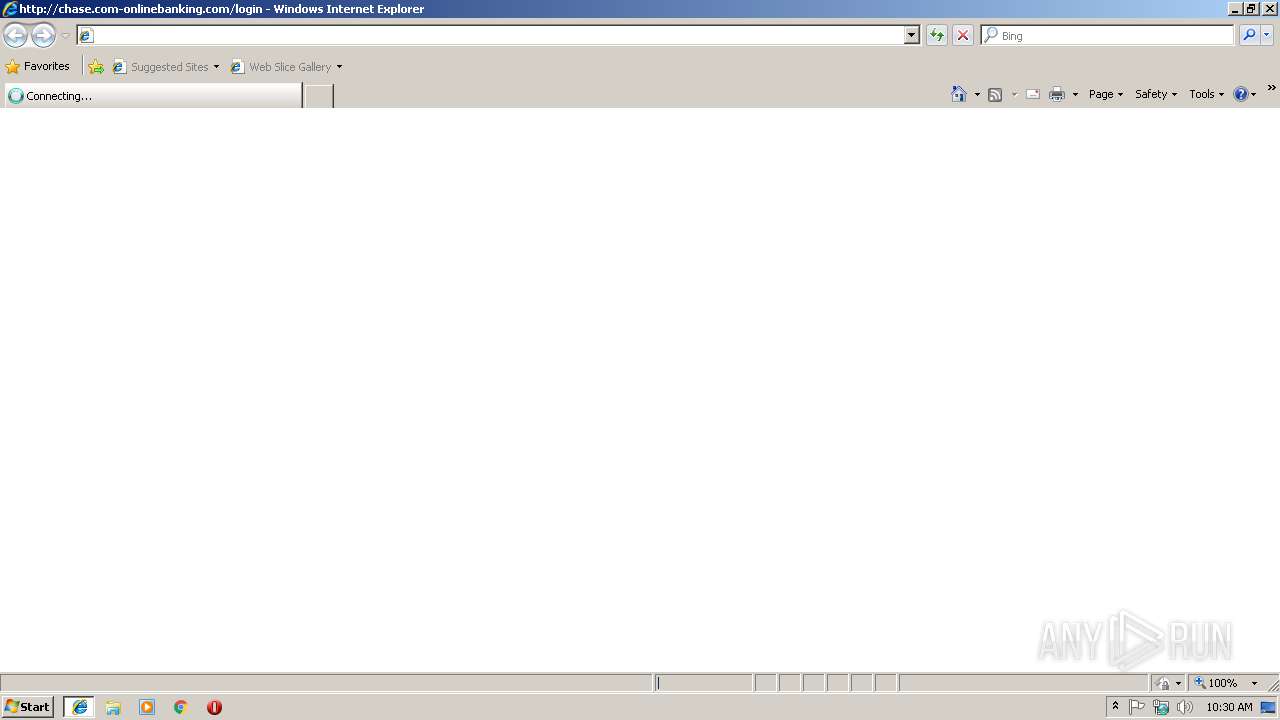
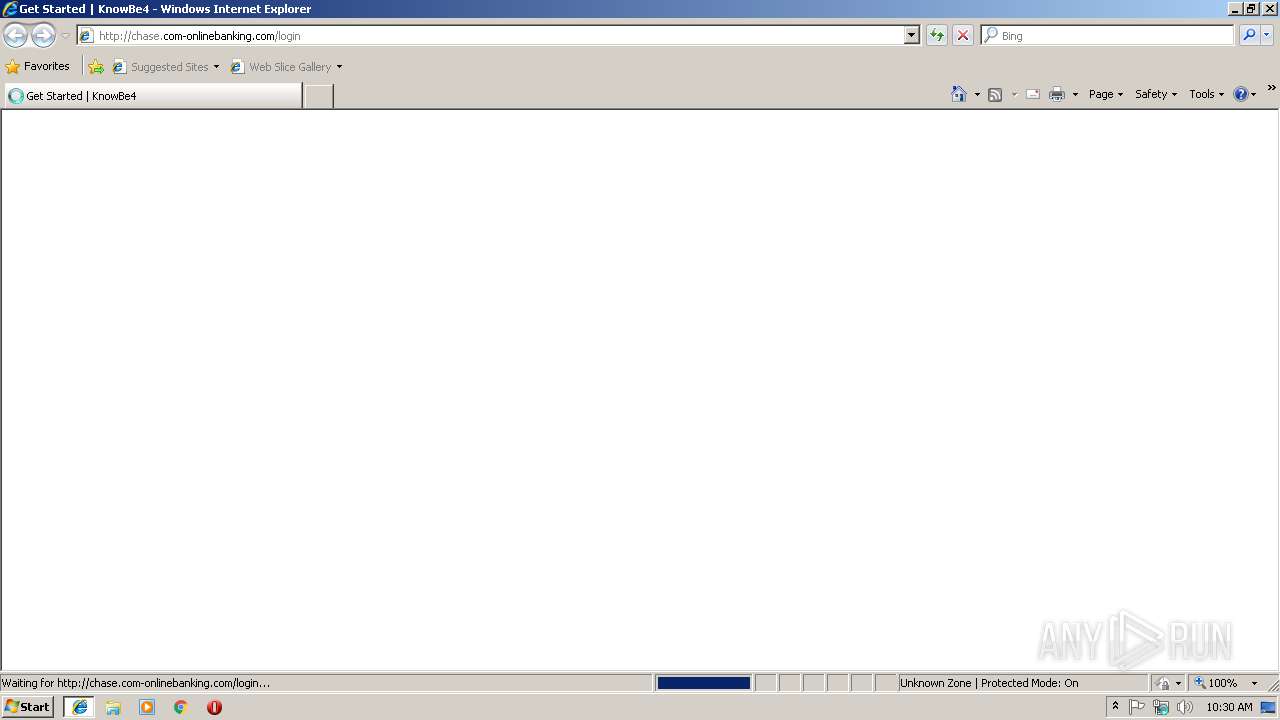
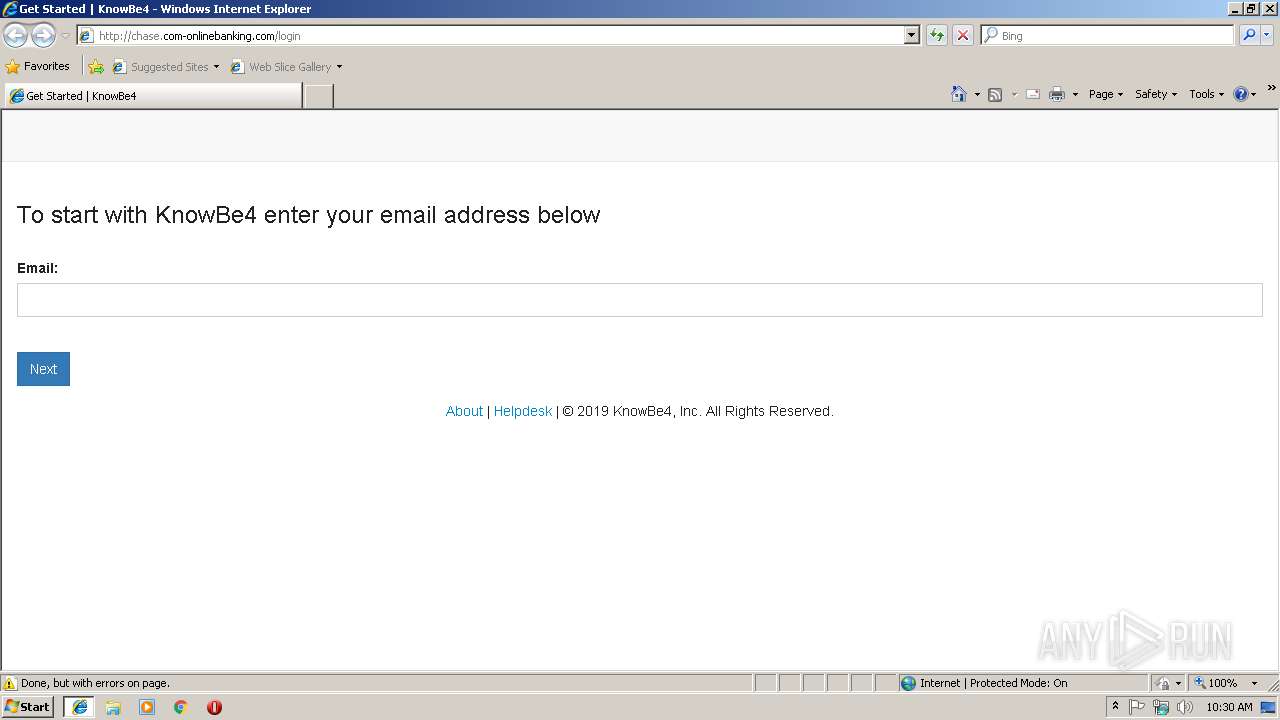
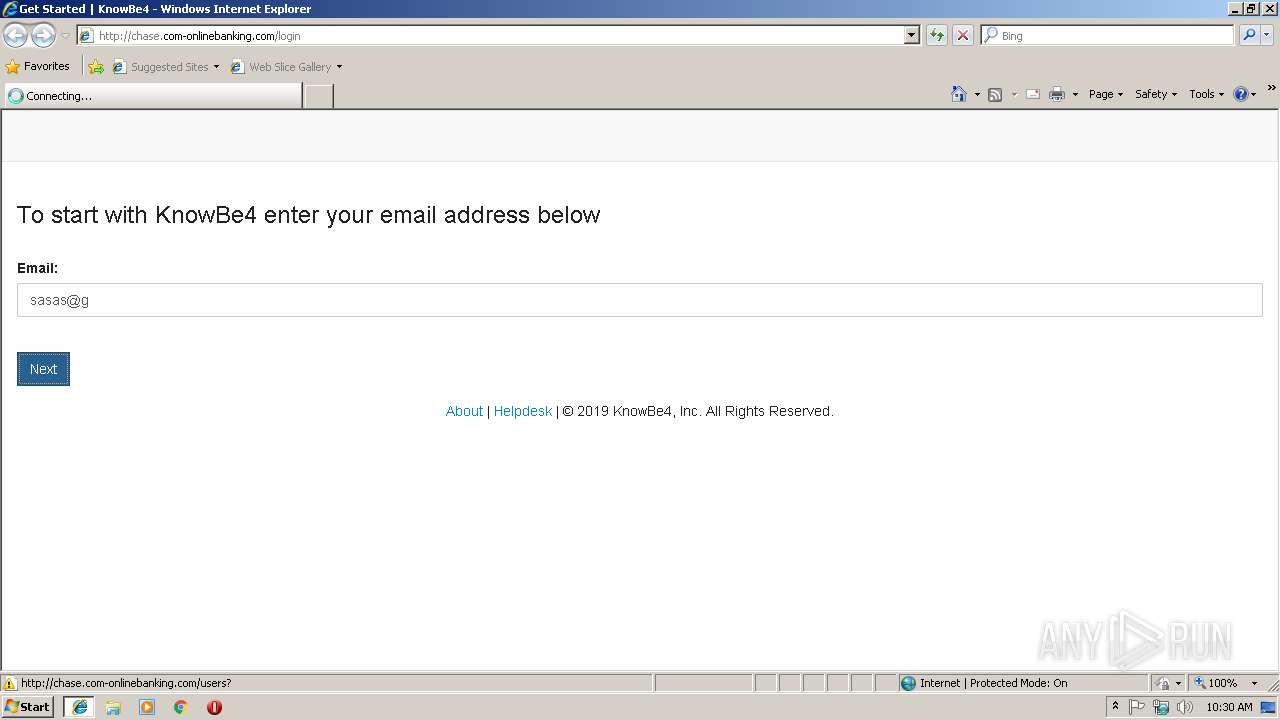
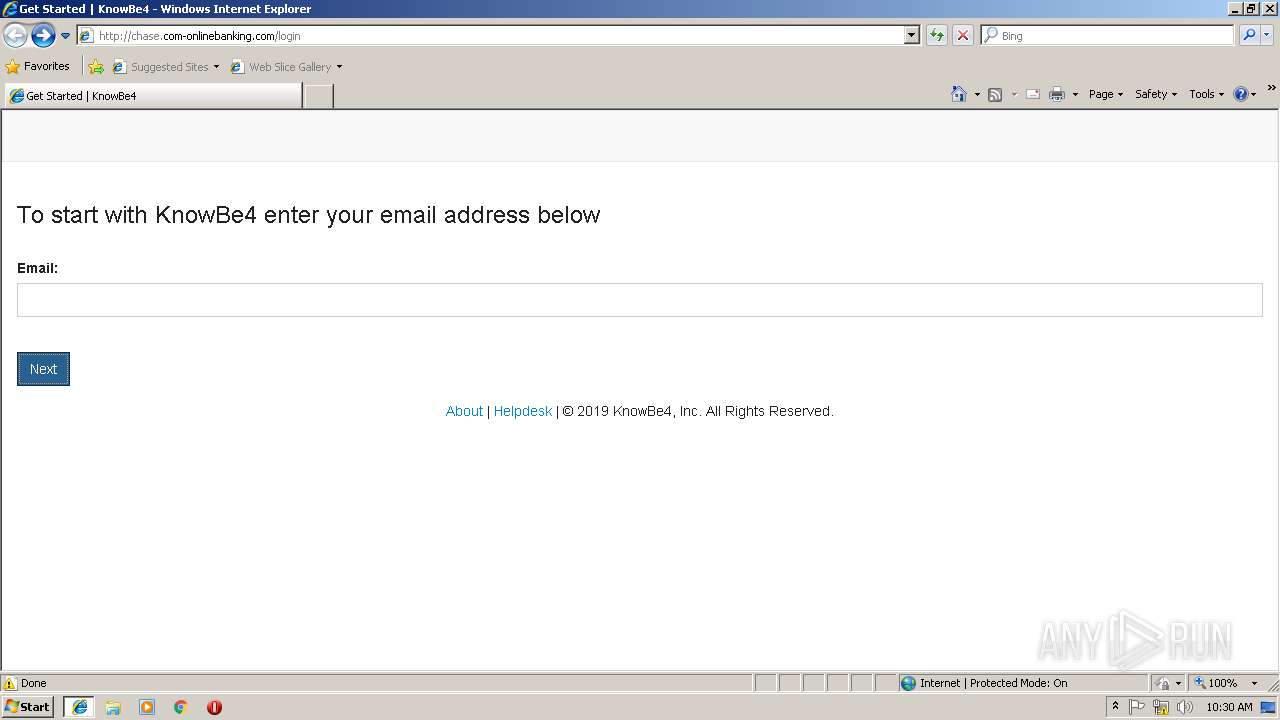
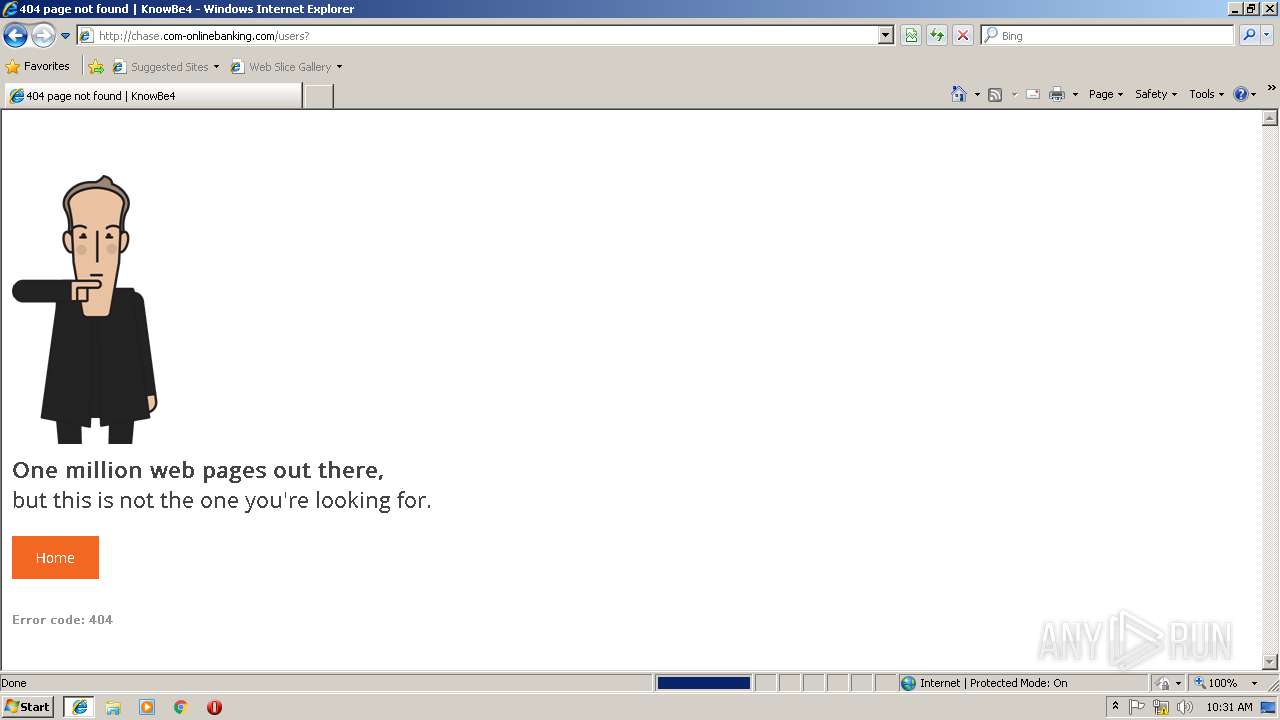
| URL: | http://chase.com-onlinebanking.com |
| Full analysis: | https://app.any.run/tasks/2ca172cd-c157-4921-a5fa-f4c72786c215 |
| Verdict: | Malicious activity |
| Analysis date: | January 28, 2019, 10:29:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 15A840A49E5BC70E40240B7E32DC261B |
| SHA1: | D82C75BEECAE0484128B1E7486A8FE82D093B661 |
| SHA256: | 9A20FCF55A7BA60B94D3571FC6B286BAB838489C52CA182F1029C3318C90C8D3 |
| SSDEEP: | 3:N1KdNErd1pT:COZ |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads internet explorer settings
- iexplore.exe (PID: 3144)
Changes internet zones settings
- iexplore.exe (PID: 2844)
Reads Internet Cache Settings
- iexplore.exe (PID: 3144)
