| File name: | CCSetup.exe |
| Full analysis: | https://app.any.run/tasks/82beab2d-d04e-40b6-87dc-f87dc573bbea |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2025, 22:13:01 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 7DE41EA51E2C5A4DB90DD1DD5658C4BD |
| SHA1: | F4E1D1289B97CA9312B082EFF9A010FBAB0DD7FF |
| SHA256: | 99D9B3E49C9EAED0615AAF6289A235FF9F39CB5C3B7382D6F51304A6EC04594A |
| SSDEEP: | 98304:u9V8taQEx5Tf+S+PJYfVHtpy6bcxQ8I7MEAIe/vgbBuMHWM9cBgVt+2ffM0uA1+l:UU8ORV |
MALICIOUS
Executing a file with an untrusted certificate
- CCSetup.exe (PID: 6852)
- CCSetup.exe (PID: 1760)
- CCSetup.exe (PID: 5424)
- ISBEW64.exe (PID: 2976)
- ISBEW64.exe (PID: 2792)
- ISBEW64.exe (PID: 1484)
- ISBEW64.exe (PID: 436)
- ISBEW64.exe (PID: 760)
- ISBEW64.exe (PID: 4012)
- ISBEW64.exe (PID: 4684)
- ISBEW64.exe (PID: 5716)
- ISBEW64.exe (PID: 6344)
- ISBEW64.exe (PID: 5928)
- ComboCleaner.Guard.exe (PID: 5904)
- ComboCleaner.WinService.exe (PID: 4456)
- ComboCleaner.exe (PID: 4156)
- ComboCleaner.exe (PID: 7084)
Connects to the CnC server
- CCSetup.exe (PID: 1760)
Changes the autorun value in the registry
- rundll32.exe (PID: 5744)
- rundll32.exe (PID: 3608)
- rundll32.exe (PID: 6344)
- CCSetup.exe (PID: 5424)
- ComboCleaner.WinService.exe (PID: 4456)
Starts NET.EXE for service management
- cmd.exe (PID: 3748)
- net.exe (PID: 6256)
- cmd.exe (PID: 3196)
- net.exe (PID: 6748)
- cmd.exe (PID: 5952)
- net.exe (PID: 7116)
SUSPICIOUS
Process drops legitimate windows executable
- CCSetup.exe (PID: 1760)
- msiexec.exe (PID: 5348)
Executable content was dropped or overwritten
- CCSetup.exe (PID: 1760)
- CCSetup.exe (PID: 5424)
- rundll32.exe (PID: 5744)
- rundll32.exe (PID: 3608)
- rundll32.exe (PID: 6344)
- ComboCleaner.Guard.exe (PID: 5904)
- ComboCleaner.WinService.exe (PID: 4456)
Starts itself from another location
- CCSetup.exe (PID: 1760)
Reads security settings of Internet Explorer
- CCSetup.exe (PID: 5424)
- CCSetup.exe (PID: 1760)
- msiexec.exe (PID: 5348)
- ComboCleaner.WinService.exe (PID: 4456)
- ComboCleaner.Guard.exe (PID: 5904)
- ComboCleaner.exe (PID: 4156)
- ComboCleaner.exe (PID: 7084)
Reads the Windows owner or organization settings
- CCSetup.exe (PID: 5424)
- msiexec.exe (PID: 5348)
There is functionality for taking screenshot (YARA)
- CCSetup.exe (PID: 1760)
- CCSetup.exe (PID: 5424)
Uses DRIVERQUERY.EXE to obtain a list of installed device drivers
- cmd.exe (PID: 5644)
Contacting a server suspected of hosting an CnC
- CCSetup.exe (PID: 1760)
Starts CMD.EXE for commands execution
- CCSetup.exe (PID: 5424)
- ComboCleaner.WinService.exe (PID: 4456)
Reads Microsoft Outlook installation path
- CCSetup.exe (PID: 5424)
Reads Internet Explorer settings
- CCSetup.exe (PID: 5424)
Creates a software uninstall entry
- CCSetup.exe (PID: 5424)
- ComboCleaner.WinService.exe (PID: 4456)
Searches for installed software
- CCSetup.exe (PID: 5424)
- ComboCleaner.WinService.exe (PID: 4456)
Uses RUNDLL32.EXE to load library
- CCSetup.exe (PID: 5424)
Drops a system driver (possible attempt to evade defenses)
- rundll32.exe (PID: 5744)
- msiexec.exe (PID: 5348)
- rundll32.exe (PID: 3608)
- rundll32.exe (PID: 6344)
Creates or modifies Windows services
- rundll32.exe (PID: 3608)
- rundll32.exe (PID: 6344)
- ComboCleaner.WinService.exe (PID: 4456)
Sets the service to start on system boot
- sc.exe (PID: 1484)
- sc.exe (PID: 2664)
Reads the date of Windows installation
- ComboCleaner.WinService.exe (PID: 4456)
Executes as Windows Service
- ComboCleaner.Guard.exe (PID: 5904)
- ComboCleaner.WinService.exe (PID: 4456)
- WmiApSrv.exe (PID: 4644)
- WmiApSrv.exe (PID: 7268)
The process checks if it is being run in the virtual environment
- ComboCleaner.WinService.exe (PID: 4456)
Application launched itself
- ComboCleaner.exe (PID: 4156)
The process deletes folder without confirmation
- CCSetup.exe (PID: 5424)
INFO
The sample compiled with english language support
- CCSetup.exe (PID: 1760)
- CCSetup.exe (PID: 5424)
- msiexec.exe (PID: 5348)
- rundll32.exe (PID: 5744)
- rundll32.exe (PID: 3608)
- rundll32.exe (PID: 6344)
- ComboCleaner.WinService.exe (PID: 4456)
- ComboCleaner.Guard.exe (PID: 5904)
Creates files in the program directory
- CCSetup.exe (PID: 1760)
- CCSetup.exe (PID: 5424)
- ComboCleaner.WinService.exe (PID: 4456)
- ComboCleaner.Guard.exe (PID: 5904)
Reads the computer name
- CCSetup.exe (PID: 1760)
- CCSetup.exe (PID: 5424)
- msiexec.exe (PID: 5348)
- ISBEW64.exe (PID: 2792)
- msiexec.exe (PID: 2368)
- ISBEW64.exe (PID: 1484)
- ISBEW64.exe (PID: 760)
- ISBEW64.exe (PID: 4012)
- ISBEW64.exe (PID: 4684)
- ISBEW64.exe (PID: 2976)
- ISBEW64.exe (PID: 436)
- ISBEW64.exe (PID: 5716)
- ISBEW64.exe (PID: 6344)
- ISBEW64.exe (PID: 5928)
- msiexec.exe (PID: 3936)
- ComboCleaner.Guard.exe (PID: 5904)
- ComboCleaner.WinService.exe (PID: 4456)
- ComboCleaner.exe (PID: 4156)
- ComboCleaner.exe (PID: 7084)
Checks supported languages
- CCSetup.exe (PID: 1760)
- msiexec.exe (PID: 5348)
- msiexec.exe (PID: 2368)
- ISBEW64.exe (PID: 2792)
- ISBEW64.exe (PID: 2976)
- ISBEW64.exe (PID: 1484)
- ISBEW64.exe (PID: 760)
- ISBEW64.exe (PID: 436)
- CCSetup.exe (PID: 5424)
- ISBEW64.exe (PID: 4012)
- ISBEW64.exe (PID: 4684)
- ISBEW64.exe (PID: 5716)
- ISBEW64.exe (PID: 6344)
- ISBEW64.exe (PID: 5928)
- msiexec.exe (PID: 3936)
- ComboCleaner.Guard.exe (PID: 5904)
- ComboCleaner.WinService.exe (PID: 4456)
- ComboCleaner.exe (PID: 7084)
- ComboCleaner.exe (PID: 4156)
Create files in a temporary directory
- CCSetup.exe (PID: 1760)
- CCSetup.exe (PID: 5424)
Creates files or folders in the user directory
- CCSetup.exe (PID: 5424)
- ComboCleaner.exe (PID: 7084)
Checks proxy server information
- CCSetup.exe (PID: 1760)
- CCSetup.exe (PID: 5424)
- slui.exe (PID: 7776)
- ComboCleaner.exe (PID: 7084)
Reads the machine GUID from the registry
- CCSetup.exe (PID: 5424)
- msiexec.exe (PID: 5348)
- ComboCleaner.WinService.exe (PID: 4456)
- ComboCleaner.Guard.exe (PID: 5904)
- ComboCleaner.exe (PID: 4156)
- ComboCleaner.exe (PID: 7084)
Reads the software policy settings
- CCSetup.exe (PID: 5424)
- msiexec.exe (PID: 5348)
- ComboCleaner.WinService.exe (PID: 4456)
- ComboCleaner.Guard.exe (PID: 5904)
- ComboCleaner.exe (PID: 7084)
- slui.exe (PID: 7776)
UPX packer has been detected
- CCSetup.exe (PID: 1760)
- CCSetup.exe (PID: 5424)
Creates a software uninstall entry
- msiexec.exe (PID: 5348)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5348)
Creates files in the driver directory
- rundll32.exe (PID: 5744)
- rundll32.exe (PID: 3608)
- rundll32.exe (PID: 6344)
Launching a file from a Registry key
- rundll32.exe (PID: 5744)
- rundll32.exe (PID: 3608)
- rundll32.exe (PID: 6344)
- CCSetup.exe (PID: 5424)
- ComboCleaner.WinService.exe (PID: 4456)
Reads the time zone
- runonce.exe (PID: 760)
- runonce.exe (PID: 4196)
- runonce.exe (PID: 6492)
- ComboCleaner.WinService.exe (PID: 4456)
Reads security settings of Internet Explorer
- runonce.exe (PID: 760)
- runonce.exe (PID: 4196)
- runonce.exe (PID: 6492)
Process checks computer location settings
- CCSetup.exe (PID: 5424)
Reads Environment values
- ComboCleaner.WinService.exe (PID: 4456)
- ComboCleaner.Guard.exe (PID: 5904)
- ComboCleaner.exe (PID: 7084)
Disables trace logs
- ComboCleaner.WinService.exe (PID: 4456)
- ComboCleaner.Guard.exe (PID: 5904)
- ComboCleaner.exe (PID: 7084)
Reads CPU info
- ComboCleaner.WinService.exe (PID: 4456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:06:20 19:44:34+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 622080 |
| InitializedDataSize: | 780288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x59e5a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.67.0 |
| ProductVersionNumber: | 1.0.67.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
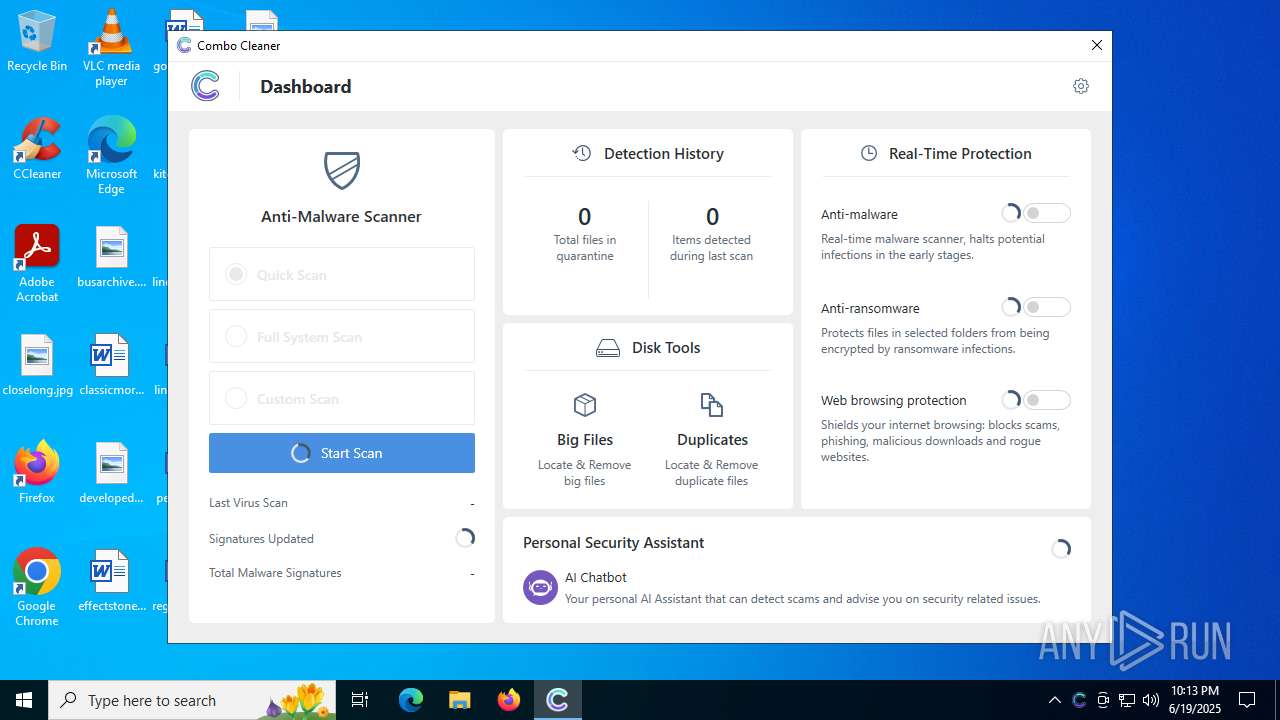
| CompanyName: | RCS LT |
| FileDescription: | Combo Cleaner |
| FileVersion: | 1.0.67.0 |
| InternalName: | Setup |
| LegalCopyright: | Copyright (c) 2024 RCS LT, UAB. All Rights Reserved. |
| OriginalFileName: | CCSetup.exe |
| ProductName: | Combo Cleaner |
| ProductVersion: | 1.0.67.0 |
| InternalBuildNumber: | 202227 |
| ISInternalVersion: | 26.0.720 |
| ISInternalDescription: | Setup Launcher Unicode |
Total processes
204
Monitored processes
54
Malicious processes
8
Suspicious processes
16
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 436 | C:\Users\admin\AppData\Local\Temp\{1060FD9B-B371-4FF7-A255-F0FFC9CA88FD}\ISBEW64.exe {EFB7539B-24F3-46B6-AF6E-3B021B51EFEF}:{23737D57-C118-4A45-8161-61711FF8890C} | C:\Users\admin\AppData\Local\Temp\{1060FD9B-B371-4FF7-A255-F0FFC9CA88FD}\ISBEW64.exe | — | CCSetup.exe | |||||||||||
User: admin Company: Flexera Integrity Level: HIGH Description: InstallShield (R) 64-bit Setup Engine Exit code: 0 Version: 26.0.720 Modules
| |||||||||||||||
| 728 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 760 | C:\Users\admin\AppData\Local\Temp\{1060FD9B-B371-4FF7-A255-F0FFC9CA88FD}\ISBEW64.exe {EFB7539B-24F3-46B6-AF6E-3B021B51EFEF}:{93BBD58E-1592-4DA6-8D94-E56598CBC18B} | C:\Users\admin\AppData\Local\Temp\{1060FD9B-B371-4FF7-A255-F0FFC9CA88FD}\ISBEW64.exe | — | CCSetup.exe | |||||||||||
User: admin Company: Flexera Integrity Level: HIGH Description: InstallShield (R) 64-bit Setup Engine Exit code: 0 Version: 26.0.720 Modules
| |||||||||||||||
| 760 | "C:\WINDOWS\system32\runonce.exe" -r | C:\Windows\System32\runonce.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 868 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1484 | C:\Users\admin\AppData\Local\Temp\{1060FD9B-B371-4FF7-A255-F0FFC9CA88FD}\ISBEW64.exe {EFB7539B-24F3-46B6-AF6E-3B021B51EFEF}:{45A0CA36-24BC-48F6-A11A-54E467B388D1} | C:\Users\admin\AppData\Local\Temp\{1060FD9B-B371-4FF7-A255-F0FFC9CA88FD}\ISBEW64.exe | — | CCSetup.exe | |||||||||||
User: admin Company: Flexera Integrity Level: HIGH Description: InstallShield (R) 64-bit Setup Engine Exit code: 0 Version: 26.0.720 Modules
| |||||||||||||||
| 1484 | "C:\Windows\SysWOW64\sc.exe" config ComboCleaner.WinService start=auto | C:\Windows\SysWOW64\sc.exe | — | CCSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1700 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1760 | "C:\Users\admin\AppData\Local\Temp\CCSetup.exe" | C:\Users\admin\AppData\Local\Temp\CCSetup.exe | explorer.exe | ||||||||||||
User: admin Company: RCS LT Integrity Level: HIGH Description: Combo Cleaner Exit code: 0 Version: 1.0.67.0 Modules
| |||||||||||||||
| 1936 | "C:\Windows\System32\grpconv.exe" -o | C:\Windows\System32\grpconv.exe | — | runonce.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
45 043
Read events
44 657
Write events
370
Delete events
16
Modification events
| (PID) Process: | (5424) CCSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion |
| Operation: | delete value | Name: | %IS_PREREQ%-Combo Cleaner |
Value: | |||
| (PID) Process: | (5424) CCSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion |
| Operation: | delete value | Name: | %IS_PREREQF%-Combo Cleaner |
Value: | |||
| (PID) Process: | (5424) CCSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | delete value | Name: | ISSetupPrerequisistes |
Value: | |||
| (PID) Process: | (5424) CCSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5424) CCSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5424) CCSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1760) CCSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1760) CCSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1760) CCSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5424) CCSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFavoritesInitialSelection |
Value: | |||
Executable files
95
Suspicious files
3 860
Text files
57
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1760 | CCSetup.exe | C:\Users\admin\AppData\Local\Temp\A1D26E2\65031306E0.tmp | executable | |
MD5:FE50297191B241C60616F04E2FEBB8BB | SHA256:E8ADC6E787862B84A865B06A8EFAECB272F618CC8733B9AE686496418BA6B35B | |||
| 1760 | CCSetup.exe | C:\Users\admin\AppData\Local\Temp\{44DF9687-5B6C-4C8B-A3D2-FFDDBDE2C0DF}\_ISMSIDEL.INI | text | |
MD5:FE927EE66DB26C74D9F9A5AAC25078CD | SHA256:860A90F4E2FB5153E54733CFA0BBA3BC15C3B106D28E62329F528A8034765591 | |||
| 1760 | CCSetup.exe | C:\Users\admin\AppData\Local\Temp\~6522.tmp | text | |
MD5:E8C4DB7E72F0C84A72E6E08CF8E7D10B | SHA256:5BF7B082ED0F731C57EA5C1A63CB30DF9C68100A8ACC37EE4568DC1FB891EF33 | |||
| 1760 | CCSetup.exe | C:\Program Files\Common Files\System\symsrv.dll | executable | |
MD5:7574CF2C64F35161AB1292E2F532AABF | SHA256:DE055A89DE246E629A8694BDE18AF2B1605E4B9B493C7E4AEF669DD67ACF5085 | |||
| 1760 | CCSetup.exe | C:\Users\admin\AppData\Local\Temp\{44DF9687-5B6C-4C8B-A3D2-FFDDBDE2C0DF}\CCSetup.exe | executable | |
MD5:7DE41EA51E2C5A4DB90DD1DD5658C4BD | SHA256:99D9B3E49C9EAED0615AAF6289A235FF9F39CB5C3B7382D6F51304A6EC04594A | |||
| 1760 | CCSetup.exe | C:\Users\admin\AppData\Local\Temp\~6533.tmp | text | |
MD5:E8C4DB7E72F0C84A72E6E08CF8E7D10B | SHA256:5BF7B082ED0F731C57EA5C1A63CB30DF9C68100A8ACC37EE4568DC1FB891EF33 | |||
| 5424 | CCSetup.exe | C:\Users\admin\AppData\Local\Temp\A1D26E2\66A918041530.tmp | executable | |
MD5:FE50297191B241C60616F04E2FEBB8BB | SHA256:E8ADC6E787862B84A865B06A8EFAECB272F618CC8733B9AE686496418BA6B35B | |||
| 1760 | CCSetup.exe | C:\Users\admin\AppData\Local\Temp\~6534.tmp | text | |
MD5:E8C4DB7E72F0C84A72E6E08CF8E7D10B | SHA256:5BF7B082ED0F731C57EA5C1A63CB30DF9C68100A8ACC37EE4568DC1FB891EF33 | |||
| 5424 | CCSetup.exe | C:\Users\admin\AppData\Local\Temp\{44DF9687-5B6C-4C8B-A3D2-FFDDBDE2C0DF}\Setup.INI | text | |
MD5:E8C4DB7E72F0C84A72E6E08CF8E7D10B | SHA256:5BF7B082ED0F731C57EA5C1A63CB30DF9C68100A8ACC37EE4568DC1FB891EF33 | |||
| 1760 | CCSetup.exe | C:\Users\admin\AppData\Local\Temp\~6545.tmp | text | |
MD5:E8C4DB7E72F0C84A72E6E08CF8E7D10B | SHA256:5BF7B082ED0F731C57EA5C1A63CB30DF9C68100A8ACC37EE4568DC1FB891EF33 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
60
DNS requests
35
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6376 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
9464 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
9596 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5424 | CCSetup.exe | GET | 200 | 104.18.21.213:80 | http://e5.c.lencr.org/47.crl | unknown | — | — | whitelisted |
5424 | CCSetup.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEA%2B4p0C5FY0DUUO8WdnwQCk%3D | unknown | — | — | whitelisted |
1760 | CCSetup.exe | GET | 200 | 76.223.54.146:80 | http://www.aieov.com/logo.gif | unknown | — | — | malicious |
2140 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.48.23.180:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1760 | CCSetup.exe | GET | 200 | 76.223.54.146:80 | http://www.aieov.com/logo.gif | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4648 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5424 | CCSetup.exe | 104.25.186.50:443 | services.combocleaner.com | CLOUDFLARENET | US | unknown |
5424 | CCSetup.exe | 104.18.21.213:80 | e5.c.lencr.org | CLOUDFLARENET | — | whitelisted |
5424 | CCSetup.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1760 | CCSetup.exe | 76.223.54.146:80 | www.aieov.com | AMAZON-02 | US | malicious |
2336 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
services.combocleaner.com |
| unknown |
e5.c.lencr.org |
| whitelisted |
5isohu.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.aieov.com |
| malicious |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1760 | CCSetup.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |
1760 | CCSetup.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |
1760 | CCSetup.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |
1760 | CCSetup.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |
1760 | CCSetup.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |
1760 | CCSetup.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Possible Floxif CnC Communication |