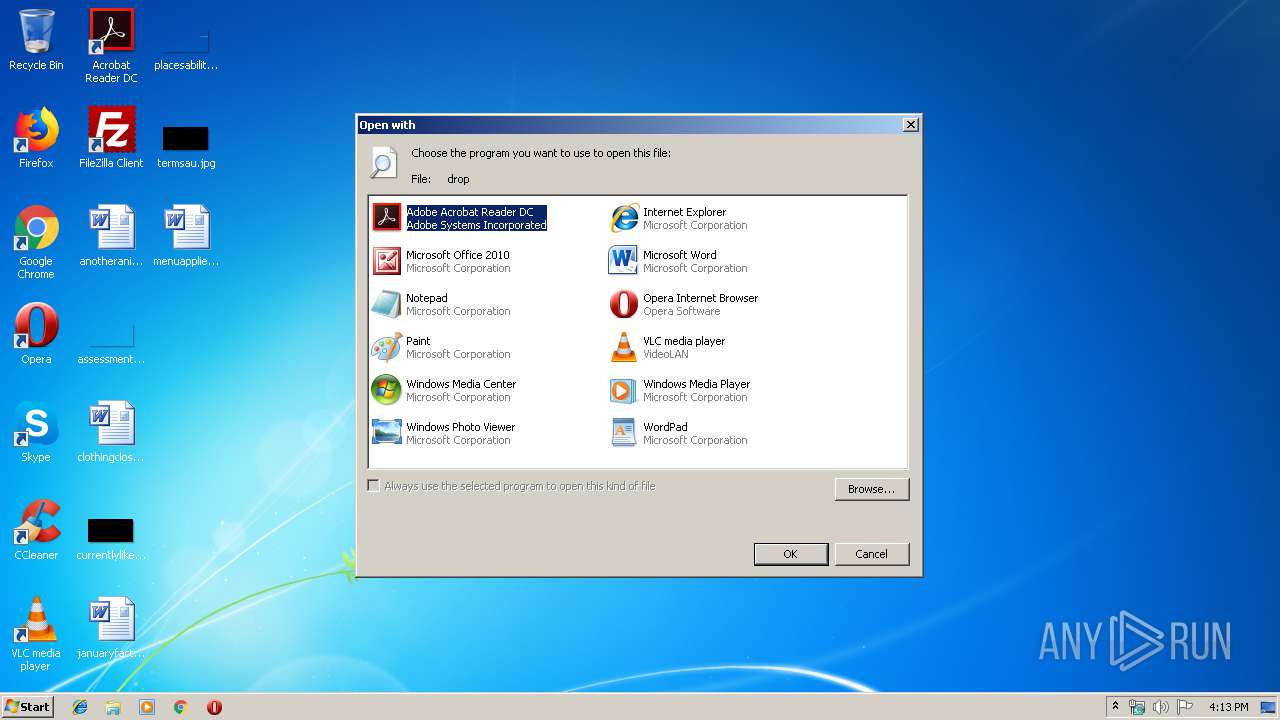
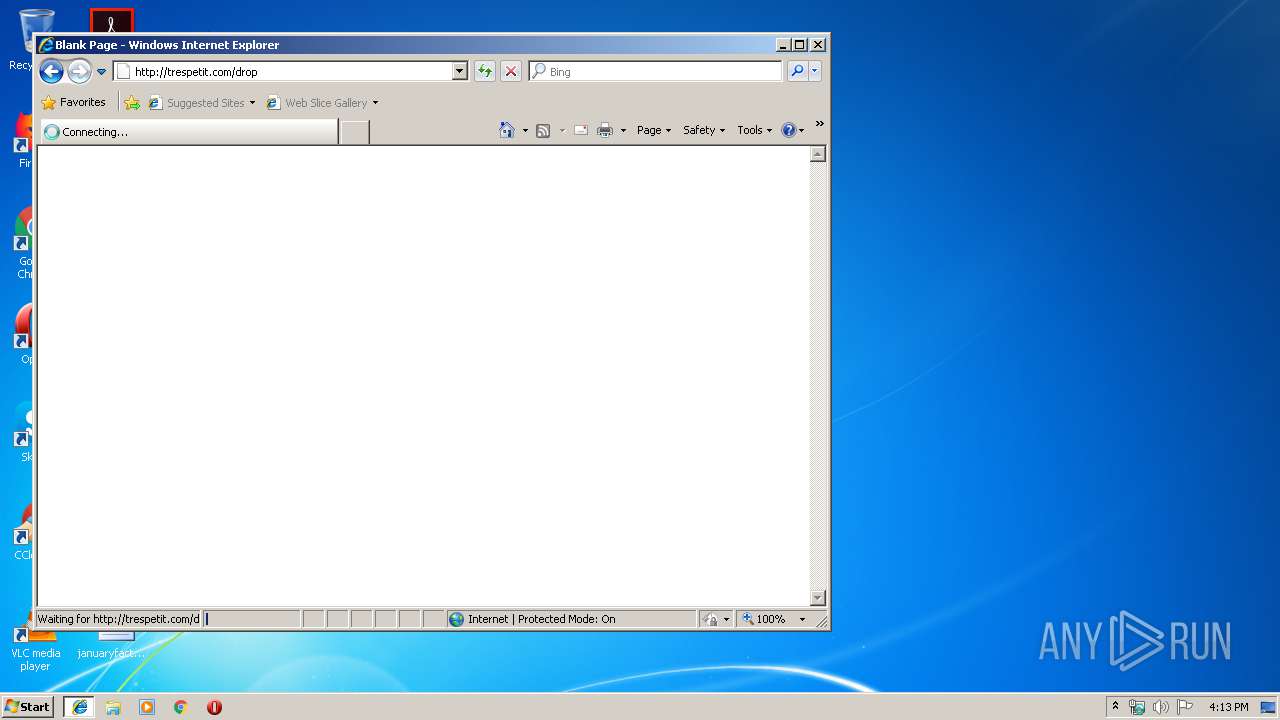
| download: | drop |
| Full analysis: | https://app.any.run/tasks/4349e48a-c946-4668-b192-4b8db06c6f16 |
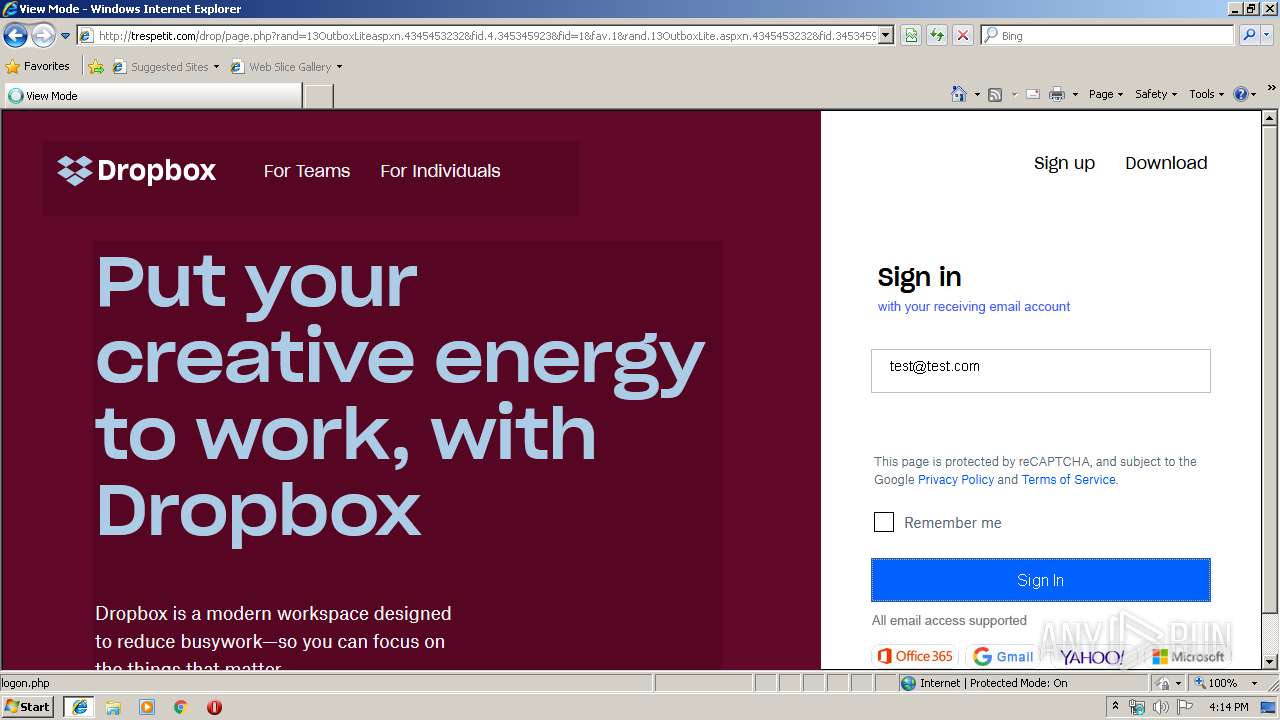
| Verdict: | Malicious activity |
| Analysis date: | October 09, 2019, 15:13:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | EB25B905964EAEFBAD86914C3FE7C795 |
| SHA1: | 04329B5BCDC844483C0B72E3497BCBE807CD8F56 |
| SHA256: | 9A2E63769009BACF150A5110C2C996AA10DD36EEC0C40C94585FCA897F27CDAF |
| SSDEEP: | 6:GpeffQcESSpuSj2QlWjucwIRF2Q+DRjG+L8aLUtpfQQKS2Gb:Gpef7SISiQlOYQ+DY0DLUttXb |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts Internet Explorer
- rundll32.exe (PID: 2804)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2516)
Reads Internet Cache Settings
- iexplore.exe (PID: 3176)
- iexplore.exe (PID: 2516)
Application launched itself
- iexplore.exe (PID: 2516)
Reads internet explorer settings
- iexplore.exe (PID: 3232)
- iexplore.exe (PID: 3176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
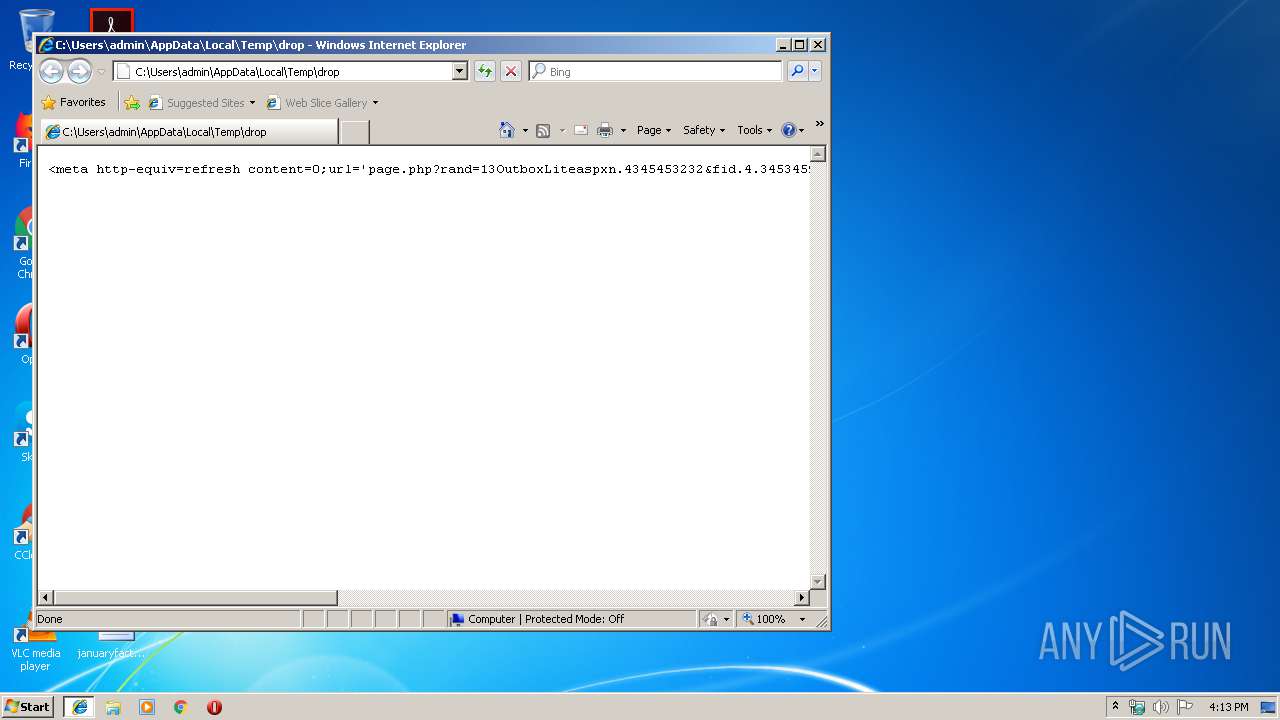
| 2516 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\drop | C:\Program Files\Internet Explorer\iexplore.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2804 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\drop | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3176 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2516 CREDAT:203009 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3232 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2516 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 030
Read events
864
Write events
164
Delete events
2
Modification events
| (PID) Process: | (2804) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (2804) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (2804) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE |
Value: Microsoft Word | |||
| (PID) Process: | (2804) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2804) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2804) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
Executable files
0
Suspicious files
1
Text files
15
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3232 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019092020190921\index.dat | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF97C96BC295E87DBA.TMP | — | |
MD5:— | SHA256:— | |||
| 3232 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019100920191010\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:— | SHA256:— | |||
| 3176 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\NDTP0WOY\drop[1].htm | text | |
MD5:— | SHA256:— | |||
| 3176 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3176 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\favicon[1].png | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
8
DNS requests
3
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
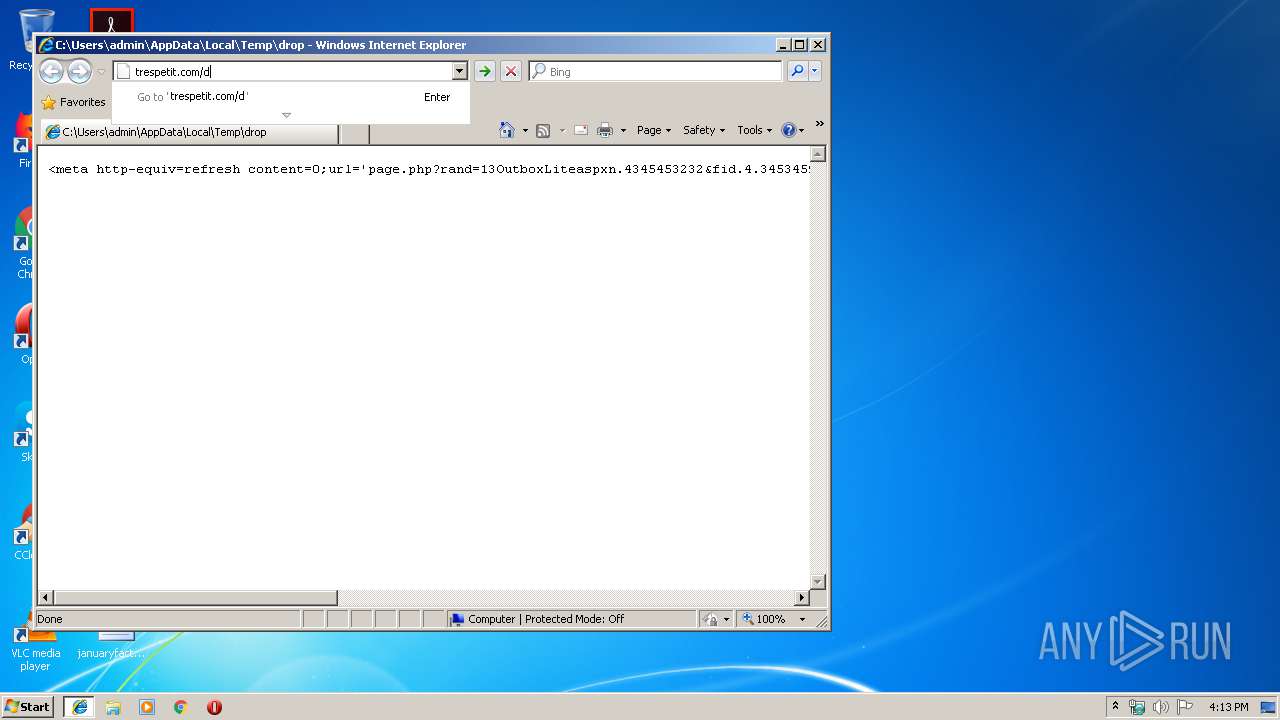
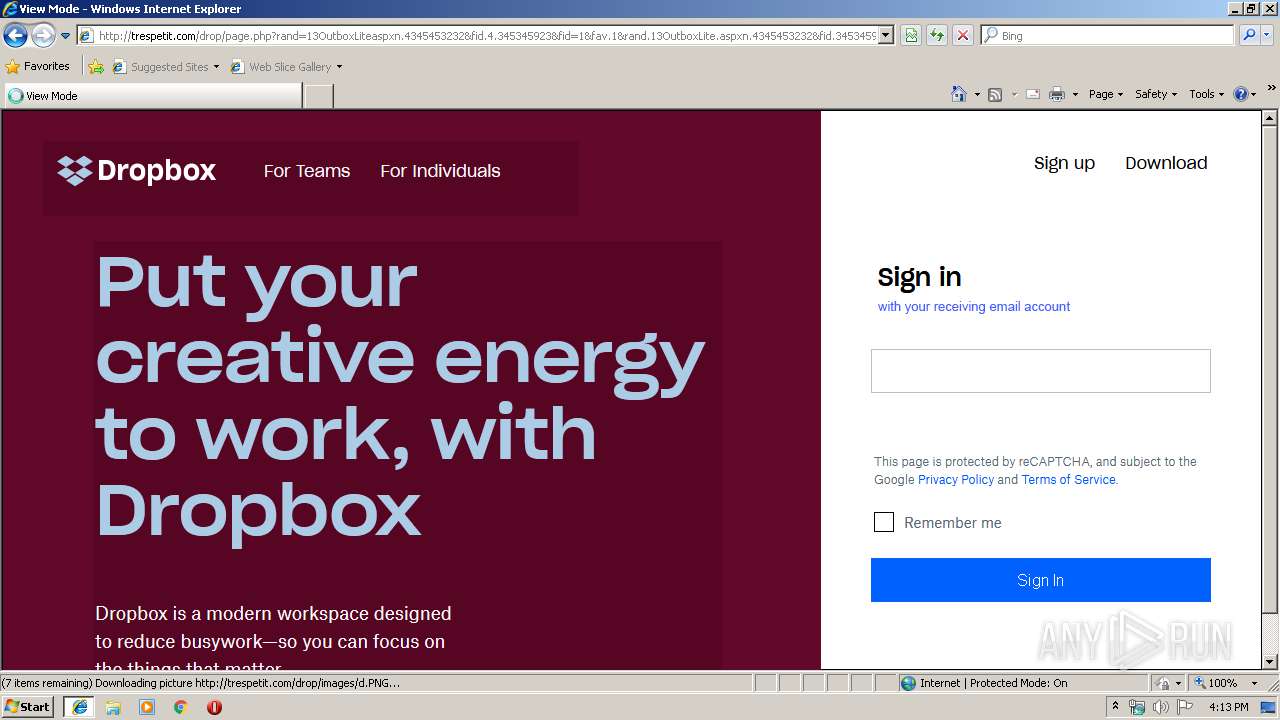
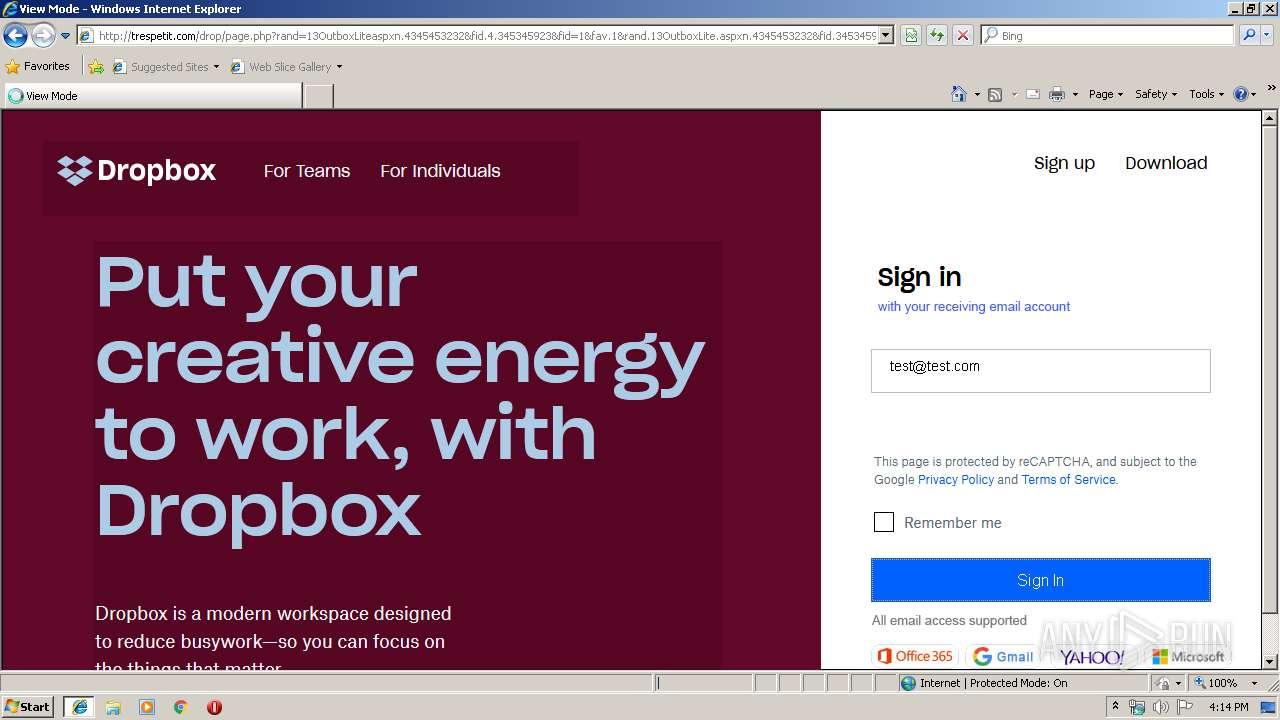
2516 | iexplore.exe | GET | 200 | 199.204.248.115:80 | http://trespetit.com/favicon.ico | US | — | — | malicious |
3176 | iexplore.exe | GET | 200 | 199.204.248.115:80 | http://trespetit.com/drop/images/top1.png | US | image | 4.50 Kb | malicious |
3176 | iexplore.exe | GET | 200 | 199.204.248.115:80 | http://trespetit.com/drop/images/text.PNG | US | image | 31.8 Kb | malicious |
3176 | iexplore.exe | GET | 200 | 199.204.248.115:80 | http://trespetit.com/drop/images/t.PNG | US | image | 4.06 Kb | malicious |
3176 | iexplore.exe | GET | 301 | 199.204.248.115:80 | http://trespetit.com/drop | US | html | 234 b | malicious |
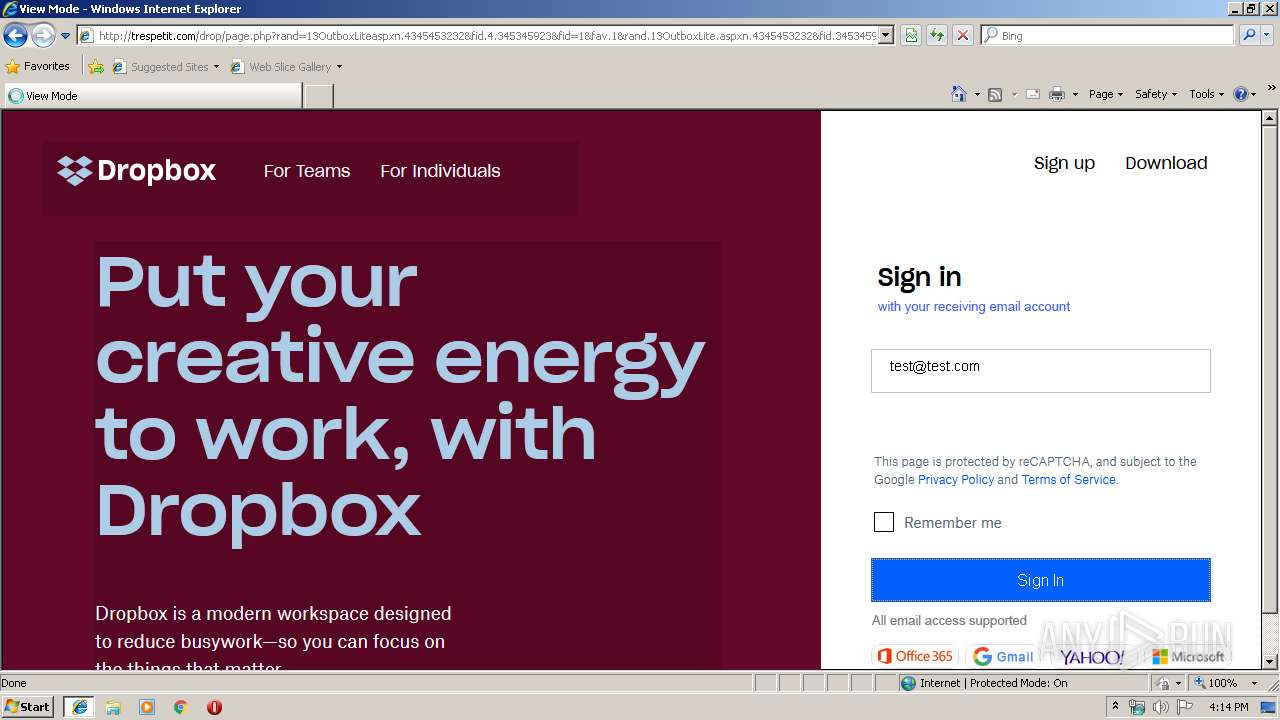
3176 | iexplore.exe | GET | — | 199.204.248.115:80 | http://trespetit.com/drop/page2.php | US | — | — | malicious |
2516 | iexplore.exe | GET | 200 | 199.204.248.115:80 | http://trespetit.com/favicon.ico | US | — | — | malicious |
3176 | iexplore.exe | GET | 200 | 199.204.248.115:80 | http://trespetit.com/drop/images/sa.png | US | image | 5.09 Kb | malicious |
3176 | iexplore.exe | GET | 200 | 199.204.248.115:80 | http://trespetit.com/drop/images/a.png | US | image | 35.0 Kb | malicious |
3176 | iexplore.exe | GET | — | 199.204.248.115:80 | http://trespetit.com/drop/page2.php | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2516 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3176 | iexplore.exe | 199.204.248.115:80 | trespetit.com | CONTINENTAL BROADBAND PENNSYLVANIA, INC. | US | malicious |
2516 | iexplore.exe | 199.204.248.115:80 | trespetit.com | CONTINENTAL BROADBAND PENNSYLVANIA, INC. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
trespetit.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3176 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] Adobe PDF Phishing Landing |