| File name: | 392a5568f161d3fb30b5464643a773b0N.exe |
| Full analysis: | https://app.any.run/tasks/39dea105-f1db-4a62-a911-880d16fb97a0 |
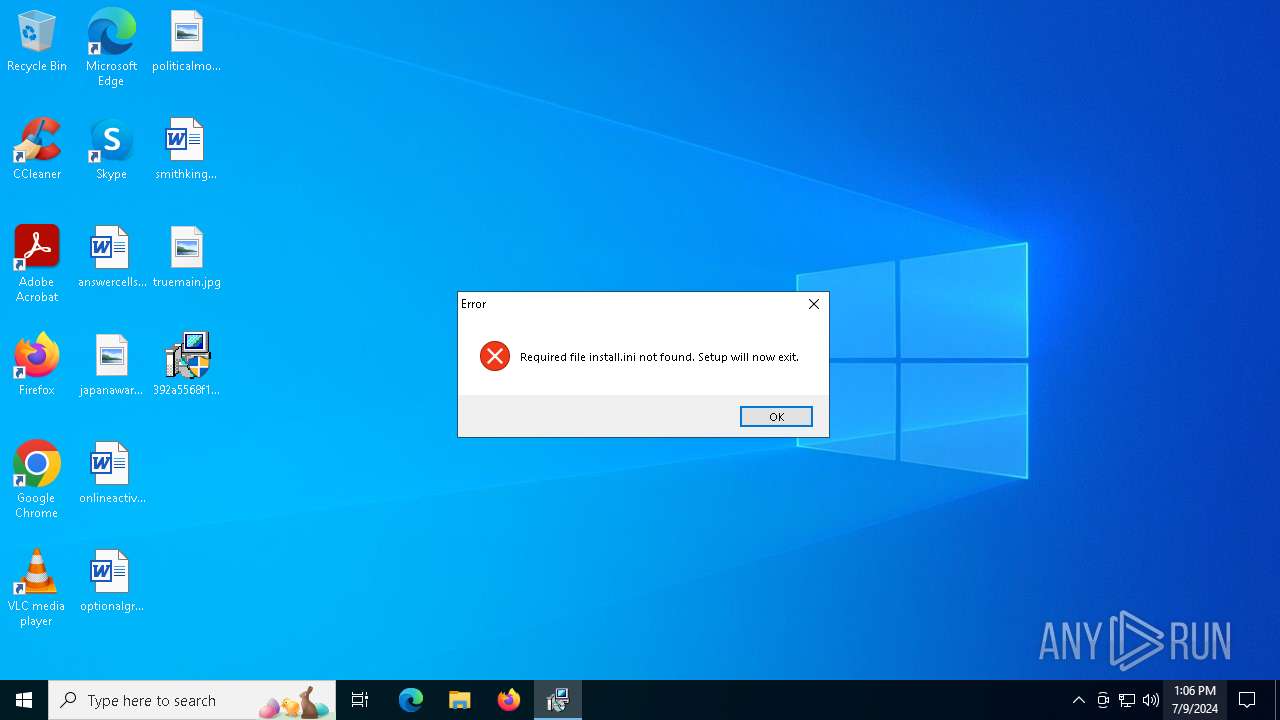
| Verdict: | Malicious activity |
| Threats: | DarkGate is a loader, which possesses extensive functionality, ranging from keylogging to crypto mining. Written in Delphi, this malware is known for the use of AutoIT scripts in its infection process. Thanks to this malicious software’s versatile architecture, it is widely used by established threat actors. |
| Analysis date: | July 09, 2024, 13:06:24 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 392A5568F161D3FB30B5464643A773B0 |
| SHA1: | 95BE597E56CE6CE4D2AD619A66073F1223D4B4EC |
| SHA256: | 9A4F855B34B4F0D020CD5263AB8E2793F4E751FD2CD724146D485F24538F9C36 |
| SSDEEP: | 49152:tSoB5z0kaMfLTLJCTOJSoBIDokd50iT4tf8/MDLdh22PjrE3+gChrGwWGoM9EoP+:10ELTLJCT7d50U4tfDLdh227XlYMWSQT |
MALICIOUS
Drops the executable file immediately after the start
- 392a5568f161d3fb30b5464643a773b0N.exe (PID: 5096)
Creates a writable file in the system directory
- FlashPlayerUpdateService.exe (PID: 836)
- alg.exe (PID: 3688)
M0YV has been detected (YARA)
- alg.exe (PID: 3688)
- DiagnosticsHub.StandardCollector.Service.exe (PID: 3780)
- elevation_service.exe (PID: 4800)
- elevation_service.exe (PID: 4240)
- PSEXESVC.exe (PID: 5988)
Connects to the CnC server
- 392a5568f161d3fb30b5464643a773b0N.exe (PID: 5096)
- alg.exe (PID: 3688)
Actions looks like stealing of personal data
- alg.exe (PID: 3688)
- DiagnosticsHub.StandardCollector.Service.exe (PID: 3780)
SUSPICIOUS
Starts a Microsoft application from unusual location
- 392a5568f161d3fb30b5464643a773b0N.exe (PID: 2808)
- 392a5568f161d3fb30b5464643a773b0N.exe (PID: 5096)
Process drops legitimate windows executable
- 392a5568f161d3fb30b5464643a773b0N.exe (PID: 5096)
- alg.exe (PID: 3688)
Executes as Windows Service
- armsvc.exe (PID: 3968)
- FlashPlayerUpdateService.exe (PID: 836)
- alg.exe (PID: 3688)
- AppVClient.exe (PID: 2044)
- DiagnosticsHub.StandardCollector.Service.exe (PID: 3780)
- GoogleUpdate.exe (PID: 2928)
- MicrosoftEdgeUpdate.exe (PID: 1708)
- PSEXESVC.exe (PID: 5988)
- maintenanceservice.exe (PID: 6064)
- MicrosoftEdgeUpdate.exe (PID: 6404)
- GoogleUpdate.exe (PID: 6824)
Executable content was dropped or overwritten
- 392a5568f161d3fb30b5464643a773b0N.exe (PID: 5096)
- alg.exe (PID: 3688)
Application launched itself
- MicrosoftEdgeUpdate.exe (PID: 1708)
- MicrosoftEdgeUpdate.exe (PID: 5224)
- GoogleUpdate.exe (PID: 2928)
- GoogleUpdate.exe (PID: 1856)
- MicrosoftEdgeUpdate.exe (PID: 6404)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 4856)
- MicrosoftEdgeUpdate.exe (PID: 5504)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2132)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 936)
Contacting a server suspected of hosting an CnC
- 392a5568f161d3fb30b5464643a773b0N.exe (PID: 5096)
- alg.exe (PID: 3688)
INFO
Checks supported languages
- 392a5568f161d3fb30b5464643a773b0N.exe (PID: 5096)
- armsvc.exe (PID: 3968)
- FlashPlayerUpdateService.exe (PID: 836)
- MicrosoftEdgeUpdate.exe (PID: 1708)
- MicrosoftEdgeUpdate.exe (PID: 5224)
- elevation_service.exe (PID: 4800)
- MicrosoftEdgeUpdate.exe (PID: 5504)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 4856)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 936)
- GoogleUpdate.exe (PID: 1856)
- MicrosoftEdgeUpdate.exe (PID: 2992)
- GoogleUpdate.exe (PID: 1956)
- GoogleCrashHandler.exe (PID: 5592)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2132)
- GoogleUpdate.exe (PID: 2928)
- GoogleUpdate.exe (PID: 4544)
- elevation_service.exe (PID: 4240)
- GoogleCrashHandler64.exe (PID: 4944)
- maintenanceservice.exe (PID: 6064)
- PSEXESVC.exe (PID: 5988)
- MicrosoftEdgeUpdate.exe (PID: 6404)
- MicrosoftEdgeUpdate.exe (PID: 6536)
- GoogleUpdate.exe (PID: 6824)
Reads the computer name
- 392a5568f161d3fb30b5464643a773b0N.exe (PID: 5096)
- armsvc.exe (PID: 3968)
- FlashPlayerUpdateService.exe (PID: 836)
- MicrosoftEdgeUpdate.exe (PID: 1708)
- MicrosoftEdgeUpdate.exe (PID: 5224)
- elevation_service.exe (PID: 4800)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 4856)
- MicrosoftEdgeUpdate.exe (PID: 5504)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 936)
- GoogleUpdate.exe (PID: 2928)
- MicrosoftEdgeUpdate.exe (PID: 2992)
- GoogleUpdate.exe (PID: 1856)
- GoogleUpdate.exe (PID: 1956)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2132)
- GoogleCrashHandler64.exe (PID: 4944)
- elevation_service.exe (PID: 4240)
- GoogleUpdate.exe (PID: 4544)
- maintenanceservice.exe (PID: 6064)
- PSEXESVC.exe (PID: 5988)
- GoogleCrashHandler.exe (PID: 5592)
- MicrosoftEdgeUpdate.exe (PID: 6404)
- MicrosoftEdgeUpdate.exe (PID: 6536)
- GoogleUpdate.exe (PID: 6824)
Creates files or folders in the user directory
- 392a5568f161d3fb30b5464643a773b0N.exe (PID: 5096)
- GoogleUpdate.exe (PID: 1956)
Checks proxy server information
- 392a5568f161d3fb30b5464643a773b0N.exe (PID: 5096)
Executes as Windows Service
- elevation_service.exe (PID: 4800)
- elevation_service.exe (PID: 4240)
Creates files in the program directory
- GoogleUpdate.exe (PID: 2928)
- GoogleUpdate.exe (PID: 1856)
- GoogleUpdate.exe (PID: 1956)
- GoogleUpdate.exe (PID: 4544)
- maintenanceservice.exe (PID: 6064)
- GoogleUpdate.exe (PID: 6824)
Reads Environment values
- MicrosoftEdgeUpdate.exe (PID: 6536)
Reads the software policy settings
- GoogleUpdate.exe (PID: 1956)
- MicrosoftEdgeUpdate.exe (PID: 6404)
- GoogleUpdate.exe (PID: 6824)
- MicrosoftEdgeUpdate.exe (PID: 6536)
Reads the machine GUID from the registry
- GoogleUpdate.exe (PID: 1956)
- GoogleUpdate.exe (PID: 6824)
Drops the executable file immediately after the start
- alg.exe (PID: 3688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (36.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (26.6) |
| .exe | | | Win64 Executable (generic) (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:11:07 07:43:31+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 501760 |
| InitializedDataSize: | 73216 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3dfd8 |
| OSVersion: | 5 |
| ImageVersion: | 9 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.0.21022.8 |
| ProductVersionNumber: | 9.0.21022.8 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | External Installer |
| FileVersion: | 9.0.21022.8 built by: RTM |
| InternalName: | Install.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | Install.exe |
| ProductName: | Microsoft® Visual Studio® 2008 |
| ProductVersion: | 9.0.21022.8 |
Total processes
149
Monitored processes
27
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 836 | C:\WINDOWS\SysWOW64\Macromed\Flash\FlashPlayerUpdateService.exe | C:\Windows\SysWOW64\Macromed\Flash\FlashPlayerUpdateService.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Adobe Integrity Level: SYSTEM Description: Adobe® Flash® Player Update Service 32.0 r0 Exit code: 0 Version: 32,0,0,465 Modules
| |||||||||||||||
| 936 | "C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.17\MicrosoftEdgeUpdateComRegisterShell64.exe" | C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.17\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.185.17 Modules
| |||||||||||||||
| 1708 | "C:\Program Files (x86)\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /svc | C:\Program Files (x86)\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.147.37 Modules
| |||||||||||||||
| 1856 | "C:\Program Files (x86)\Google\Update\GoogleUpdate.exe" /c | C:\Program Files (x86)\Google\Update\GoogleUpdate.exe | — | GoogleUpdate.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Installer Version: 1.3.36.51 Modules
| |||||||||||||||
| 1956 | "C:\Program Files (x86)\Google\Update\GoogleUpdate.exe" /cr | C:\Program Files (x86)\Google\Update\GoogleUpdate.exe | GoogleUpdate.exe | ||||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Installer Exit code: 0 Version: 1.3.36.51 Modules
| |||||||||||||||
| 2044 | C:\WINDOWS\system32\AppVClient.exe | C:\Windows\System32\AppVClient.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Application Virtualization Client Service Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2132 | "C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.17\MicrosoftEdgeUpdateComRegisterShell64.exe" | C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.17\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.185.17 Modules
| |||||||||||||||
| 2808 | "C:\Users\admin\Desktop\392a5568f161d3fb30b5464643a773b0N.exe" | C:\Users\admin\Desktop\392a5568f161d3fb30b5464643a773b0N.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: External Installer Exit code: 3221226540 Version: 9.0.21022.8 built by: RTM Modules
| |||||||||||||||
| 2928 | "C:\Program Files (x86)\Google\Update\GoogleUpdate.exe" /svc | C:\Program Files (x86)\Google\Update\GoogleUpdate.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Installer Exit code: 0 Version: 1.3.36.51 Modules
| |||||||||||||||
| 2992 | "C:\Program Files (x86)\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /ua /installsource core | C:\Program Files (x86)\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Edge Update Version: 1.3.147.37 Modules
| |||||||||||||||
Total events
23 778
Read events
19 270
Write events
4 443
Delete events
65
Modification events
| (PID) Process: | (3968) armsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Adobe\Adobe ARM\1.0\ARM |
| Operation: | write | Name: | iLastSvcSuccess |
Value: 1897062 | |||
| (PID) Process: | (1708) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\UsageStats\Daily\Integers |
| Operation: | write | Name: | omaha_version |
Value: 1100B90003000100 | |||
| (PID) Process: | (1708) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\UsageStats\Daily\Booleans |
| Operation: | write | Name: | is_system_install |
Value: 01000000 | |||
| (PID) Process: | (1708) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\UsageStats\Daily\Counts |
| Operation: | write | Name: | goopdate_main |
Value: 1500000000000000 | |||
| (PID) Process: | (1708) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\UsageStats\Daily\Counts |
| Operation: | write | Name: | goopdate_constructor |
Value: 1500000000000000 | |||
| (PID) Process: | (1708) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\UsageStats\Daily\Integers |
| Operation: | write | Name: | windows_major_version |
Value: 0A00000000000000 | |||
| (PID) Process: | (5224) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | InstallTime |
Value: | |||
| (PID) Process: | (5224) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientState\{F3017226-FE2A-4295-8BDF-00C3A9A7E4C5} |
| Operation: | write | Name: | InstallTime |
Value: | |||
| (PID) Process: | (5504) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{9E8F1B36-249F-4FC3-9994-974AFAA07B26}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (5504) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{A2F5CB38-265F-4A02-9D1E-F25B664968AB}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
Executable files
127
Suspicious files
2
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3688 | alg.exe | — | ||
MD5:— | SHA256:— | |||
| 3688 | alg.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\AcroCEF\SingleClientServicesUpdater.exe | — | |
MD5:— | SHA256:— | |||
| 5096 | 392a5568f161d3fb30b5464643a773b0N.exe | C:\WINDOWS\SysWOW64\Macromed\Flash\FlashPlayerUpdateService.exe | executable | |
MD5:0118C7AF5B003F595F8C3BB9223C9F0E | SHA256:70501DC1EB277C9857D9F727BFFB452720B8E2F0032CF28C11B0A75259C45A61 | |||
| 3688 | alg.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\SingleClientServicesUpdater.exe | — | |
MD5:— | SHA256:— | |||
| 5096 | 392a5568f161d3fb30b5464643a773b0N.exe | C:\WINDOWS\System32\alg.exe | executable | |
MD5:DA4A21264D8EF76D11B3CA2E72F2E2E0 | SHA256:0A48FB2EE6961D3553832F9095D61C28442D65FCA1F2AF1D932530E9E83C2F8C | |||
| 3688 | alg.exe | C:\WINDOWS\system32\config\systemprofile\AppData\Roaming\26b799fa89ba8c8f.bin | binary | |
MD5:E8CD78585895377A3C3C7CF51614629D | SHA256:EB59A58C71D3350BD96172134715EDC7974B8D421B55A129C52A7E4DB07EDDE7 | |||
| 5096 | 392a5568f161d3fb30b5464643a773b0N.exe | C:\Users\admin\AppData\Roaming\26b799fa89ba8c8f.bin | binary | |
MD5:350C0D58D737C2AA8F03D934EECD2C60 | SHA256:F4000952D2BAFE0E04A7FE50BC60528CAA526AF7C7E3EF0B0533161315A5BE35 | |||
| 5096 | 392a5568f161d3fb30b5464643a773b0N.exe | C:\WINDOWS\system32\AppVClient.exe | executable | |
MD5:9F80DC96B4E7140DC20DFD5FB9F52305 | SHA256:1BEB274E8BBA4A5BBF7230A0E3DB1DABAE2D8CA3CBFC95C7B92FE24D4C6B5493 | |||
| 5096 | 392a5568f161d3fb30b5464643a773b0N.exe | C:\WINDOWS\system32\DiagSvcs\DiagnosticsHub.StandardCollector.Service.exe | executable | |
MD5:65A4ED578DE7E54F897AD34A61CE536D | SHA256:8B76F751C424CAA4DC70402EA8B9FC8A204FB51D9D73B019FF8103D5A867BFD6 | |||
| 5096 | 392a5568f161d3fb30b5464643a773b0N.exe | C:\Program Files (x86)\Common Files\Adobe\ARM\1.0\armsvc.exe | executable | |
MD5:ECE9F7724B46B6FB503A157562AAF16B | SHA256:FA78561C5A03A4974D3240F820C7DF0A931912305FB989DBB2537DB4E9B5E30B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
34
DNS requests
23
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3688 | alg.exe | POST | 200 | 54.244.188.177:80 | http://pywolwnvd.biz/viclkgsn | unknown | — | — | unknown |
5096 | 392a5568f161d3fb30b5464643a773b0N.exe | POST | 302 | 54.244.188.177:80 | http://pywolwnvd.biz/oxyewwyqevp | unknown | — | — | unknown |
3688 | alg.exe | POST | 200 | 18.141.10.107:80 | http://ssbzmoy.biz/ifaaxiocnk | unknown | — | — | unknown |
2248 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
2248 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
3688 | alg.exe | POST | 200 | 44.221.84.105:80 | http://npukfztj.biz/vjdumyst | unknown | — | — | unknown |
3688 | alg.exe | POST | 200 | 54.244.188.177:80 | http://cvgrf.biz/kkb | unknown | — | — | unknown |
3688 | alg.exe | POST | — | 172.234.222.138:80 | http://przvgke.biz/cw | unknown | — | — | unknown |
— | — | POST | 200 | 142.250.185.163:443 | https://update.googleapis.com/service/update2?cup2key=13:hdb5Cd93Ot5CFL20Rt8Lbnv6jB185b7Vet4wXvraRT8&cup2hreq=c49667bfeba16209c4985afa63ed599b2f33920cd7daddcfaf0571e414b4413d | unknown | xml | 2.76 Kb | unknown |
— | — | GET | 200 | 13.107.42.16:443 | https://config.edge.skype.com/config/v1/EdgeUpdate/1.3.185.17?clientId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4 | unknown | binary | 219 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4820 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2248 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5096 | 392a5568f161d3fb30b5464643a773b0N.exe | 54.244.188.177:80 | pywolwnvd.biz | AMAZON-02 | US | unknown |
3688 | alg.exe | 54.244.188.177:80 | pywolwnvd.biz | AMAZON-02 | US | unknown |
2248 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
3688 | alg.exe | 18.141.10.107:80 | ssbzmoy.biz | AMAZON-02 | SG | unknown |
2248 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1956 | GoogleUpdate.exe | 142.250.185.110:443 | — | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pywolwnvd.biz |
| unknown |
crl.microsoft.com |
| whitelisted |
ssbzmoy.biz |
| unknown |
www.microsoft.com |
| whitelisted |
clients2.google.com |
| whitelisted |
cvgrf.biz |
| malicious |
settings-win.data.microsoft.com |
| whitelisted |
npukfztj.biz |
| unknown |
config.edge.skype.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3688 | alg.exe | A Network Trojan was detected | ET MALWARE Possible Compromised Host AnubisNetworks Sinkhole Cookie Value btst |
3688 | alg.exe | A Network Trojan was detected | ET MALWARE Possible Compromised Host AnubisNetworks Sinkhole Cookie Value Snkz |
3688 | alg.exe | A Network Trojan was detected | ET MALWARE Possible Compromised Host AnubisNetworks Sinkhole Cookie Value Snkz |
3688 | alg.exe | A Network Trojan was detected | ET MALWARE Possible Compromised Host AnubisNetworks Sinkhole Cookie Value btst |
3688 | alg.exe | A Network Trojan was detected | ET MALWARE Possible Compromised Host AnubisNetworks Sinkhole Cookie Value Snkz |
3688 | alg.exe | A Network Trojan was detected | ET MALWARE Possible Compromised Host AnubisNetworks Sinkhole Cookie Value btst |
2168 | svchost.exe | A Network Trojan was detected | ET MALWARE DNS Query to DarkGate/Expiro Related Domain (knjghuig .biz) |
3 ETPRO signatures available at the full report
Process | Message |
|---|---|
MicrosoftEdgeUpdate.exe | LOG_SYSTEM: [MicrosoftEdgeUpdate:msedgeupdate]: Could not acquire logging mutex _Microsoft_EdgeUpdate_logging_mutex_C:ProgramDataMicrosoftEdgeUpdateLogMicrosoftEdgeUpdate.log
|