| File name: | b4a51418a774a766137e7fa75a0ce6ab.exe |
| Full analysis: | https://app.any.run/tasks/6bd7204f-0ae7-45eb-9521-18281e75a28e |
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | April 01, 2023, 04:52:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B4A51418A774A766137E7FA75A0CE6AB |
| SHA1: | 346AA7732D0E56614289D4B46DDB2D699FCE0DEC |
| SHA256: | 9A341AD8B4BEC65E5426D01D02776A351C3834F4BEC8B2E7697CE70BADDFEBCD |
| SSDEEP: | 24576:O2G/nvxW3Ww0tGjiRdpVWXhSsxcwUPkffThANFkY/uoHMqo:ObA30GedpV4SsxzUszhwLGoHMJ |
MALICIOUS
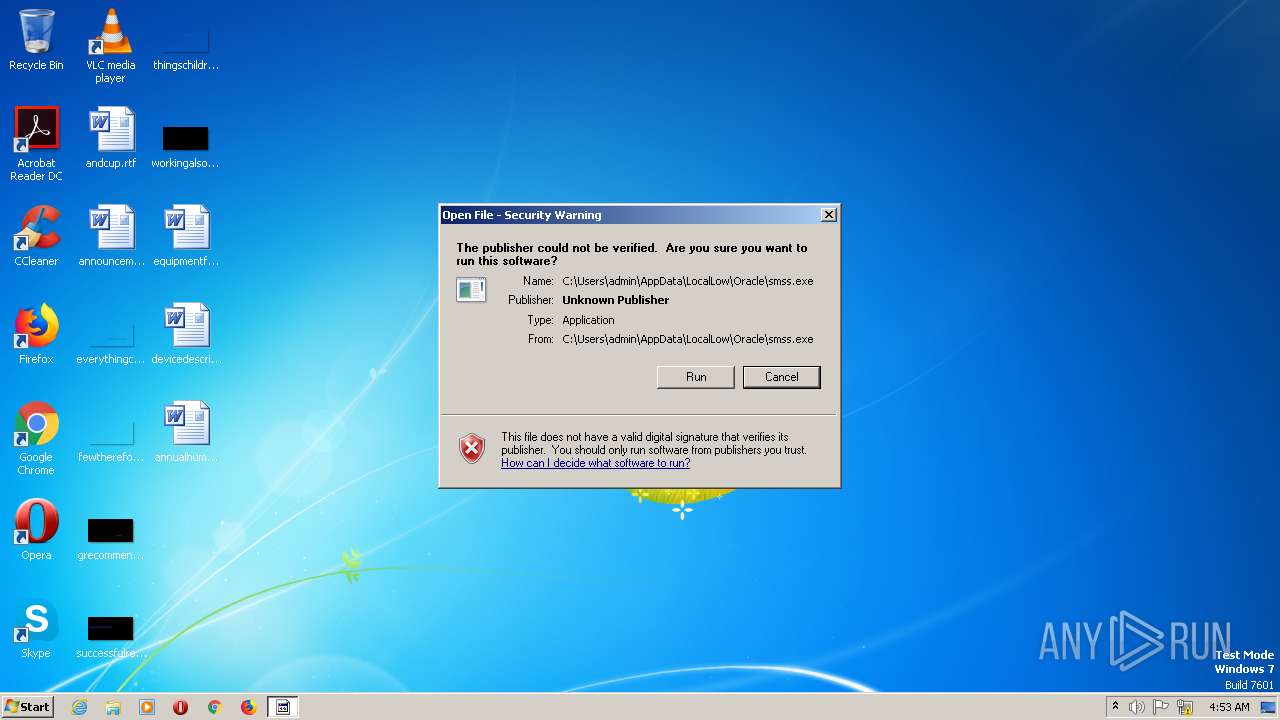
Application was dropped or rewritten from another process
- Windows Driver Foundation (WDF).exe (PID: 596)
- Windows Driver Foundation (WDF).exe (PID: 1200)
- Windows Driver Foundation (WDF).exe (PID: 2600)
DCRAT detected by memory dumps
- Windows Driver Foundation (WDF).exe (PID: 2600)
SUSPICIOUS
Executable content was dropped or overwritten
- b4a51418a774a766137e7fa75a0ce6ab.exe (PID: 1376)
- Windows Driver Foundation (WDF).exe (PID: 596)
- Windows Driver Foundation (WDF).exe (PID: 1200)
- Windows Driver Foundation (WDF).exe (PID: 2600)
Reads the Internet Settings
- b4a51418a774a766137e7fa75a0ce6ab.exe (PID: 1376)
- Windows Driver Foundation (WDF).exe (PID: 596)
- wscript.exe (PID: 1200)
- Windows Driver Foundation (WDF).exe (PID: 1200)
- Windows Driver Foundation (WDF).exe (PID: 2600)
Executing commands from a ".bat" file
- wscript.exe (PID: 1200)
- Windows Driver Foundation (WDF).exe (PID: 1200)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 1200)
- Windows Driver Foundation (WDF).exe (PID: 1200)
Executed via WMI
- schtasks.exe (PID: 2740)
- schtasks.exe (PID: 2148)
- schtasks.exe (PID: 1936)
- schtasks.exe (PID: 1612)
- schtasks.exe (PID: 2324)
- schtasks.exe (PID: 2408)
- schtasks.exe (PID: 2520)
- schtasks.exe (PID: 2332)
- schtasks.exe (PID: 2656)
- schtasks.exe (PID: 2872)
- schtasks.exe (PID: 3040)
- schtasks.exe (PID: 2088)
- schtasks.exe (PID: 2212)
- schtasks.exe (PID: 2692)
- schtasks.exe (PID: 2792)
- schtasks.exe (PID: 2900)
- schtasks.exe (PID: 2888)
- schtasks.exe (PID: 2756)
- schtasks.exe (PID: 2404)
- schtasks.exe (PID: 2568)
- schtasks.exe (PID: 3068)
- schtasks.exe (PID: 2560)
- schtasks.exe (PID: 2056)
- schtasks.exe (PID: 2812)
- schtasks.exe (PID: 2124)
- schtasks.exe (PID: 2604)
- schtasks.exe (PID: 2188)
- schtasks.exe (PID: 2312)
- schtasks.exe (PID: 2476)
- schtasks.exe (PID: 2652)
- schtasks.exe (PID: 3028)
- schtasks.exe (PID: 2984)
- schtasks.exe (PID: 2756)
- schtasks.exe (PID: 1116)
- schtasks.exe (PID: 2392)
- schtasks.exe (PID: 2672)
- schtasks.exe (PID: 2652)
- schtasks.exe (PID: 2964)
- schtasks.exe (PID: 2928)
- schtasks.exe (PID: 1660)
- schtasks.exe (PID: 2828)
- schtasks.exe (PID: 2240)
- schtasks.exe (PID: 2212)
- schtasks.exe (PID: 2448)
- schtasks.exe (PID: 2588)
- schtasks.exe (PID: 2420)
- schtasks.exe (PID: 2344)
- schtasks.exe (PID: 3064)
- schtasks.exe (PID: 1440)
- schtasks.exe (PID: 2792)
- schtasks.exe (PID: 1200)
- schtasks.exe (PID: 2416)
- schtasks.exe (PID: 2500)
- schtasks.exe (PID: 2412)
- schtasks.exe (PID: 2656)
- schtasks.exe (PID: 2144)
- schtasks.exe (PID: 2204)
- schtasks.exe (PID: 308)
- schtasks.exe (PID: 2936)
- schtasks.exe (PID: 2304)
- schtasks.exe (PID: 2432)
- schtasks.exe (PID: 2844)
- schtasks.exe (PID: 2632)
- schtasks.exe (PID: 2696)
- schtasks.exe (PID: 2924)
- schtasks.exe (PID: 2092)
Probably delay the execution using 'w32tm.exe'
- cmd.exe (PID: 2160)
The process creates files with name similar to system file names
- Windows Driver Foundation (WDF).exe (PID: 1200)
- Windows Driver Foundation (WDF).exe (PID: 2600)
Checks Windows Trust Settings
- Windows Driver Foundation (WDF).exe (PID: 2600)
Reads security settings of Internet Explorer
- Windows Driver Foundation (WDF).exe (PID: 2600)
INFO
Checks supported languages
- b4a51418a774a766137e7fa75a0ce6ab.exe (PID: 1376)
- Windows Driver Foundation (WDF).exe (PID: 596)
- Windows Driver Foundation (WDF).exe (PID: 1200)
- Windows Driver Foundation (WDF).exe (PID: 2600)
The process checks LSA protection
- b4a51418a774a766137e7fa75a0ce6ab.exe (PID: 1376)
- Windows Driver Foundation (WDF).exe (PID: 596)
- Windows Driver Foundation (WDF).exe (PID: 1200)
- Windows Driver Foundation (WDF).exe (PID: 2600)
Reads the computer name
- b4a51418a774a766137e7fa75a0ce6ab.exe (PID: 1376)
- Windows Driver Foundation (WDF).exe (PID: 596)
- Windows Driver Foundation (WDF).exe (PID: 1200)
- Windows Driver Foundation (WDF).exe (PID: 2600)
Create files in a temporary directory
- b4a51418a774a766137e7fa75a0ce6ab.exe (PID: 1376)
- Windows Driver Foundation (WDF).exe (PID: 596)
- Windows Driver Foundation (WDF).exe (PID: 1200)
Reads Environment values
- Windows Driver Foundation (WDF).exe (PID: 1200)
- Windows Driver Foundation (WDF).exe (PID: 2600)
Reads the machine GUID from the registry
- Windows Driver Foundation (WDF).exe (PID: 1200)
- Windows Driver Foundation (WDF).exe (PID: 2600)
Creates files or folders in the user directory
- Windows Driver Foundation (WDF).exe (PID: 1200)
- Windows Driver Foundation (WDF).exe (PID: 2600)
Creates files in the program directory
- Windows Driver Foundation (WDF).exe (PID: 2600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
DcRat
(PID) Process(2600) Windows Driver Foundation (WDF).exe
C2 (1)http://a0761206.xsph.ru/@lZWasFGdhRGe15WaM9GV
Options
MutexDCR_MUTEX-1F2Ca6VeLLRoltvmPlML
searchpath%UsersFolder% - Fast
Targetals
TRiD
| .exe | | | InstallShield setup (53.2) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (17.5) |
| .scr | | | Windows screen saver (16.1) |
| .exe | | | Win32 Executable (generic) (5.5) |
| .exe | | | Win16/32 Executable Delphi generic (2.5) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x20cc |
| UninitializedDataSize: | - |
| InitializedDataSize: | 1245184 |
| CodeSize: | 5120 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x000013B8 | 0x00001400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.34099 |
DATA | 0x00003000 | 0x0000007C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.11763 |
BSS | 0x00004000 | 0x00000695 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00005000 | 0x00000302 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.47732 |
.tls | 0x00006000 | 0x00000004 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00007000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.199108 |
.reloc | 0x00008000 | 0x000001C8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.7833 |
.rsrc | 0x00009000 | 0x0012F4FC | 0x0012F600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.5315 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
A1 | 6.53197 | 1241797 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
B1 | 4.1643 | 35 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
C1 | 0 | 1 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
D1 | 0 | 1 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
DVCLAL | 4 | 16 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
E1 | 0 | 1 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 4.08834 | 56 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
kernel32.dll |
shell32.dll |
shfolder.dll |
Total processes
104
Monitored processes
74
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | schtasks.exe /create /tn "taskhost" /sc ONLOGON /tr "'C:\Users\All Users\Documents\taskhost.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 596 | "C:\Users\admin\AppData\Local\Temp\Windows Driver Foundation (WDF).exe" | C:\Users\admin\AppData\Local\Temp\Windows Driver Foundation (WDF).exe | b4a51418a774a766137e7fa75a0ce6ab.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1116 | schtasks.exe /create /tn "IMEDICTUPDATEI" /sc MINUTE /mo 12 /tr "'C:\Users\Public\Music\Sample Music\IMEDICTUPDATE.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1200 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Windows\BVHTprimxG0zwz49LhrmEC6BsWD.vbe" | C:\Windows\SysWOW64\wscript.exe | — | Windows Driver Foundation (WDF).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1200 | "C:\Users\admin\AppData\Local\Temp\Windows\Windows Driver Foundation (WDF).exe" | C:\Users\admin\AppData\Local\Temp\Windows\Windows Driver Foundation (WDF).exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.1.1o Modules
| |||||||||||||||
| 1200 | schtasks.exe /create /tn "lsass" /sc ONLOGON /tr "'C:\Windows\Tasks\lsass.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1260 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Windows\hlXC2FInD0MhsFNJzolev0pWo.bat" " | C:\Windows\SysWOW64\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1376 | "C:\Users\admin\AppData\Local\Temp\b4a51418a774a766137e7fa75a0ce6ab.exe" | C:\Users\admin\AppData\Local\Temp\b4a51418a774a766137e7fa75a0ce6ab.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1440 | schtasks.exe /create /tn "dwmd" /sc MINUTE /mo 10 /tr "'C:\Users\Public\Documents\My Pictures\dwm.exe'" /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1612 | schtasks.exe /create /tn "spoolsv" /sc ONLOGON /tr "'C:\Users\Public\Pictures\Sample Pictures\spoolsv.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
10 114
Read events
10 032
Write events
82
Delete events
0
Modification events
| (PID) Process: | (1376) b4a51418a774a766137e7fa75a0ce6ab.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1376) b4a51418a774a766137e7fa75a0ce6ab.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1376) b4a51418a774a766137e7fa75a0ce6ab.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1376) b4a51418a774a766137e7fa75a0ce6ab.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (596) Windows Driver Foundation (WDF).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (596) Windows Driver Foundation (WDF).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (596) Windows Driver Foundation (WDF).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (596) Windows Driver Foundation (WDF).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1200) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1200) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
48
Suspicious files
0
Text files
50
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1200 | Windows Driver Foundation (WDF).exe | C:\Windows\debug\WIA\0bcb650e8adc8c | text | |
MD5:— | SHA256:— | |||
| 1200 | Windows Driver Foundation (WDF).exe | C:\Users\Public\Recorded TV\Sample Media\6ccacd8608530f | text | |
MD5:— | SHA256:— | |||
| 1200 | Windows Driver Foundation (WDF).exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\6203df4a6bafc7 | text | |
MD5:— | SHA256:— | |||
| 1200 | Windows Driver Foundation (WDF).exe | C:\Users\admin\AppData\Local\Temp\ByuAs1jpR6.bat | text | |
MD5:— | SHA256:— | |||
| 1200 | Windows Driver Foundation (WDF).exe | C:\Windows\debug\WIA\1173b9a28a9c10 | text | |
MD5:— | SHA256:— | |||
| 1200 | Windows Driver Foundation (WDF).exe | C:\Users\admin\AppData\Local\Temp\P4d6soi8LF | text | |
MD5:— | SHA256:— | |||
| 2600 | Windows Driver Foundation (WDF).exe | C:\Users\Public\27d1bcfc3c54e0 | text | |
MD5:— | SHA256:— | |||
| 1200 | Windows Driver Foundation (WDF).exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\088424020bedd6 | text | |
MD5:— | SHA256:— | |||
| 596 | Windows Driver Foundation (WDF).exe | C:\Users\admin\AppData\Local\Temp\Windows\Windows Driver Foundation (WDF).exe | executable | |
MD5:D0C133555FAE9D5612D11E5B7DBF8482 | SHA256:4B23F7BC07FD2CD707AA84FF7B8B7EDE9C47567C1C921F8E6FC3477E5745499E | |||
| 1376 | b4a51418a774a766137e7fa75a0ce6ab.exe | C:\Users\admin\AppData\Local\Temp\Windows Driver Foundation (WDF).exe | executable | |
MD5:F87389DAD0B71E56CCF30B19C58F9A3E | SHA256:5978B9BF6D1324C63EC34A773F8A77AF0F7DFA67E43DB579E72F3CF9840A426D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report