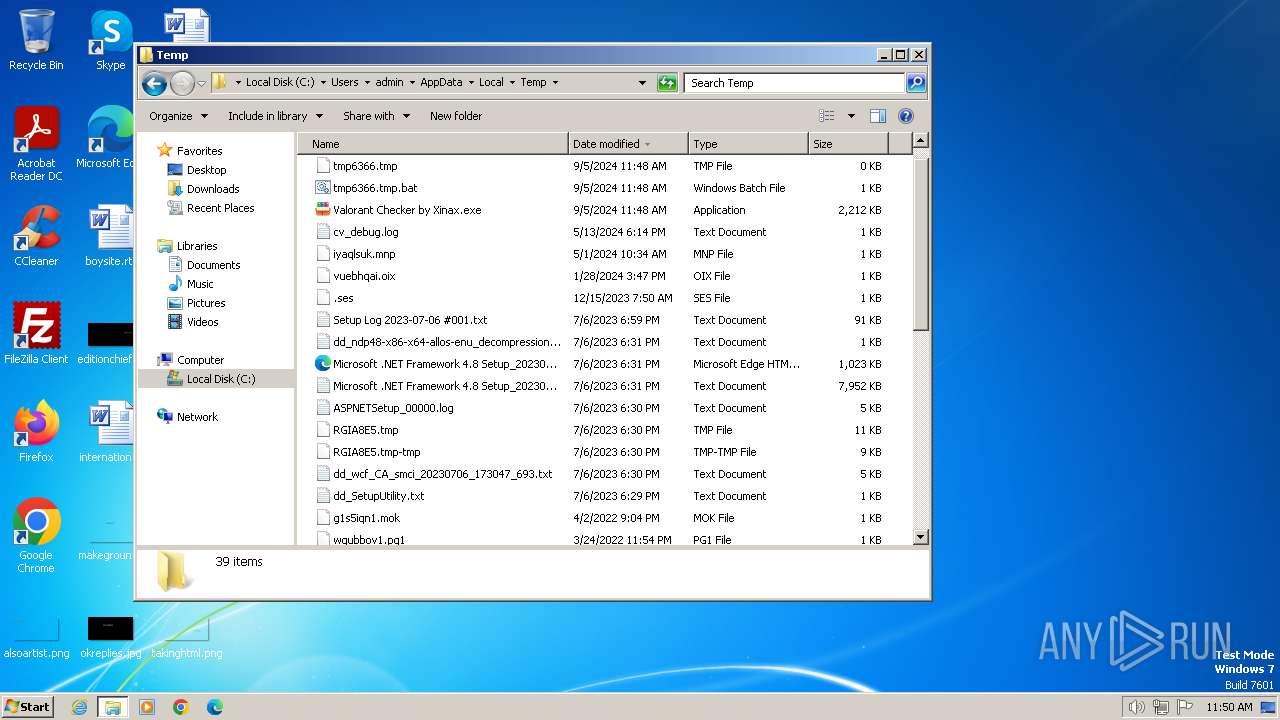
| File name: | Valorant Checker by Xinax.exe |
| Full analysis: | https://app.any.run/tasks/9057274f-8886-4af6-b9c5-977047461079 |
| Verdict: | Malicious activity |
| Analysis date: | September 05, 2024, 10:48:33 |
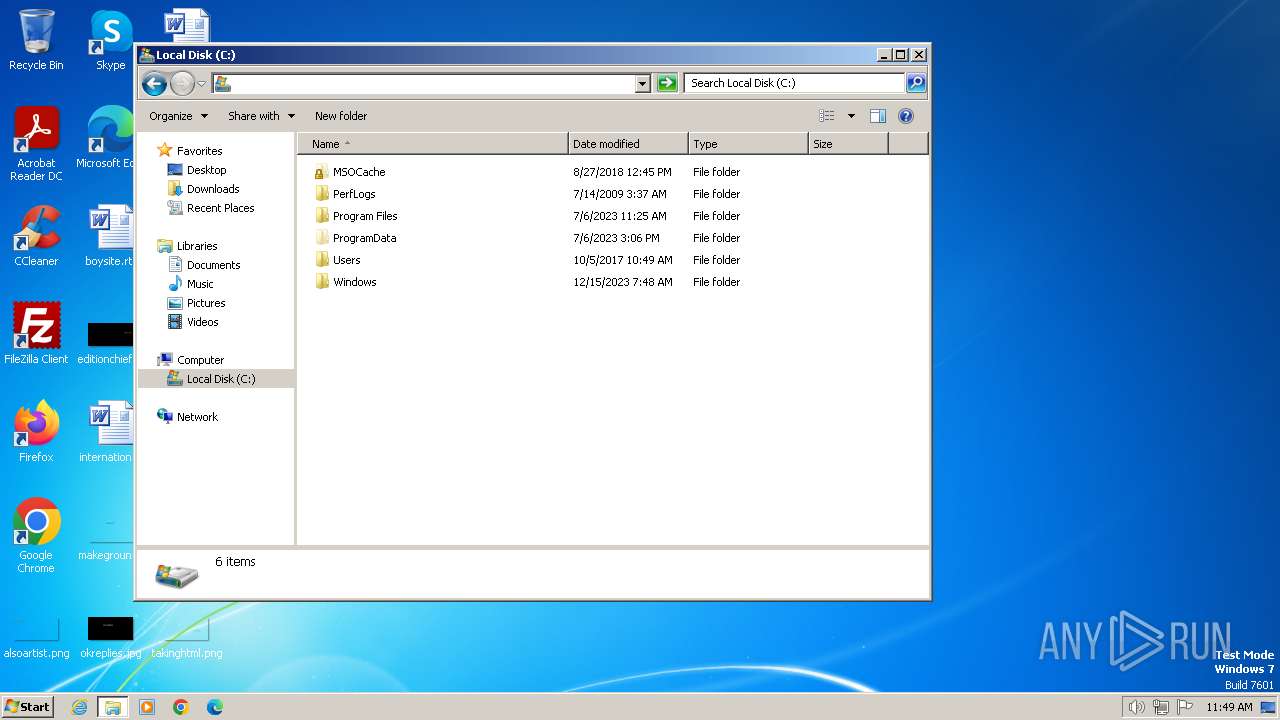
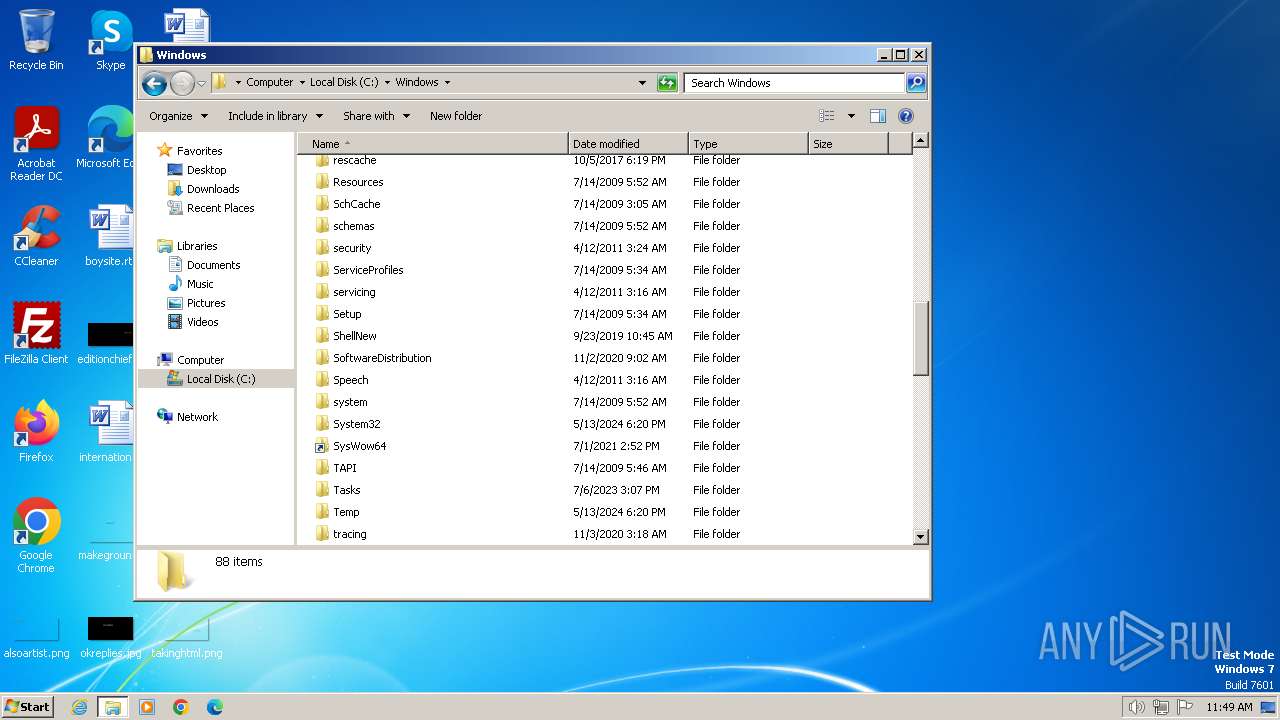
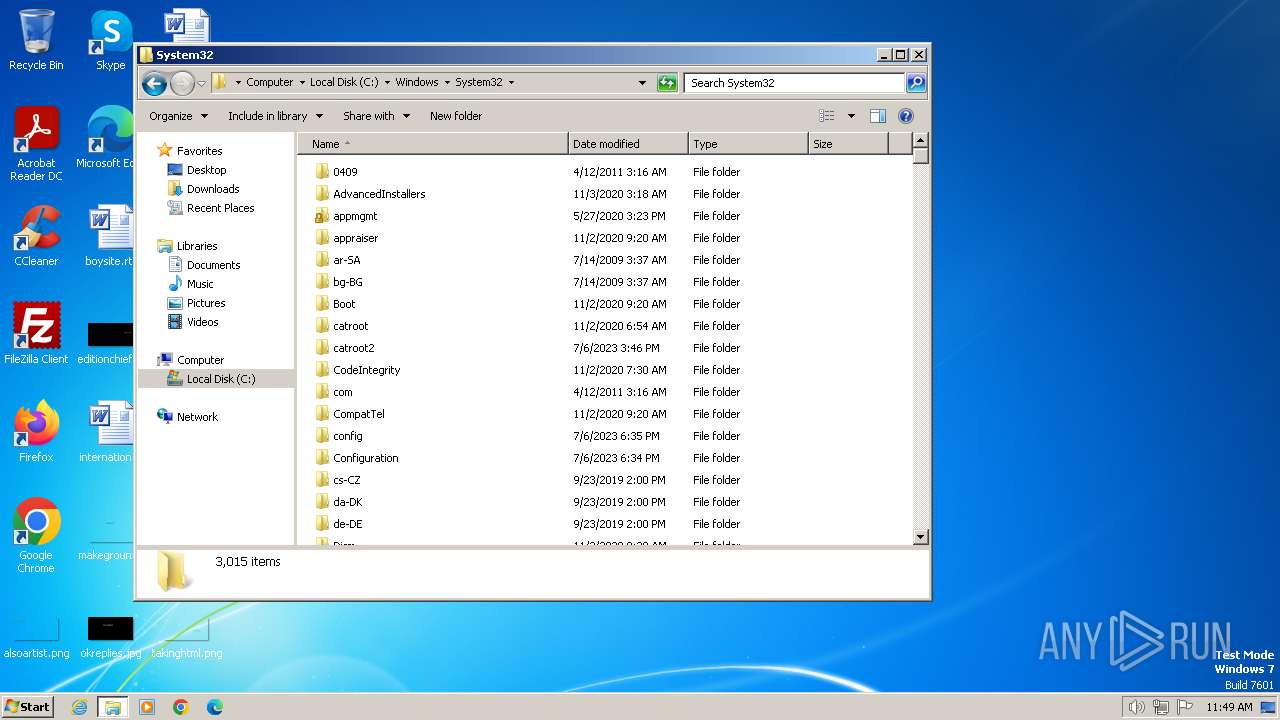
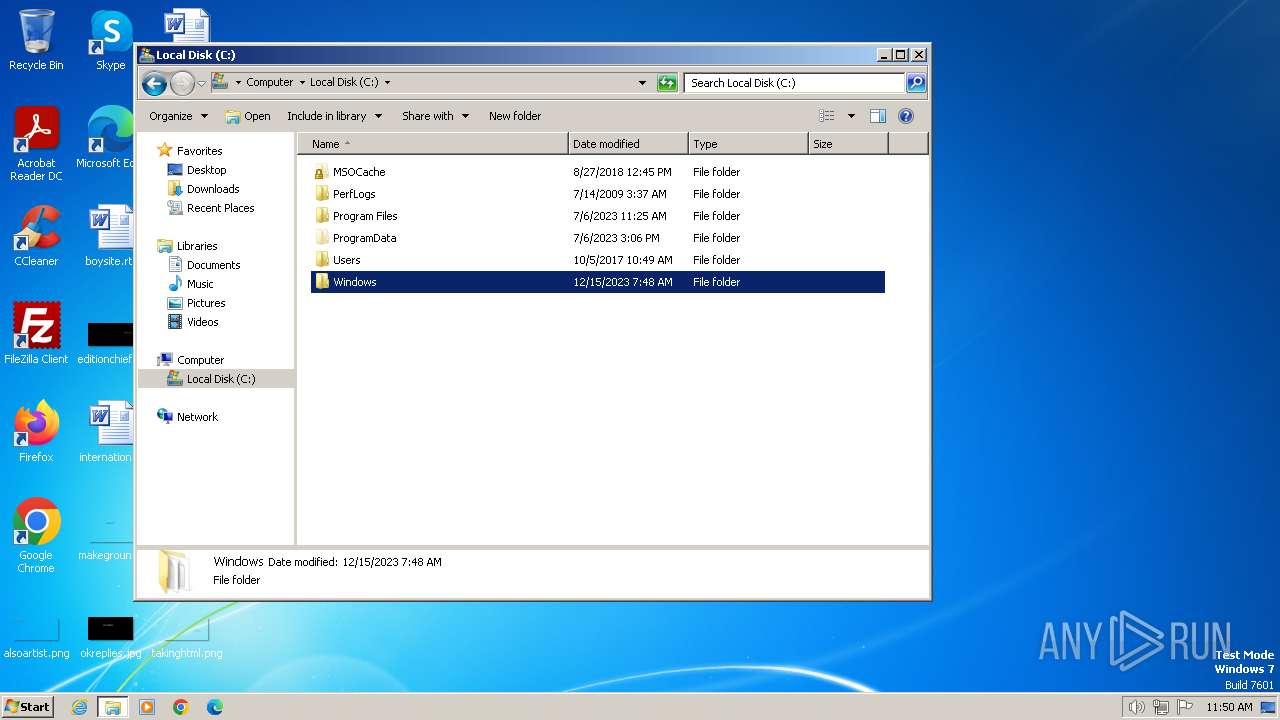
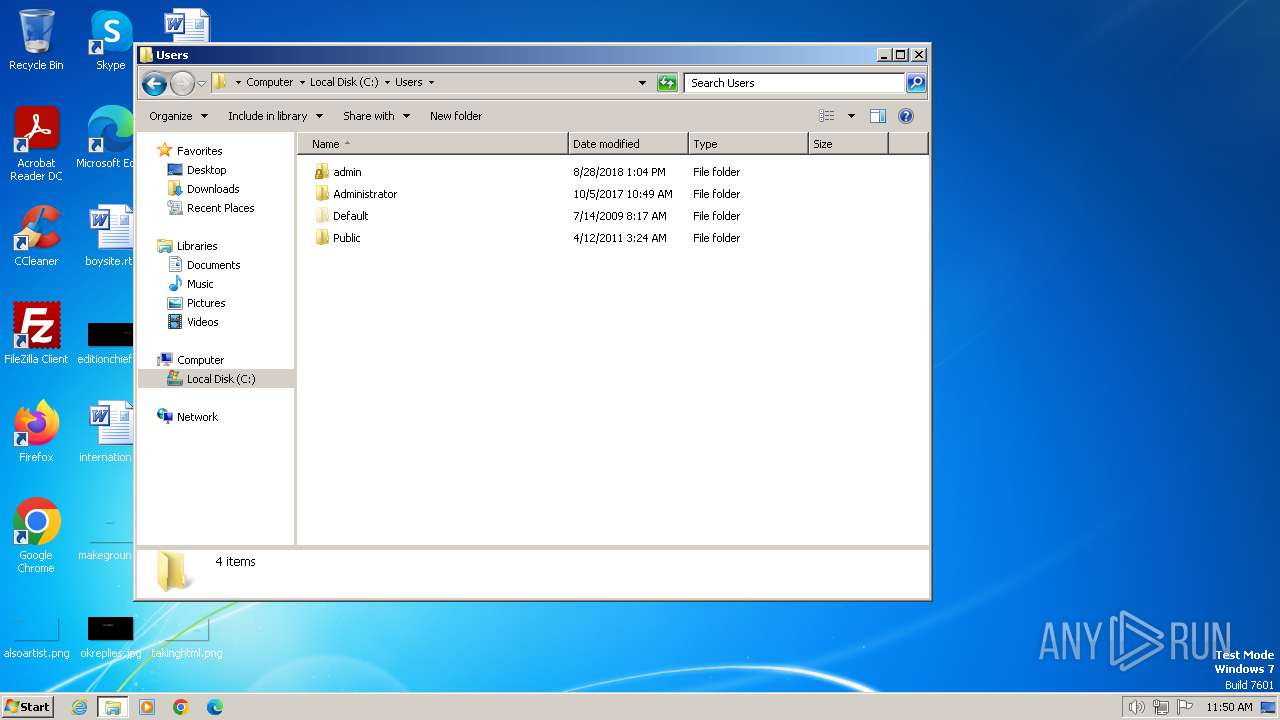
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 737B4BEB0D2D9DF17F9CD77DD5DF149C |
| SHA1: | E54A157C6A7661AA3275213E5B35ABA21E79BBE8 |
| SHA256: | 9A1E210A7BF171FE6BCDEDDDAE899207D11F38122D4BEE14DFD4FE375A78DECF |
| SSDEEP: | 49152:IBJAfdK/QU9lR8V8gtCBrap0g5H6rZTvDS6zNwykkcak:yAdUB8uvBrap95Hmdvm6z2R |
MALICIOUS
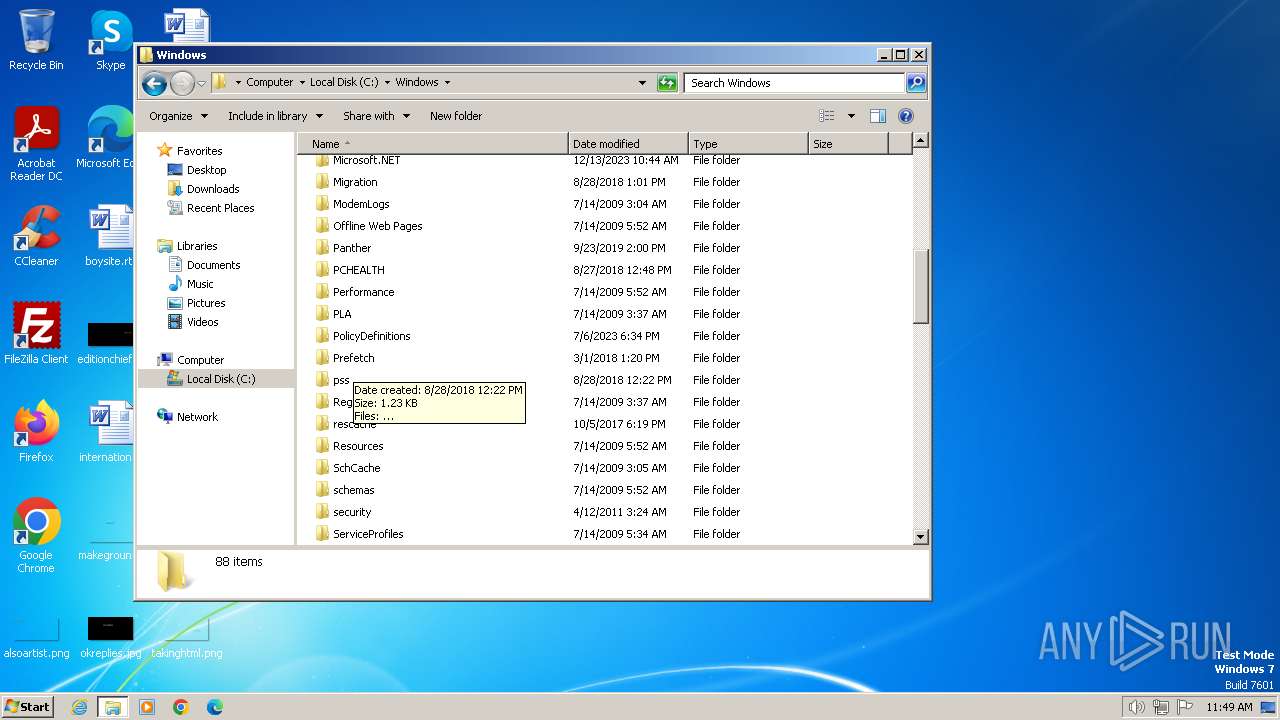
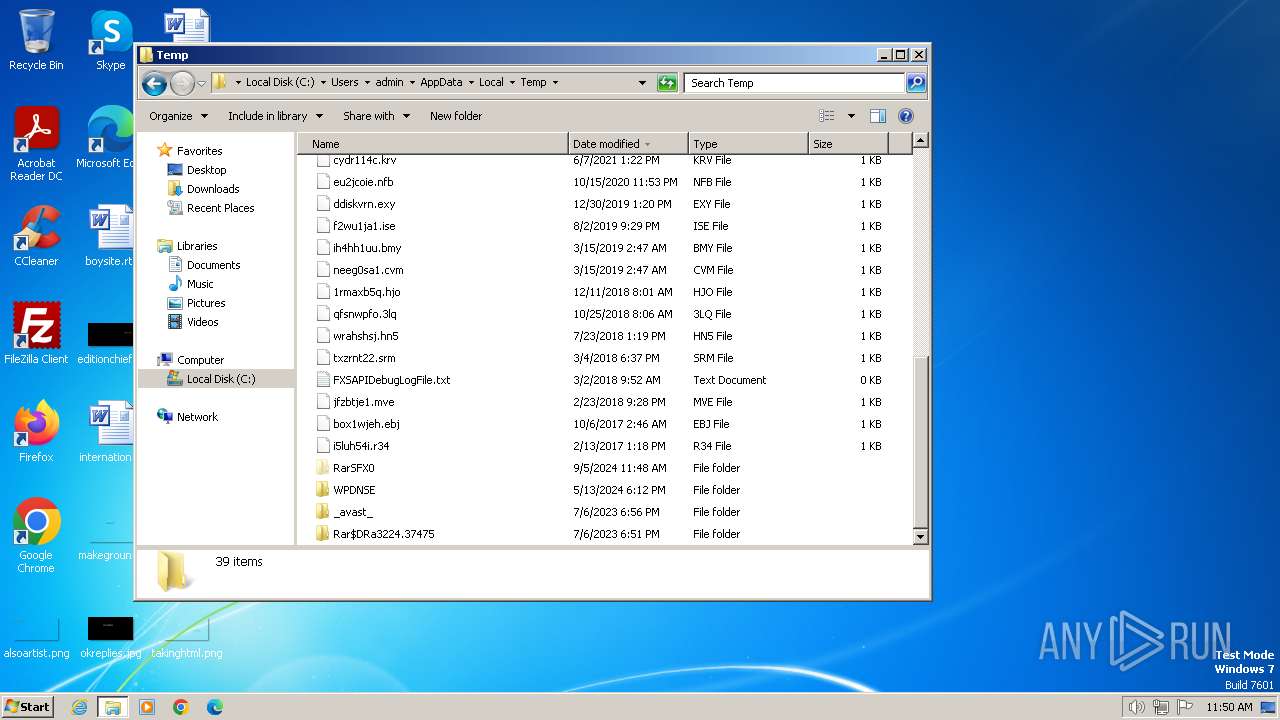
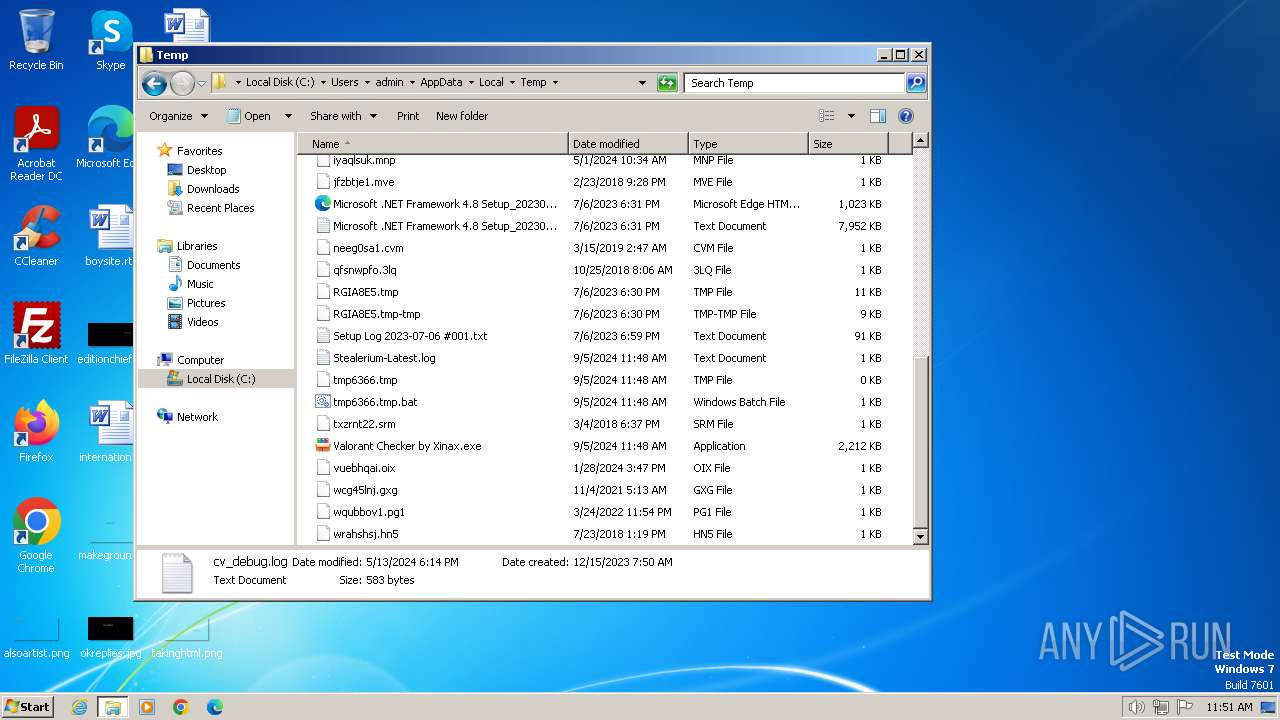
Create files in the Startup directory
- Valorant_Checker by Xinax.exe (PID: 3752)
SUSPICIOUS
Executable content was dropped or overwritten
- Valorant Checker by Xinax.exe (PID: 2396)
- Valorant_Checker by Xinax.exe (PID: 3752)
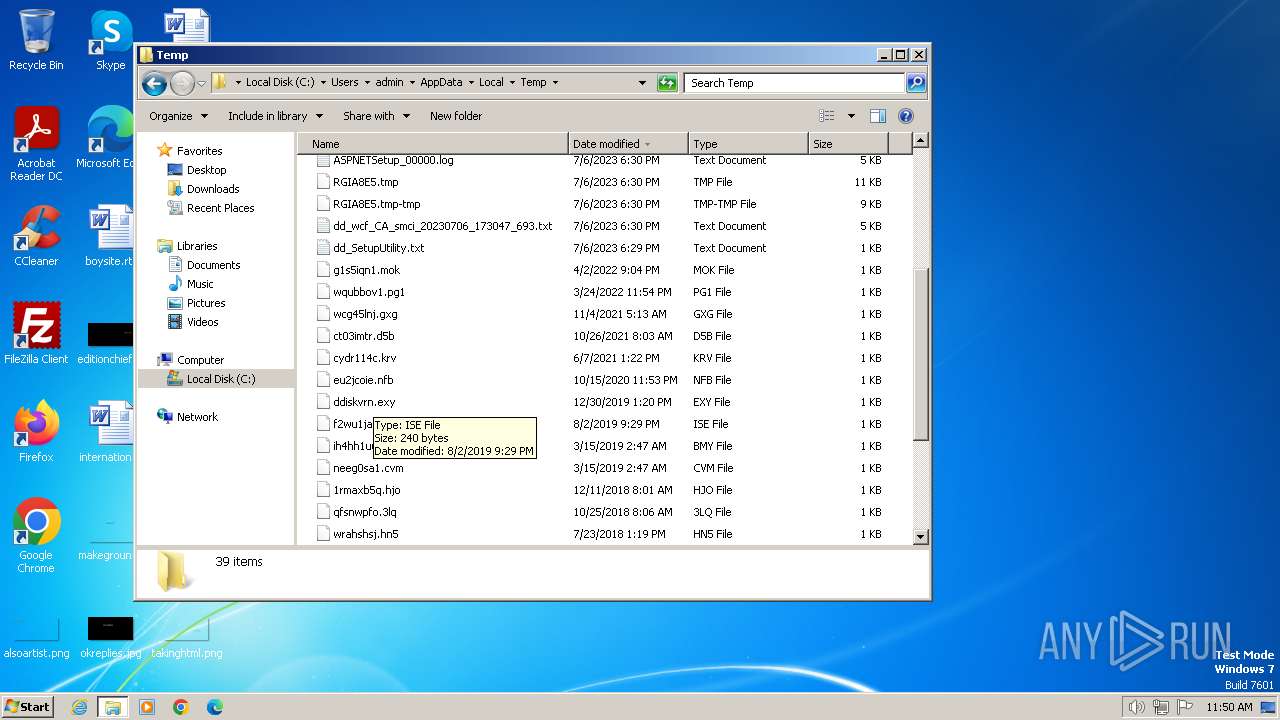
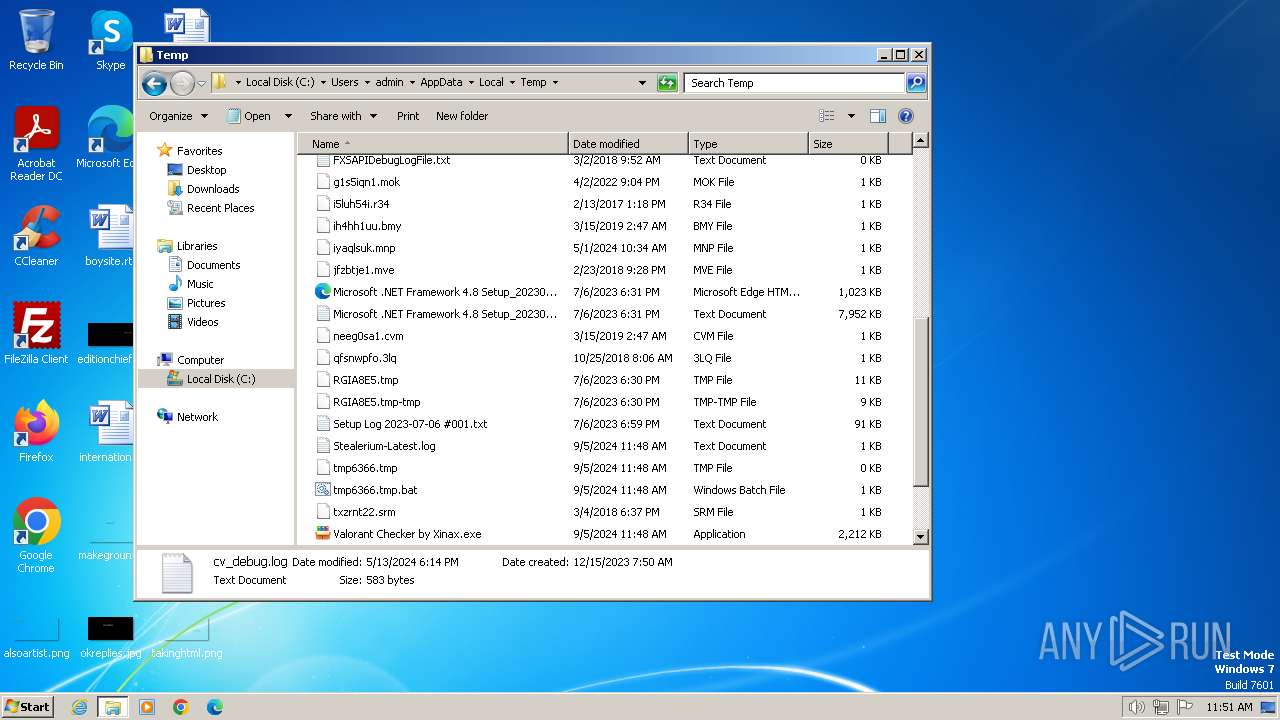
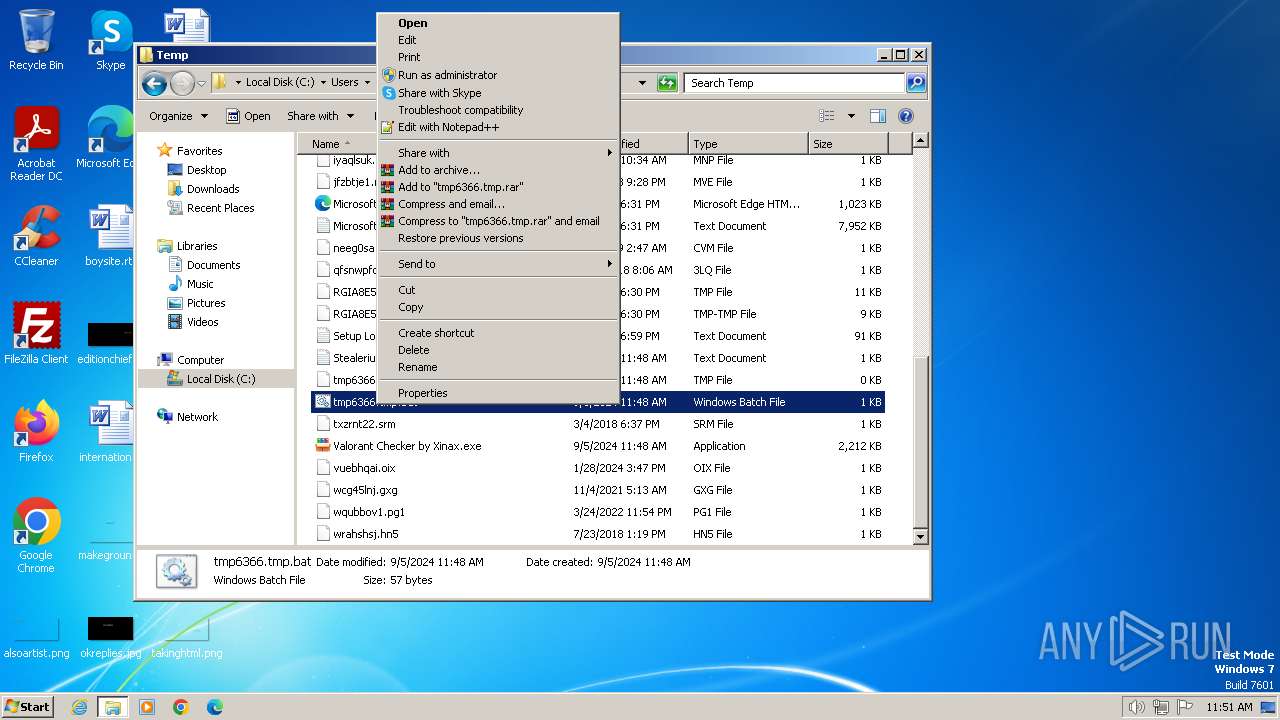
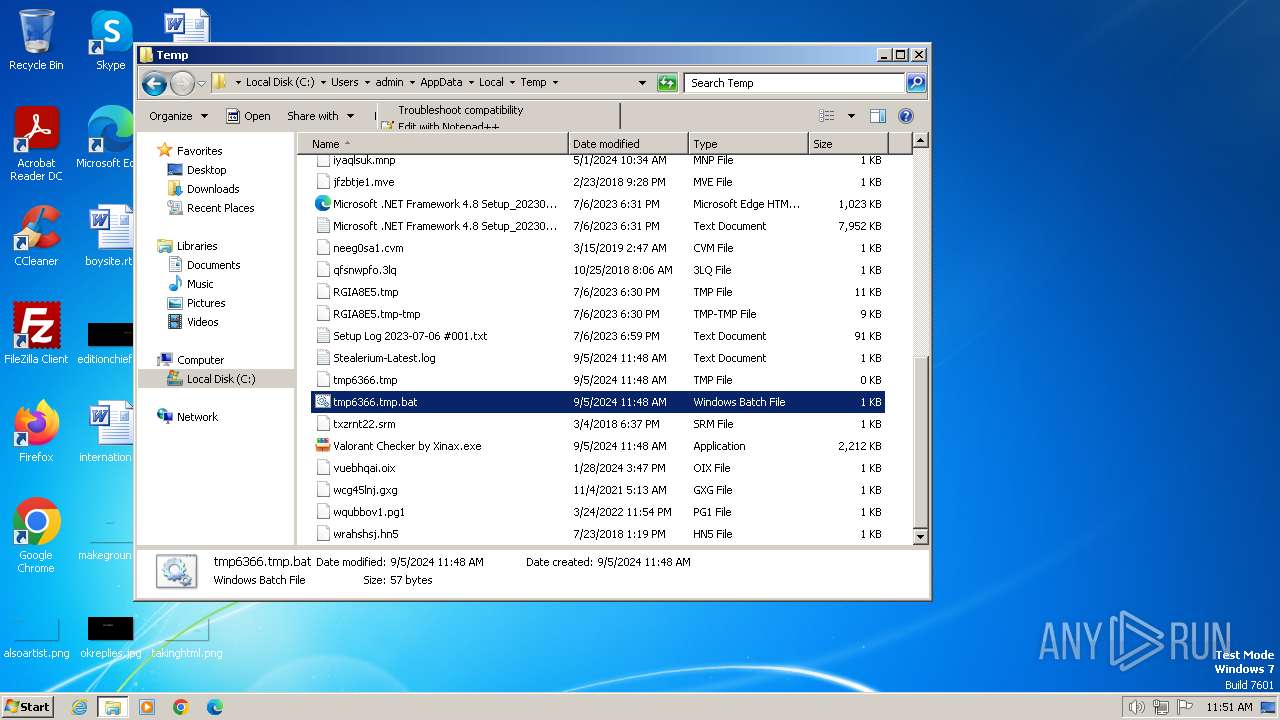
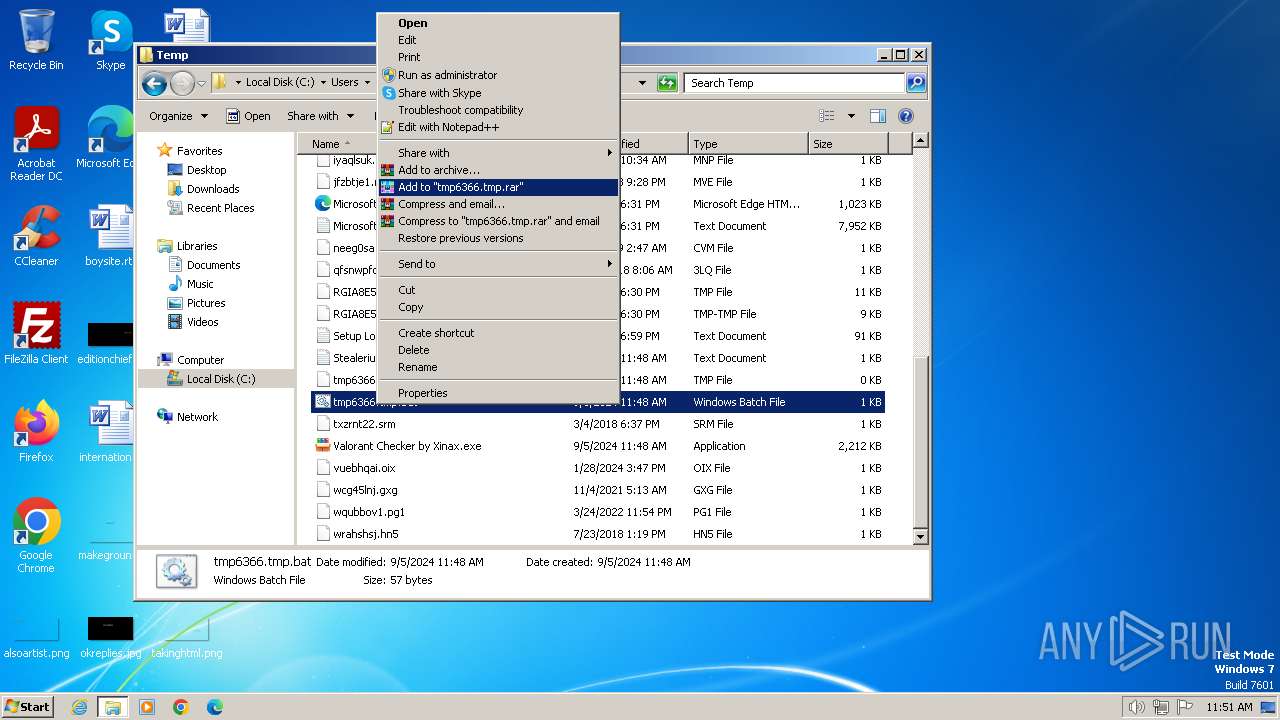
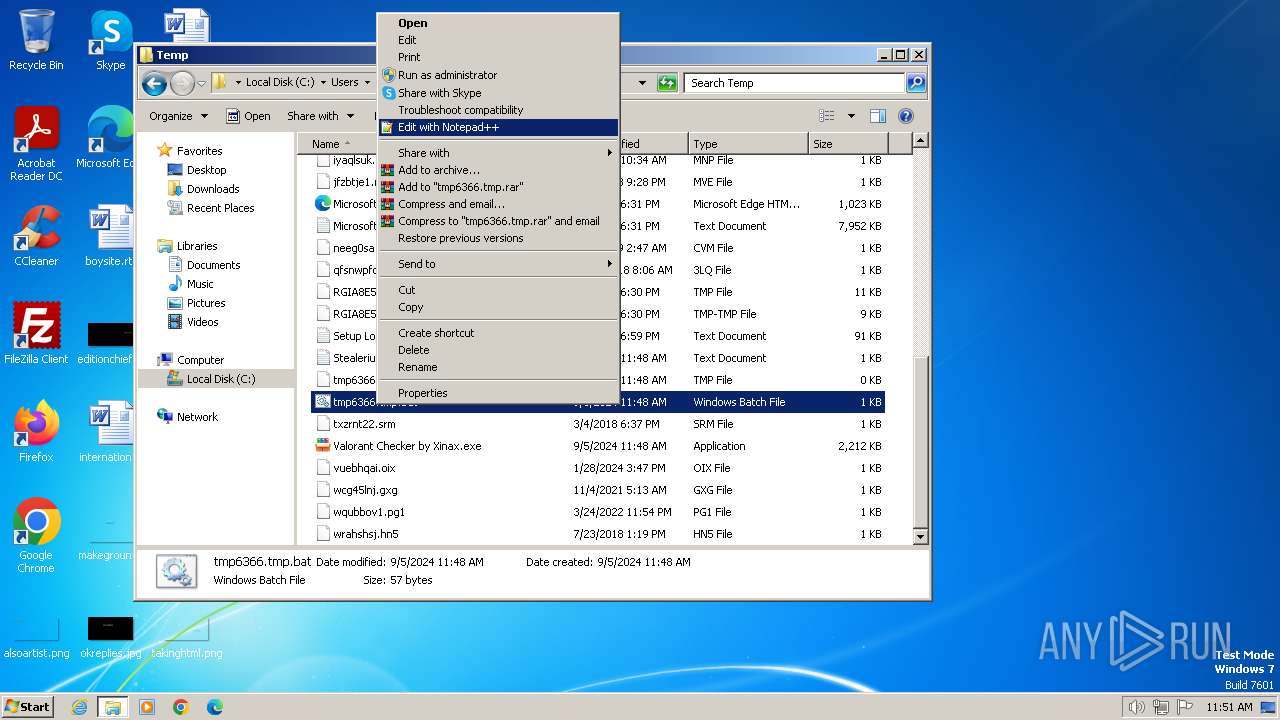
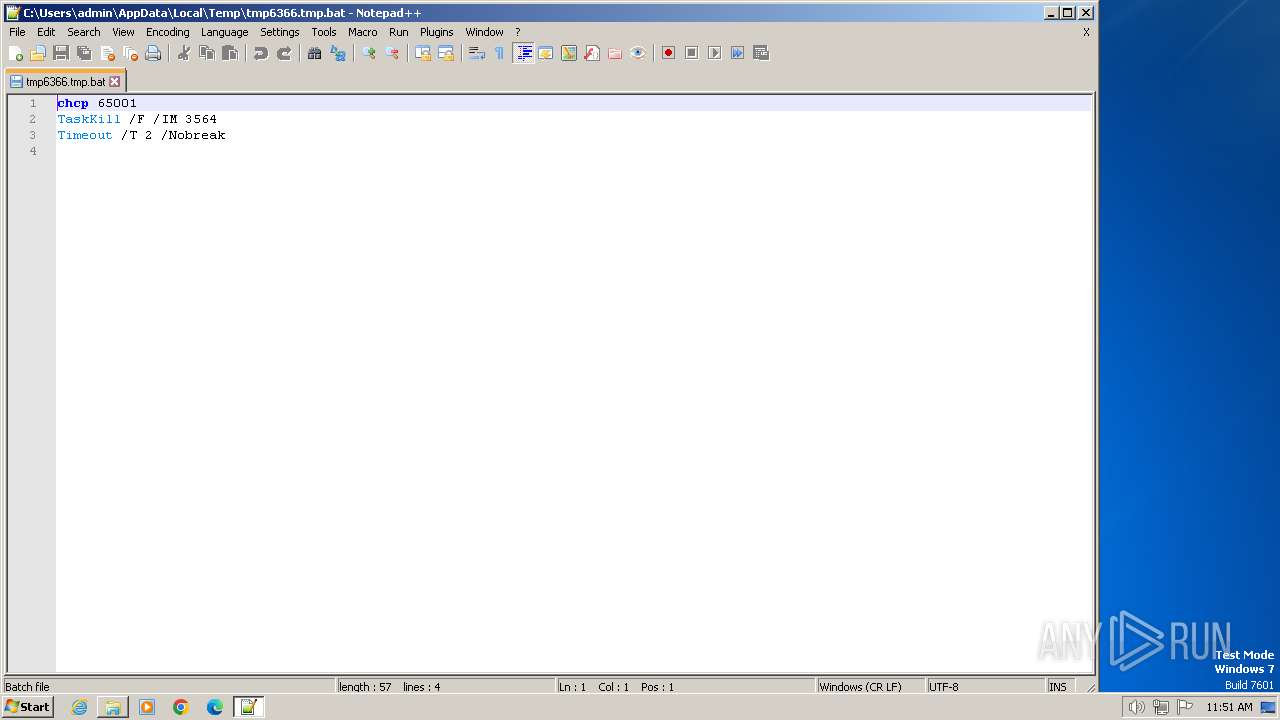
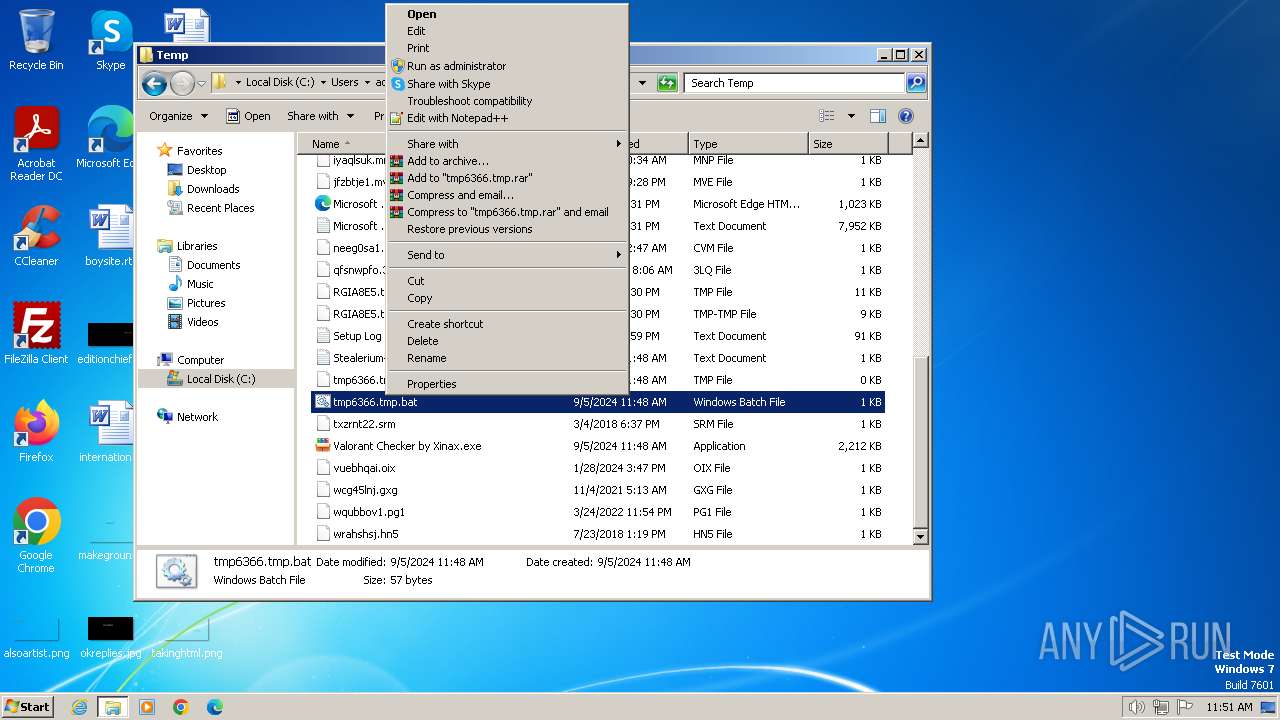
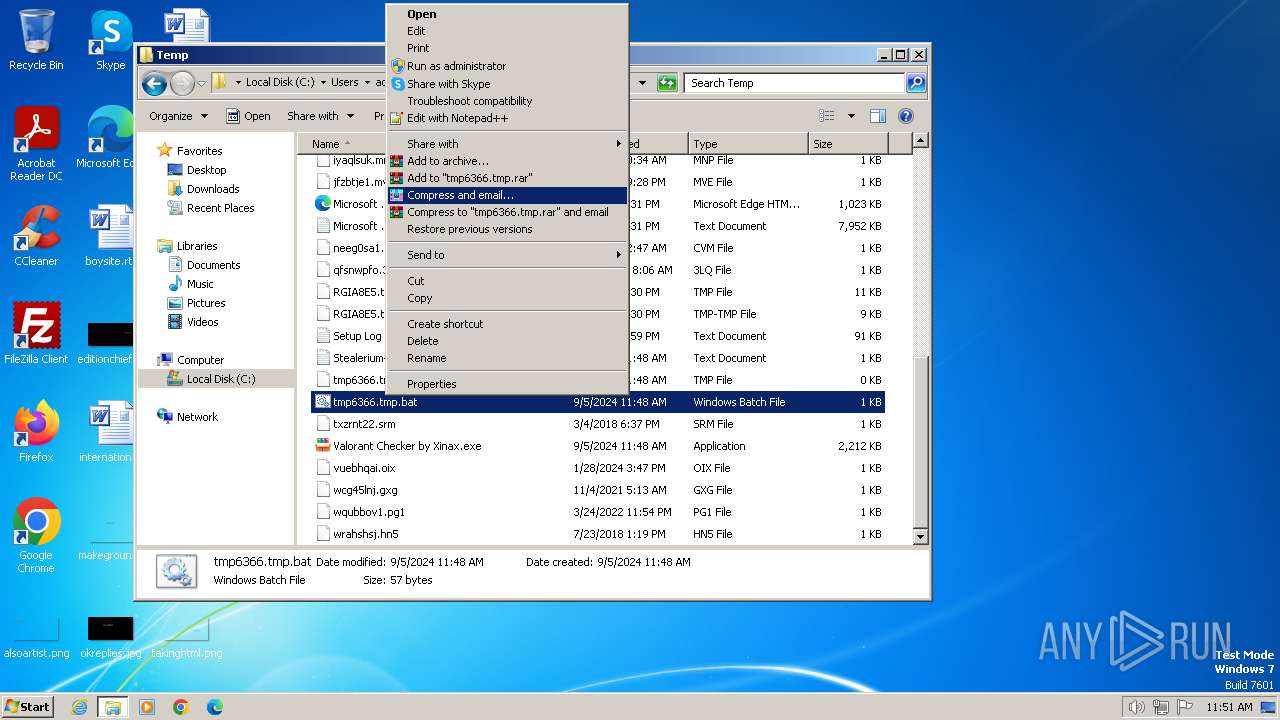
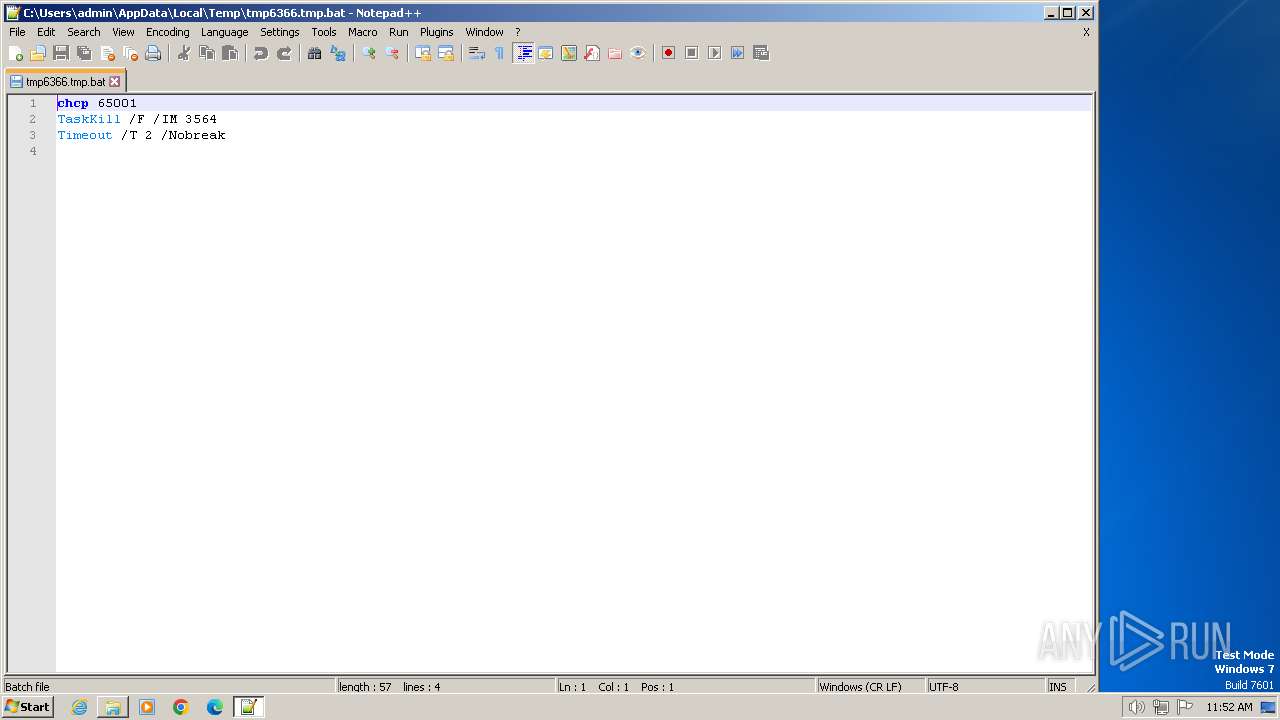
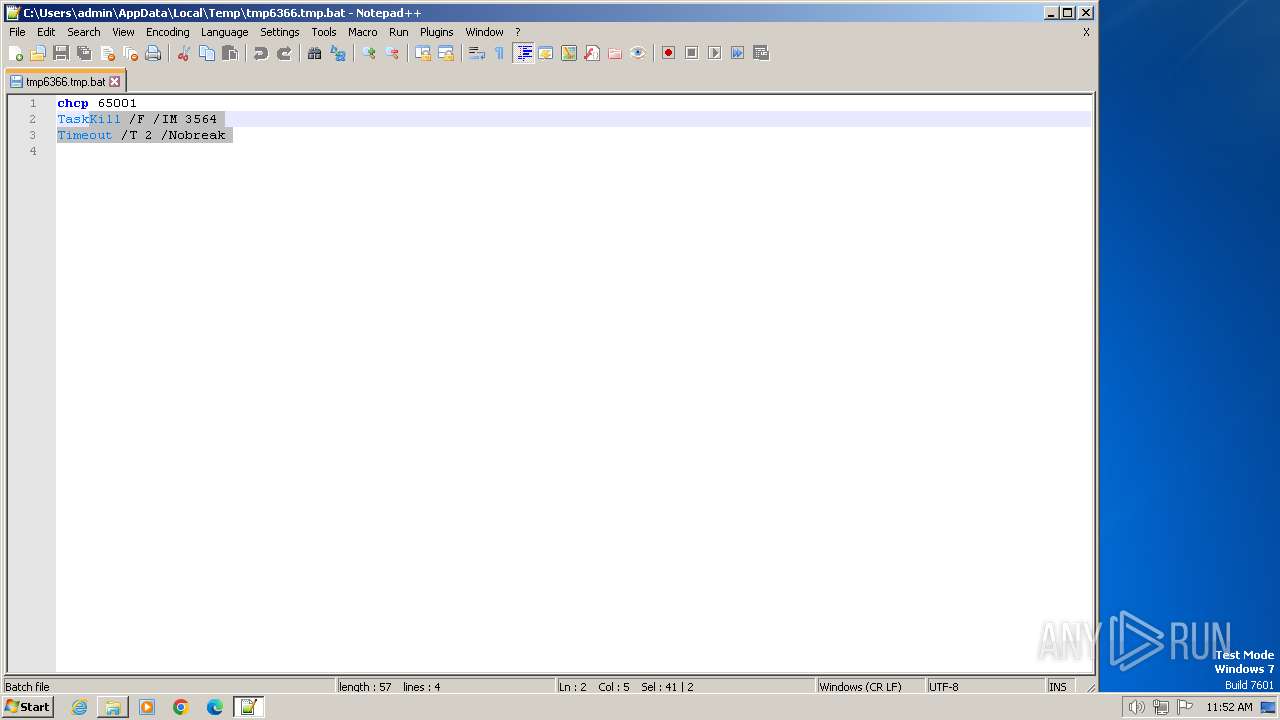
Executing commands from a ".bat" file
- Valorant Checker by Xinax.exe (PID: 3564)
Reads the Internet Settings
- Valorant Checker by Xinax.exe (PID: 2396)
- Valorant Checker by Xinax.exe (PID: 3564)
Reads security settings of Internet Explorer
- Valorant Checker by Xinax.exe (PID: 2396)
- Valorant Checker by Xinax.exe (PID: 3564)
Starts application with an unusual extension
- cmd.exe (PID: 3444)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3444)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 3444)
Starts CMD.EXE for commands execution
- Valorant Checker by Xinax.exe (PID: 3564)
Found regular expressions for crypto-addresses (YARA)
- Valorant_Checker by Xinax.exe (PID: 3752)
Reads settings of System Certificates
- Valorant Checker by Xinax.exe (PID: 3564)
Checks for external IP
- Valorant Checker by Xinax.exe (PID: 3564)
- svchost.exe (PID: 1060)
INFO
Checks supported languages
- Valorant Checker by Xinax.exe (PID: 2396)
- Valorant Checker by Xinax.exe (PID: 3564)
- chcp.com (PID: 1948)
- Valorant_Checker by Xinax.exe (PID: 3752)
- wmpnscfg.exe (PID: 3720)
Reads the computer name
- Valorant Checker by Xinax.exe (PID: 2396)
- Valorant Checker by Xinax.exe (PID: 3564)
- wmpnscfg.exe (PID: 3720)
- Valorant_Checker by Xinax.exe (PID: 3752)
The process uses the downloaded file
- Valorant Checker by Xinax.exe (PID: 2396)
- Valorant Checker by Xinax.exe (PID: 3564)
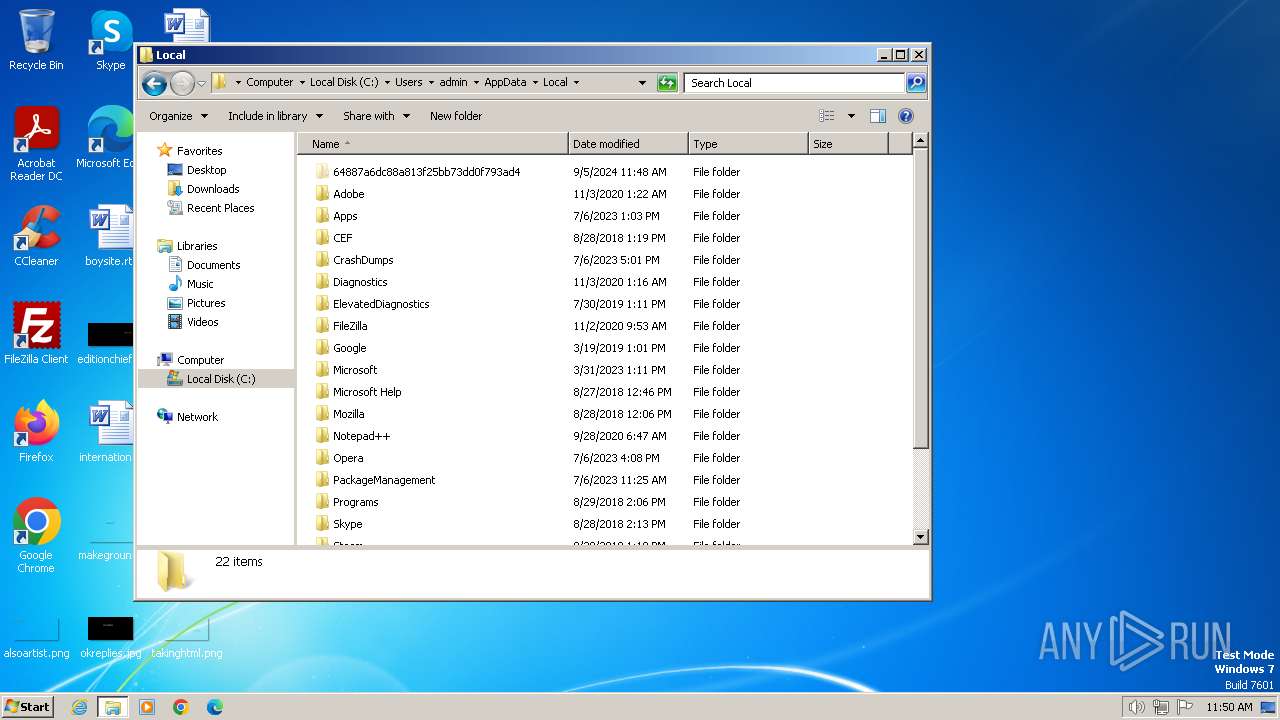
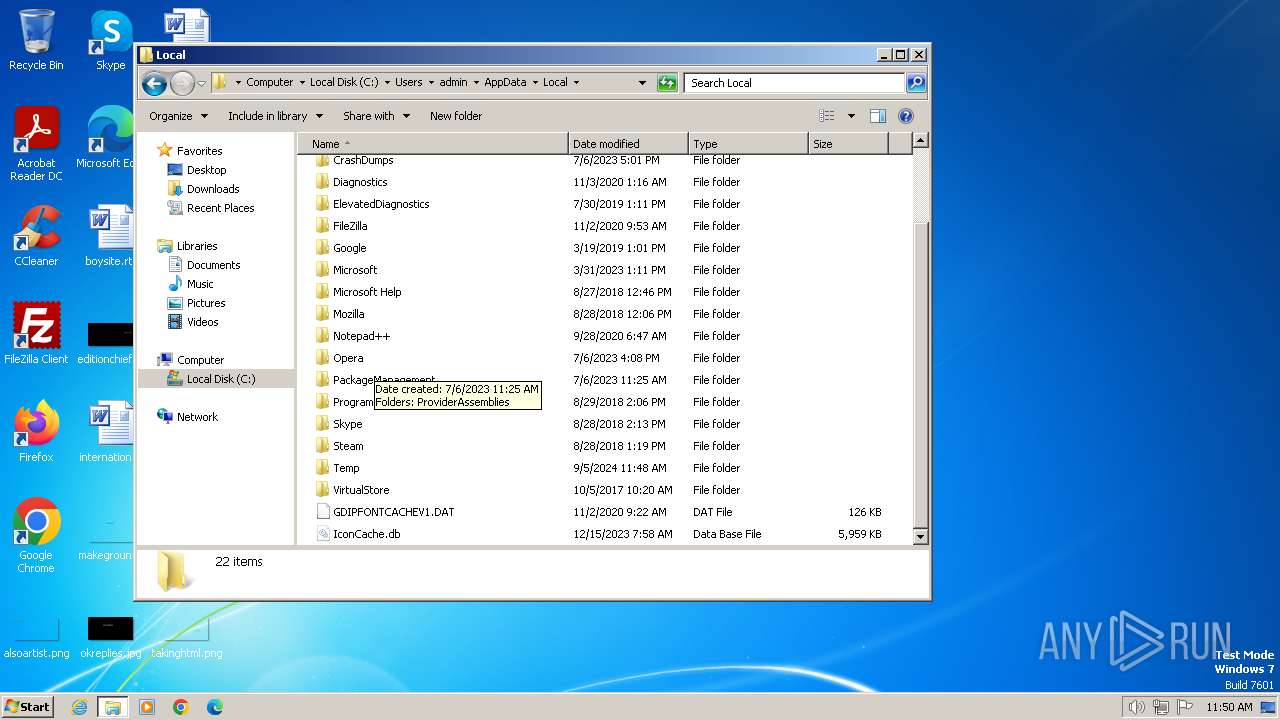
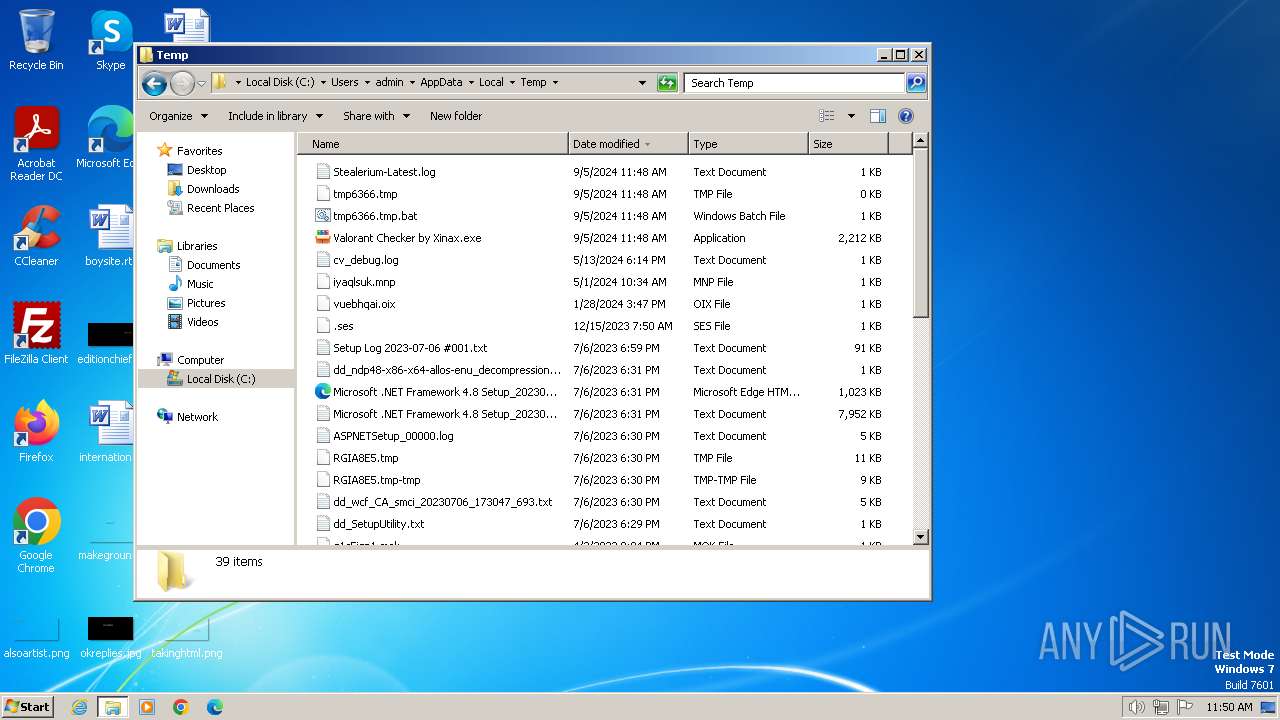
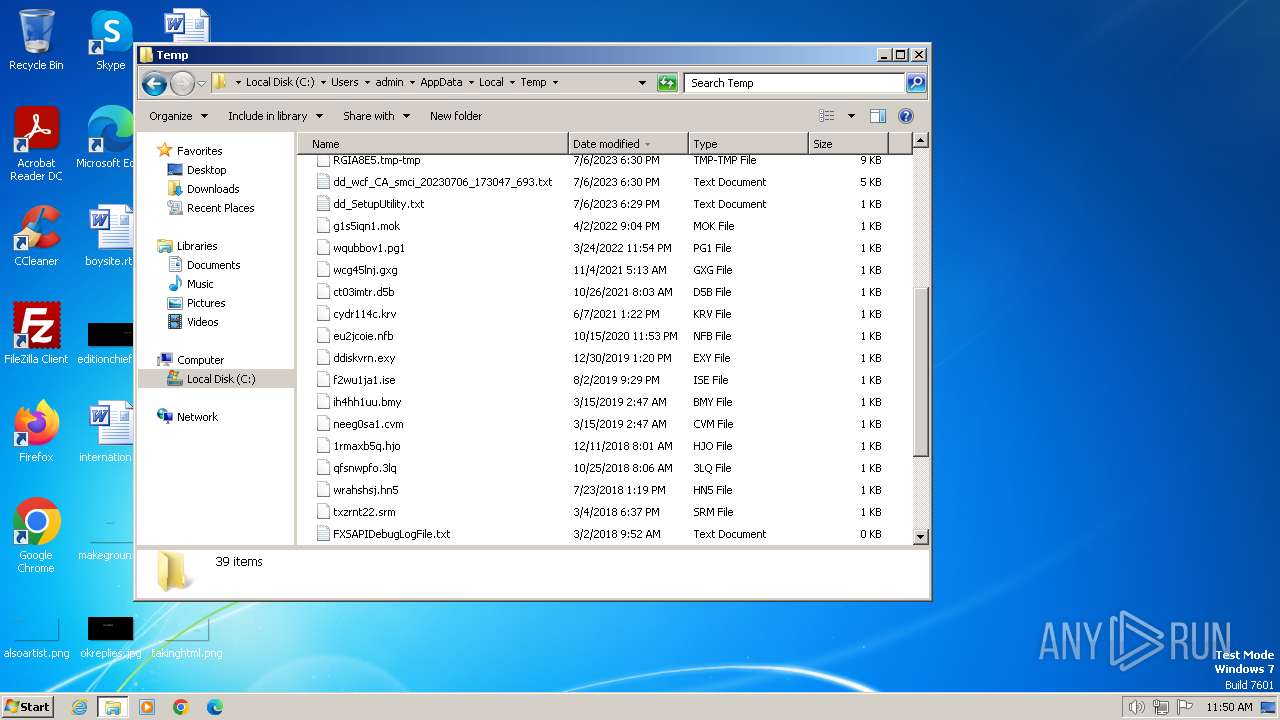
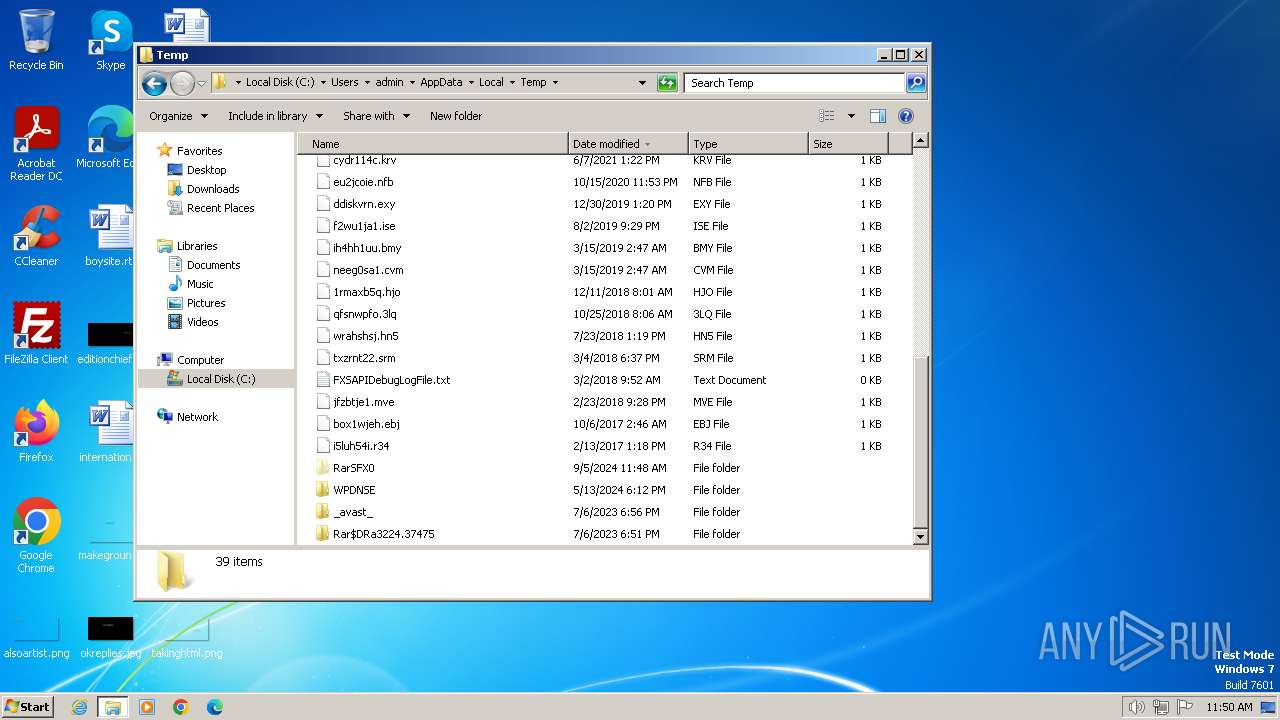
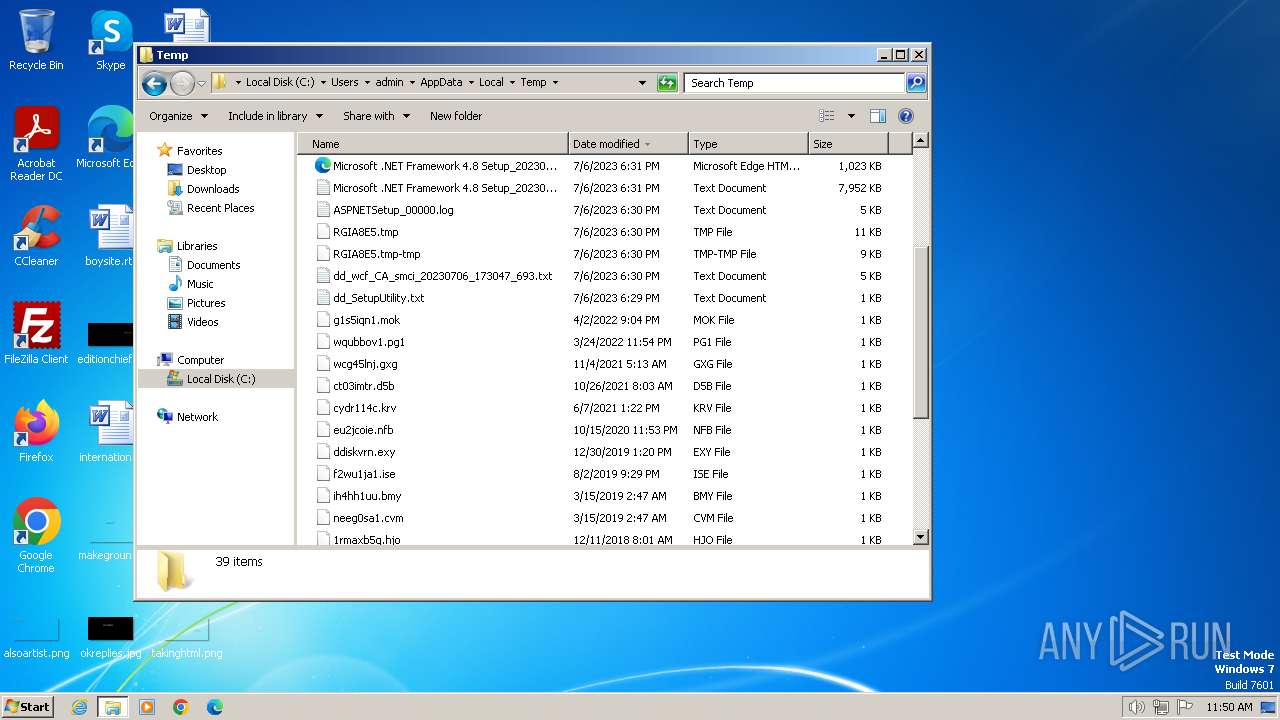
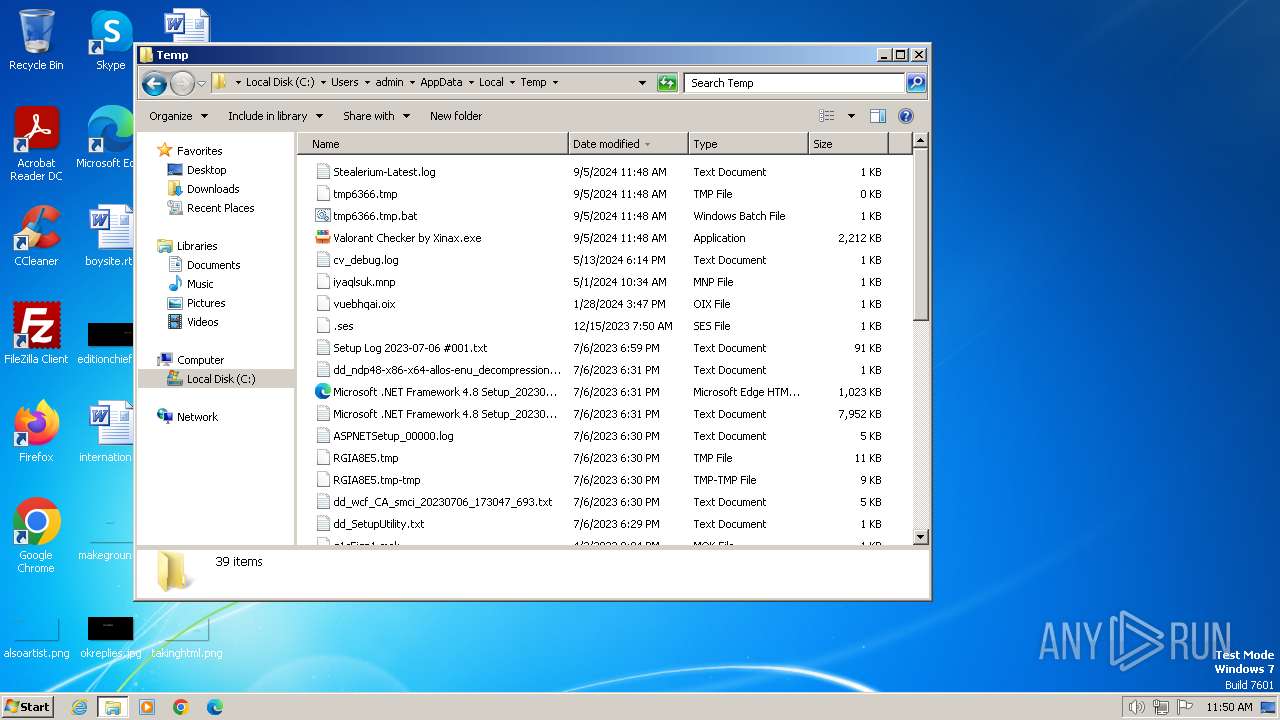
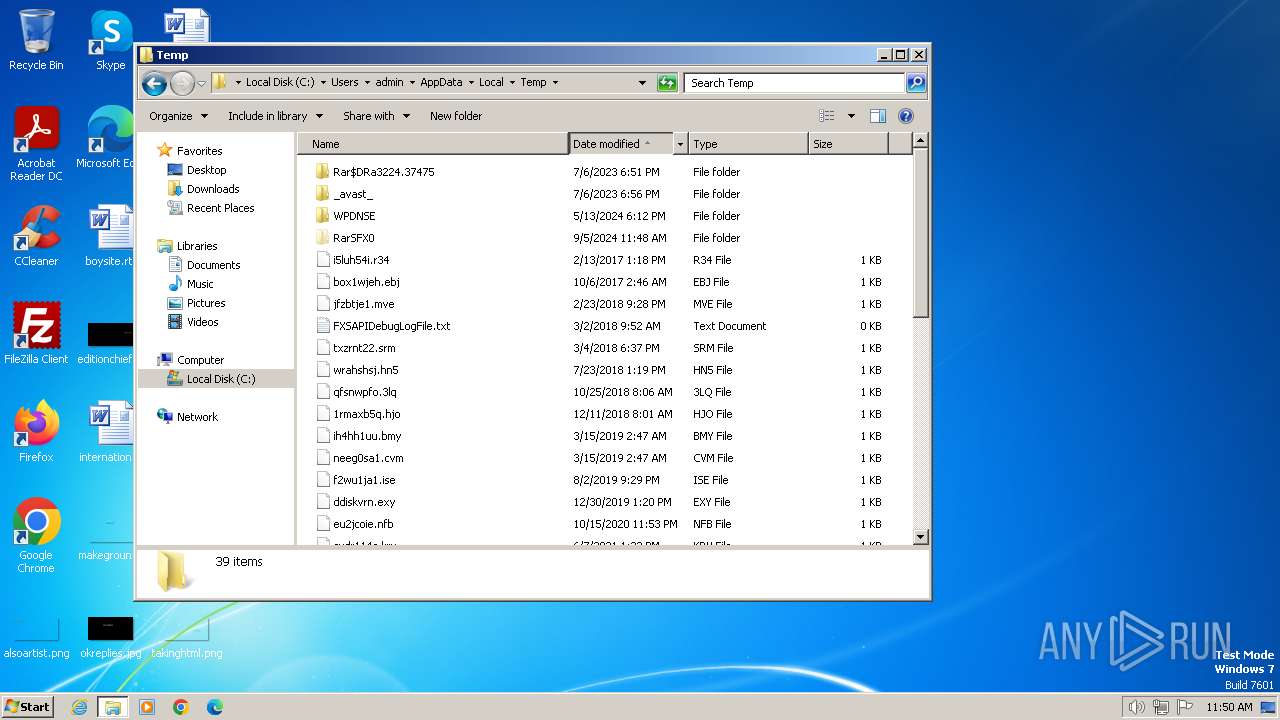
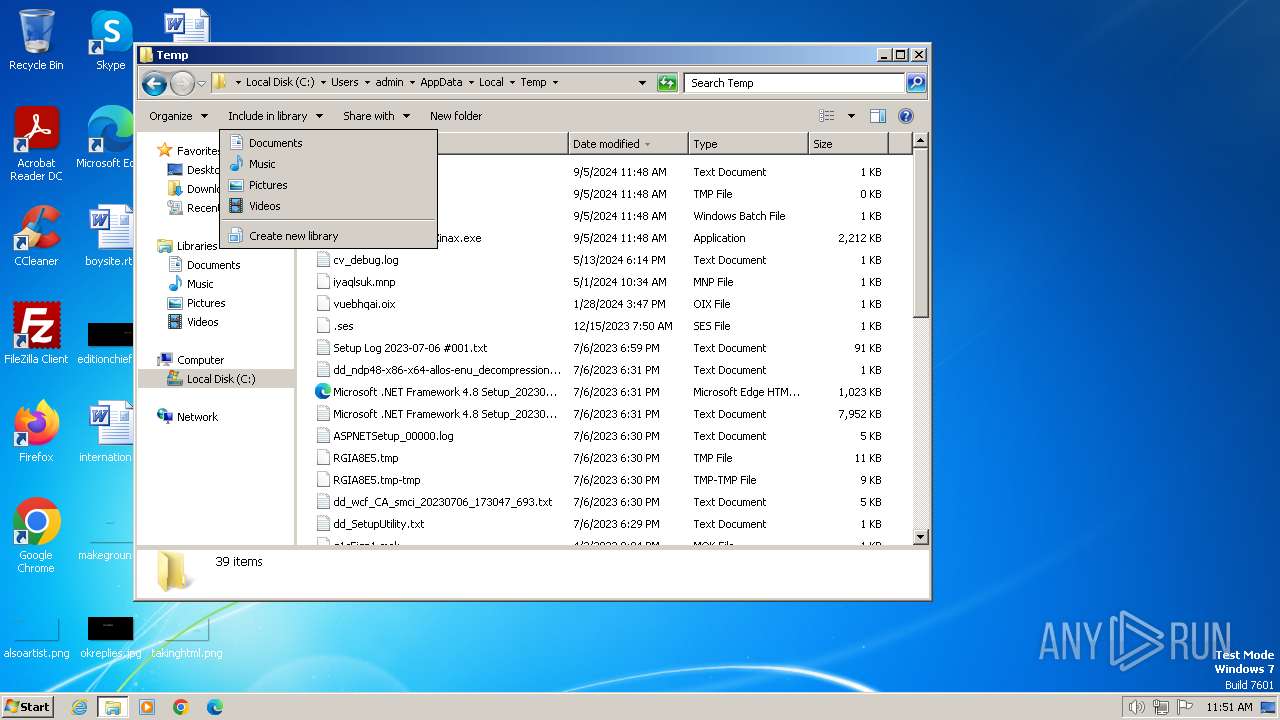
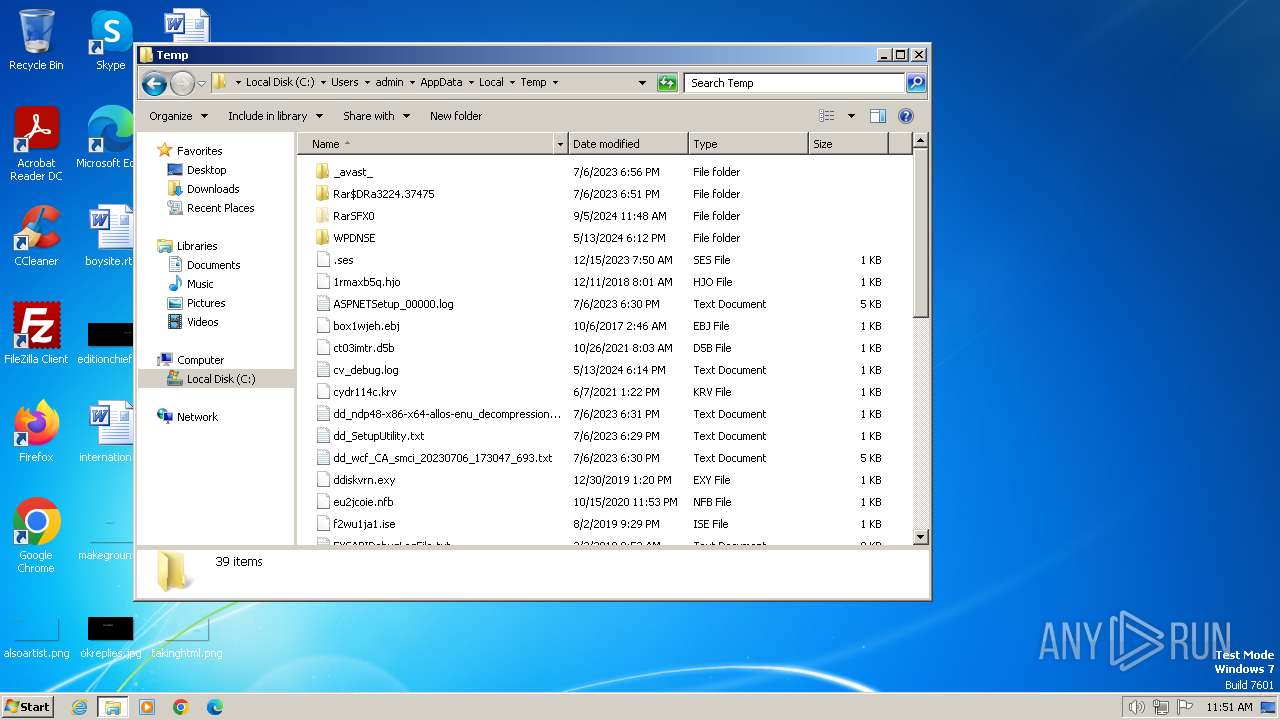
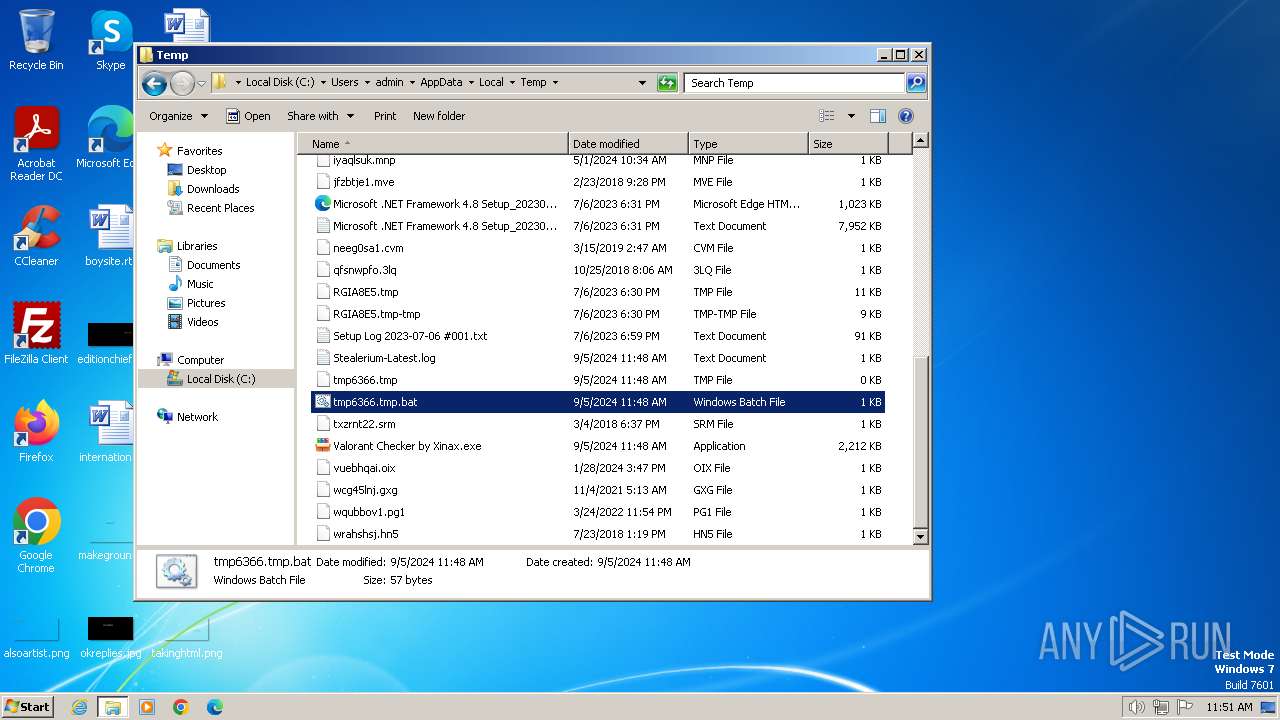
Create files in a temporary directory
- Valorant Checker by Xinax.exe (PID: 2396)
- Valorant Checker by Xinax.exe (PID: 3564)
Reads Environment values
- Valorant Checker by Xinax.exe (PID: 3564)
Reads the machine GUID from the registry
- Valorant Checker by Xinax.exe (PID: 3564)
- Valorant_Checker by Xinax.exe (PID: 3752)
Disables trace logs
- Valorant Checker by Xinax.exe (PID: 3564)
Changes the display of characters in the console
- cmd.exe (PID: 3444)
Attempting to use instant messaging service
- svchost.exe (PID: 1060)
- Valorant Checker by Xinax.exe (PID: 3564)
Manual execution by a user
- wmpnscfg.exe (PID: 3720)
- explorer.exe (PID: 1836)
- notepad++.exe (PID: 2840)
- notepad++.exe (PID: 2716)
.NET Reactor protector has been detected
- Valorant_Checker by Xinax.exe (PID: 3752)
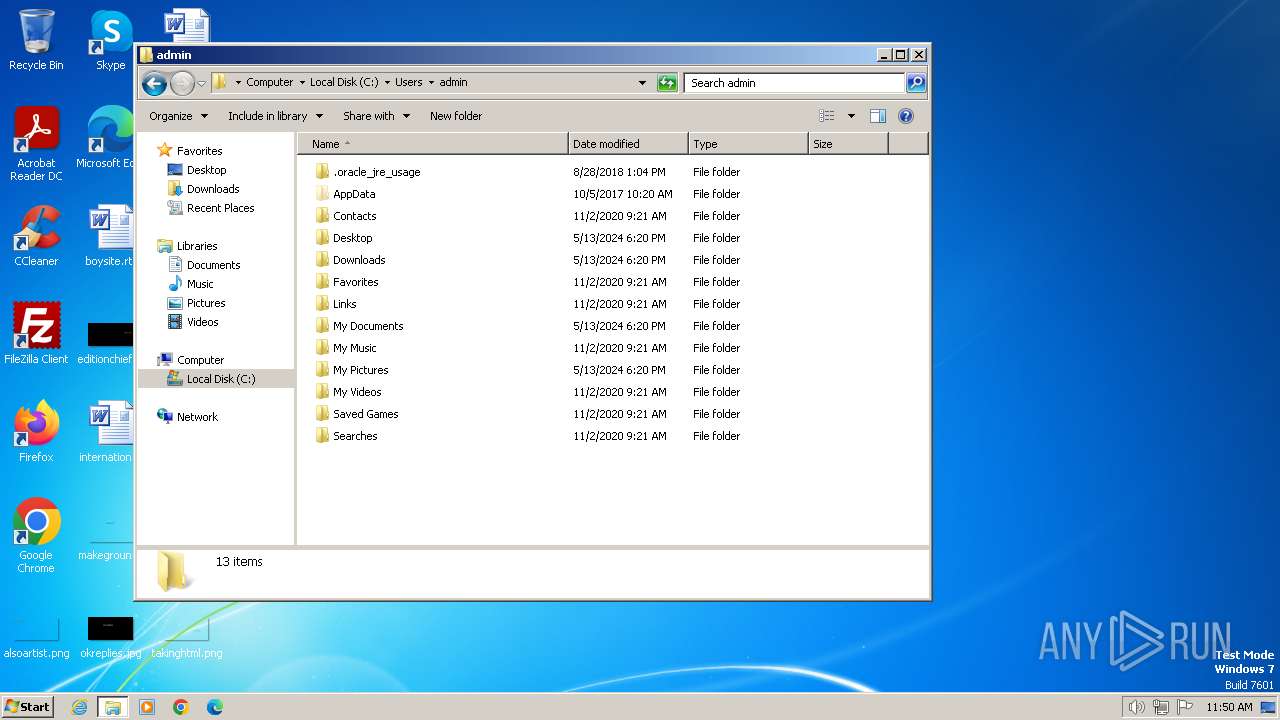
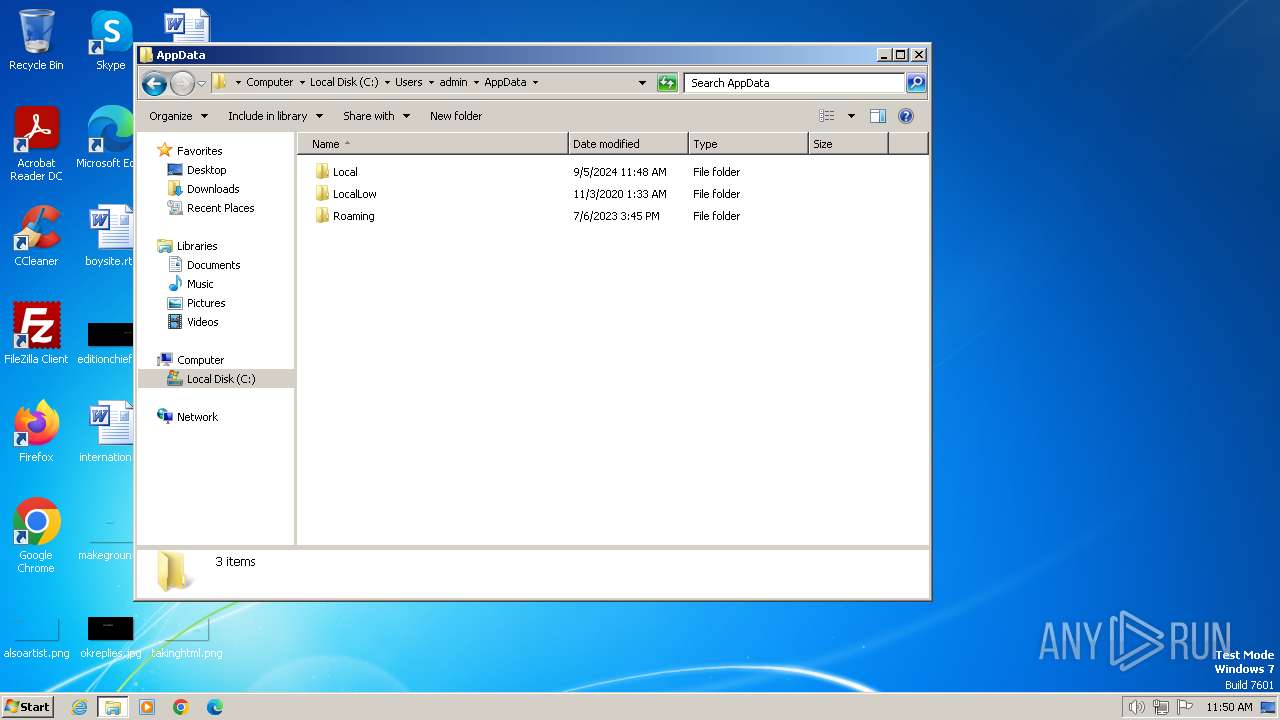
Creates files or folders in the user directory
- Valorant_Checker by Xinax.exe (PID: 3752)
Sends debugging messages
- notepad++.exe (PID: 2716)
- notepad++.exe (PID: 2840)
Reads the software policy settings
- Valorant Checker by Xinax.exe (PID: 3564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:03:03 13:15:57+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.3 |
| CodeSize: | 203776 |
| InitializedDataSize: | 261632 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1f530 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
54
Monitored processes
12
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1060 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1836 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1948 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2396 | "C:\Users\admin\AppData\Local\Temp\Valorant Checker by Xinax.exe" | C:\Users\admin\AppData\Local\Temp\Valorant Checker by Xinax.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 2704 | Timeout /T 2 /Nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2716 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\AppData\Local\Temp\tmp6366.tmp.bat" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Version: 7.91 Modules
| |||||||||||||||
| 2840 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\AppData\Local\Temp\tmp6366.tmp.bat" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 3188 | TaskKill /F /IM 3564 | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3444 | "C:\Windows\System32\cmd.exe" /C C:\Users\admin\AppData\Local\Temp\tmp6366.tmp.bat | C:\Windows\System32\cmd.exe | — | Valorant Checker by Xinax.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3564 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\Valorant Checker by Xinax.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\Valorant Checker by Xinax.exe | Valorant Checker by Xinax.exe | ||||||||||||
User: admin Company: market.eu Integrity Level: MEDIUM Description: market.eu Exit code: 1 Version: 2.5.2.1 Modules
| |||||||||||||||
Total events
4 729
Read events
4 657
Write events
72
Delete events
0
Modification events
| (PID) Process: | (2396) Valorant Checker by Xinax.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2396) Valorant Checker by Xinax.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2396) Valorant Checker by Xinax.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2396) Valorant Checker by Xinax.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3564) Valorant Checker by Xinax.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3564) Valorant Checker by Xinax.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Valorant Checker by Xinax_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3564) Valorant Checker by Xinax.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Valorant Checker by Xinax_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3564) Valorant Checker by Xinax.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Valorant Checker by Xinax_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (3564) Valorant Checker by Xinax.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Valorant Checker by Xinax_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (3564) Valorant Checker by Xinax.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Valorant Checker by Xinax_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
3
Suspicious files
5
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3564 | Valorant Checker by Xinax.exe | C:\Users\admin\AppData\Local\Temp\Stealerium-Latest.log | text | |
MD5:1AC47A28CABC6B7B63A8C78C0DB4C1C3 | SHA256:4515D5487CE70CDA38DE9ADE119E29992BD27F362D5DC046B804A0BC2EB50032 | |||
| 1060 | svchost.exe | C:\Windows\ServiceProfiles\NetworkService\AppData\Local\Temp\CabE116.tmp | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 1060 | svchost.exe | C:\Windows\ServiceProfiles\NetworkService\AppData\Local\Temp\Cab6AEA.tmp | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 1060 | svchost.exe | C:\Windows\ServiceProfiles\NetworkService\AppData\Local\Temp\TarE117.tmp | cat | |
MD5:78785956AB4E54D6116D673C3491EDFF | SHA256:C514DBDBB13632CBB378C59086C1EBB0BC9B25FFB0A349F2B052B065C0D913E6 | |||
| 2840 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\session.xml | text | |
MD5:B603A402B507AB791AAF84AB98FA0047 | SHA256:B7092CE91B45904646D9C16E475BD3DCF8E14DBCBE03CBE97905E6BF55BC06B2 | |||
| 3564 | Valorant Checker by Xinax.exe | C:\Users\admin\AppData\Local\Temp\tmp6366.tmp.bat | text | |
MD5:A49889A32BE1367A3C3F13DF4D002394 | SHA256:131B2C2B6FF853FB737F0FB9B510AABF818030A7E822B6216BB1731CED9A6C55 | |||
| 1060 | svchost.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:80A9DB962B7BFBA2C80FA179E74C7B96 | SHA256:9C87D1869F7A048BCBBC777564CA508AA6B2BD24A072CA854A53A92DABB5D177 | |||
| 2396 | Valorant Checker by Xinax.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Valorant Checker by Xinax.exe | executable | |
MD5:5989BAA8CB04CA6BA45E71744937D96C | SHA256:FE9004DC4EAB9BB39F2D66DE153863EC5B097993DECBA65EEC005093CD839C62 | |||
| 2396 | Valorant Checker by Xinax.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Valorant_Checker by Xinax.exe | executable | |
MD5:9AC1D433D1648B9AC8D90A1B13A938FE | SHA256:24E15BCECDEF5DE18450AD9274701D119212FA6DB1F848F686950107EB524AD0 | |||
| 3752 | Valorant_Checker by Xinax.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\svhost64.exe | executable | |
MD5:9AC1D433D1648B9AC8D90A1B13A938FE | SHA256:24E15BCECDEF5DE18450AD9274701D119212FA6DB1F848F686950107EB524AD0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
14
DNS requests
8
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3564 | Valorant Checker by Xinax.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | shared |
1372 | svchost.exe | GET | 304 | 23.50.131.200:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | whitelisted |
1060 | svchost.exe | GET | 304 | 23.50.131.200:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?67a3611ec3c0260d | unknown | — | — | whitelisted |
1372 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 239.255.255.250:3702 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
1372 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
3564 | Valorant Checker by Xinax.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | shared |
3564 | Valorant Checker by Xinax.exe | 162.159.128.233:443 | discord.com | CLOUDFLARENET | — | whitelisted |
1372 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1372 | svchost.exe | 23.50.131.200:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
ip-api.com |
| shared |
discord.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
3564 | Valorant Checker by Xinax.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
3564 | Valorant Checker by Xinax.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
1060 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
1060 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
3564 | Valorant Checker by Xinax.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\plugins\Config\nppPluginList.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|