- iexplore.exe (PID: 2844)
Application launched itself
- iexplore.exe (PID: 2844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
32
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2844 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3144 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2844 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
448
Read events
378
Write events
67
Delete events
3
Modification events
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {ACA574AB-22E7-11E9-BAD8-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307010001001C000A001E0005009402 | |||
Executable files
0
Suspicious files
0
Text files
12
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2844 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2844 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3144 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\login[1].txt | — | |
MD5:— | SHA256:— | |||
| 2844 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon-af6643024af4ecfc57b7e5358608edc94ccd3042dc4849ccdc5befa304b79bf1[1].ico | — | |
MD5:— | SHA256:— | |||
| 3144 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\css[1].txt | text | |
MD5:— | SHA256:— | |||
| 3144 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\application-36583680c7b989e24d71ceca81eb8fa2a12fee9511569da5c5280d209d778a57[1].css | text | |
MD5:— | SHA256:— | |||
| 3144 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\vendor-5cfa144590860214394c[1].js | text | |
MD5:— | SHA256:— | |||
| 3144 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\login[1].htm | html | |
MD5:— | SHA256:— | |||
| 2844 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[3].png | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
| 3144 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\glyphicons-halflings-regular-13634da87d9e23f8c3ed9108ce1724d183a39ad072e73e1b3d8cbf646d2d0407[1].eot | eot | |
