| URL: | https://www.eventbrite.com/organizations/missive/activity/redirect/?p=ABIdvVvMqADWbJv9oP8KjnlpYPGb8zdmWGV8I_UGq7gq1-F54V8AjqXrj1e2X1RoA4UPRbL1cc32lkkCja7eyQp0H0oEC6pIrH58rXk_9MP0mCtUOT6nhdY5jIx7KTlnSnzrLwW6mSfdhmPcYveGDxEXE0es9H2R4yY6PhlmuP_tpjHblhzUgXrcBx2VoEa7_9IOpagcErmeDK_sCGC1SYkixA7iiXL6dtga5O3ChljoYXV2hSSeeMONgOisx6ZUgyRkRuVSB4lXsNY8Yj1sxloa6PzZEJqJwfYiSYmz5ACyzS9vp73mhzuMBpaiKnmRlLi9tNhfLNDFNfRGewV1xxhTc7E8sZNlXWNaZct35vtWUVqgoT7XswShbGe64nz0PnVdpTK0qw0XDqjGam7-yWo84kbHXibbkbciydCssx6-n-tKk0xFzDFnOUr99HEONd9CLYrU_83SsdAiqcEB9MU-iGtNGSRWNG7EC3KnYZh7aqlTfZHHsVL7YJEvbKamCs0kec3gIhkuucHynwXsyRc8EOKwRI5cARxLRwHT02-eOaTVMkT0flmnfujxZ0tnD5DWaRdxasPH&eid=339765948097&c=6478209&co=1133217599&t=e__;!!KEc8uF_xo8-al5zF!B6j9cWg0ByOE4MxHcfjo1MhfK7tcocf9JzcI0WiSFMdXci1QaOfLxSx5qz6WNwaM$ |
| Full analysis: | https://app.any.run/tasks/cad30c45-4125-46ff-905b-18b32f27fa38 |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2022, 10:24:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E591A78703B3623893E1E7916583A656 |
| SHA1: | FAD217DB8A4933D17AA6B46494B84AF09BC16F9F |
| SHA256: | 99F154555EFE327AFF7BBE549E80C4FBFAF9BBABE516EC970E03E0D0B3B160CE |
| SSDEEP: | 12:27MYJ1v+xks6893qt94TErc7HL6UXkByey5fMN9FBZ27rJit9IDt+kpeYUmg7eD:27MYJ1v+O89394aGvgJ5fMN5ckXkXZ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2980)
Checks supported languages
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2980)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2980)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3832)
Reads the computer name
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2980)
INFO
Checks supported languages
- iexplore.exe (PID: 3832)
- iexplore.exe (PID: 2924)
Reads the computer name
- iexplore.exe (PID: 2924)
- iexplore.exe (PID: 3832)
Changes internet zones settings
- iexplore.exe (PID: 2924)
Application launched itself
- iexplore.exe (PID: 2924)
Reads settings of System Certificates
- iexplore.exe (PID: 3832)
- iexplore.exe (PID: 2924)
Checks Windows Trust Settings
- iexplore.exe (PID: 2924)
- iexplore.exe (PID: 3832)
Reads CPU info
- iexplore.exe (PID: 3832)
Reads internet explorer settings
- iexplore.exe (PID: 3832)
Creates files in the user directory
- iexplore.exe (PID: 3832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2924 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.eventbrite.com/organizations/missive/activity/redirect/?p=ABIdvVvMqADWbJv9oP8KjnlpYPGb8zdmWGV8I_UGq7gq1-F54V8AjqXrj1e2X1RoA4UPRbL1cc32lkkCja7eyQp0H0oEC6pIrH58rXk_9MP0mCtUOT6nhdY5jIx7KTlnSnzrLwW6mSfdhmPcYveGDxEXE0es9H2R4yY6PhlmuP_tpjHblhzUgXrcBx2VoEa7_9IOpagcErmeDK_sCGC1SYkixA7iiXL6dtga5O3ChljoYXV2hSSeeMONgOisx6ZUgyRkRuVSB4lXsNY8Yj1sxloa6PzZEJqJwfYiSYmz5ACyzS9vp73mhzuMBpaiKnmRlLi9tNhfLNDFNfRGewV1xxhTc7E8sZNlXWNaZct35vtWUVqgoT7XswShbGe64nz0PnVdpTK0qw0XDqjGam7-yWo84kbHXibbkbciydCssx6-n-tKk0xFzDFnOUr99HEONd9CLYrU_83SsdAiqcEB9MU-iGtNGSRWNG7EC3KnYZh7aqlTfZHHsVL7YJEvbKamCs0kec3gIhkuucHynwXsyRc8EOKwRI5cARxLRwHT02-eOaTVMkT0flmnfujxZ0tnD5DWaRdxasPH&eid=339765948097&c=6478209&co=1133217599&t=e__;!!KEc8uF_xo8-al5zF!B6j9cWg0ByOE4MxHcfjo1MhfK7tcocf9JzcI0WiSFMdXci1QaOfLxSx5qz6WNwaMf7f81a39-5f63-5b42-9efd-1f13b5431005quot; | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2980 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
| 3832 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2924 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
20 863
Read events
20 737
Write events
126
Delete events
0
Modification events
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30960892 | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 295615922 | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30960893 | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
21
Text files
100
Unknown types
57
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3832 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3832 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | der | |
MD5:— | SHA256:— | |||
| 3832 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E573CDF4C6D731D56A665145182FD759_6070720F7A4B9D1E4F72D90EF4FFB3A9 | binary | |
MD5:— | SHA256:— | |||
| 3832 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\KC4DDKR5.txt | text | |
MD5:— | SHA256:— | |||
| 3832 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E573CDF4C6D731D56A665145182FD759_6070720F7A4B9D1E4F72D90EF4FFB3A9 | der | |
MD5:— | SHA256:— | |||
| 3832 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\G77T5QV3.txt | text | |
MD5:— | SHA256:— | |||
| 3832 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:— | SHA256:— | |||
| 3832 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\1E2HJO4P.txt | text | |
MD5:— | SHA256:— | |||
| 3832 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\DBYEOURF.txt | text | |
MD5:— | SHA256:— | |||
| 3832 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\F3FID5GQ.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
70
DNS requests
31
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3832 | iexplore.exe | GET | — | 142.250.186.67:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDwQ9JNOs3IcArkp%2FBu7NbU | US | — | — | whitelisted |
3832 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
3832 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHr7M35ZTSPHb9t8TGKb2tY%3D | US | der | 1.40 Kb | whitelisted |
3832 | iexplore.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEG3aTvFLTYzNCmxS2fUJutw%3D | US | der | 471 b | whitelisted |
3832 | iexplore.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEFsL8ccV6MRJElibH7RYju4%3D | US | der | 471 b | whitelisted |
3832 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHophRq39F1meVBmQbb%2F1x0%3D | US | der | 1.40 Kb | whitelisted |
3832 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAZa%2F8PboiqWHhthMXi1fss%3D | US | der | 471 b | whitelisted |
3832 | iexplore.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3832 | iexplore.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2924 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3832 | iexplore.exe | 18.235.224.167:443 | www.eventbrite.com | — | US | suspicious |
3832 | iexplore.exe | 18.215.76.51:443 | www.eventbrite.com | — | US | unknown |
3832 | iexplore.exe | 23.216.77.69:80 | ctldl.windowsupdate.com | NTT DOCOMO, INC. | US | suspicious |
3832 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3832 | iexplore.exe | 151.101.2.110:443 | cdn.evbstatic.com | Fastly | US | suspicious |
3832 | iexplore.exe | 151.101.1.169:443 | img.evbuc.com | Fastly | US | unknown |
3832 | iexplore.exe | 142.250.186.164:443 | www.google.com | Google Inc. | US | whitelisted |
3832 | iexplore.exe | 151.101.66.217:443 | browser.sentry-cdn.com | Fastly | US | suspicious |
3832 | iexplore.exe | 104.18.20.226:80 | ocsp2.globalsign.com | Cloudflare Inc | US | shared |
3832 | iexplore.exe | 142.250.186.67:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.eventbrite.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
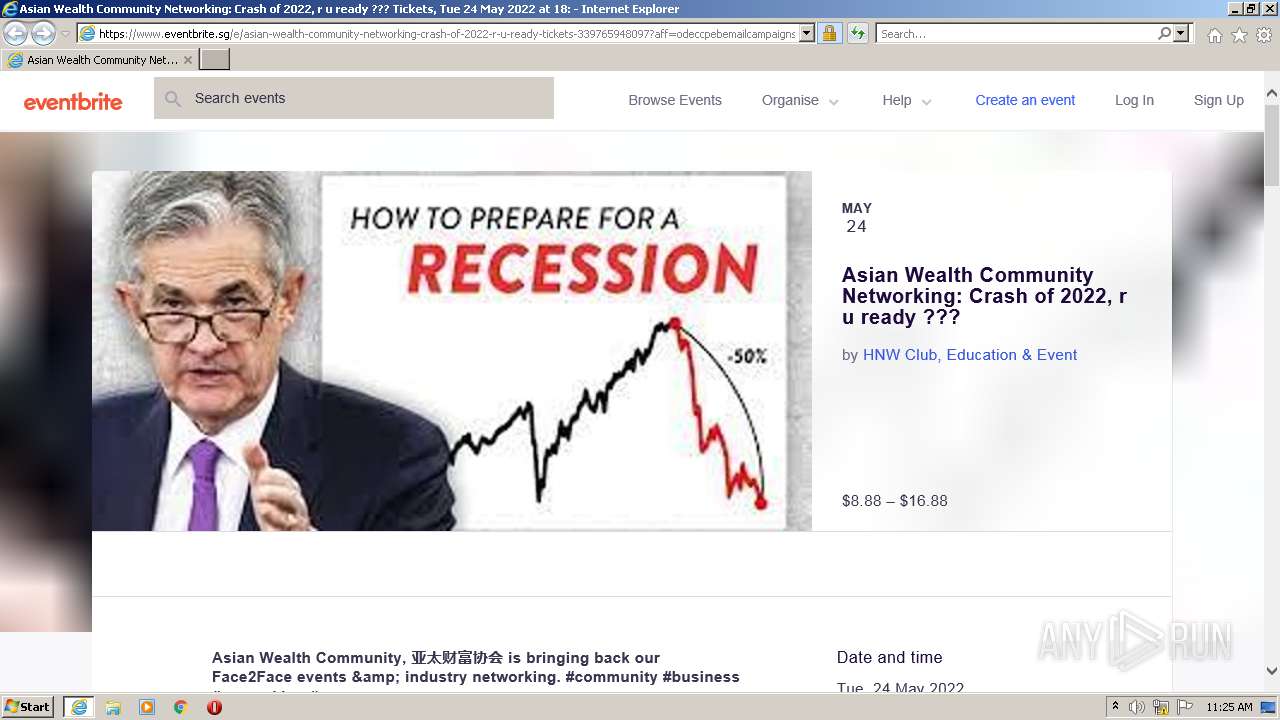
www.eventbrite.sg |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
cdn.evbstatic.com |
| whitelisted |
img.evbuc.com |
| whitelisted |
browser.sentry-cdn.com |
| whitelisted |
www.google.com |
| malicious |