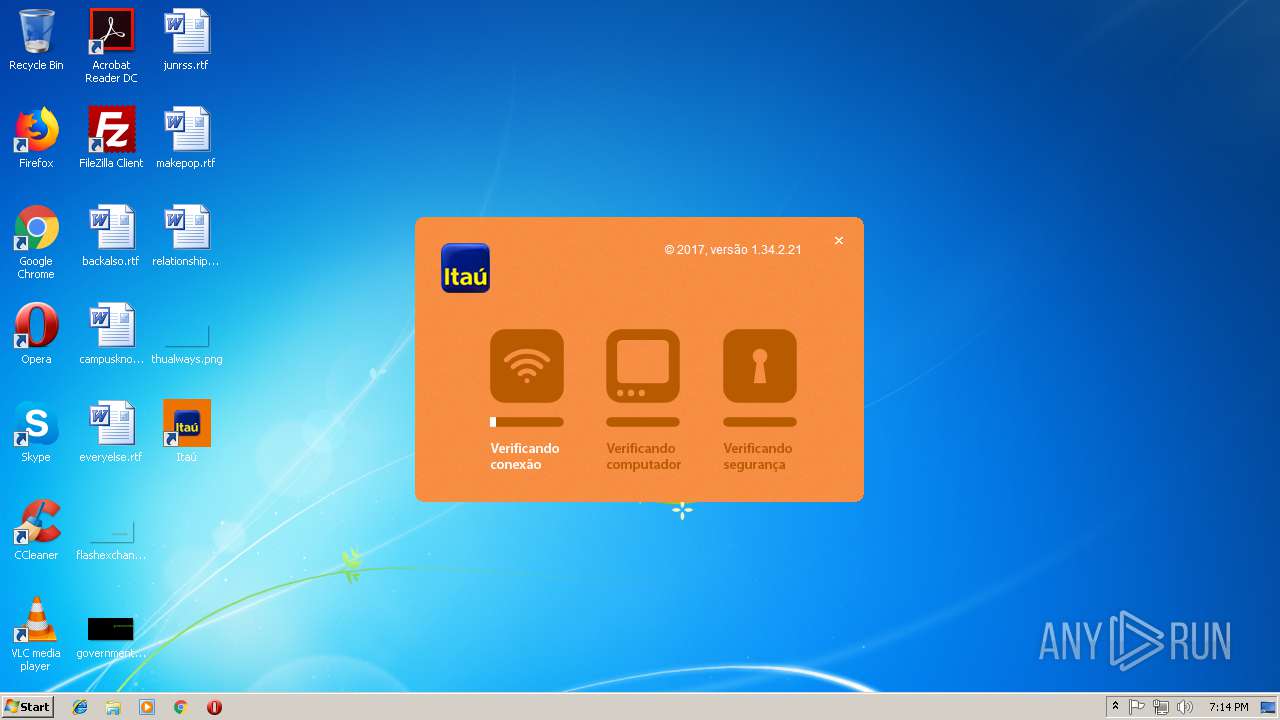
BANLOAD was detected
- 9a52d1615be6f25a1ae7b93238cb8c70c27466ce73ed4f135c3e9695ac0ea502_visualizePend278609.bin.exe (PID: 4060)
Writes to a start menu file
- msIO5Xbiogs.exe (PID: 1824)
Connects to CnC server
- msIO5Xbiogs.exe (PID: 1824)
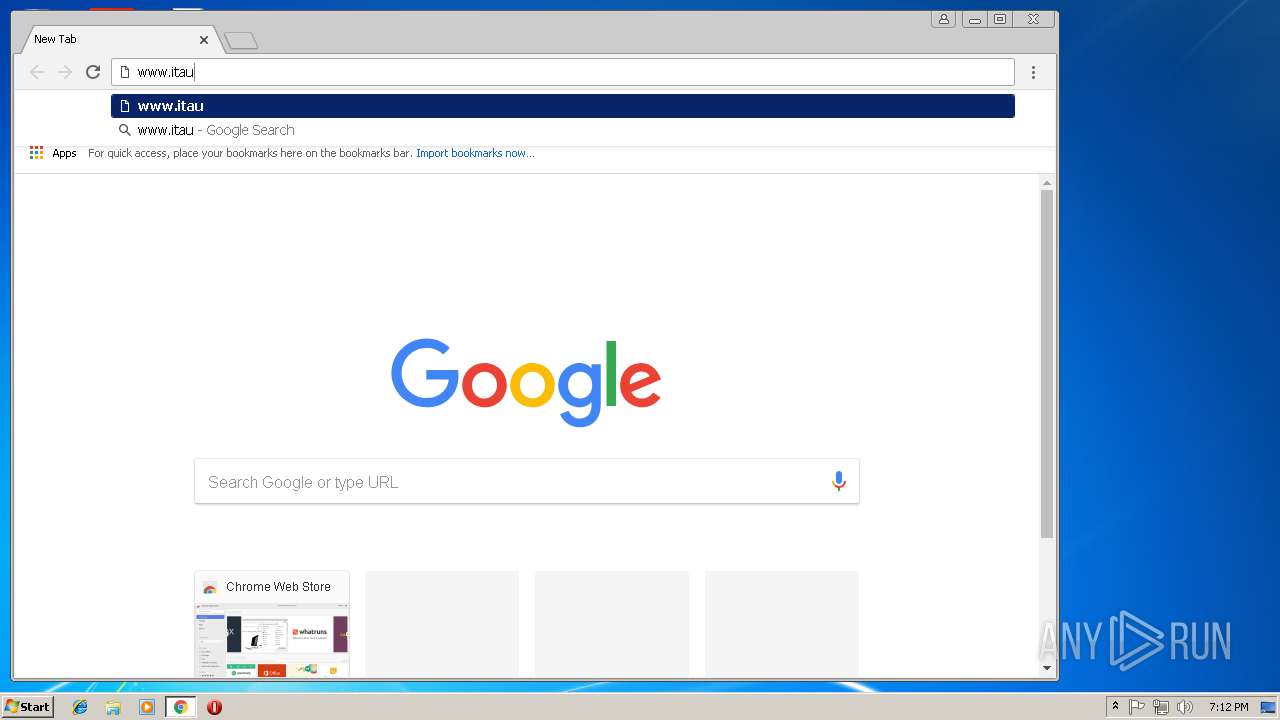
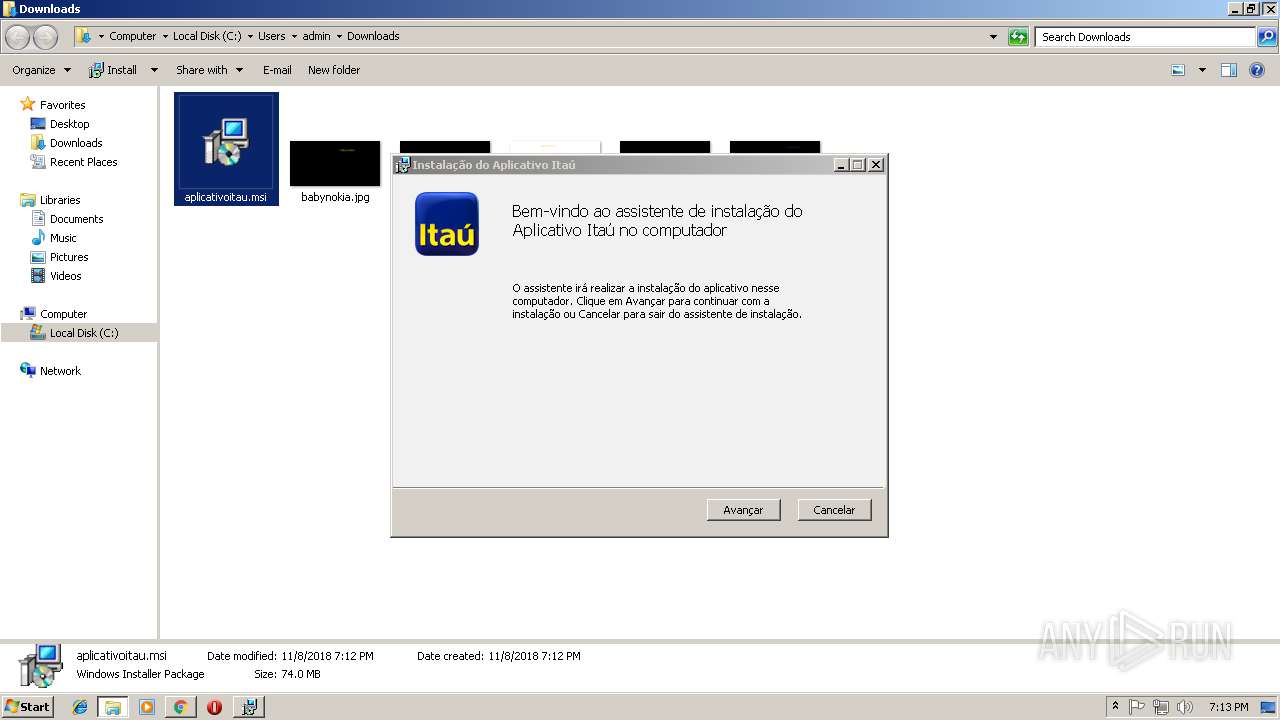
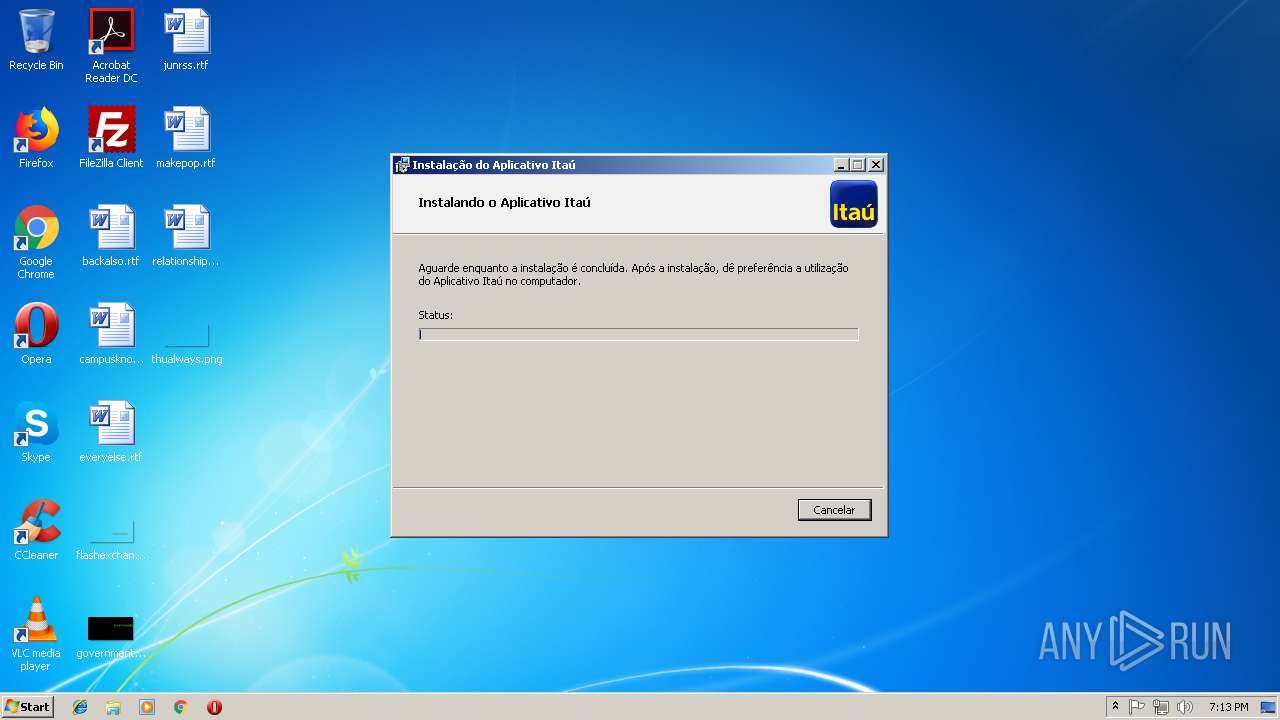
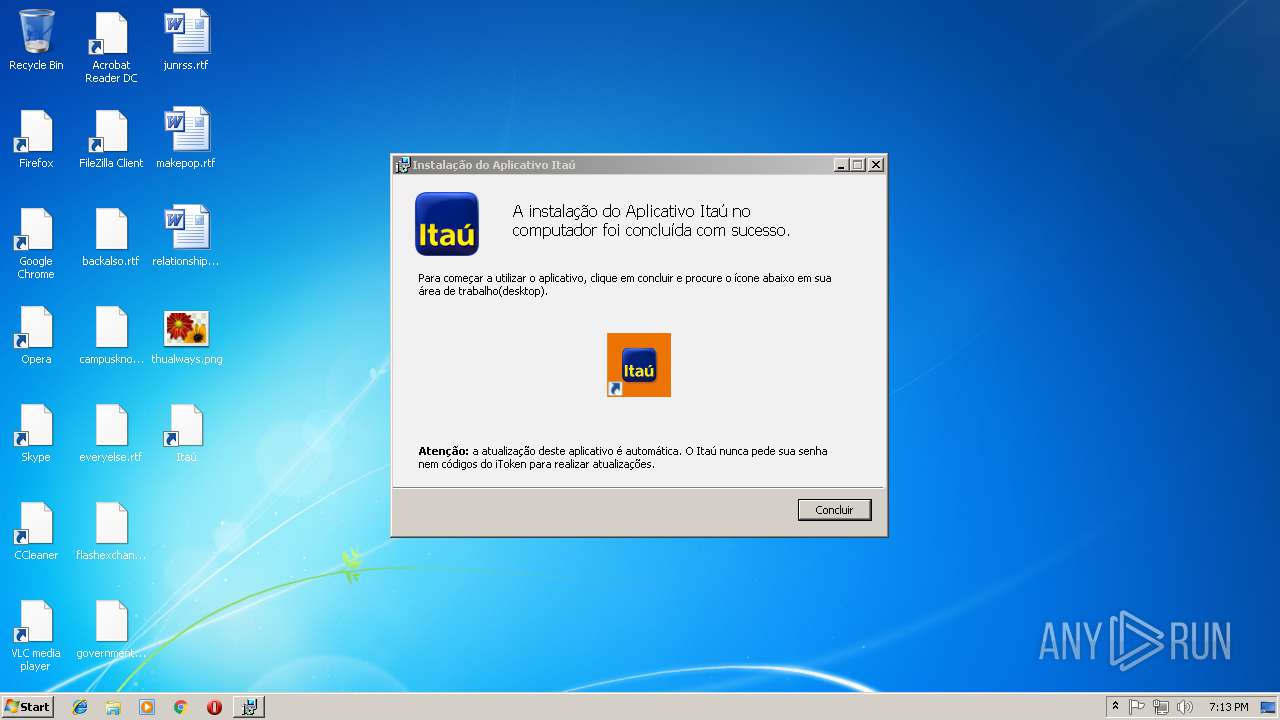
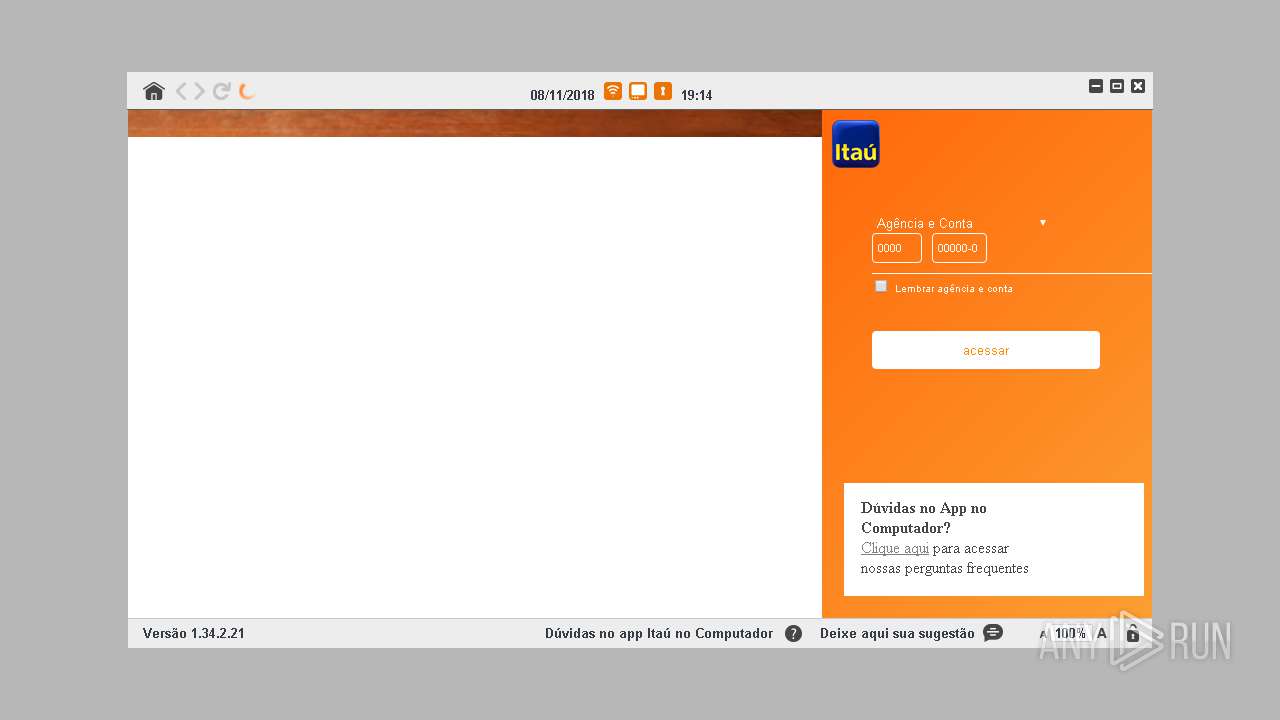
Loads dropped or rewritten executable
- itauaplicativo.exe (PID: 1088)
- itauaplicativo.exe (PID: 2304)
- itauaplicativo.exe (PID: 276)
- itauaplicativo.exe (PID: 3492)
- itauaplicativo.exe (PID: 1672)
- itauaplicativo.exe (PID: 3112)
Application was dropped or rewritten from another process
- itauaplicativo.exe (PID: 276)
- itauaplicativo.exe (PID: 2304)
- itauaplicativo.exe (PID: 3492)
- itauaplicativo.exe (PID: 1088)
- itauaplicativo.exe (PID: 3112)
- itauaplicativo.exe (PID: 1672)
SUSPICIOUS
Changes tracing settings of the file or console
- 9a52d1615be6f25a1ae7b93238cb8c70c27466ce73ed4f135c3e9695ac0ea502_visualizePend278609.bin.exe (PID: 4060)
Creates files in the user directory
- msIO5Xbiogs.exe (PID: 1824)
- 9a52d1615be6f25a1ae7b93238cb8c70c27466ce73ed4f135c3e9695ac0ea502_visualizePend278609.bin.exe (PID: 4060)
- msiexec.exe (PID: 3264)
Reads internet explorer settings
- 9a52d1615be6f25a1ae7b93238cb8c70c27466ce73ed4f135c3e9695ac0ea502_visualizePend278609.bin.exe (PID: 4060)
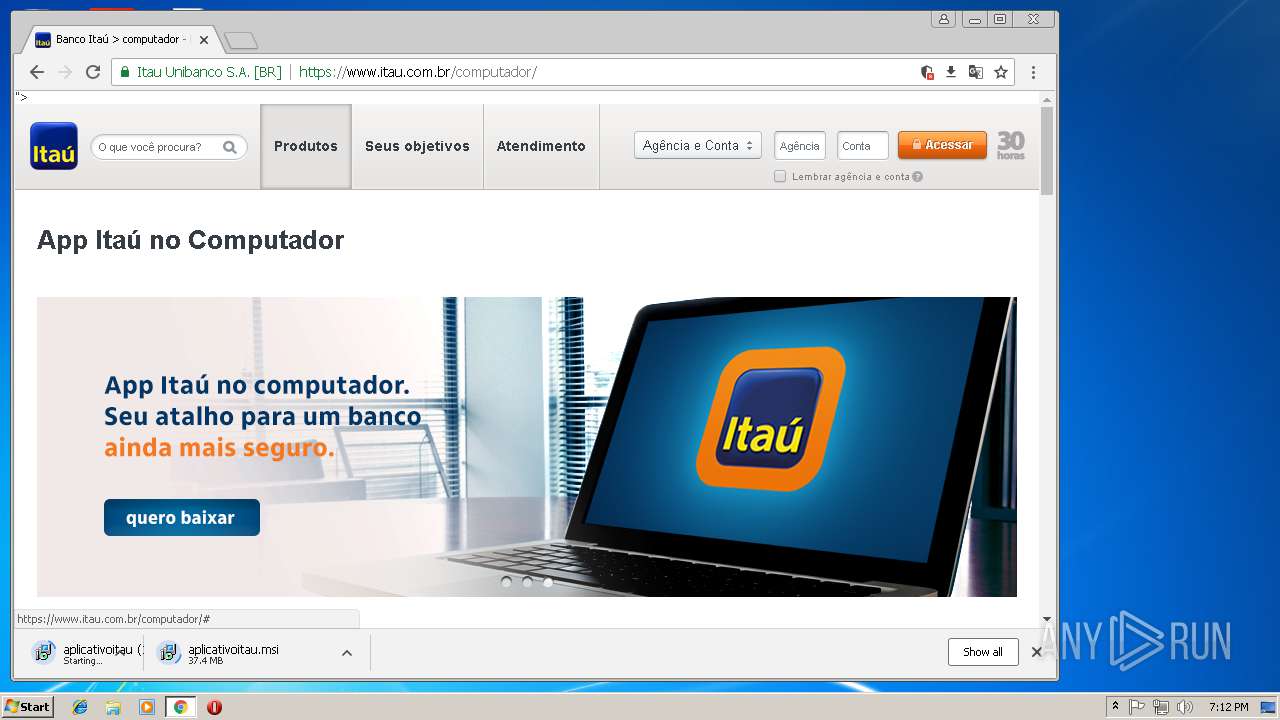
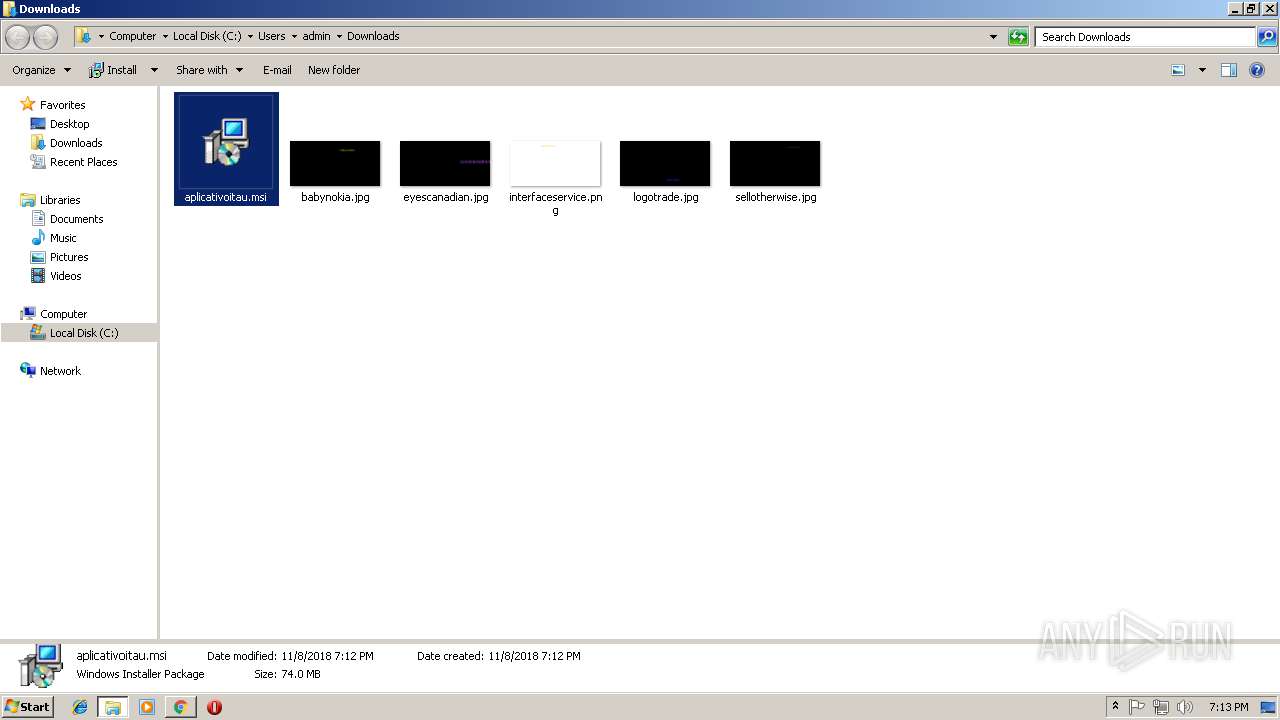
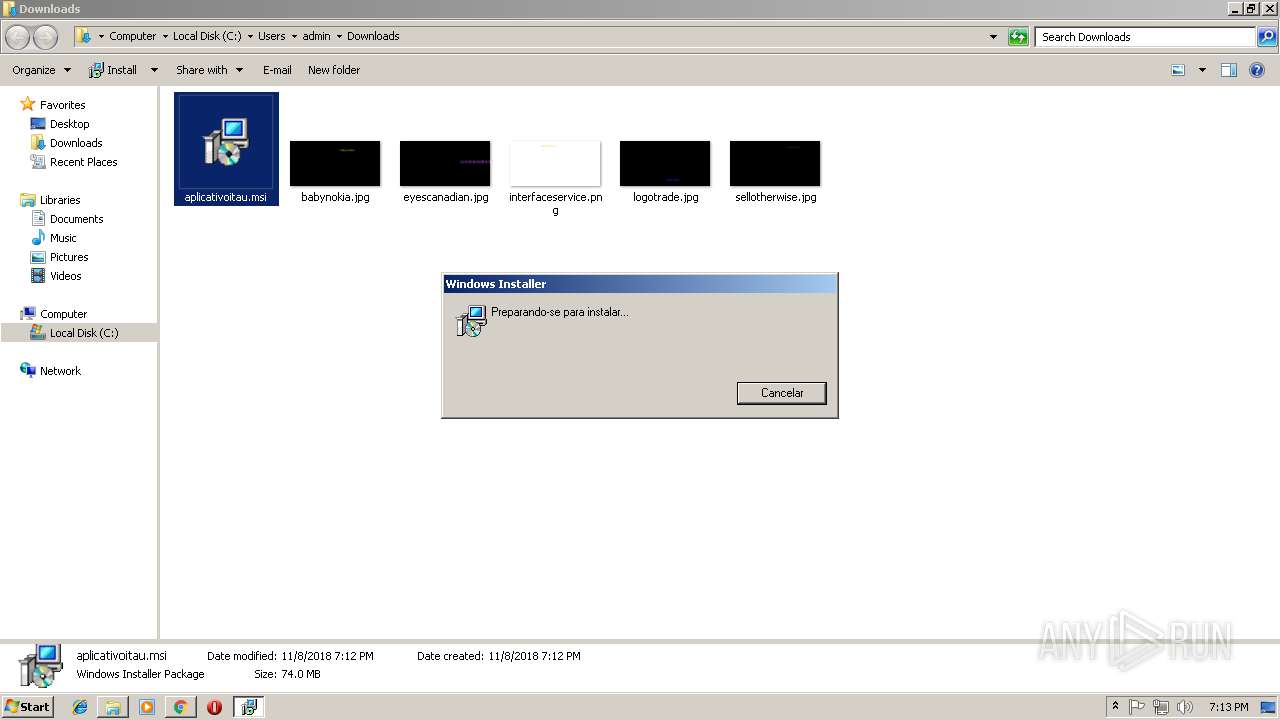
Executable content was dropped or overwritten
- msiexec.exe (PID: 3264)
Application launched itself
- itauaplicativo.exe (PID: 276)