MD5:F4769F9BDB7466BE65088239C12046D1 | SHA256:13634DA87D9E23F8C3ED9108CE1724D183A39AD072E73E1B3D8CBF646D2D0407 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
9
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3144 | iexplore.exe | GET | 200 | 52.3.198.50:80 | http://chase.com-onlinebanking.com/assets/application-784a43c4e711cf668205abe41cc9c17867fcd44eae58972b48404843851ac315.js | US | text | 844 Kb | whitelisted |
3144 | iexplore.exe | GET | 200 | 52.3.198.50:80 | http://chase.com-onlinebanking.com/login | US | html | 4.46 Kb | whitelisted |
3144 | iexplore.exe | GET | 200 | 52.3.198.50:80 | http://chase.com-onlinebanking.com/login | US | html | 4.46 Kb | whitelisted |
3144 | iexplore.exe | GET | 200 | 52.3.198.50:80 | http://chase.com-onlinebanking.com/assets/font-awesome/fa-regular-400-473a9adc2b00aa237a66b820706d1c0255efb0fe6864760042fd576be97fd9ae.eot | US | eot | 39.6 Kb | whitelisted |
3144 | iexplore.exe | GET | 200 | 52.3.198.50:80 | http://chase.com-onlinebanking.com/assets/font-awesome/fa-solid-900-263c75a8cab8bdd6b642f29ddbf3bbb0b83af4a66e45604c93cbbf970996b5b3.eot | US | eot | 164 Kb | whitelisted |
3144 | iexplore.exe | GET | 200 | 52.3.198.50:80 | http://chase.com-onlinebanking.com/assets/font-awesome/fa-brands-400-914a7ba14b7d4eb4ff3bd34d48e258834bcb96764d49e710654f5f8094e9f9f9.eot | US | eot | 113 Kb | whitelisted |
3144 | iexplore.exe | GET | 200 | 52.3.198.50:80 | http://chase.com-onlinebanking.com/assets/bootstrap/glyphicons-halflings-regular-13634da87d9e23f8c3ed9108ce1724d183a39ad072e73e1b3d8cbf646d2d0407.eot? | US | eot | 19.6 Kb | whitelisted |
2844 | iexplore.exe | GET | 200 | 52.3.198.50:80 | http://chase.com-onlinebanking.com/assets/favicon-af6643024af4ecfc57b7e5358608edc94ccd3042dc4849ccdc5befa304b79bf1.ico | US | image | 341 b | whitelisted |
3144 | iexplore.exe | GET | 200 | 52.3.198.50:80 | http://chase.com-onlinebanking.com/assets/modernizr-654222debe8018b12f1993ceddff30dc163a7d5008d79869c399d6d167321f97.js | US | html | 15.3 Kb | whitelisted |
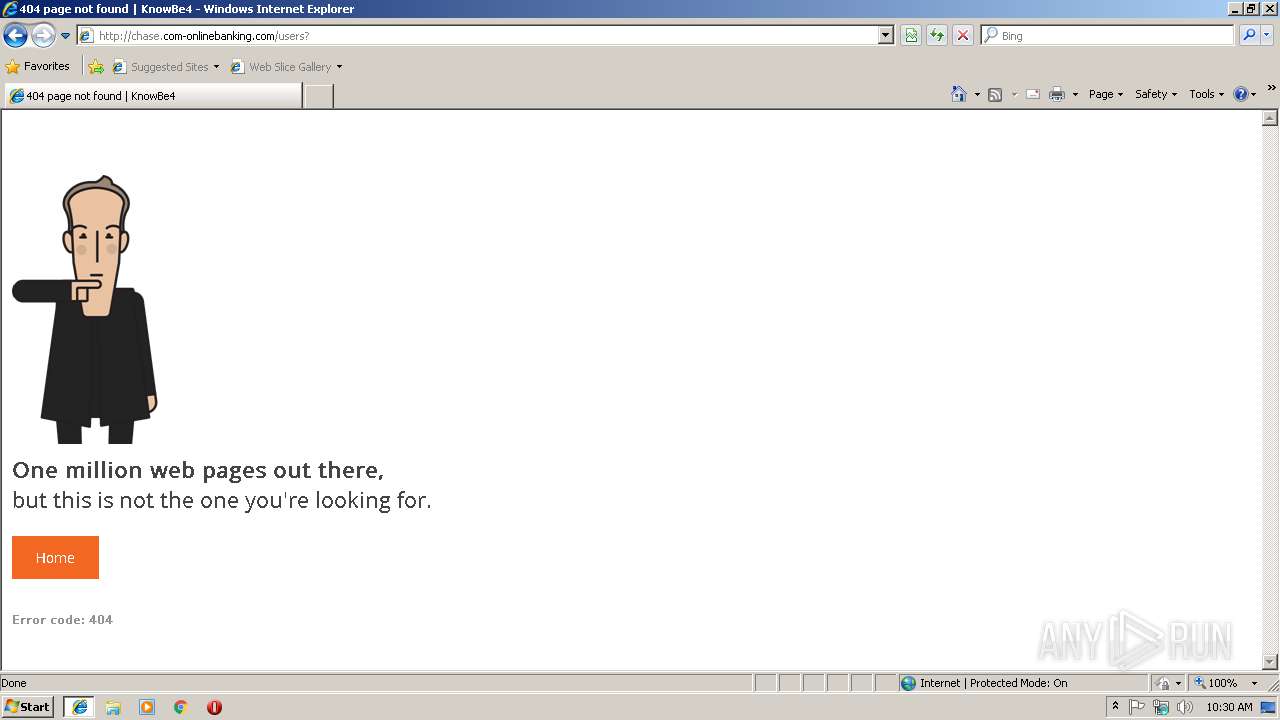
3144 | iexplore.exe | POST | 404 | 52.3.198.50:80 | http://chase.com-onlinebanking.com/users? | US | html | 1.87 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2844 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3144 | iexplore.exe | 52.3.198.50:80 | chase.com-onlinebanking.com | Amazon.com, Inc. | US | suspicious |
3144 | iexplore.exe | 172.217.16.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3144 | iexplore.exe | 108.177.15.95:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2844 | iexplore.exe | 52.3.198.50:80 | chase.com-onlinebanking.com | Amazon.com, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
chase.com-onlinebanking.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |