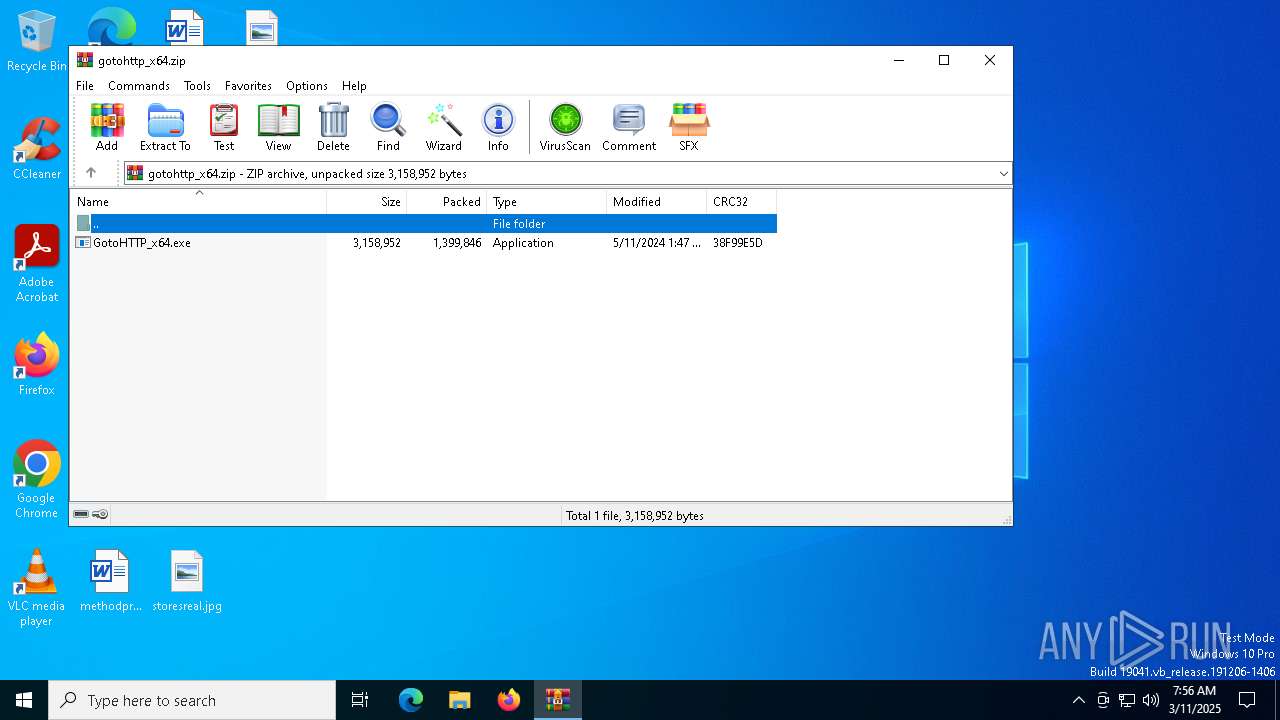
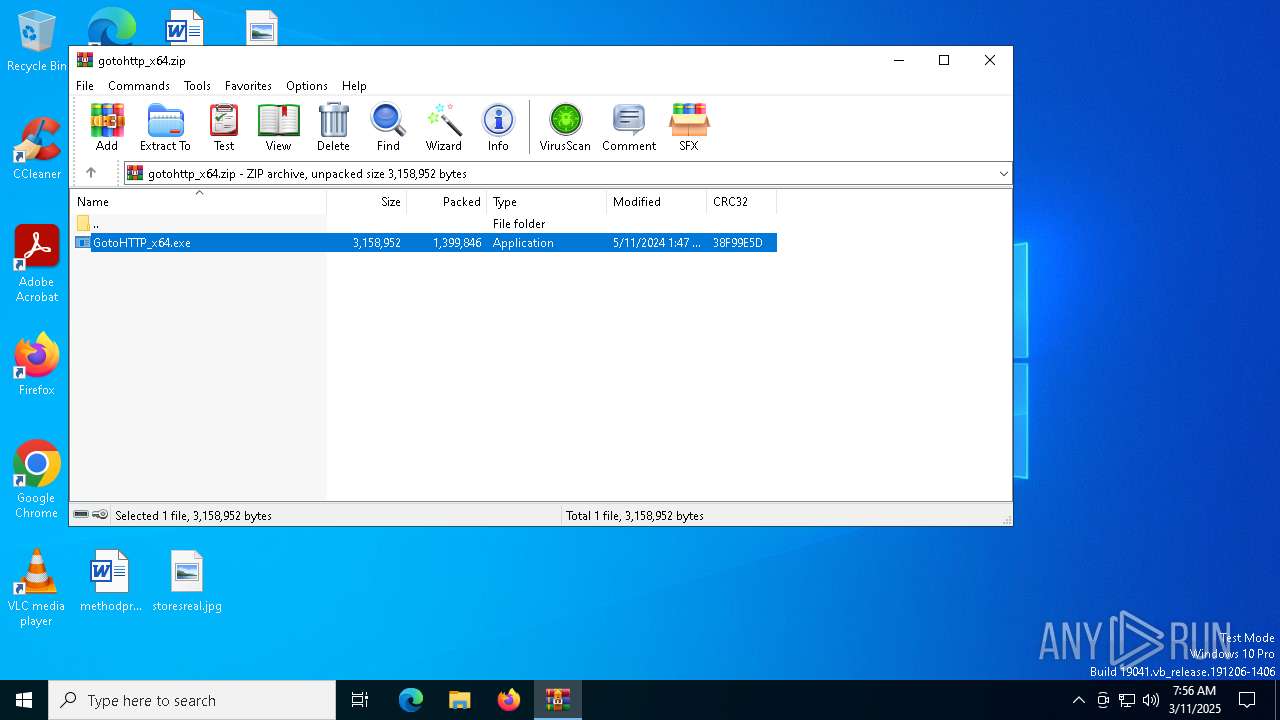
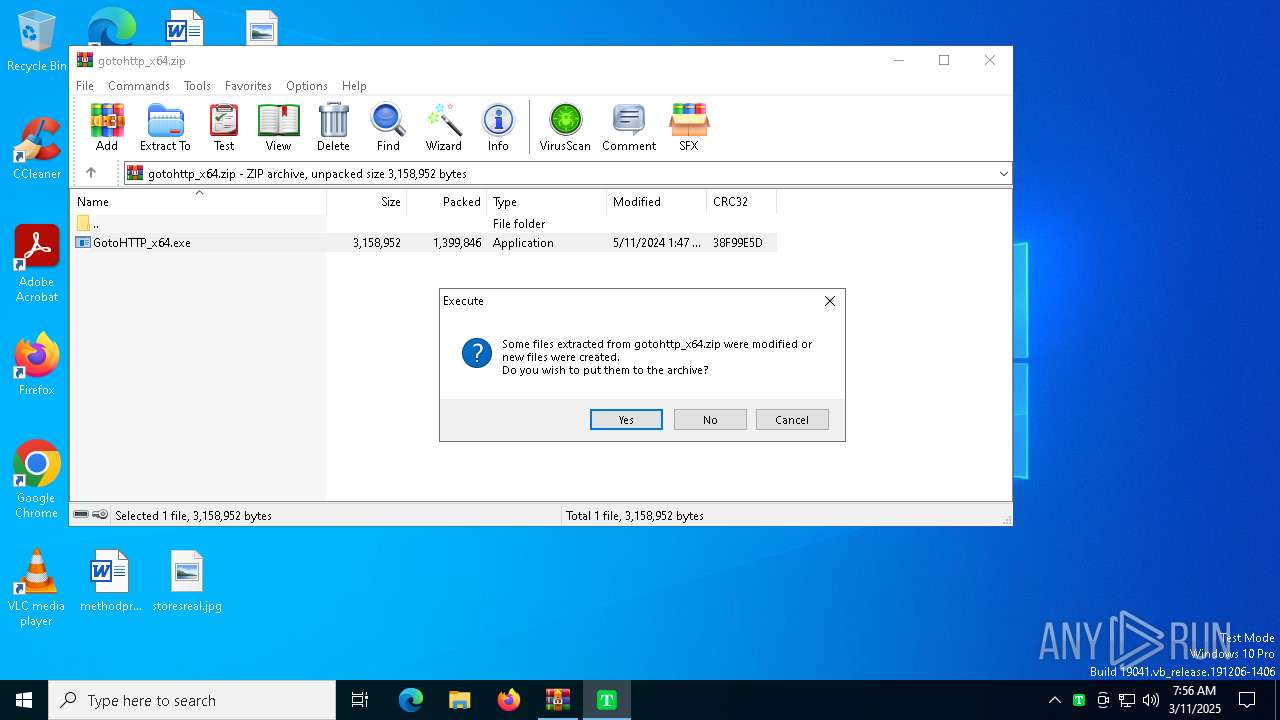
| File name: | gotohttp_x64.zip |
| Full analysis: | https://app.any.run/tasks/eee97a92-3af5-4e13-b652-d397c39cee0f |
| Verdict: | Malicious activity |
| Analysis date: | March 11, 2025, 07:56:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 7607B44FDB7027722320AF54CA3E5C74 |
| SHA1: | 92150E37AFCDA5F226C138FD269AF8FE7E7A6F09 |
| SHA256: | 9A4C2813A879CFABAD5047B69C4261075BF74943825CE181A93B07F1B8E66A0B |
| SSDEEP: | 49152:qxBdW9pRWugOFCF9/Ul55pQNjgXRZLDmUD8+mNRw2MElWNr+9Zr6zqHsg17KzXnf:qxBQ9p8uMvCGgXRZLqUlhrfNr+9JOWMv |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7388)
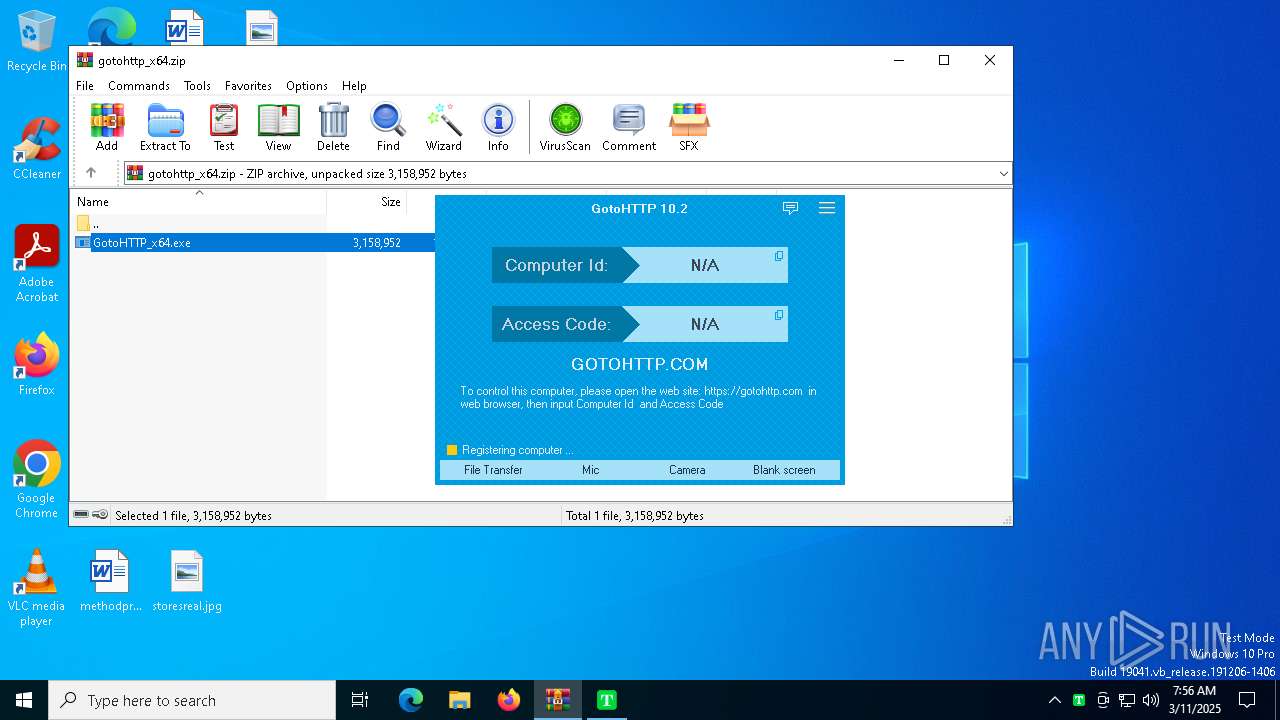
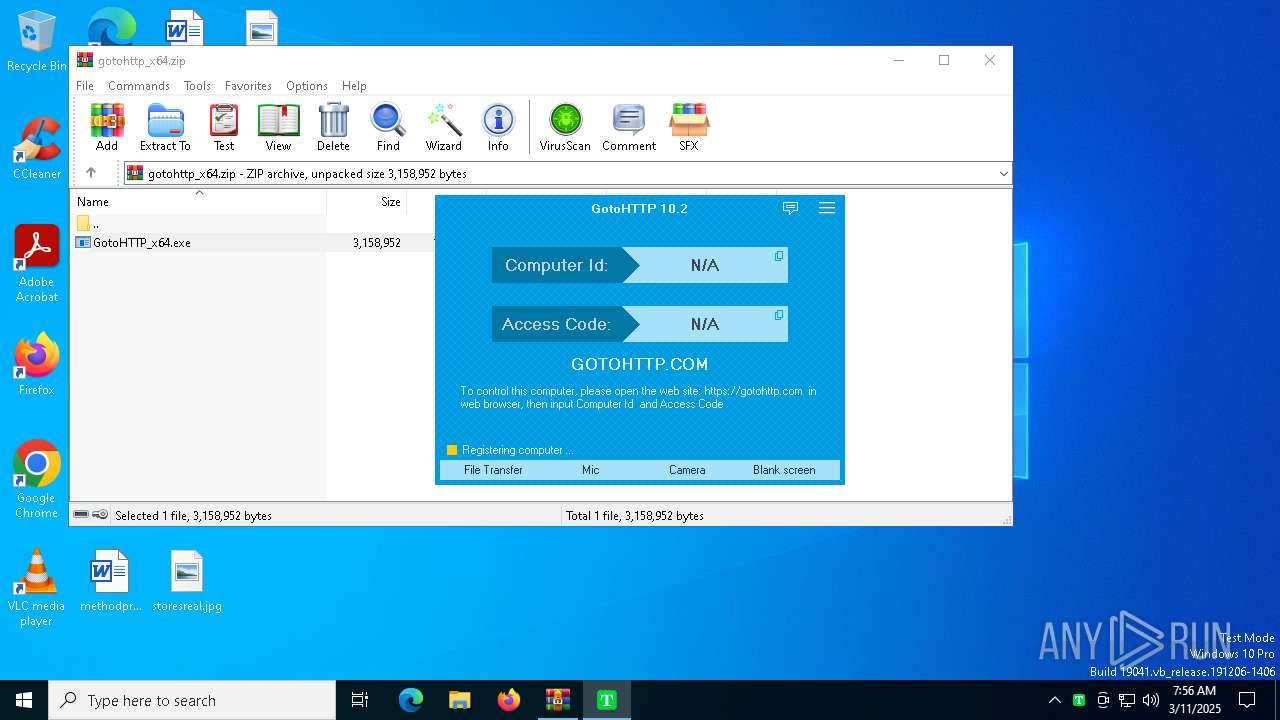
GOTOHTTP has been found
- GotoHTTP_x64.exe (PID: 4560)
- GotoHTTP_x64.exe (PID: 744)
- GotoHTTP_x64.exe (PID: 7272)
GOTOHTTP mutex has been found
- GotoHTTP_x64.exe (PID: 7272)
- GotoHTTP_x64.exe (PID: 744)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7388)
Executes as Windows Service
- GotoHTTP_x64.exe (PID: 744)
Application launched itself
- GotoHTTP_x64.exe (PID: 744)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7388)
The sample compiled with english language support
- WinRAR.exe (PID: 7388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:05:11 09:47:24 |
| ZipCRC: | 0x38f99e5d |
| ZipCompressedSize: | 1399846 |
| ZipUncompressedSize: | 3158952 |
| ZipFileName: | GotoHTTP_x64.exe |
Total processes
139
Monitored processes
7
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 744 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7388.8745\GotoHTTP_x64.exe" service | C:\Users\admin\AppData\Local\Temp\Rar$EXa7388.8745\GotoHTTP_x64.exe | services.exe | ||||||||||||
User: SYSTEM Company: Pingbo Inc Integrity Level: SYSTEM Description: GotoHTTP Version: 10.2.0.1925 Modules
| |||||||||||||||
| 4560 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7388.8745\GotoHTTP_x64.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7388.8745\GotoHTTP_x64.exe | WinRAR.exe | ||||||||||||
User: admin Company: Pingbo Inc Integrity Level: HIGH Description: GotoHTTP Exit code: 0 Version: 10.2.0.1925 Modules
| |||||||||||||||
| 7208 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7388.8745\GotoHTTP_x64.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa7388.8745\GotoHTTP_x64.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Pingbo Inc Integrity Level: MEDIUM Description: GotoHTTP Exit code: 3221226540 Version: 10.2.0.1925 Modules
| |||||||||||||||
| 7272 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa7388.8745\GotoHTTP_x64.exe" Global\GotoHTTP_5 | C:\Users\admin\AppData\Local\Temp\Rar$EXa7388.8745\GotoHTTP_x64.exe | GotoHTTP_x64.exe | ||||||||||||
User: SYSTEM Company: Pingbo Inc Integrity Level: SYSTEM Description: GotoHTTP Version: 10.2.0.1925 Modules
| |||||||||||||||
| 7388 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\gotohttp_x64.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7540 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7572 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 264
Read events
2 255
Write events
9
Delete events
0
Modification events
| (PID) Process: | (7388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\gotohttp_x64.zip | |||
| (PID) Process: | (7388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7388) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4560) GotoHTTP_x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | SoftwareSASGeneration |
Value: 1 | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7388 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7388.8745\GotoHTTP_x64.exe | executable | |
MD5:F4EA4E9B8017B5EDD392B7416BD390AF | SHA256:230B84398E873938BBCC7E4A1A358BDE4345385D58EB45C1726CEE22028026E9 | |||
| 7272 | GotoHTTP_x64.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa7388.8745\gotohttp.ini | text | |
MD5:A3768258DA60810C8E37BAD9FF62843A | SHA256:77F78CD08D2852051E3DE8E836297E86E40CB1E92DD22894D0CA1C1F1F714E95 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
28
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7316 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7316 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7924 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7272 | GotoHTTP_x64.exe | 43.153.10.125:443 | def.gotohttp.com | Tencent Building, Kejizhongyi Avenue | US | suspicious |
7272 | GotoHTTP_x64.exe | 43.153.10.125:80 | def.gotohttp.com | Tencent Building, Kejizhongyi Avenue | US | suspicious |
7272 | GotoHTTP_x64.exe | 47.252.31.236:80 | use.gotohttp.com | Alibaba US Technology Co., Ltd. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
def.gotohttp.com |
| unknown |
usw.gotohttp.com |
| unknown |
use.gotohttp.com |
| unknown |
hk.gotohttp.com |
| unknown |
arc.msn.com |
| whitelisted |