- itauaplicativo.exe (PID: 2304)
Reads Internet Cache Settings
- msIO5Xbiogs.exe (PID: 1824)
Connects to unusual port
- msIO5Xbiogs.exe (PID: 1824)
INFO
Application launched itself
- chrome.exe (PID: 2624)
- chrome.exe (PID: 3156)
Reads settings of System Certificates
- chrome.exe (PID: 2624)
- chrome.exe (PID: 3156)
- itauaplicativo.exe (PID: 2304)
Reads Internet Cache Settings
- chrome.exe (PID: 2624)
Creates or modifies windows services
- msiexec.exe (PID: 3264)
- vssvc.exe (PID: 3684)
Creates files in the user directory
- chrome.exe (PID: 2624)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 3264)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3684)
Searches for installed software
- msiexec.exe (PID: 3264)
Creates a software uninstall entry
- msiexec.exe (PID: 3264)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (56.1) |
|---|---|---|
| .exe | | | Win32 Executable Borland Delphi 5 (38.1) |
| .exe | | | InstallShield setup (3.6) |
| .exe | | | Win32 Executable Delphi generic (1.1) |
| .exe | | | Win32 Executable (generic) (0.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 1970688 |
| InitializedDataSize: | 348672 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1e2074 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x001E1120 | 0x001E1200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.51532 |
DATA | 0x001E3000 | 0x0000D344 | 0x0000D400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.97414 |
BSS | 0x001F1000 | 0x0000321D | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x001F5000 | 0x00002CFC | 0x00002E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.87075 |
.tls | 0x001F8000 | 0x00000024 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x001F9000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.210826 |
.reloc | 0x001FA000 | 0x000157F0 | 0x00015800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.69045 |
.rsrc | 0x00210000 | 0x0002F600 | 0x0002F600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.20944 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.62916 | 1128 | UNKNOWN | Portuguese - Brazil | RT_ICON |
2 | 4.23483 | 4264 | UNKNOWN | Portuguese - Brazil | RT_ICON |
3 | 3.8155 | 9640 | UNKNOWN | Portuguese - Brazil | RT_ICON |
4 | 3.33133 | 67624 | UNKNOWN | Portuguese - Brazil | RT_ICON |
5 | 2.6949 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
6 | 2.62527 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
3682 | 2.04342 | 76 | UNKNOWN | UNKNOWN | RT_STRING |
3683 | 2.92331 | 170 | UNKNOWN | UNKNOWN | RT_STRING |
3684 | 3.47221 | 390 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
URLMON.DLL |
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
Total processes
78
Monitored processes
41
Malicious processes
4
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=864,355557849173385500,6814054076651989089,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=4EE3072C96B9581C82D52EA5C945C99B --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4EE3072C96B9581C82D52EA5C945C99B --renderer-client-id=8 --mojo-platform-channel-handle=2668 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=868,16618494220639714172,17863717396746753143,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=8598DC99532534C225DA7A8759D696C1 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8598DC99532534C225DA7A8759D696C1 --renderer-client-id=8 --mojo-platform-channel-handle=3968 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 276 | "C:\Users\admin\AppData\Local\Aplicativo Itau\itauaplicativo.exe" | C:\Users\admin\AppData\Local\Aplicativo Itau\itauaplicativo.exe | explorer.exe | ||||||||||||
User: admin Company: Banco Itaú Integrity Level: MEDIUM Description: Aplicativo Itaú Exit code: 0 Version: 1.34.2.21 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=864,355557849173385500,6814054076651989089,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=C050B9314C84745C62906EFEEF72A8E3 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=C050B9314C84745C62906EFEEF72A8E3 --renderer-client-id=11 --mojo-platform-channel-handle=1736 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=868,16618494220639714172,17863717396746753143,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=E162901BE15FCB38E55E787FF4E8826C --mojo-platform-channel-handle=5016 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=864,355557849173385500,6814054076651989089,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1AF40AA8CCE1F4F46FFCC2CFED7E0F59 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1AF40AA8CCE1F4F46FFCC2CFED7E0F59 --renderer-client-id=10 --mojo-platform-channel-handle=3856 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
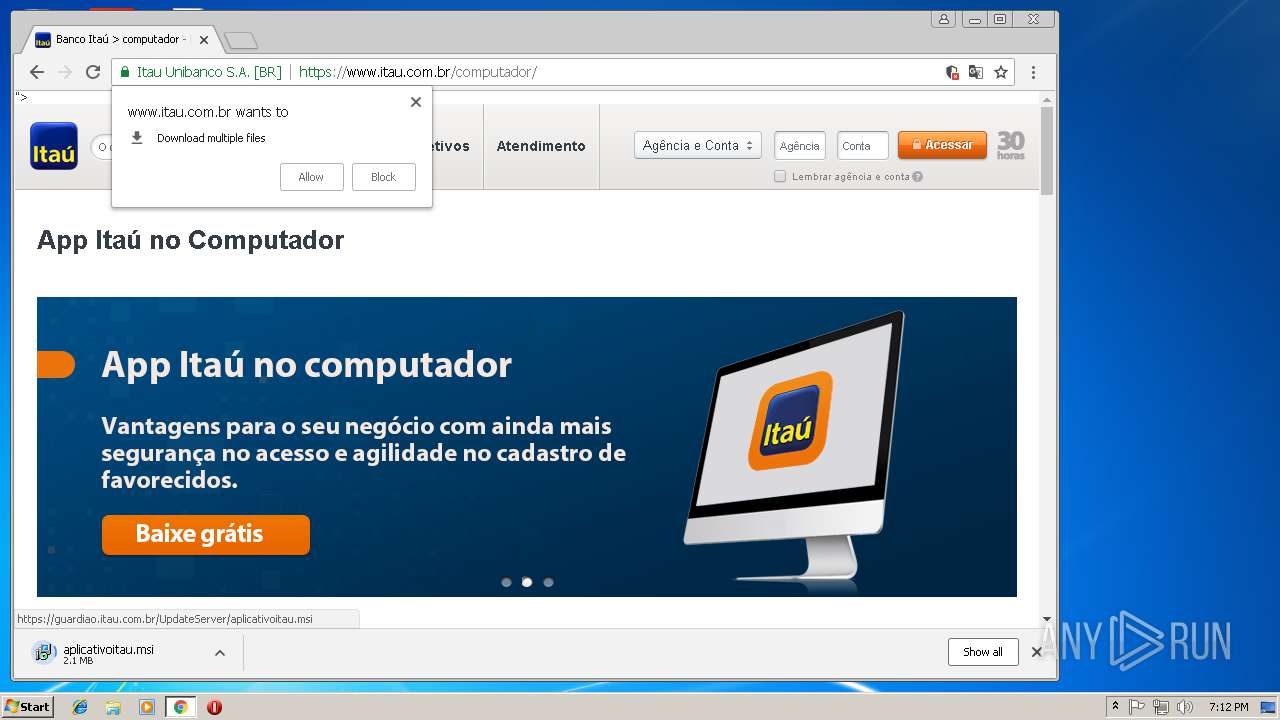
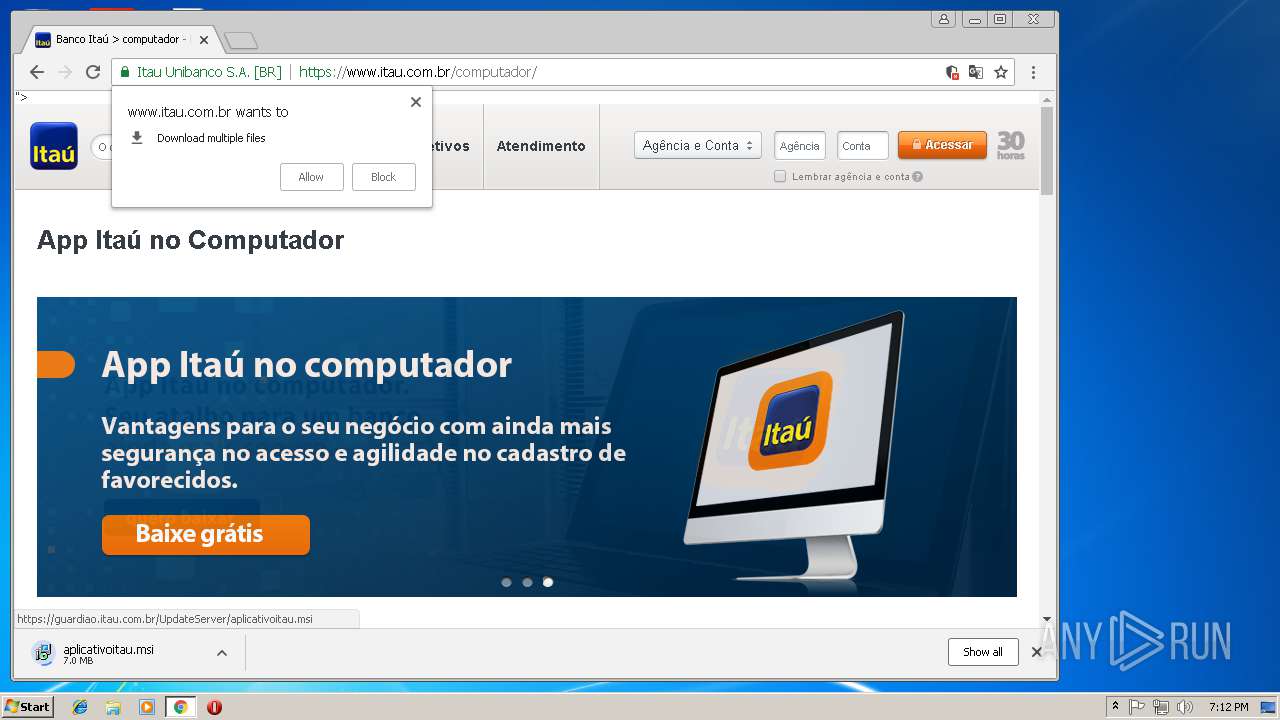
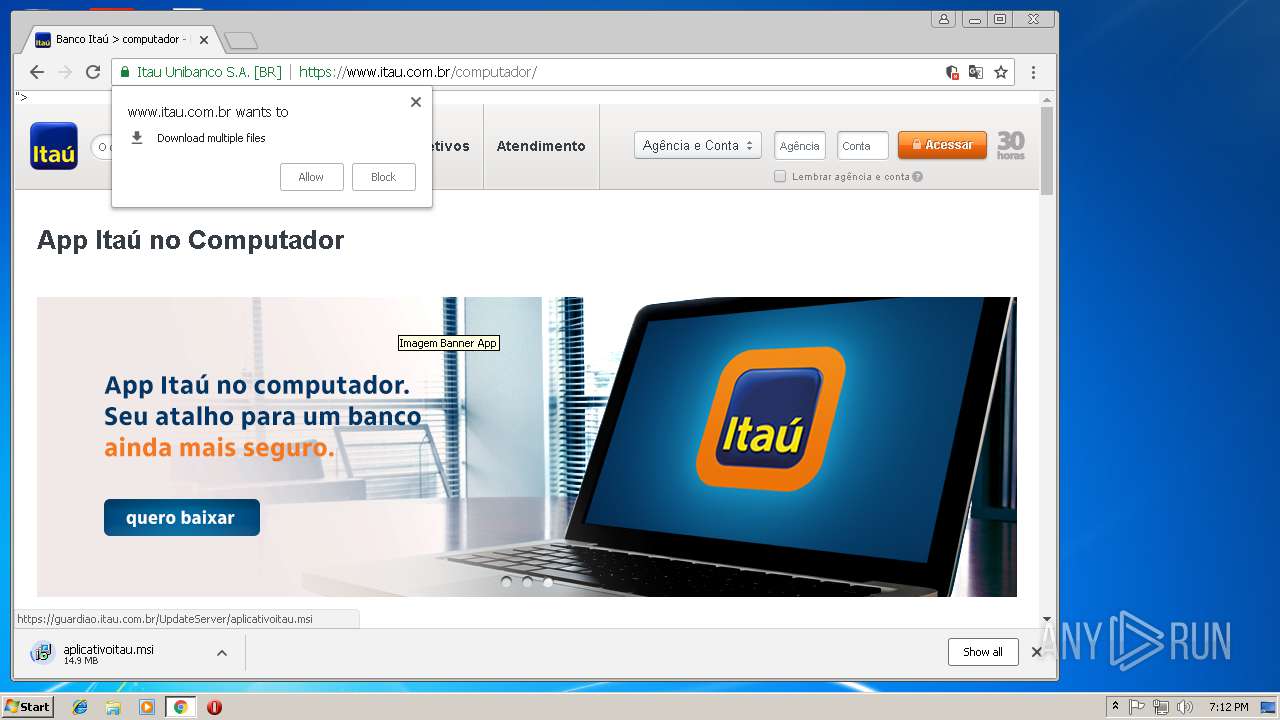
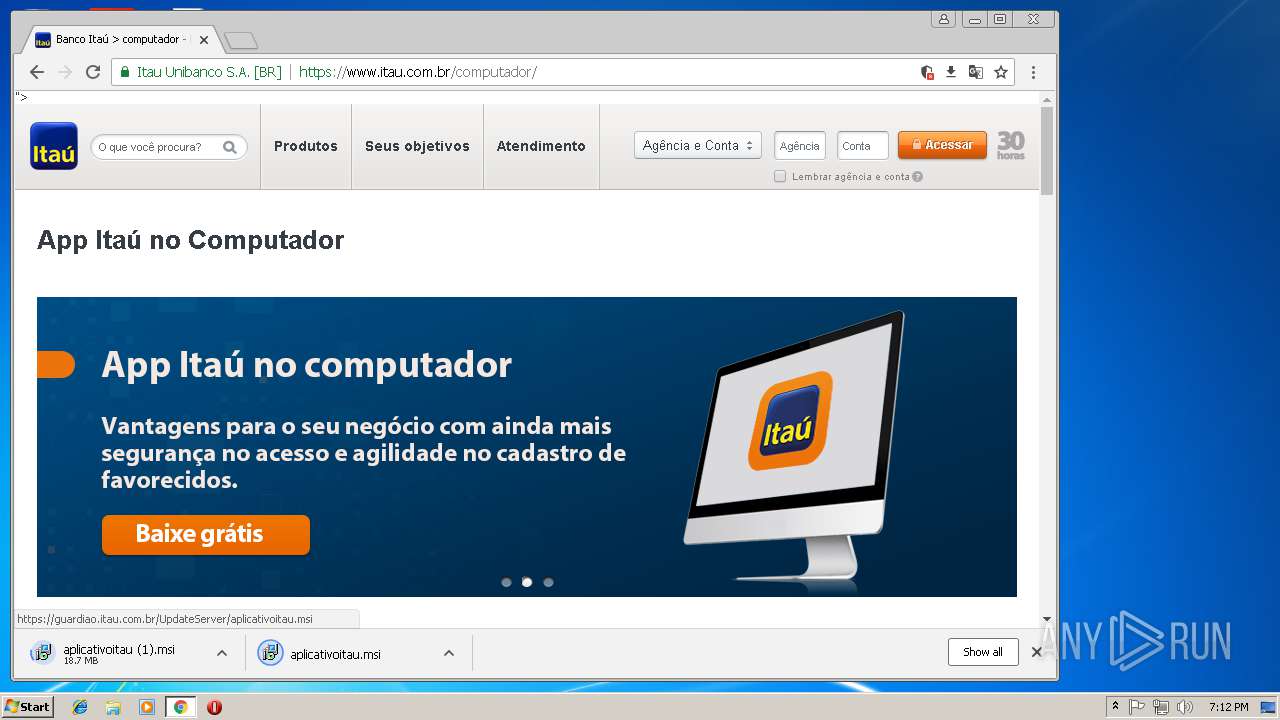
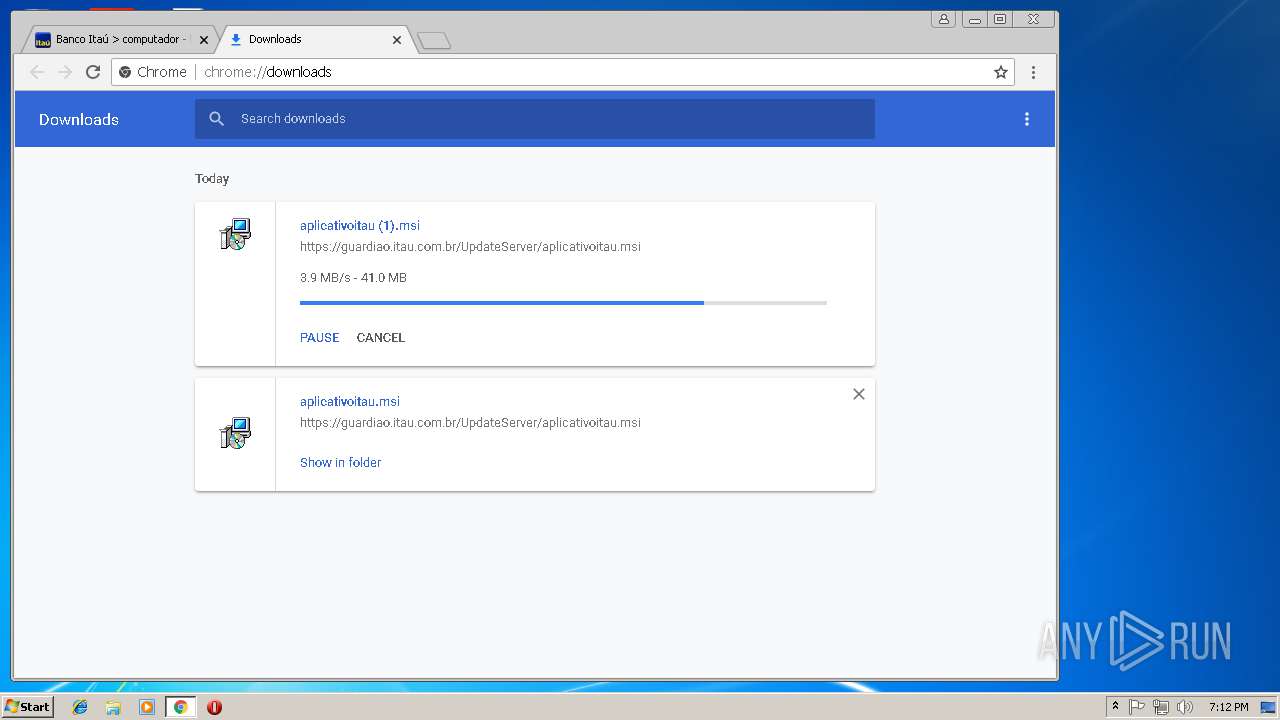
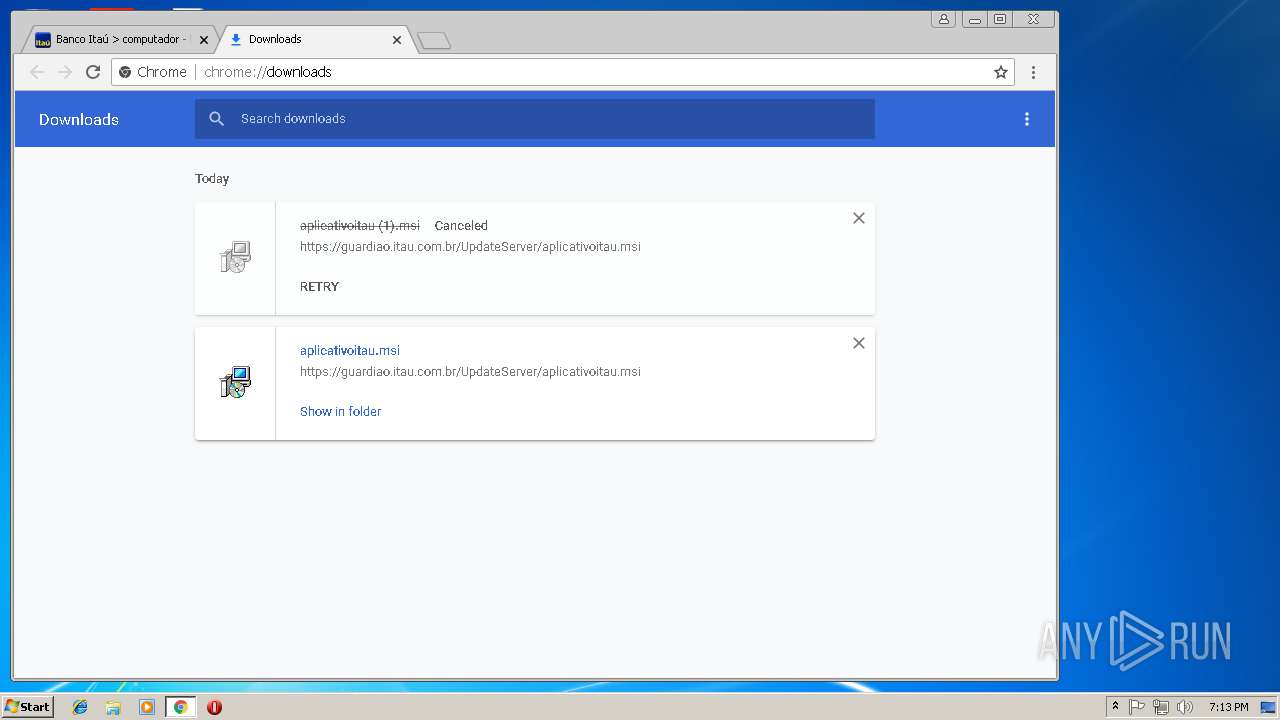
| 1016 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\Downloads\aplicativoitau.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1088 | "C:\Users\admin\AppData\Local\Aplicativo Itau\itauaplicativo.exe" --type=renderer --no-sandbox --disable-databases --primordial-pipe-token=89B5BDA178B847273A0AD15C617F28AB --lang=en-US --lang=pt-BR --log-file="C:\Users\admin\AppData\Local\Aplicativo Itau\debug.log" --log-severity=disable --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553 --disable-accelerated-video-decode --disable-webrtc-hw-vp8-encoding --disable-gpu-compositing --service-request-channel-token=89B5BDA178B847273A0AD15C617F28AB --renderer-client-id=2 --mojo-platform-channel-handle=1776 /prefetch:1 | C:\Users\admin\AppData\Local\Aplicativo Itau\itauaplicativo.exe | — | itauaplicativo.exe | |||||||||||
User: admin Company: Banco Itaú Integrity Level: MEDIUM Description: Aplicativo Itaú Exit code: 0 Version: 1.34.2.21 Modules
| |||||||||||||||
| 1460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=864,355557849173385500,6814054076651989089,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=6048F19DB7F9D2CFF1EF2A0165C9A5EE --mojo-platform-channel-handle=3724 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1672 | "C:\Users\admin\AppData\Local\Aplicativo Itau\itauaplicativo.exe" --type=gpu-process --no-sandbox --lang=pt-BR --log-file="C:\Users\admin\AppData\Local\Aplicativo Itau\debug.log" --log-severity=disable --disable-direct-composition --use-gl=swiftshader-webgl --supports-dual-gpus=false --gpu-driver-bug-workarounds=7,10,11,19,20,21,24,43,76 --disable-gl-extensions="GL_KHR_blend_equation_advanced GL_KHR_blend_equation_advanced_coherent" --disable-webrtc-hw-encoding --gpu-vendor-id=0x1234 --gpu-device-id=0x1111 --gpu-driver-vendor="Google Inc." --gpu-driver-version=3.3.0.2 --gpu-driver-date=2017/04/07 --lang=pt-BR --log-file="C:\Users\admin\AppData\Local\Aplicativo Itau\debug.log" --log-severity=disable --service-request-channel-token=34BD0AB25392DF5997C4CF3F58590244 --mojo-platform-channel-handle=2160 /prefetch:2 | C:\Users\admin\AppData\Local\Aplicativo Itau\itauaplicativo.exe | — | itauaplicativo.exe | |||||||||||
User: admin Company: Banco Itaú Integrity Level: MEDIUM Description: Aplicativo Itaú Exit code: 4 Version: 1.34.2.21 Modules
| |||||||||||||||
Total events
3 285
Read events
2 678
Write events
589
Delete events
18
Modification events
| (PID) Process: | (2624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2624-13186177939987625 |
Value: 259 | |||
| (PID) Process: | (2624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2624) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2624-13186177939987625 |
Value: 259 | |||
Executable files
19
Suspicious files
232
Text files
292
Unknown types
32
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4094828f-434f-4431-b283-4d27fe3ae8b2.tmp | — | |
MD5:— | SHA256:— | |||
| 2624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f996eb19-561c-4fa0-aa85-a4e0ac442c39.tmp | — | |
MD5:— | SHA256:— | |||
| 2624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF5dd27e.TMP | text | |
MD5:— | SHA256:— | |||
| 2624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\caecb3bd-7969-4305-84d6-3a376453ec73\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
| 2624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF5dd24f.TMP | text | |
MD5:— | SHA256:— | |||
| 2624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
109
DNS requests
57
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
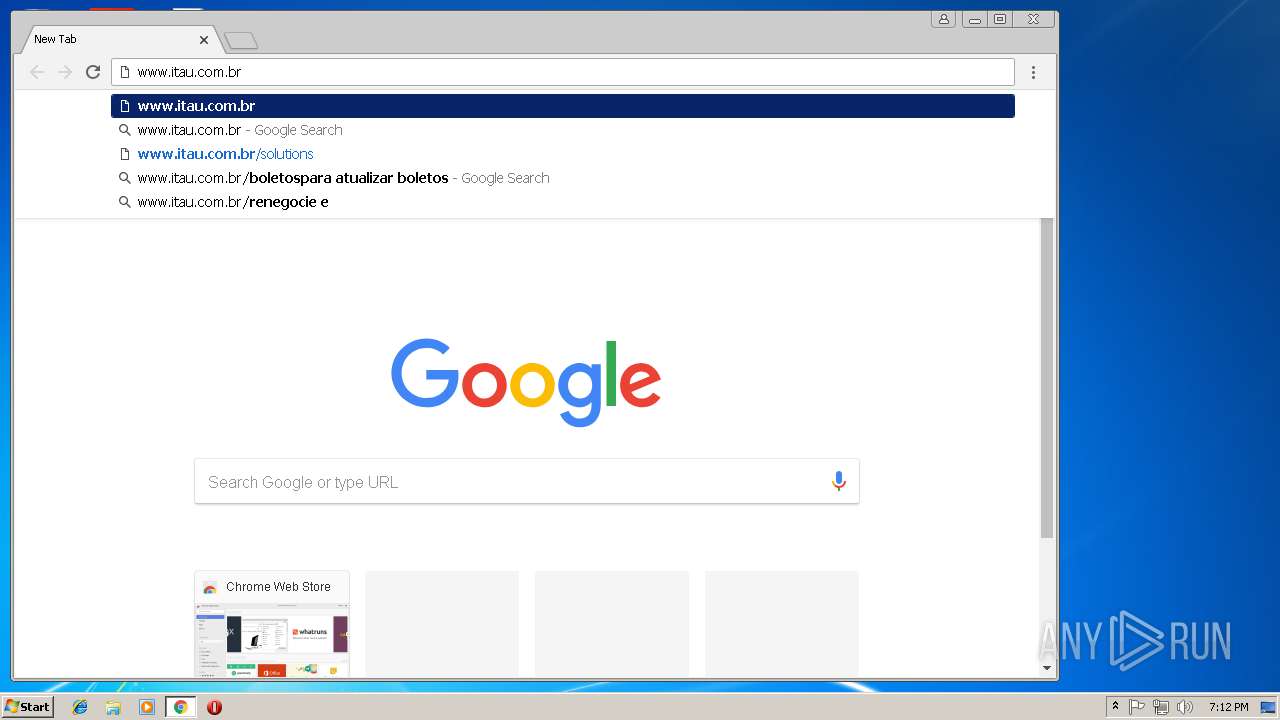
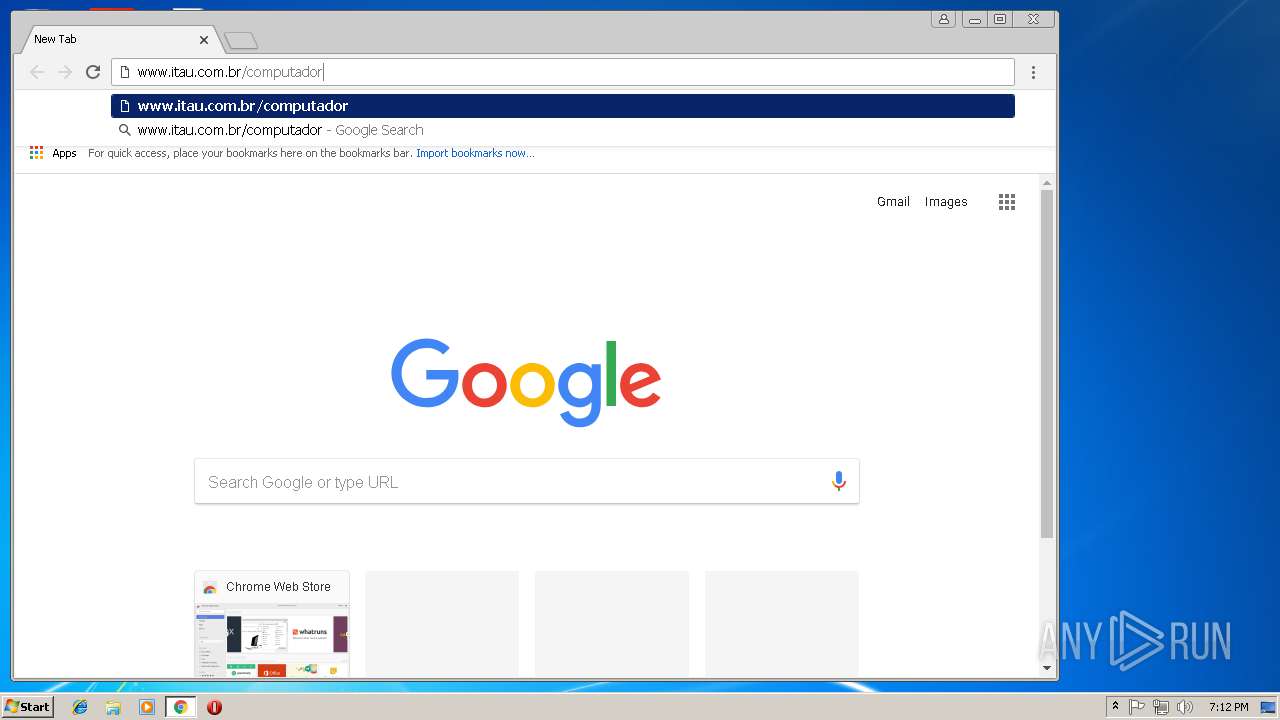
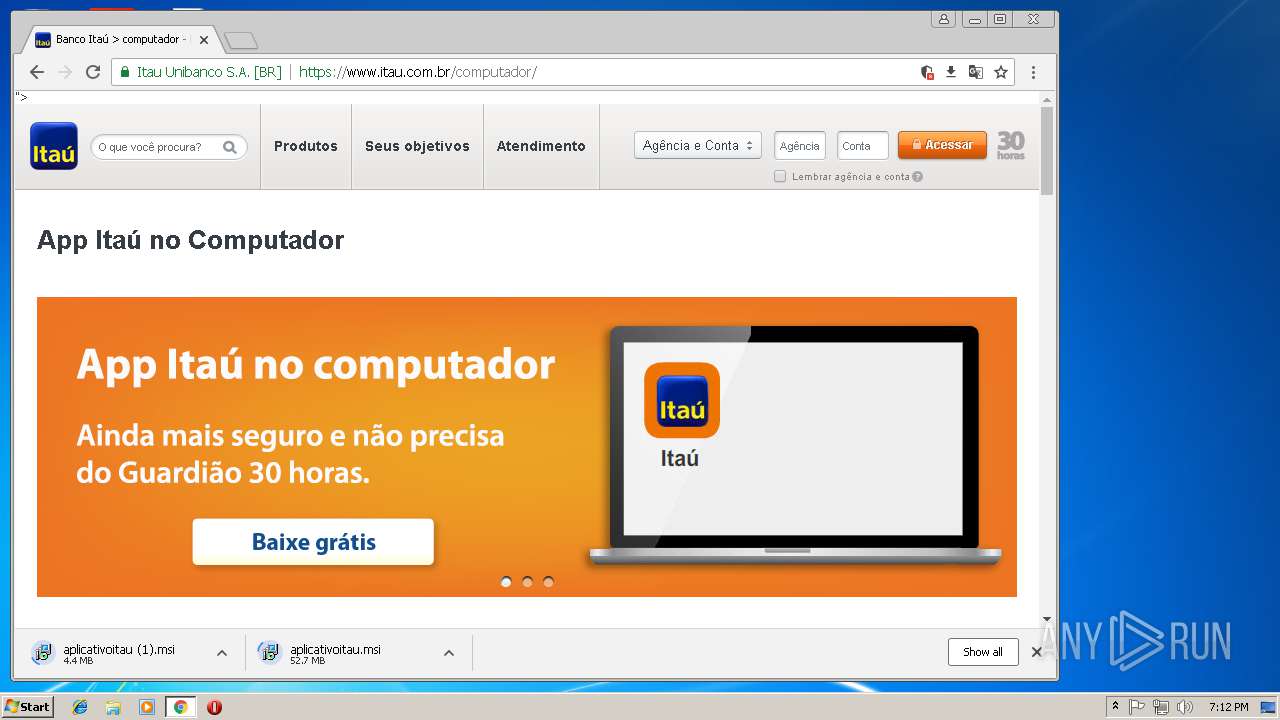
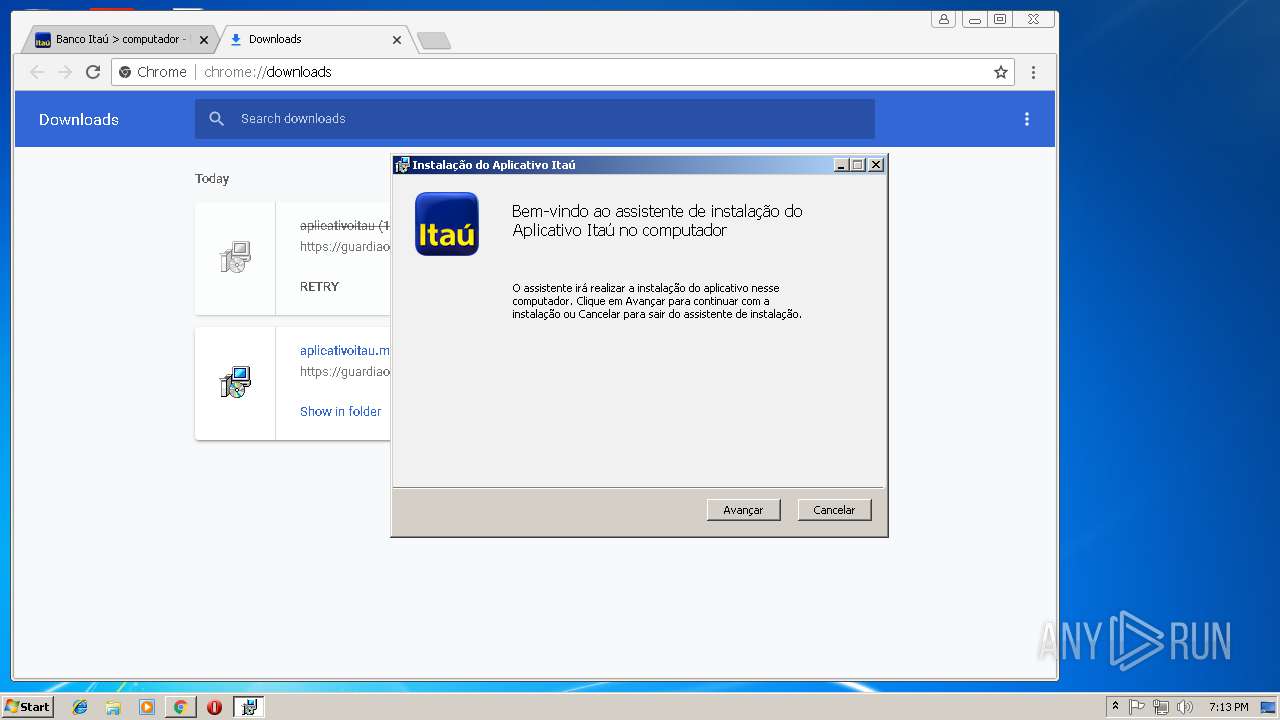
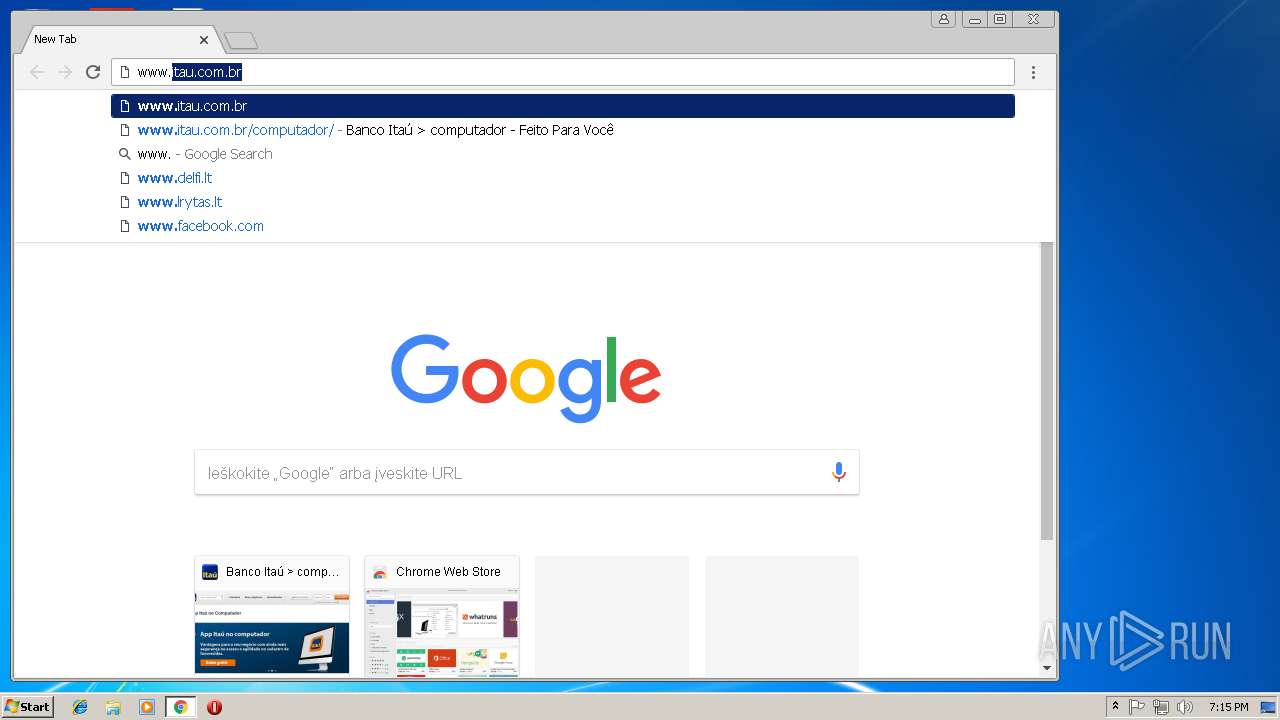
2624 | chrome.exe | GET | 301 | 2.18.233.32:80 | http://www.itau.com.br/computador/ | unknown | — | — | whitelisted |
4060 | 9a52d1615be6f25a1ae7b93238cb8c70c27466ce73ed4f135c3e9695ac0ea502_visualizePend278609.bin.exe | GET | 200 | 68.183.115.117:80 | http://68.183.115.117/Abi492Si0tons.zip | US | compressed | 9.84 Mb | malicious |
1824 | msIO5Xbiogs.exe | POST | 200 | 18.228.191.152:1077 | http://DNT4IU3H698OLSTO64VTEL0ERBOS.SERVEMINECRAFT.NET:1077/$rdgate?ACTION=HELLO | US | binary | 408 b | malicious |
1824 | msIO5Xbiogs.exe | POST | 200 | 18.228.191.152:1077 | http://DNT4IU3H698OLSTO64VTEL0ERBOS.SERVEMINECRAFT.NET:1077/$rdgate?ID=59A20FEC90F54ECCB280202D6A1AFC8C | US | binary | 14 b | malicious |
1824 | msIO5Xbiogs.exe | POST | 200 | 18.228.191.152:1077 | http://DNT4IU3H698OLSTO64VTEL0ERBOS.SERVEMINECRAFT.NET:1077/$rdgate?ID=59A20FEC90F54ECCB280202D6A1AFC8C | US | binary | 25 b | malicious |
1824 | msIO5Xbiogs.exe | POST | 200 | 18.228.191.152:1077 | http://DNT4IU3H698OLSTO64VTEL0ERBOS.SERVEMINECRAFT.NET:1077/$rdgate?ACTION=HELLO | US | binary | 412 b | malicious |
1824 | msIO5Xbiogs.exe | POST | 200 | 18.228.191.152:1077 | http://DNT4IU3H698OLSTO64VTEL0ERBOS.SERVEMINECRAFT.NET:1077/$rdgate?ID=4AEF376A1B71467CB7E02AACAC5852E4 | US | binary | 13 b | malicious |
1824 | msIO5Xbiogs.exe | POST | 200 | 18.228.191.152:1077 | http://DNT4IU3H698OLSTO64VTEL0ERBOS.SERVEMINECRAFT.NET:1077/$rdgate?ID=4AEF376A1B71467CB7E02AACAC5852E4 | US | binary | 12 b | malicious |
1824 | msIO5Xbiogs.exe | POST | — | 18.228.191.152:1077 | http://DNT4IU3H698OLSTO64VTEL0ERBOS.SERVEMINECRAFT.NET:1077/$rdgate?ID=4AEF376A1B71467CB7E02AACAC5852E4 | US | — | — | malicious |
1824 | msIO5Xbiogs.exe | POST | 200 | 18.228.191.152:1077 | http://DNT4IU3H698OLSTO64VTEL0ERBOS.SERVEMINECRAFT.NET:1077/$rdgate?ID=4AEF376A1B71467CB7E02AACAC5852E4 | US | binary | 12 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2624 | chrome.exe | 216.58.215.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2624 | chrome.exe | 172.217.168.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2624 | chrome.exe | 216.58.215.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2624 | chrome.exe | 172.217.168.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2624 | chrome.exe | 173.194.76.94:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2624 | chrome.exe | 108.177.15.94:443 | www.google.de | Google Inc. | US | whitelisted |
2624 | chrome.exe | 216.58.215.238:443 | apis.google.com | Google Inc. | US | whitelisted |
2624 | chrome.exe | 172.217.168.4:443 | www.google.com | Google Inc. | US | whitelisted |
2624 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4060 | 9a52d1615be6f25a1ae7b93238cb8c70c27466ce73ed4f135c3e9695ac0ea502_visualizePend278609.bin.exe | 68.183.115.117:80 | — | DSL Extreme | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.lt |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4060 | 9a52d1615be6f25a1ae7b93238cb8c70c27466ce73ed4f135c3e9695ac0ea502_visualizePend278609.bin.exe | A Network Trojan was detected | MALWARE [PTsecurity] Banload.WRI (Trojan.Agent.DDSA) Requesting Zip Archive |
1824 | msIO5Xbiogs.exe | A Network Trojan was detected | MALWARE [PTsecurity] LatentBot HTTP POST Checkin |
1824 | msIO5Xbiogs.exe | A Network Trojan was detected | MALWARE [PTsecurity] LatentBot HTTP POST Checkin |
3 ETPRO signatures available at the full report
Process | Message |
|---|---|
itauaplicativo.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |