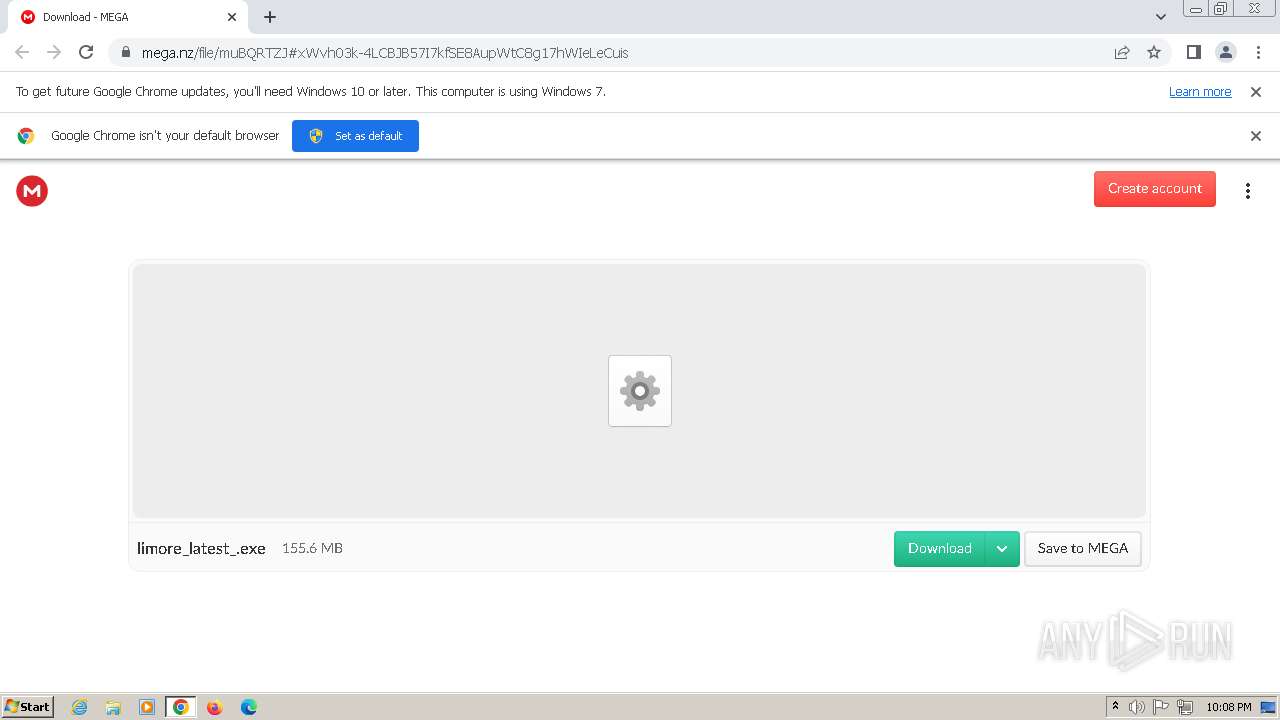
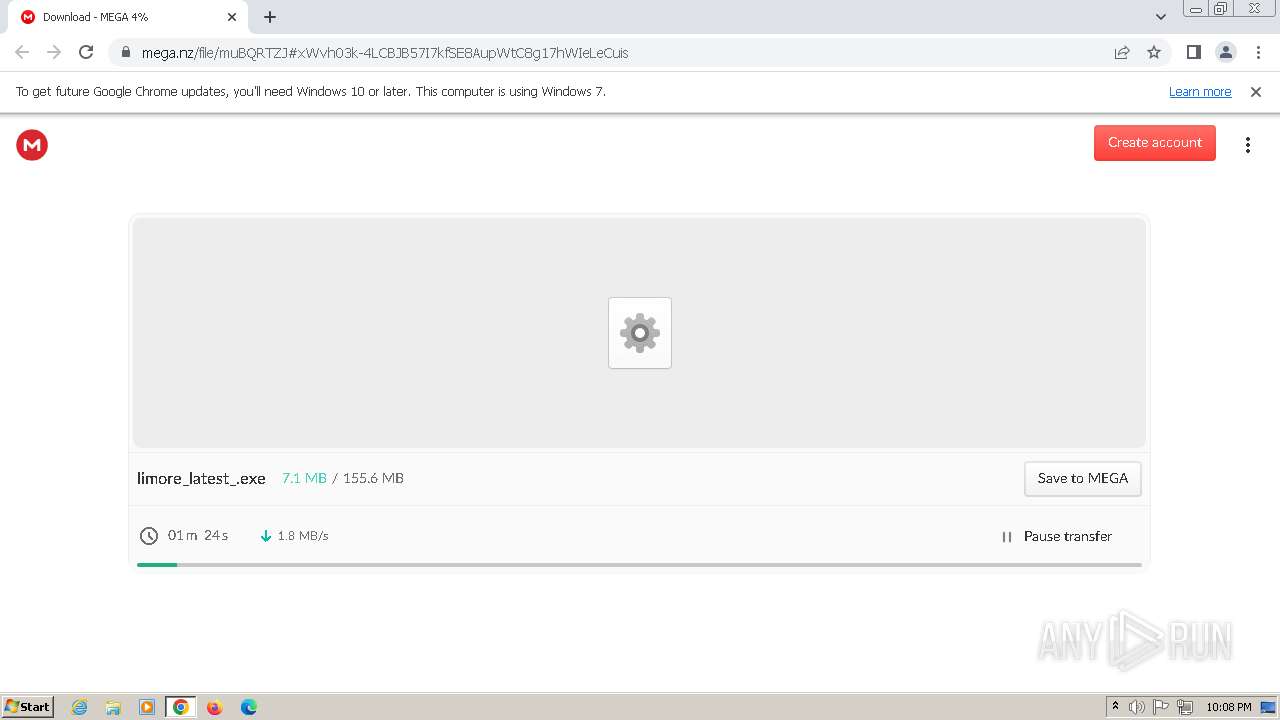
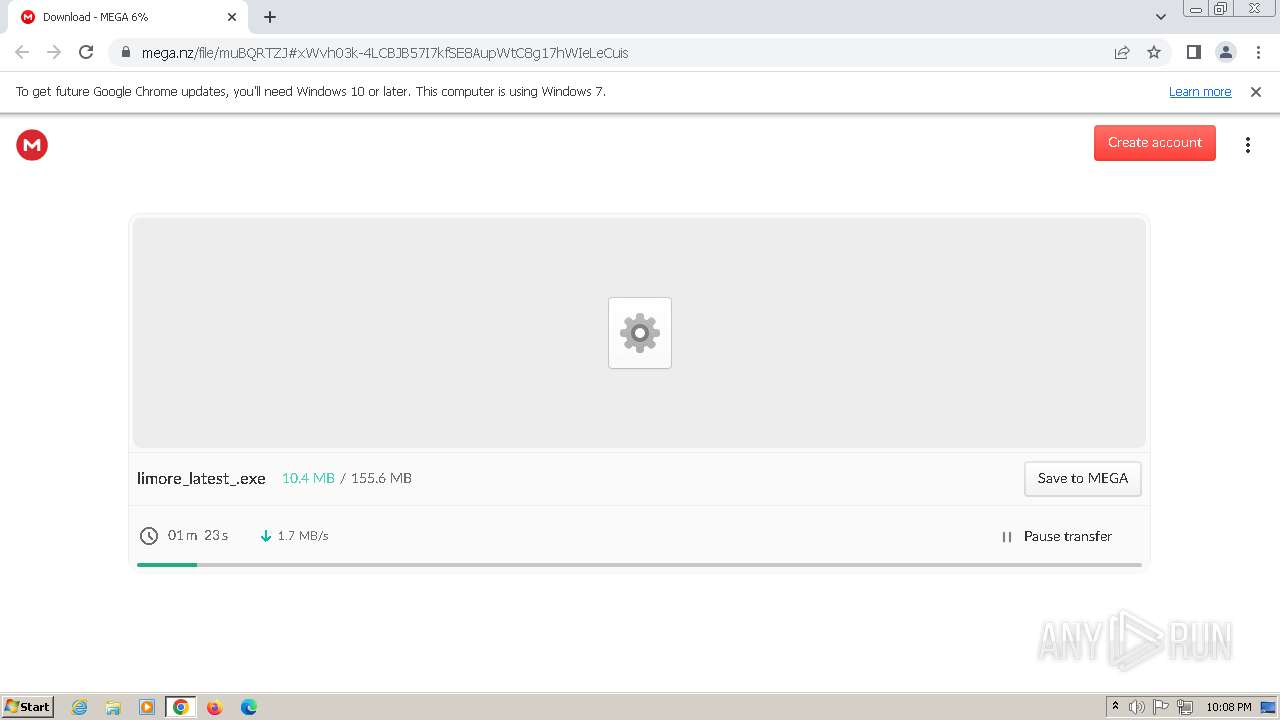
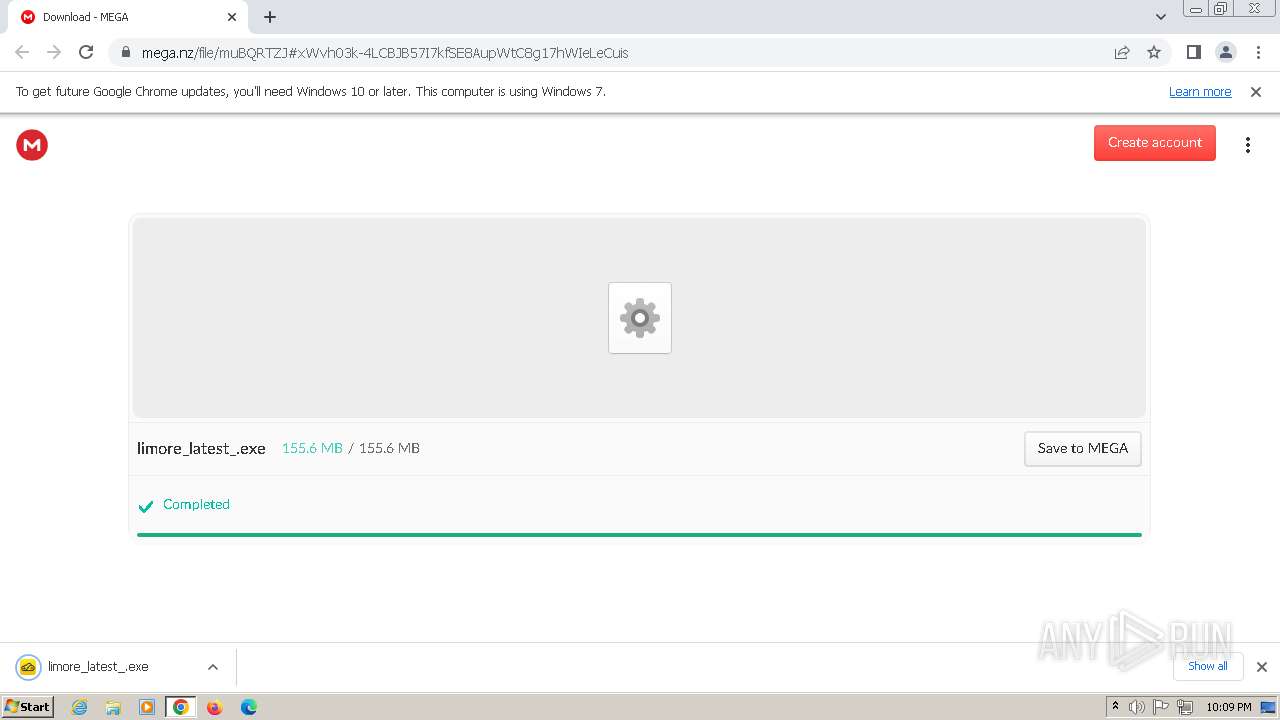
| URL: | https://mega.nz/file/muBQRTZJ#xWvh03k-4LCBJB57I7kfSE8AupWtC8g17hWIeLeCuis |
| Full analysis: | https://app.any.run/tasks/30366094-4fe0-4662-a60d-8c3366267140 |
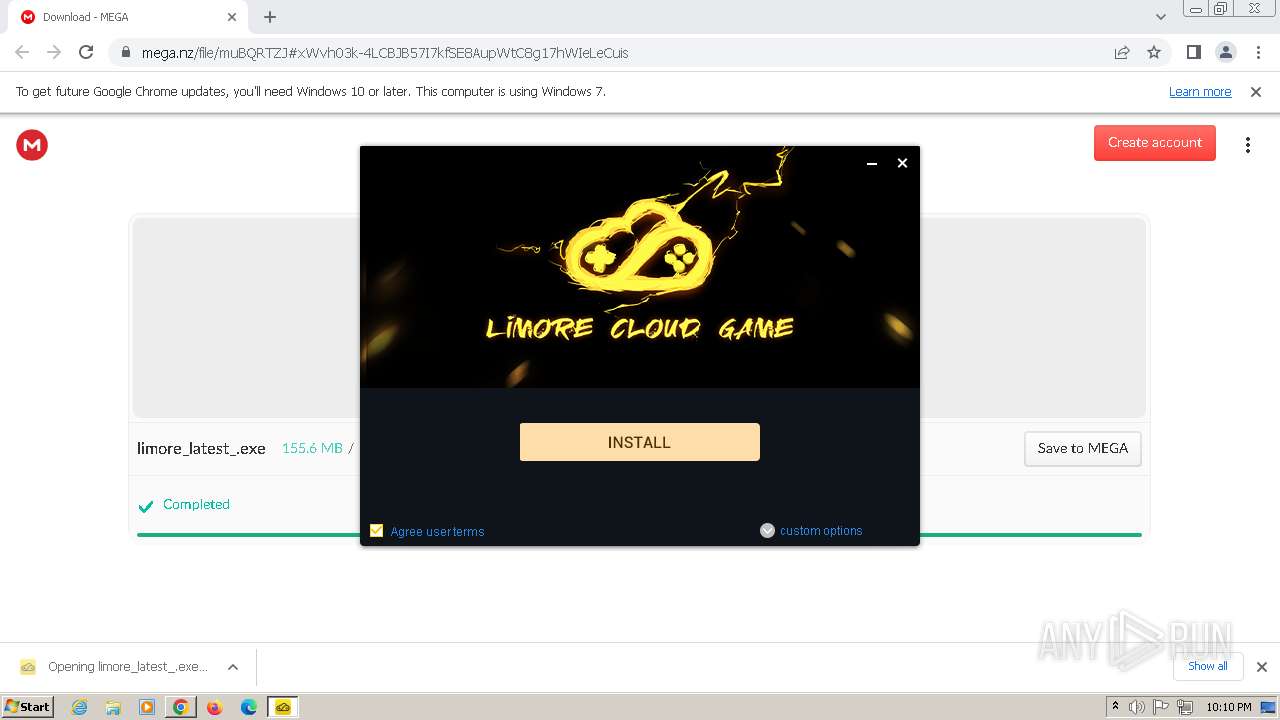
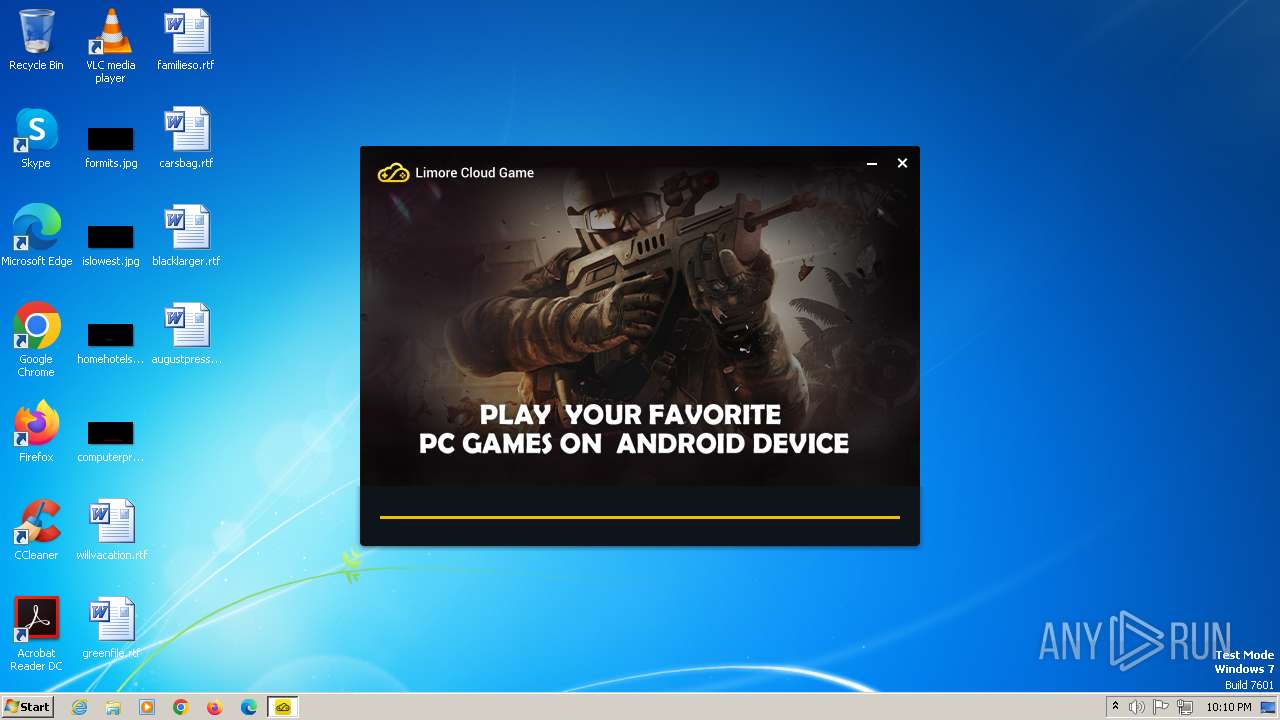
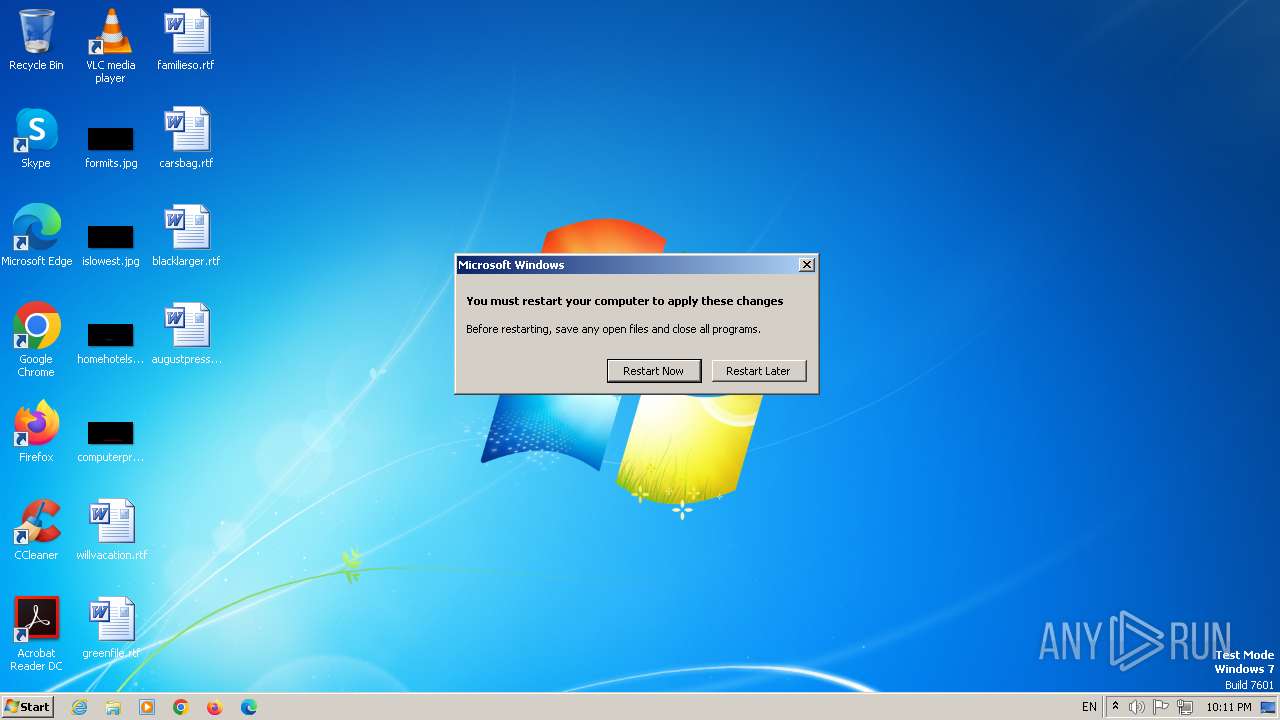
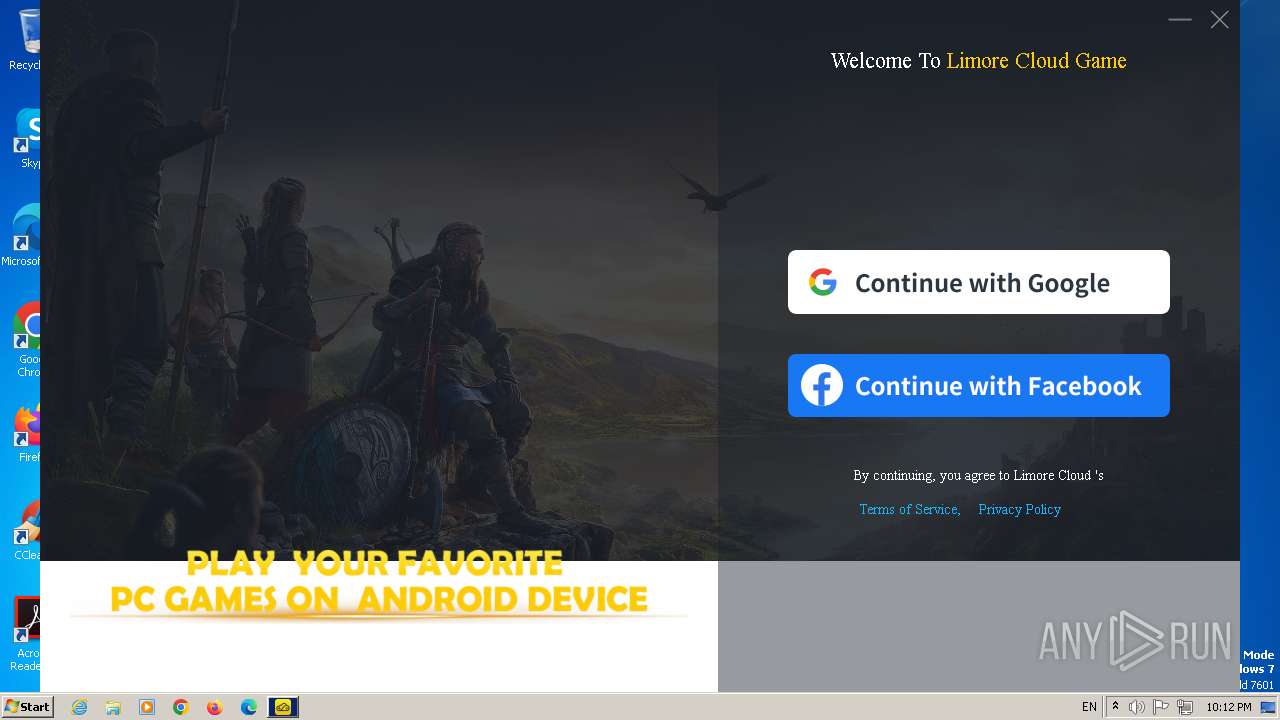
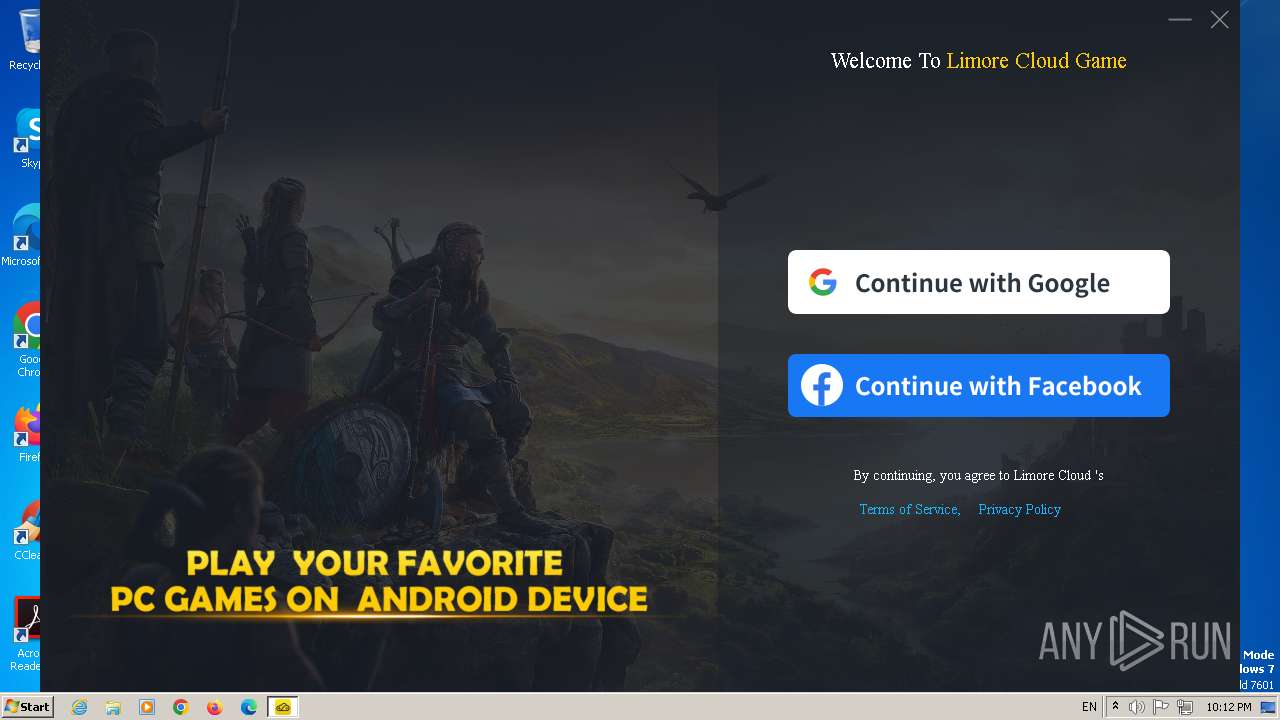
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2023, 22:07:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MD5: | 866E54AE619CA31262A50A38927656A0 |
| SHA1: | FEEC0C33D4E841273E401DBC64F7C2F83E4012F5 |
| SHA256: | 99F00A1A0E3E5562B536AB0E89563F4E3DFECA20642A33DC95D23C3967923B56 |
| SSDEEP: | 3:N8X/ien0hEevnC5ZVyRqC5ybo:2uCevnC7Y4C5Z |
MALICIOUS
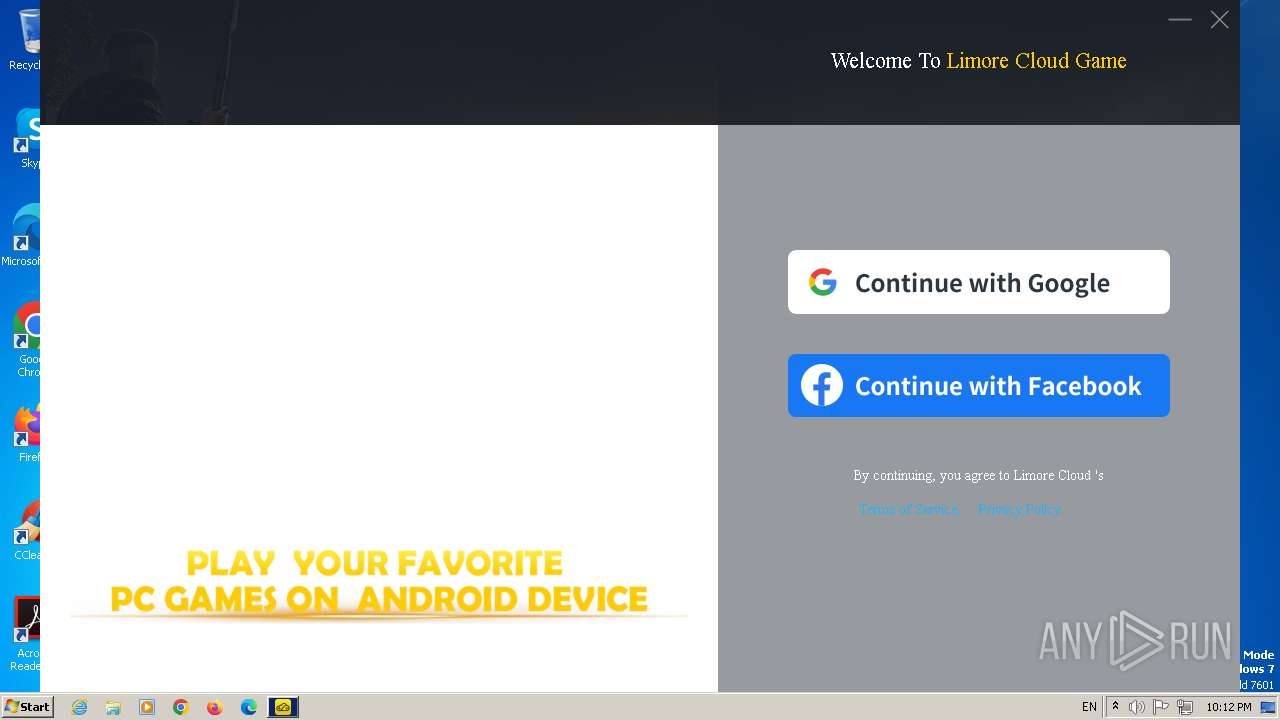
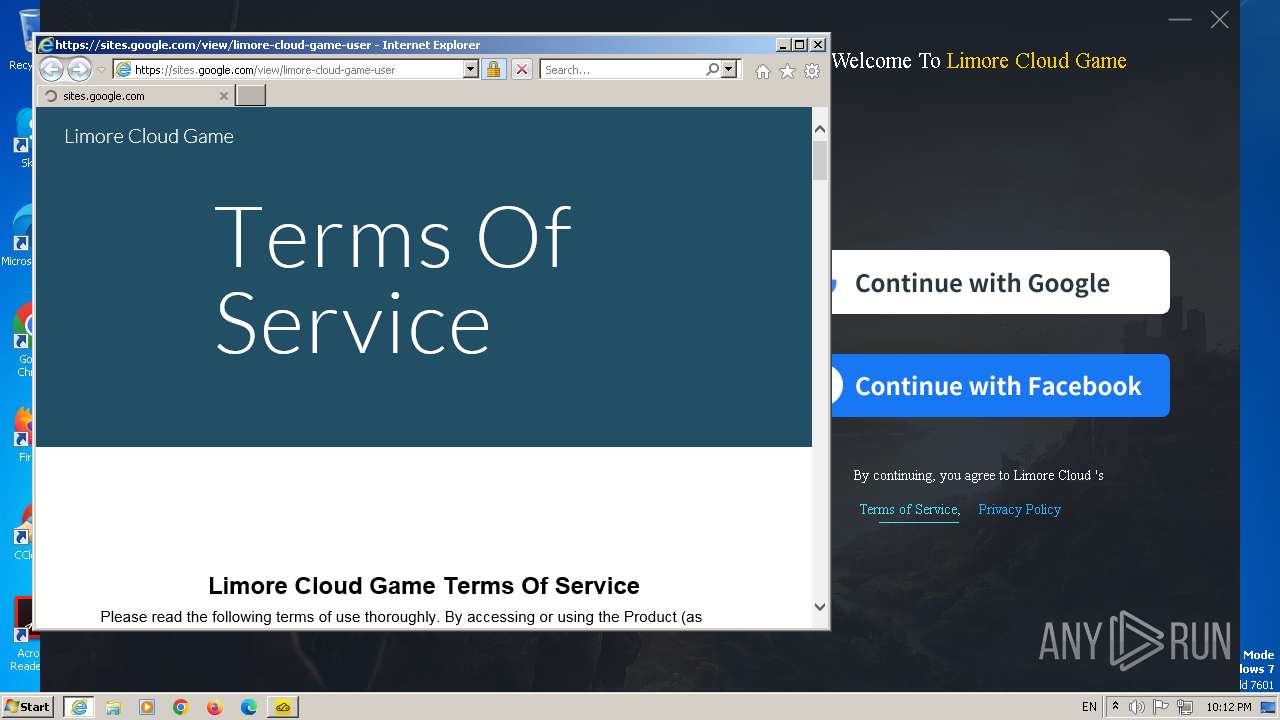
Actions looks like stealing of personal data
- limore_latest_.exe (PID: 2064)
- update.exe (PID: 1368)
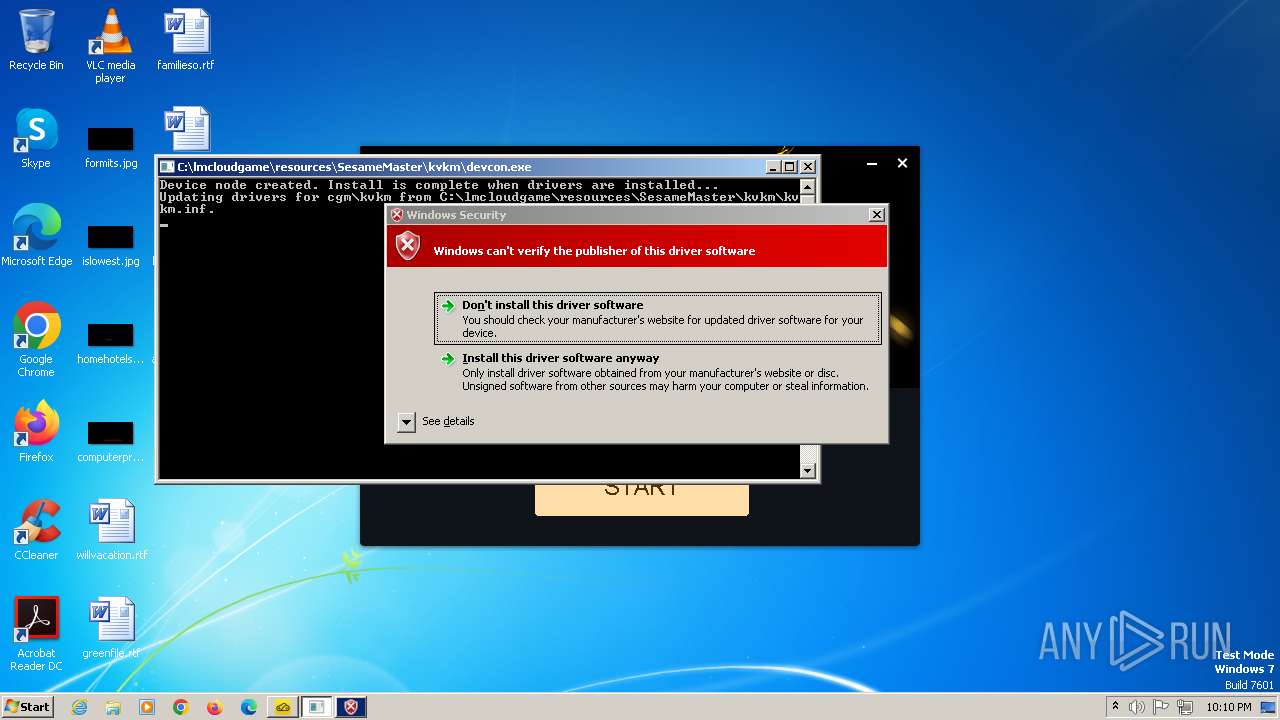
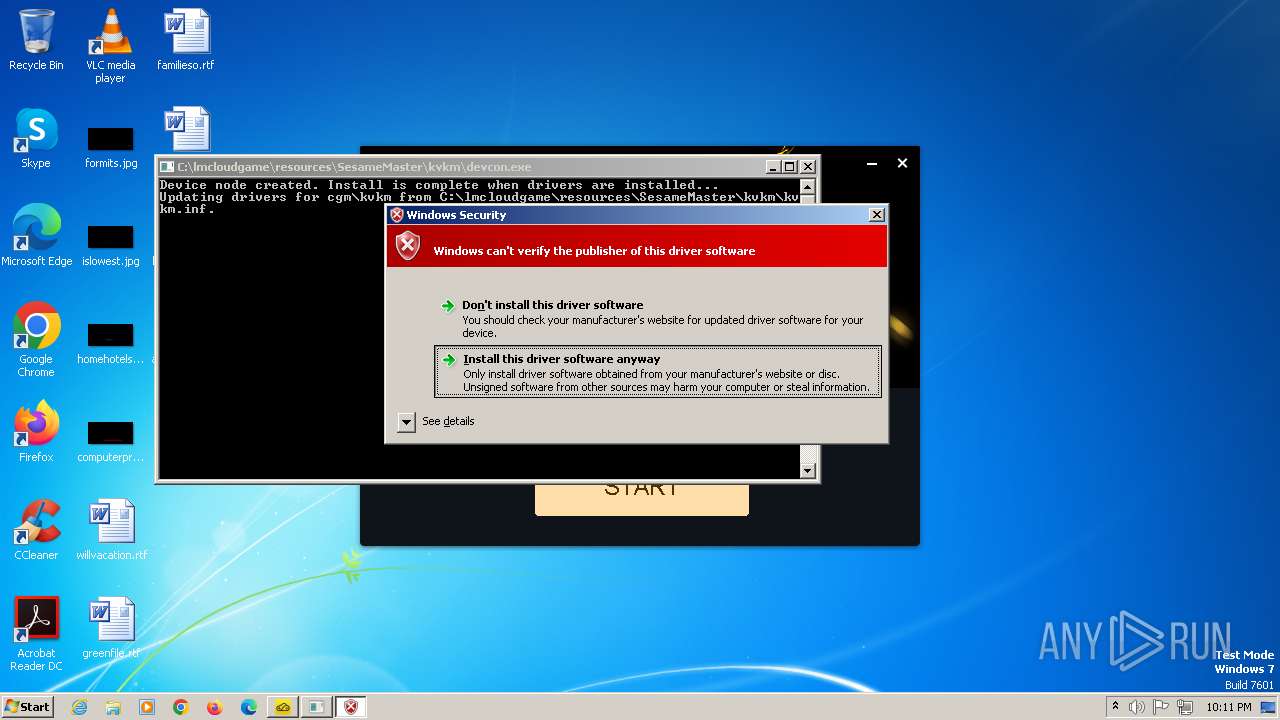
Create files in the Startup directory
- limore_latest_.exe (PID: 2064)
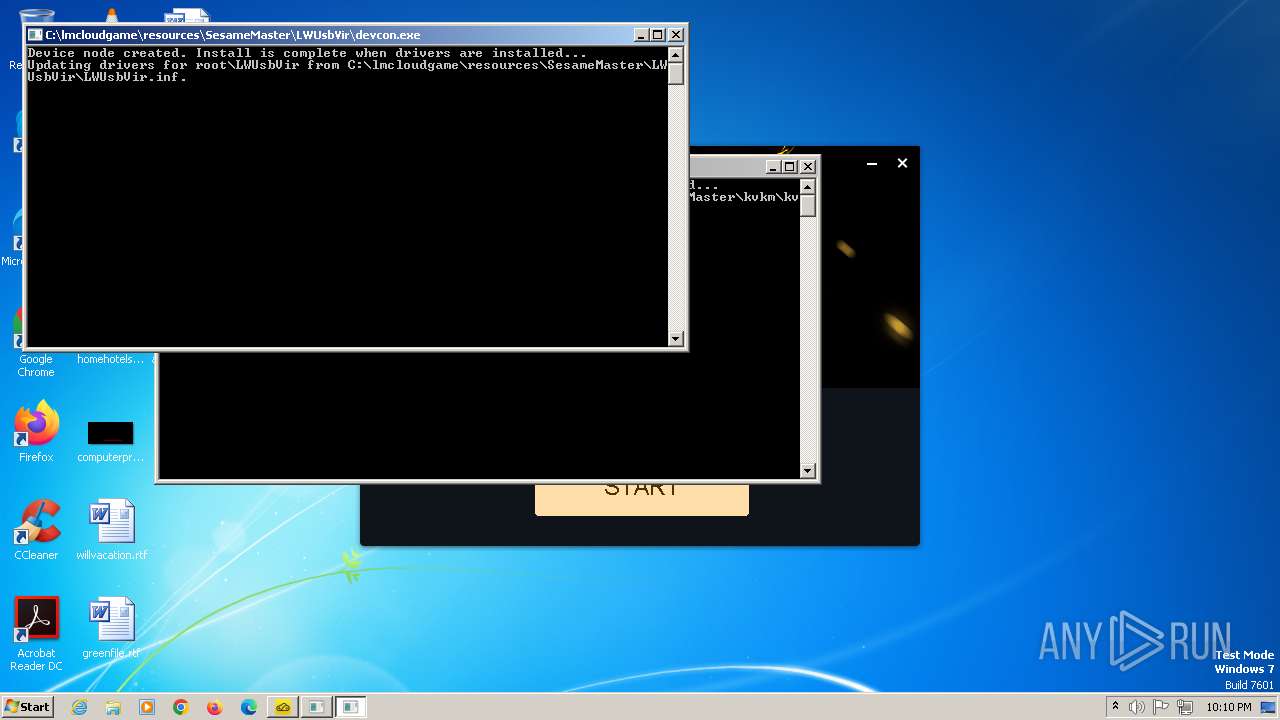
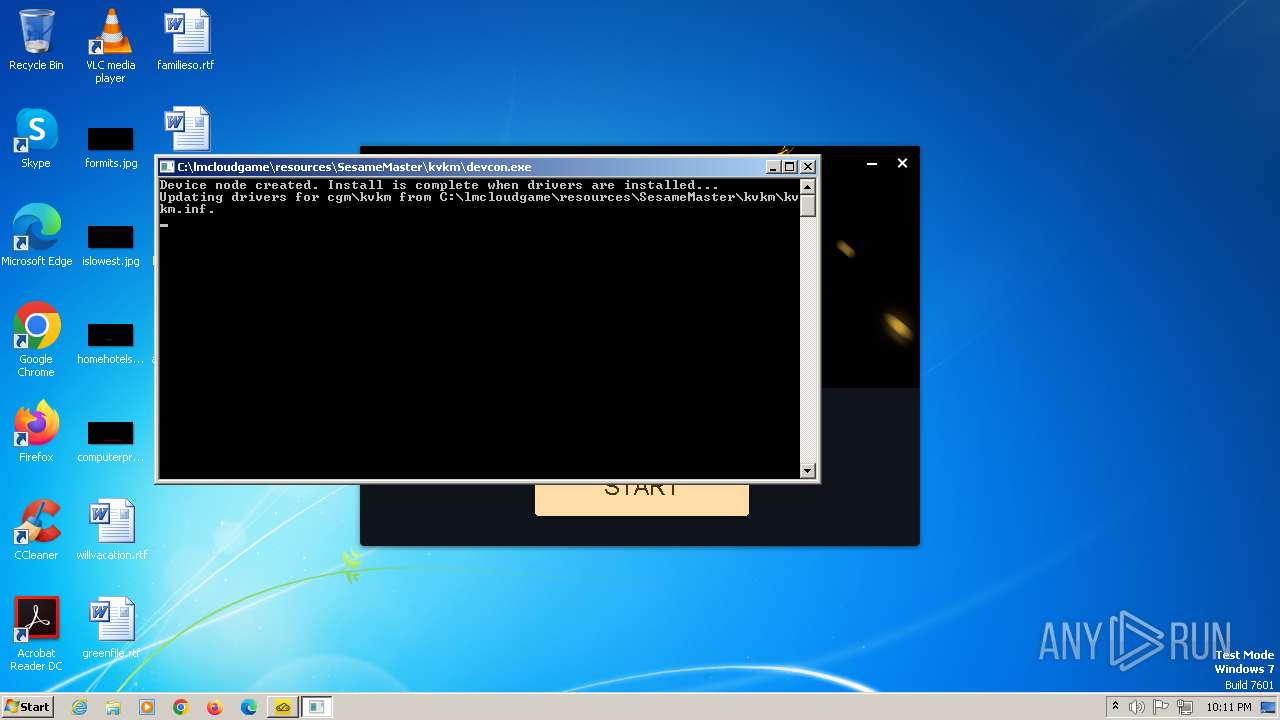
Drops the executable file immediately after the start
- ViGEmBus_1.21.442_x64_x86_arm64.exe (PID: 2336)
- limore_latest_.exe (PID: 2064)
- devcon.exe (PID: 2444)
- drvinst.exe (PID: 2720)
- devcon.exe (PID: 2456)
- drvinst.exe (PID: 1460)
- msiexec.exe (PID: 1268)
- drvinst.exe (PID: 2864)
- drvinst.exe (PID: 2056)
- limore-cloud-game.exe (PID: 3016)
- limore-cloud-game.exe (PID: 3156)
Creates a writable file in the system directory
- drvinst.exe (PID: 1460)
- drvinst.exe (PID: 2720)
- drvinst.exe (PID: 2056)
- drvinst.exe (PID: 2864)
UAC/LUA settings modification
- limore_latest_.exe (PID: 2064)
SUSPICIOUS
The process creates files with name similar to system file names
- limore_latest_.exe (PID: 2064)
Drops 7-zip archiver for unpacking
- limore_latest_.exe (PID: 2064)
Malware-specific behavior (creating "System.dll" in Temp)
- limore_latest_.exe (PID: 2064)
Process drops legitimate windows executable
- limore_latest_.exe (PID: 2064)
- drvinst.exe (PID: 1460)
- devcon.exe (PID: 2444)
Drops a system driver (possible attempt to evade defenses)
- limore_latest_.exe (PID: 2064)
- drvinst.exe (PID: 1460)
- devcon.exe (PID: 2444)
- devcon.exe (PID: 2456)
- drvinst.exe (PID: 2720)
- drvinst.exe (PID: 2864)
- drvinst.exe (PID: 2056)
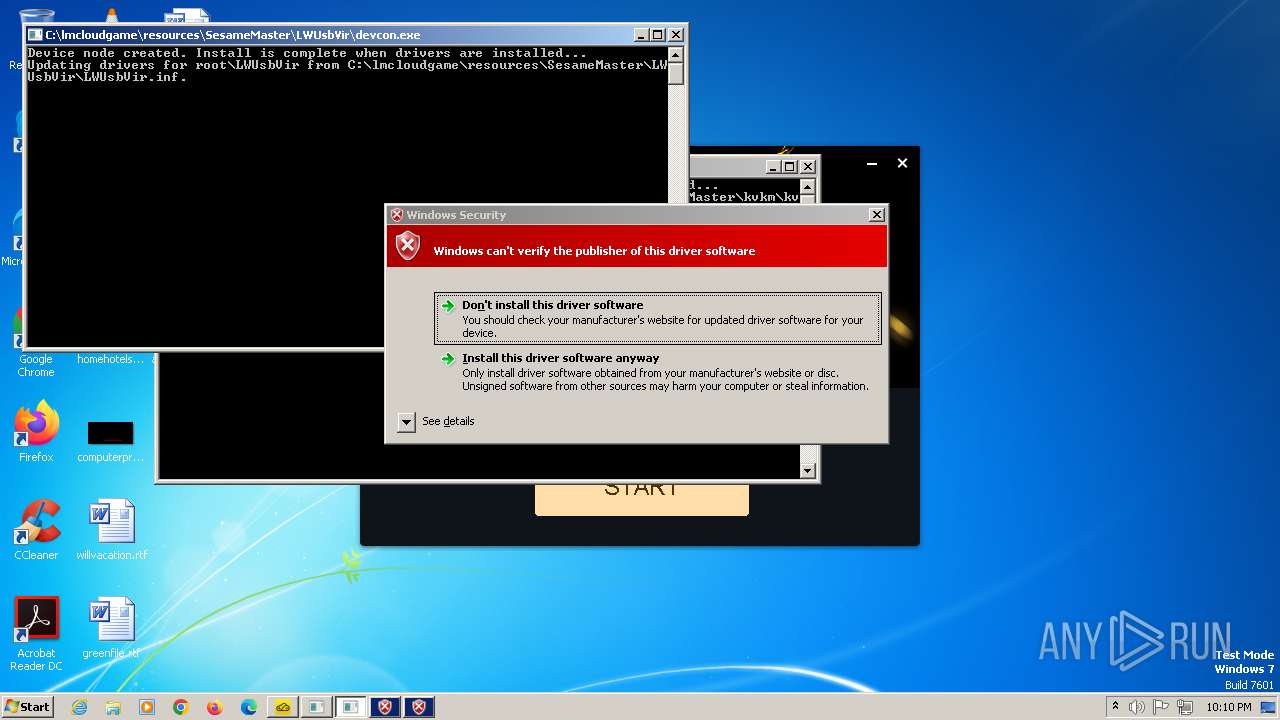
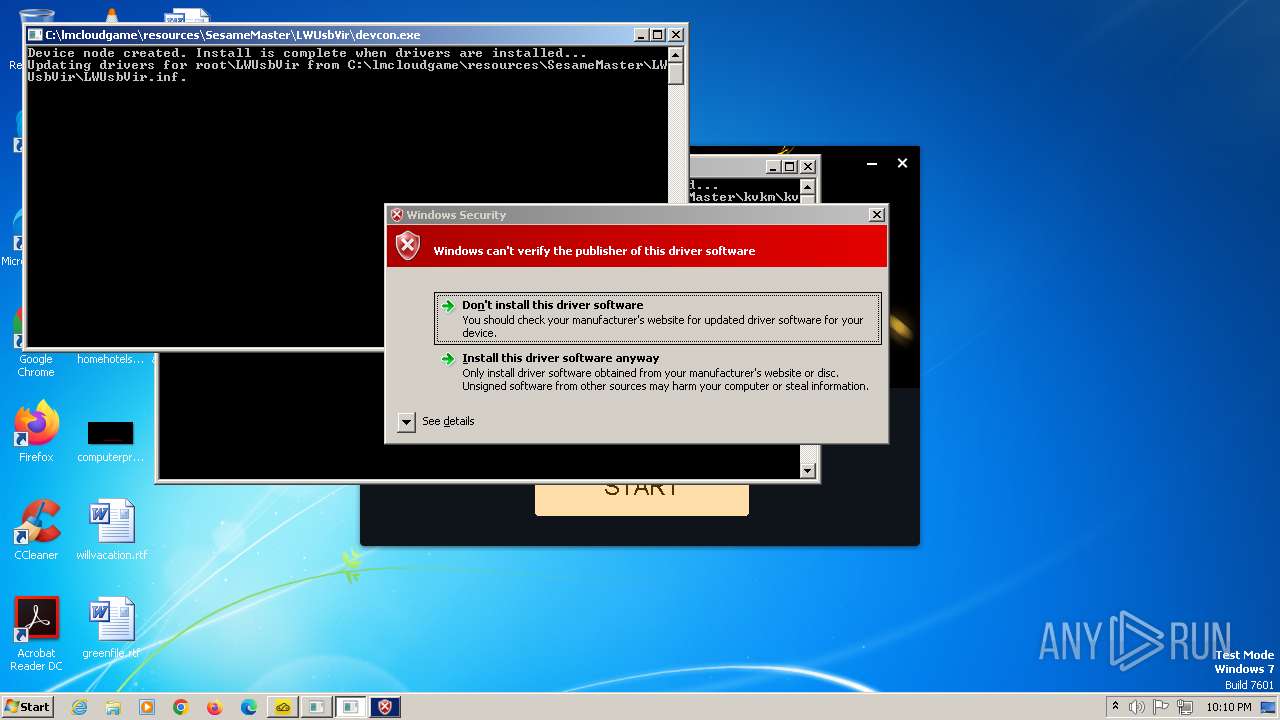
Checks Windows Trust Settings
- devcon.exe (PID: 2444)
- ViGEmBus_1.21.442_x64_x86_arm64.exe (PID: 2336)
- devcon.exe (PID: 2456)
- msiexec.exe (PID: 1268)
- drvinst.exe (PID: 2864)
- drvinst.exe (PID: 2056)
- drvinst.exe (PID: 304)
- drvinst.exe (PID: 2872)
- drvinst.exe (PID: 1368)
- drvinst.exe (PID: 2348)
Reads settings of System Certificates
- devcon.exe (PID: 2444)
- devcon.exe (PID: 2456)
- ViGEmBus_1.21.442_x64_x86_arm64.exe (PID: 2336)
- limore-cloud-game.exe (PID: 3016)
- update.exe (PID: 1368)
- limore-cloud-game.exe (PID: 3156)
Reads security settings of Internet Explorer
- devcon.exe (PID: 2444)
- devcon.exe (PID: 2456)
- ViGEmBus_1.21.442_x64_x86_arm64.exe (PID: 2336)
Creates files in the driver directory
- drvinst.exe (PID: 1460)
- drvinst.exe (PID: 2720)
- drvinst.exe (PID: 2864)
- drvinst.exe (PID: 2056)
Reads the Internet Settings
- ViGEmBus_1.21.442_x64_x86_arm64.exe (PID: 2336)
- rundll32.exe (PID: 1664)
- limore-cloud-game.exe (PID: 3016)
- limore-cloud-game.exe (PID: 3156)
- limore-cloud-game.exe (PID: 3440)
Adds/modifies Windows certificates
- ViGEmBus_1.21.442_x64_x86_arm64.exe (PID: 2336)
- msiexec.exe (PID: 1268)
- update.exe (PID: 1368)
Reads the Windows owner or organization settings
- ViGEmBus_1.21.442_x64_x86_arm64.exe (PID: 2336)
- msiexec.exe (PID: 1268)
Executes as Windows Service
- VSSVC.exe (PID: 2844)
The process drops C-runtime libraries
- limore_latest_.exe (PID: 2064)
Starts CMD.EXE for commands execution
- limore-cloud-game.exe (PID: 3016)
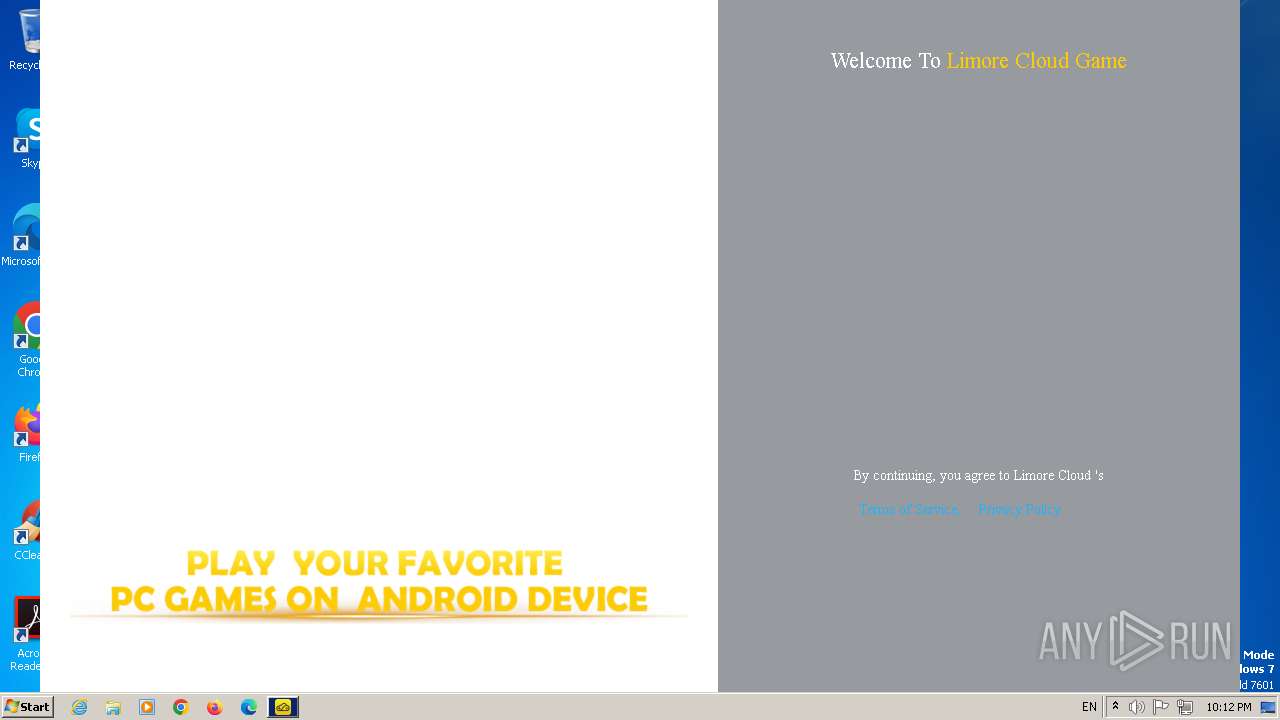
Application launched itself
- limore-cloud-game.exe (PID: 3016)
- limore-cloud-game.exe (PID: 3156)
INFO
The process uses the downloaded file
- chrome.exe (PID: 640)
- chrome.exe (PID: 776)
- chrome.exe (PID: 1940)
- chrome.exe (PID: 1036)
- chrome.exe (PID: 2744)
Application launched itself
- chrome.exe (PID: 1036)
Reads the computer name
- limore_latest_.exe (PID: 2064)
- devcon.exe (PID: 2456)
- devcon.exe (PID: 2444)
- ViGEmBus_1.21.442_x64_x86_arm64.exe (PID: 2336)
- drvinst.exe (PID: 1460)
- msiexec.exe (PID: 1268)
- drvinst.exe (PID: 2720)
- msiexec.exe (PID: 1128)
- msiexec.exe (PID: 3056)
- drvinst.exe (PID: 2864)
- drvinst.exe (PID: 2056)
- drvinst.exe (PID: 1844)
- drvinst.exe (PID: 1368)
- drvinst.exe (PID: 304)
- drvinst.exe (PID: 2872)
- drvinst.exe (PID: 2528)
- drvinst.exe (PID: 1936)
- drvinst.exe (PID: 2764)
- drvinst.exe (PID: 2348)
- drvinst.exe (PID: 2456)
- limore-cloud-game.exe (PID: 3016)
- limore-cloud-game.exe (PID: 2848)
- limore-cloud-game.exe (PID: 1076)
- update.exe (PID: 1368)
- limore-cloud-game.exe (PID: 2800)
- limore-cloud-game.exe (PID: 1208)
- limore-cloud-game.exe (PID: 2092)
- limore-cloud-game.exe (PID: 3312)
- limore-cloud-game.exe (PID: 3328)
- limore-cloud-game.exe (PID: 3568)
- limore-cloud-game.exe (PID: 3156)
- limore-cloud-game.exe (PID: 3440)
- limore-cloud-game.exe (PID: 3644)
Checks supported languages
- limore_latest_.exe (PID: 2064)
- devcon.exe (PID: 2456)
- devcon.exe (PID: 2444)
- ViGEmBus_1.21.442_x64_x86_arm64.exe (PID: 2336)
- drvinst.exe (PID: 1460)
- drvinst.exe (PID: 2720)
- msiexec.exe (PID: 1268)
- msiexec.exe (PID: 1128)
- msiexec.exe (PID: 3056)
- drvinst.exe (PID: 2864)
- drvinst.exe (PID: 2056)
- drvinst.exe (PID: 1368)
- drvinst.exe (PID: 2528)
- drvinst.exe (PID: 2872)
- drvinst.exe (PID: 1844)
- drvinst.exe (PID: 304)
- drvinst.exe (PID: 1936)
- drvinst.exe (PID: 2348)
- drvinst.exe (PID: 2764)
- drvinst.exe (PID: 2456)
- limore-cloud-game.exe (PID: 3016)
- limore-cloud-game.exe (PID: 1076)
- limore-cloud-game.exe (PID: 2848)
- limore-cloud-game.exe (PID: 2856)
- update.exe (PID: 1368)
- limore-cloud-game.exe (PID: 2800)
- limore-cloud-game.exe (PID: 1208)
- limore-cloud-game.exe (PID: 2304)
- limore-cloud-game.exe (PID: 2092)
- limore-cloud-game.exe (PID: 2552)
- limore-cloud-game.exe (PID: 3156)
- limore-cloud-game.exe (PID: 3328)
- limore-cloud-game.exe (PID: 3312)
- limore-cloud-game.exe (PID: 3336)
- limore-cloud-game.exe (PID: 3440)
- limore-cloud-game.exe (PID: 3568)
- limore-cloud-game.exe (PID: 3692)
- limore-cloud-game.exe (PID: 3644)
- limore-cloud-game.exe (PID: 3760)
Create files in a temporary directory
- limore_latest_.exe (PID: 2064)
- devcon.exe (PID: 2444)
- devcon.exe (PID: 2456)
- ViGEmBus_1.21.442_x64_x86_arm64.exe (PID: 2336)
- msiexec.exe (PID: 2520)
- rundll32.exe (PID: 2852)
- limore-cloud-game.exe (PID: 3016)
- limore-cloud-game.exe (PID: 3156)
Creates files in the program directory
- limore_latest_.exe (PID: 2064)
- ViGEmBus_1.21.442_x64_x86_arm64.exe (PID: 2336)
Reads the machine GUID from the registry
- devcon.exe (PID: 2444)
- ViGEmBus_1.21.442_x64_x86_arm64.exe (PID: 2336)
- devcon.exe (PID: 2456)
- drvinst.exe (PID: 1460)
- drvinst.exe (PID: 2720)
- msiexec.exe (PID: 1268)
- msiexec.exe (PID: 1128)
- msiexec.exe (PID: 3056)
- drvinst.exe (PID: 2864)
- drvinst.exe (PID: 2056)
- drvinst.exe (PID: 1844)
- drvinst.exe (PID: 304)
- drvinst.exe (PID: 2528)
- drvinst.exe (PID: 1368)
- drvinst.exe (PID: 1936)
- drvinst.exe (PID: 2348)
- drvinst.exe (PID: 2764)
- drvinst.exe (PID: 2456)
- drvinst.exe (PID: 2872)
- update.exe (PID: 1368)
- limore-cloud-game.exe (PID: 3016)
- limore-cloud-game.exe (PID: 3156)
Reads Environment values
- ViGEmBus_1.21.442_x64_x86_arm64.exe (PID: 2336)
- limore-cloud-game.exe (PID: 3016)
- limore-cloud-game.exe (PID: 2800)
- limore-cloud-game.exe (PID: 3156)
- limore-cloud-game.exe (PID: 3440)
Creates files or folders in the user directory
- ViGEmBus_1.21.442_x64_x86_arm64.exe (PID: 2336)
- rundll32.exe (PID: 2852)
- rundll32.exe (PID: 1756)
- limore-cloud-game.exe (PID: 2856)
- limore-cloud-game.exe (PID: 1076)
- limore-cloud-game.exe (PID: 3016)
- limore-cloud-game.exe (PID: 3156)
- limore-cloud-game.exe (PID: 3328)
Reads product name
- limore-cloud-game.exe (PID: 3016)
- limore-cloud-game.exe (PID: 2800)
- limore-cloud-game.exe (PID: 3156)
- limore-cloud-game.exe (PID: 3440)
Process checks computer location settings
- limore-cloud-game.exe (PID: 3016)
- limore-cloud-game.exe (PID: 2800)
- limore-cloud-game.exe (PID: 2304)
- limore-cloud-game.exe (PID: 2552)
- limore-cloud-game.exe (PID: 3156)
- limore-cloud-game.exe (PID: 3440)
- limore-cloud-game.exe (PID: 3692)
- limore-cloud-game.exe (PID: 3760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
118
Monitored processes
76
Malicious processes
13
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1440 --field-trial-handle=1148,i,7114154677758275406,9392342603969911364,131072 /prefetch:8 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 284 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --disable-quic --mojo-platform-channel-handle=3236 --field-trial-handle=1148,i,7114154677758275406,9392342603969911364,131072 /prefetch:8 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 304 | DrvInst.exe "1" "200" "HID\kvkm&Col04\1&2d595ca7&0&0003" "" "" "603e69cb7" "0000000000000000" "000000000000061C" "0000000000000630" | C:\Windows\System32\drvinst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 640 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3396 --field-trial-handle=1148,i,7114154677758275406,9392342603969911364,131072 /prefetch:8 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 776 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1096 --field-trial-handle=1148,i,7114154677758275406,9392342603969911364,131072 /prefetch:2 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 776 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3352 --field-trial-handle=1148,i,7114154677758275406,9392342603969911364,131072 /prefetch:8 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 776 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1832 --field-trial-handle=1148,i,7114154677758275406,9392342603969911364,131072 /prefetch:8 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1000 | C:\Windows\system32\cmd.exe /d /s /c "C:\lmcloudgame\update.exe" | C:\Windows\System32\cmd.exe | — | limore-cloud-game.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1036 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://mega.nz/file/muBQRTZJ#xWvh03k-4LCBJB57I7kfSE8AupWtC8g17hWIeLeCuis" | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1076 | "C:\lmcloudgame\limore-cloud-game.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Roaming\limore-cloud-game" --mojo-platform-channel-handle=1280 --field-trial-handle=1176,i,2542751213548327725,13050077800614815097,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:8 | C:\lmcloudgame\limore-cloud-game.exe | limore-cloud-game.exe | ||||||||||||
User: admin Company: Limore cloud Integrity Level: HIGH Description: limore-cloud-game Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
Total events
27 725
Read events
27 028
Write events
690
Delete events
7
Modification events
| (PID) Process: | (1036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (1036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1036) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (1036) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
156
Suspicious files
317
Text files
147
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF22b909.TMP | — | |
MD5:— | SHA256:— | |||
| 1036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C7925A6B262C5676D1C36638981A6EA | SHA256:07F6FB1E9CBCE4D15C00A9FBF9A95C1F31DE20C4C48B433198862E8759CD128D | |||
| 1036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:0C72670573294869D03666D769ED7C66 | SHA256:— | |||
| 1036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF22b909.TMP | text | |
MD5:C6D185D8A4B1BEEF3316D60882DABFE5 | SHA256:3D1A9C960141CFAC6F3F6F0ADEA6D65EC4058E795F34B75C4BD4A0629EA52EC2 | |||
| 1036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | text | |
MD5:BEB86D981077CAE20D5D7F61F208C684 | SHA256:— | |||
| 1036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 1036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 1036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF22bfa1.TMP | — | |
MD5:— | SHA256:— | |||
| 1036 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
76
DNS requests
50
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | US | binary | 5.60 Kb | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | US | binary | 7.67 Kb | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | US | binary | 9.43 Kb | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acwcdm4bj7lx4xbm2ireywxlhvca_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win64_adsurwm4gclupf32xdrpgdnapira.crx3 | US | binary | 35.3 Kb | unknown |
884 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acwcdm4bj7lx4xbm2ireywxlhvca_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win64_adsurwm4gclupf32xdrpgdnapira.crx3 | US | binary | 1.61 Kb | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acwcdm4bj7lx4xbm2ireywxlhvca_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win64_adsurwm4gclupf32xdrpgdnapira.crx3 | US | binary | 73.1 Kb | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acwcdm4bj7lx4xbm2ireywxlhvca_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win64_adsurwm4gclupf32xdrpgdnapira.crx3 | US | binary | 42.4 Kb | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acwcdm4bj7lx4xbm2ireywxlhvca_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win64_adsurwm4gclupf32xdrpgdnapira.crx3 | US | binary | 188 Kb | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acwcdm4bj7lx4xbm2ireywxlhvca_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win64_adsurwm4gclupf32xdrpgdnapira.crx3 | US | binary | 21.1 Kb | unknown |
884 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | US | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
324 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1956 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1036 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2868 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | unknown |
2868 | chrome.exe | 31.216.145.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | unknown |
2868 | chrome.exe | 142.250.186.138:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
2868 | chrome.exe | 66.203.127.13:443 | eu.static.mega.co.nz | MEGA Cloud Services Limited | NZ | unknown |
2868 | chrome.exe | 66.203.125.12:443 | g.api.mega.co.nz | Datacenter Luxembourg S.A. | LU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mega.nz |
| whitelisted |
accounts.google.com |
| shared |
content-autofill.googleapis.com |
| whitelisted |
eu.static.mega.co.nz |
| shared |
g.api.mega.co.nz |
| shared |
gfs214n176.userstorage.mega.co.nz |
| unknown |
optimizationguide-pa.googleapis.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2868 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
2868 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
2868 | chrome.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
2868 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
2868 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
2868 | chrome.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
2868 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
2868 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
2868 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
2868 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |